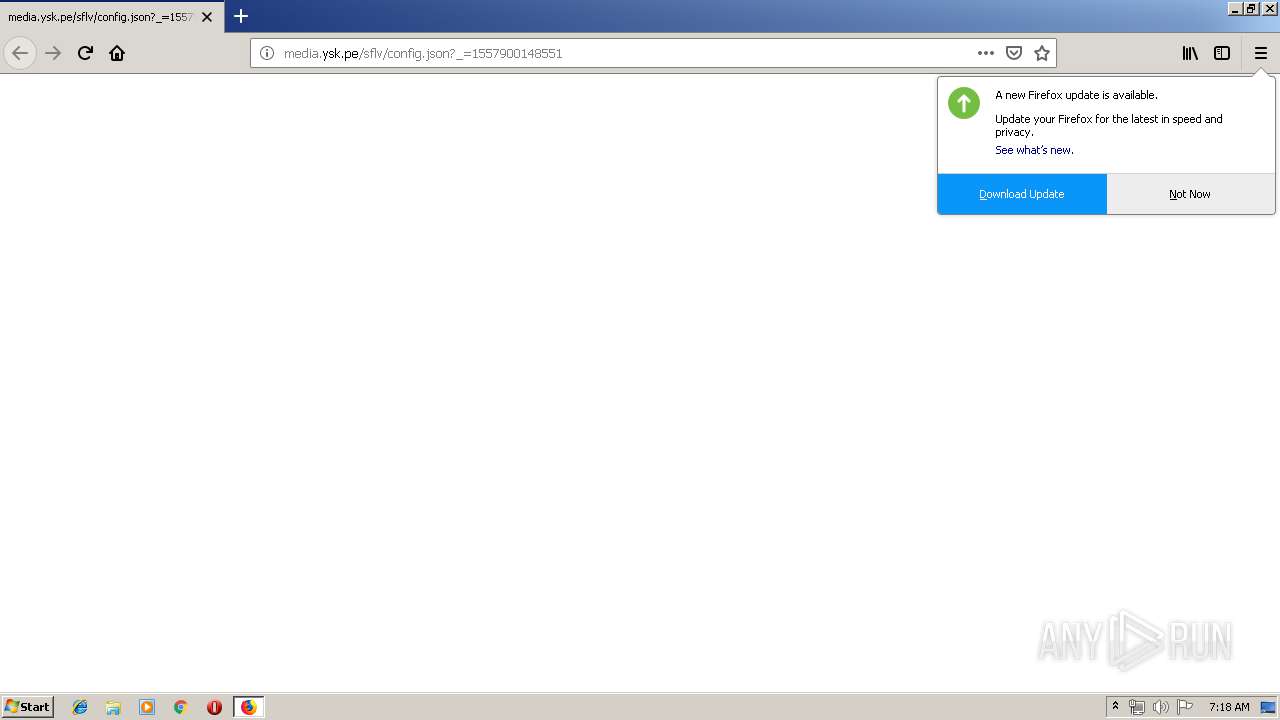
| URL: | http://media.ysk.pe/sflv/config.json?_=1557900148551 |
| Full analysis: | https://app.any.run/tasks/a565f471-9302-47a7-bf12-b82b9b8b2c15 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 06:18:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5A65BCB556918E2693ACA1D7A65BB017 |
| SHA1: | CDBDD96E1B23385D0BFE58F097BC5B51E901EEAE |
| SHA256: | 4E04976E3B7B5C70D651CF10BAB5C0D05FD7CB59154636DBD2142A2F6FE0FE62 |
| SSDEEP: | 3:N1KTFicWOyqXSKu6YJFJU:Cp/WOy051YJFa |
MALICIOUS
Connects to CnC server
- firefox.exe (PID: 2860)
SUSPICIOUS
Executable content was dropped or overwritten
- firefox.exe (PID: 2860)
Creates files in the program directory
- firefox.exe (PID: 2860)
INFO
Application launched itself
- firefox.exe (PID: 2860)
Creates files in the user directory
- firefox.exe (PID: 2860)
Reads CPU info
- firefox.exe (PID: 2860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2776 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2860.20.931168104\194060414" -childID 3 -isForBrowser -prefsHandle 3252 -prefMapHandle 3404 -prefsLen 5824 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2860 "\\.\pipe\gecko-crash-server-pipe.2860" 3380 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2860 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://media.ysk.pe/sflv/config.json?_=1557900148551 | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 3276 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2860.6.1002748484\545621460" -childID 1 -isForBrowser -prefsHandle 792 -prefMapHandle 1532 -prefsLen 1 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2860 "\\.\pipe\gecko-crash-server-pipe.2860" 1748 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 3888 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2860.0.480228716\920549496" -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - "C:\Users\admin\AppData\LocalLow\Mozilla\Temp-{ce348e4c-7d33-445e-89f9-60108c51bcaf}" 2860 "\\.\pipe\gecko-crash-server-pipe.2860" 1160 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 3896 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2860.13.4941295\1926756952" -childID 2 -isForBrowser -prefsHandle 2536 -prefMapHandle 1984 -prefsLen 216 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2860 "\\.\pipe\gecko-crash-server-pipe.2860" 2660 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
Total events
548
Read events
546
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2860) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2860) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
54
Text files
21
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2860 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2860 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2860 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2860 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2860 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2860 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\FFB67DC1A94183F06F834DB9CC8014B6AAB26B3B | der | |
MD5:— | SHA256:— | |||
| 2860 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 2860 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashsubdoc-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 2860 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashsubdoc-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
| 2860 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\google4\goog-badbinurl-proto.metadata | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
21
DNS requests
50
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2860 | firefox.exe | GET | — | 195.22.26.248:80 | http://media.ysk.pe/sflv/config.json?_=1557900148551 | PT | — | — | malicious |
2860 | firefox.exe | GET | — | 195.22.26.248:80 | http://media.ysk.pe/sflv/config.json?_=1557900148551 | PT | — | — | malicious |
2860 | firefox.exe | POST | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2860 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2860 | firefox.exe | POST | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2860 | firefox.exe | POST | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2860 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2860 | firefox.exe | GET | 200 | 2.16.106.209:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2860 | firefox.exe | GET | — | 195.22.26.248:80 | http://media.ysk.pe/favicon.ico | PT | — | — | malicious |
2860 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2860 | firefox.exe | 195.22.26.248:80 | media.ysk.pe | Claranet Ltd | PT | malicious |
2860 | firefox.exe | 52.26.166.58:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2860 | firefox.exe | 2.16.106.209:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2860 | firefox.exe | 172.217.18.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2860 | firefox.exe | 52.36.109.121:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2860 | firefox.exe | 52.27.144.31:443 | aus5.mozilla.org | Amazon.com, Inc. | US | unknown |
2860 | firefox.exe | 143.204.101.101:443 | tracking-protection.cdn.mozilla.net | — | US | malicious |
2860 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2860 | firefox.exe | 172.217.23.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
media.ysk.pe |
| malicious |
detectportal.firefox.com |
| whitelisted |
aus5.mozilla.org |
| whitelisted |
balrog-aus5.r53-2.services.mozilla.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2860 | firefox.exe | A Network Trojan was detected | ET CNC Ransomware Tracker Reported CnC Server group 63 |