| File name: | pbsvc.exe |
| Full analysis: | https://app.any.run/tasks/52d3b63e-a66c-4890-885d-db68835cc119 |
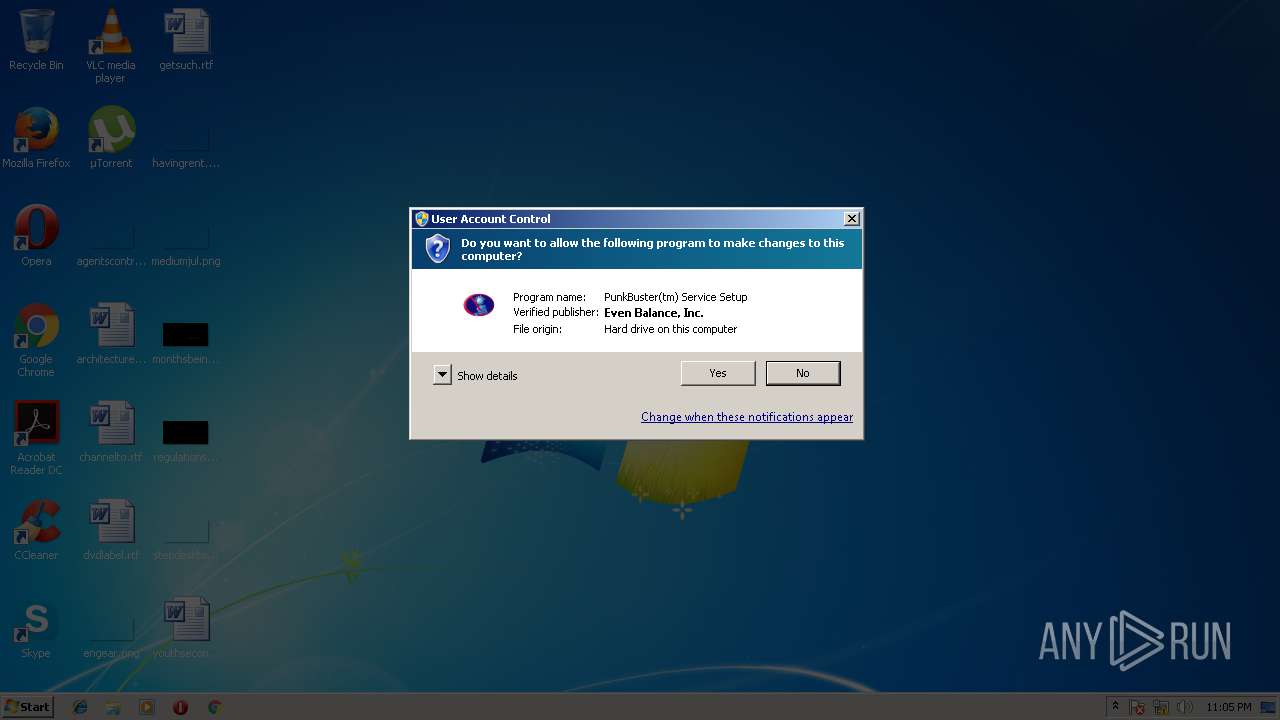
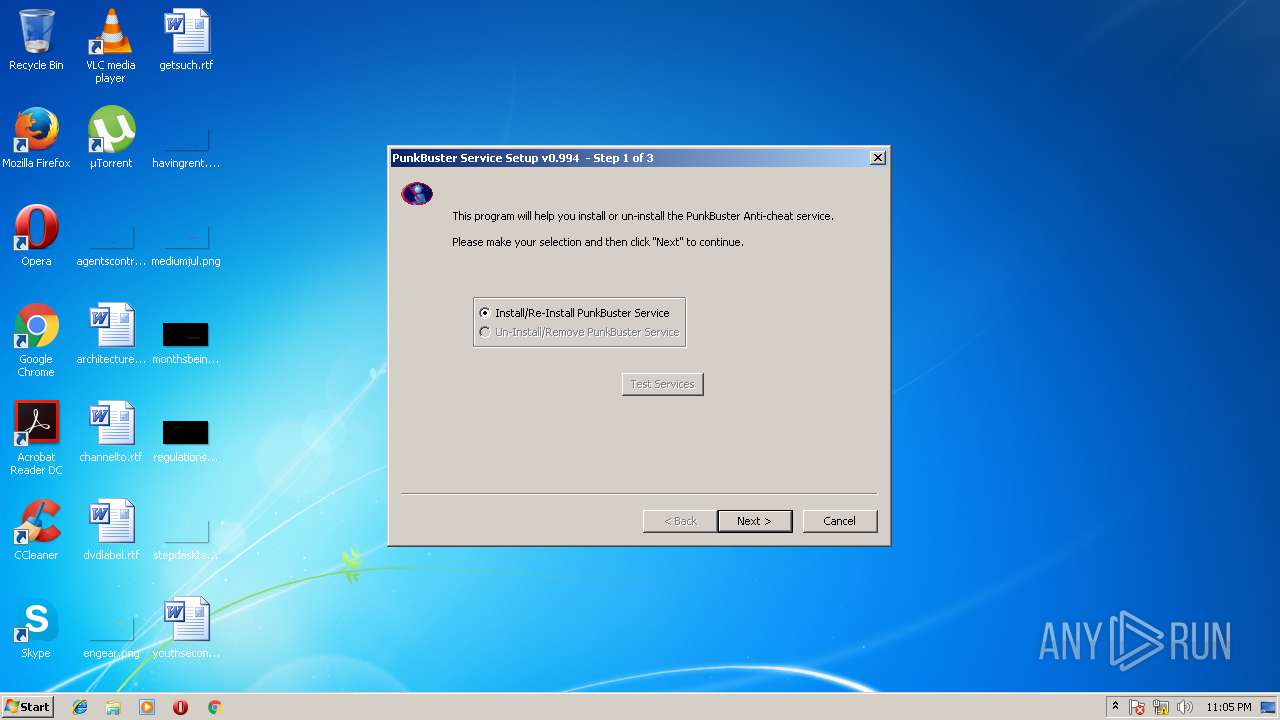
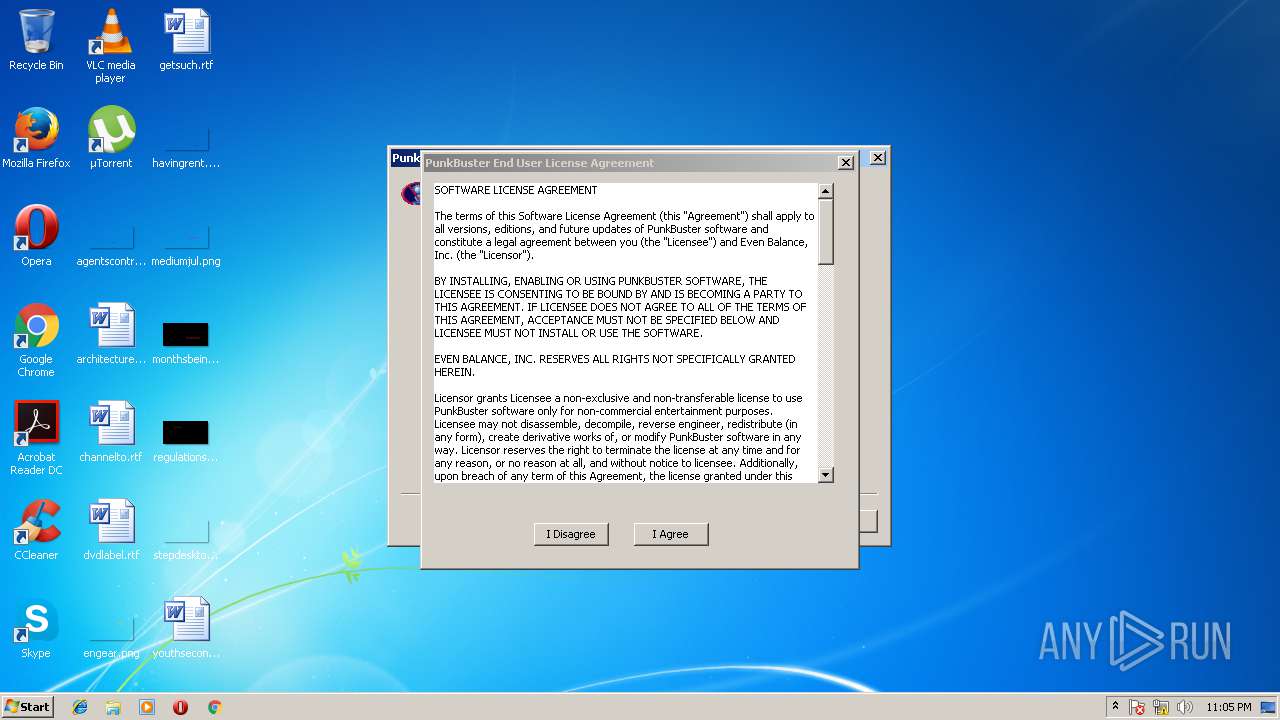
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2018, 23:05:05 |
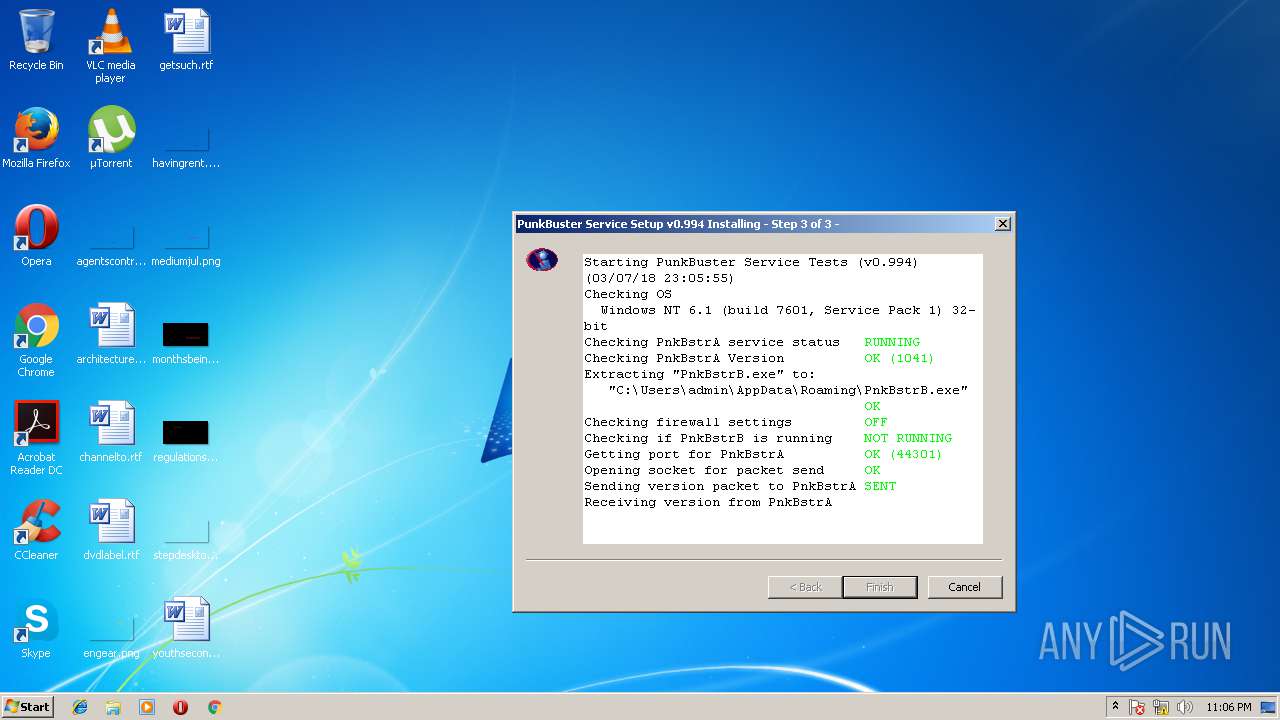
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | F4F60CAD9005F2079BDC0D570D5BAC64 |
| SHA1: | DBC4AA6F3BEBD60310BD53C52691DF401B9B4EA1 |
| SHA256: | 4DEF2FC5F862BC424E7F6857456EF05947231032583848CF9D86AA1ED452F921 |
| SSDEEP: | 24576:raXg3JnLzgubLHNxcD77DJH01rcSQcWIa+mO4MjXAgW:rZ3JLzrbLtxcDvtKrzpWN+maEgW |
MALICIOUS
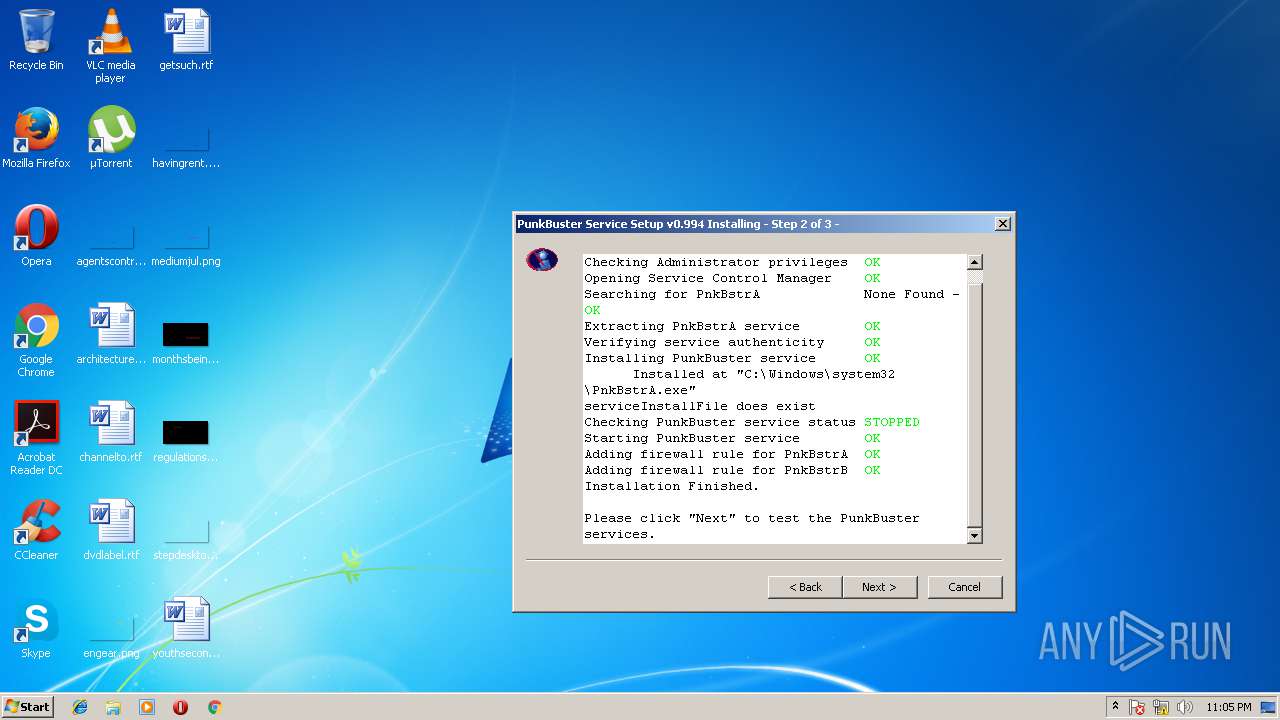
Application was dropped or rewritten from another process
- PnkBstrB.exe (PID: 4056)
- PnkBstrA.exe (PID: 2608)
SUSPICIOUS
Creates files in the Windows directory
- PnkBstrA.exe (PID: 2608)
- pbsvc.exe (PID: 3184)
- PnkBstrB.exe (PID: 4056)
Creates or modifies windows services
- PnkBstrB.exe (PID: 4056)
- PnkBstrA.exe (PID: 2608)
Modifies files in the system directory
- PnkBstrA.exe (PID: 2608)
- PnkBstrB.exe (PID: 4056)
- pbsvc.exe (PID: 3184)
Removes files from Windows directory
- PnkBstrB.exe (PID: 4056)
- PnkBstrA.exe (PID: 2608)
Creates files in the user directory
- pbsvc.exe (PID: 3184)
Creates a software uninstall entry
- pbsvc.exe (PID: 3184)
Creates files in the driver directory
- PnkBstrB.exe (PID: 4056)
INFO
Loads rich edit control libraries
- pbsvc.exe (PID: 3184)
Dropped object may contain URL's
- PnkBstrB.exe (PID: 4056)
- PnkBstrA.exe (PID: 2608)
- pbsvc.exe (PID: 3184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:06:03 01:06:35+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 798720 |
| InitializedDataSize: | 110592 |
| UninitializedDataSize: | 991232 |
| EntryPoint: | 0x1b5bb0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Jun-2014 23:06:35 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 02-Jun-2014 23:06:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x000F2000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x000F3000 | 0x000C3000 | 0x000C2E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89017 |
.rsrc | 0x001B6000 | 0x0001B000 | 0x0001A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.51279 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93207 | 633 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.63044 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.55243 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.43672 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.34576 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.84214 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.80661 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.89075 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 4.47688 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.54069 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
WINTRUST.dll |
Total processes
39
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1000 | "C:\Users\admin\AppData\Local\Temp\pbsvc.exe" | C:\Users\admin\AppData\Local\Temp\pbsvc.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 2608 | C:\Windows\system32\PnkBstrA.exe | C:\Windows\system32\PnkBstrA.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 3184 | "C:\Users\admin\AppData\Local\Temp\pbsvc.exe" | C:\Users\admin\AppData\Local\Temp\pbsvc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4056 | C:\Windows\system32\PnkBstrB.exe | C:\Windows\system32\PnkBstrB.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
Total events
113
Read events
65
Write events
48
Delete events
0
Modification events
| (PID) Process: | (3184) pbsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PunkBusterSvc |
| Operation: | write | Name: | UninstallString |
Value: C:\Windows\system32\pbsvc.exe -u | |||
| (PID) Process: | (3184) pbsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PunkBusterSvc |
| Operation: | write | Name: | DisplayName |
Value: PunkBuster Services | |||
| (PID) Process: | (3184) pbsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PunkBusterSvc |
| Operation: | write | Name: | DisplayVersion |
Value: 0.994 | |||
| (PID) Process: | (3184) pbsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PunkBusterSvc |
| Operation: | write | Name: | HelpLink |
Value: http://www.evenbalance.com/index.php?page=pbsvcfaq.php | |||
| (PID) Process: | (3184) pbsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PunkBusterSvc |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.evenbalance.com/index.php?page=pbsvcfaq.php | |||
| (PID) Process: | (3184) pbsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PunkBusterSvc |
| Operation: | write | Name: | Publisher |
Value: Even Balance, Inc. | |||
| (PID) Process: | (3184) pbsvc.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2608) PnkBstrA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Even Balance\PnkBstrA |
| Operation: | write | Name: | Port |
Value: 44301 | |||
| (PID) Process: | (2608) PnkBstrA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Even Balance\PnkBstrA |
| Operation: | write | Name: | Version |
Value: 1041 | |||
| (PID) Process: | (2608) PnkBstrA.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\PnkBstrA |
| Operation: | write | Name: | Description |
Value: PunkBuster Service Component [v1041] http://www.evenbalance.com | |||
Executable files
8
Suspicious files
8
Text files
81
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3184 | pbsvc.exe | C:\Users\admin\AppData\Local\Temp\Cab9740.tmp | — | |
MD5:— | SHA256:— | |||
| 3184 | pbsvc.exe | C:\Users\admin\AppData\Local\Temp\Tar9741.tmp | — | |
MD5:— | SHA256:— | |||
| 2608 | PnkBstrA.exe | C:\Windows\TEMP\CabF36A.tmp | — | |
MD5:— | SHA256:— | |||
| 2608 | PnkBstrA.exe | C:\Windows\TEMP\TarF36B.tmp | — | |
MD5:— | SHA256:— | |||
| 4056 | PnkBstrB.exe | C:\Windows\TEMP\CabFF03.tmp | — | |
MD5:— | SHA256:— | |||
| 4056 | PnkBstrB.exe | C:\Windows\TEMP\TarFF04.tmp | — | |
MD5:— | SHA256:— | |||
| 3184 | pbsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7D266D9E1E69FA1EEFB9699B009B34C8_0A9BFDD75B598C2110CBF610C078E6E6 | binary | |
MD5:— | SHA256:— | |||
| 3184 | pbsvc.exe | C:\Windows\system32\LogFiles\PunkBuster\pbsvc.log | text | |
MD5:— | SHA256:— | |||
| 2608 | PnkBstrA.exe | C:\Windows\system32\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7D266D9E1E69FA1EEFB9699B009B34C8_0A9BFDD75B598C2110CBF610C078E6E6 | binary | |
MD5:— | SHA256:— | |||
| 3184 | pbsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7B8944BA8AD0EFDF0E01A43EF62BECD0_99B19D26BD58DA7B2BD394E131904932 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.43.75.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEFIA5aolVvwahu2WydRLM8c%3D | NL | der | 1.71 Kb | whitelisted |
— | — | GET | 200 | 23.43.75.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTSqZMG5M8TA9rdzkbCnNwuMAd5VgQUz5mp6nsm9EvJjo%2FX8AUm7%2BPSp50CECcrUt%2FpzwJGAyc4zugcPBc%3D | NL | der | 1.62 Kb | whitelisted |
— | — | GET | 200 | 23.43.75.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTSqZMG5M8TA9rdzkbCnNwuMAd5VgQUz5mp6nsm9EvJjo%2FX8AUm7%2BPSp50CECcrUt%2FpzwJGAyc4zugcPBc%3D | NL | der | 1.62 Kb | whitelisted |
— | — | GET | 200 | 23.43.75.27:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEFIA5aolVvwahu2WydRLM8c%3D | NL | der | 1.71 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 23.43.75.27:80 | ocsp.verisign.com | Akamai Technologies, Inc. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.verisign.com |
| whitelisted |