| File name: | SandeLLoCHECKER_Installer.exe |
| Full analysis: | https://app.any.run/tasks/e47e3dc1-c24a-4a42-8a60-b8c0f49677e5 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2024, 21:16:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8A0591A6B534E32FA179F2D781B79026 |
| SHA1: | 61E1AFF6F862CBCE0E1F6E9E70D186E5013D9846 |
| SHA256: | 4DF8350850592B587C4D2AAABDDC8454BC4652DF0082B85C3336139A9C6EA53E |
| SSDEEP: | 98304:I1jGCCHTimtt+Sz2o+oXtuunddvk7WlX66rG2/9Q/oMQ0WEBkcWYWJh/Jl5gKLwU:vXEeov |
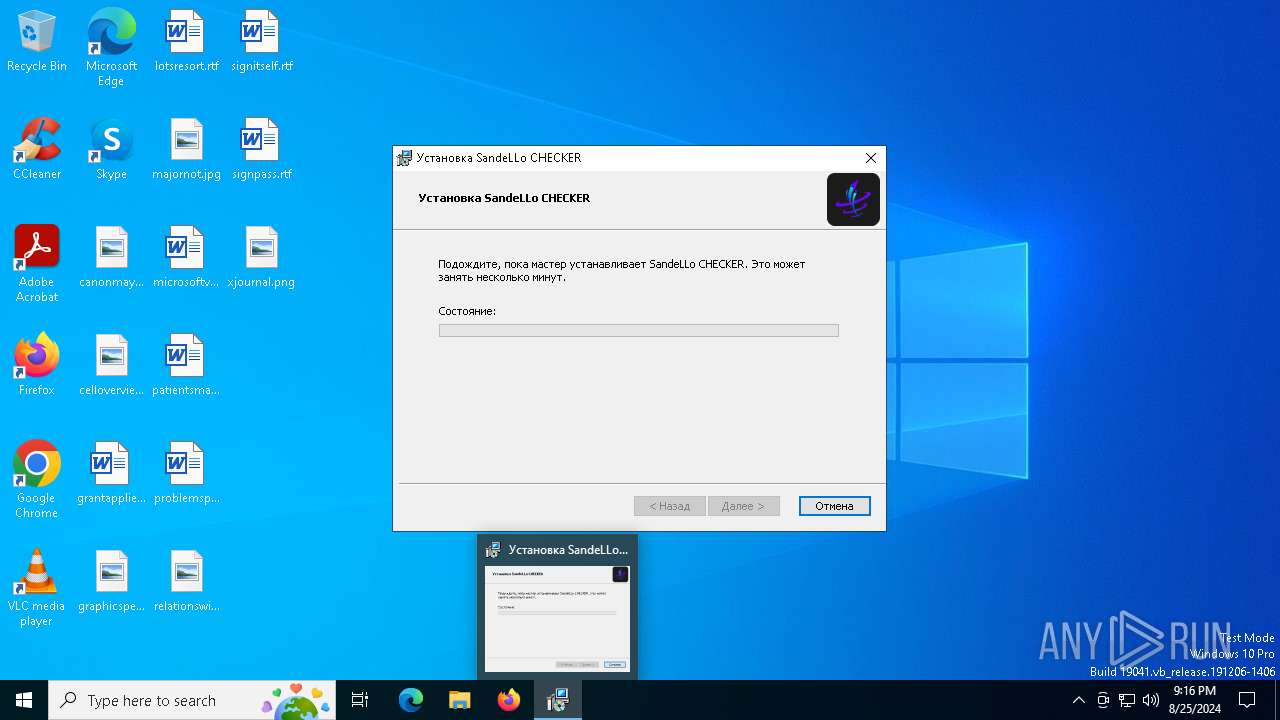
MALICIOUS
No malicious indicators.SUSPICIOUS
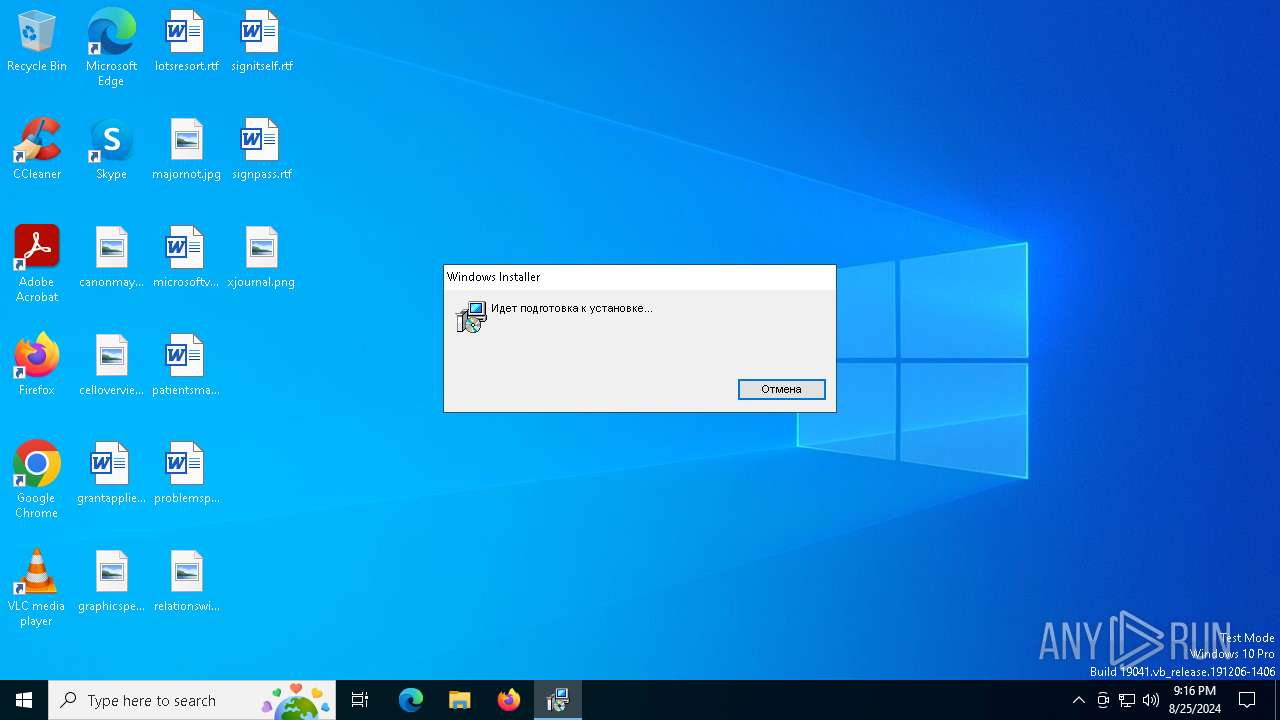
Drops the executable file immediately after the start
- SandeLLoCHECKER_Installer.exe (PID: 6788)
- msiexec.exe (PID: 6904)
Reads security settings of Internet Explorer
- SandeLLoCHECKER_Installer.exe (PID: 6788)
- SandeLLo CHECKER.exe (PID: 6156)
- msiexec.exe (PID: 6664)
Process drops legitimate windows executable
- SandeLLoCHECKER_Installer.exe (PID: 6788)
Executable content was dropped or overwritten
- SandeLLoCHECKER_Installer.exe (PID: 6788)
Reads the Windows owner or organization settings
- SandeLLoCHECKER_Installer.exe (PID: 6788)
- msiexec.exe (PID: 6904)
Checks Windows Trust Settings
- msiexec.exe (PID: 6904)
- SandeLLoCHECKER_Installer.exe (PID: 6788)
Executes as Windows Service
- VSSVC.exe (PID: 6516)
Reads the date of Windows installation
- msiexec.exe (PID: 6664)
INFO
Reads the computer name
- SandeLLoCHECKER_Installer.exe (PID: 6788)
- msiexec.exe (PID: 6904)
- msiexec.exe (PID: 7024)
- msiexec.exe (PID: 6332)
- SandeLLo CHECKER.exe (PID: 6156)
- msiexec.exe (PID: 6664)
Reads the software policy settings
- SandeLLoCHECKER_Installer.exe (PID: 6788)
- msiexec.exe (PID: 7148)
- msiexec.exe (PID: 6904)
- SandeLLo CHECKER.exe (PID: 6156)
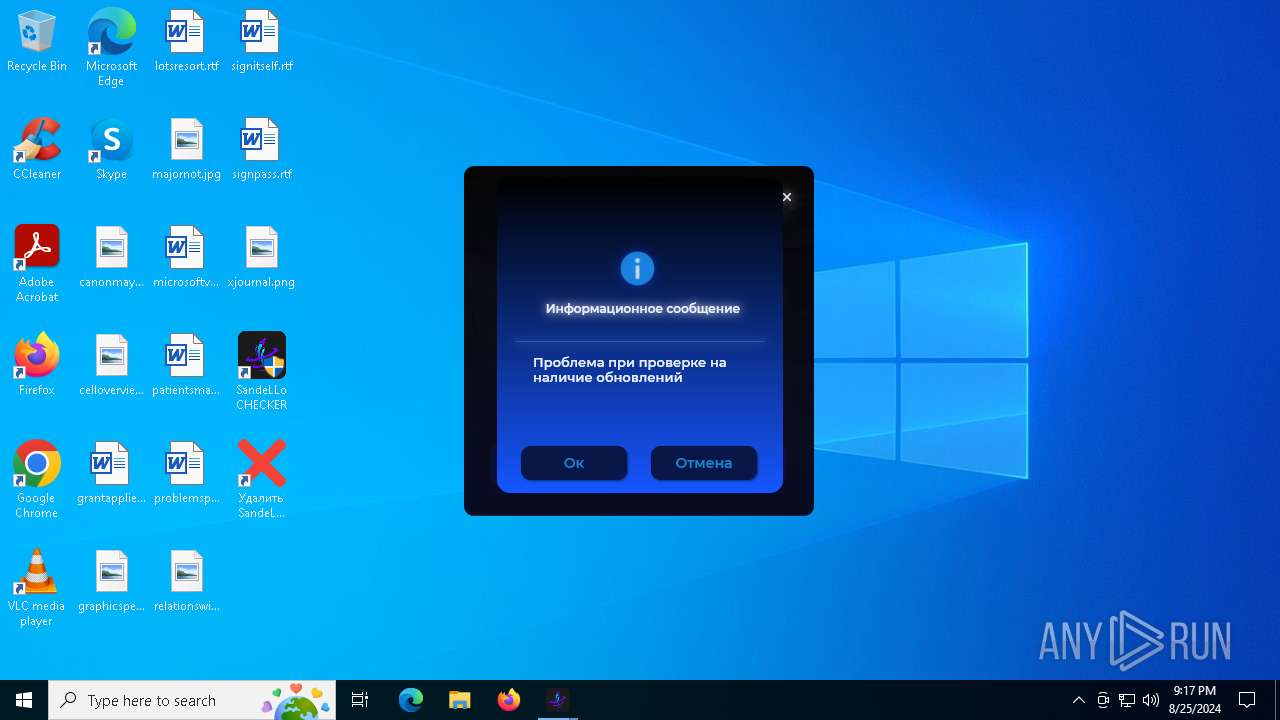
Checks proxy server information
- SandeLLoCHECKER_Installer.exe (PID: 6788)
- SandeLLo CHECKER.exe (PID: 6156)
Reads Environment values
- msiexec.exe (PID: 7024)
- SandeLLoCHECKER_Installer.exe (PID: 6788)
- msiexec.exe (PID: 6664)
- msiexec.exe (PID: 6332)
- SandeLLo CHECKER.exe (PID: 6156)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7148)
Checks supported languages
- msiexec.exe (PID: 6904)
- SandeLLoCHECKER_Installer.exe (PID: 6788)
- msiexec.exe (PID: 7024)
- msiexec.exe (PID: 6664)
- SandeLLo CHECKER.exe (PID: 6156)
- msiexec.exe (PID: 6332)
Create files in a temporary directory
- SandeLLoCHECKER_Installer.exe (PID: 6788)
- msiexec.exe (PID: 6332)
Reads the machine GUID from the registry
- SandeLLoCHECKER_Installer.exe (PID: 6788)
- msiexec.exe (PID: 6904)
- SandeLLo CHECKER.exe (PID: 6156)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7148)
- msiexec.exe (PID: 6904)
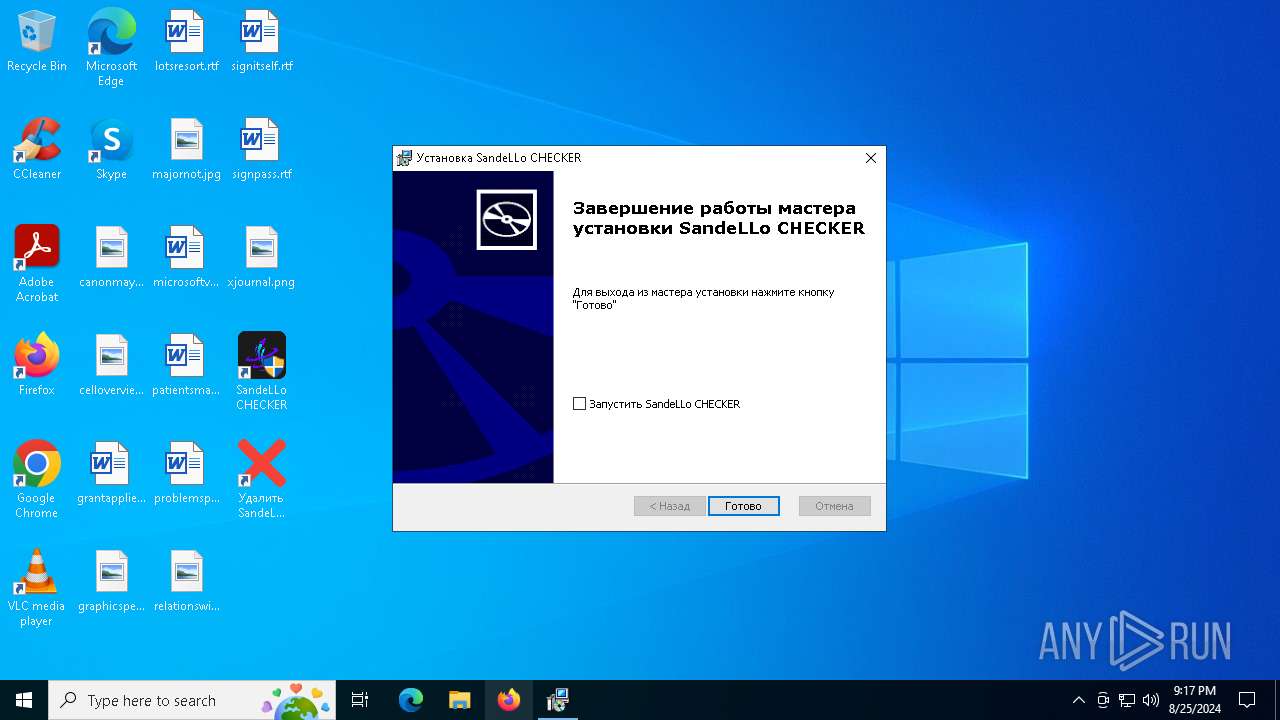
Creates a software uninstall entry
- msiexec.exe (PID: 6904)
Process checks computer location settings
- msiexec.exe (PID: 6664)
Disables trace logs
- SandeLLo CHECKER.exe (PID: 6156)
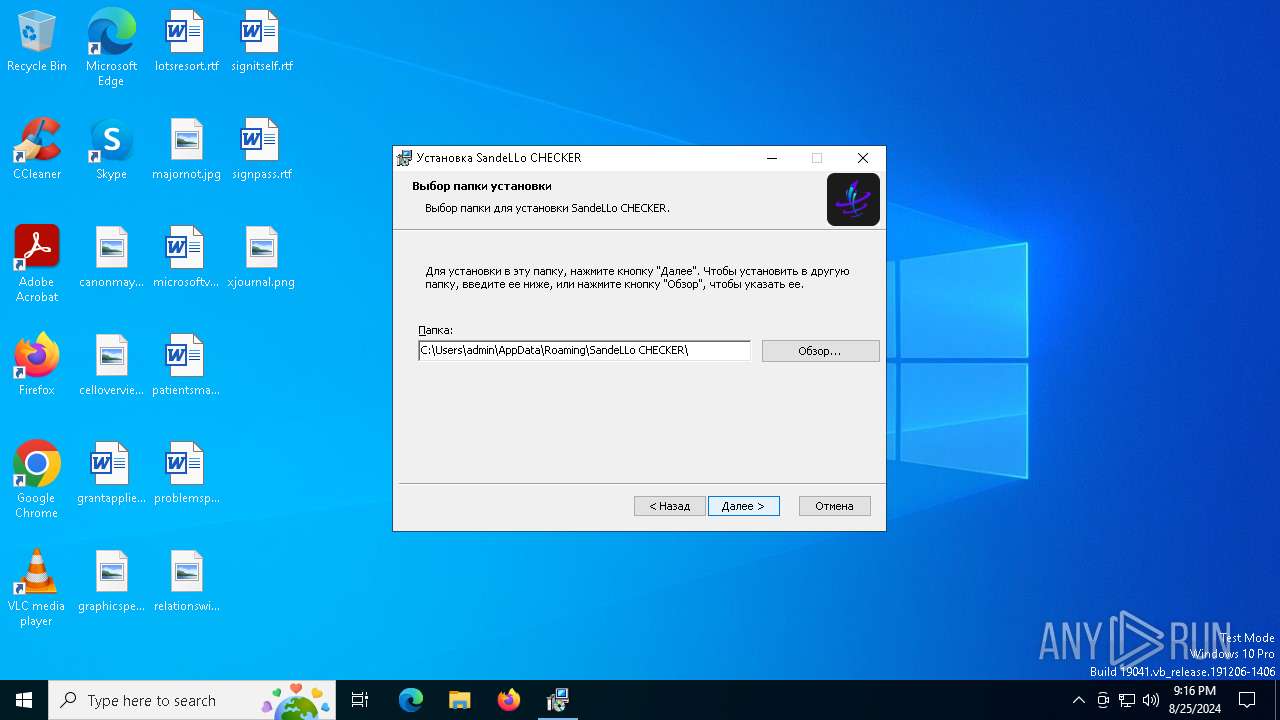
Creates files or folders in the user directory
- msiexec.exe (PID: 6904)
- SandeLLoCHECKER_Installer.exe (PID: 6788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:05:25 08:35:12+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.35 |
| CodeSize: | 2482176 |
| InitializedDataSize: | 956416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d68a4 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.7.2.8 |
| ProductVersionNumber: | 1.7.2.8 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Unicode |
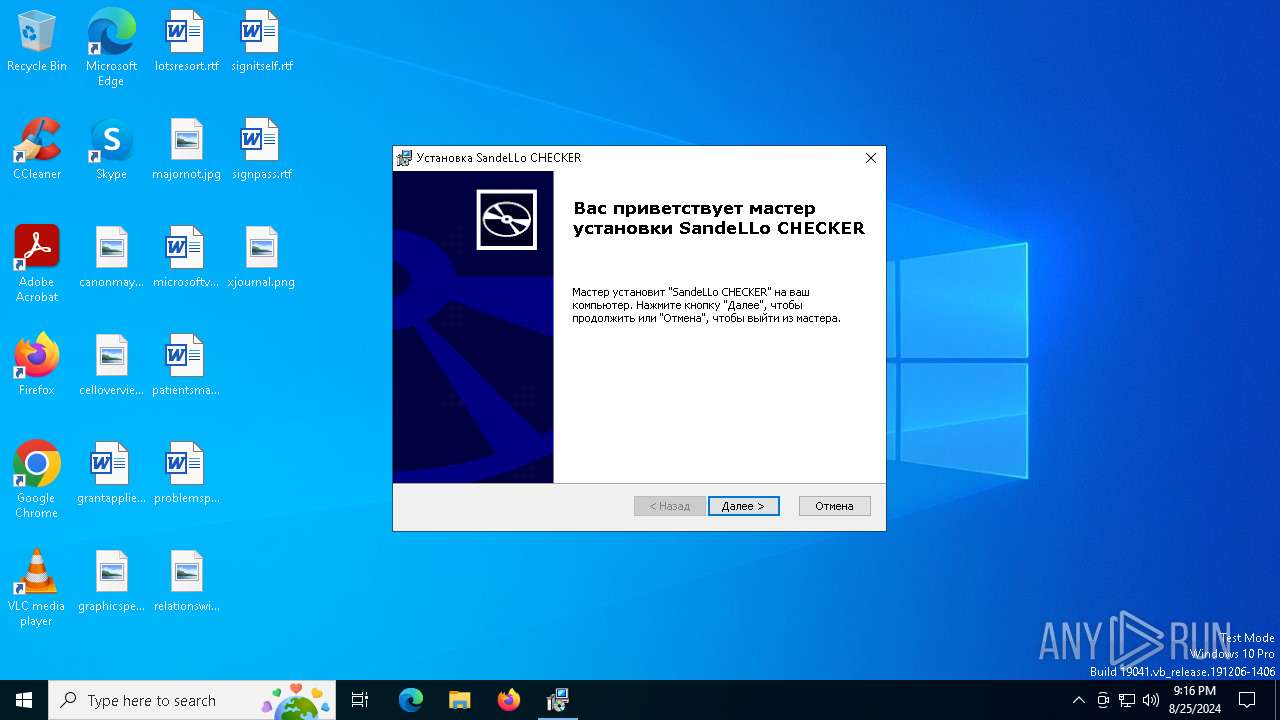
| CompanyName: | LIMITED LIABILITY COMPANY "SANDELLO" |
| FileDescription: | SandeLLo CHECKER Installer |
| FileVersion: | 1.7.2.8 |
| InternalName: | SandeLLoCHECKER_Installer |
| LegalCopyright: | Copyright (C) 2024 LIMITED LIABILITY COMPANY "SANDELLO" |
| OriginalFileName: | SandeLLoCHECKER_Installer.exe |
| ProductName: | SandeLLo CHECKER |
| ProductVersion: | 1.7.2.8 |
Total processes
144
Monitored processes
11
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4008 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4280 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6156 | "C:\Users\admin\AppData\Roaming\SandeLLo CHECKER\SandeLLo CHECKER.exe" | C:\Users\admin\AppData\Roaming\SandeLLo CHECKER\SandeLLo CHECKER.exe | msiexec.exe | ||||||||||||
User: admin Company: SandeLLo Integrity Level: HIGH Description: SandeLLo CHECKER Exit code: 0 Version: 1.7.2.8 Modules
| |||||||||||||||
| 6332 | C:\Windows\syswow64\MsiExec.exe -Embedding 76DCA2C8324123590460E588C7575188 | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6516 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6664 | C:\Windows\syswow64\MsiExec.exe -Embedding 8B4C54836FFE5CABDC325867A36CB897 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6740 | "C:\Users\admin\AppData\Local\Temp\SandeLLoCHECKER_Installer.exe" | C:\Users\admin\AppData\Local\Temp\SandeLLoCHECKER_Installer.exe | — | explorer.exe | |||||||||||
User: admin Company: LIMITED LIABILITY COMPANY "SANDELLO" Integrity Level: MEDIUM Description: SandeLLo CHECKER Installer Exit code: 3221226540 Version: 1.7.2.8 Modules
| |||||||||||||||
| 6788 | "C:\Users\admin\AppData\Local\Temp\SandeLLoCHECKER_Installer.exe" | C:\Users\admin\AppData\Local\Temp\SandeLLoCHECKER_Installer.exe | explorer.exe | ||||||||||||
User: admin Company: LIMITED LIABILITY COMPANY "SANDELLO" Integrity Level: HIGH Description: SandeLLo CHECKER Installer Exit code: 3221225547 Version: 1.7.2.8 Modules
| |||||||||||||||
| 6904 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7024 | C:\Windows\syswow64\MsiExec.exe -Embedding 2DAE3A30D7AD1028923E5B7355942268 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
31 439
Read events
31 092
Write events
325
Delete events
22
Modification events
| (PID) Process: | (6788) SandeLLoCHECKER_Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6788) SandeLLoCHECKER_Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6788) SandeLLoCHECKER_Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6788) SandeLLoCHECKER_Installer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7148) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{618736E0-3C3D-11CF-810C-00AA00389B71}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7148) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{618736E0-3C3D-11CF-810C-00AA00389B71}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7148) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Volatile\00\MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{03022430-ABC4-11D0-BDE2-00AA001A1953}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7148) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Volatile\00\MACHINE\SOFTWARE\Classes\Interface\{03022430-ABC4-11D0-BDE2-00AA001A1953}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (6904) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000E02B861634F7DA01F81A00005C190000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6904) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000767D881634F7DA01F81A00005C190000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
64
Suspicious files
26
Text files
40
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6788 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_6788\checkernewicon.jpg | image | |
MD5:643516C9C88C63A4F6AC51E7E31413CC | SHA256:474629078C3E4C414EFF6FC939F9DEEA9CF7C7BE4C69B3ACC0B3F26BDF4ABA32 | |||
| 6788 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\Local\Temp\{F123046A-2CBF-4743-A59B-E3D2751B5780}\51B5780\SandeLLoCHECKER_Installer.msi | executable | |
MD5:E47C6582751CDC22D8C0EEAC60DE6D0B | SHA256:C645A247C399AE2E8CCF8F826415E7287B52080FCAE3DAC203E7E543FE792CCB | |||
| 6788 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\Local\Temp\MSIF7CC.tmp | executable | |
MD5:9E0AEF52F6C03B2FEA067342D9D4F22F | SHA256:42B8ADAFCB4E8496D9822A0C504F449E56456528A9251C153381D3F63D197E5B | |||
| 6788 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:541DF5734D73882FC00B5690DA317394 | SHA256:0E8967EEF2CF25095A5353FBF780E47626A0D3B9074FE147522E00328753CB78 | |||
| 6788 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\Local\Temp\MSIF710.tmp | executable | |
MD5:9E0AEF52F6C03B2FEA067342D9D4F22F | SHA256:42B8ADAFCB4E8496D9822A0C504F449E56456528A9251C153381D3F63D197E5B | |||
| 6788 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_6788\completi | image | |
MD5:C23AF89757665BC0386FD798A61B2112 | SHA256:031ED0378F819926D7B5B2C6C9367A0FB1CBAE40E1A3959E2652FE30A47D52F2 | |||
| 6788 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_6788\dialog.jpg | image | |
MD5:ABF1076064505DEE794FA7AED67252B8 | SHA256:FB0D133F05DE6AA6A7A3491AE532191A60C438B35D9FF7BFEC9E63131F6F0C73 | |||
| 6788 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_6788\info | image | |
MD5:8595D2A2D58310B448729E28649443D6 | SHA256:27F13C4829994B214BB1A26EEF474DA67C521FD429536CB8421BA2F7C3E02B5F | |||
| 6788 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_6788\New | image | |
MD5:1E80DE80CEFEE55D7CFDA0DF2EDCF3B2 | SHA256:4E64F4E40D8CBFF082B37186C831AF4B49E3131C62C00A0CF53E0A6E7E24AC2B | |||
| 6788 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\Local\Temp\AI_EXTUI_BIN_6788\Up | image | |
MD5:FD64F54DB4CBF736A6FC0D7049F5991E | SHA256:C269353D19D50E2688DB102FEF8226CA492DB17133043D7EB5420EE8542D571C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
34
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6788 | SandeLLoCHECKER_Installer.exe | GET | 200 | 216.58.212.163:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
6700 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6788 | SandeLLoCHECKER_Installer.exe | GET | 200 | 216.58.212.163:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
6700 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4404 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3992 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
208 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6788 | SandeLLoCHECKER_Installer.exe | 172.67.184.109:443 | cdn.semkrill.ru | CLOUDFLARENET | US | unknown |
6788 | SandeLLoCHECKER_Installer.exe | 216.58.212.163:80 | c.pki.goog | GOOGLE | US | whitelisted |
3992 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4404 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
cdn.semkrill.ru |
| unknown |
c.pki.goog |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
Process | Message |
|---|---|
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |