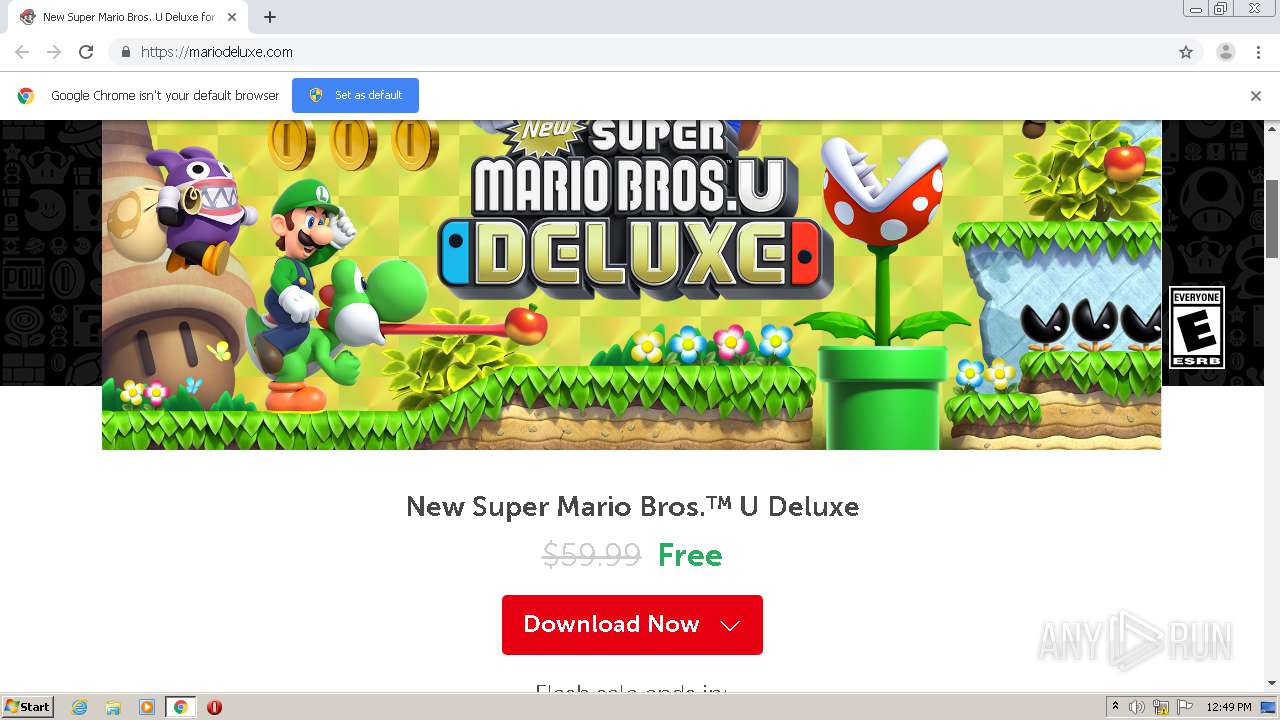
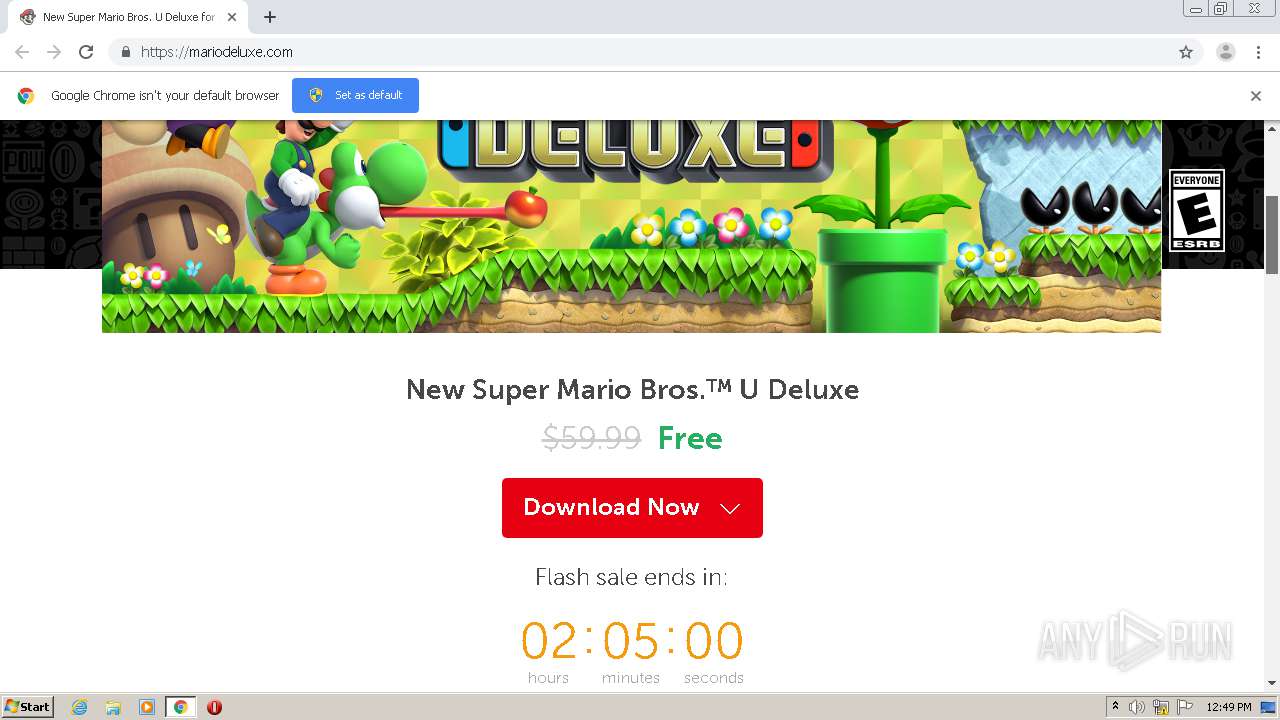
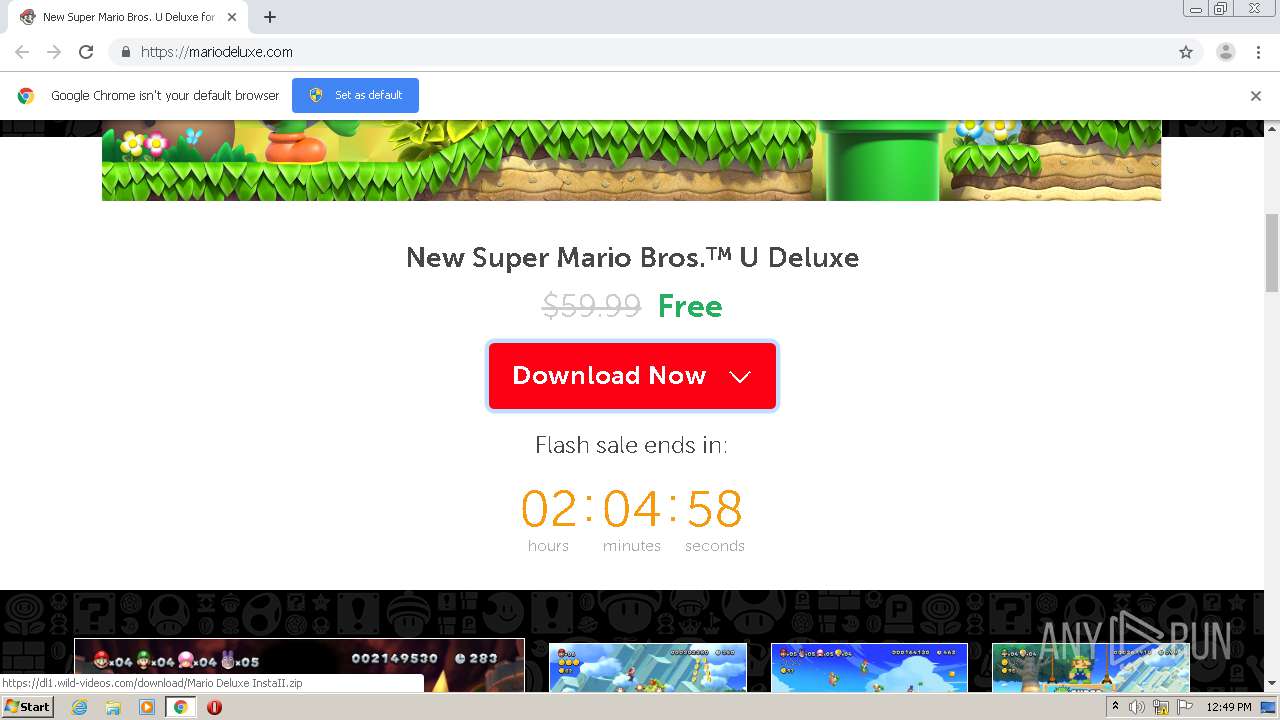
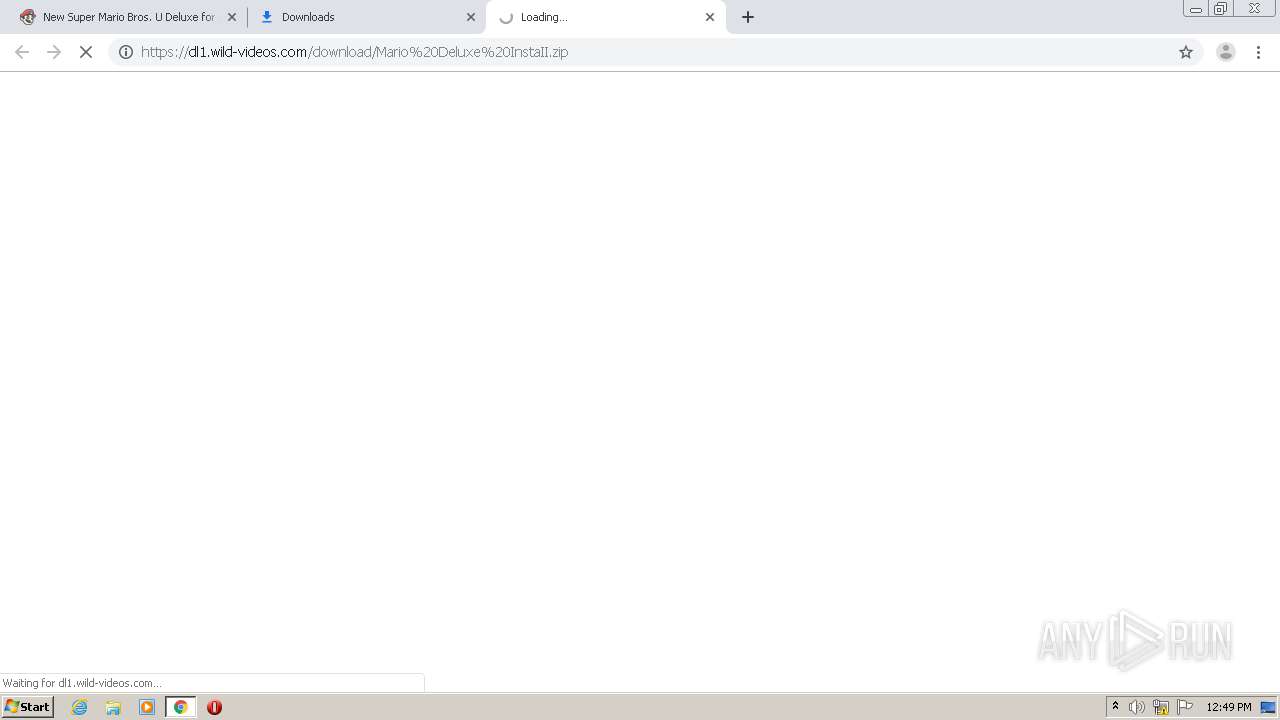
| URL: | https://mariodeluxe.com/ |
| Full analysis: | https://app.any.run/tasks/44a1a869-3c22-4050-9fcd-2413a8657c27 |
| Verdict: | Malicious activity |
| Analysis date: | January 08, 2021, 12:48:21 |
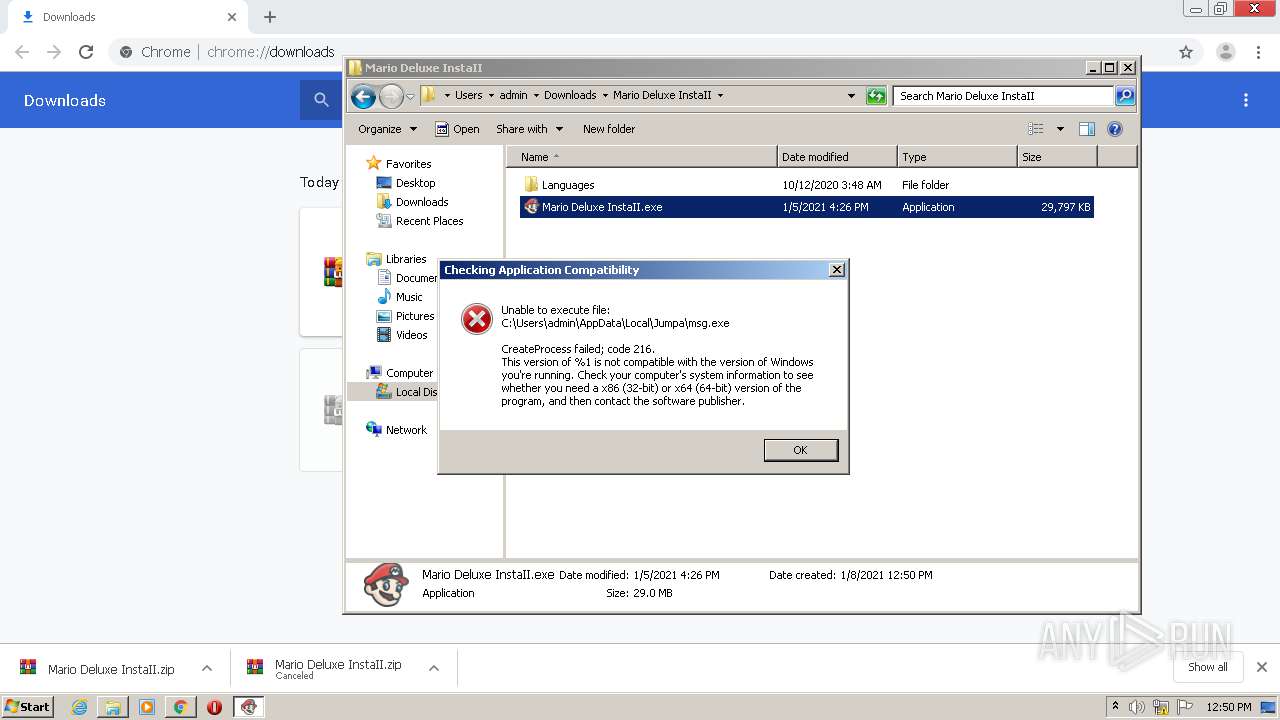
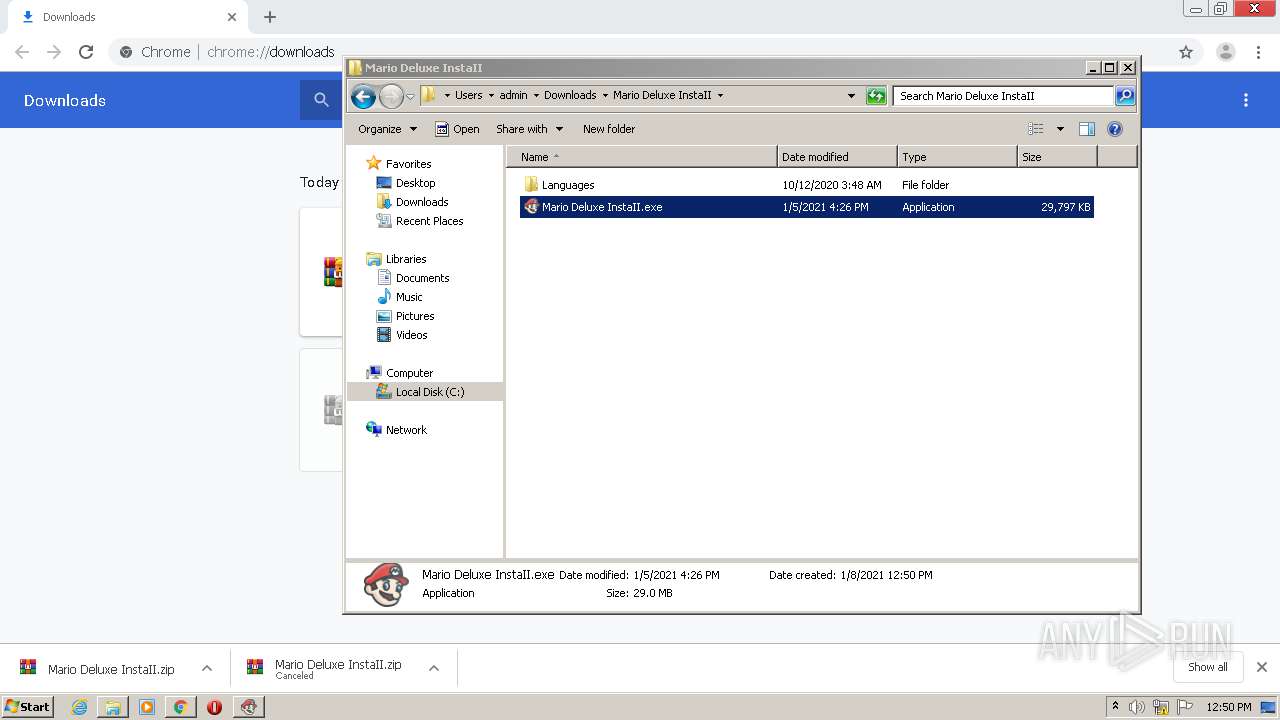
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4A6A0DE9B8B86E8B64A34E6E52948591 |
| SHA1: | 4A6DFFCE78BE0142B44C821CA29D5B3964A8E8D7 |
| SHA256: | 4DF3FA0C5FA95439BF820643997DCCB2A8A60B9A1FE3271F5B73C5046147AF0D |
| SSDEEP: | 3:N8IvyG:2IvyG |
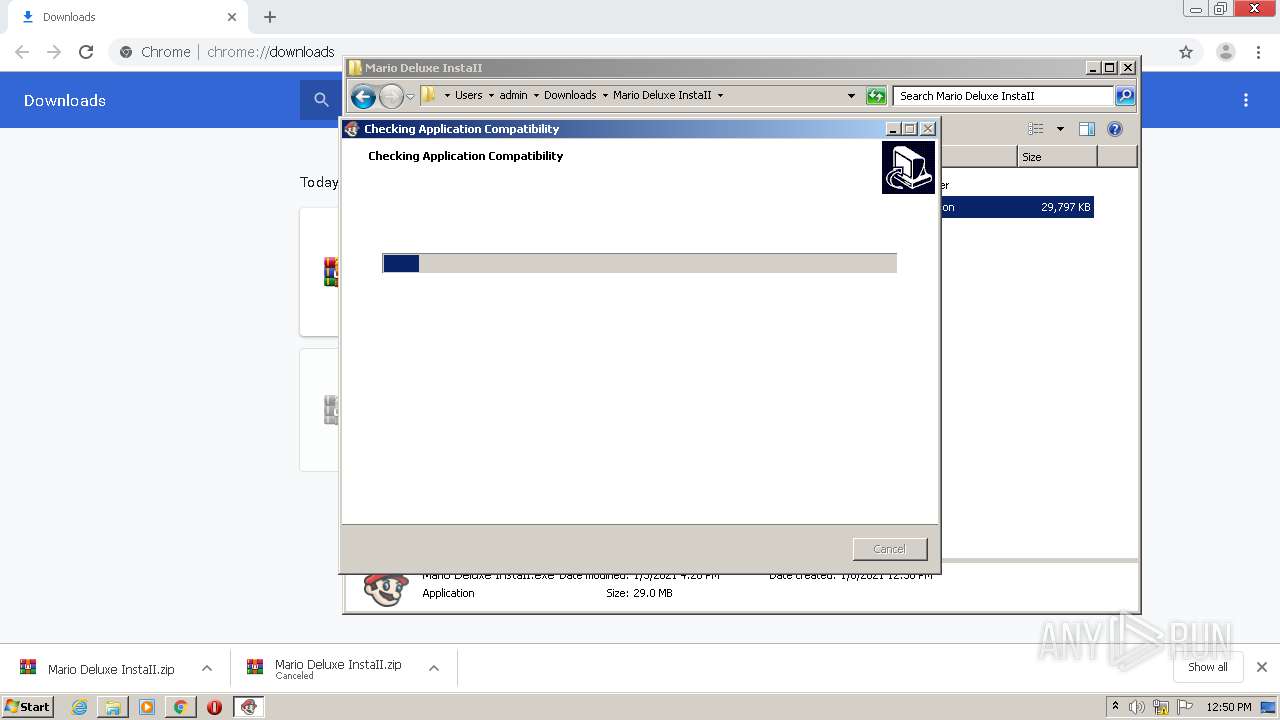
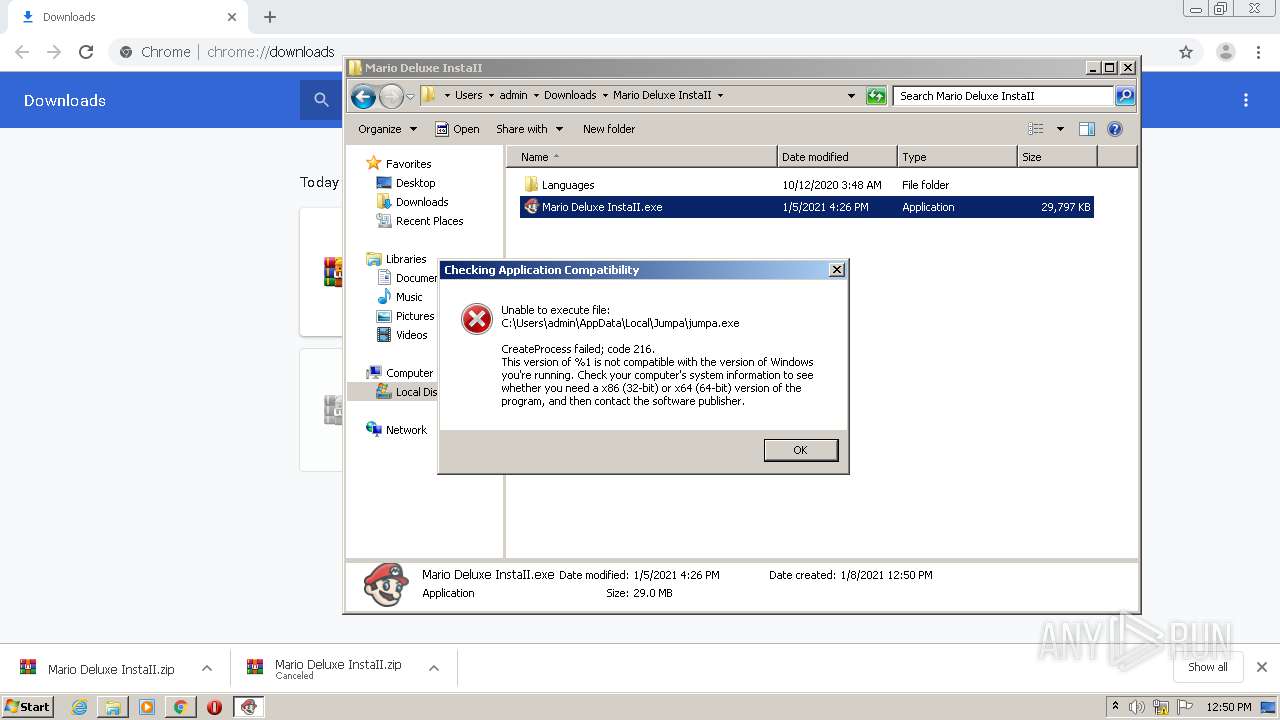
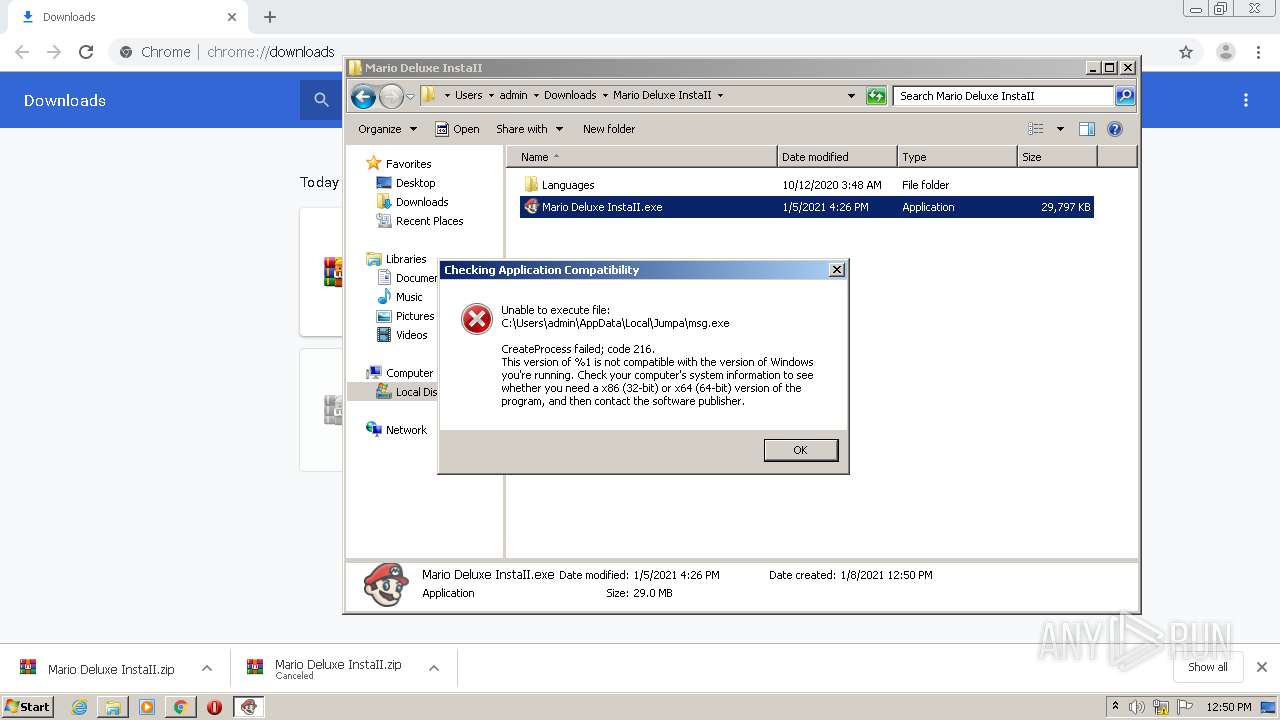
MALICIOUS
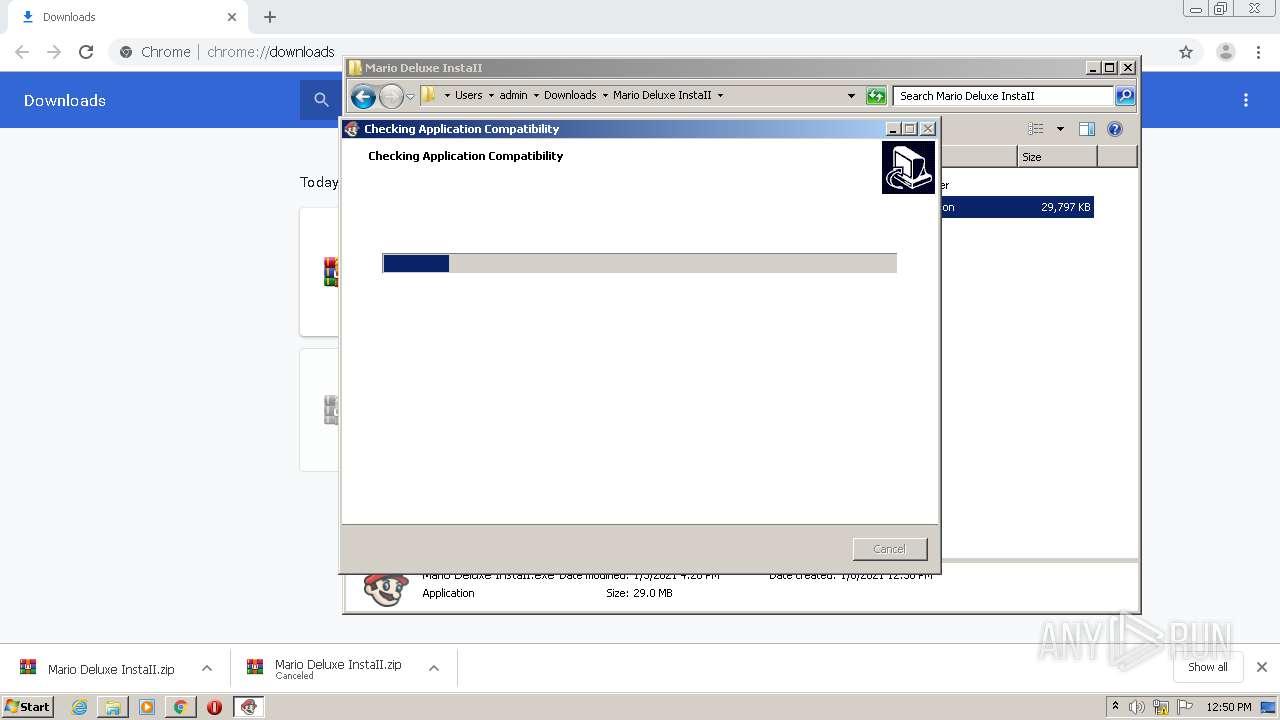
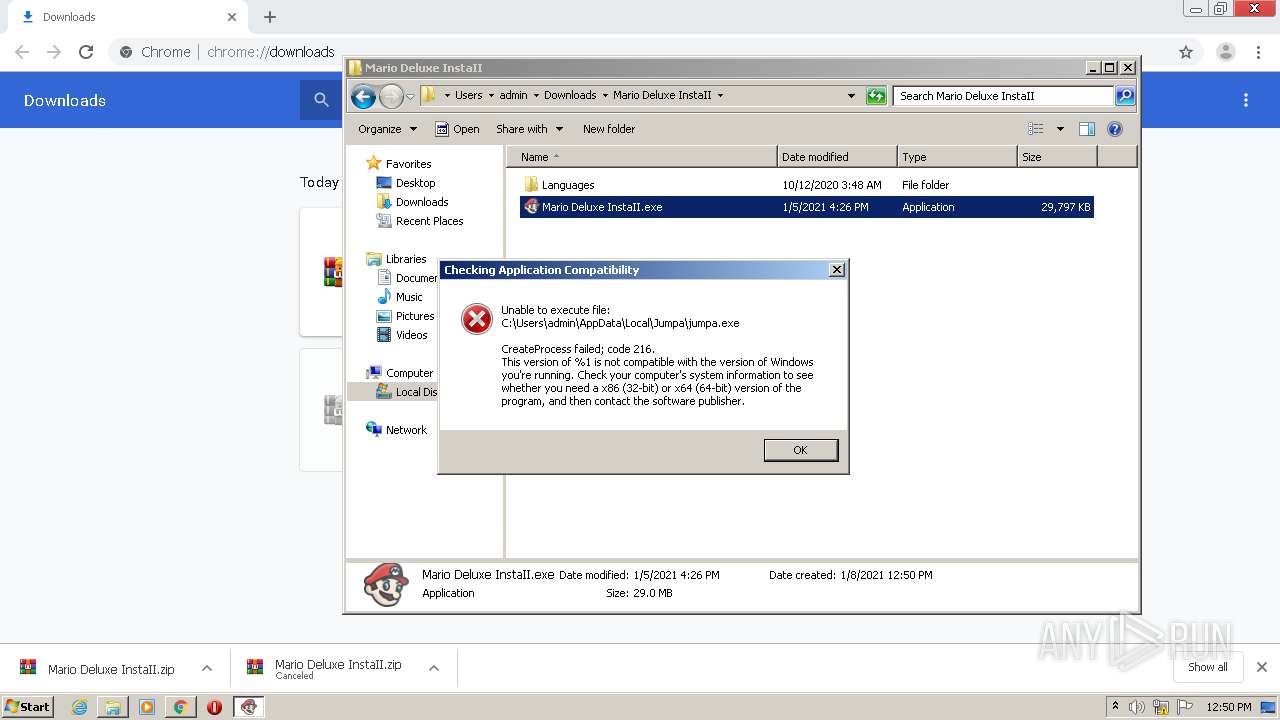
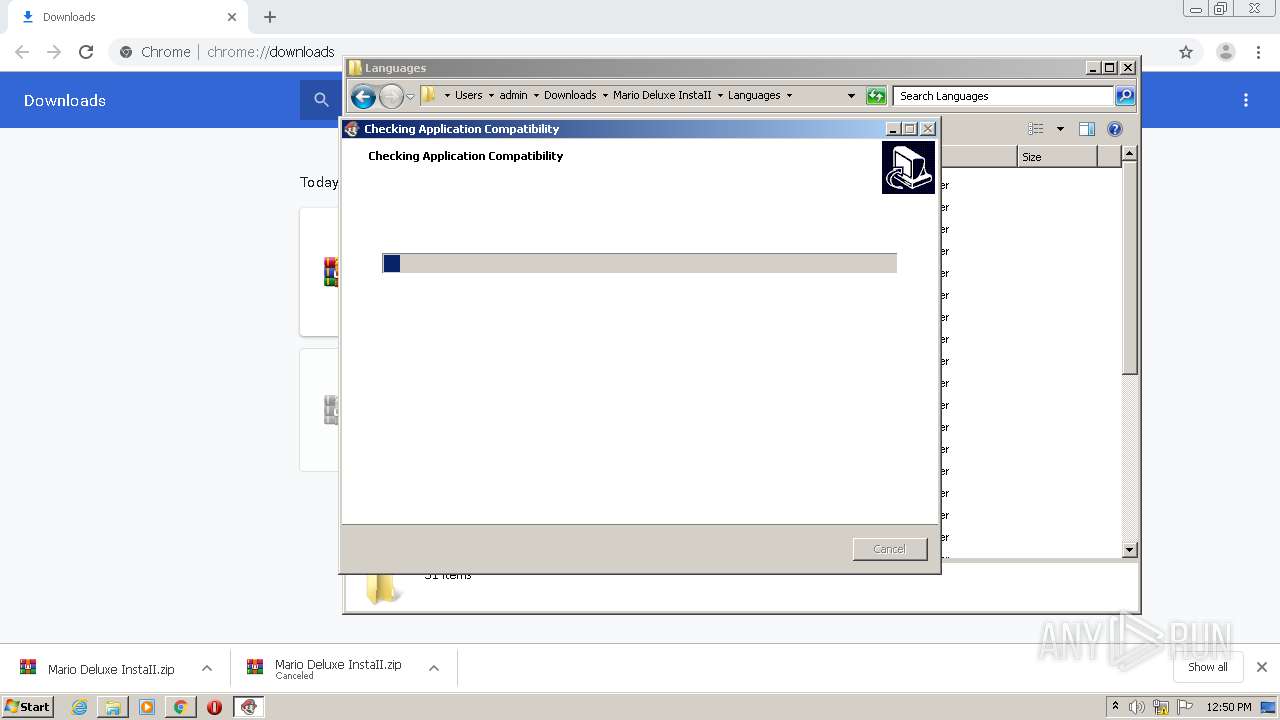
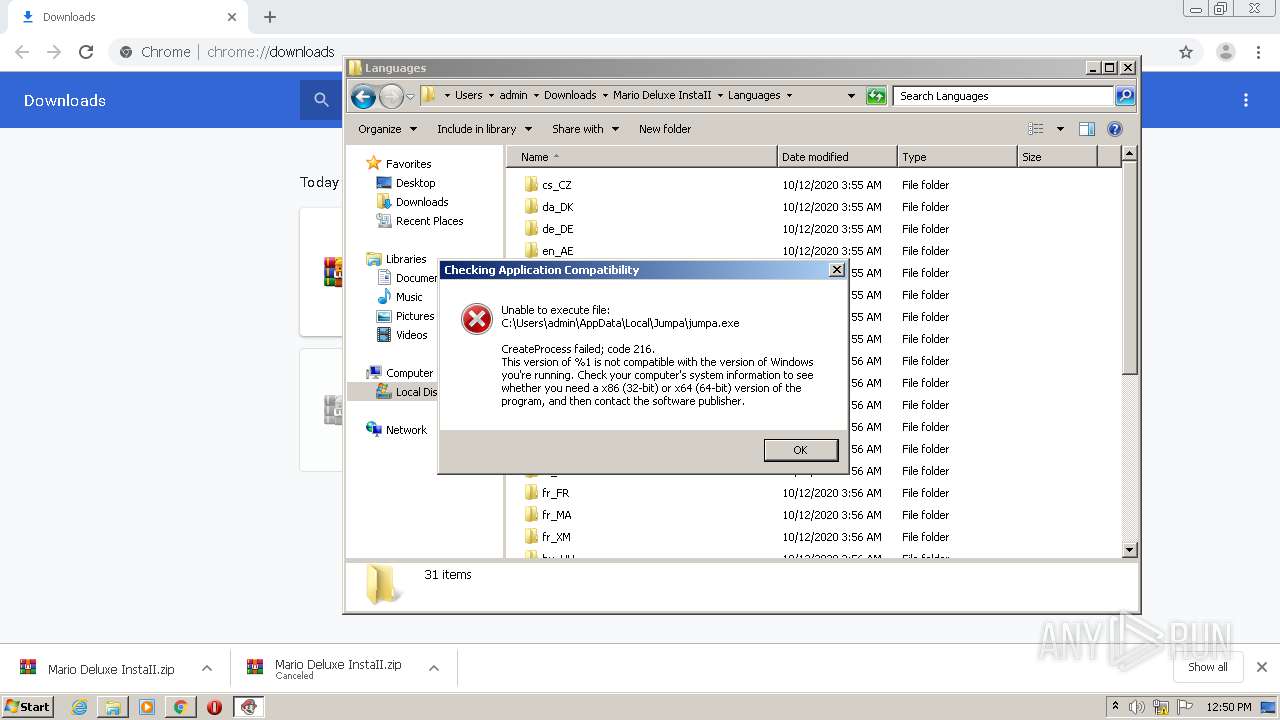
Drops executable file immediately after starts
- Mario Deluxe InstaII.exe (PID: 980)
- Mario Deluxe InstaII.tmp (PID: 3796)
- WinRAR.exe (PID: 3208)
- Mario Deluxe InstaII.exe (PID: 2580)
- Mario Deluxe InstaII.exe (PID: 1900)
- Mario Deluxe InstaII.exe (PID: 3124)
- Mario Deluxe InstaII.tmp (PID: 2328)
- Mario Deluxe InstaII.exe (PID: 3792)
- Mario Deluxe InstaII.exe (PID: 2500)
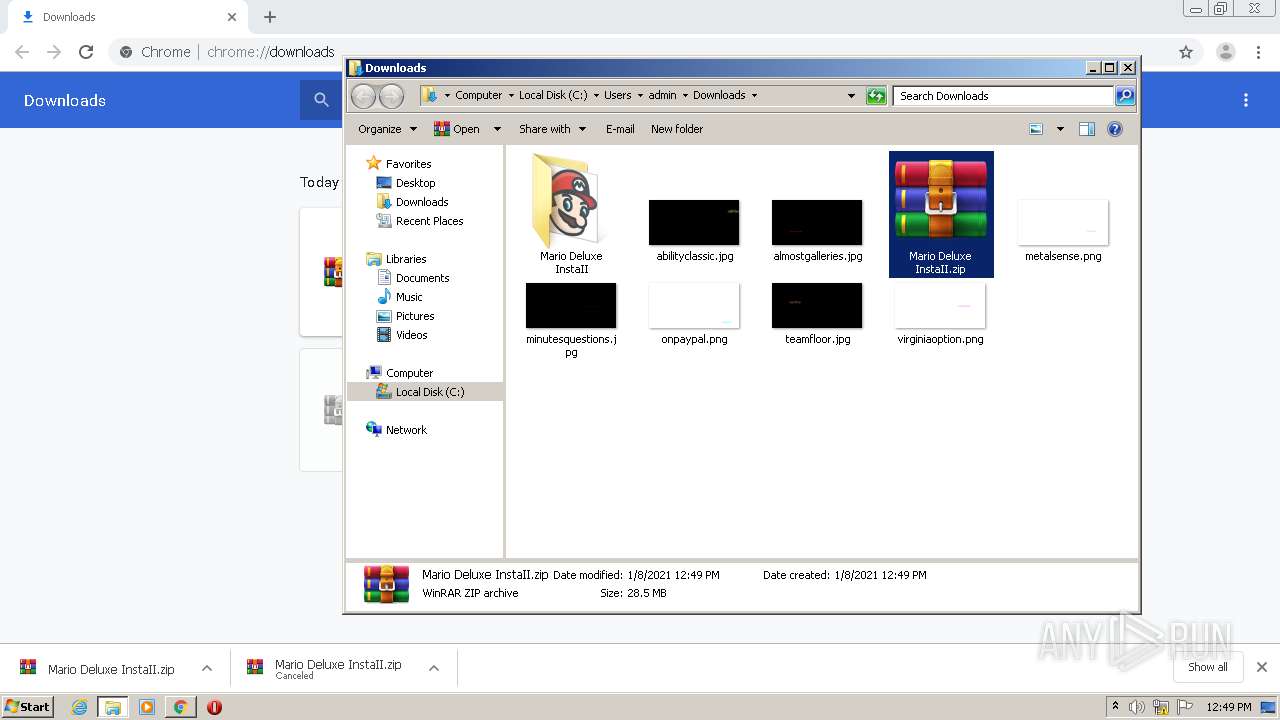
Application was dropped or rewritten from another process
- Mario Deluxe InstaII.exe (PID: 2580)
- Mario Deluxe InstaII.exe (PID: 980)
- Mario Deluxe InstaII.exe (PID: 1900)
- Mario Deluxe InstaII.exe (PID: 3124)
- Mario Deluxe InstaII.exe (PID: 2500)
- Mario Deluxe InstaII.exe (PID: 3792)
SUSPICIOUS
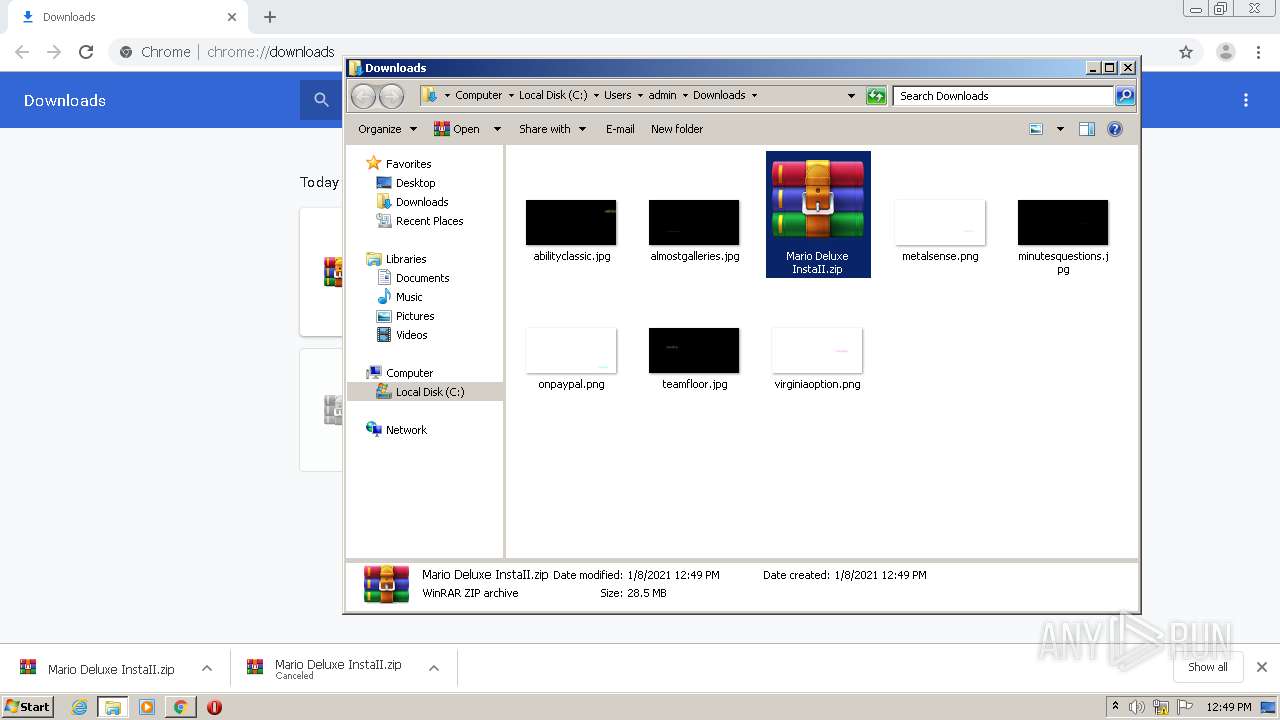
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3208)
- Mario Deluxe InstaII.exe (PID: 980)
- Mario Deluxe InstaII.exe (PID: 2580)
- Mario Deluxe InstaII.exe (PID: 1900)
- Mario Deluxe InstaII.exe (PID: 3124)
- Mario Deluxe InstaII.exe (PID: 3792)
- Mario Deluxe InstaII.exe (PID: 2500)
- Mario Deluxe InstaII.tmp (PID: 3796)
- Mario Deluxe InstaII.tmp (PID: 2588)
- Mario Deluxe InstaII.tmp (PID: 2328)
Reads the Windows organization settings
- Mario Deluxe InstaII.tmp (PID: 3796)
- Mario Deluxe InstaII.tmp (PID: 1680)
- Mario Deluxe InstaII.tmp (PID: 2932)
- Mario Deluxe InstaII.tmp (PID: 2844)
- Mario Deluxe InstaII.tmp (PID: 2328)
- Mario Deluxe InstaII.tmp (PID: 2588)
Reads Windows owner or organization settings
- Mario Deluxe InstaII.tmp (PID: 3796)
- Mario Deluxe InstaII.tmp (PID: 1680)
- Mario Deluxe InstaII.tmp (PID: 2932)
- Mario Deluxe InstaII.tmp (PID: 2328)
- Mario Deluxe InstaII.tmp (PID: 2844)
- Mario Deluxe InstaII.tmp (PID: 2588)
Drops a file that was compiled in debug mode
- Mario Deluxe InstaII.tmp (PID: 3796)
- Mario Deluxe InstaII.tmp (PID: 2328)
- Mario Deluxe InstaII.tmp (PID: 2588)
Drops a file with too old compile date
- Mario Deluxe InstaII.tmp (PID: 3796)
- Mario Deluxe InstaII.tmp (PID: 2588)
- Mario Deluxe InstaII.tmp (PID: 2328)
Drops a file with a compile date too recent
- Mario Deluxe InstaII.tmp (PID: 3796)
- Mario Deluxe InstaII.tmp (PID: 2328)
- Mario Deluxe InstaII.tmp (PID: 2588)
INFO
Reads the hosts file
- chrome.exe (PID: 2464)
- chrome.exe (PID: 2552)
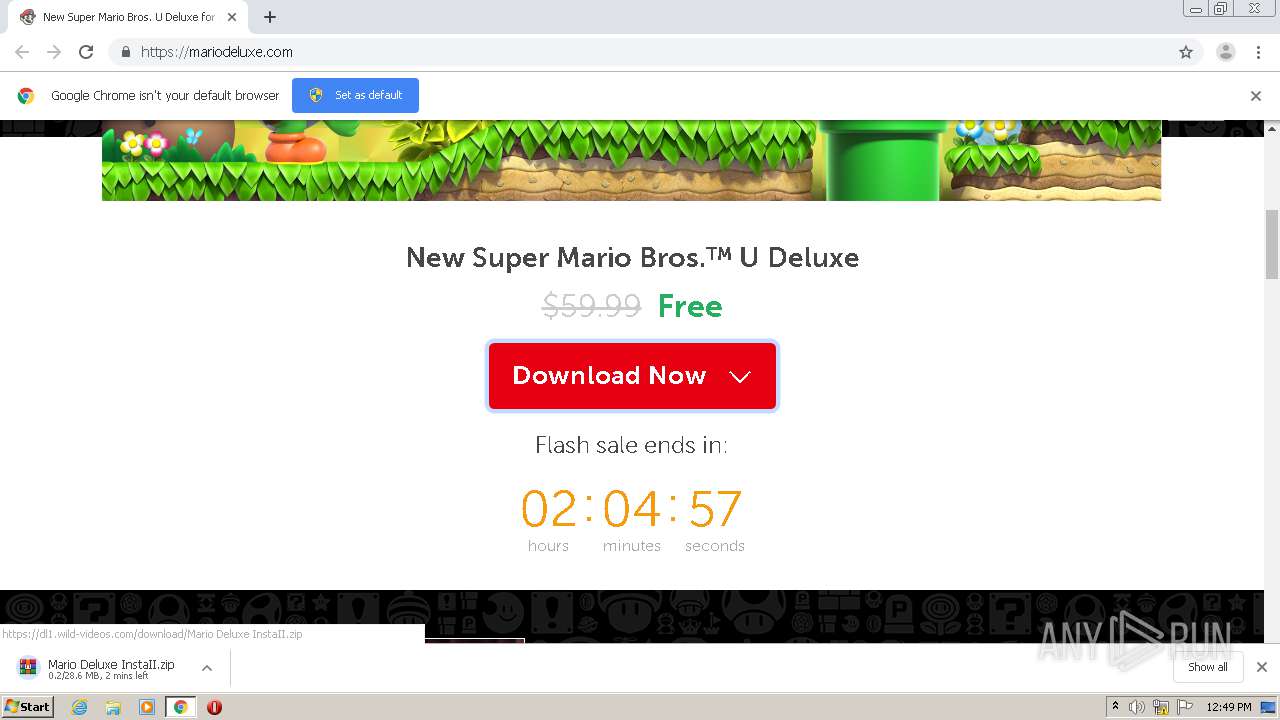
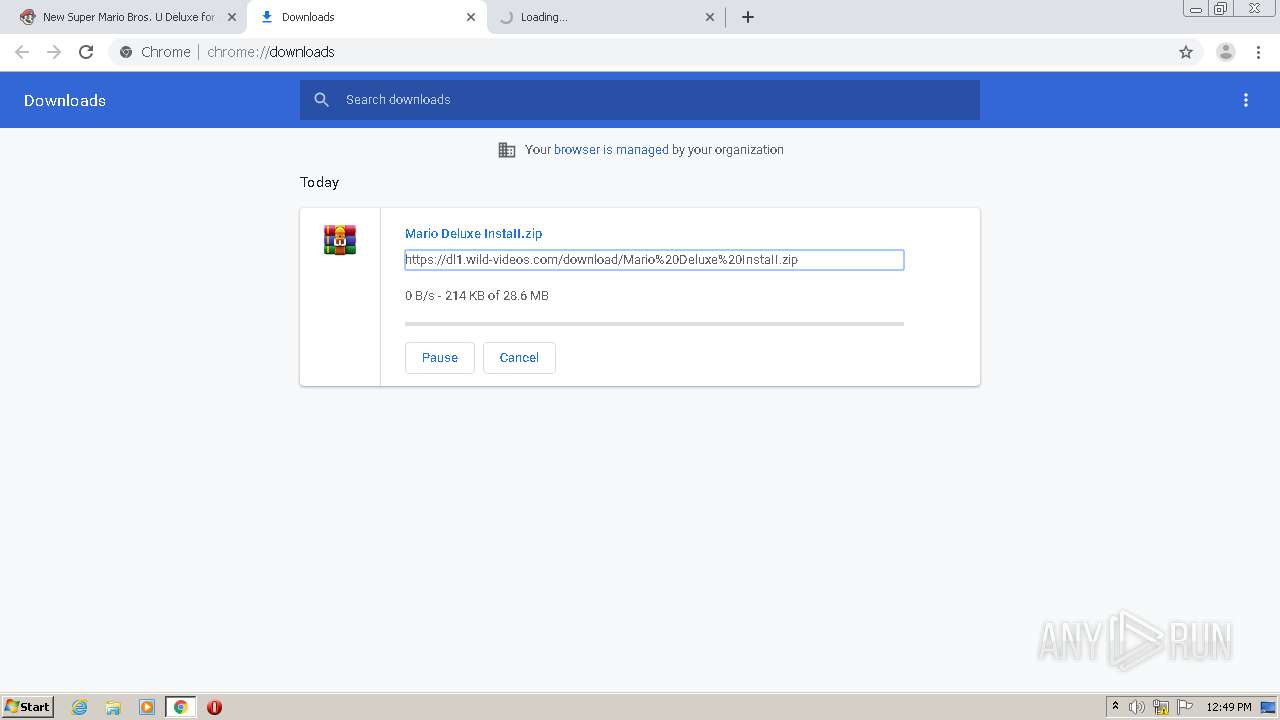
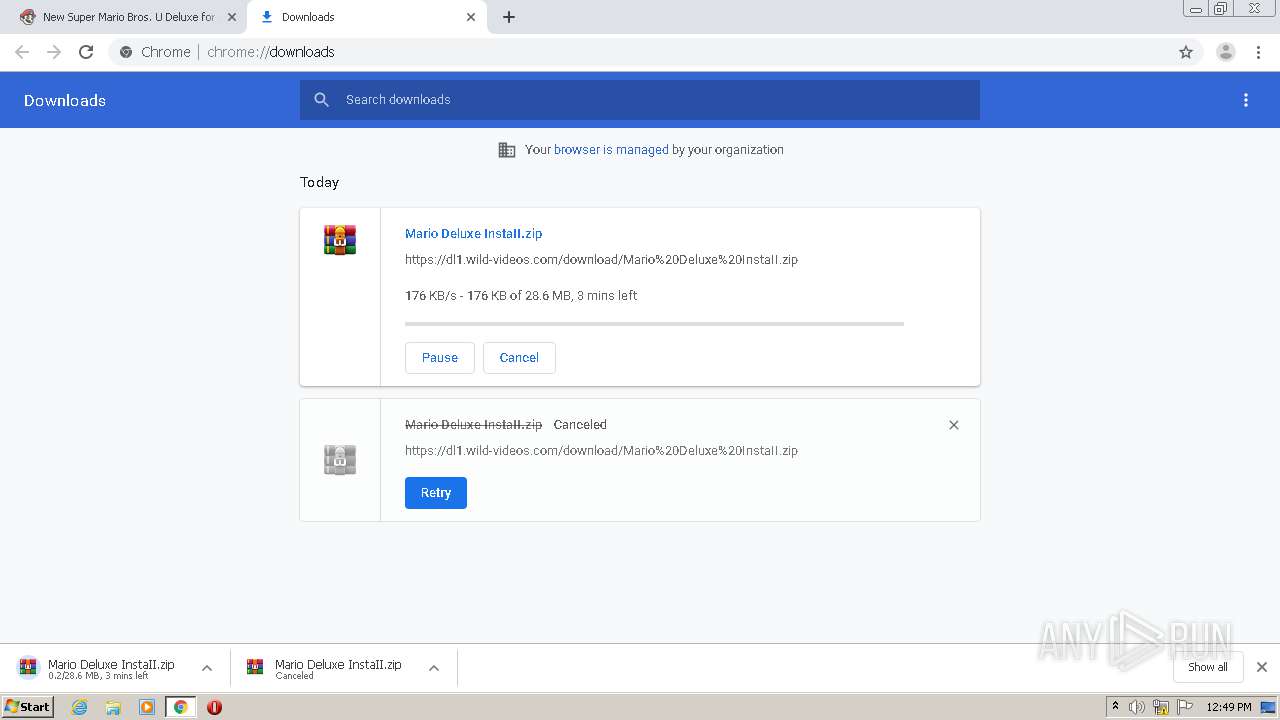
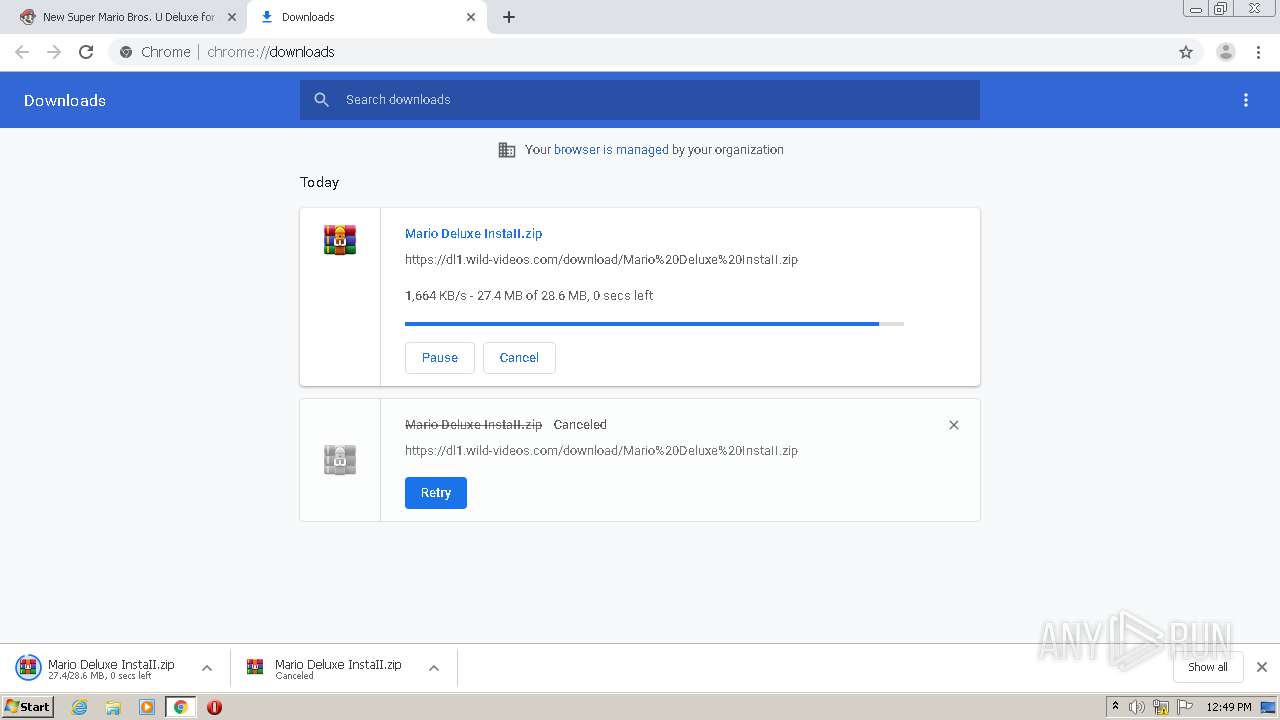
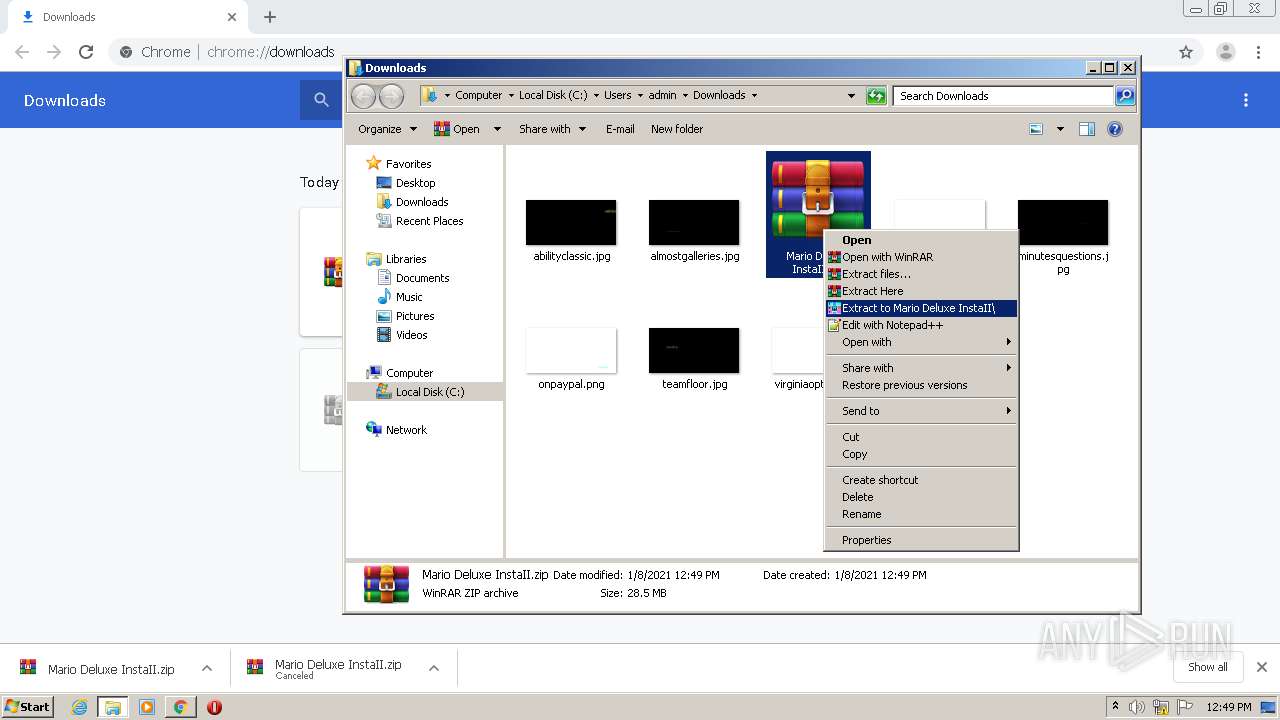
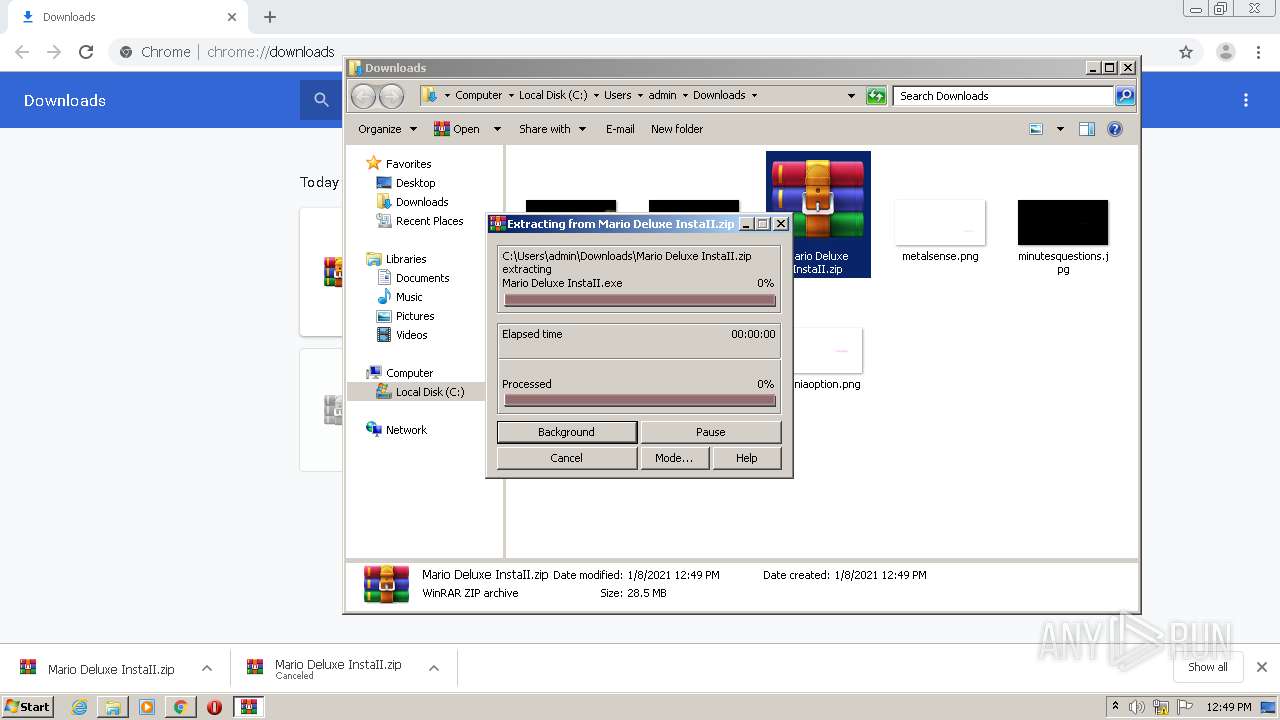
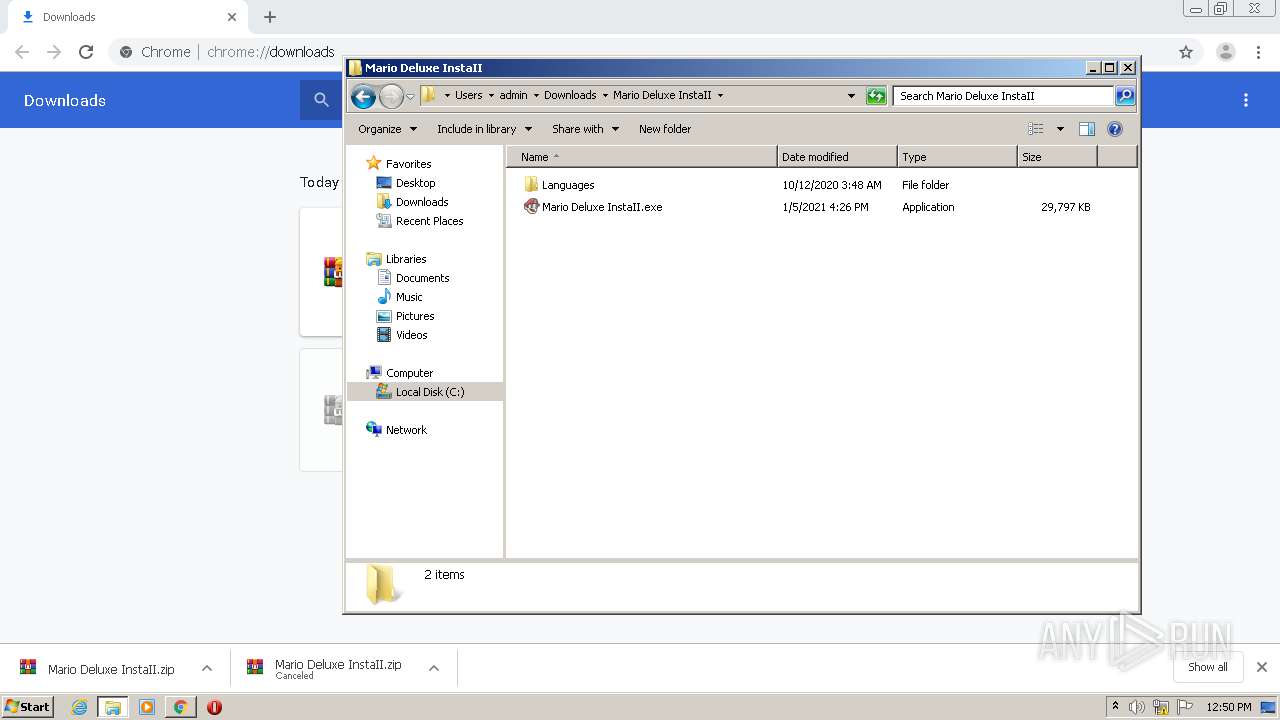
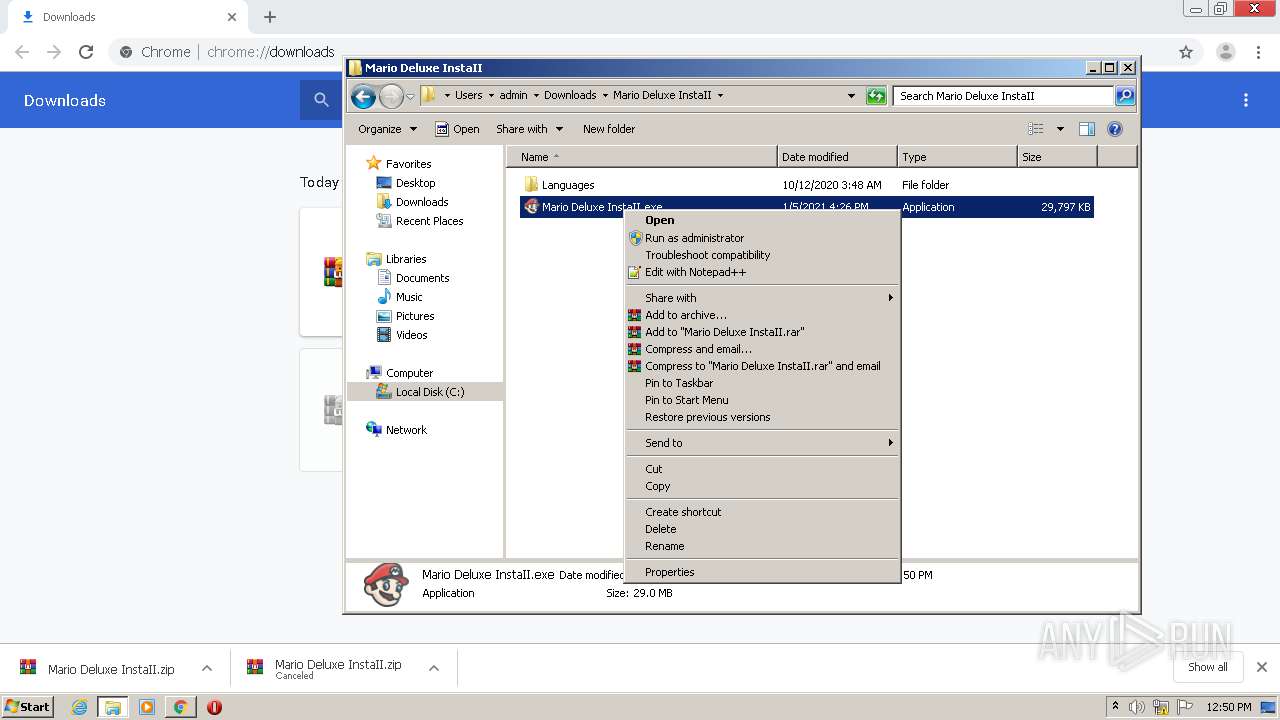
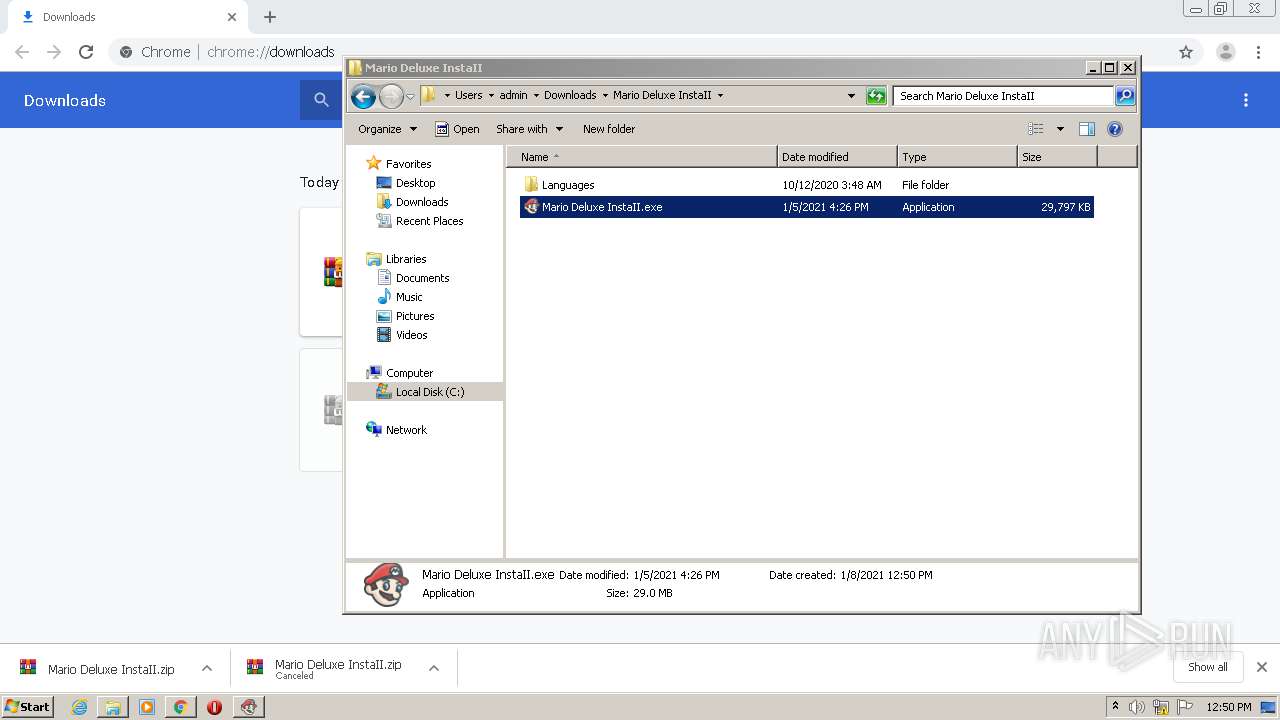
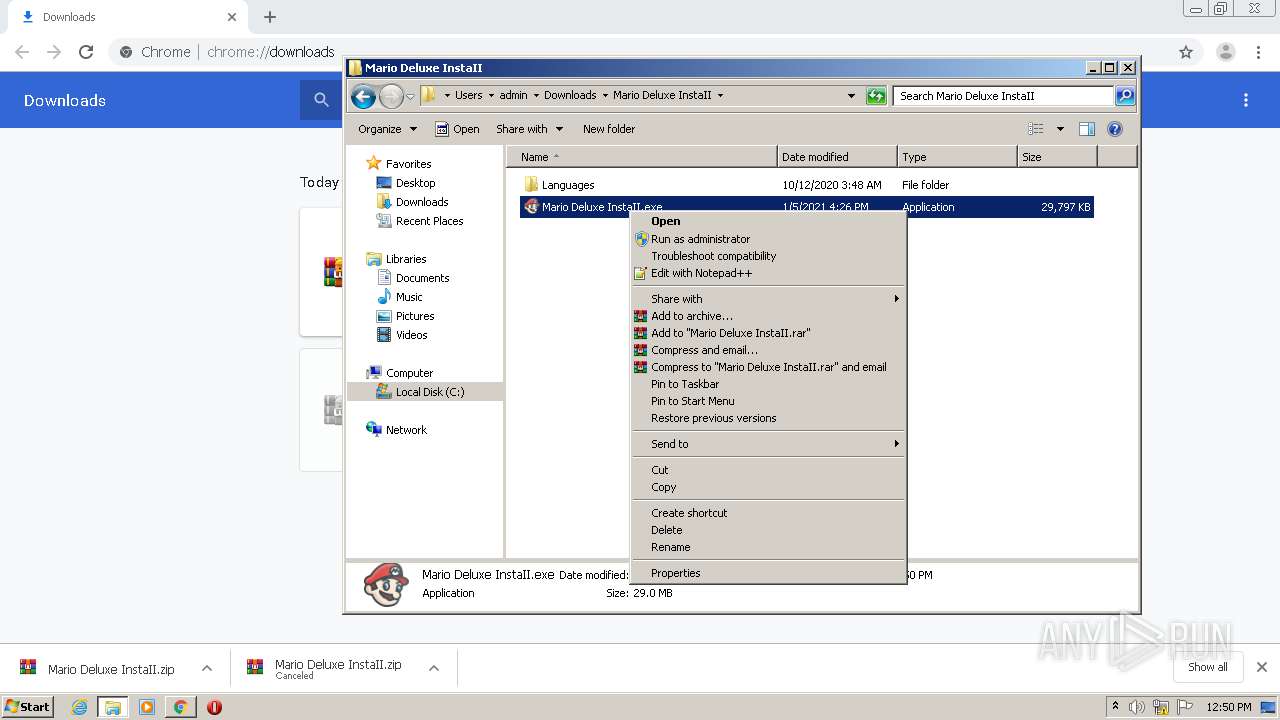
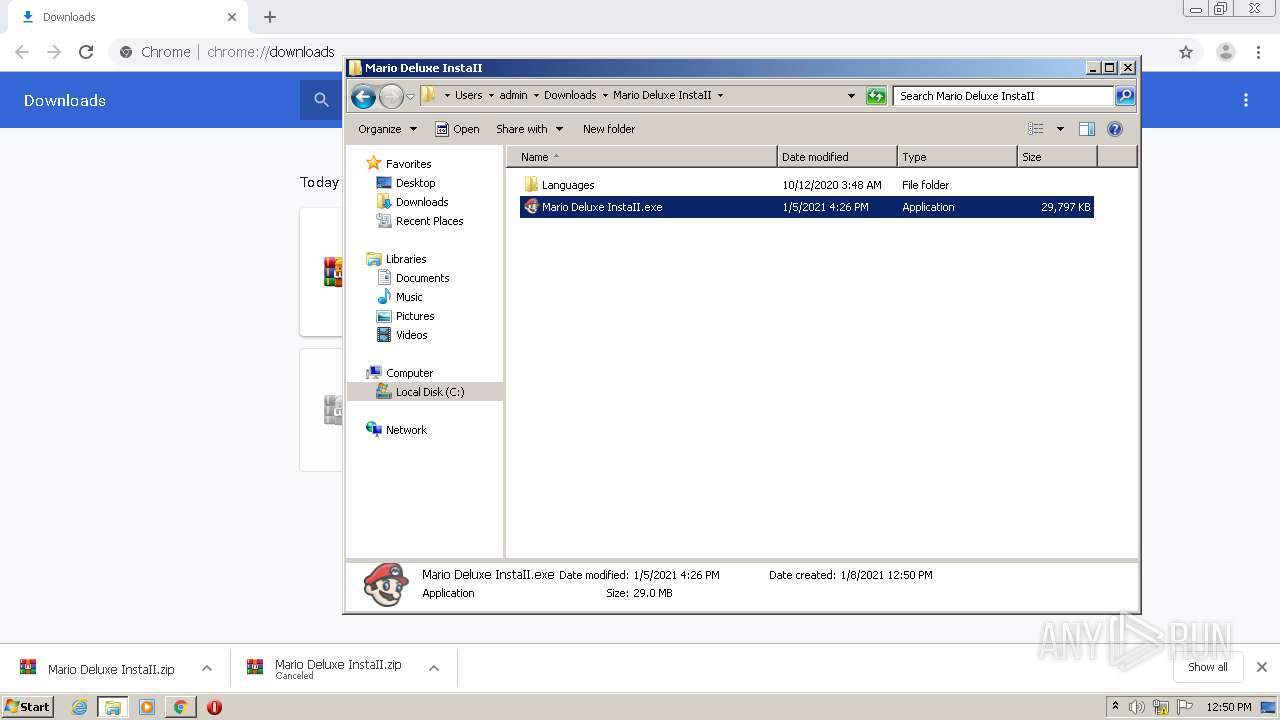
Manual execution by user
- WinRAR.exe (PID: 3208)
- Mario Deluxe InstaII.exe (PID: 980)
- Mario Deluxe InstaII.exe (PID: 1900)
- Mario Deluxe InstaII.exe (PID: 3792)
Application launched itself
- chrome.exe (PID: 2552)
Application was dropped or rewritten from another process
- Mario Deluxe InstaII.tmp (PID: 1680)
- Mario Deluxe InstaII.tmp (PID: 2932)
- Mario Deluxe InstaII.tmp (PID: 2328)
- Mario Deluxe InstaII.tmp (PID: 2844)
- Mario Deluxe InstaII.tmp (PID: 2588)
- Mario Deluxe InstaII.tmp (PID: 3796)
Dropped object may contain Bitcoin addresses
- Mario Deluxe InstaII.tmp (PID: 3796)
- Mario Deluxe InstaII.tmp (PID: 2328)
- Mario Deluxe InstaII.tmp (PID: 2588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
28
Malicious processes
12
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5552748000050799271 --mojo-platform-channel-handle=3132 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
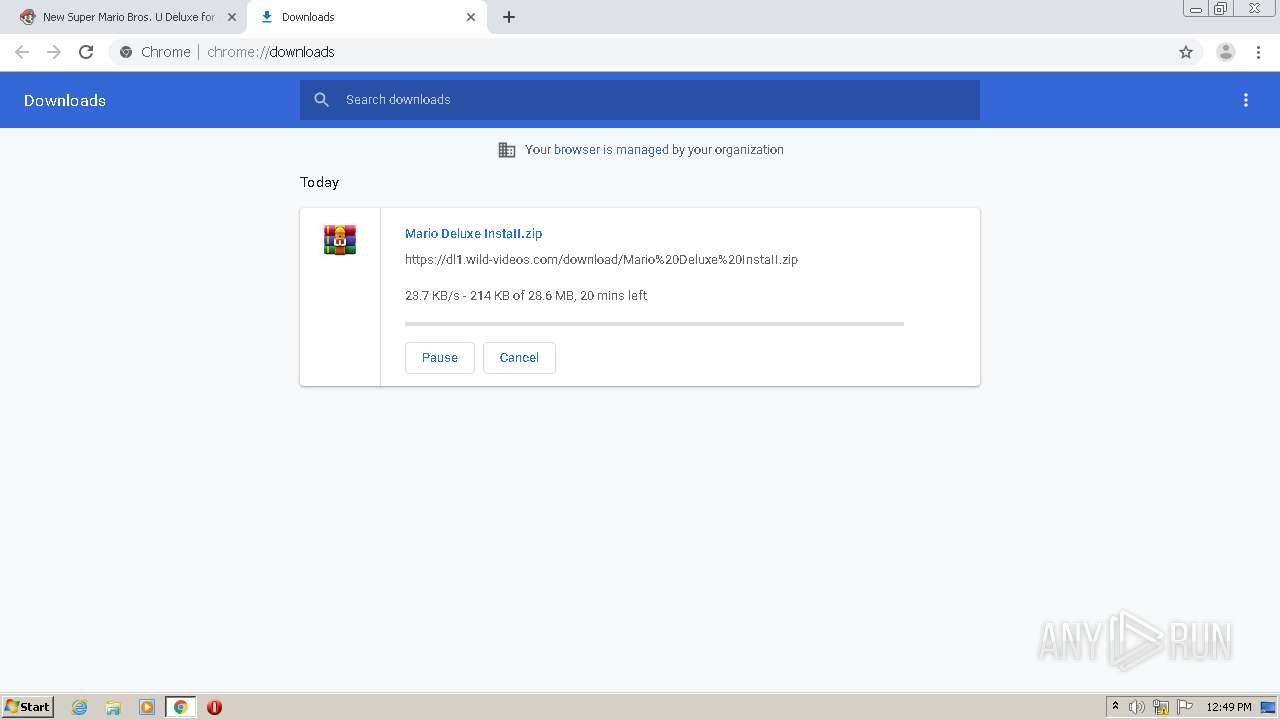
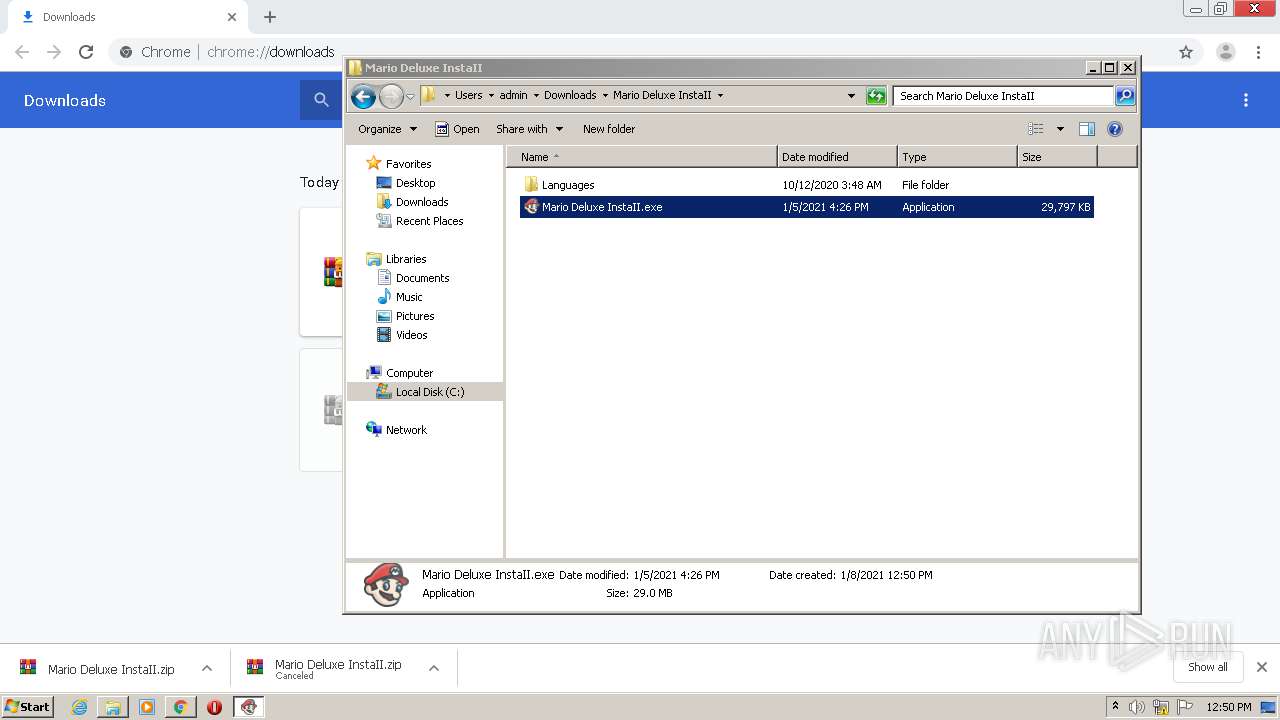
| 980 | "C:\Users\admin\Downloads\Mario Deluxe InstaII\Mario Deluxe InstaII.exe" | C:\Users\admin\Downloads\Mario Deluxe InstaII\Mario Deluxe InstaII.exe | explorer.exe | ||||||||||||
User: admin Company: LGN Software Integrity Level: MEDIUM Description: Jumpa Setup Exit code: 1 Version: Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18336449230662684705 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1680 | "C:\Users\admin\AppData\Local\Temp\is-8TUPD.tmp\Mario Deluxe InstaII.tmp" /SL5="$201DA,29720690,906752,C:\Users\admin\Downloads\Mario Deluxe InstaII\Mario Deluxe InstaII.exe" | C:\Users\admin\AppData\Local\Temp\is-8TUPD.tmp\Mario Deluxe InstaII.tmp | — | Mario Deluxe InstaII.exe | |||||||||||
User: admin Company: LGN Software Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=42078645113662106 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16302337297677506450 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2352 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2940194978191331349 --mojo-platform-channel-handle=3764 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1900 | "C:\Users\admin\Downloads\Mario Deluxe InstaII\Mario Deluxe InstaII.exe" | C:\Users\admin\Downloads\Mario Deluxe InstaII\Mario Deluxe InstaII.exe | explorer.exe | ||||||||||||
User: admin Company: LGN Software Integrity Level: HIGH Description: Jumpa Setup Exit code: 1 Version: Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,16210819403292476892,7277912509099608071,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7039653111581829984 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2740 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2328 | "C:\Users\admin\AppData\Local\Temp\is-V9CV0.tmp\Mario Deluxe InstaII.tmp" /SL5="$70196,29720690,906752,C:\Users\admin\Downloads\Mario Deluxe InstaII\Mario Deluxe InstaII.exe" /SILENT | C:\Users\admin\AppData\Local\Temp\is-V9CV0.tmp\Mario Deluxe InstaII.tmp | Mario Deluxe InstaII.exe | ||||||||||||
User: admin Company: LGN Software Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
2 175
Read events
2 044
Write events
104
Delete events
27
Modification events
| (PID) Process: | (2544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2552-13254583717523000 |
Value: 259 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
384
Suspicious files
19
Text files
2 851
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FF854A6-9F8.pma | — | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c742b92c-b22c-44ee-9e85-8cdbb436b719.tmp | — | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF154436.TMP | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF154436.TMP | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15464a.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
36
DNS requests
16
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2464 | chrome.exe | 104.28.18.76:443 | mariodeluxe.com | Cloudflare Inc | US | shared |
2464 | chrome.exe | 2.16.186.49:443 | use.typekit.net | Akamai International B.V. | — | whitelisted |
2464 | chrome.exe | 104.111.251.202:443 | www.nintendo.com | Akamai International B.V. | NL | unknown |
2464 | chrome.exe | 151.101.2.109:443 | cdn.jsdelivr.net | Fastly | US | suspicious |
2464 | chrome.exe | 104.28.19.76:443 | mariodeluxe.com | Cloudflare Inc | US | shared |
2464 | chrome.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
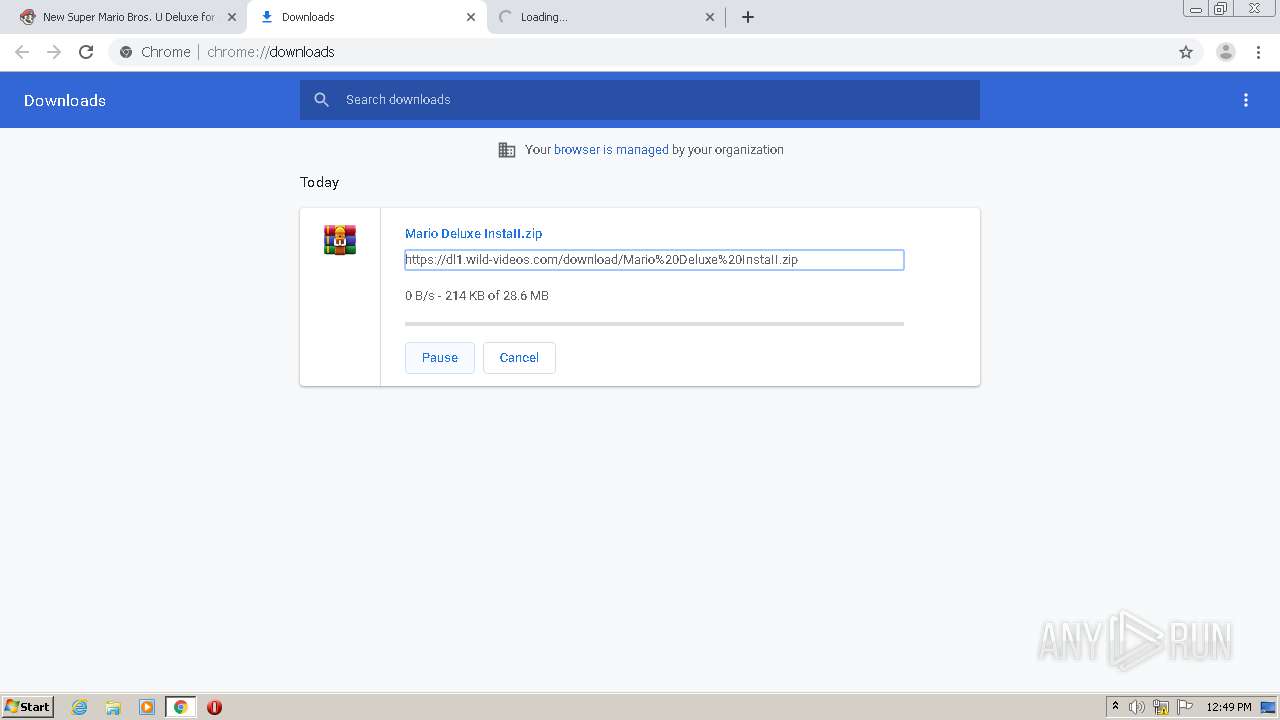
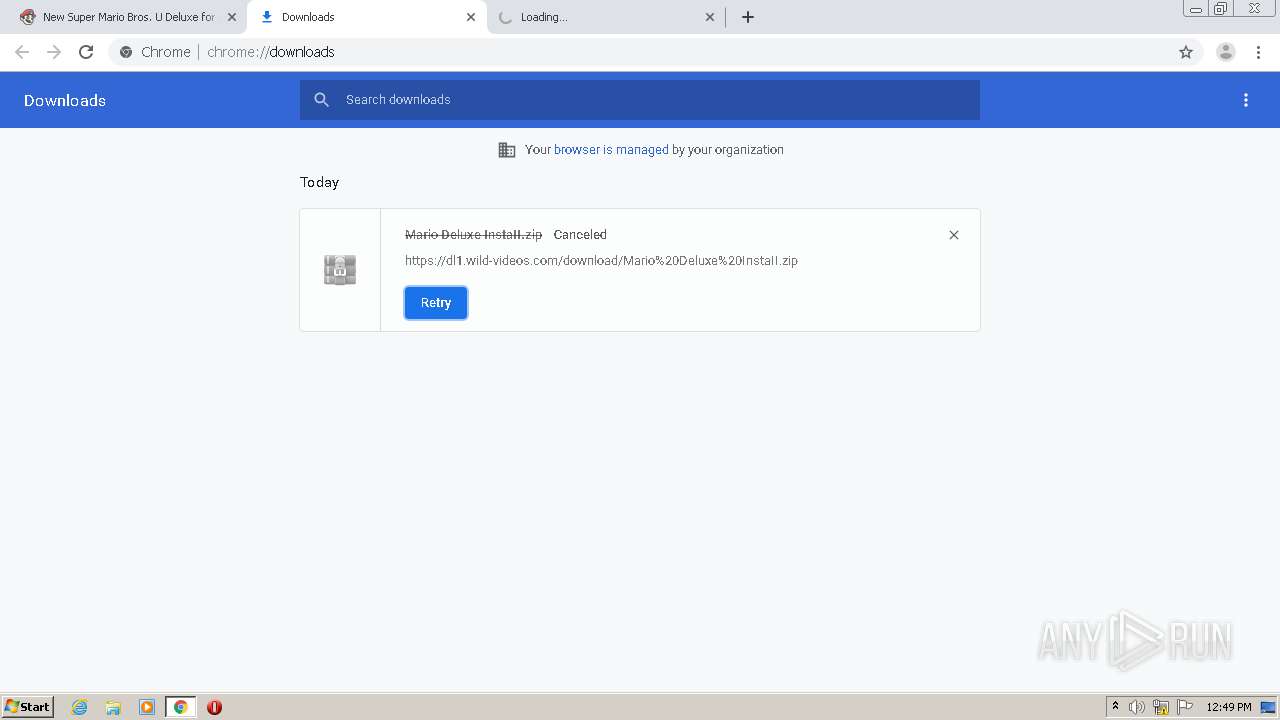
2464 | chrome.exe | 104.24.100.220:443 | dl1.wild-videos.com | Cloudflare Inc | US | shared |
2464 | chrome.exe | 172.217.18.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2464 | chrome.exe | 142.250.74.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2464 | chrome.exe | 142.250.74.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mariodeluxe.com |
| suspicious |
accounts.google.com |
| shared |
use.typekit.net |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.nintendo.com |
| malicious |
vjs.zencdn.net |
| whitelisted |
p.typekit.net |
| shared |
assets.nintendo.com |
| unknown |