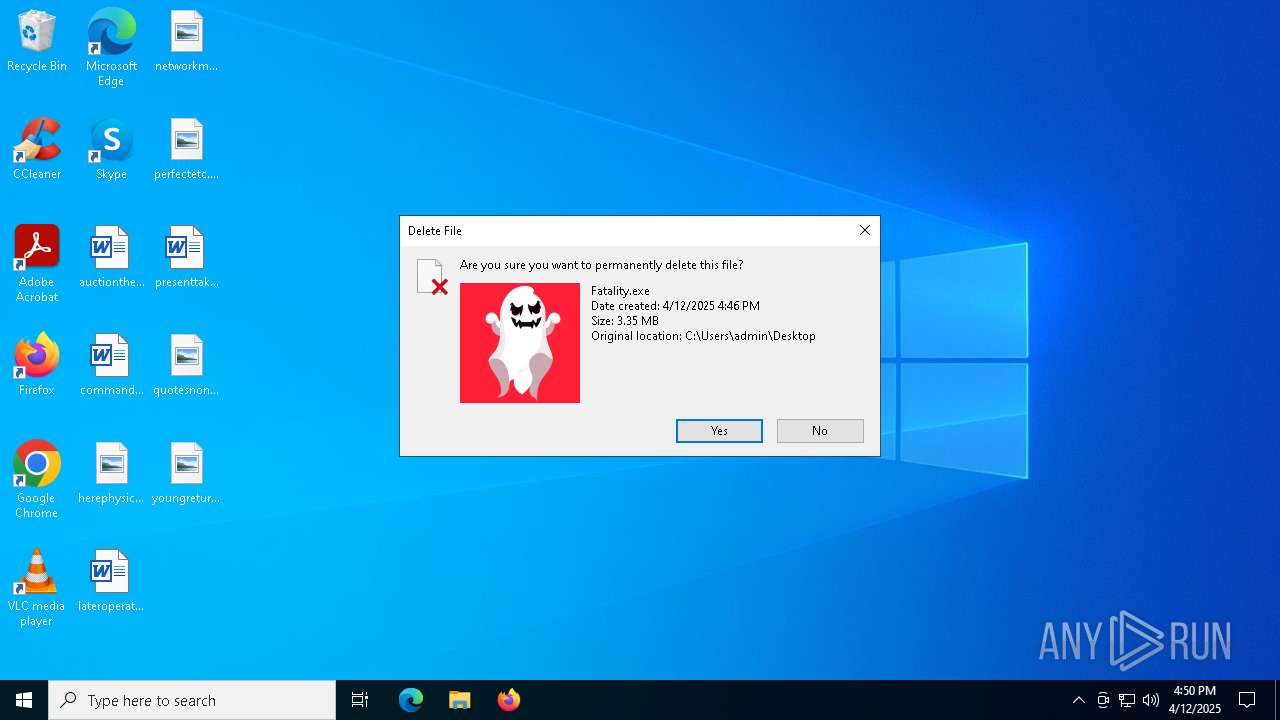
| File name: | Fatality.exe |
| Full analysis: | https://app.any.run/tasks/87a7b1f6-ba98-4779-b7b7-c28bbc7dc419 |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | April 12, 2025, 16:45:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 9 sections |
| MD5: | A5A9CDE94B59BC5B8B88D60FC28177D3 |
| SHA1: | ABA15BC72CDEB915369B481926676F0A452D6DCC |
| SHA256: | 4DDD25095CCE5DADC01782611513331E9FB1E37746ADC5501A5B27C2B7AECFA6 |
| SSDEEP: | 98304:b7i1UGL37sVlGvX0UgRBYgaxkEb2nzkNTHae2y5XfW7OM1N8nNBv5guSGC5H/yR3:8+63DAS/mGR |
MALICIOUS
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2320)
DCRAT mutex has been found
- BridgeInto.exe (PID: 2236)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
Changes the autorun value in the registry
- BridgeInto.exe (PID: 2236)
Connects to the CnC server
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
DARKCRYSTAL has been detected (SURICATA)
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
SUSPICIOUS
Executable content was dropped or overwritten
- Fatality.exe (PID: 1196)
- BridgeInto.exe (PID: 2236)
- csc.exe (PID: 5392)
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
Reads security settings of Internet Explorer
- Fatality.exe (PID: 1196)
- BridgeInto.exe (PID: 2236)
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
Executing commands from a ".bat" file
- wscript.exe (PID: 2320)
- BridgeInto.exe (PID: 2236)
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2320)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2320)
- BridgeInto.exe (PID: 2236)
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
The process creates files with name similar to system file names
- BridgeInto.exe (PID: 2236)
Executed via WMI
- schtasks.exe (PID: 5216)
- schtasks.exe (PID: 2284)
- schtasks.exe (PID: 3100)
- schtasks.exe (PID: 208)
- schtasks.exe (PID: 2772)
- schtasks.exe (PID: 4188)
- schtasks.exe (PID: 5956)
- schtasks.exe (PID: 728)
- schtasks.exe (PID: 3008)
- schtasks.exe (PID: 6272)
- schtasks.exe (PID: 6972)
- schtasks.exe (PID: 2148)
- schtasks.exe (PID: 6044)
- schtasks.exe (PID: 6744)
- schtasks.exe (PID: 5800)
- schtasks.exe (PID: 1628)
- schtasks.exe (PID: 1128)
- schtasks.exe (PID: 3676)
Process drops legitimate windows executable
- BridgeInto.exe (PID: 2236)
Reads the date of Windows installation
- BridgeInto.exe (PID: 2236)
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
Starts application with an unusual extension
- cmd.exe (PID: 1040)
- cmd.exe (PID: 4980)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 1912)
- cmd.exe (PID: 2664)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 5044)
- cmd.exe (PID: 7152)
- cmd.exe (PID: 3024)
- cmd.exe (PID: 4284)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6072)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 4304)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 2776)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 4208)
- cmd.exe (PID: 5756)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 6900)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 4932)
- cmd.exe (PID: 3192)
- cmd.exe (PID: 680)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 1040)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 2664)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 5044)
- cmd.exe (PID: 7152)
- cmd.exe (PID: 3024)
- cmd.exe (PID: 4284)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6072)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 4304)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 2776)
- cmd.exe (PID: 4208)
- cmd.exe (PID: 6900)
- cmd.exe (PID: 4932)
- cmd.exe (PID: 680)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 4980)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 1912)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 5756)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 3192)
Loads DLL from Mozilla Firefox
- default-browser-agent.exe (PID: 6592)
The process executes via Task Scheduler
- default-browser-agent.exe (PID: 6592)
INFO
Reads the computer name
- Fatality.exe (PID: 1196)
- BridgeInto.exe (PID: 2236)
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
Checks supported languages
- Fatality.exe (PID: 1196)
- BridgeInto.exe (PID: 2236)
- csc.exe (PID: 5392)
- cvtres.exe (PID: 3896)
- chcp.com (PID: 2040)
- fontdrvhost.exe (PID: 2108)
- chcp.com (PID: 5964)
- fontdrvhost.exe (PID: 3020)
- chcp.com (PID: 2772)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- chcp.com (PID: 6668)
- chcp.com (PID: 4464)
- fontdrvhost.exe (PID: 1616)
- chcp.com (PID: 6852)
- fontdrvhost.exe (PID: 1096)
- chcp.com (PID: 4180)
- chcp.com (PID: 6872)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- chcp.com (PID: 5332)
- fontdrvhost.exe (PID: 5324)
- chcp.com (PID: 4040)
- fontdrvhost.exe (PID: 2552)
- chcp.com (PID: 6032)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- chcp.com (PID: 6668)
- chcp.com (PID: 5328)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 5756)
- chcp.com (PID: 6244)
- chcp.com (PID: 6824)
- fontdrvhost.exe (PID: 2776)
- chcp.com (PID: 1660)
- fontdrvhost.exe (PID: 6564)
- chcp.com (PID: 4188)
- fontdrvhost.exe (PID: 6456)
- chcp.com (PID: 1164)
- fontdrvhost.exe (PID: 4980)
- chcp.com (PID: 2244)
- fontdrvhost.exe (PID: 3804)
- chcp.com (PID: 3032)
- chcp.com (PID: 5800)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- chcp.com (PID: 684)
- fontdrvhost.exe (PID: 3888)
- chcp.com (PID: 6268)
- fontdrvhost.exe (PID: 5960)
- chcp.com (PID: 2392)
- fontdrvhost.exe (PID: 4740)
- default-browser-agent.exe (PID: 6592)
- chcp.com (PID: 4172)
- fontdrvhost.exe (PID: 3828)
- chcp.com (PID: 6404)
- fontdrvhost.exe (PID: 1300)
- chcp.com (PID: 6564)
- chcp.com (PID: 1748)
- fontdrvhost.exe (PID: 660)
- chcp.com (PID: 2104)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
- chcp.com (PID: 6148)
- chcp.com (PID: 5036)
Process checks computer location settings
- Fatality.exe (PID: 1196)
- BridgeInto.exe (PID: 2236)
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
Drops encrypted VBS script (Microsoft Script Encoder)
- Fatality.exe (PID: 1196)
Reads the machine GUID from the registry
- BridgeInto.exe (PID: 2236)
- csc.exe (PID: 5392)
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
Reads Environment values
- BridgeInto.exe (PID: 2236)
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
The sample compiled with english language support
- BridgeInto.exe (PID: 2236)
Creates files or folders in the user directory
- csc.exe (PID: 5392)
Create files in a temporary directory
- cvtres.exe (PID: 3896)
- BridgeInto.exe (PID: 2236)
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
Changes the display of characters in the console
- cmd.exe (PID: 1040)
- cmd.exe (PID: 4980)
- cmd.exe (PID: 2040)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 1912)
- cmd.exe (PID: 2664)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 5044)
- cmd.exe (PID: 7152)
- cmd.exe (PID: 3024)
- cmd.exe (PID: 4284)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6072)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 4304)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 2776)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 4208)
- cmd.exe (PID: 5756)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 6900)
- cmd.exe (PID: 4528)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 4932)
- cmd.exe (PID: 3192)
- cmd.exe (PID: 680)
Checks proxy server information
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- slui.exe (PID: 6192)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
Disables trace logs
- fontdrvhost.exe (PID: 2108)
- fontdrvhost.exe (PID: 3020)
- fontdrvhost.exe (PID: 4844)
- fontdrvhost.exe (PID: 6372)
- fontdrvhost.exe (PID: 1616)
- fontdrvhost.exe (PID: 1096)
- fontdrvhost.exe (PID: 5588)
- fontdrvhost.exe (PID: 6660)
- fontdrvhost.exe (PID: 5324)
- fontdrvhost.exe (PID: 2552)
- fontdrvhost.exe (PID: 4920)
- fontdrvhost.exe (PID: 1056)
- fontdrvhost.exe (PID: 5756)
- fontdrvhost.exe (PID: 7100)
- fontdrvhost.exe (PID: 2776)
- fontdrvhost.exe (PID: 6564)
- fontdrvhost.exe (PID: 6456)
- fontdrvhost.exe (PID: 4980)
- fontdrvhost.exe (PID: 3804)
- fontdrvhost.exe (PID: 132)
- fontdrvhost.exe (PID: 6436)
- fontdrvhost.exe (PID: 3888)
- fontdrvhost.exe (PID: 5960)
- fontdrvhost.exe (PID: 4740)
- fontdrvhost.exe (PID: 3828)
- fontdrvhost.exe (PID: 1300)
- fontdrvhost.exe (PID: 660)
- fontdrvhost.exe (PID: 444)
- fontdrvhost.exe (PID: 208)
- fontdrvhost.exe (PID: 7100)
Reads the software policy settings
- slui.exe (PID: 668)
- slui.exe (PID: 6192)
Application launched itself
- firefox.exe (PID: 6516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:03:03 13:15:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 203776 |
| InitializedDataSize: | 348160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x17172 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
316
Monitored processes
187
Malicious processes
60
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Bridgemonitor\fontdrvhost.exe" | C:\Bridgemonitor\fontdrvhost.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 208 | schtasks.exe /create /tn "audiodg" /sc ONLOGON /tr "'C:\Users\admin\Recent\audiodg.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | "C:\Bridgemonitor\fontdrvhost.exe" | C:\Bridgemonitor\fontdrvhost.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | "C:\Bridgemonitor\fontdrvhost.exe" | C:\Bridgemonitor\fontdrvhost.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 536 | w32tm /stripchart /computer:localhost /period:5 /dataonly /samples:2 | C:\Windows\System32\w32tm.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Time Service Diagnostic Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Bridgemonitor\fontdrvhost.exe" | C:\Bridgemonitor\fontdrvhost.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 668 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | w32tm /stripchart /computer:localhost /period:5 /dataonly /samples:2 | C:\Windows\System32\w32tm.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Time Service Diagnostic Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\jAyUy8CkP5.bat" " | C:\Windows\System32\cmd.exe | — | fontdrvhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
92 644
Read events
92 620
Write events
24
Delete events
0
Modification events
| (PID) Process: | (1196) Fatality.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbe\OpenWithProgids |
| Operation: | write | Name: | VBEFile |
Value: | |||
| (PID) Process: | (2236) BridgeInto.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\b0eaa1f92064a8cd0be1d4f73315790eb62badcd |
| Operation: | write | Name: | a6a1bc5c8616b7ba2e4c1d8bdc1c5da2d943c8c0 |
Value: H4sIAAAAAAAEAH2NsQ5AUAxF/8UsPsDIwipMahAtOmjlvT7x+YTFgPHknNzbRnkKkDnGiRYVNnUAnmf1ltBOUfzmwzoOD9t4ch6gx4UFoKKBxE4MyIrT98qoYui2/6uaditlDVb8ZjeWYno13QFr1yXG1wAAAA== | |||
| (PID) Process: | (2236) BridgeInto.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | sihost |
Value: "C:\Bridgemonitor\sihost.exe" | |||
| (PID) Process: | (2236) BridgeInto.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | audiodg |
Value: "C:\Users\admin\Recent\audiodg.exe" | |||
| (PID) Process: | (2236) BridgeInto.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | upfc |
Value: "C:\Bridgemonitor\upfc.exe" | |||
| (PID) Process: | (2236) BridgeInto.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | fontdrvhost |
Value: "C:\Bridgemonitor\fontdrvhost.exe" | |||
| (PID) Process: | (2236) BridgeInto.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | TextInputHost |
Value: "C:\Bridgemonitor\TextInputHost.exe" | |||
| (PID) Process: | (2236) BridgeInto.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | BridgeInto |
Value: "C:\Bridgemonitor\BridgeInto.exe" | |||
| (PID) Process: | (2108) fontdrvhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\fontdrvhost_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2108) fontdrvhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\fontdrvhost_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
163
Suspicious files
5
Text files
74
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2236 | BridgeInto.exe | C:\Bridgemonitor\66fc9ff0ee96c2 | text | |
MD5:C2F570BE2824418573A7C9170244EB28 | SHA256:4EF611DFD3605BCA05F539F0E7E84CD20F0DB7F91592DE590EDC4A24D213ABA3 | |||
| 1196 | Fatality.exe | C:\Bridgemonitor\zS0fKDlKT05bxtO58C1eiBYQ1f.bat | text | |
MD5:A7FA89383504A3BAD95435CD5195F415 | SHA256:39258C93ECEA054B48C5713407938AA5358BE3BA254D935DE85A9533169BB7E4 | |||
| 2236 | BridgeInto.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\42af1c969fbb7b | text | |
MD5:9D4F6088F461CC335FF50D451076ADFC | SHA256:FD44D06605216B53162A8680376D9A3FC8B759F9C68B10884F6E675BACDE441D | |||
| 2236 | BridgeInto.exe | C:\Bridgemonitor\TextInputHost.exe | executable | |
MD5:910284D590BDF27BBEEDBDE3F3A2A94D | SHA256:6A397C6E1041AD55295C3FE2CF7F795DA853004C1A02E1D77C65F0DA86AD312E | |||
| 2236 | BridgeInto.exe | C:\Bridgemonitor\ea1d8f6d871115 | text | |
MD5:98A0E368C1ACC815D6B4C1EC15E23B56 | SHA256:A2C9005232AA7DEA80C5F529044C68225FCB6F089CD814DF84CB07C2ED578E06 | |||
| 1196 | Fatality.exe | C:\Bridgemonitor\BridgeInto.exe | executable | |
MD5:910284D590BDF27BBEEDBDE3F3A2A94D | SHA256:6A397C6E1041AD55295C3FE2CF7F795DA853004C1A02E1D77C65F0DA86AD312E | |||
| 2236 | BridgeInto.exe | C:\Bridgemonitor\fontdrvhost.exe | executable | |
MD5:910284D590BDF27BBEEDBDE3F3A2A94D | SHA256:6A397C6E1041AD55295C3FE2CF7F795DA853004C1A02E1D77C65F0DA86AD312E | |||
| 2236 | BridgeInto.exe | C:\Bridgemonitor\5b884080fd4f94 | text | |
MD5:D8043C614901601ED1072AC5F8B8E421 | SHA256:2FA165C082BDB00E6079F23B93FF1382F7B527C8A533593C4574CF66641CC79D | |||
| 2236 | BridgeInto.exe | C:\Users\admin\Desktop\BeGNCjtE.log | executable | |
MD5:F4B38D0F95B7E844DD288B441EBC9AAF | SHA256:AAB95596475CA74CEDE5BA50F642D92FA029F6F74F6FAEAE82A9A07285A5FB97 | |||
| 2236 | BridgeInto.exe | C:\Users\admin\Desktop\kXpiiwOp.log | executable | |
MD5:0B2AFABFAF0DD55AD21AC76FBF03B8A0 | SHA256:DD4560987BD87EF3E6E8FAE220BA22AA08812E9743352523C846553BD99E4254 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
52
DNS requests
16
Threats
90
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5892 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2108 | fontdrvhost.exe | POST | 200 | 15.197.130.221:80 | http://373292cm.nyashka.top/JavascriptSecureSqlLocalTemporary.php | unknown | — | — | malicious |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5892 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3020 | fontdrvhost.exe | POST | 200 | 15.197.130.221:80 | http://373292cm.nyashka.top/JavascriptSecureSqlLocalTemporary.php | unknown | — | — | malicious |
1616 | fontdrvhost.exe | POST | 200 | 15.197.130.221:80 | http://373292cm.nyashka.top/JavascriptSecureSqlLocalTemporary.php | unknown | — | — | malicious |
1096 | fontdrvhost.exe | POST | 200 | 15.197.130.221:80 | http://373292cm.nyashka.top/JavascriptSecureSqlLocalTemporary.php | unknown | — | — | malicious |
6660 | fontdrvhost.exe | POST | 200 | 15.197.130.221:80 | http://373292cm.nyashka.top/JavascriptSecureSqlLocalTemporary.php | unknown | — | — | malicious |
5324 | fontdrvhost.exe | POST | 200 | 15.197.130.221:80 | http://373292cm.nyashka.top/JavascriptSecureSqlLocalTemporary.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5892 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2108 | fontdrvhost.exe | 15.197.130.221:80 | 373292cm.nyashka.top | AMAZON-02 | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
373292cm.nyashka.top |
| malicious |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2108 | fontdrvhost.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 5 |
2108 | fontdrvhost.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2108 | fontdrvhost.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 4 |
2108 | fontdrvhost.exe | Generic Protocol Command Decode | SURICATA HTTP status 100-Continue already seen |
2108 | fontdrvhost.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
2108 | fontdrvhost.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
3020 | fontdrvhost.exe | Generic Protocol Command Decode | SURICATA HTTP status 100-Continue already seen |
3020 | fontdrvhost.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
3020 | fontdrvhost.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |