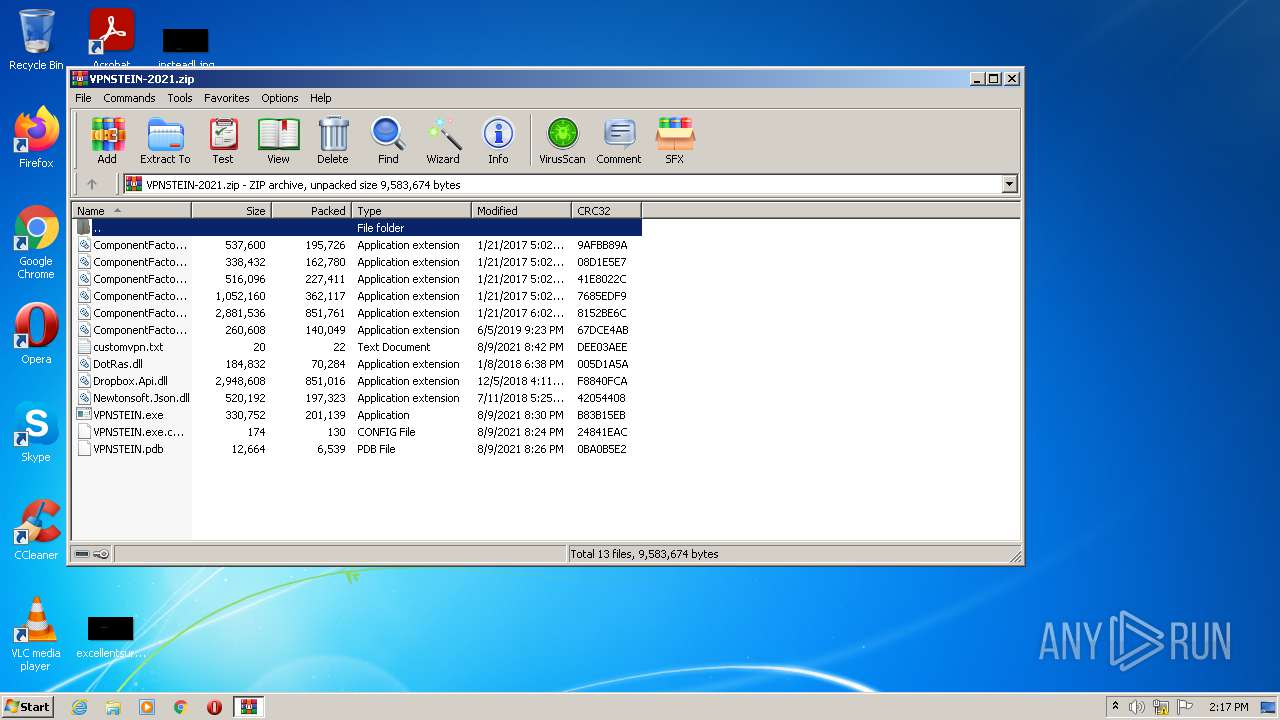
| File name: | VPNSTEIN-2021.zip |
| Full analysis: | https://app.any.run/tasks/527da28c-d2bd-45db-adf4-e8758d5d3050 |
| Verdict: | Malicious activity |
| Analysis date: | August 16, 2021, 13:16:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B04BE173C1BF3B253960C318A86BB117 |
| SHA1: | 005C9EFE92C017A51C59EB0D6F0443DAE40358BC |
| SHA256: | 4DCF7A22FE3C62AA08E55C2286C21BCC1AA30C046BBDFD455D5ABF8FE3464A01 |
| SSDEEP: | 98304:R8bZUgZx8Bckt7ItiDmxktPpLI0C+dSVFC2Lg9JMWo/:R8bWQx8rt8tixxITLZg4X/ |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2092)
- VPNSTEIN.exe (PID: 3980)
Application was dropped or rewritten from another process
- VPNSTEIN.exe (PID: 2792)
- VPNSTEIN.exe (PID: 3980)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2268)
- VPNSTEIN.exe (PID: 3980)
Reads the computer name
- WinRAR.exe (PID: 2268)
- VPNSTEIN.exe (PID: 3980)
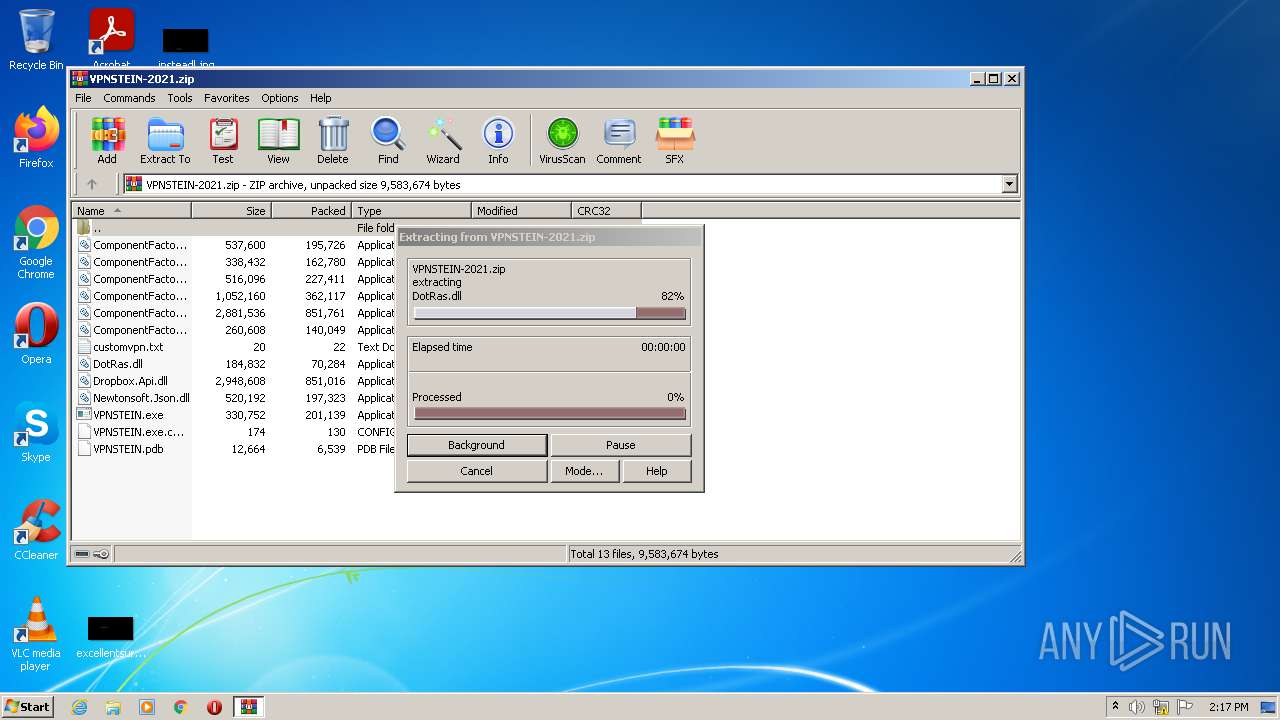
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2268)
Drops a file with too old compile date
- WinRAR.exe (PID: 2268)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2268)
Reads Environment values
- VPNSTEIN.exe (PID: 3980)
Reads internet explorer settings
- VPNSTEIN.exe (PID: 3980)
Creates files in the program directory
- VPNSTEIN.exe (PID: 3980)
INFO
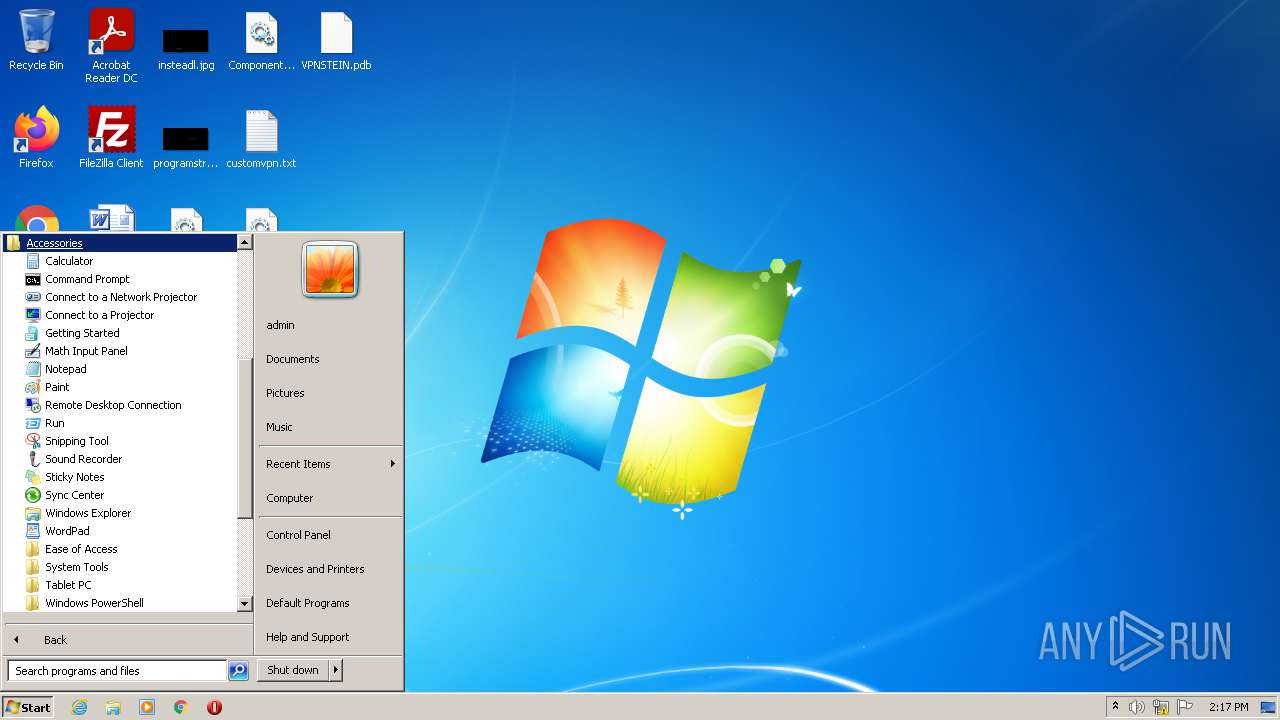
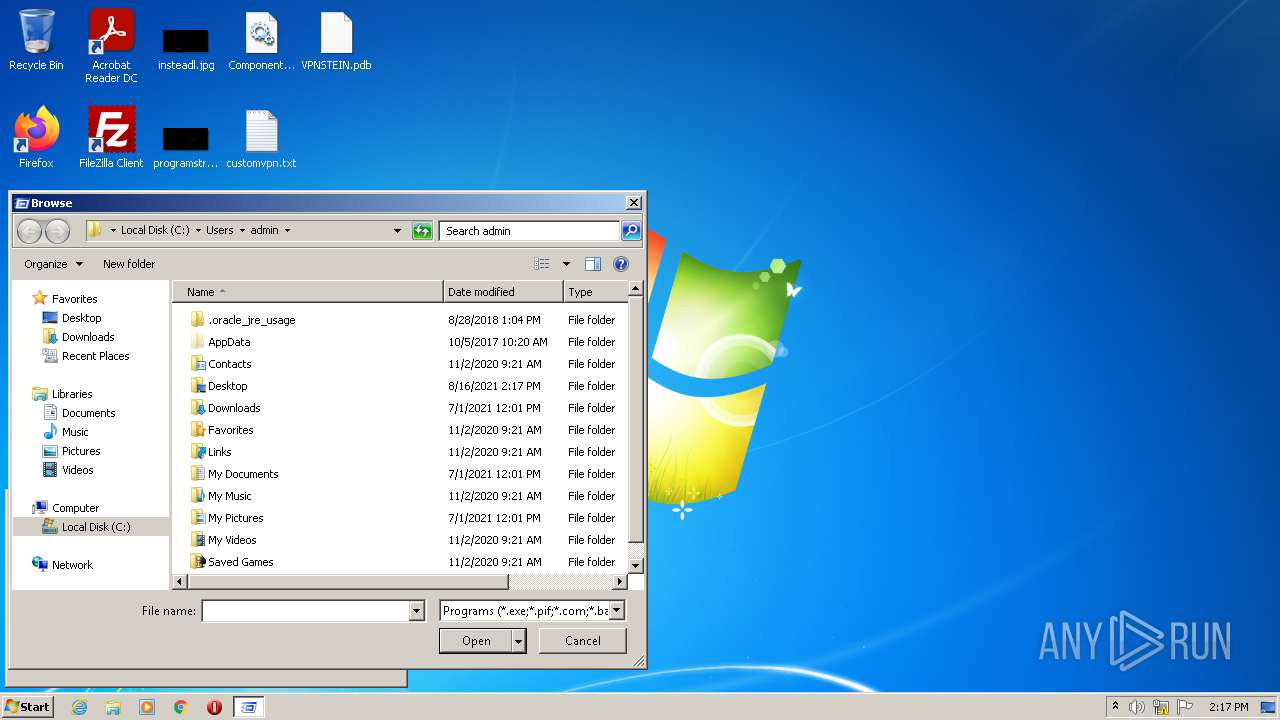
Manual execution by user
- VPNSTEIN.exe (PID: 2792)
- VPNSTEIN.exe (PID: 3980)
Reads settings of System Certificates
- VPNSTEIN.exe (PID: 3980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
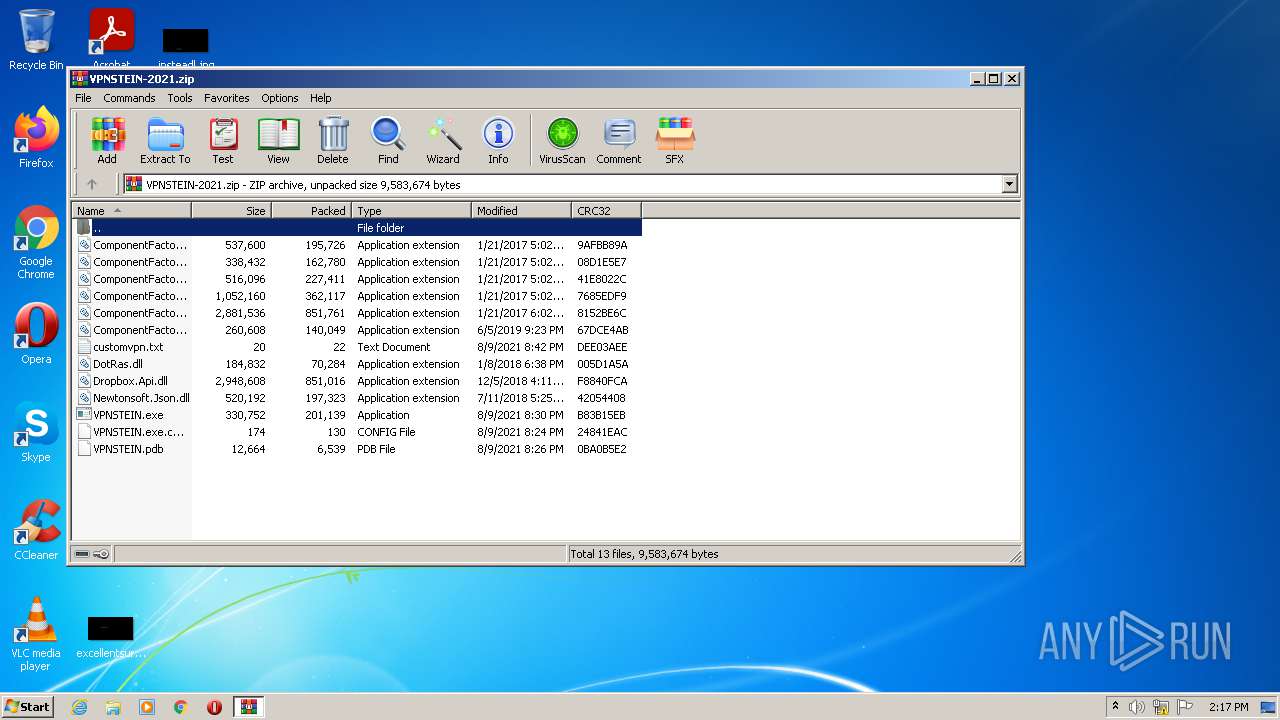
| ZipFileName: | VPNSTEIN.exe |
|---|---|
| ZipUncompressedSize: | 330752 |
| ZipCompressedSize: | 201139 |
| ZipCRC: | 0xb83b15eb |
| ZipModifyDate: | 2021:08:09 21:30:00 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
43
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2092 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
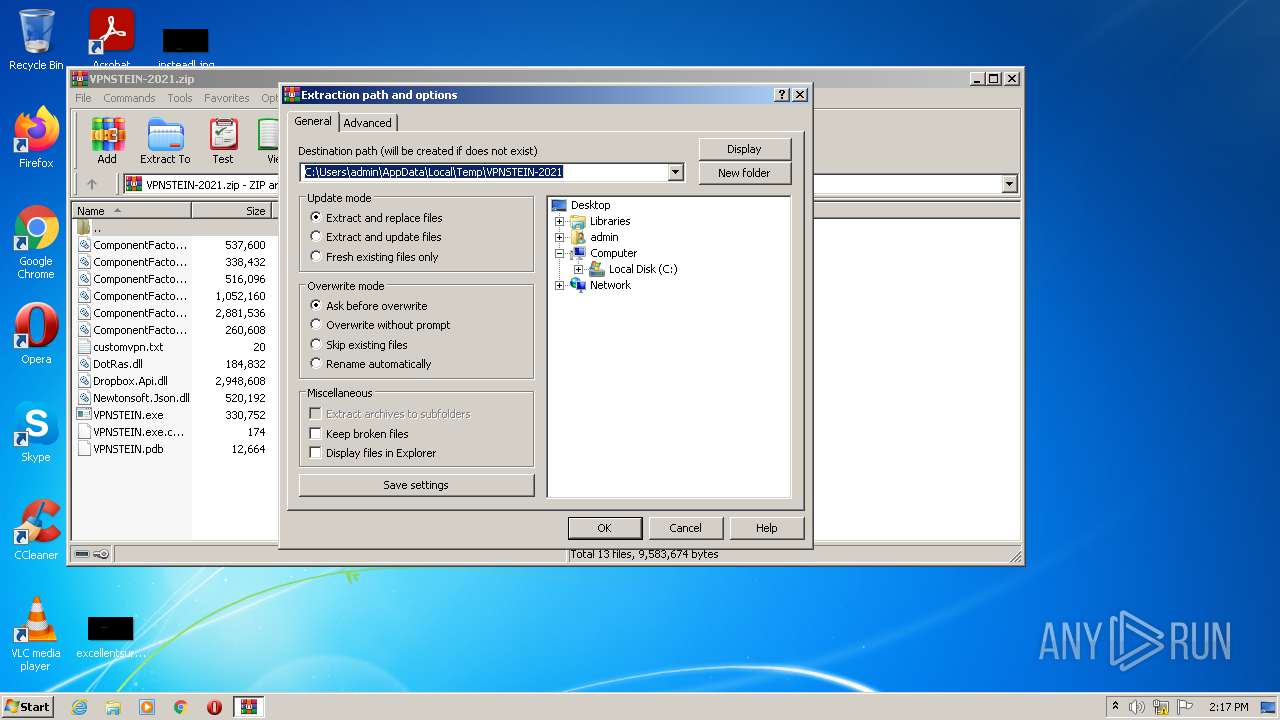
| 2268 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\VPNSTEIN-2021.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
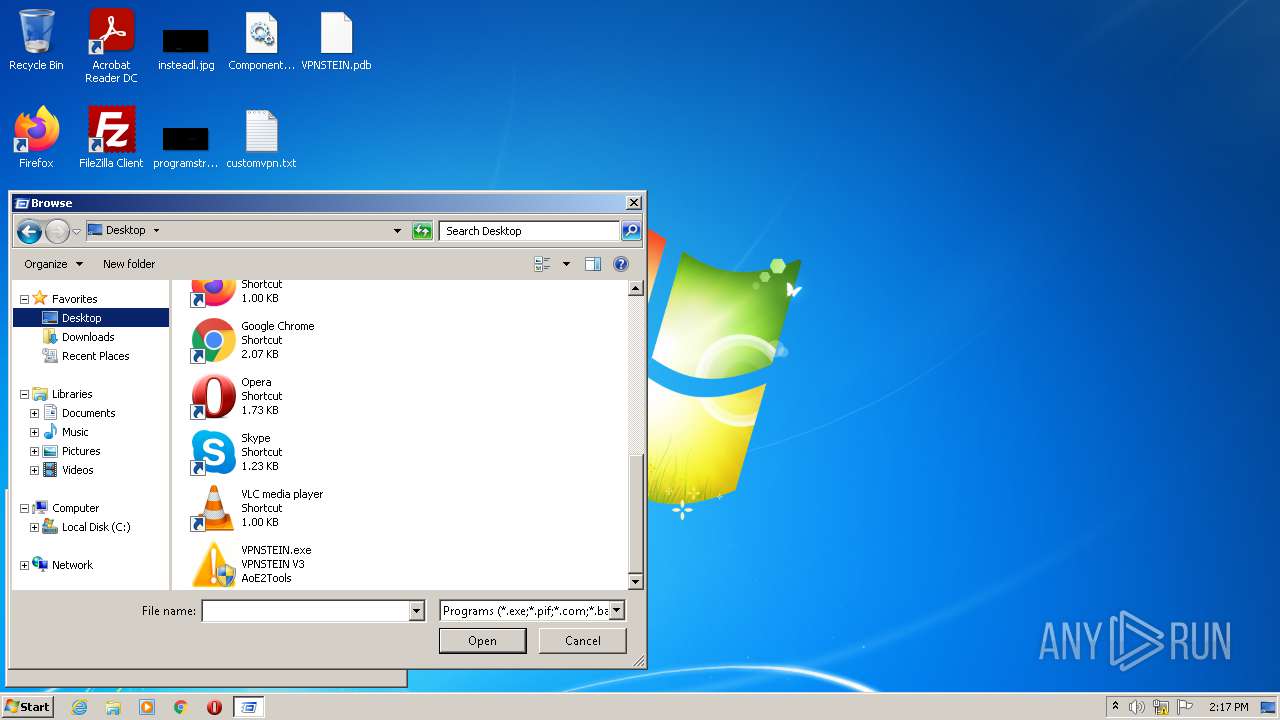
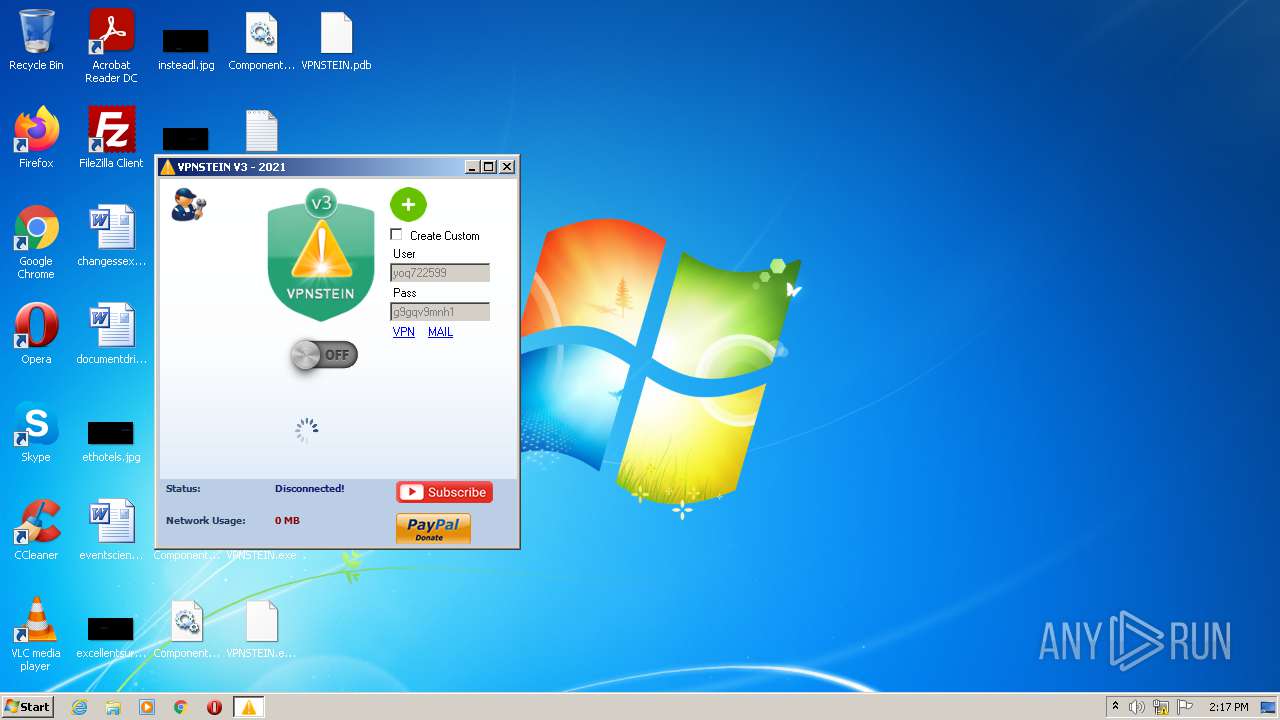
| 2792 | "C:\Users\admin\Desktop\VPNSTEIN.exe" | C:\Users\admin\Desktop\VPNSTEIN.exe | — | Explorer.EXE | |||||||||||
User: admin Company: AoE2Tools Integrity Level: MEDIUM Description: VPNSTEIN V3 Exit code: 3221226540 Version: 3.0.0.0 Modules
| |||||||||||||||
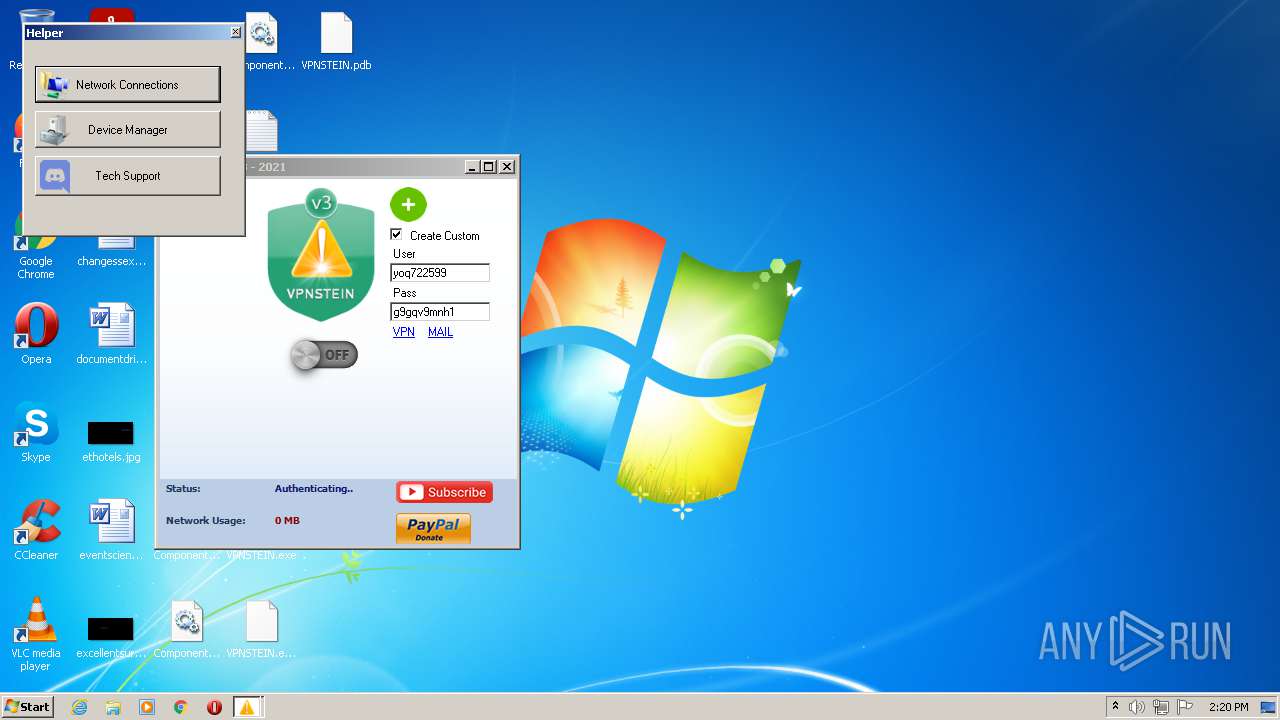
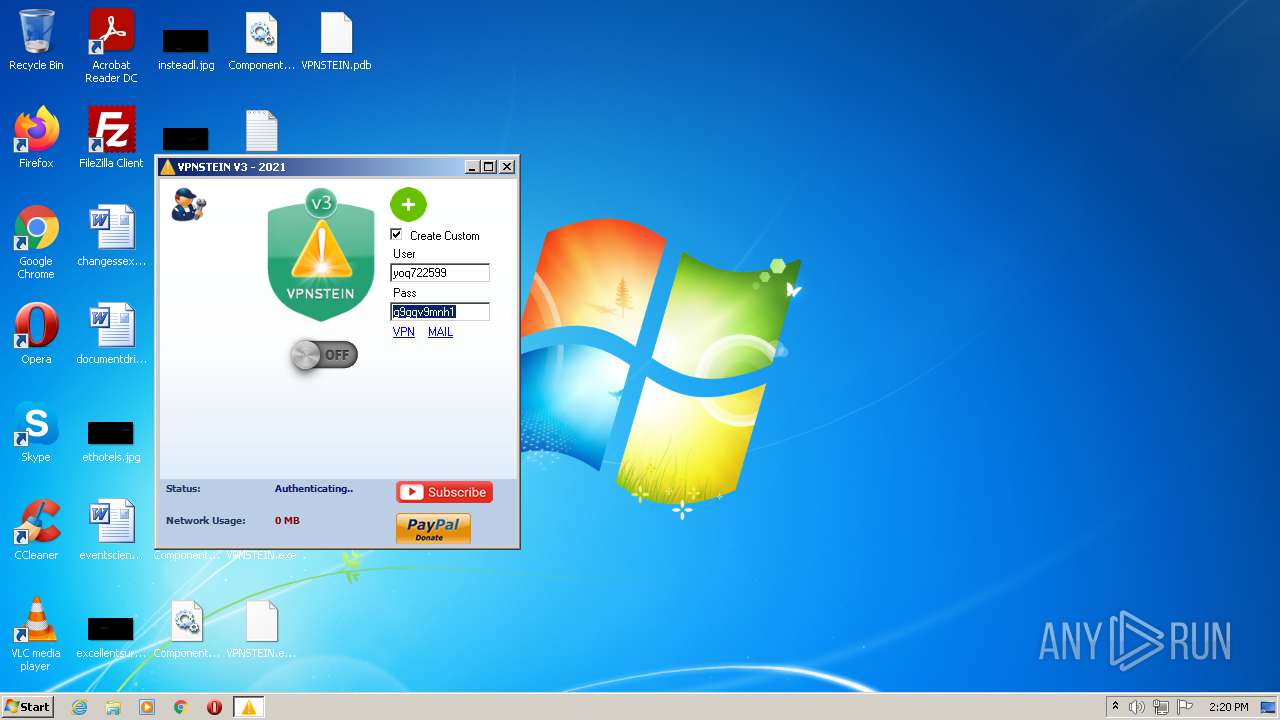
| 3980 | "C:\Users\admin\Desktop\VPNSTEIN.exe" | C:\Users\admin\Desktop\VPNSTEIN.exe | Explorer.EXE | ||||||||||||
User: admin Company: AoE2Tools Integrity Level: HIGH Description: VPNSTEIN V3 Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
Total events
5 256
Read events
5 183
Write events
73
Delete events
0
Modification events
| (PID) Process: | (2268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2268) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\VPNSTEIN-2021.zip | |||
| (PID) Process: | (2268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2268) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
10
Suspicious files
1
Text files
5
Unknown types
0
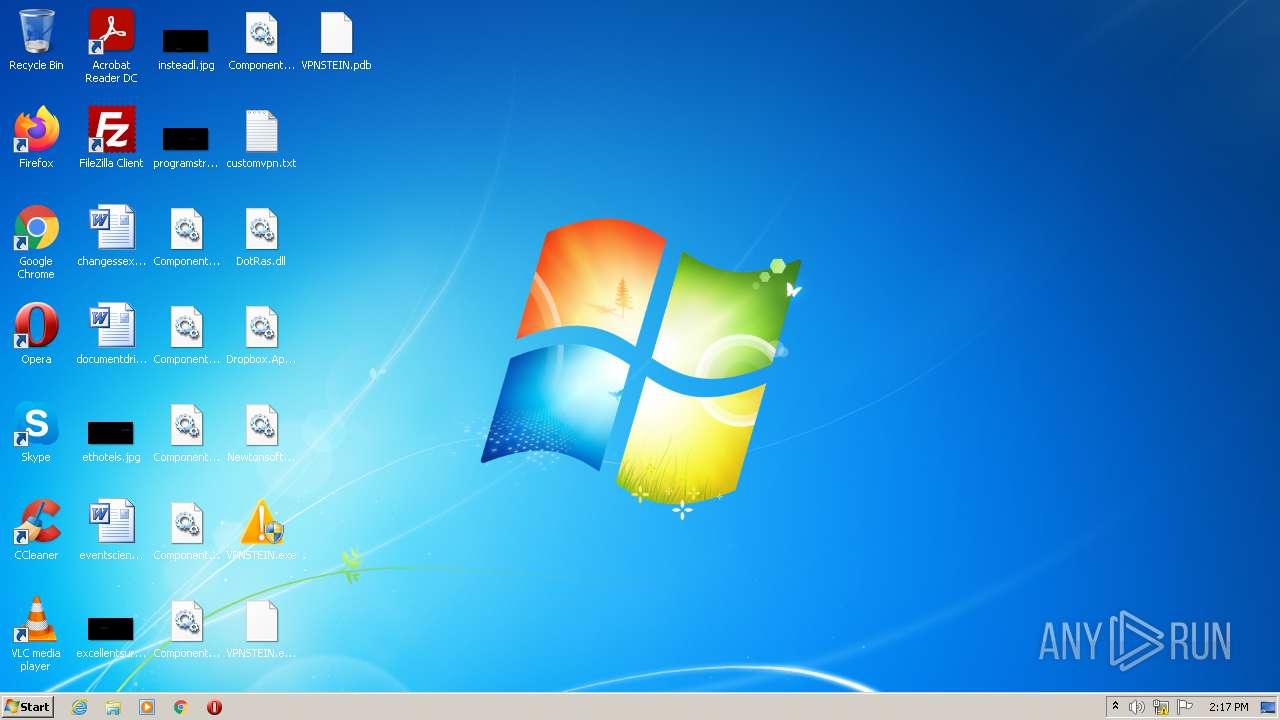
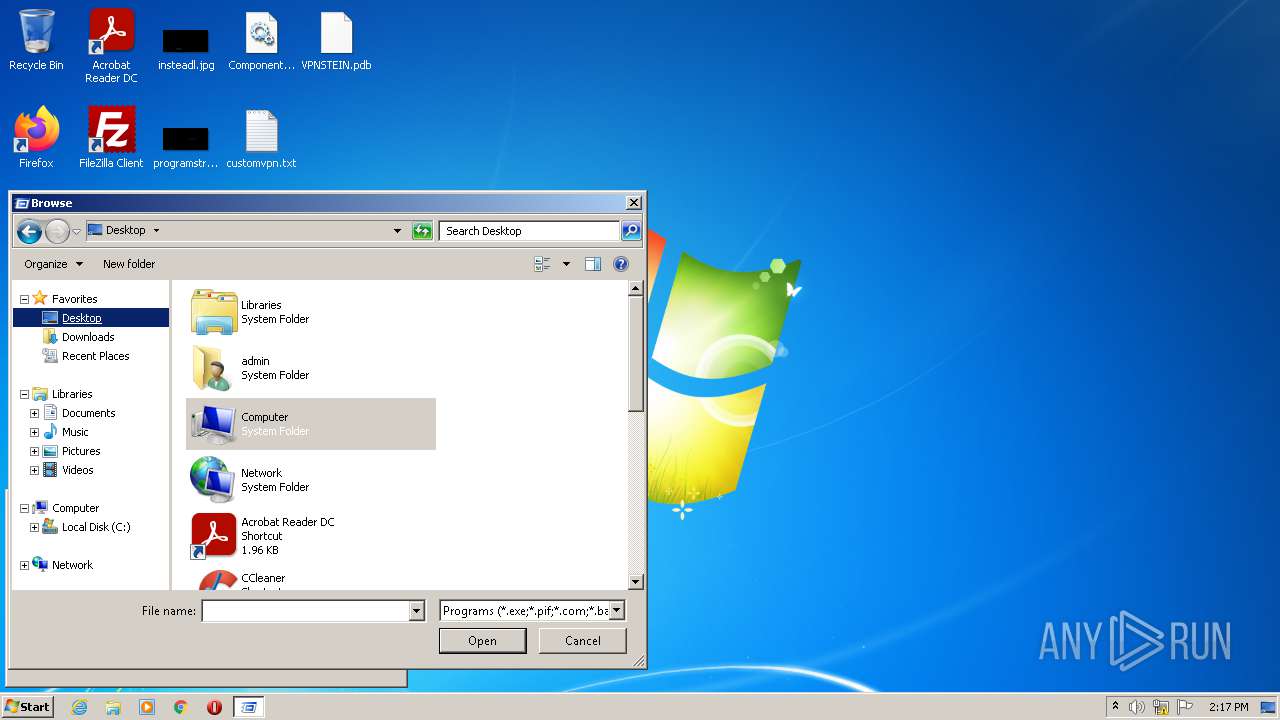
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2268 | WinRAR.exe | C:\Users\admin\Desktop\ComponentFactory.Krypton.Navigator.dll | executable | |
MD5:— | SHA256:— | |||
| 2268 | WinRAR.exe | C:\Users\admin\Desktop\customvpn.txt | text | |
MD5:— | SHA256:— | |||
| 2268 | WinRAR.exe | C:\Users\admin\Desktop\ComponentFactory.Krypton.Toolkit.dll | executable | |
MD5:— | SHA256:— | |||
| 2268 | WinRAR.exe | C:\Users\admin\Desktop\DotRas.dll | executable | |
MD5:— | SHA256:— | |||
| 2268 | WinRAR.exe | C:\Users\admin\Desktop\VPNSTEIN.exe | executable | |
MD5:— | SHA256:— | |||
| 2268 | WinRAR.exe | C:\Users\admin\Desktop\ComponentFactory.Krypton.Ribbon.dll | executable | |
MD5:— | SHA256:— | |||
| 2268 | WinRAR.exe | C:\Users\admin\Desktop\ComponentFactory.Krypton.Workspace.dll | executable | |
MD5:— | SHA256:— | |||
| 3980 | VPNSTEIN.exe | C:\ProgramData\Microsoft\Network\Connections\Pbk\rasphone.pbk | text | |
MD5:— | SHA256:— | |||
| 3980 | VPNSTEIN.exe | C:\Users\admin\AppData\Local\Temp\server.txt | text | |
MD5:— | SHA256:— | |||
| 2268 | WinRAR.exe | C:\Users\admin\Desktop\ComponentFactory.Krypton.Design.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
5
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3980 | VPNSTEIN.exe | 162.125.66.14:443 | content.dropboxapi.com | Dropbox, Inc. | DE | suspicious |
4 | System | 188.121.240.37:1723 | pptp.ipjetable.net | Lost Oasis SARL | NL | unknown |
4 | System | 188.121.240.6:1723 | pptp.ipjetable.net | Lost Oasis SARL | NL | suspicious |
— | — | 188.121.240.37:443 | pptp.ipjetable.net | Lost Oasis SARL | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |
content.dropboxapi.com |
| suspicious |
pptp.ipjetable.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3980 | VPNSTEIN.exe | Potential Corporate Privacy Violation | ET POLICY [401TRG] DropBox Access via API (SNI) |
3980 | VPNSTEIN.exe | Potential Corporate Privacy Violation | ET POLICY [401TRG] DropBox Access via API (Certificate) |
896 | svchost.exe | Generic Protocol Command Decode | SURICATA IKEv2 malformed request data |