| File name: | x4da978ee2ca82aae1b32f929670e5457f8d1d1fd8c2433a9ec7904d27da4a7c7.exe |
| Full analysis: | https://app.any.run/tasks/1b8f4637-58cd-4d60-9044-04698d22b791 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | January 10, 2026, 03:06:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | D91E2575C4E578AAE120E92B859C1FA0 |
| SHA1: | 427CA3AA7B3F300BD1C764F8F2FF4DF9D38393B4 |
| SHA256: | 4DA978EE2CA82AAE1B32F929670E5457F8D1D1FD8C2433A9EC7904D27DA4A7C7 |
| SSDEEP: | 196608:vtf6oQbyk6+Ly/CcFsmXVGfEeudS7m5u:v2byk3BcnXVGHMS7m5u |
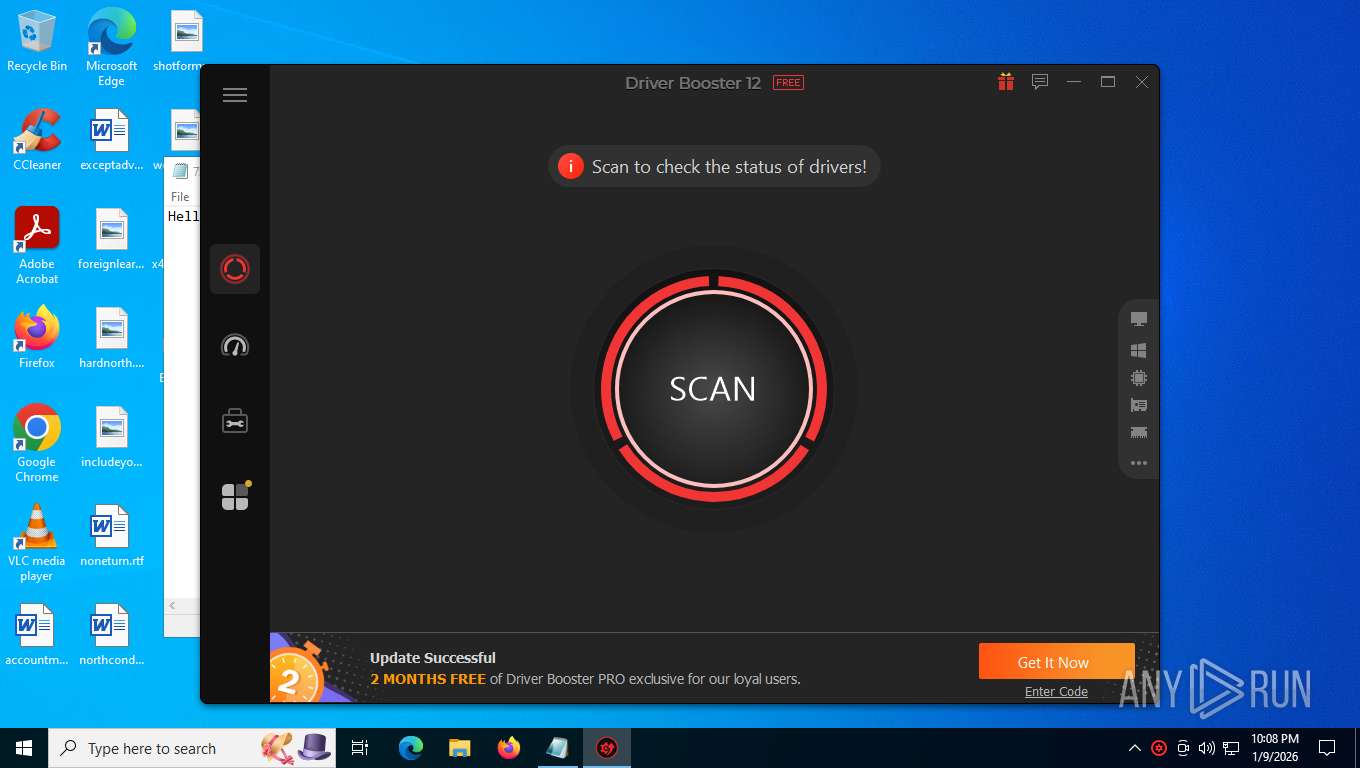
MALICIOUS
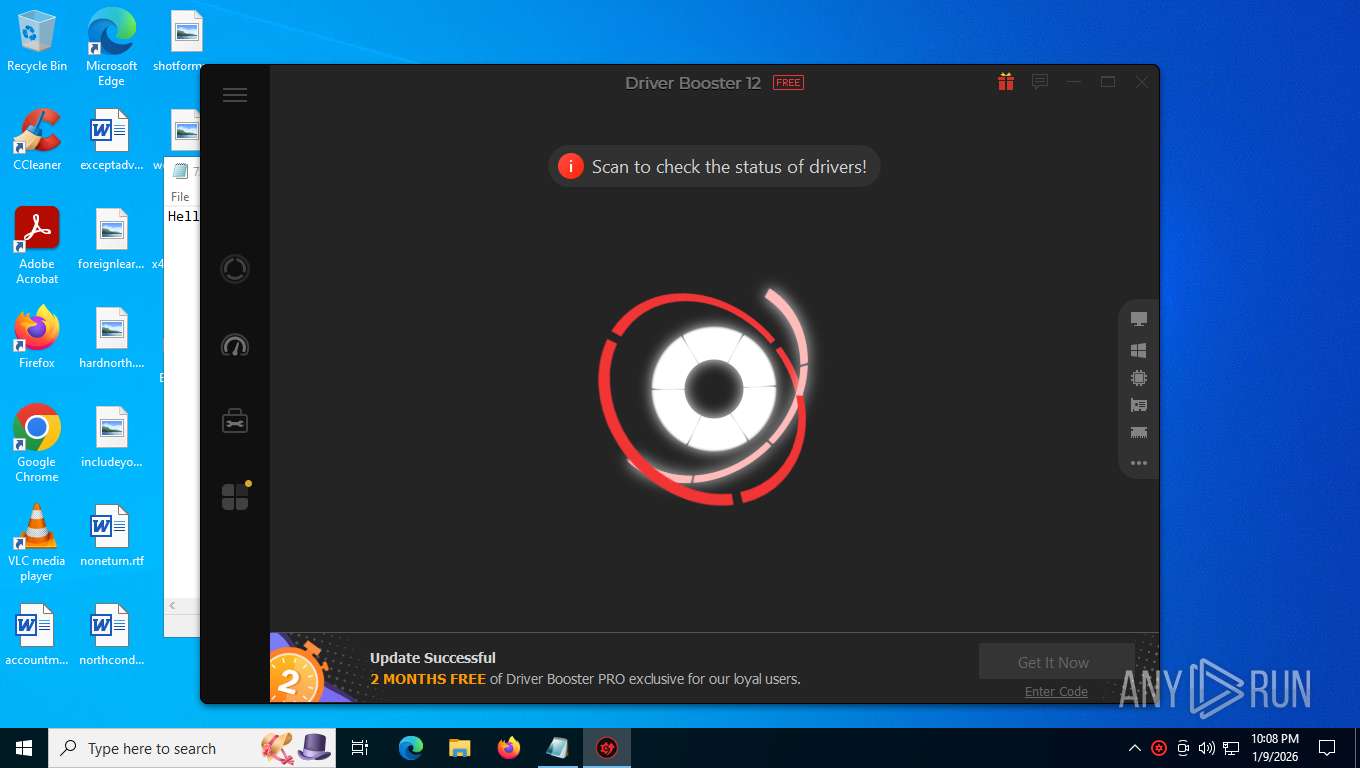
Executing a file with an untrusted certificate
- HWiNFO.exe (PID: 8100)
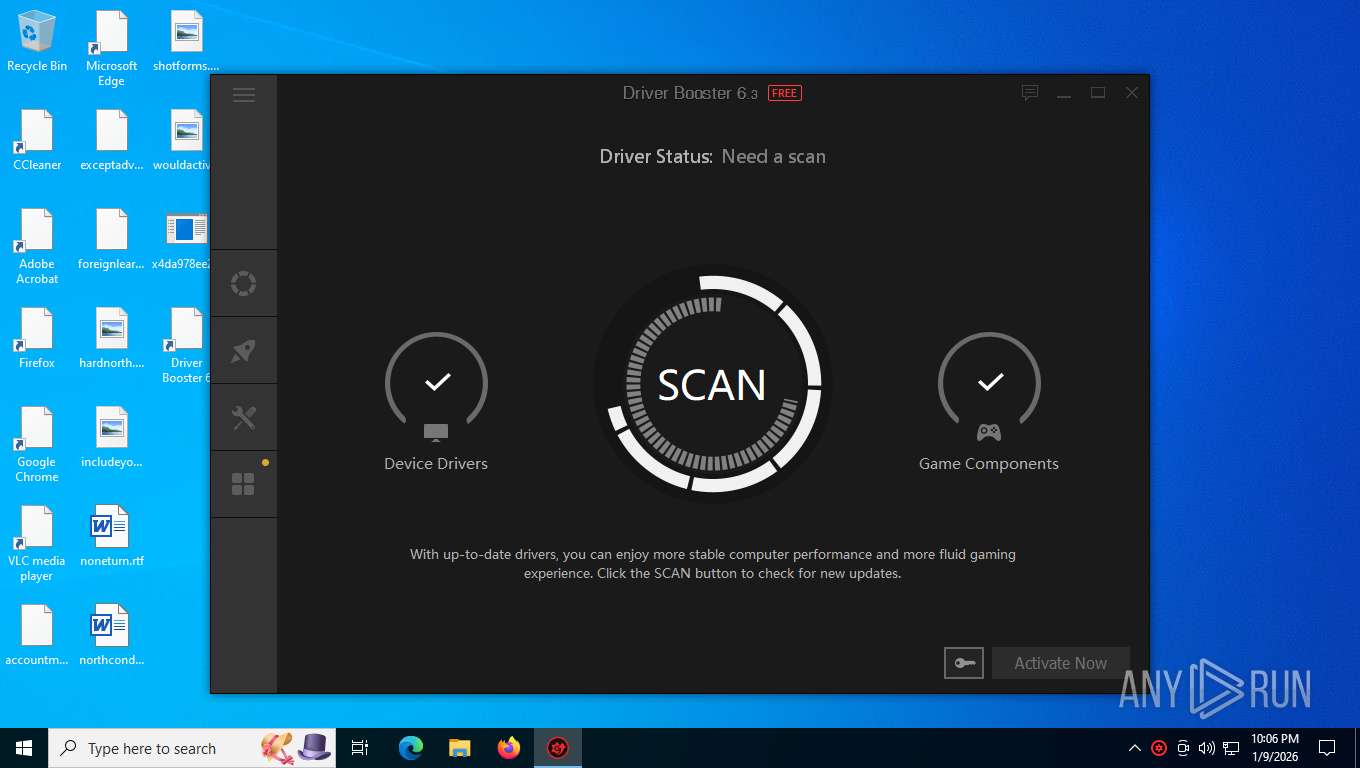
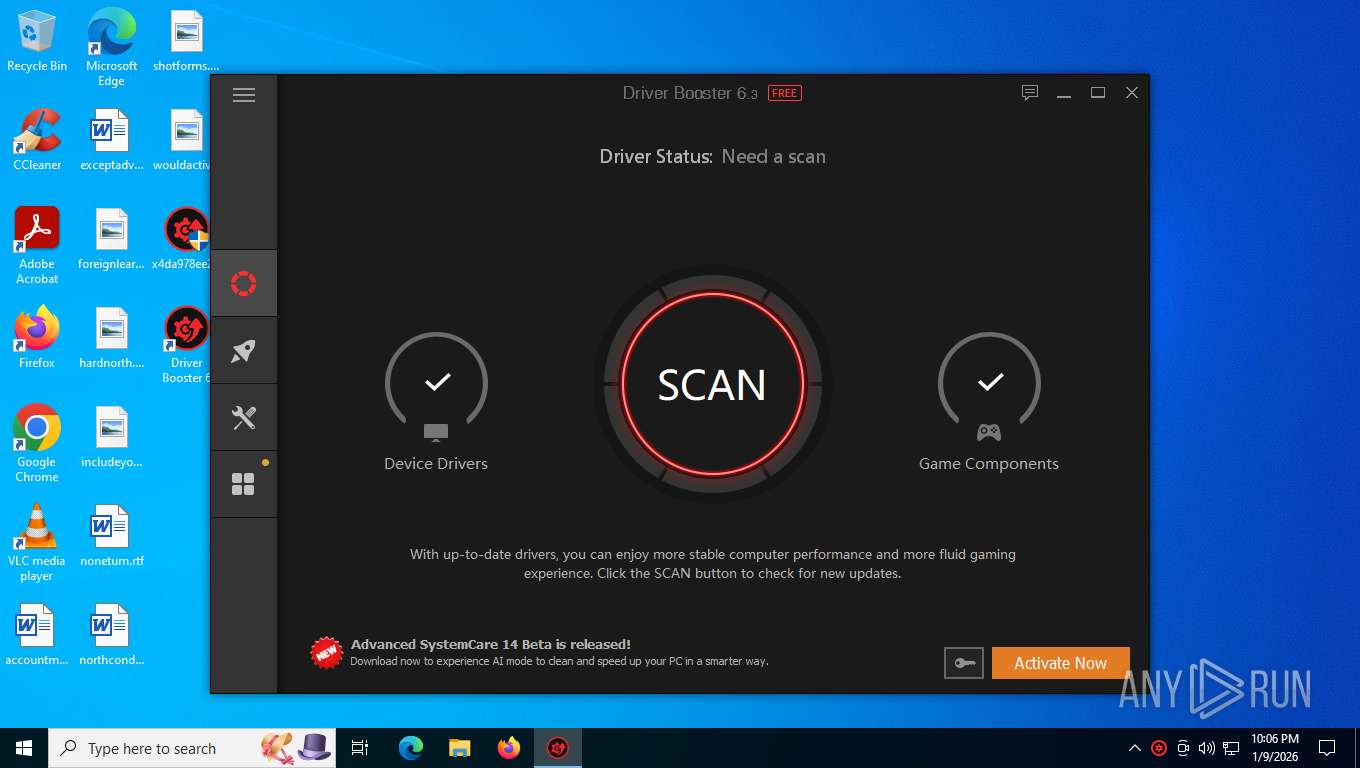
- DriverBooster.exe (PID: 8120)
- SetupHlp.exe (PID: 1000)
- AutoUpdate.exe (PID: 3344)
- ICONPIN64.exe (PID: 7428)
- ChangeIcon.exe (PID: 1872)
- NoteIcon.exe (PID: 6084)
- FaultFixes.exe (PID: 7176)
- RttHlp.exe (PID: 2092)
- FaultFixes.exe (PID: 7196)
- RttHlp.exe (PID: 7212)
- AUpdate.exe (PID: 7272)
- unins000.exe (PID: 2224)
- InstStat.exe (PID: 1948)
- SetupHlp.exe (PID: 4920)
Runs injected code in another process
- ICONPIN64.exe (PID: 7428)
- ICONPIN64.exe (PID: 5704)
- ICONPIN64.exe (PID: 7488)
Application was injected by another process
- explorer.exe (PID: 4972)
Changes settings of System certificates
- DriverBooster.exe (PID: 7604)
Steals credentials from Web Browsers
- CareScan.exe (PID: 7728)
Actions looks like stealing of personal data
- CareScan.exe (PID: 7728)
SUSPICIOUS
Executable content was dropped or overwritten
- x4da978ee2ca82aae1b32f929670e5457f8d1d1fd8c2433a9ec7904d27da4a7c7.exe (PID: 7960)
- ~plczrlj.ibo (PID: 7988)
- ~plczrlj.tmp (PID: 8008)
- HWiNFO.exe (PID: 8100)
- AutoUpdate.exe (PID: 3344)
- db910_20211220.exe (PID: 7564)
- db910_20211220.tmp (PID: 7536)
- _iu14D2N.tmp (PID: 7600)
- unins000.exe (PID: 2224)
- AutoUpdate.exe (PID: 7952)
- db1200_20240920.exe (PID: 7616)
- db1200_20240920.tmp (PID: 7700)
- _iu14D2N.tmp (PID: 3344)
- AutoUpdate.exe (PID: 2740)
- AutoUpdate.exe (PID: 5180)
Starts application with an unusual extension
- x4da978ee2ca82aae1b32f929670e5457f8d1d1fd8c2433a9ec7904d27da4a7c7.exe (PID: 7960)
- unins000.exe (PID: 2224)
- unins000.exe (PID: 7696)
Reads the Windows owner or organization settings
- ~plczrlj.tmp (PID: 8008)
- db910_20211220.tmp (PID: 7536)
- _iu14D2N.tmp (PID: 7600)
- db1200_20240920.tmp (PID: 7700)
- _iu14D2N.tmp (PID: 3344)
Process drops legitimate windows executable
- ~plczrlj.tmp (PID: 8008)
- db910_20211220.tmp (PID: 7536)
- db1200_20240920.tmp (PID: 7700)
Drops 7-zip archiver for unpacking
- ~plczrlj.tmp (PID: 8008)
- db910_20211220.tmp (PID: 7536)
- db1200_20240920.tmp (PID: 7700)
Creates files in the driver directory
- HWiNFO.exe (PID: 8100)
Drops a system driver (possible attempt to evade defenses)
- HWiNFO.exe (PID: 8100)
There is functionality for taking screenshot (YARA)
- x4da978ee2ca82aae1b32f929670e5457f8d1d1fd8c2433a9ec7904d27da4a7c7.exe (PID: 7960)
- DriverBooster.exe (PID: 8120)
- DriverBooster.exe (PID: 7604)
Reads security settings of Internet Explorer
- ~plczrlj.tmp (PID: 8008)
- DriverBooster.exe (PID: 8120)
- AUpdate.exe (PID: 7272)
- AutoUpdate.exe (PID: 3344)
- db910_20211220.tmp (PID: 7536)
- _iu14D2N.tmp (PID: 7600)
- SetupHlp.exe (PID: 8108)
- DriverBooster.exe (PID: 7604)
- AUpdate.exe (PID: 7500)
- SetupHlp.exe (PID: 7176)
- AutoUpdate.exe (PID: 7952)
- db1200_20240920.tmp (PID: 7700)
- _iu14D2N.tmp (PID: 3344)
- AutoUpdate.exe (PID: 2740)
- DriverBooster.exe (PID: 7968)
- AutoUpdate.exe (PID: 5180)
- SetupHlp.exe (PID: 7704)
Searches for installed software
- AUpdate.exe (PID: 7272)
- db910_20211220.tmp (PID: 7536)
- _iu14D2N.tmp (PID: 7600)
- InstStat.exe (PID: 1948)
- SetupHlp.exe (PID: 8108)
- CareScan.exe (PID: 7728)
- InstStat.exe (PID: 8188)
- db1200_20240920.tmp (PID: 7700)
- _iu14D2N.tmp (PID: 3344)
- InstStat.exe (PID: 2352)
- SetupHlp.exe (PID: 3656)
- InstStat.exe (PID: 6096)
- dbpm.exe (PID: 4940)
There is functionality for communication over UDP network (YARA)
- DriverBooster.exe (PID: 8120)
- DriverBooster.exe (PID: 7604)
Starts itself from another location
- unins000.exe (PID: 2224)
- unins000.exe (PID: 7696)
Process drops SQLite DLL files
- db910_20211220.tmp (PID: 7536)
- db1200_20240920.tmp (PID: 7700)
The process verifies whether the antivirus software is installed
- CareScan.exe (PID: 7728)
Reads Microsoft Outlook installation path
- CareScan.exe (PID: 7728)
Adds/modifies Windows certificates
- DriverBooster.exe (PID: 7604)
Possible stealing from browsers
- CareScan.exe (PID: 7728)
There is functionality for VM detection VMWare (YARA)
- CareScan.exe (PID: 7728)
INFO
Reads mouse settings
- x4da978ee2ca82aae1b32f929670e5457f8d1d1fd8c2433a9ec7904d27da4a7c7.exe (PID: 7960)
- CareScan.exe (PID: 7728)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4972)
- notepad.exe (PID: 7244)
Checks supported languages
- x4da978ee2ca82aae1b32f929670e5457f8d1d1fd8c2433a9ec7904d27da4a7c7.exe (PID: 7960)
- ~plczrlj.ibo (PID: 7988)
- ~plczrlj.tmp (PID: 8008)
- HWiNFO.exe (PID: 8100)
- DriverBooster.exe (PID: 8120)
- SetupHlp.exe (PID: 1000)
- ICONPIN64.exe (PID: 7428)
- AutoUpdate.exe (PID: 3344)
- ChangeIcon.exe (PID: 1872)
- NoteIcon.exe (PID: 6084)
- RttHlp.exe (PID: 2092)
- FaultFixes.exe (PID: 7176)
- RttHlp.exe (PID: 7212)
- FaultFixes.exe (PID: 7196)
- AUpdate.exe (PID: 7272)
- db910_20211220.exe (PID: 7564)
- db910_20211220.tmp (PID: 7536)
- unins000.exe (PID: 2224)
- _iu14D2N.tmp (PID: 7600)
- InstStat.exe (PID: 1948)
- SetupHlp.exe (PID: 4920)
- HWiNFO.exe (PID: 7716)
- CareScan.exe (PID: 7728)
- DriverBooster.exe (PID: 7604)
- Manta.exe (PID: 5868)
- ICONPIN64.exe (PID: 5704)
- AutoUpdate.exe (PID: 7952)
- SetupHlp.exe (PID: 8108)
- ChangeIcon.exe (PID: 5176)
- RttHlp.exe (PID: 2568)
- RttHlp.exe (PID: 4700)
- Manta.exe (PID: 7116)
- Manta.exe (PID: 6456)
- SetupHlp.exe (PID: 7176)
- FaultFixes.exe (PID: 7208)
- RttHlp.exe (PID: 7196)
- FaultFixes.exe (PID: 7240)
- AUpdate.exe (PID: 7500)
- InstStat.exe (PID: 8188)
- db1200_20240920.exe (PID: 7616)
- db1200_20240920.tmp (PID: 7700)
- rma.exe (PID: 7180)
- InstStat.exe (PID: 2352)
- _iu14D2N.tmp (PID: 3344)
- unins000.exe (PID: 7696)
- SetupHlp.exe (PID: 3656)
- SetupHlp.exe (PID: 6684)
- HWiNFO.exe (PID: 4508)
- AutoUpdate.exe (PID: 2740)
- rma.exe (PID: 7184)
- DriverBooster.exe (PID: 7968)
- ICONPIN64.exe (PID: 7488)
- RttHlp.exe (PID: 1960)
- InstStat.exe (PID: 6096)
- ProductStat3.exe (PID: 4620)
- Manta.exe (PID: 7984)
- Manta.exe (PID: 4516)
- Manta.exe (PID: 5876)
- ChangeIcon.exe (PID: 6640)
- AutoUpdate.exe (PID: 5180)
- NoteIcon.exe (PID: 1700)
- Manta.exe (PID: 6788)
- RttHlp.exe (PID: 4212)
- ProductStat3.exe (PID: 7972)
- FaultFixes.exe (PID: 7540)
- ScanWinUpd.exe (PID: 8088)
- FaultFixes.exe (PID: 7228)
- SetupHlp.exe (PID: 7704)
- dbpm.exe (PID: 4940)
- RttHlp.exe (PID: 7804)
- AUpdate.exe (PID: 7760)
Create files in a temporary directory
- ~plczrlj.ibo (PID: 7988)
- ~plczrlj.tmp (PID: 8008)
- x4da978ee2ca82aae1b32f929670e5457f8d1d1fd8c2433a9ec7904d27da4a7c7.exe (PID: 7960)
- explorer.exe (PID: 4972)
- ICONPIN64.exe (PID: 7428)
- db910_20211220.exe (PID: 7564)
- db910_20211220.tmp (PID: 7536)
- unins000.exe (PID: 2224)
- _iu14D2N.tmp (PID: 7600)
- SetupHlp.exe (PID: 4920)
- CareScan.exe (PID: 7728)
- ICONPIN64.exe (PID: 5704)
- db1200_20240920.exe (PID: 7616)
- db1200_20240920.tmp (PID: 7700)
- unins000.exe (PID: 7696)
- _iu14D2N.tmp (PID: 3344)
- SetupHlp.exe (PID: 3656)
- ICONPIN64.exe (PID: 7488)
The sample compiled with english language support
- ~plczrlj.tmp (PID: 8008)
- HWiNFO.exe (PID: 8100)
- db910_20211220.tmp (PID: 7536)
- _iu14D2N.tmp (PID: 7600)
- db1200_20240920.tmp (PID: 7700)
- _iu14D2N.tmp (PID: 3344)
- AutoUpdate.exe (PID: 2740)
- AutoUpdate.exe (PID: 5180)
Reads the computer name
- ~plczrlj.tmp (PID: 8008)
- HWiNFO.exe (PID: 8100)
- DriverBooster.exe (PID: 8120)
- AutoUpdate.exe (PID: 3344)
- NoteIcon.exe (PID: 6084)
- AUpdate.exe (PID: 7272)
- FaultFixes.exe (PID: 7196)
- FaultFixes.exe (PID: 7176)
- db910_20211220.tmp (PID: 7536)
- _iu14D2N.tmp (PID: 7600)
- SetupHlp.exe (PID: 4920)
- InstStat.exe (PID: 1948)
- CareScan.exe (PID: 7728)
- DriverBooster.exe (PID: 7604)
- Manta.exe (PID: 5868)
- SetupHlp.exe (PID: 8108)
- AutoUpdate.exe (PID: 7952)
- Manta.exe (PID: 7116)
- Manta.exe (PID: 6456)
- SetupHlp.exe (PID: 7176)
- AUpdate.exe (PID: 7500)
- InstStat.exe (PID: 8188)
- db1200_20240920.tmp (PID: 7700)
- _iu14D2N.tmp (PID: 3344)
- InstStat.exe (PID: 2352)
- SetupHlp.exe (PID: 3656)
- SetupHlp.exe (PID: 6684)
- AutoUpdate.exe (PID: 2740)
- InstStat.exe (PID: 6096)
- Manta.exe (PID: 5876)
- ProductStat3.exe (PID: 4620)
- Manta.exe (PID: 4516)
- DriverBooster.exe (PID: 7968)
- NoteIcon.exe (PID: 1700)
- ProductStat3.exe (PID: 7972)
- ScanWinUpd.exe (PID: 8088)
- AutoUpdate.exe (PID: 5180)
- SetupHlp.exe (PID: 7704)
- AUpdate.exe (PID: 7760)
Creates files in the program directory
- ~plczrlj.tmp (PID: 8008)
- DriverBooster.exe (PID: 8120)
- x4da978ee2ca82aae1b32f929670e5457f8d1d1fd8c2433a9ec7904d27da4a7c7.exe (PID: 7960)
- ChangeIcon.exe (PID: 1872)
- AutoUpdate.exe (PID: 3344)
- RttHlp.exe (PID: 2092)
- SetupHlp.exe (PID: 4920)
- db910_20211220.tmp (PID: 7536)
- InstStat.exe (PID: 1948)
- CareScan.exe (PID: 7728)
- DriverBooster.exe (PID: 7604)
- Manta.exe (PID: 5868)
- AutoUpdate.exe (PID: 7952)
- SetupHlp.exe (PID: 8108)
- SetupHlp.exe (PID: 3656)
- db1200_20240920.tmp (PID: 7700)
- SetupHlp.exe (PID: 6684)
- AutoUpdate.exe (PID: 2740)
- ChangeIcon.exe (PID: 5176)
- DriverBooster.exe (PID: 7968)
- ProductStat3.exe (PID: 4620)
- ChangeIcon.exe (PID: 6640)
- AutoUpdate.exe (PID: 5180)
Creates files or folders in the user directory
- ~plczrlj.tmp (PID: 8008)
- DriverBooster.exe (PID: 8120)
- explorer.exe (PID: 4972)
- AUpdate.exe (PID: 7272)
- FaultFixes.exe (PID: 7176)
- InstStat.exe (PID: 1948)
- _iu14D2N.tmp (PID: 7600)
- AUpdate.exe (PID: 7500)
- FaultFixes.exe (PID: 7208)
- CareScan.exe (PID: 7728)
- _iu14D2N.tmp (PID: 3344)
- AutoUpdate.exe (PID: 2740)
Creates a software uninstall entry
- ~plczrlj.tmp (PID: 8008)
- db910_20211220.tmp (PID: 7536)
- db1200_20240920.tmp (PID: 7700)
The sample compiled with arabic language support
- ~plczrlj.tmp (PID: 8008)
- db910_20211220.tmp (PID: 7536)
- db1200_20240920.tmp (PID: 7700)
The process uses AutoIt
- x4da978ee2ca82aae1b32f929670e5457f8d1d1fd8c2433a9ec7904d27da4a7c7.exe (PID: 7960)
Process checks computer location settings
- ~plczrlj.tmp (PID: 8008)
- AutoUpdate.exe (PID: 3344)
- db910_20211220.tmp (PID: 7536)
- _iu14D2N.tmp (PID: 7600)
- AutoUpdate.exe (PID: 7952)
- _iu14D2N.tmp (PID: 3344)
- db1200_20240920.tmp (PID: 7700)
- AutoUpdate.exe (PID: 2740)
- DriverBooster.exe (PID: 7968)
Compiled with Borland Delphi (YARA)
- x4da978ee2ca82aae1b32f929670e5457f8d1d1fd8c2433a9ec7904d27da4a7c7.exe (PID: 7960)
- ~plczrlj.ibo (PID: 7988)
- ~plczrlj.tmp (PID: 8008)
- DriverBooster.exe (PID: 8120)
- db910_20211220.tmp (PID: 7536)
- CareScan.exe (PID: 7728)
- DriverBooster.exe (PID: 7604)
Reads the machine GUID from the registry
- DriverBooster.exe (PID: 8120)
- ICONPIN64.exe (PID: 7428)
- ICONPIN64.exe (PID: 5704)
- DriverBooster.exe (PID: 7604)
- AutoUpdate.exe (PID: 7952)
- ICONPIN64.exe (PID: 7488)
- AutoUpdate.exe (PID: 2740)
- InstStat.exe (PID: 6096)
- DriverBooster.exe (PID: 7968)
- ScanWinUpd.exe (PID: 8088)
- AutoUpdate.exe (PID: 5180)
- AUpdate.exe (PID: 7760)
Detects InnoSetup installer (YARA)
- ~plczrlj.ibo (PID: 7988)
- ~plczrlj.tmp (PID: 8008)
- db910_20211220.tmp (PID: 7536)
Checks proxy server information
- AUpdate.exe (PID: 7272)
- AUpdate.exe (PID: 7500)
- DriverBooster.exe (PID: 7604)
- AutoUpdate.exe (PID: 2740)
- slui.exe (PID: 7620)
TEAMVIEWER has been detected
- CareScan.exe (PID: 7728)
Reads CPU info
- DriverBooster.exe (PID: 7604)
- DriverBooster.exe (PID: 7968)
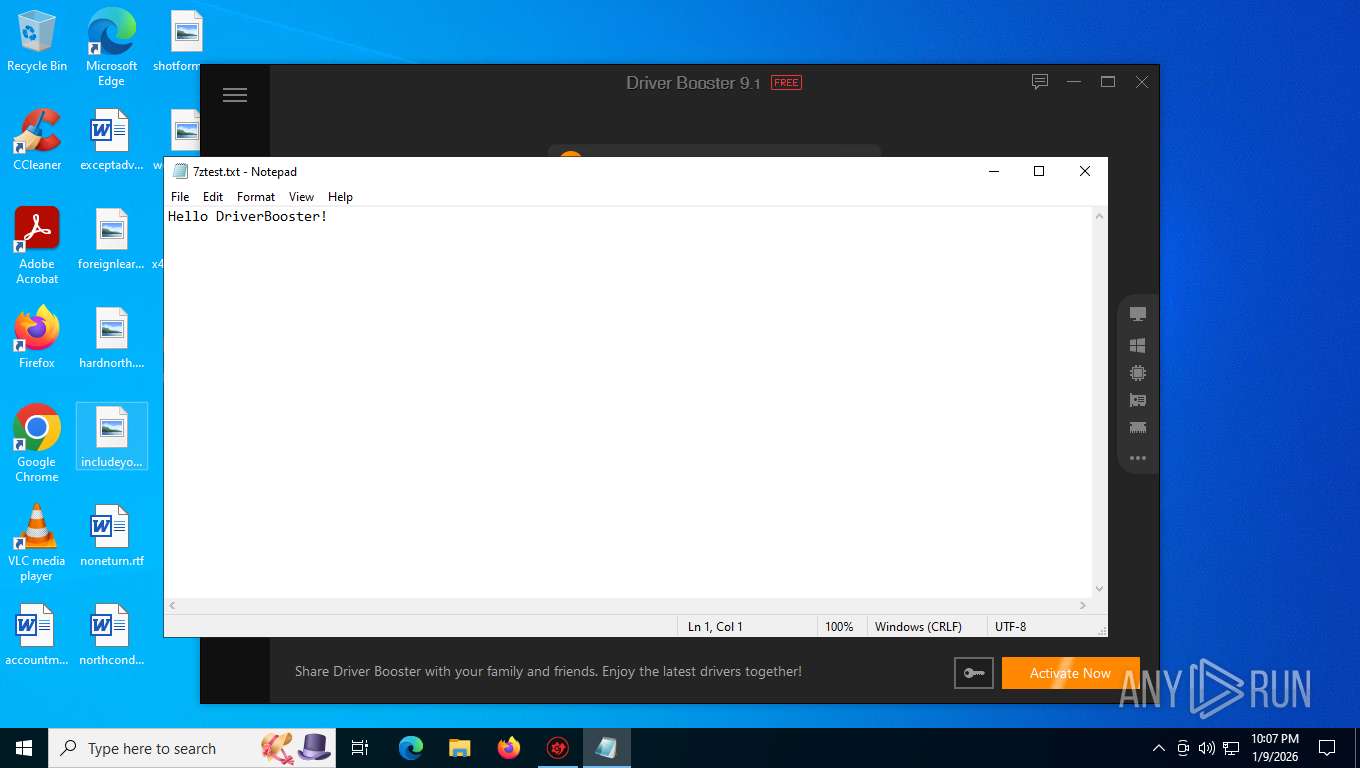
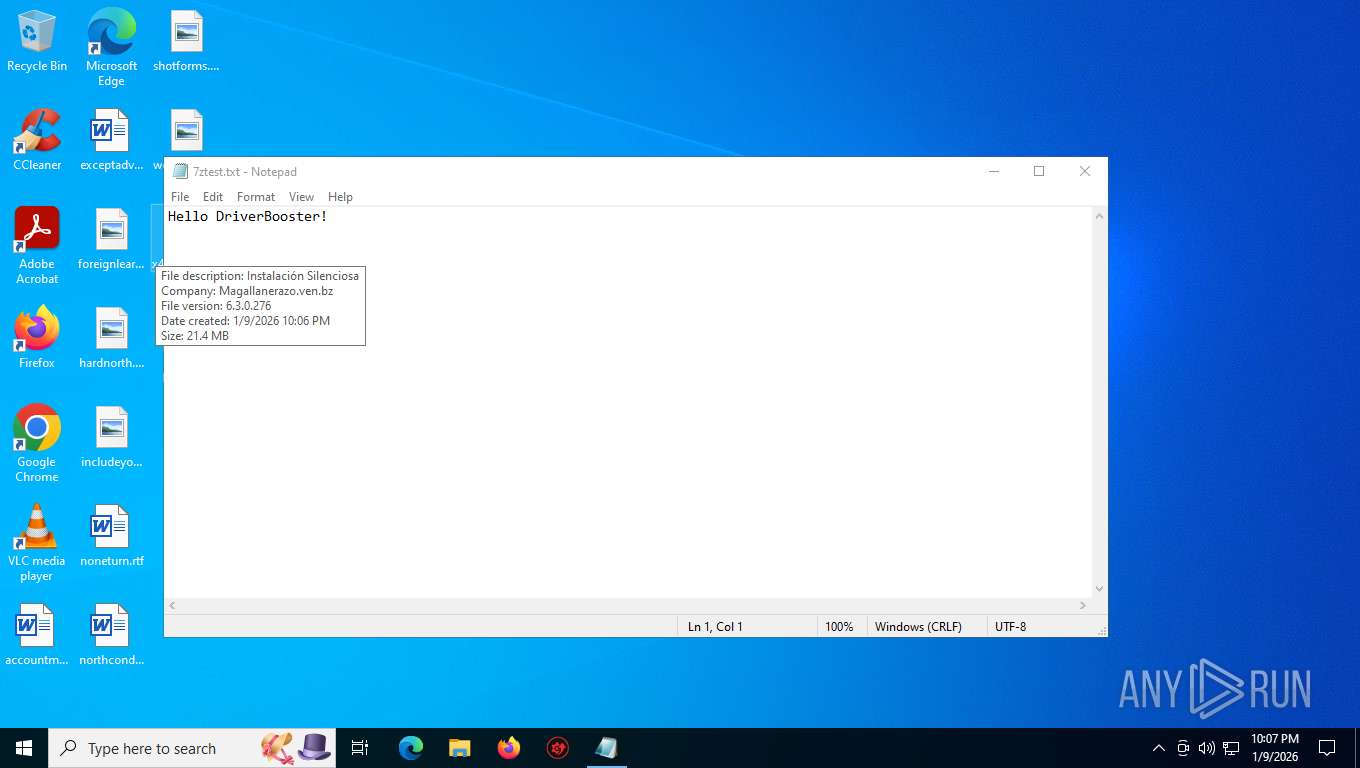
Manual execution by a user
- notepad.exe (PID: 7244)
Reads Microsoft Office registry keys
- CareScan.exe (PID: 7728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (39.8) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.4) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:20 14:53:51+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581632 |
| InitializedDataSize: | 21924352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2800a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.3.0.276 |
| ProductVersionNumber: | 6.3.0.276 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Unknown (200A) |
| CharacterSet: | Unicode |
| FileVersion: | 6.3.0.276 |
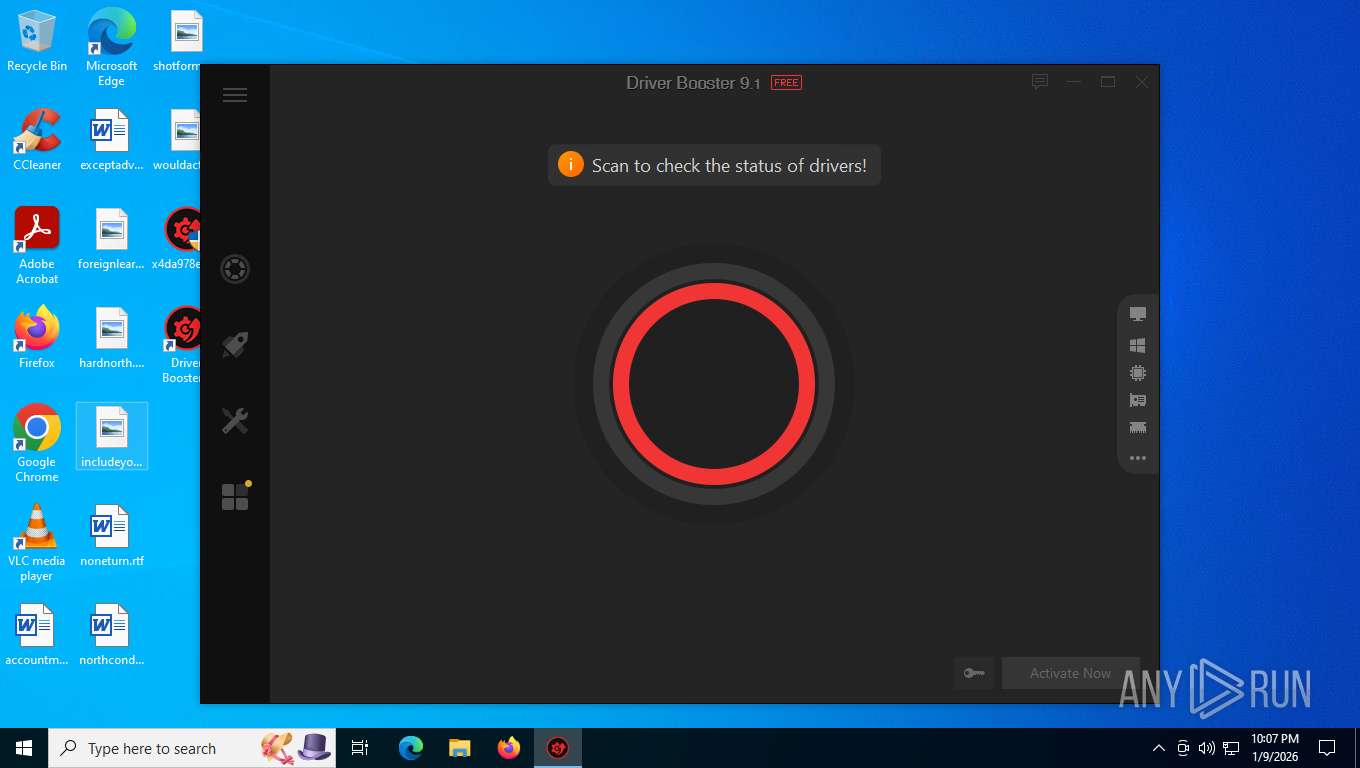
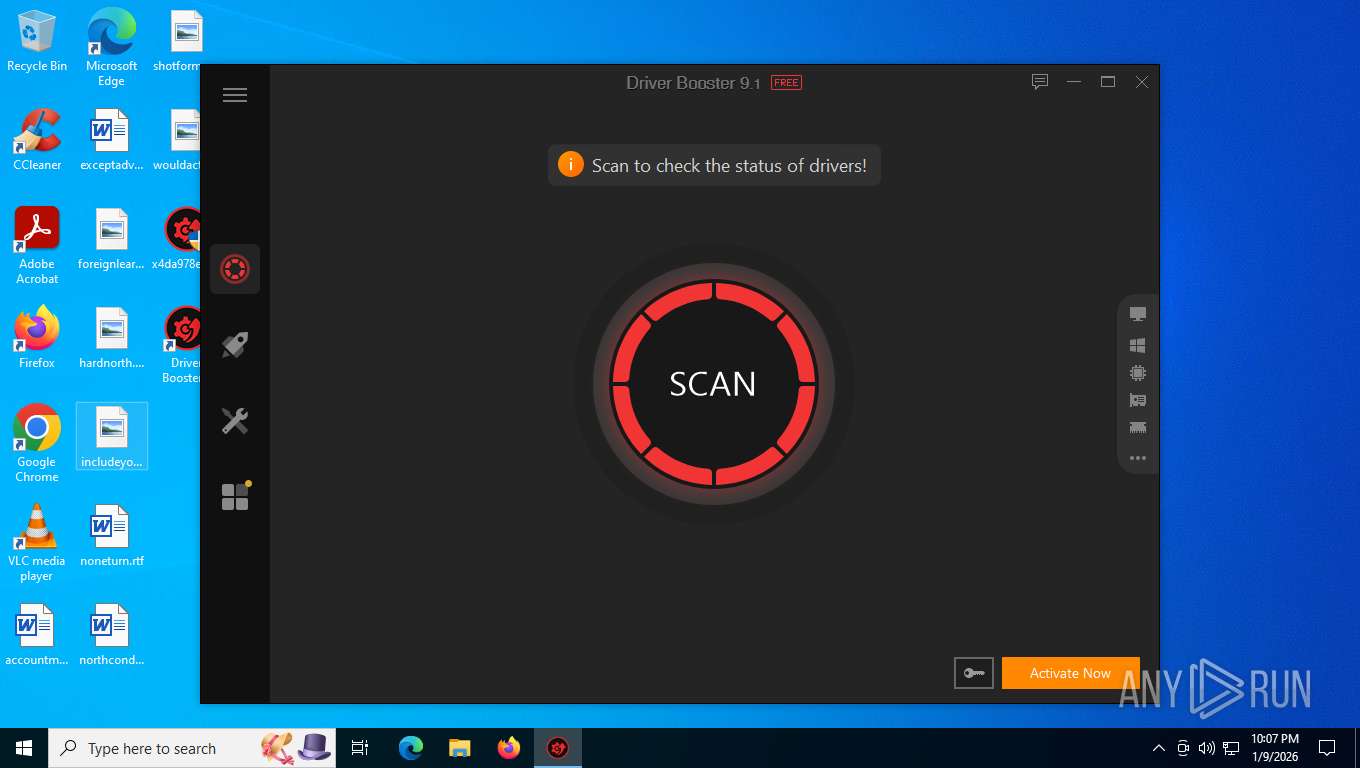
| Comments: | Driver Booster |
| FileDescription: | Instalación Silenciosa |
| LegalCopyright: | © 2019 Miguela_Pipo & Mafe |
| CompanyName: | Magallanerazo.ven.bz |
| ProductName: | IObit Driver Booster Pro |
| ProductVersion: | 6.3.0.276 |
Total processes
202
Monitored processes
75
Malicious processes
17
Suspicious processes
13
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1000 | "C:\Program Files (x86)\IObit\Driver Booster\6.3.0\SetupHlp.exe" /checkover | C:\Program Files (x86)\IObit\Driver Booster\6.3.0\SetupHlp.exe | — | DriverBooster.exe | |||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: Driver Booster Setup Helper Exit code: 0 Version: 6.2.0.92 Modules
| |||||||||||||||
| 1700 | "C:\Program Files (x86)\IObit\Driver Booster\12.0.0\NoteIcon.exe" "C:\Program Files (x86)\IObit\Driver Booster\12.0.0\DriverBooster.exe" | C:\Program Files (x86)\IObit\Driver Booster\12.0.0\NoteIcon.exe | DriverBooster.exe | ||||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: IObit NoteIcon Exit code: 0 Version: 4.3.0.7 Modules
| |||||||||||||||
| 1872 | "C:\Program Files (x86)\IObit\Driver Booster\6.3.0\ChangeIcon.exe" /0 "C:\Program Files (x86)\IObit\Driver Booster\6.3.0\Icons\Main\" | C:\Program Files (x86)\IObit\Driver Booster\6.3.0\ChangeIcon.exe | — | DriverBooster.exe | |||||||||||
User: admin Company: IObit. Integrity Level: HIGH Description: ChangeIcon Exit code: 0 Version: 1.0.0.166 Modules
| |||||||||||||||
| 1948 | "C:\Users\admin\AppData\Local\Temp\is-L3FG4.tmp\stat\InstStat.exe" /uninstall db6 /bigupgrade | C:\Users\admin\AppData\Local\Temp\is-L3FG4.tmp\stat\InstStat.exe | _iu14D2N.tmp | ||||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: Driver Booster InstStat Exit code: 0 Version: 6.0.0.334 Modules
| |||||||||||||||
| 1960 | "C:\Program Files (x86)\IObit\Driver Booster\12.0.0\RttHlp.exe" /winstdate | C:\Program Files (x86)\IObit\Driver Booster\12.0.0\RttHlp.exe | — | SetupHlp.exe | |||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: IObit RttHlp Exit code: 0 Version: 12.0.0.3 Modules
| |||||||||||||||
| 2092 | "C:\Program Files (x86)\IObit\Driver Booster\6.3.0\RttHlp.exe" /cnt | C:\Program Files (x86)\IObit\Driver Booster\6.3.0\RttHlp.exe | — | DriverBooster.exe | |||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: IObit RttHlp Exit code: 0 Version: 6.0.0.42 Modules
| |||||||||||||||
| 2224 | "C:\Program Files (x86)\IObit\Driver Booster\6.3.0\unins000.exe" /VerySilent /Uninstall /BigUpgrade /UninstallUpgrade | C:\Program Files (x86)\IObit\Driver Booster\6.3.0\unins000.exe | db910_20211220.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2352 | "C:\Users\admin\AppData\Local\Temp\is-J0KKS.tmp\stat\InstStat.exe" /uninstall db9 /bigupgrade /UninstallUpgrade | C:\Users\admin\AppData\Local\Temp\is-J0KKS.tmp\stat\InstStat.exe | _iu14D2N.tmp | ||||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: Driver Booster InstStat Exit code: 0 Version: 9.0.0.30 Modules
| |||||||||||||||
| 2568 | "C:\Program Files (x86)\IObit\Driver Booster\9.1.0\RttHlp.exe" /cnt | C:\Program Files (x86)\IObit\Driver Booster\9.1.0\RttHlp.exe | — | DriverBooster.exe | |||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: IObit RttHlp Exit code: 0 Version: 9.0.0.15 Modules
| |||||||||||||||
| 2740 | "C:\Program Files (x86)\IObit\Driver Booster\12.0.0\AutoUpdate.exe" /install | C:\Program Files (x86)\IObit\Driver Booster\12.0.0\AutoUpdate.exe | db1200_20240920.tmp | ||||||||||||
User: admin Company: IObit Integrity Level: HIGH Description: Driver Booster Updater Exit code: 0 Version: 12.0.0.434 Modules
| |||||||||||||||
Total events
59 291
Read events
59 006
Write events
245
Delete events
40
Modification events
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000040000000000000 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000030288 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456E9BC50E45F05DB4C86F7D791C25A96C7 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000030288 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8008) ~plczrlj.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\IObit\Driver Booster |
| Operation: | write | Name: | insur |
Value: other | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000302BC |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456E9BC50E45F05DB4C86F7D791C25A96C7 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000402BC |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456E9BC50E45F05DB4C86F7D791C25A96C7 | |||
| (PID) Process: | (8120) DriverBooster.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\IObit\Driver Booster |
| Operation: | write | Name: | Status |
Value: 1 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000402BC |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (8008) ~plczrlj.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Driver Booster_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.9 (u) | |||
| (PID) Process: | (8008) ~plczrlj.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Driver Booster_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\IObit\Driver Booster | |||
Executable files
473
Suspicious files
142
Text files
783
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7960 | x4da978ee2ca82aae1b32f929670e5457f8d1d1fd8c2433a9ec7904d27da4a7c7.exe | C:\Program Files (x86)\Common Files\~plczrlj.ibo | executable | |
MD5:A484EB4CDC7F8228D7919D8DBFE57A39 | SHA256:A0468940CB548D7C147BA6596233475E445FEA805B137594C2CD4E3D703F3789 | |||
| 8008 | ~plczrlj.tmp | C:\Users\admin\AppData\Local\Temp\is-ISJ1E.tmp\RdZone.dll | executable | |
MD5:61AD4BFDB2885D3497596DFAD2889C9A | SHA256:4AE86843FBB76C8A9BC3C364F85EC8EC1727556970E7ED5C2D31868E631C3162 | |||
| 8008 | ~plczrlj.tmp | C:\Users\admin\AppData\Roaming\IObit\Driver Booster\Config.ini | text | |
MD5:B266CD06B2BB39396274323B1D6E2E09 | SHA256:9FAB3E200539B4C110CEEBF0D58E1AEF60D77EB9D00FBE6313A33B01643E668F | |||
| 8008 | ~plczrlj.tmp | C:\Users\admin\AppData\Local\Temp\is-ISJ1E.tmp\DpInstX64.exe | executable | |
MD5:075BFD326D843832853BEC6DAF6DF977 | SHA256:BFCD58B3D713ABFD3EE4AC5C0B432EA986086E1583AAD982BBA06EFE29371C5C | |||
| 8008 | ~plczrlj.tmp | C:\Users\admin\AppData\Local\Temp\is-ISJ1E.tmp\AutoUpdate.exe | executable | |
MD5:341F711C20B0E55E919FD94970D93C23 | SHA256:9D16C35B87774BE8C4EABD971E7432ED6EBAD771A22FCE1ABF09CA910B91C9A4 | |||
| 8008 | ~plczrlj.tmp | C:\Users\admin\AppData\Local\Temp\is-ISJ1E.tmp\db_xp_support.bmp | image | |
MD5:E22EC5AC618A9AE0A74D3E532A9B03E8 | SHA256:39D2AB1131B927B986301A98CC64859EEB0A4A16FE4E6D18DB0F5345F2750DD4 | |||
| 8008 | ~plczrlj.tmp | C:\Users\admin\AppData\Local\Temp\is-ISJ1E.tmp\Scanner.dll | executable | |
MD5:7FAE01639DDD9C88DBC2C7258C25AFF4 | SHA256:C1039B0D7C4FFA621977B931803AE122C8317AEC7BADAA4B8F19CCA100B12558 | |||
| 8008 | ~plczrlj.tmp | C:\Program Files (x86)\IObit\Driver Booster\6.3.0\unins000.exe | executable | |
MD5:645A723945F3A30F0EF1AF6FF266670D | SHA256:357E13E2B7B7869A07A62BC9A8D2550ED9EC92F394A5CCDFC1A3B2B832BBD2E9 | |||
| 8008 | ~plczrlj.tmp | C:\Program Files (x86)\IObit\Driver Booster\6.3.0\EULA.rtf | text | |
MD5:690D87559F5BB3D8CDAB10279E79EEFF | SHA256:07D95E2DEEF703EEE991FAB15C2198F53D91BCDAC70D39CD220E166B97B53A59 | |||
| 8008 | ~plczrlj.tmp | C:\Users\admin\AppData\Local\Temp\is-ISJ1E.tmp\Register.dll | executable | |
MD5:5AB66648F7C41CFE0C0639753C97D1CF | SHA256:C82D0B3949683D73A30C82F9D1FC96F66A22E4BED167402FA0D037CB74BAC342 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
120
TCP/UDP connections
129
DNS requests
23
Threats
87
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8120 | DriverBooster.exe | POST | 200 | 23.48.23.36:80 | http://download.iobit.com/news/idb/v6/idb6_ln.dat | unknown | — | — | unknown |
3344 | AutoUpdate.exe | GET | 200 | 23.48.23.64:80 | http://update.iobit.com/infofiles/db6/db6_free.upt | unknown | — | — | unknown |
5156 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8120 | DriverBooster.exe | GET | 200 | 23.48.23.36:80 | http://download.iobit.com/news/images/new_04.png | unknown | — | — | unknown |
8120 | DriverBooster.exe | POST | 200 | 23.48.23.36:80 | http://download.iobit.com/news/version-check.ini | unknown | — | — | unknown |
3344 | AutoUpdate.exe | GET | 206 | 23.48.23.64:80 | http://update.iobit.com/infofiles/db6/freeware_ac.upt | unknown | — | — | unknown |
3344 | AutoUpdate.exe | GET | 206 | 23.48.23.64:80 | http://update.iobit.com/infofiles/db6/db6_free.upt | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5156 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5156 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3344 | AutoUpdate.exe | 23.48.23.64:80 | update.iobit.com | AKAMAI-ASN1 | NL | whitelisted |
8120 | DriverBooster.exe | 23.48.23.36:80 | download.iobit.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
update.iobit.com |
| whitelisted |
download.iobit.com |
| whitelisted |
ascstats.iobit.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.aws.iobit.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3344 | AutoUpdate.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
7952 | AutoUpdate.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
7952 | AutoUpdate.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
7952 | AutoUpdate.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
7952 | AutoUpdate.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
7952 | AutoUpdate.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
7952 | AutoUpdate.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
7952 | AutoUpdate.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
7952 | AutoUpdate.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
7952 | AutoUpdate.exe | Potentially Bad Traffic | ET HUNTING Suspicious Mozilla User-Agent - Likely Fake (Mozilla/4.0) |
Process | Message |
|---|---|
explorer.exe | vItemVerbs.Item(i)Run as &administrator |
explorer.exe | vItemVerbs.Item(i)Troubleshoot compatibilit&y |
explorer.exe | vItemVerbs.Item(i)&Pin to Start |
explorer.exe | vItemVerbs.Item(i)Edit with &Notepad++ |
explorer.exe | vItemVerbs.Item(i)Share |
explorer.exe | vItemVerbs.Item(i)&Add to archive... |
explorer.exe | vItemVerbs.Item(i)Add &to "DriverBooster.rar" |
explorer.exe | vItemVerbs.Item(i)Compress and email... |
explorer.exe | vItemVerbs.Item(i)Compress to "DriverBooster.rar" and email |
explorer.exe | vItemVerbs.Item(i)Pin to tas&kbar |