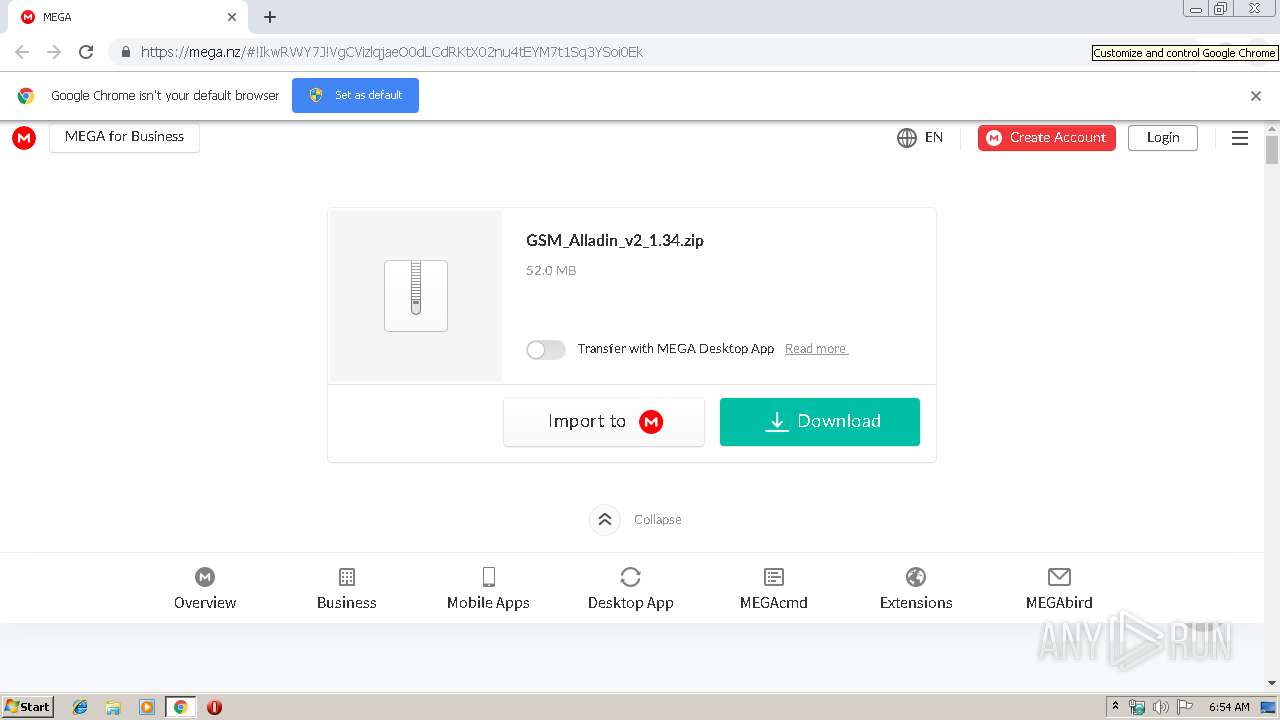
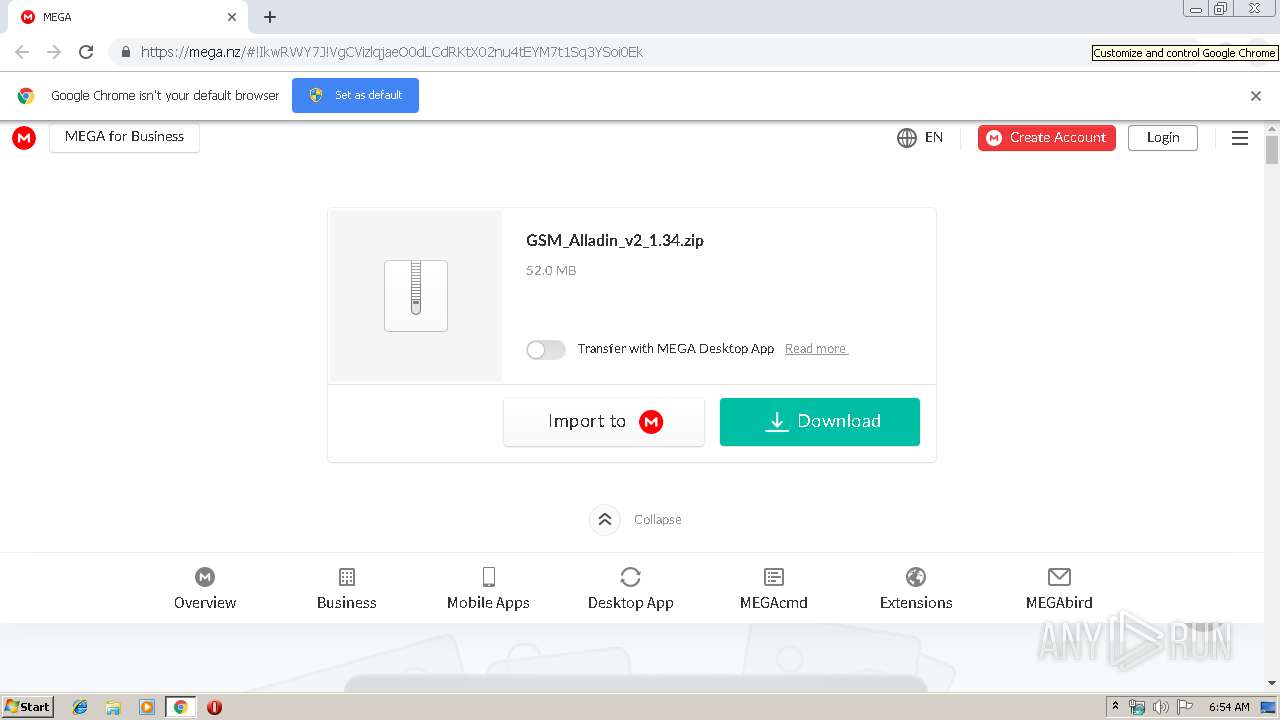
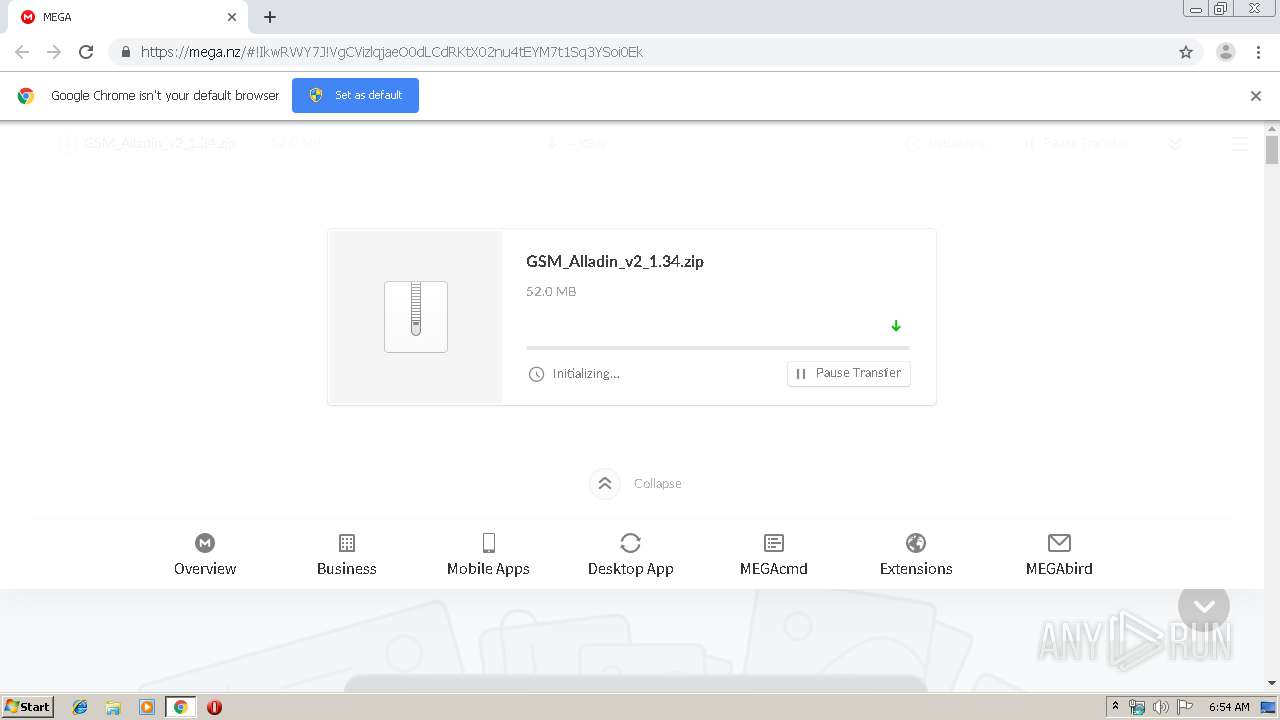
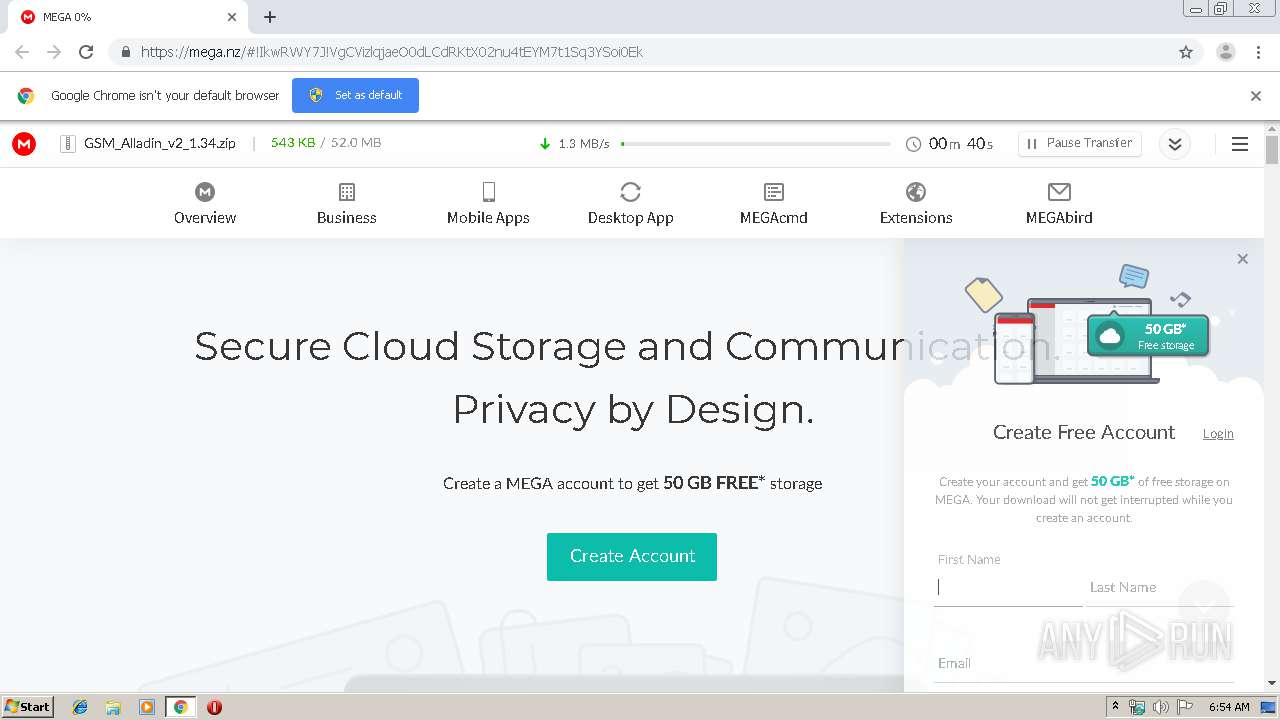
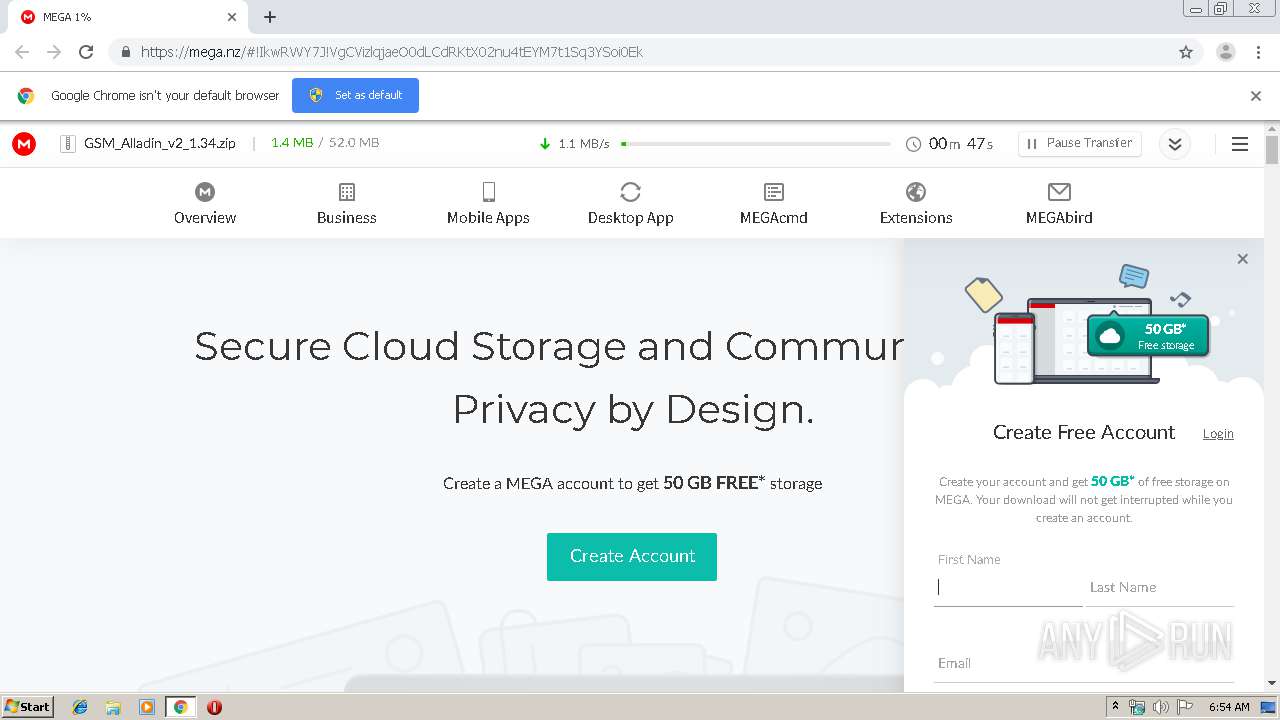
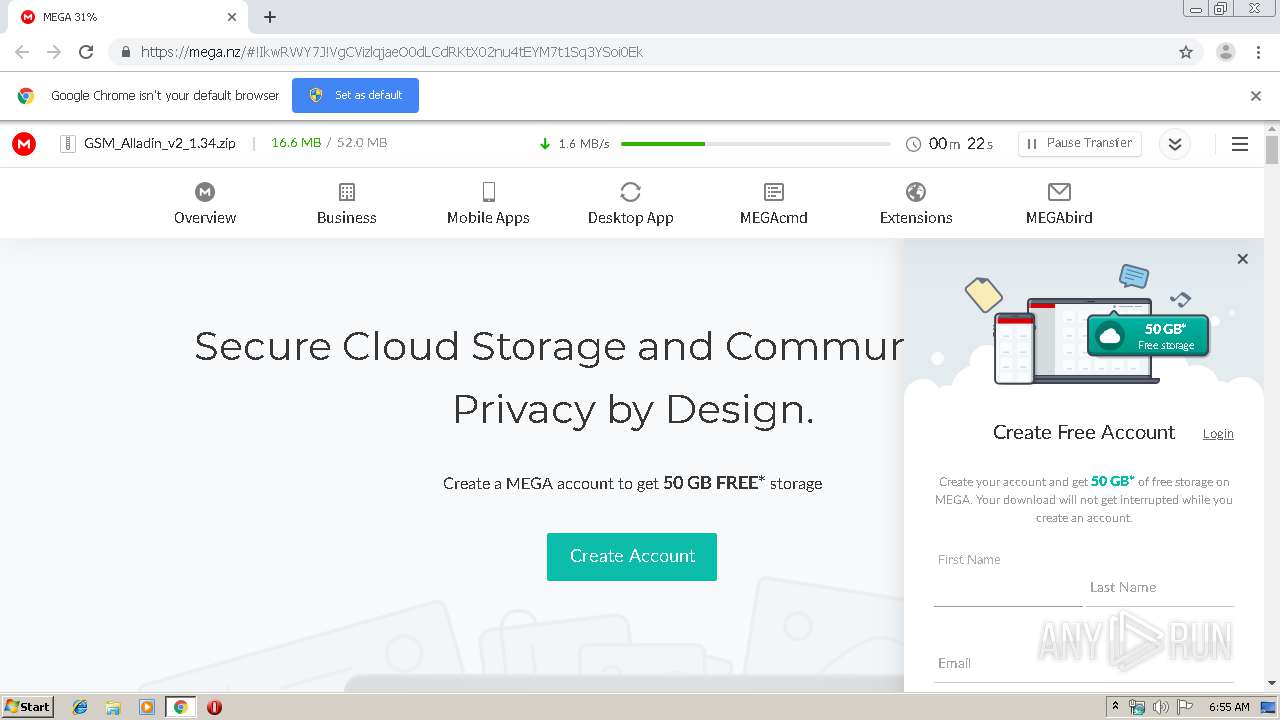
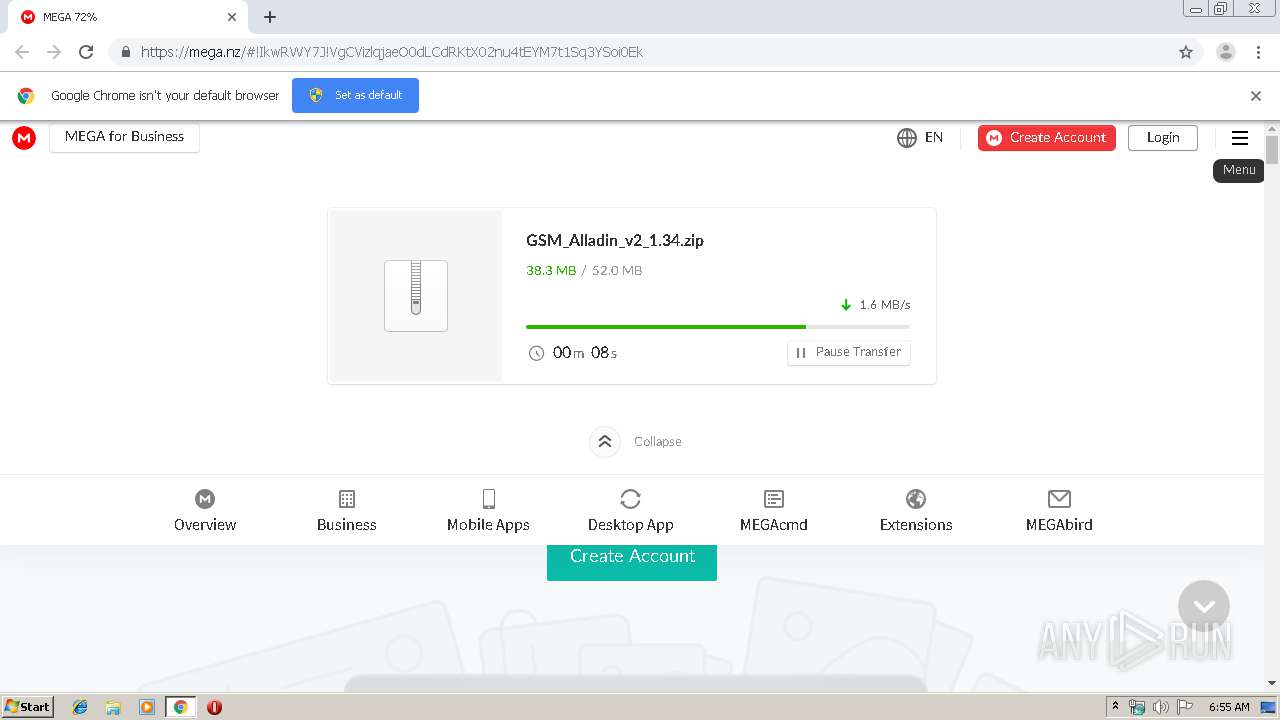
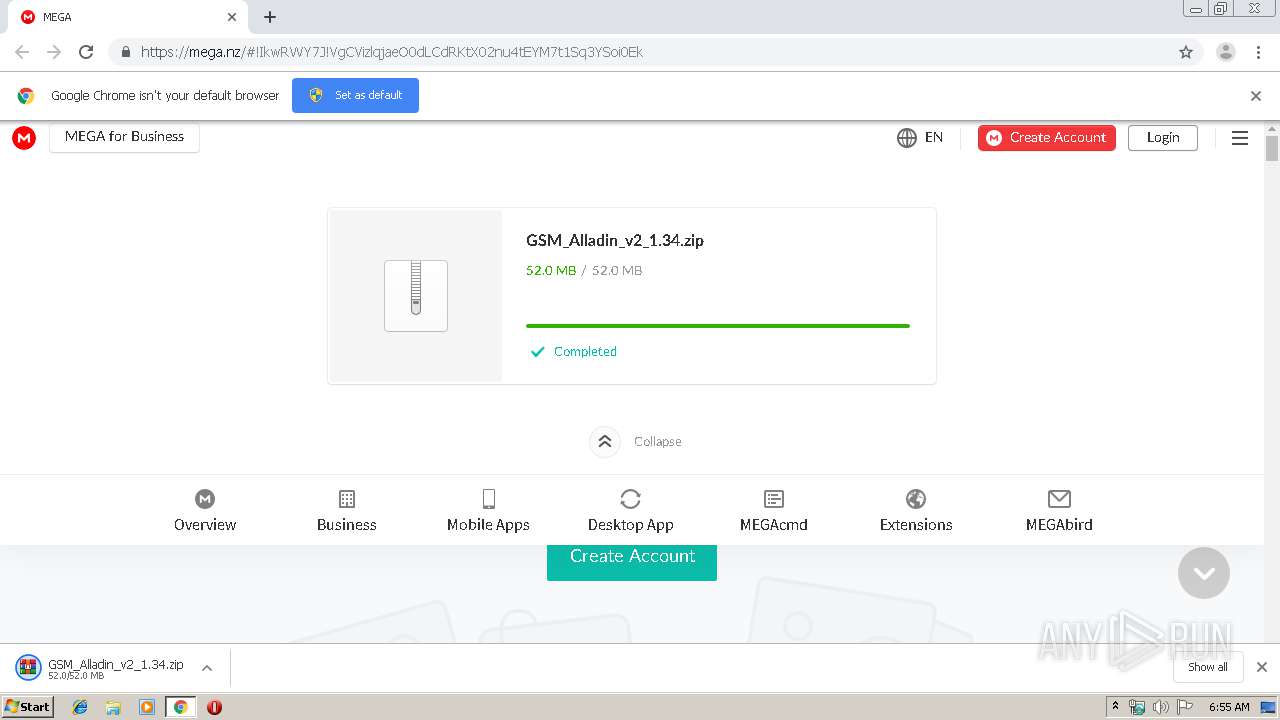
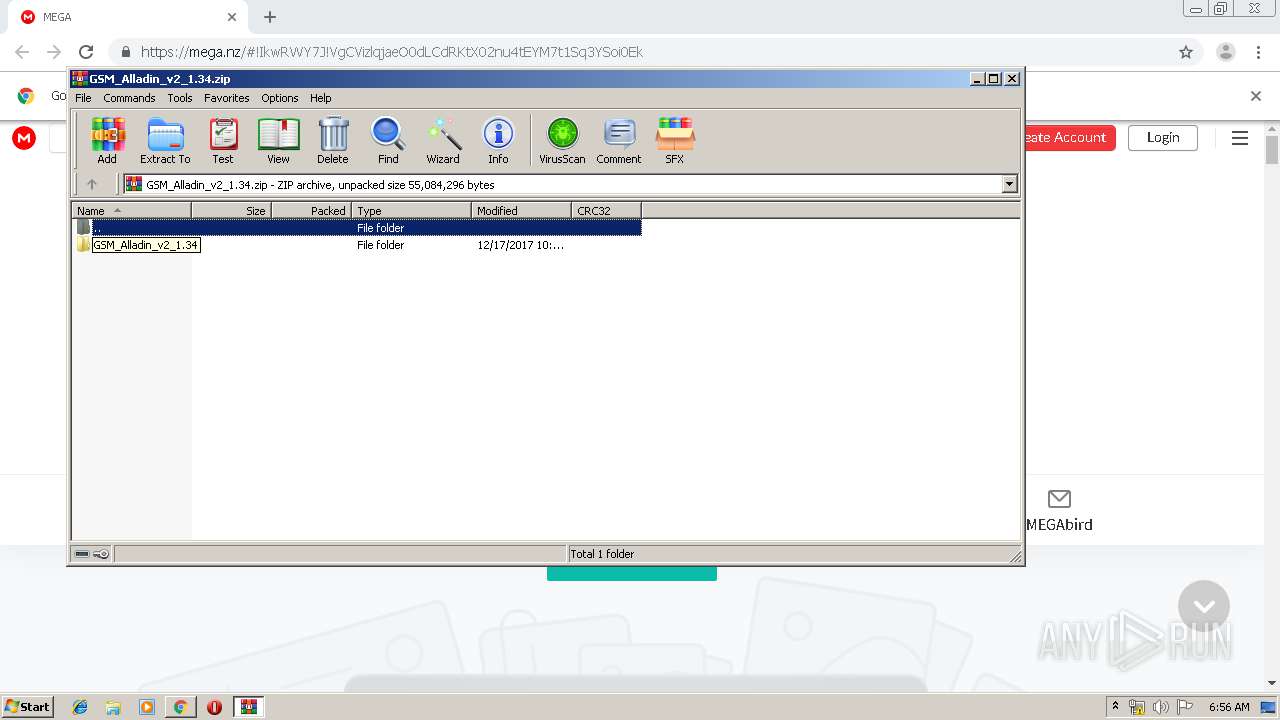
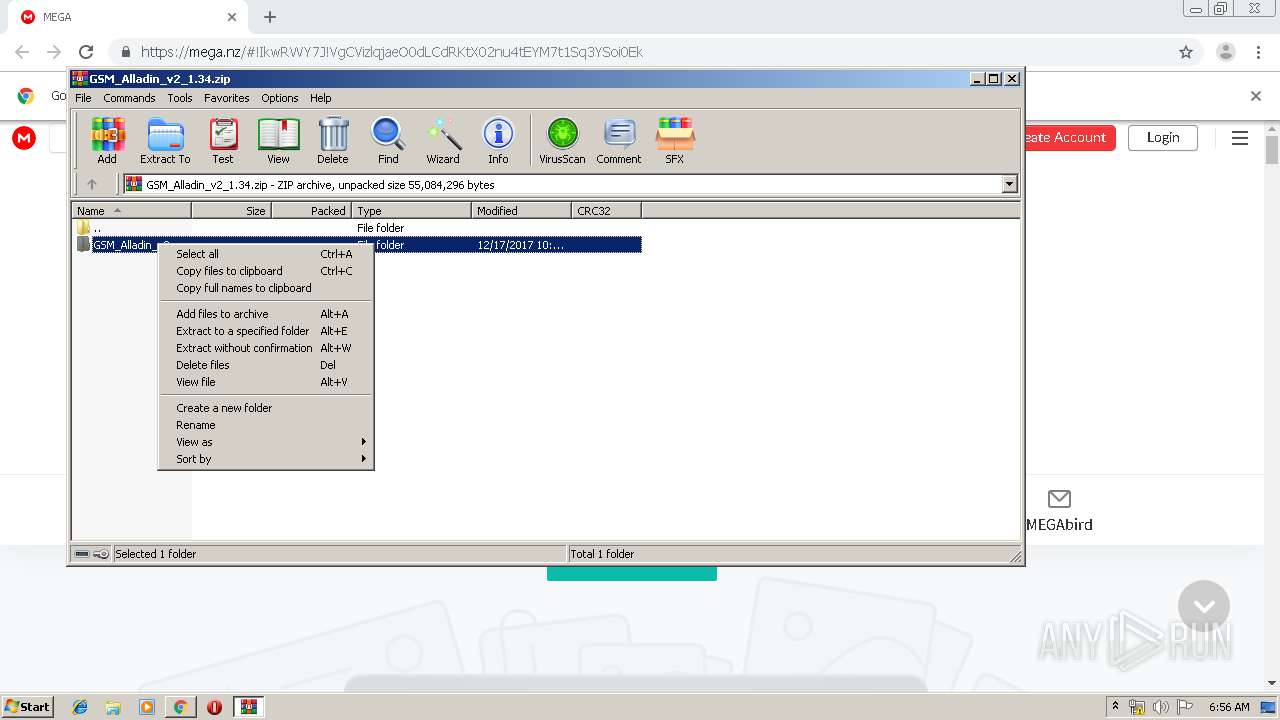
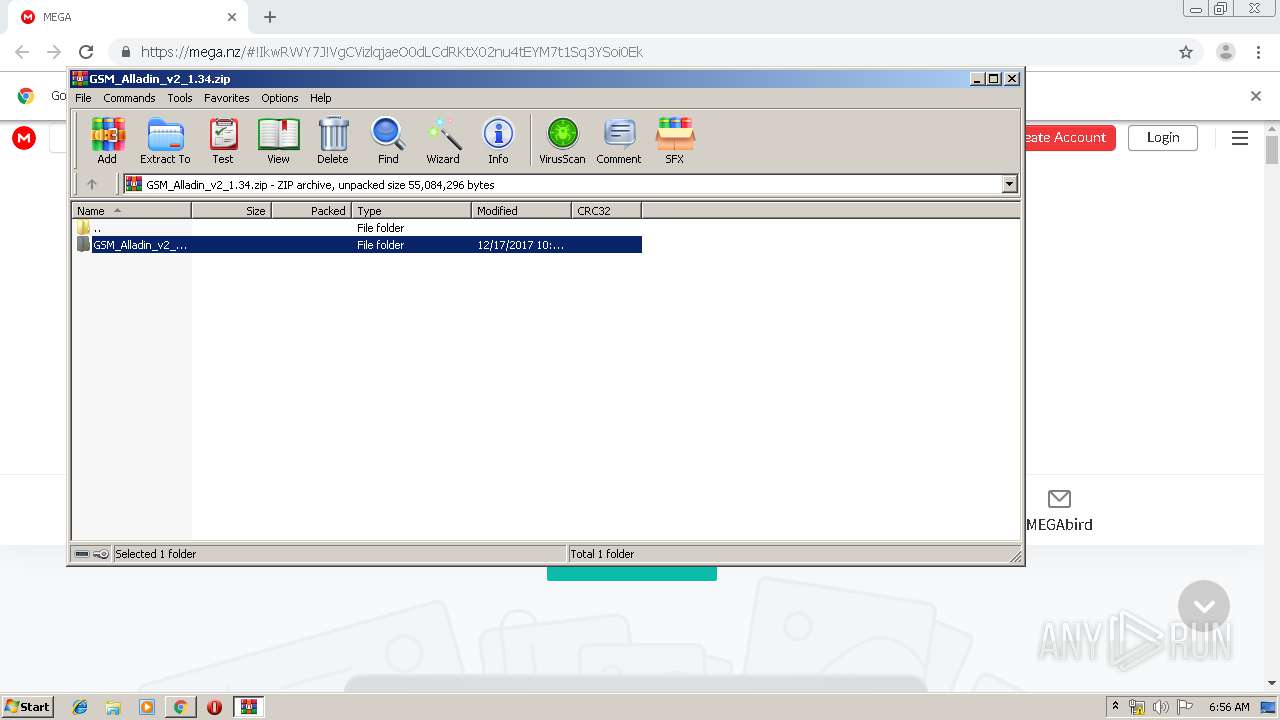
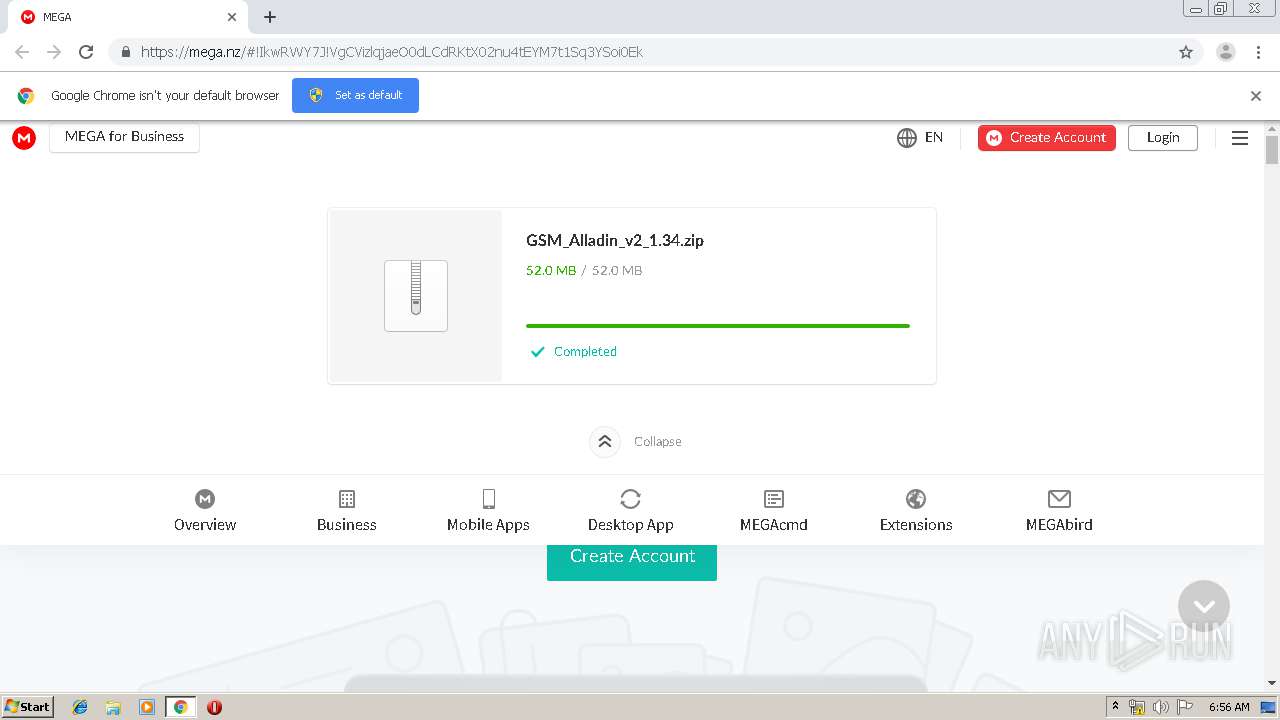
| URL: | https://mega.nz/#!IkwRWY7J!VgCVizlqjaeO0dLCdRKtX02nu4tEYM7t1Sq3YSoi0Ek |
| Full analysis: | https://app.any.run/tasks/172a9f73-4050-4447-b775-e5c533618789 |
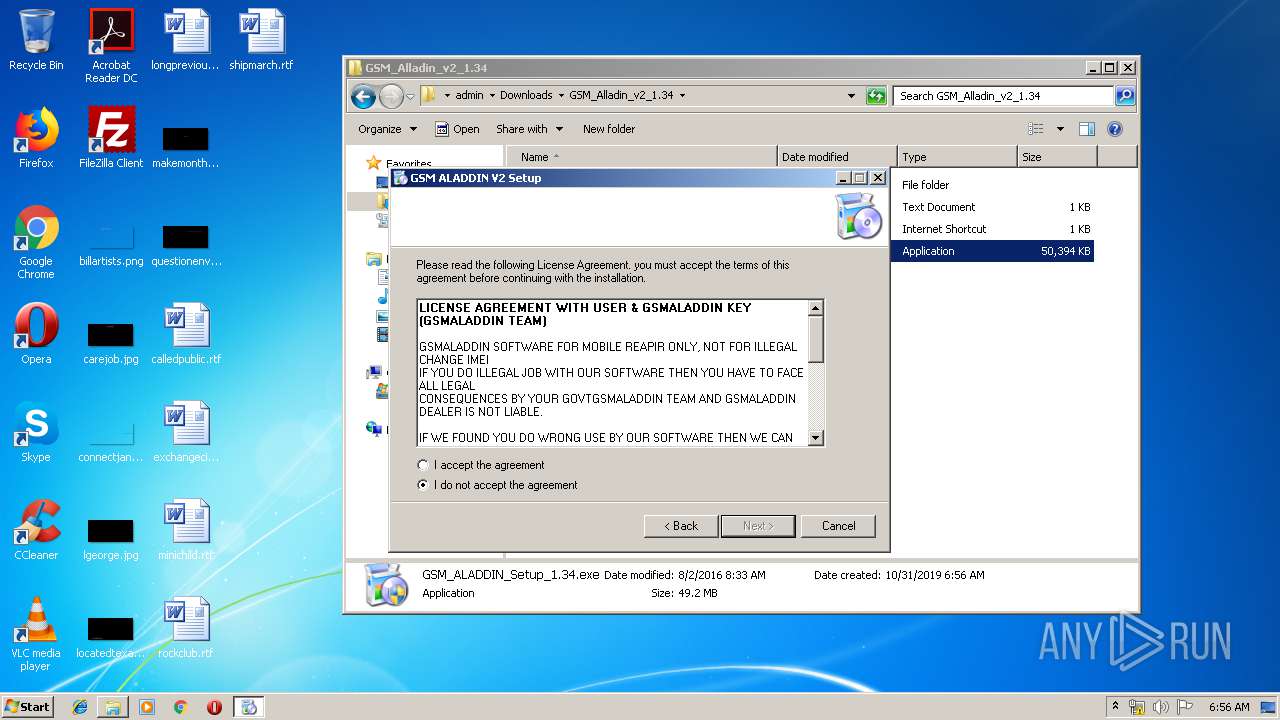
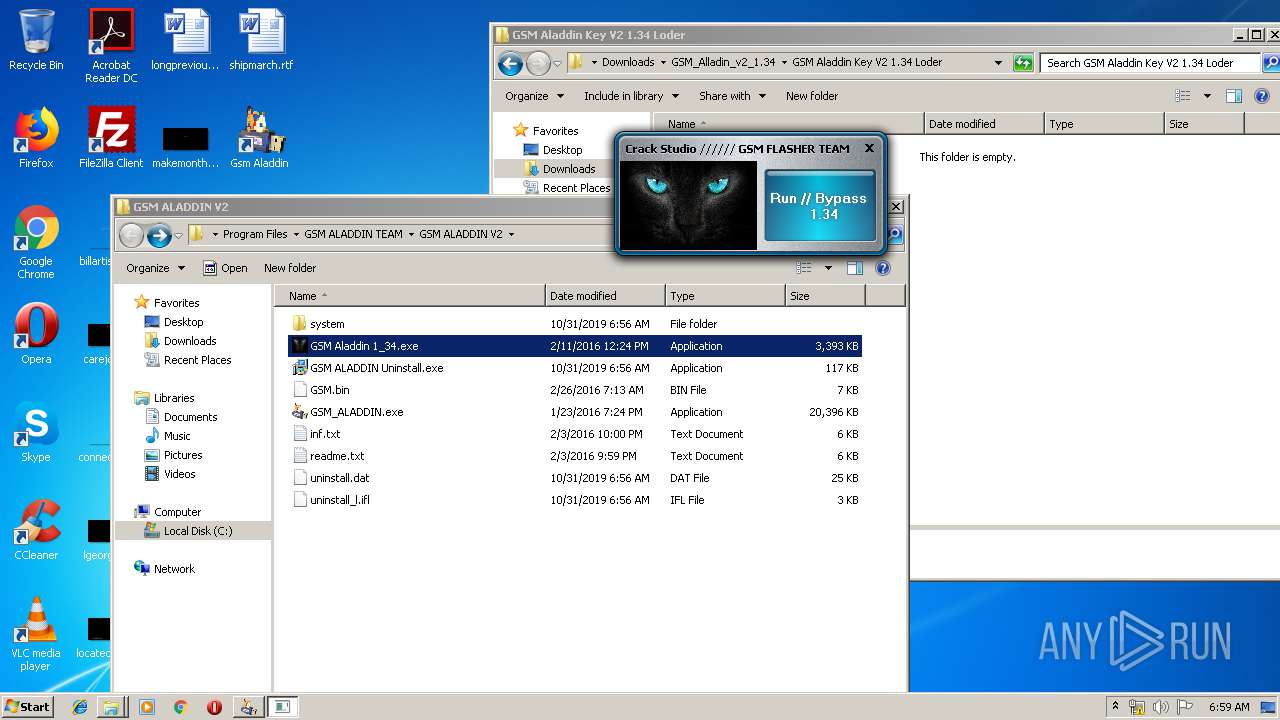
| Verdict: | Malicious activity |
| Analysis date: | October 31, 2019, 06:54:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
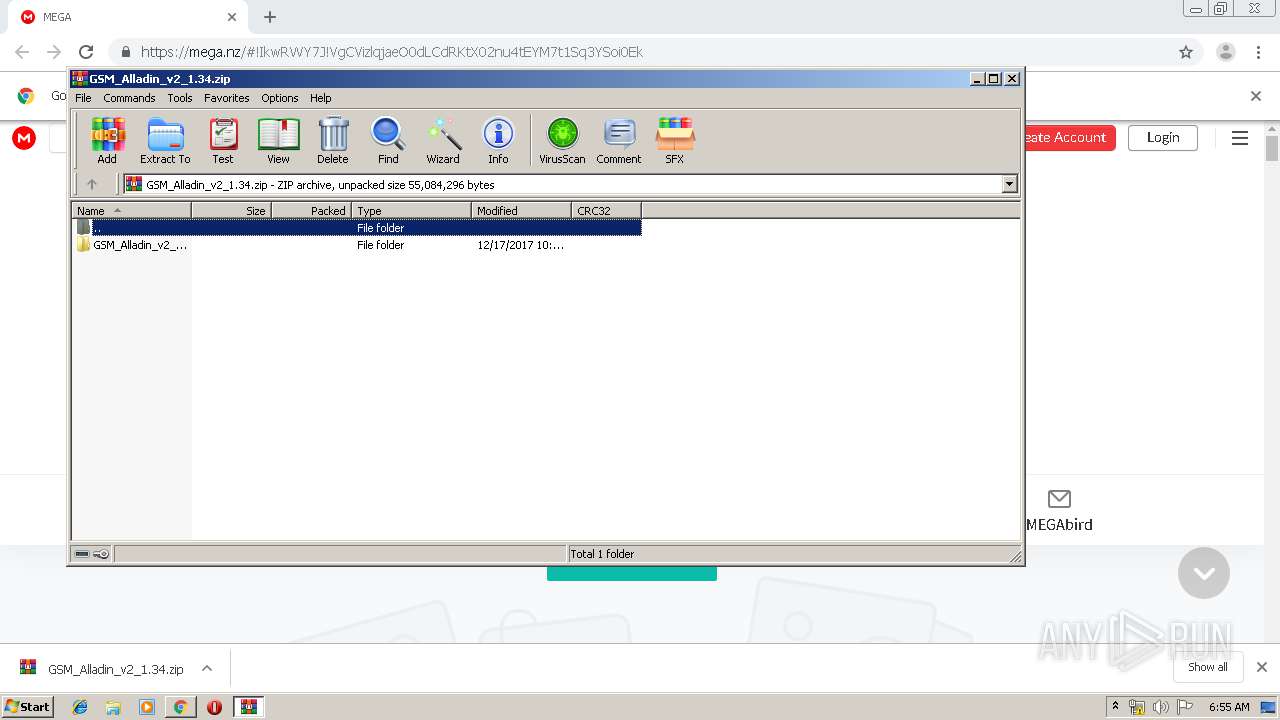
| MD5: | 054FC7625D727AA9BEC719E9C5FAE15B |
| SHA1: | F9A46A50F2D2F9BE4D51DCC70F41E25EC80F4C69 |
| SHA256: | 4DB75ABEBDF36E563ADEE16C5033B839B3C57952151F4D2A99C173427FA49D19 |
| SSDEEP: | 3:N8X/iGEvEKtDPVf2S9kQ8oiX8bO:290EKtxP+GnbO |
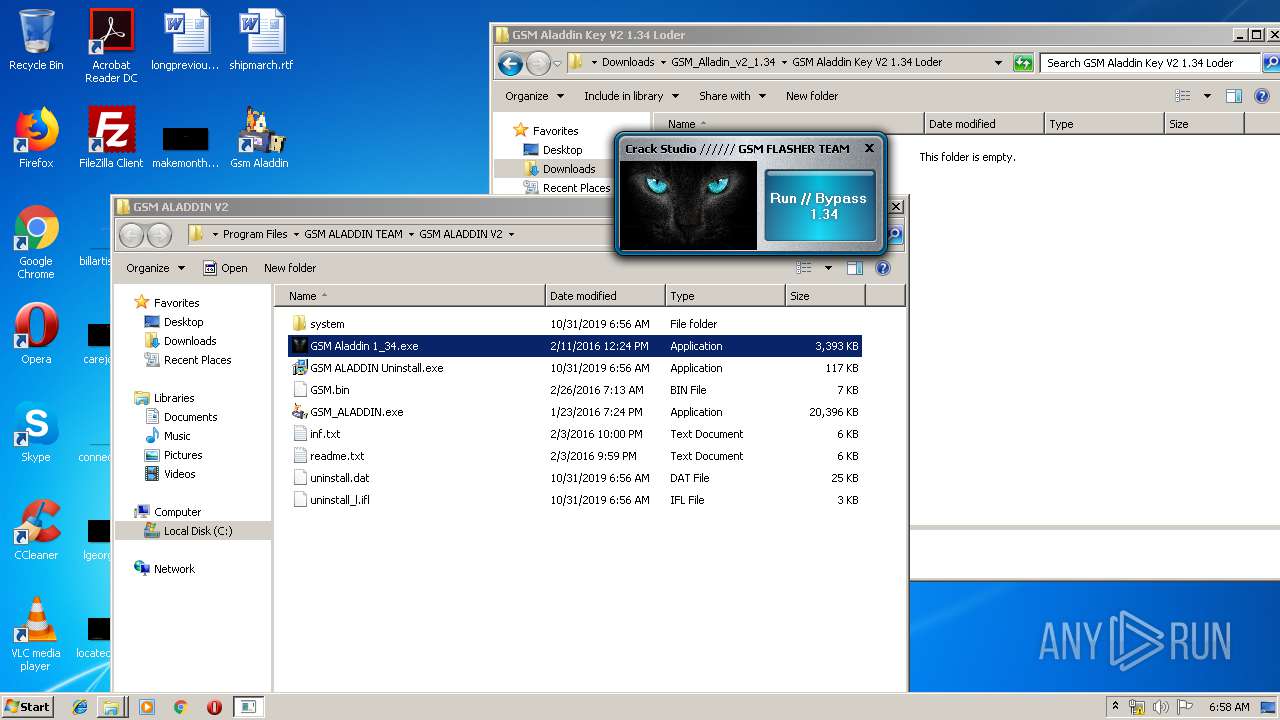
MALICIOUS
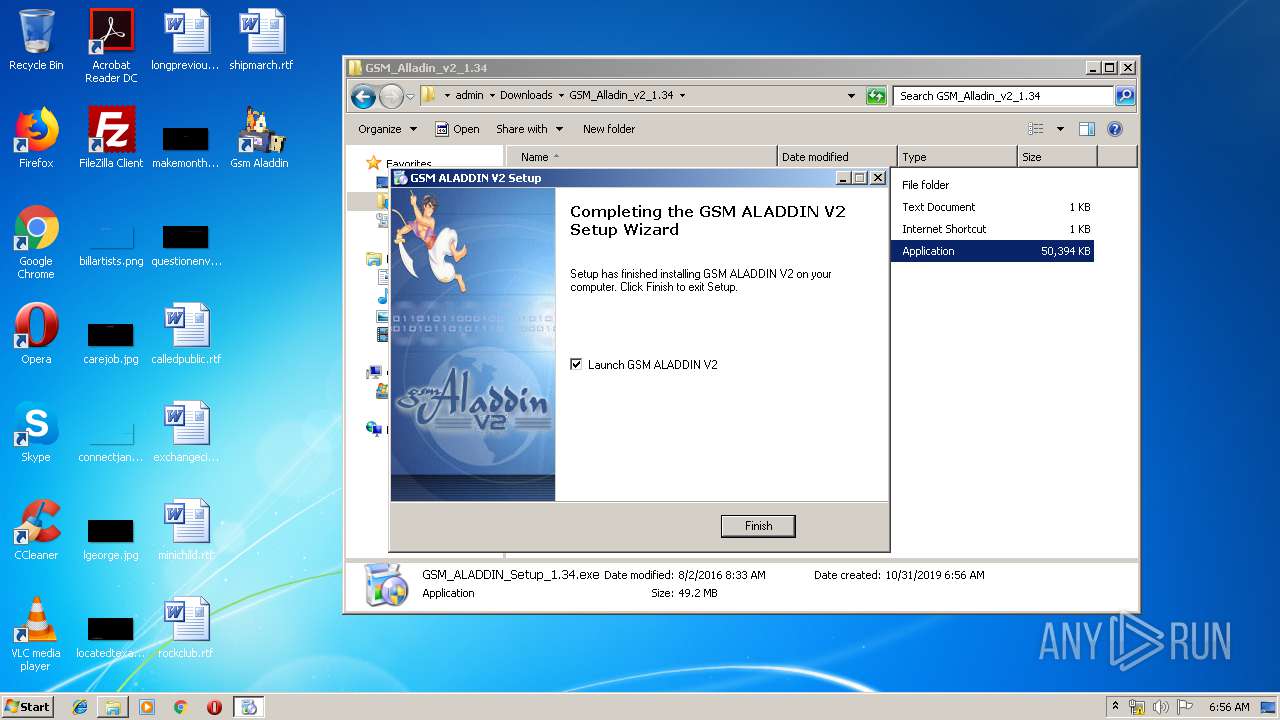
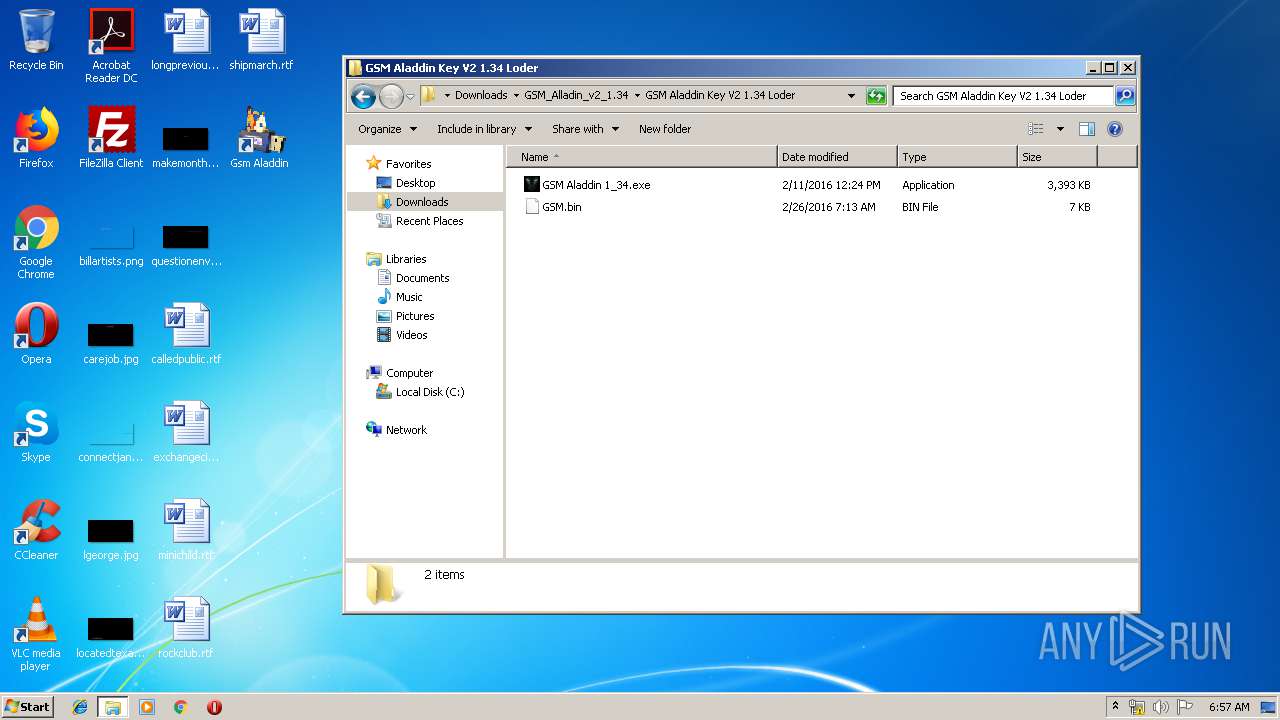
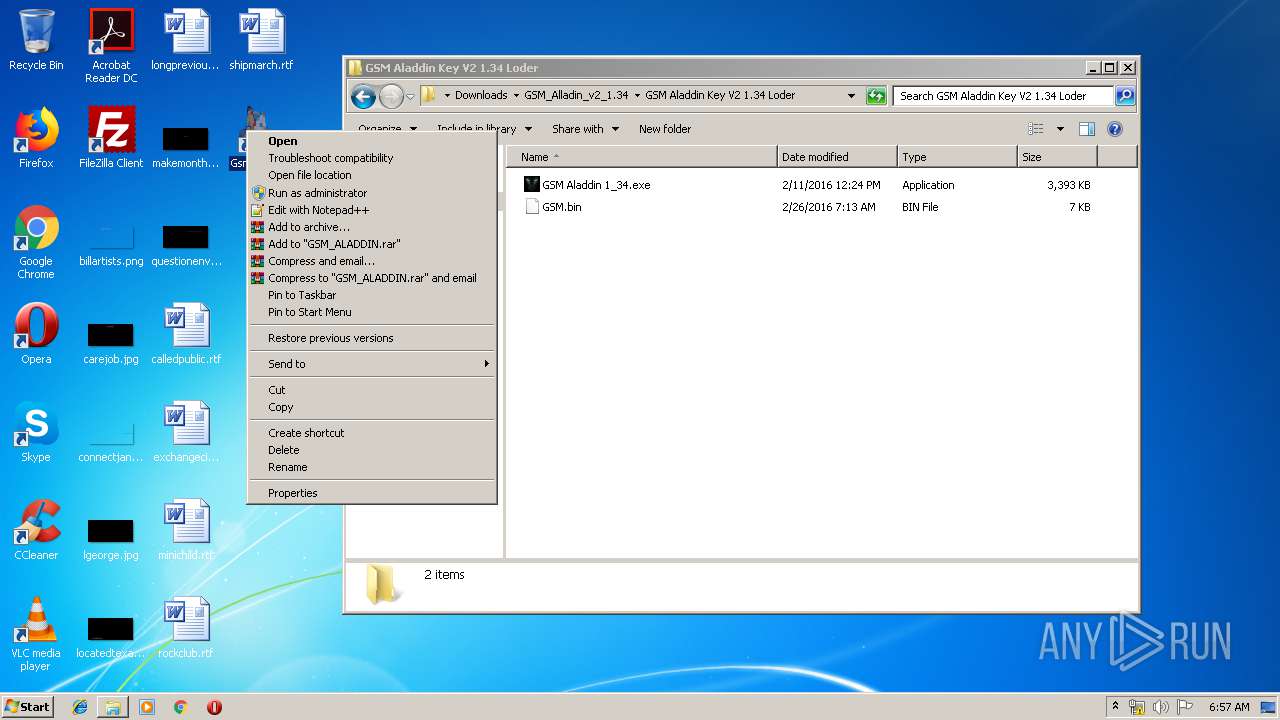
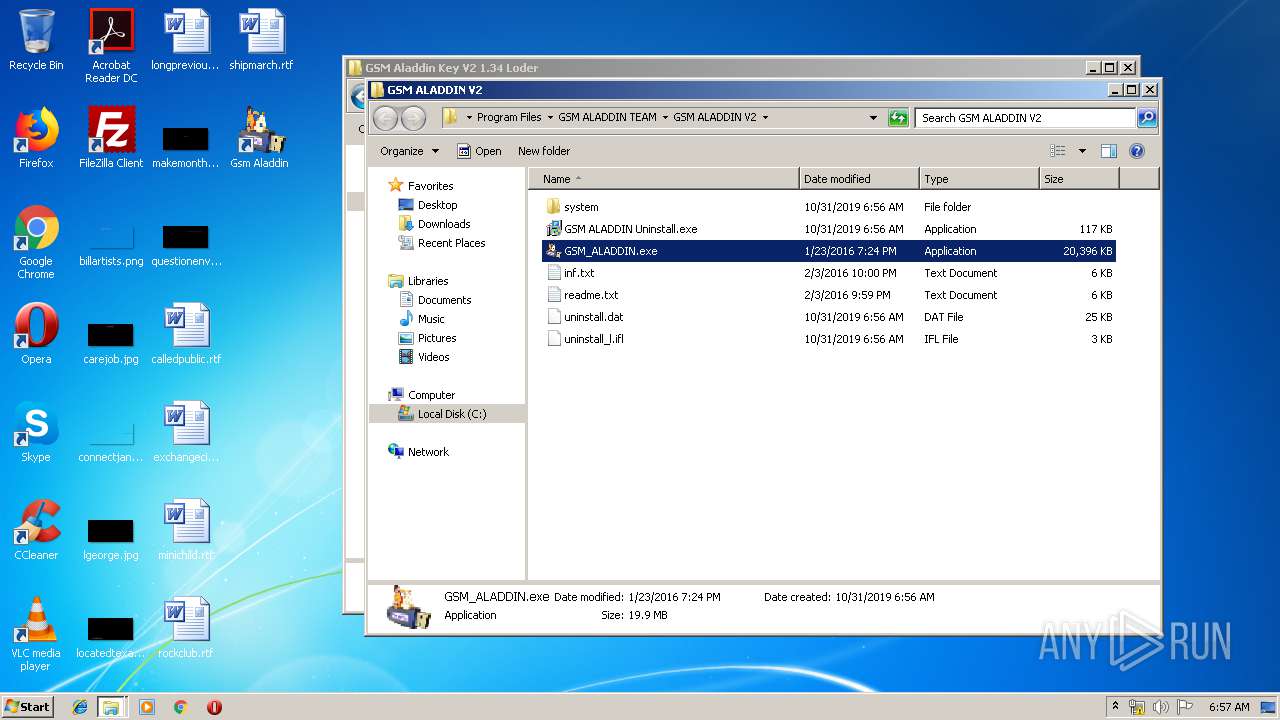
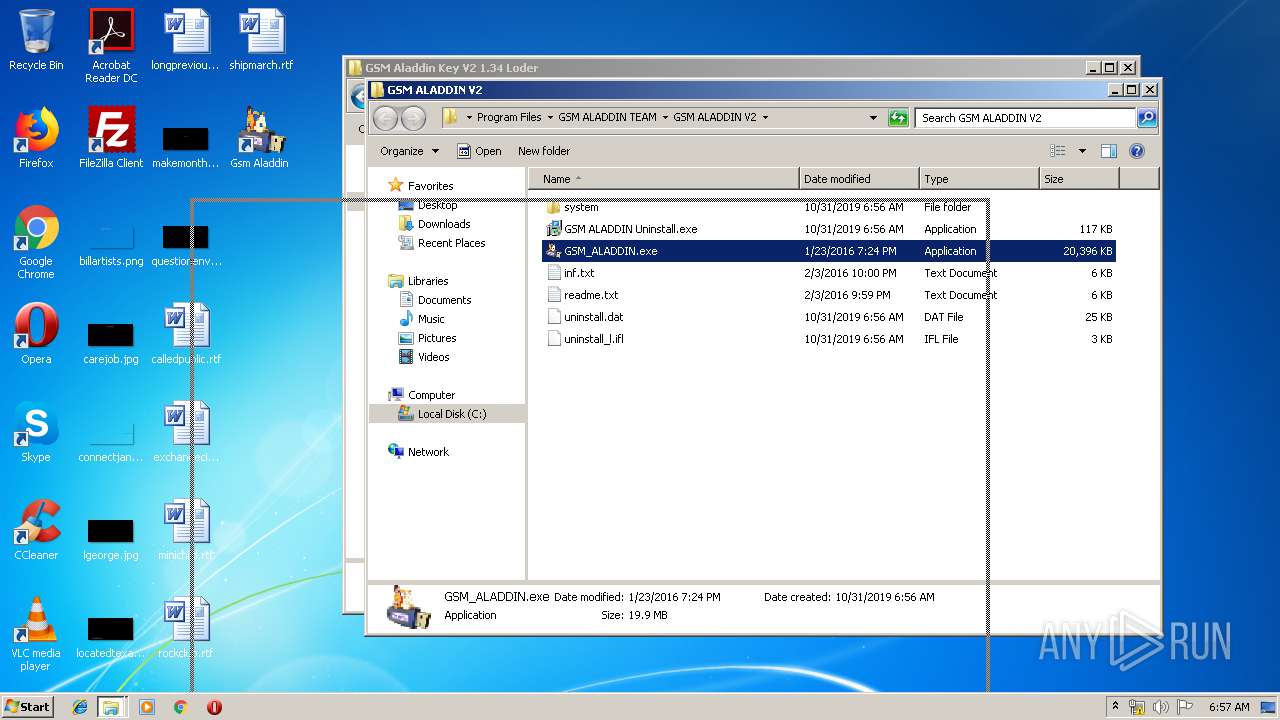
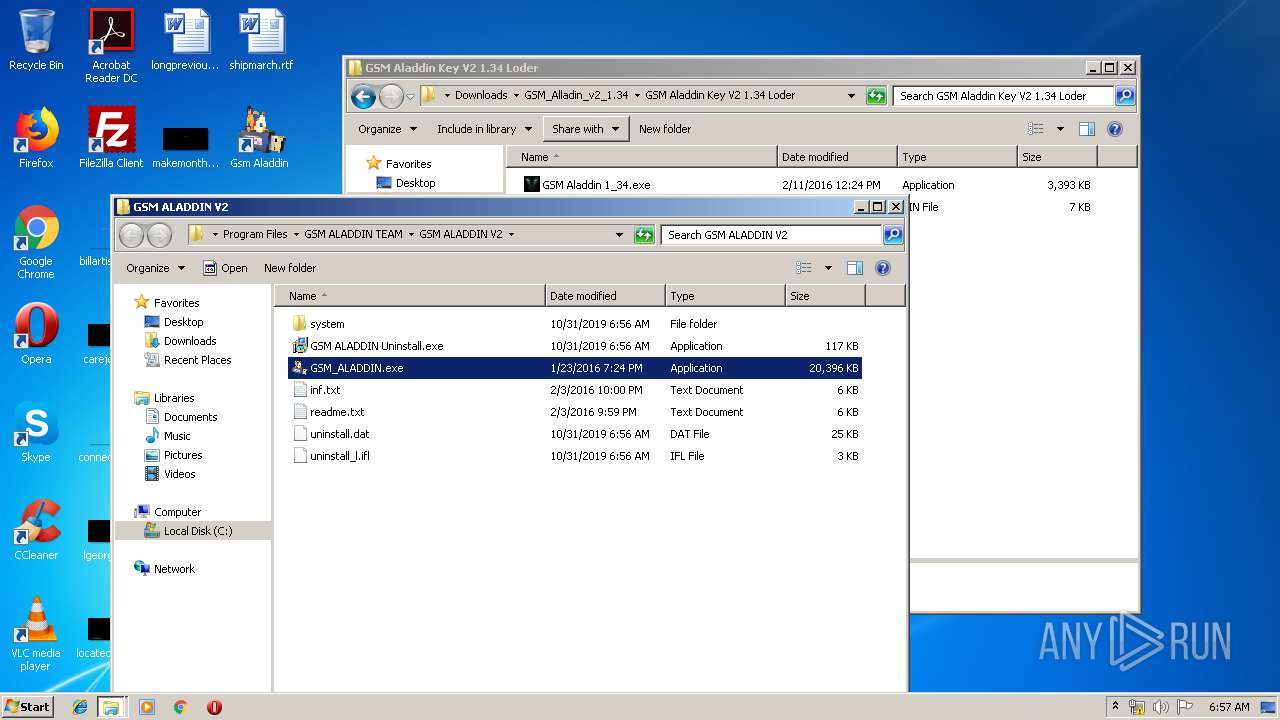
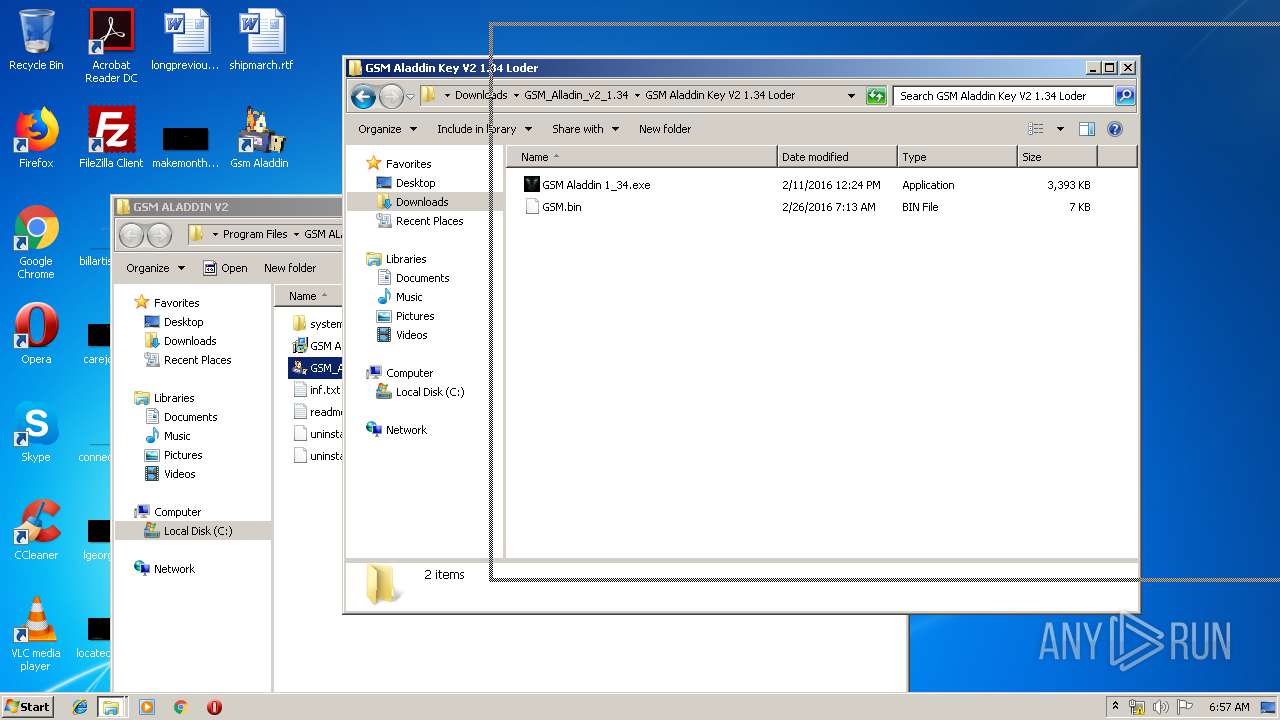
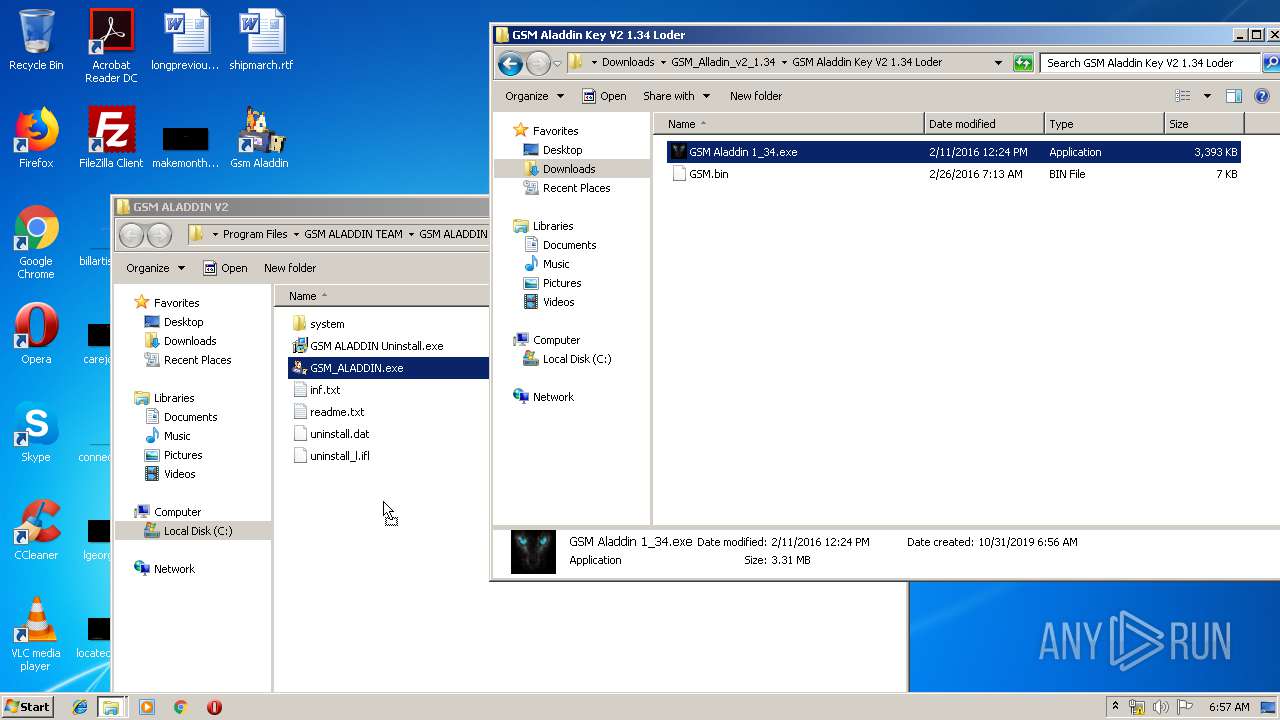
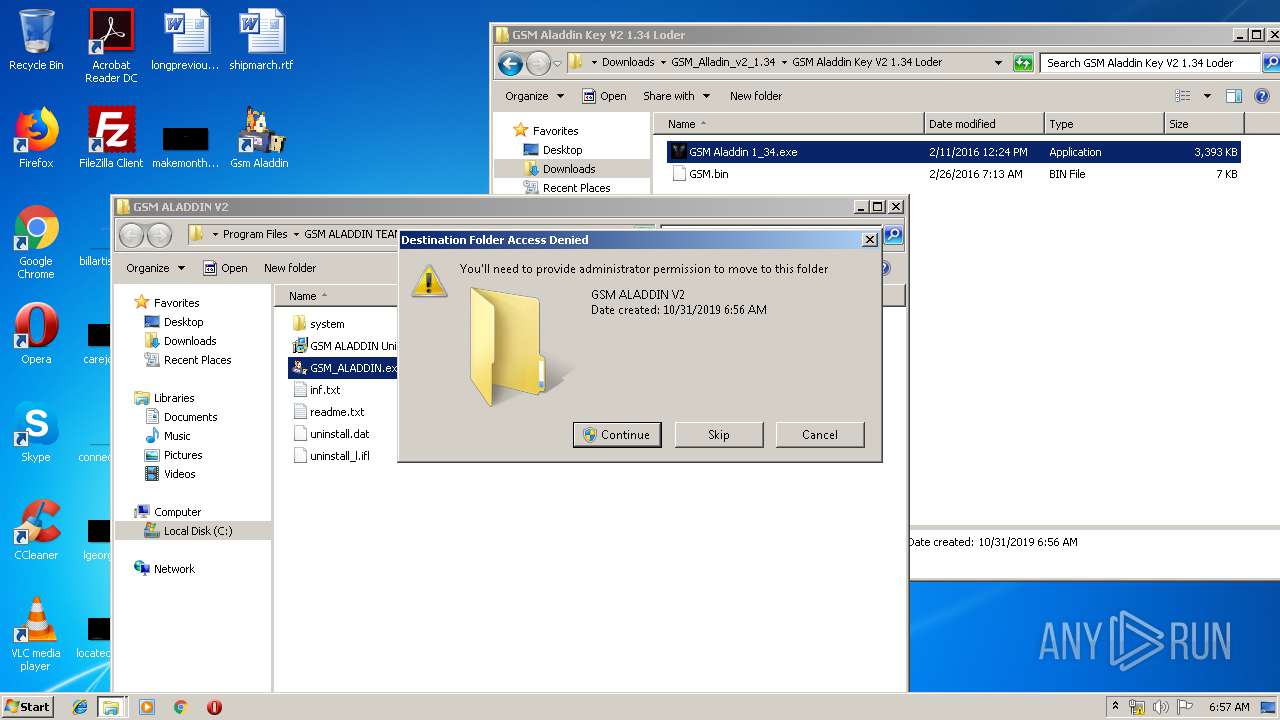
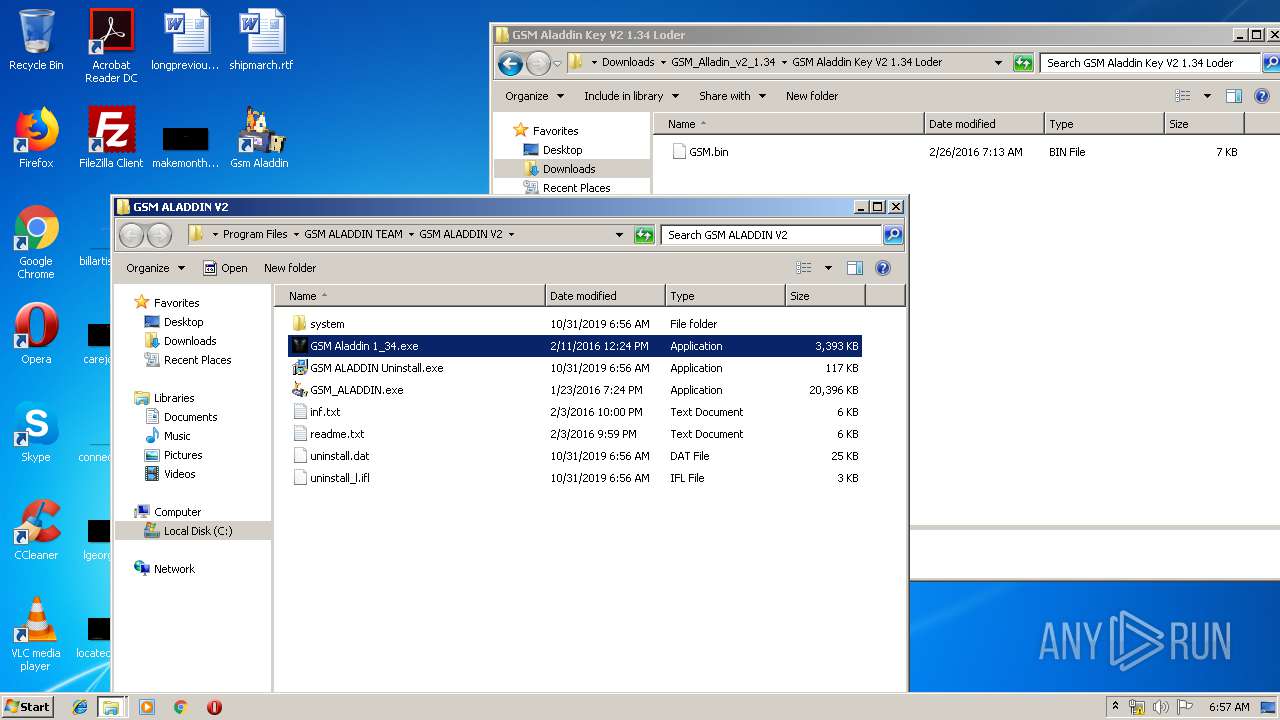
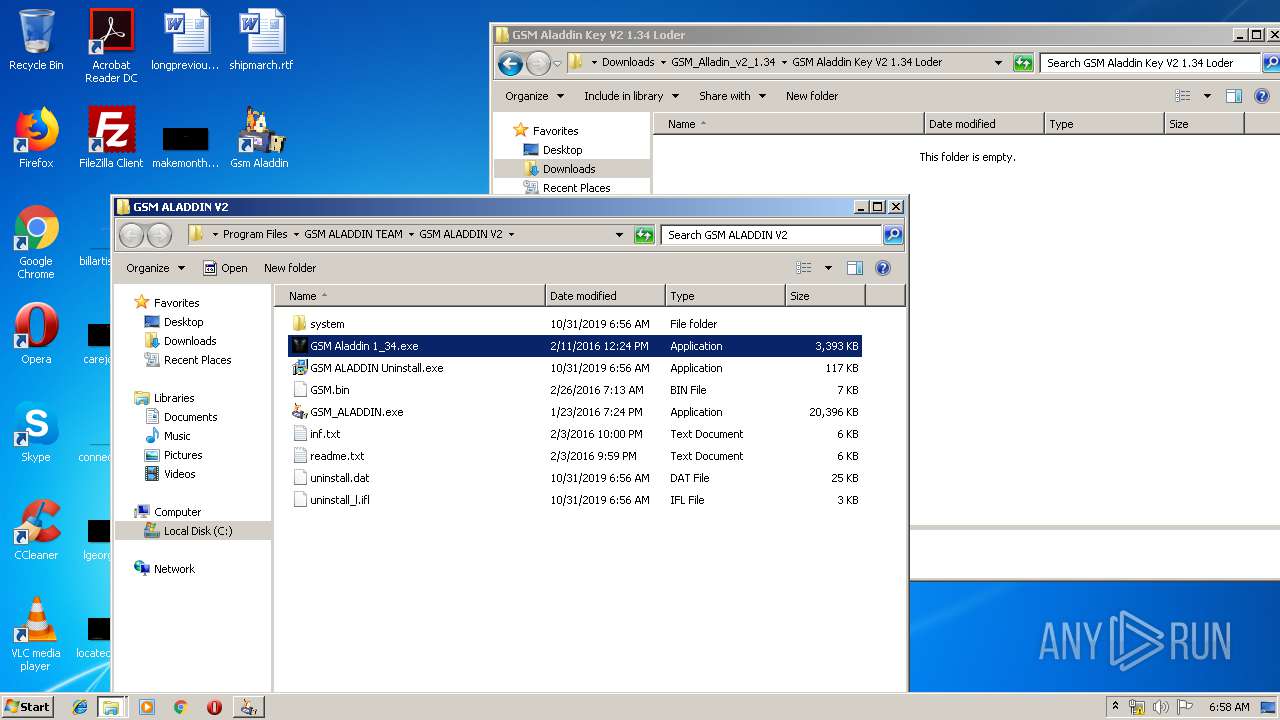
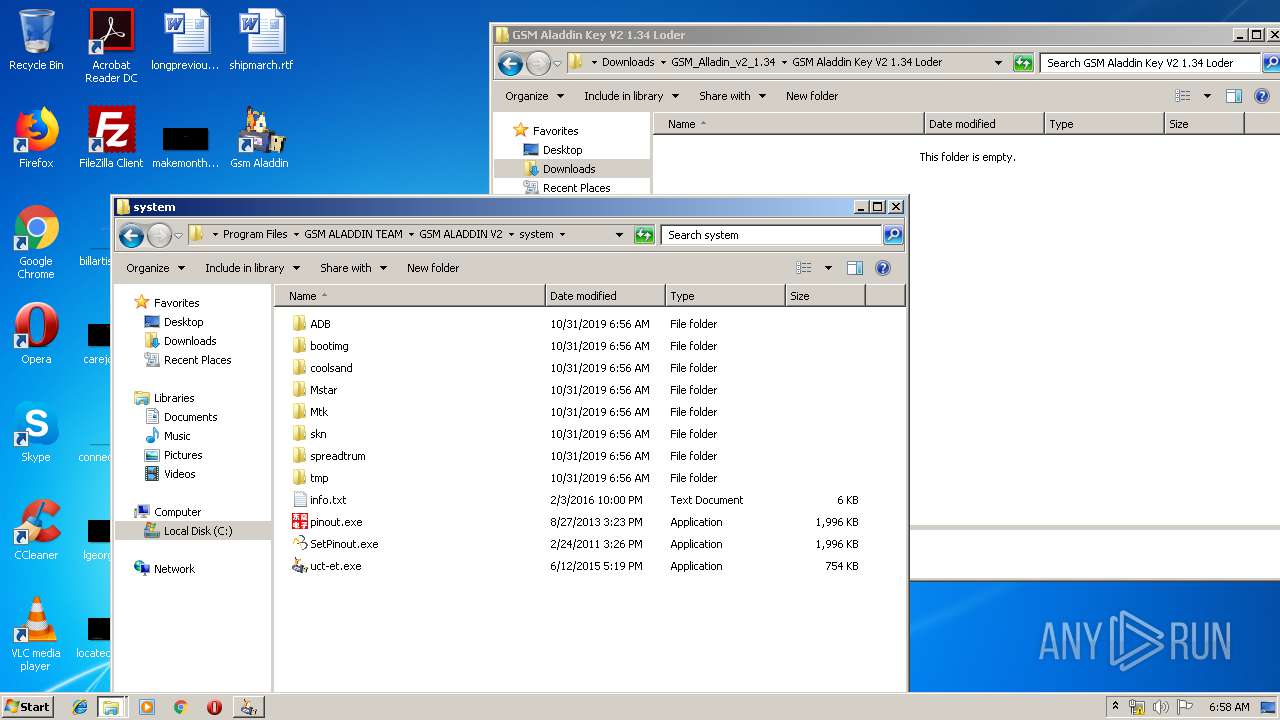
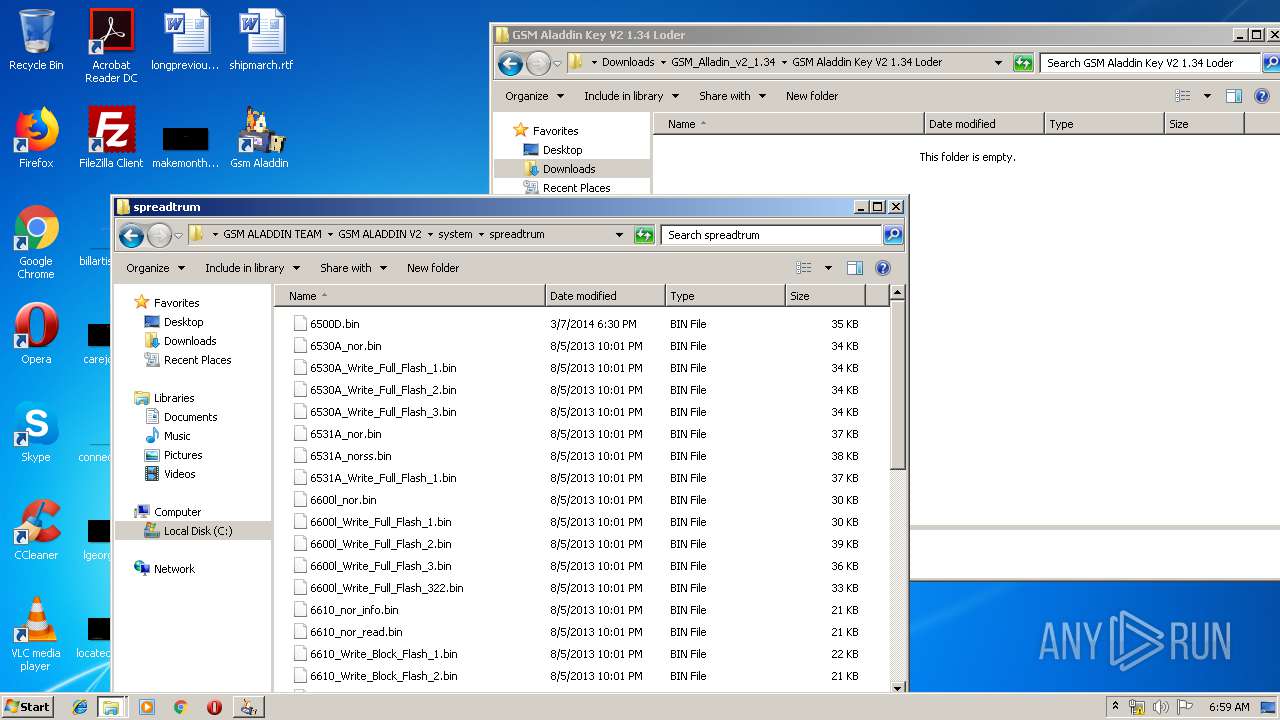
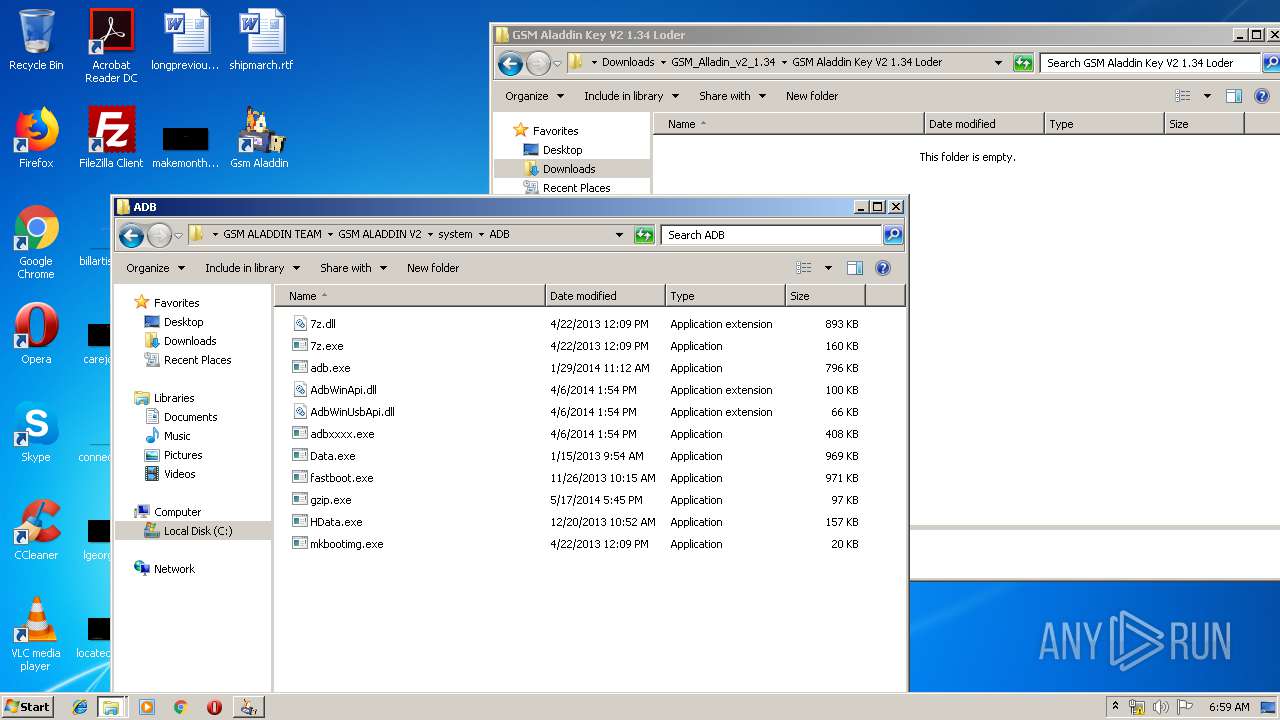
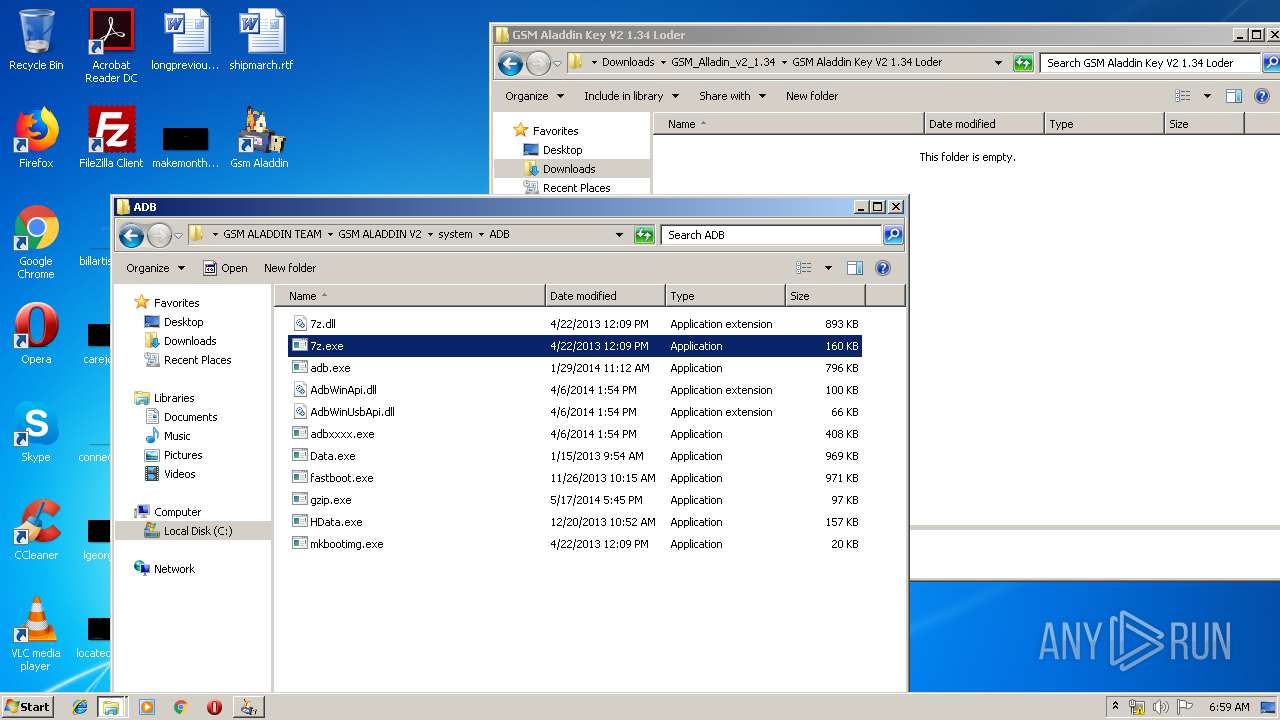
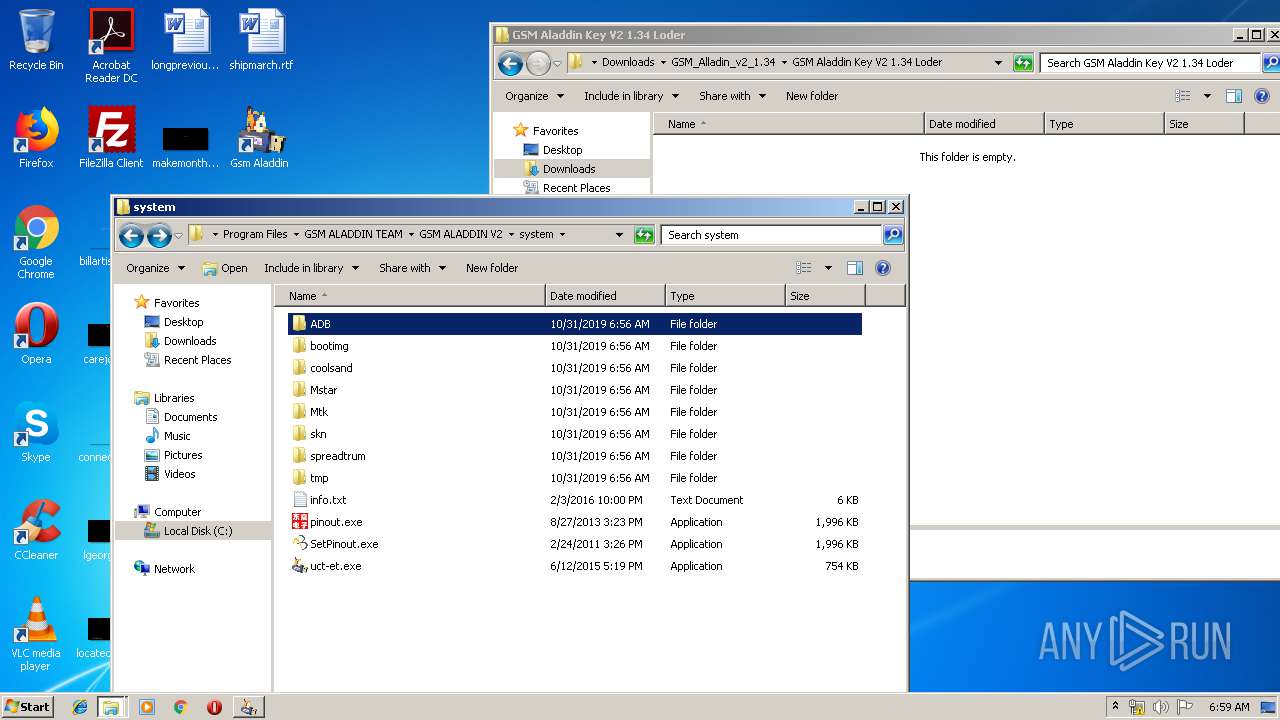
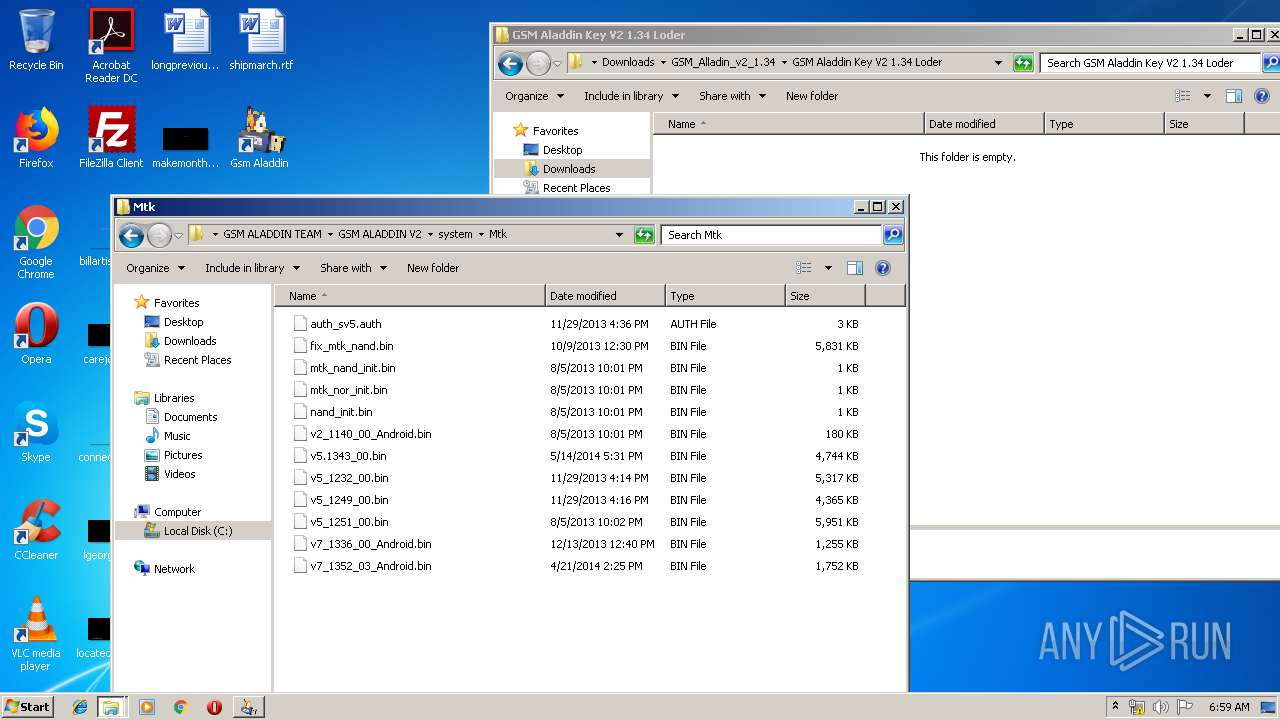
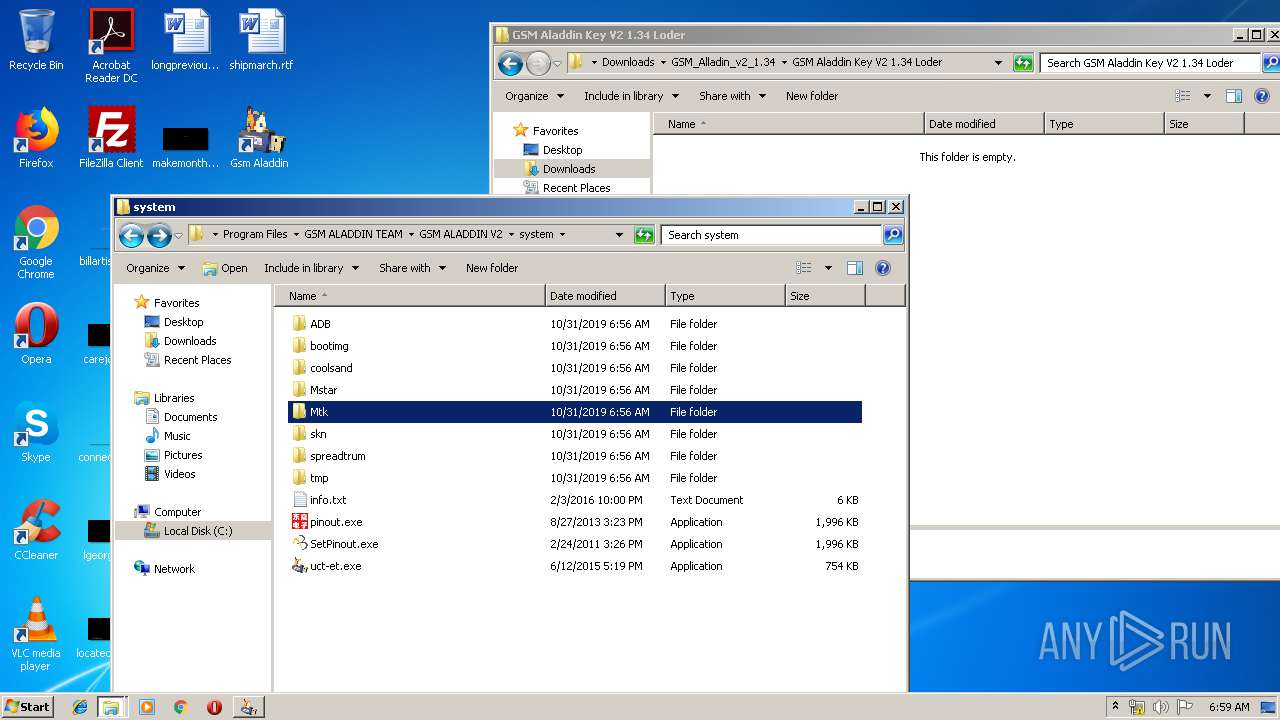
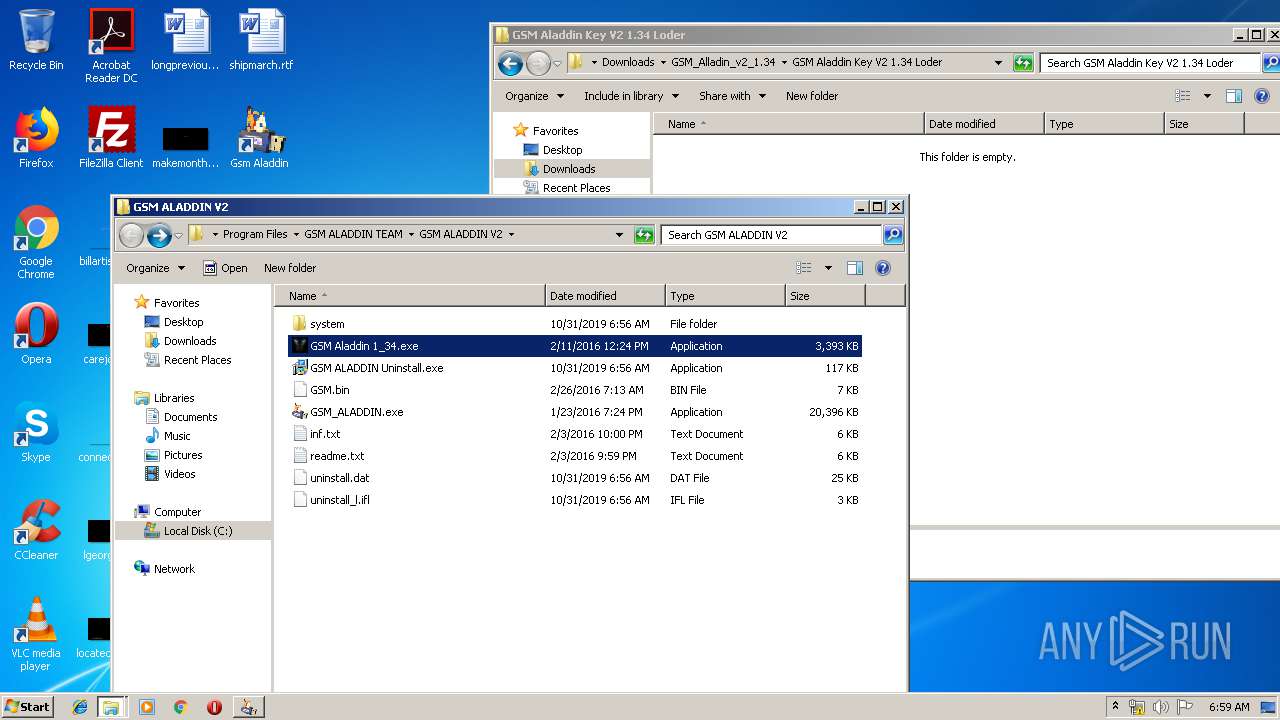
Application was dropped or rewritten from another process
- GSM_ALADDIN.exe (PID: 2684)
- GSM Aladdin 1_34.exe (PID: 912)
- GSM_ALADDIN.exe (PID: 1648)
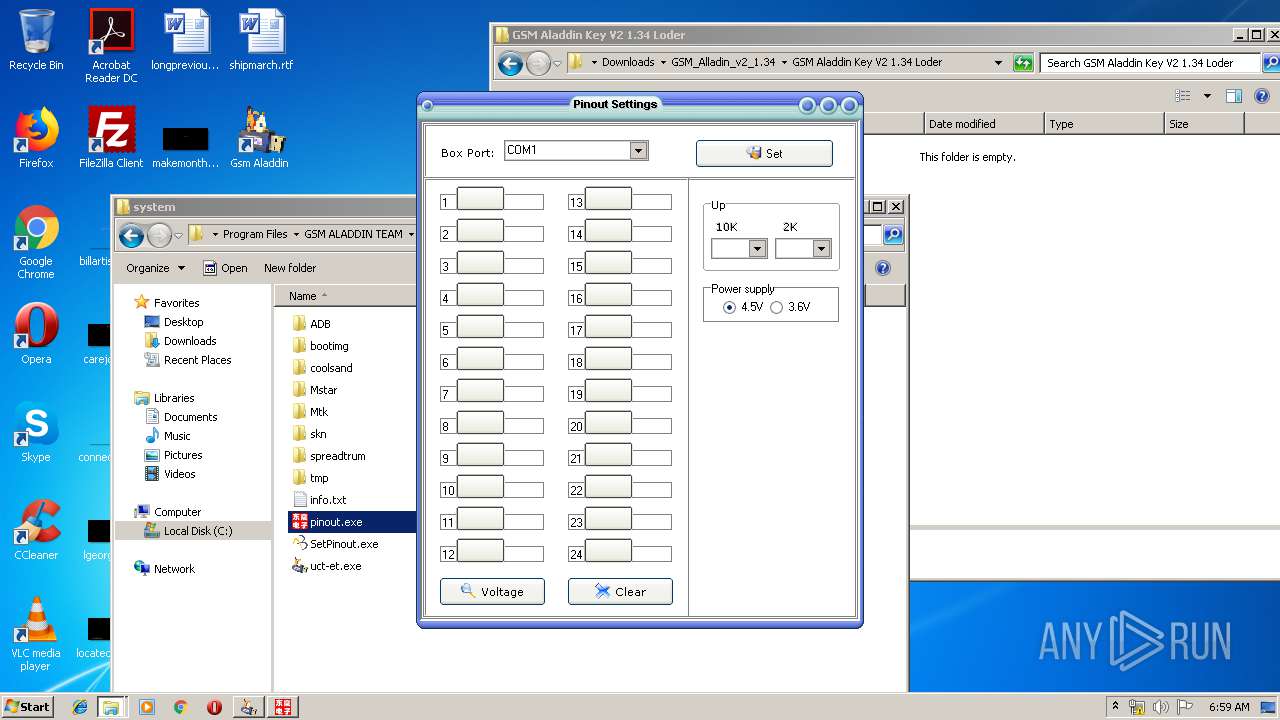
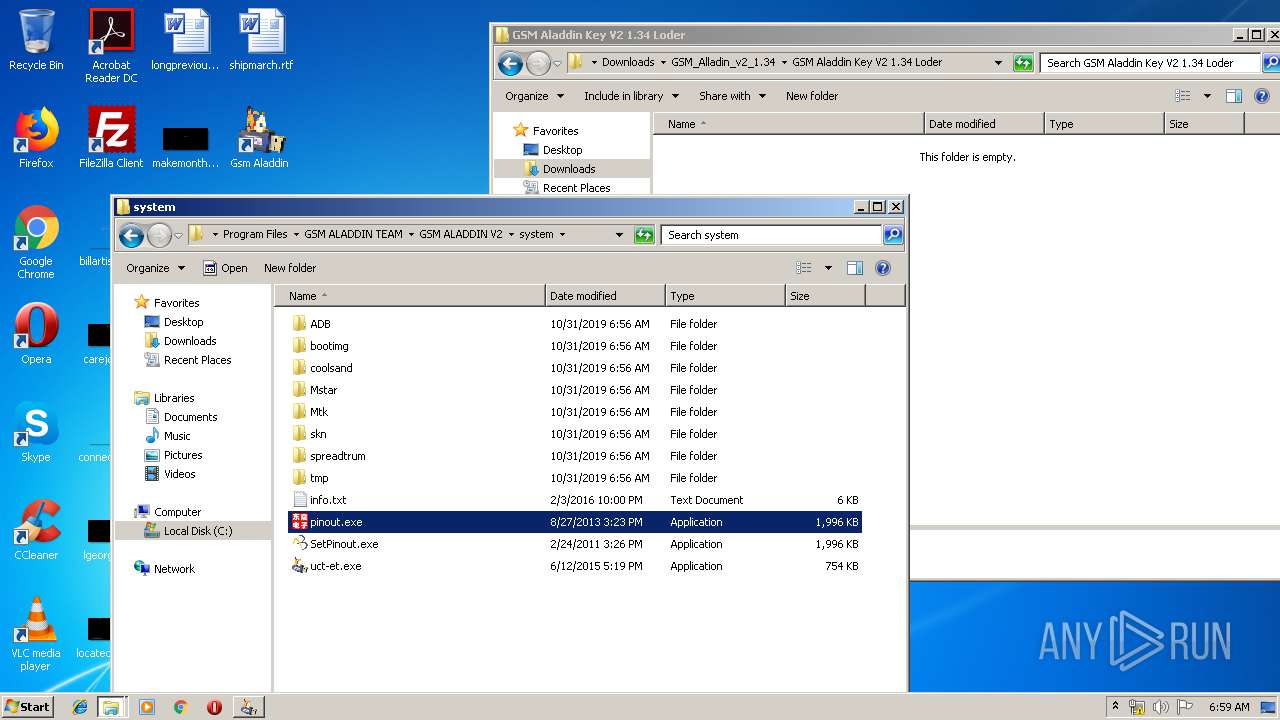
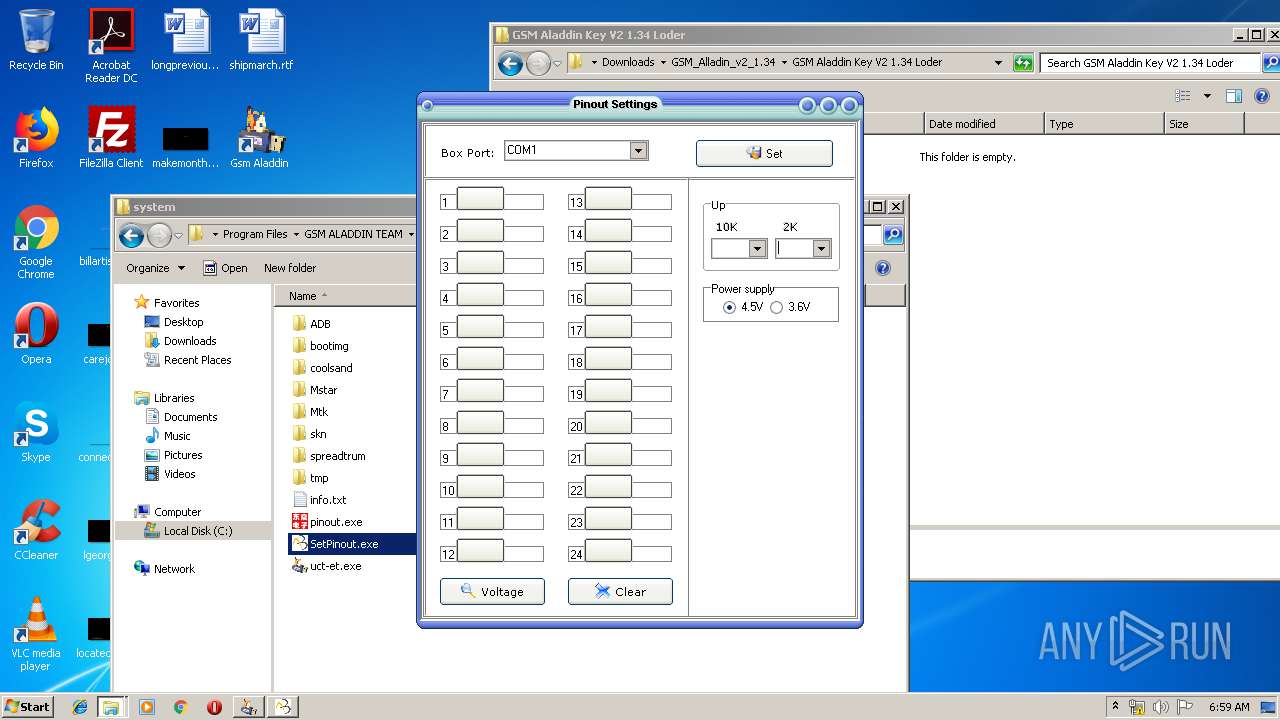
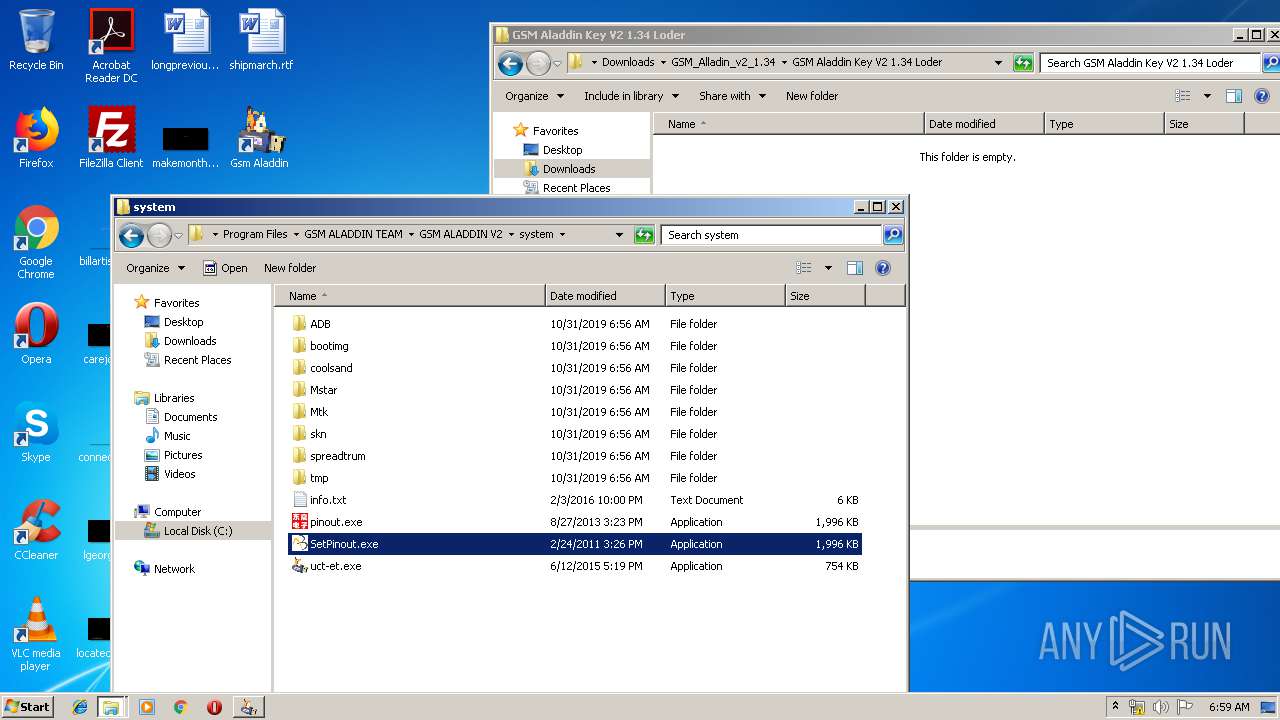
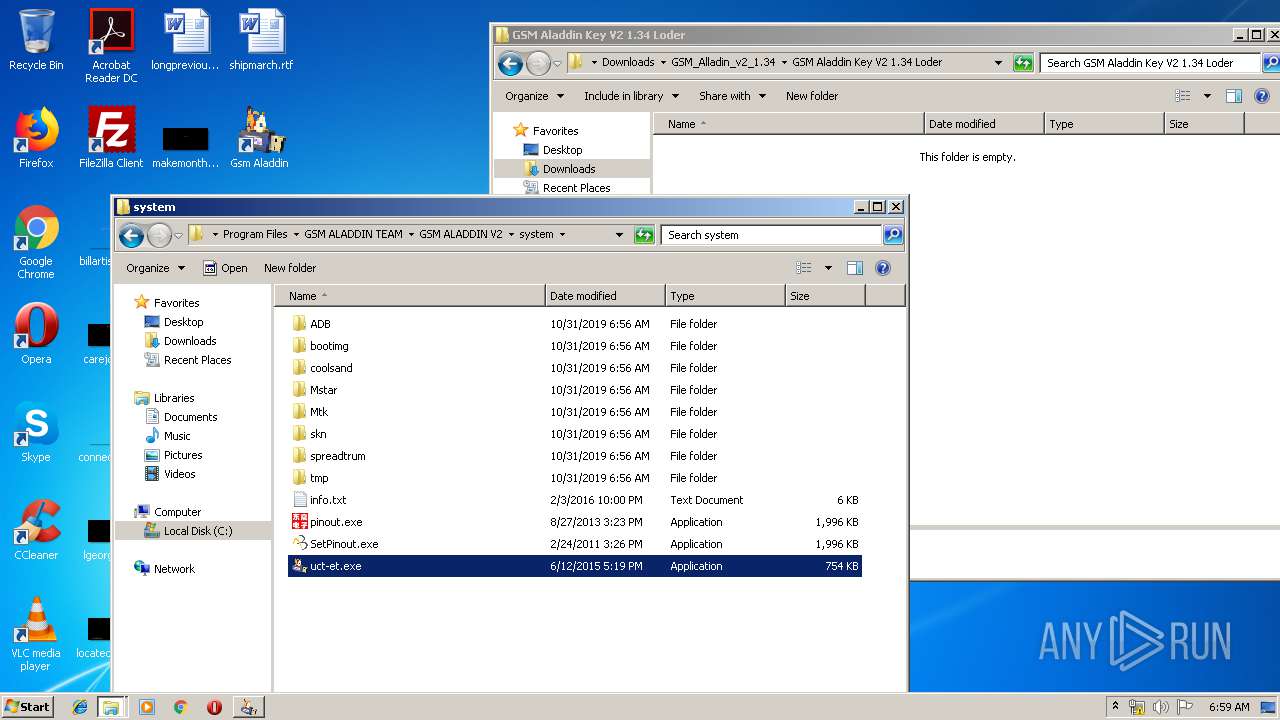
- pinout.exe (PID: 2428)
- evbF902.tmp (PID: 2208)
- SetPinout.exe (PID: 1316)
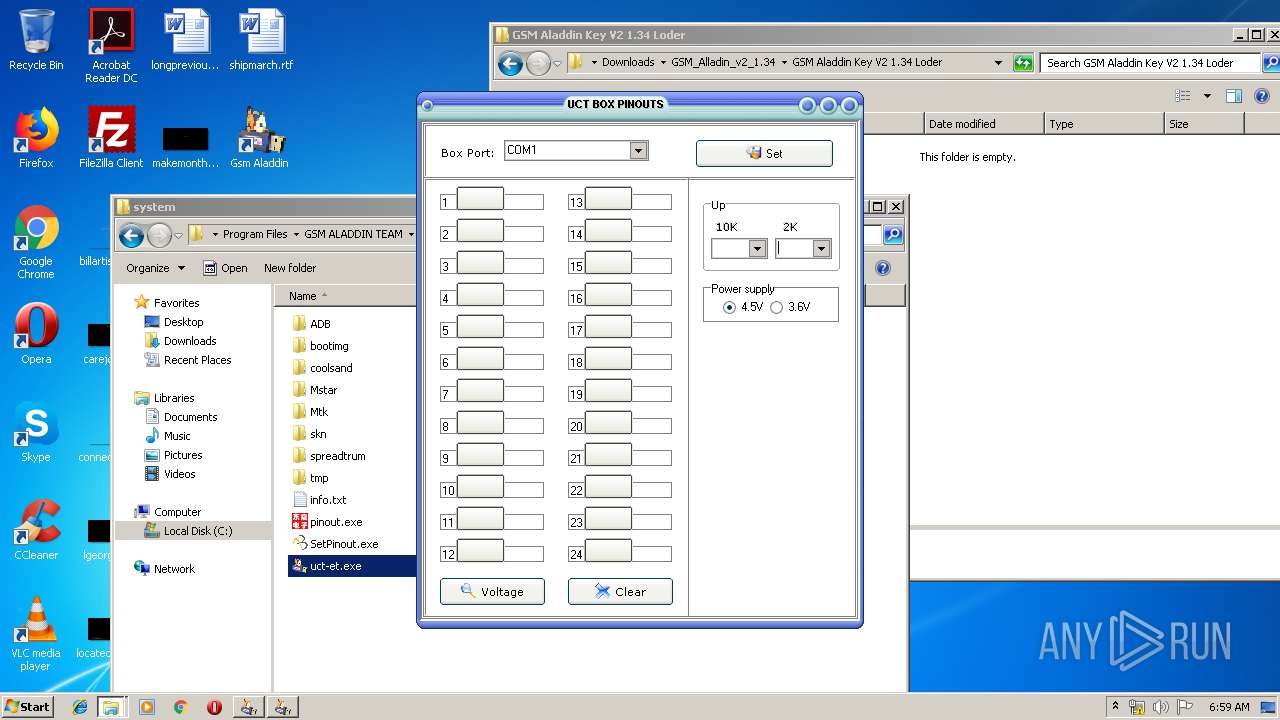
- uct-et.exe (PID: 2788)
- GSM Aladdin 1_34.exe (PID: 1036)
- GSM_ALADDIN.exe (PID: 3276)
- evb1129.tmp (PID: 2564)
- GSM_ALADDIN.exe (PID: 1252)
- 7z.exe (PID: 1776)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1732)
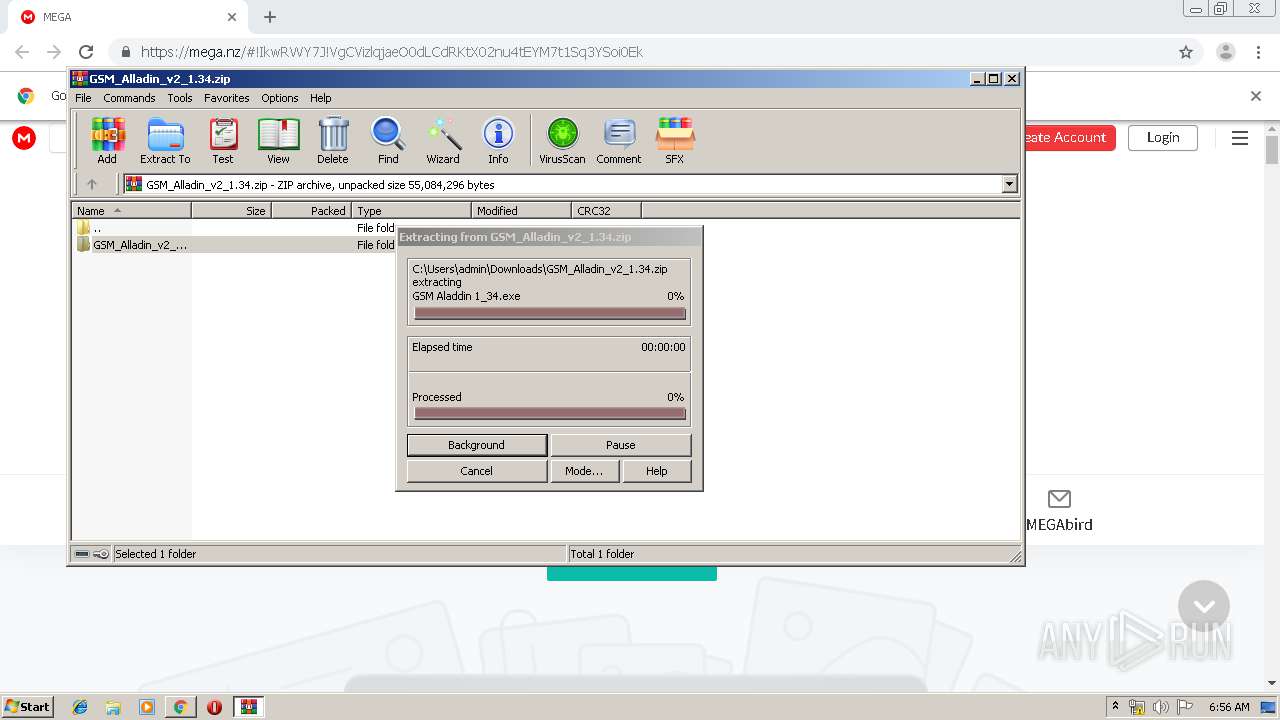
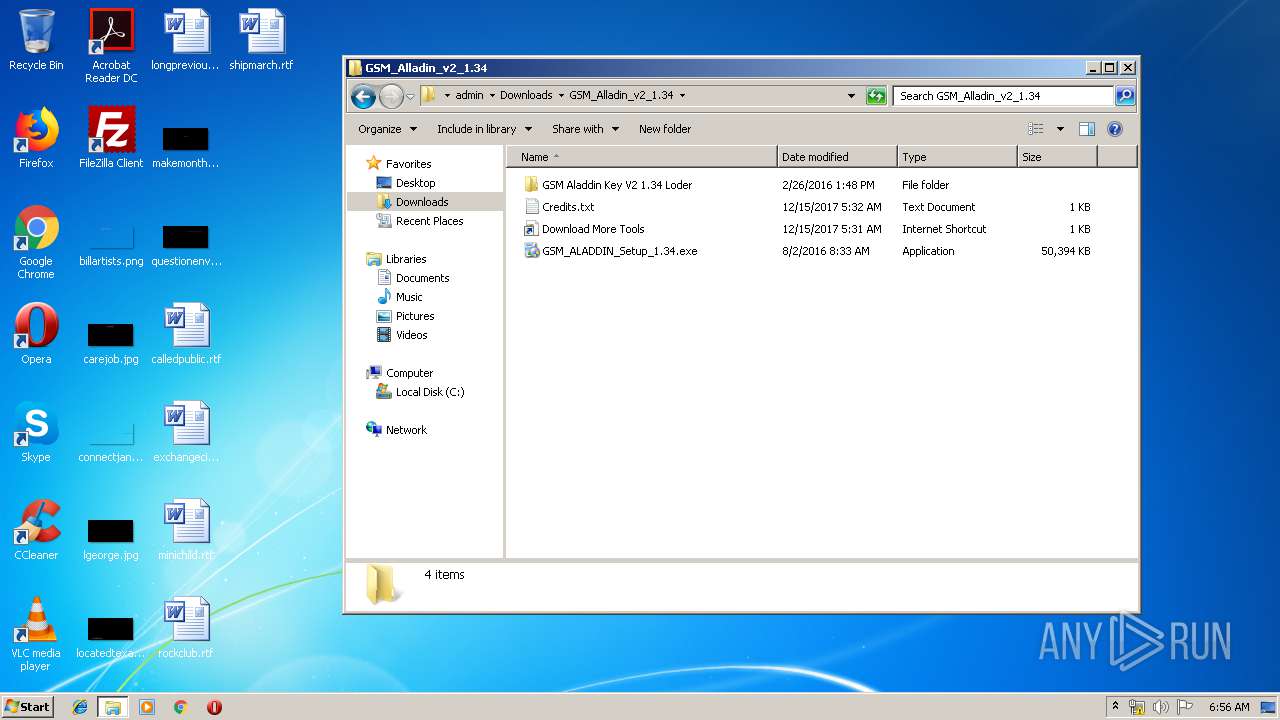
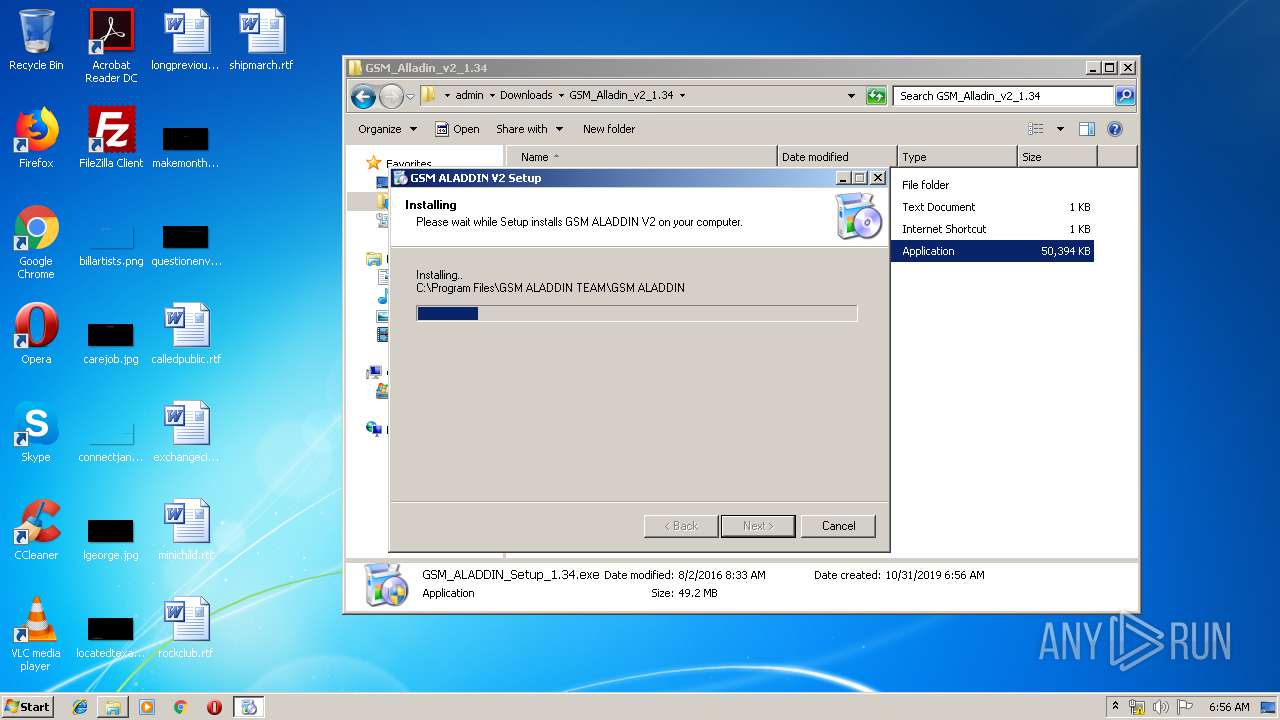
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3384)
- DllHost.exe (PID: 992)
- GSM Aladdin 1_34.exe (PID: 912)
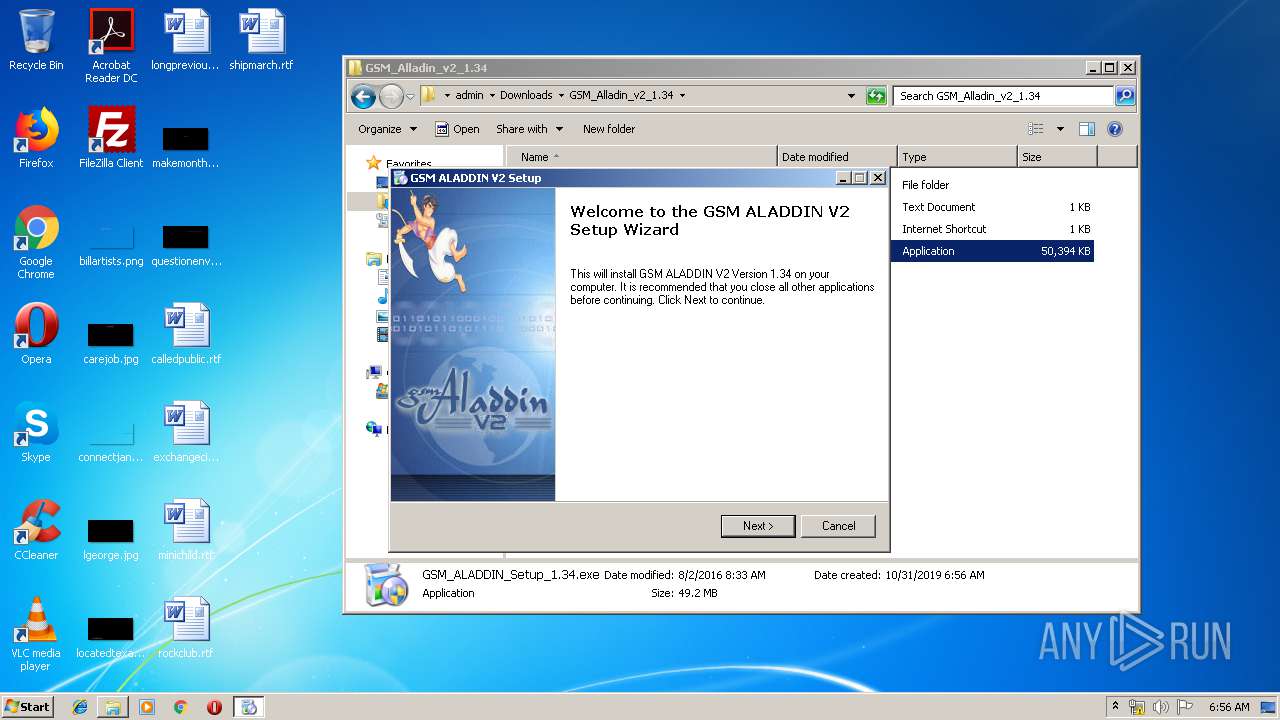
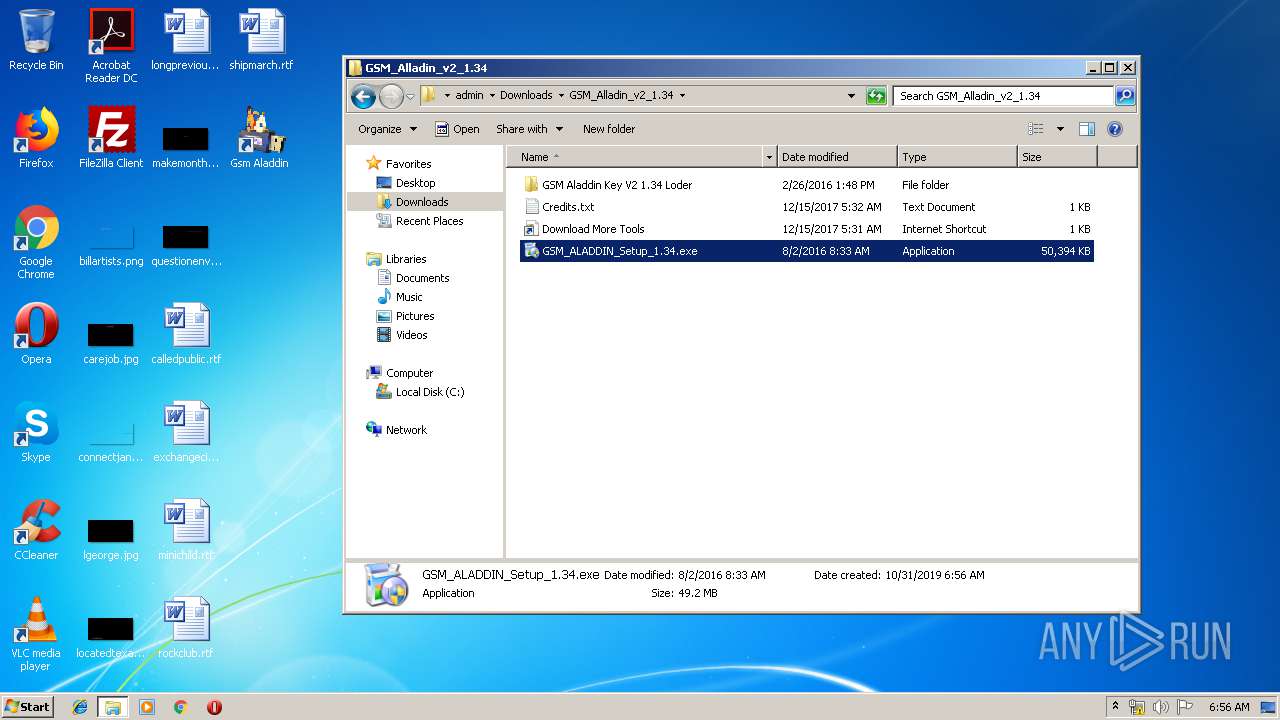
- GSM_ALADDIN_Setup_1.34.exe (PID: 4000)
- GSM Aladdin 1_34.exe (PID: 1036)
Executed via COM
- DllHost.exe (PID: 992)
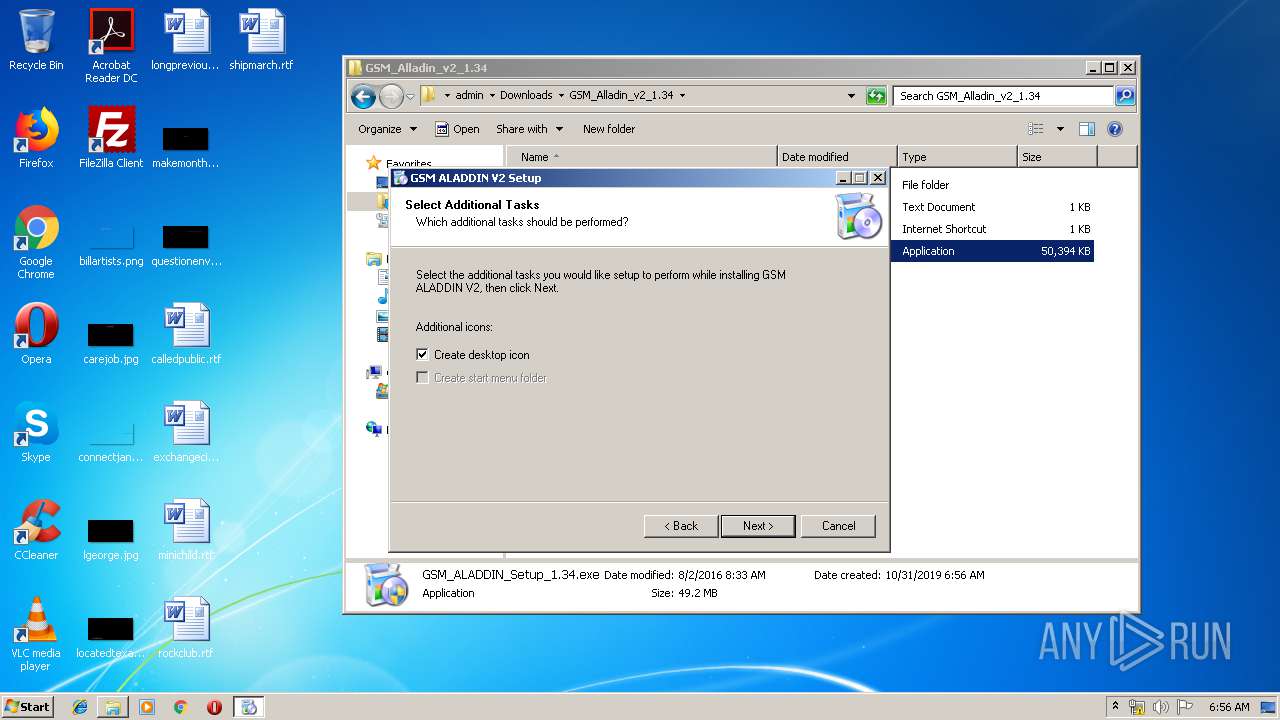
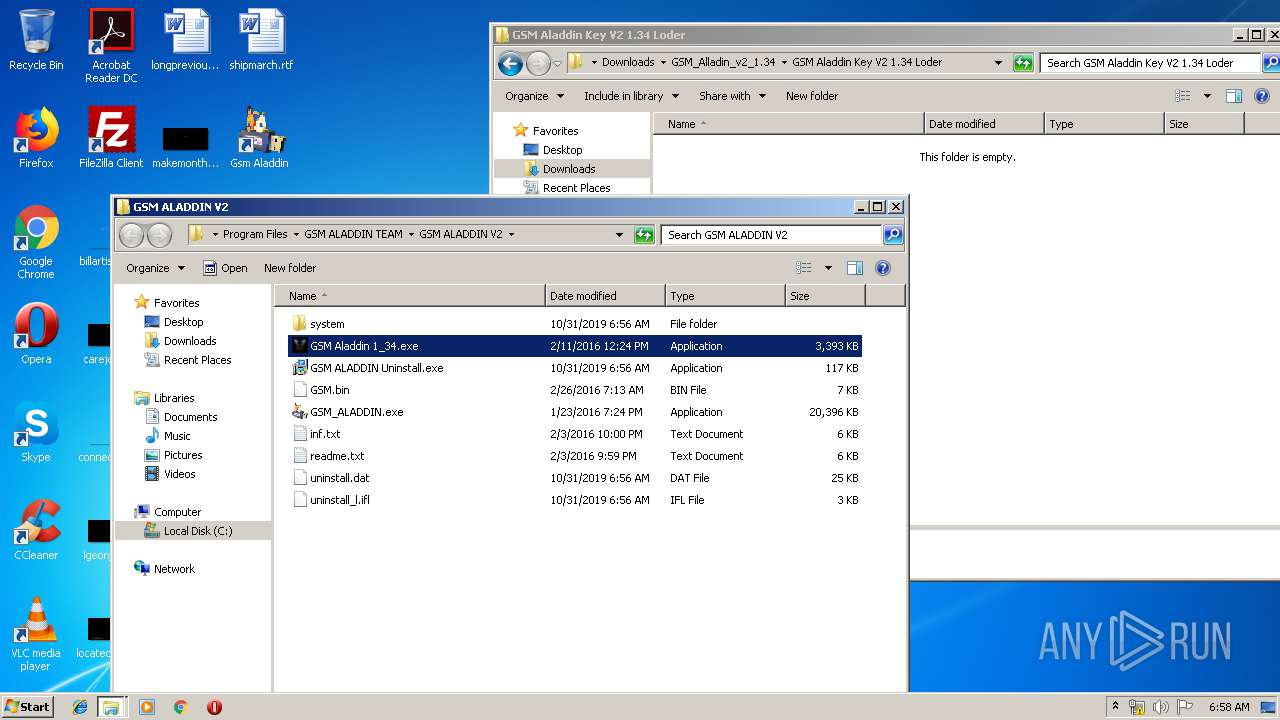
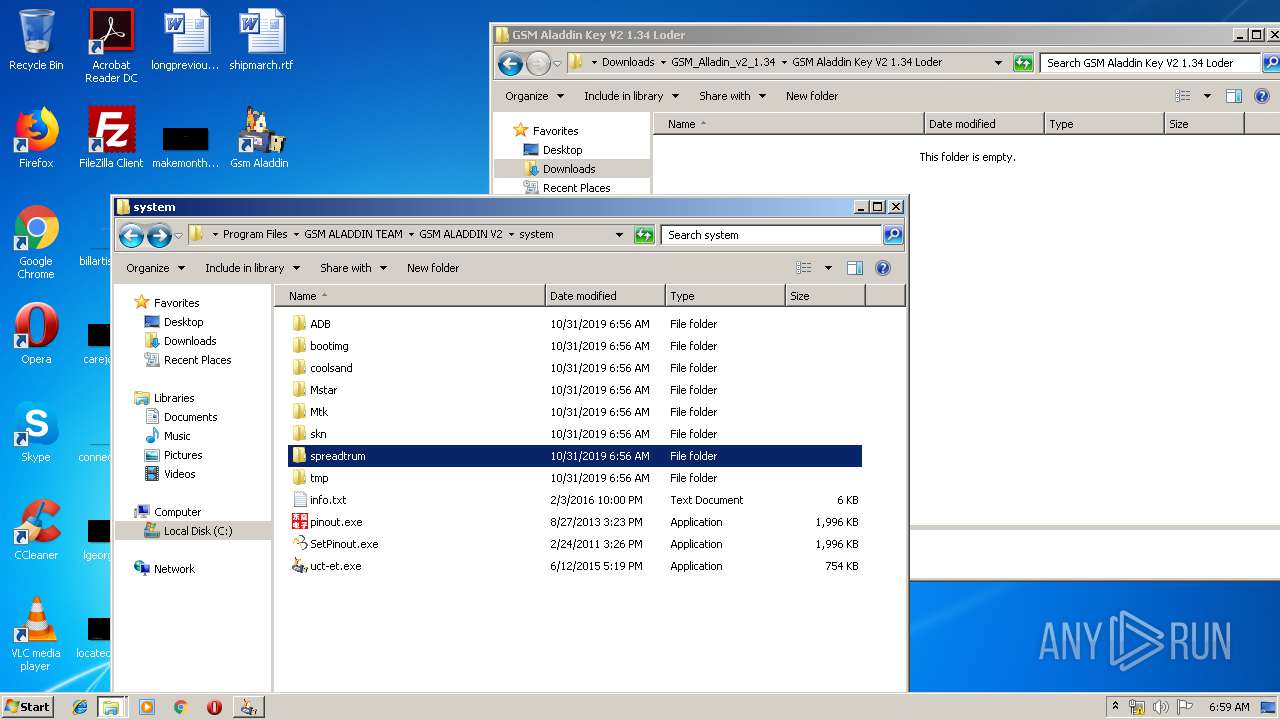
Creates a software uninstall entry
- GSM_ALADDIN_Setup_1.34.exe (PID: 4000)
Starts application with an unusual extension
- GSM Aladdin 1_34.exe (PID: 912)
- GSM Aladdin 1_34.exe (PID: 1036)
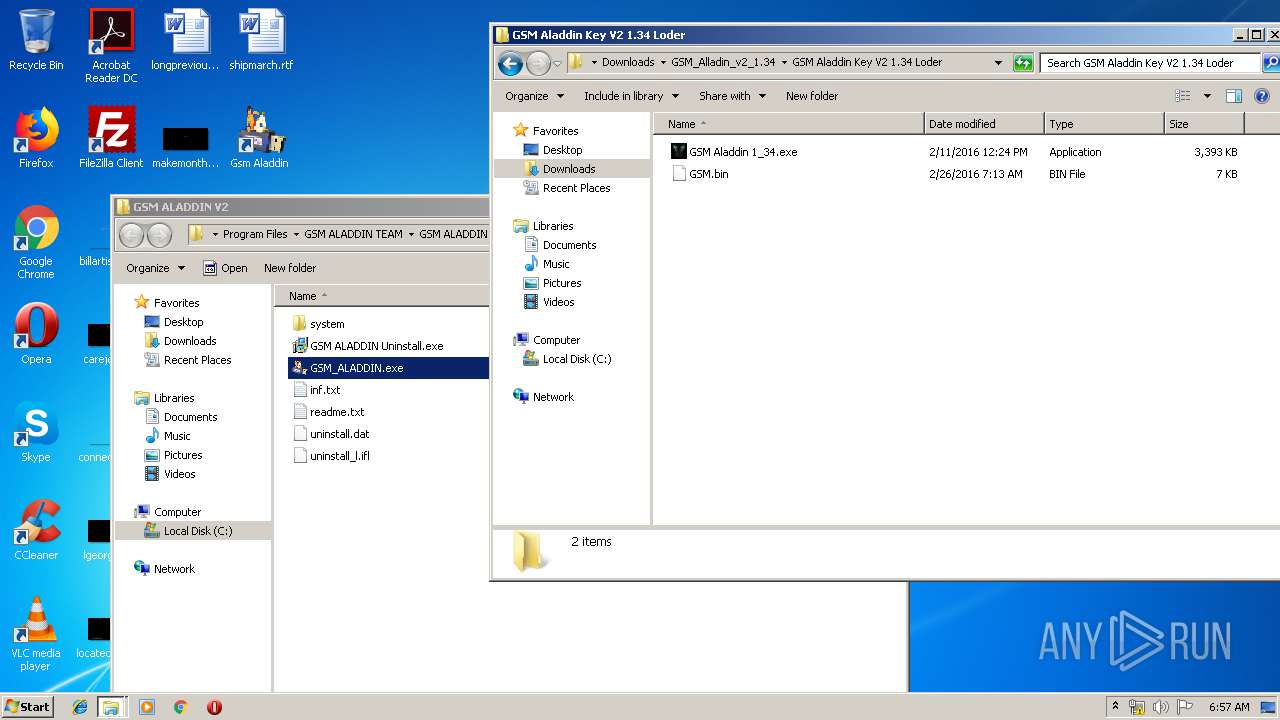
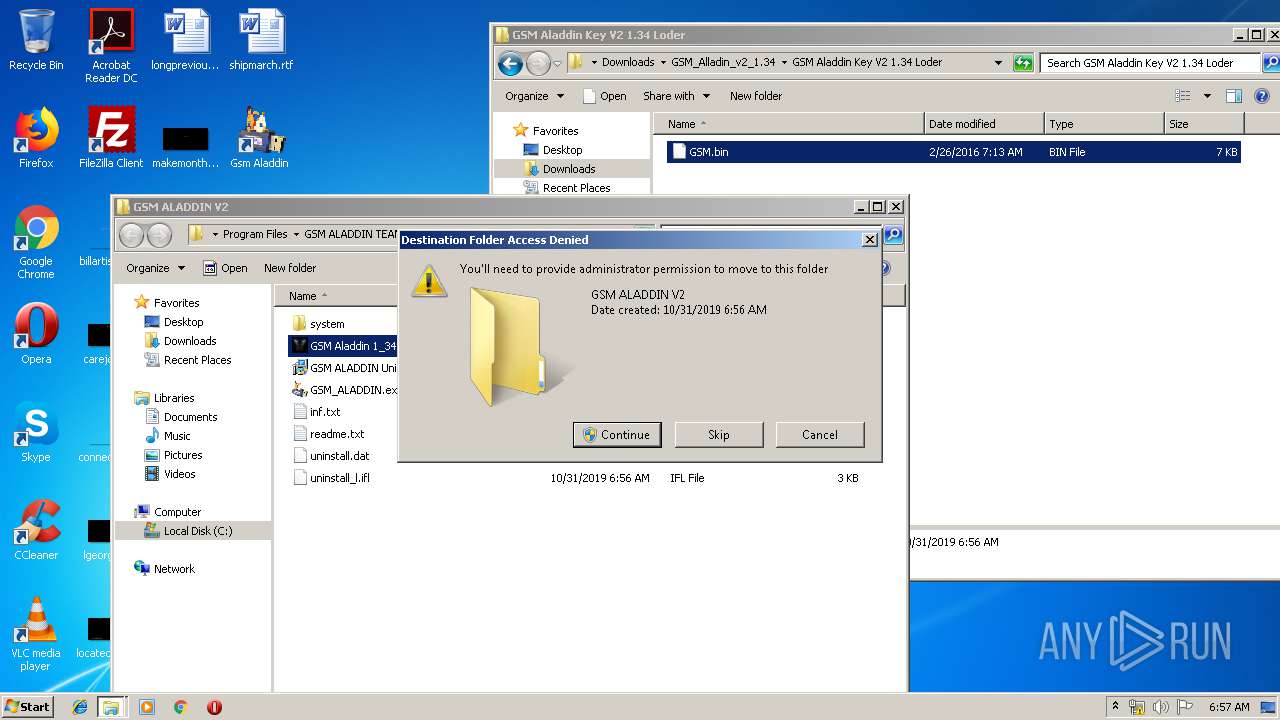
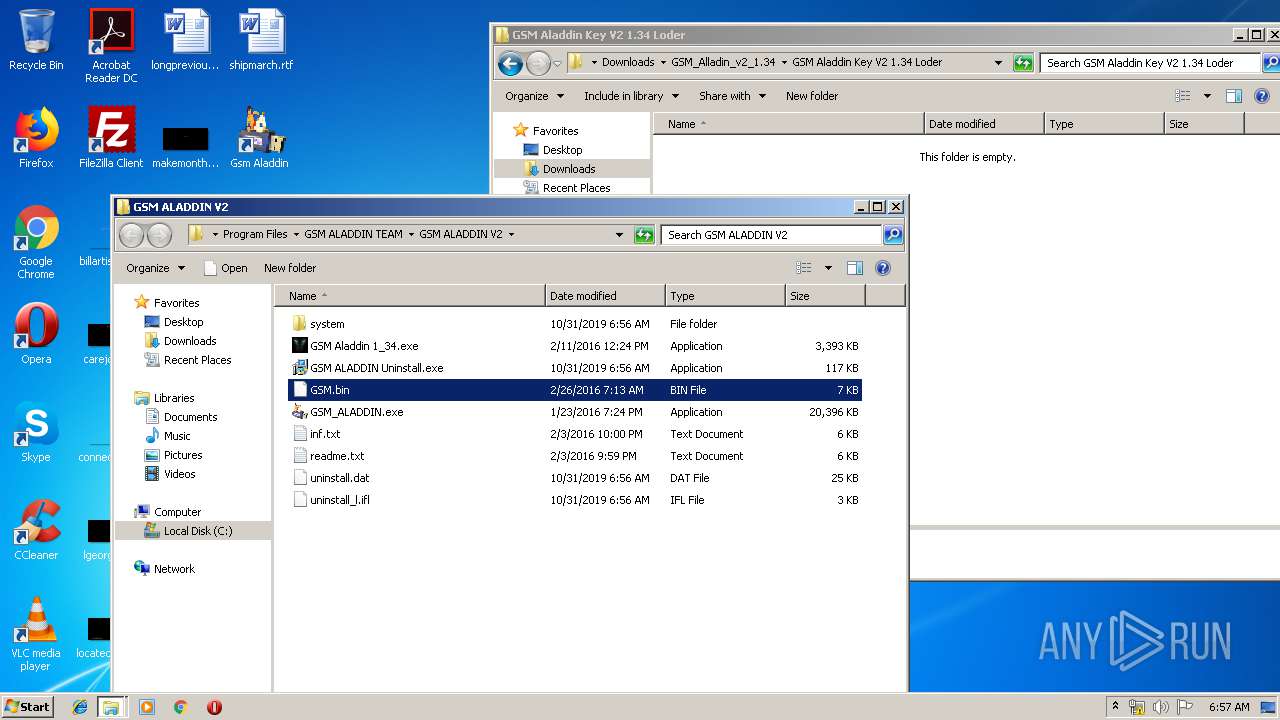
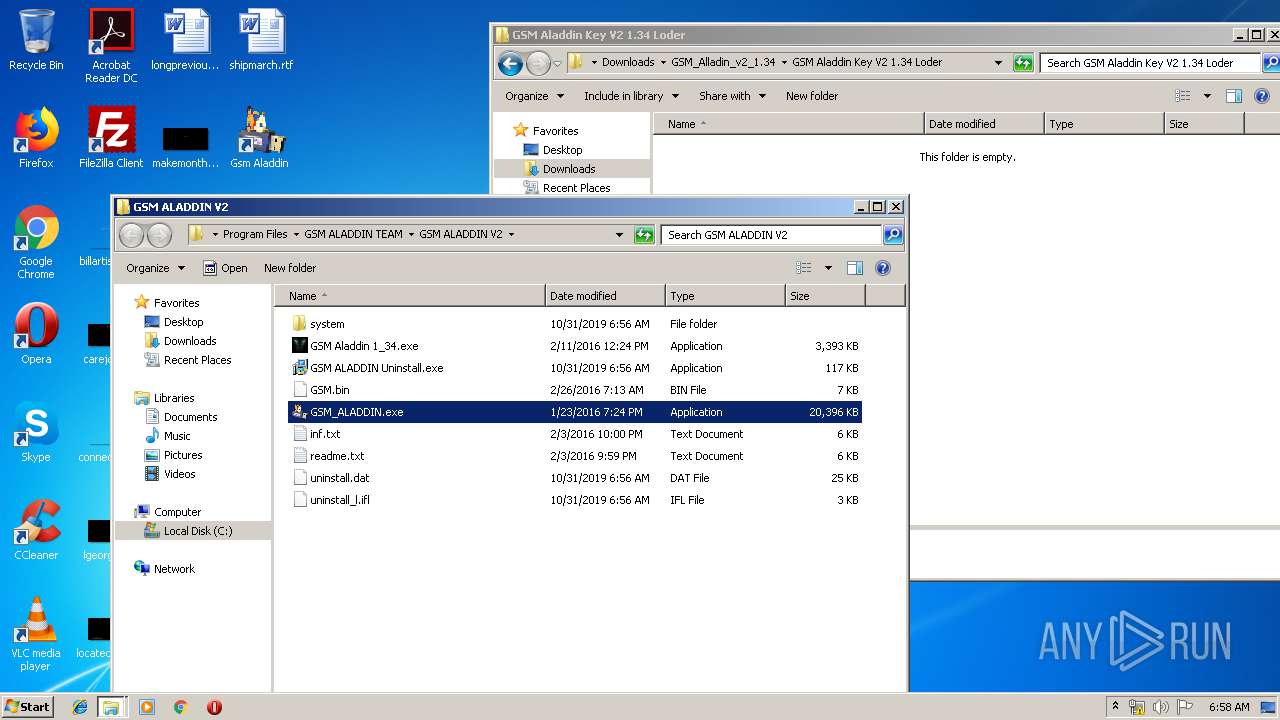
Creates files in the program directory
- GSM_ALADDIN_Setup_1.34.exe (PID: 4000)
INFO
Reads the hosts file
- chrome.exe (PID: 1484)
- chrome.exe (PID: 1732)
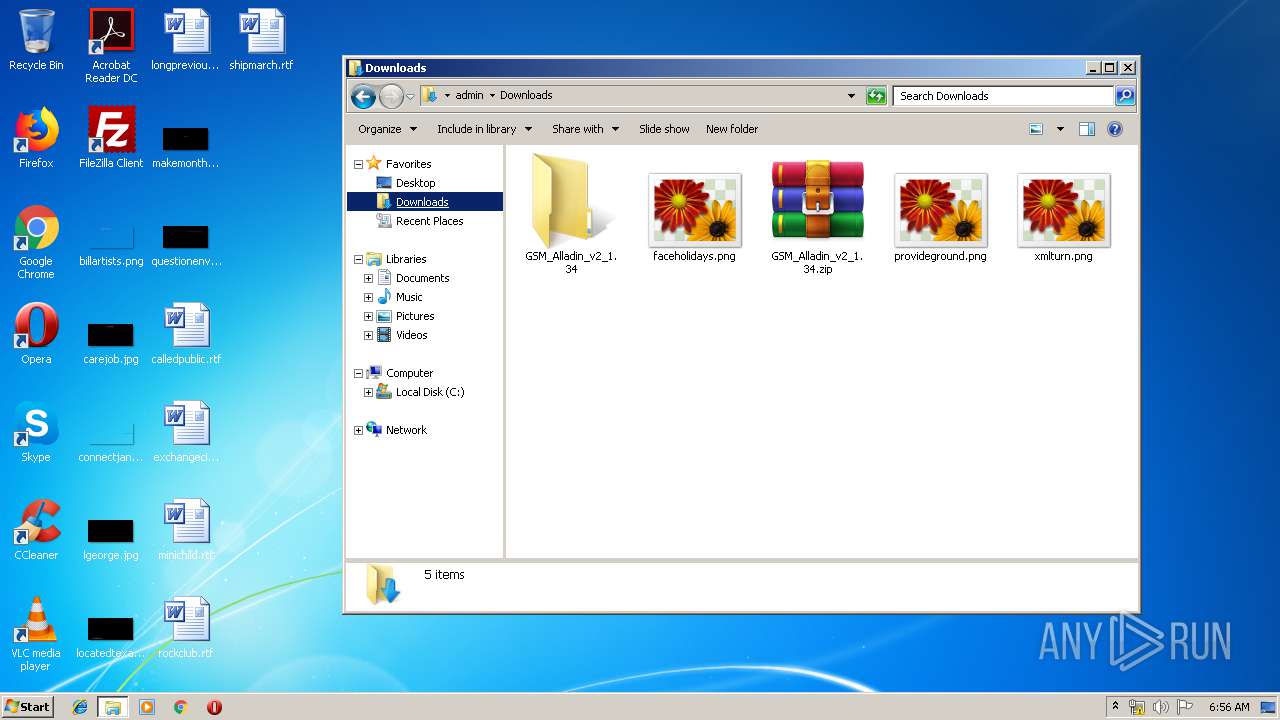
Manual execution by user
- explorer.exe (PID: 2488)
- GSM_ALADDIN_Setup_1.34.exe (PID: 4000)
- GSM_ALADDIN_Setup_1.34.exe (PID: 2892)
- GSM_ALADDIN.exe (PID: 2684)
- GSM Aladdin 1_34.exe (PID: 912)
- pinout.exe (PID: 2428)
- uct-et.exe (PID: 2788)
- 7z.exe (PID: 1776)
- SetPinout.exe (PID: 1316)
- GSM Aladdin 1_34.exe (PID: 1036)
- GSM_ALADDIN.exe (PID: 3276)
Application launched itself
- chrome.exe (PID: 1732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
44
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16200105832939842238 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
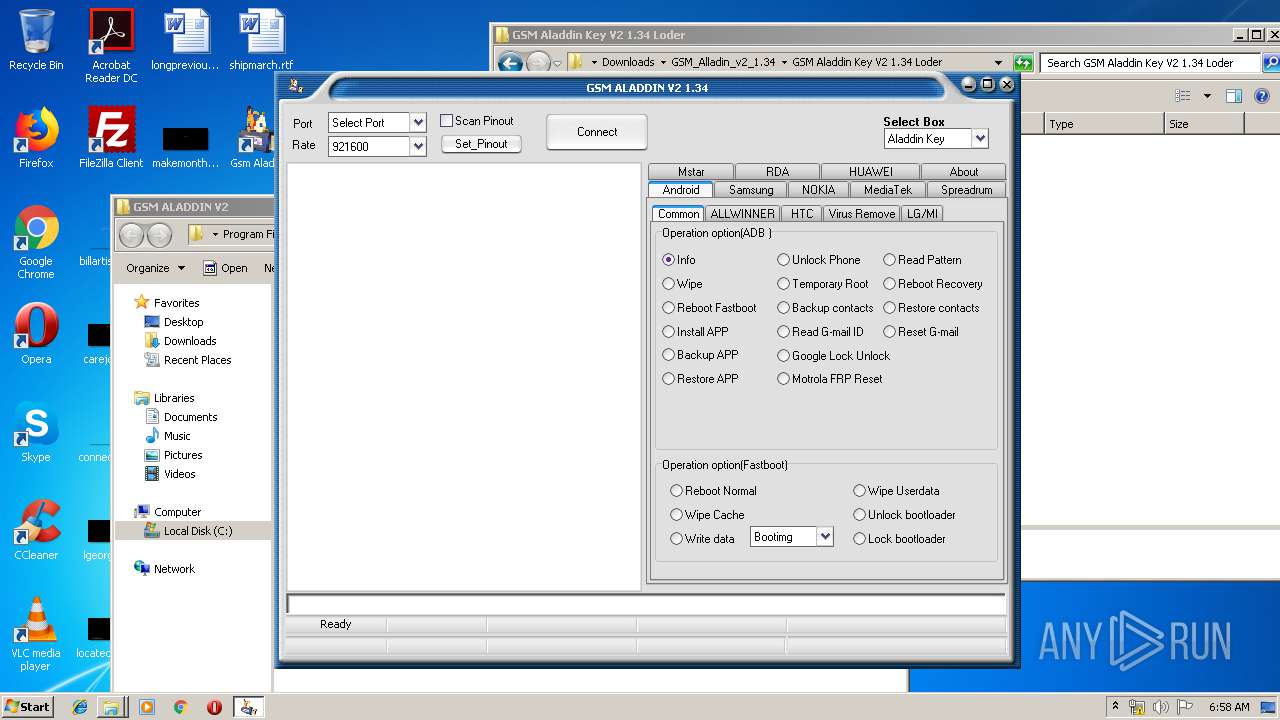
| 912 | "C:\Program Files\GSM ALADDIN TEAM\GSM ALADDIN V2\GSM Aladdin 1_34.exe" | C:\Program Files\GSM ALADDIN TEAM\GSM ALADDIN V2\GSM Aladdin 1_34.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 992 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11135251144170800654 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11257626850814580812 --mojo-platform-channel-handle=3996 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\GSM ALADDIN TEAM\GSM ALADDIN V2\GSM Aladdin 1_34.exe" | C:\Program Files\GSM ALADDIN TEAM\GSM ALADDIN V2\GSM Aladdin 1_34.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
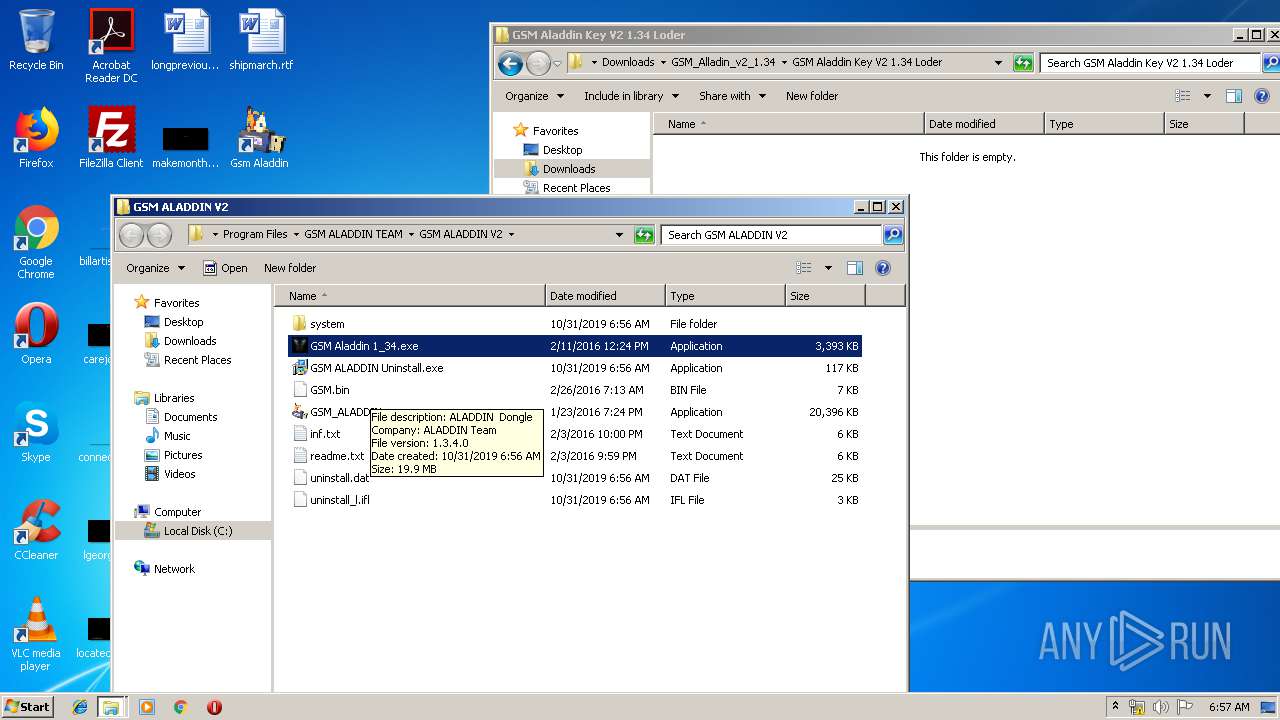
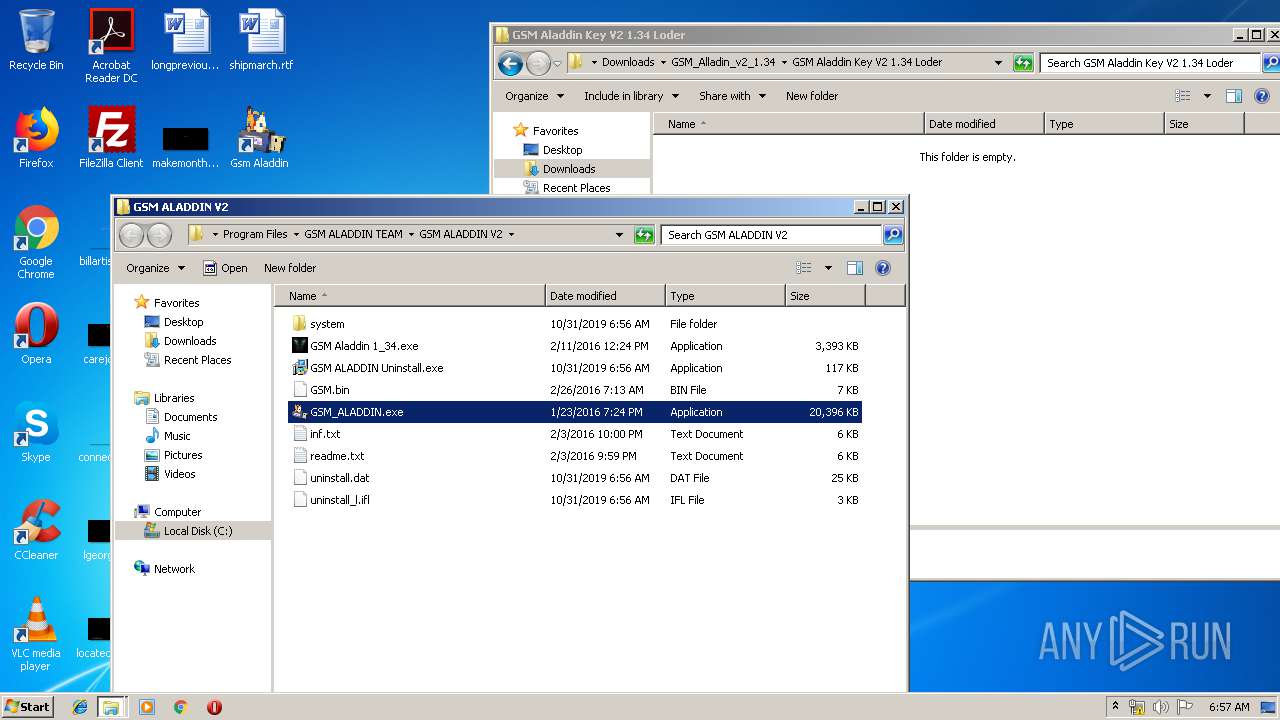
| 1252 | "c:\program files\gsm aladdin team\gsm aladdin v2\GSM_ALADDIN.exe" | c:\program files\gsm aladdin team\gsm aladdin v2\GSM_ALADDIN.exe | evb1129.tmp | ||||||||||||
User: admin Company: ALADDIN Team Integrity Level: MEDIUM Description: ALADDIN Dongle Exit code: 0 Version: 1.3.4.0 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\GSM ALADDIN TEAM\GSM ALADDIN V2\system\SetPinout.exe" | C:\Program Files\GSM ALADDIN TEAM\GSM ALADDIN V2\system\SetPinout.exe | — | explorer.exe | |||||||||||
User: admin Company: 东震电子 Integrity Level: MEDIUM Exit code: 0 Version: 1.7.6.0 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4959057040537527172 --mojo-platform-channel-handle=1628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,8126699356046047243,15623242143448375955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11324844470473248639 --mojo-platform-channel-handle=4504 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 093
Read events
1 938
Write events
150
Delete events
5
Modification events
| (PID) Process: | (2200) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1732-13216978484953750 |
Value: 259 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1732-13216978484953750 |
Value: 259 | |||
Executable files
22
Suspicious files
219
Text files
367
Unknown types
50
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6256c899-dedb-4b31-ab09-0a371175649e.tmp | — | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a62d.TMP | text | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a61e.TMP | text | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39a66c.TMP | text | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1732 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
44
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
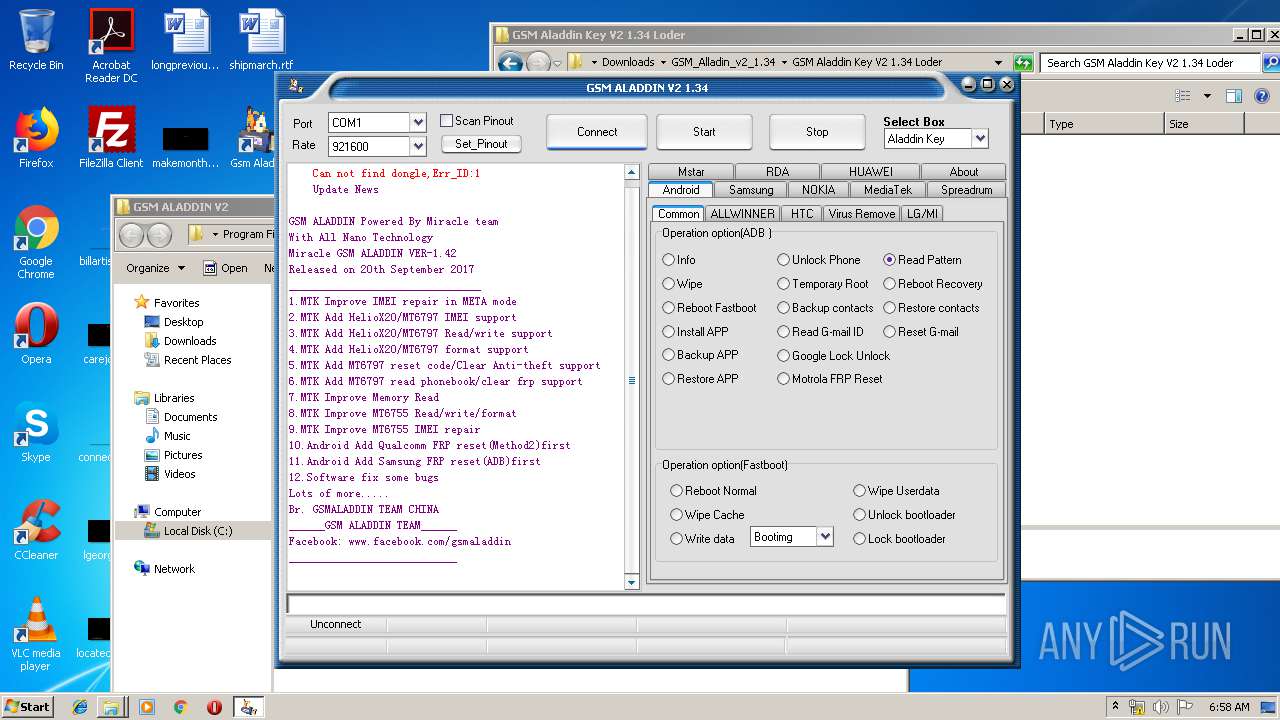
1484 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
1484 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
1648 | GSM_ALADDIN.exe | GET | 200 | 104.237.255.13:80 | http://miraclesserver.com/upd/news/aladdin.txt | US | text | 797 b | whitelisted |
1484 | chrome.exe | GET | 200 | 173.194.164.153:80 | http://r3---sn-4g5edne6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=89.187.165.52&mm=28&mn=sn-4g5edne6&ms=nvh&mt=1572504794&mv=m&mvi=2&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
1484 | chrome.exe | GET | 200 | 173.194.188.135:80 | http://r2---sn-4g5ednsz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=89.187.165.52&mm=28&mn=sn-4g5ednsz&ms=nvh&mt=1572504794&mv=m&mvi=1&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1484 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1484 | chrome.exe | 89.44.169.135:443 | mega.nz | Datacenter Luxembourg S.A. | LU | suspicious |
1484 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
1484 | chrome.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1484 | chrome.exe | 172.217.22.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
1484 | chrome.exe | 31.216.148.11:443 | eu.static.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
1484 | chrome.exe | 172.217.18.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
1484 | chrome.exe | 172.217.21.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1484 | chrome.exe | 31.216.147.136:443 | g.api.mega.co.nz | Datacenter Luxembourg S.A. | LU | shared |
1484 | chrome.exe | 173.194.188.135:80 | r2---sn-4g5ednsz.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mega.nz |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-4g5edne6.gvt1.com |
| whitelisted |
g.api.mega.co.nz |
| shared |
Threats
Process | Message |
|---|---|
GSM_ALADDIN.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
GSM_ALADDIN.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
GSM_ALADDIN.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
GSM_ALADDIN.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|