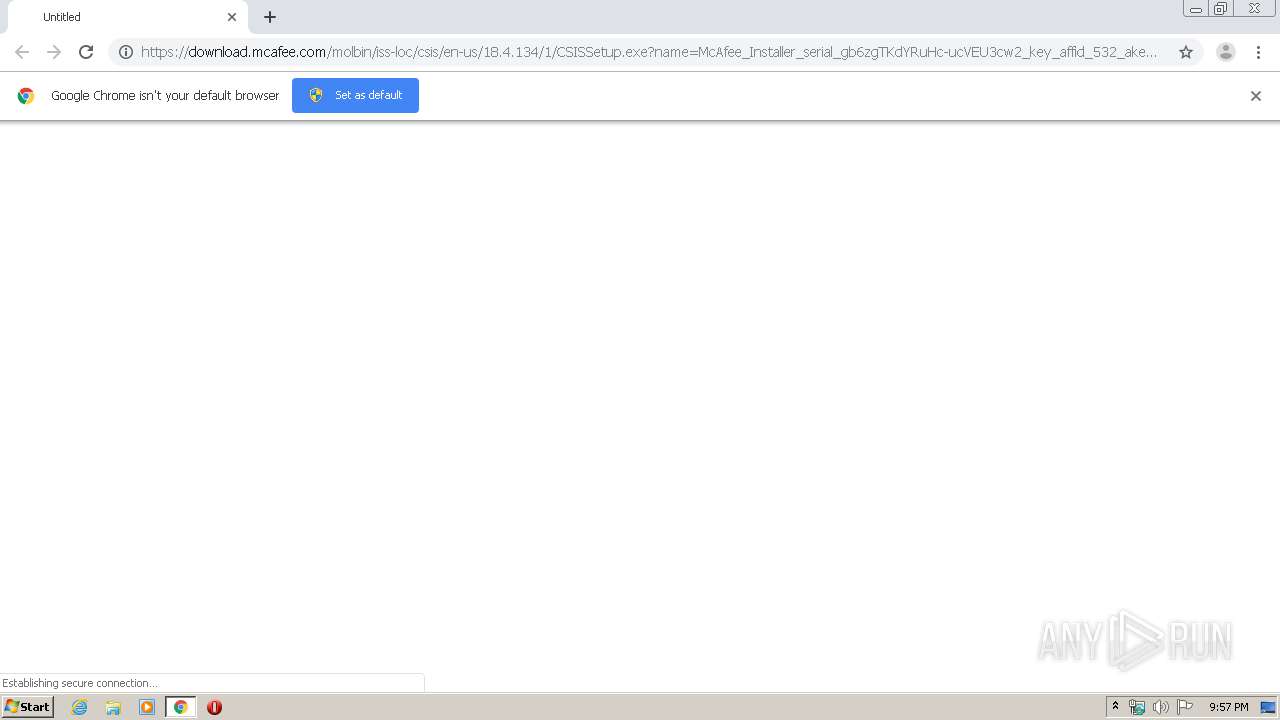
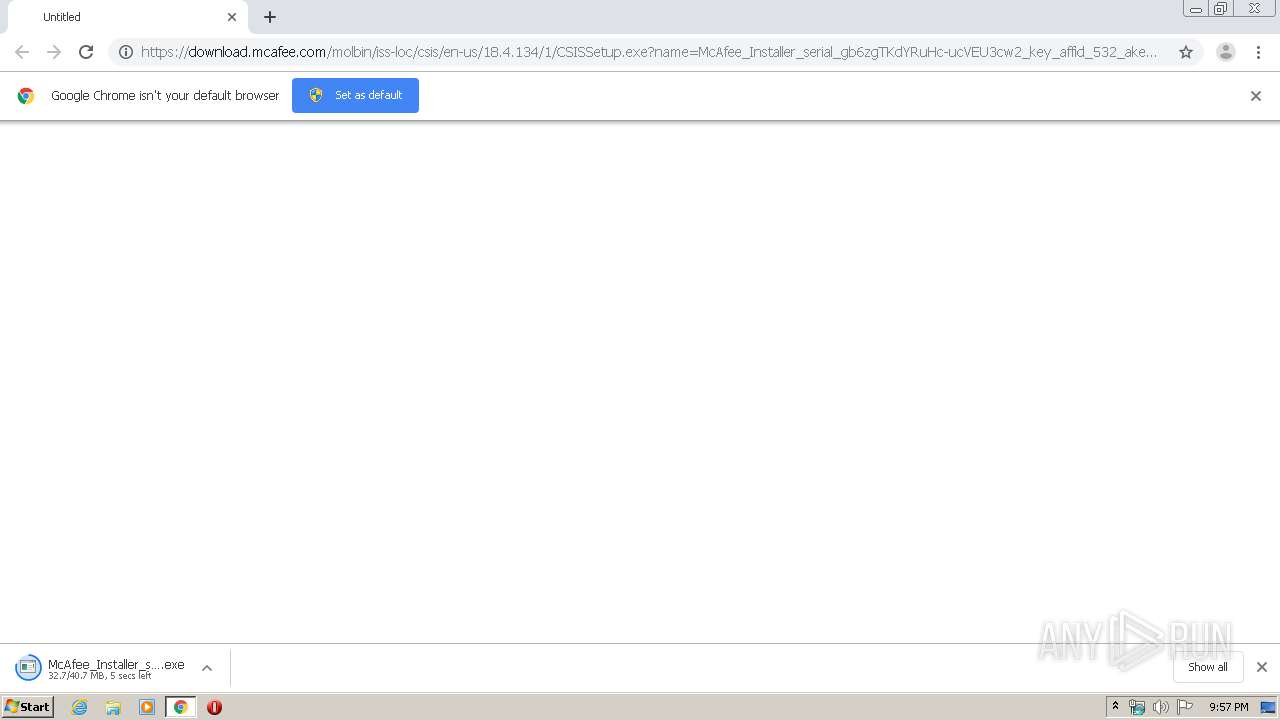
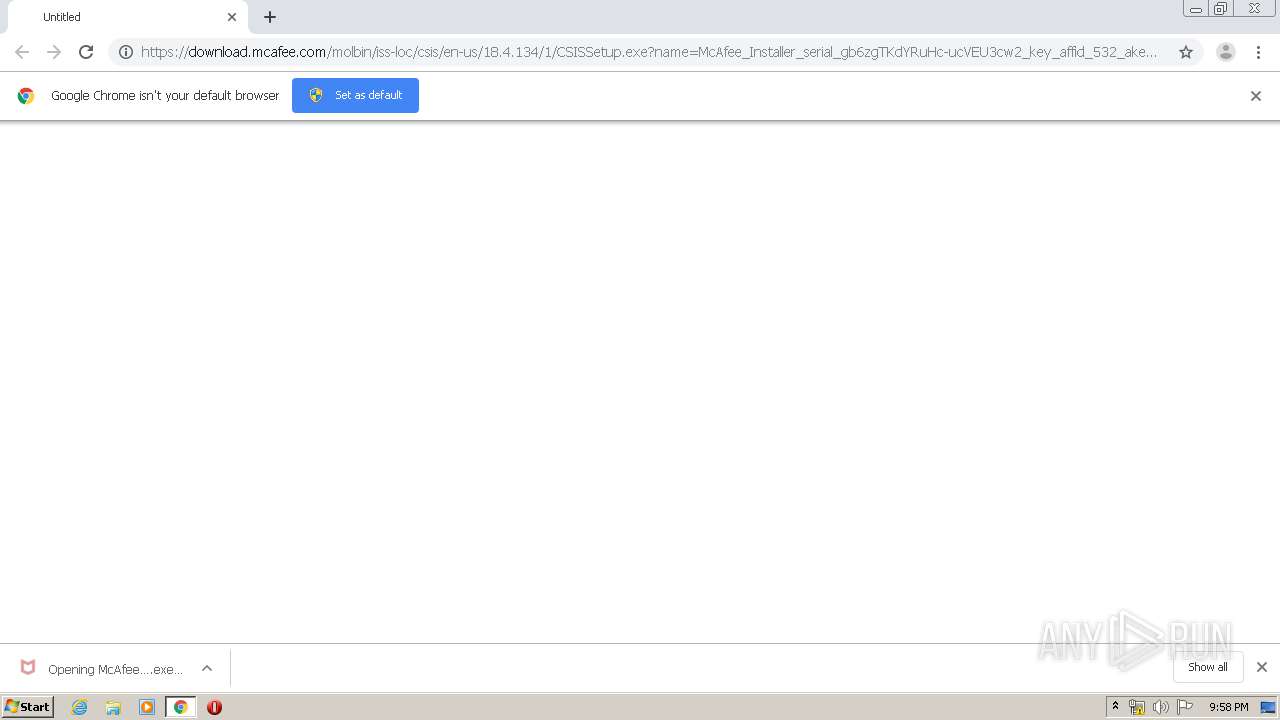
| URL: | https://download.mcafee.com/molbin/iss-loc/csis/en-us/18.4.134/1/CSISSetup.exe?name=McAfee_Installer_serial_gb6zgTKdYRuHc-ucVEU3cw2_key_affid_532_akey.exe |
| Full analysis: | https://app.any.run/tasks/f25a7c6b-c4b1-4c03-a08e-145361414241 |
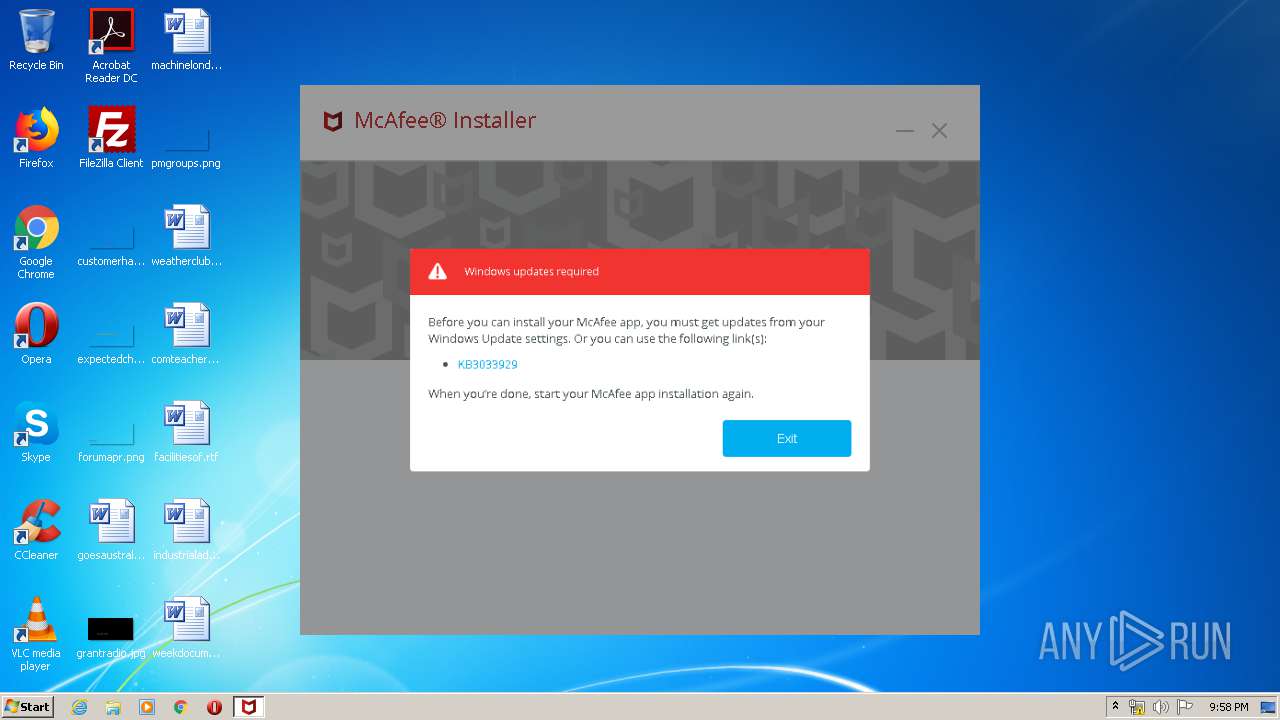
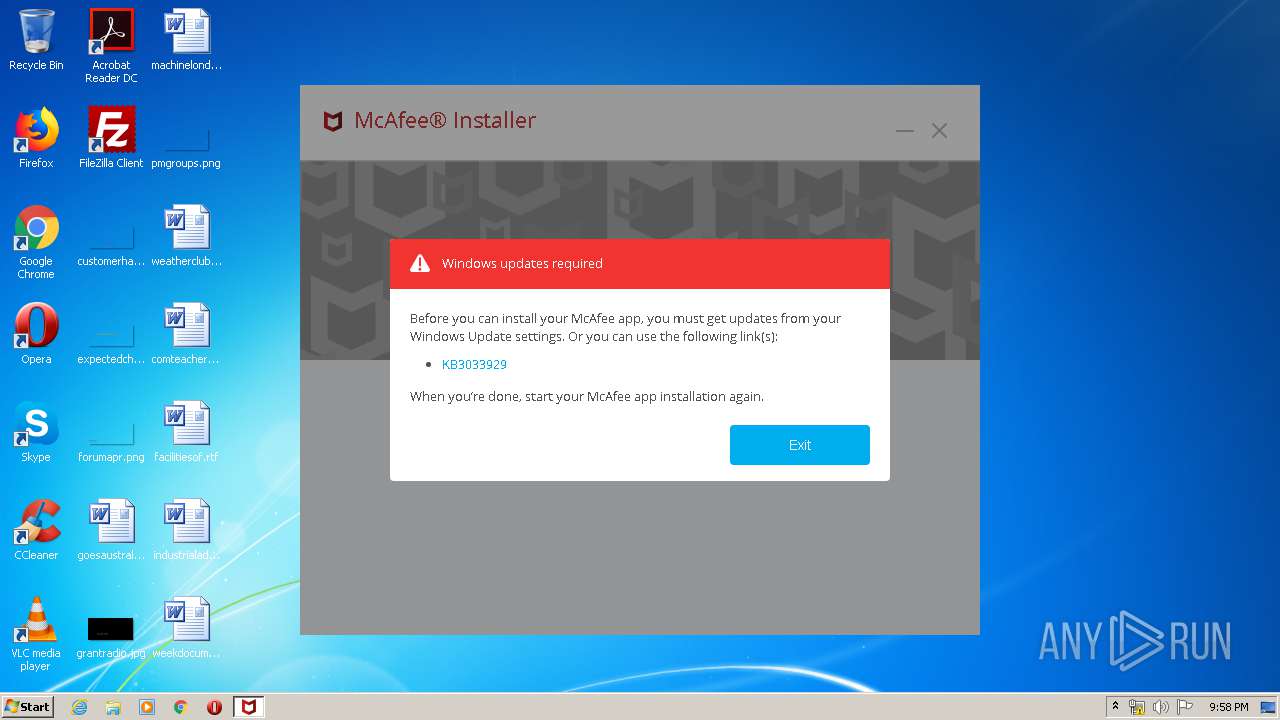
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2020, 21:56:47 |
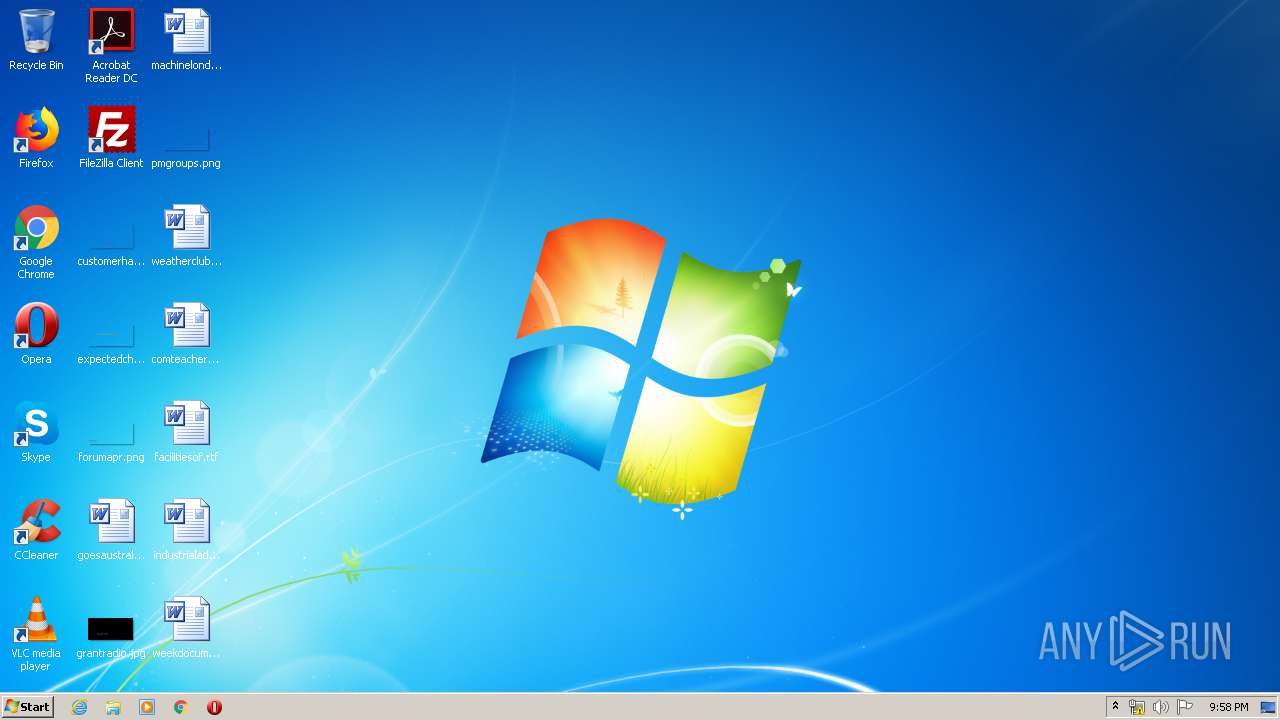
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 05F5D664666ABE4CE9BB3031C72BBC39 |
| SHA1: | CDC77B5D63D332E1B94D6235FF3D7CA3F00A3242 |
| SHA256: | 4D99CC9ABB28D6B18FCB6E4A6855DD46D3D2F4B15B5C24045485C66CFA85C80F |
| SSDEEP: | 3:N8SEl3AyKIT0KKGQPdF2yk/wIKvpLWREgXimCHOox0tGMjGAz8J:2SK5KIToPdfk/wIKvMRBXNCRx07jx8J |
MALICIOUS
Application was dropped or rewritten from another process
- McAfee_Installer_serial_gb6zgTKdYRuHc-ucVEU3cw2_key_affid_532_akey.exe (PID: 2688)
- Install.exe (PID: 3296)
- McAfee_Installer_serial_gb6zgTKdYRuHc-ucVEU3cw2_key_affid_532_akey.exe (PID: 3112)
- delegate.exe (PID: 3696)
- mfehidin.exe (PID: 2212)
- McVscIns.exe (PID: 3540)
- mfemms.exe (PID: 1632)
Changes settings of System certificates
- Install.exe (PID: 3296)
- mfehidin.exe (PID: 2212)
- McAfee_Installer_serial_gb6zgTKdYRuHc-ucVEU3cw2_key_affid_532_akey.exe (PID: 3112)
Loads dropped or rewritten executable
- Install.exe (PID: 3296)
- delegate.exe (PID: 3696)
- mfehidin.exe (PID: 2212)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2804)
- McAfee_Installer_serial_gb6zgTKdYRuHc-ucVEU3cw2_key_affid_532_akey.exe (PID: 3112)
- mfehidin.exe (PID: 2212)
Creates files in the program directory
- Install.exe (PID: 3296)
- McAfee_Installer_serial_gb6zgTKdYRuHc-ucVEU3cw2_key_affid_532_akey.exe (PID: 3112)
- delegate.exe (PID: 3696)
- mfehidin.exe (PID: 2212)
Adds / modifies Windows certificates
- Install.exe (PID: 3296)
- mfehidin.exe (PID: 2212)
- McAfee_Installer_serial_gb6zgTKdYRuHc-ucVEU3cw2_key_affid_532_akey.exe (PID: 3112)
Reads Internet Cache Settings
- Install.exe (PID: 3296)
Creates COM task schedule object
- McVscIns.exe (PID: 3540)
Executed as Windows Service
- mfemms.exe (PID: 1632)
Creates files in the Windows directory
- mfehidin.exe (PID: 2212)
Removes files from Windows directory
- mfehidin.exe (PID: 2212)
Creates files in the driver directory
- mfehidin.exe (PID: 2212)
Creates or modifies windows services
- mfehidin.exe (PID: 2212)
INFO
Reads the hosts file
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2804)
- Install.exe (PID: 3296)
- chrome.exe (PID: 3248)
- chrome.exe (PID: 2764)
Reads settings of System Certificates
- chrome.exe (PID: 2752)
- McAfee_Installer_serial_gb6zgTKdYRuHc-ucVEU3cw2_key_affid_532_akey.exe (PID: 3112)
- Install.exe (PID: 3296)
- mfehidin.exe (PID: 2212)
- chrome.exe (PID: 2764)
Reads Internet Cache Settings
- chrome.exe (PID: 2804)
Dropped object may contain Bitcoin addresses
- McAfee_Installer_serial_gb6zgTKdYRuHc-ucVEU3cw2_key_affid_532_akey.exe (PID: 3112)
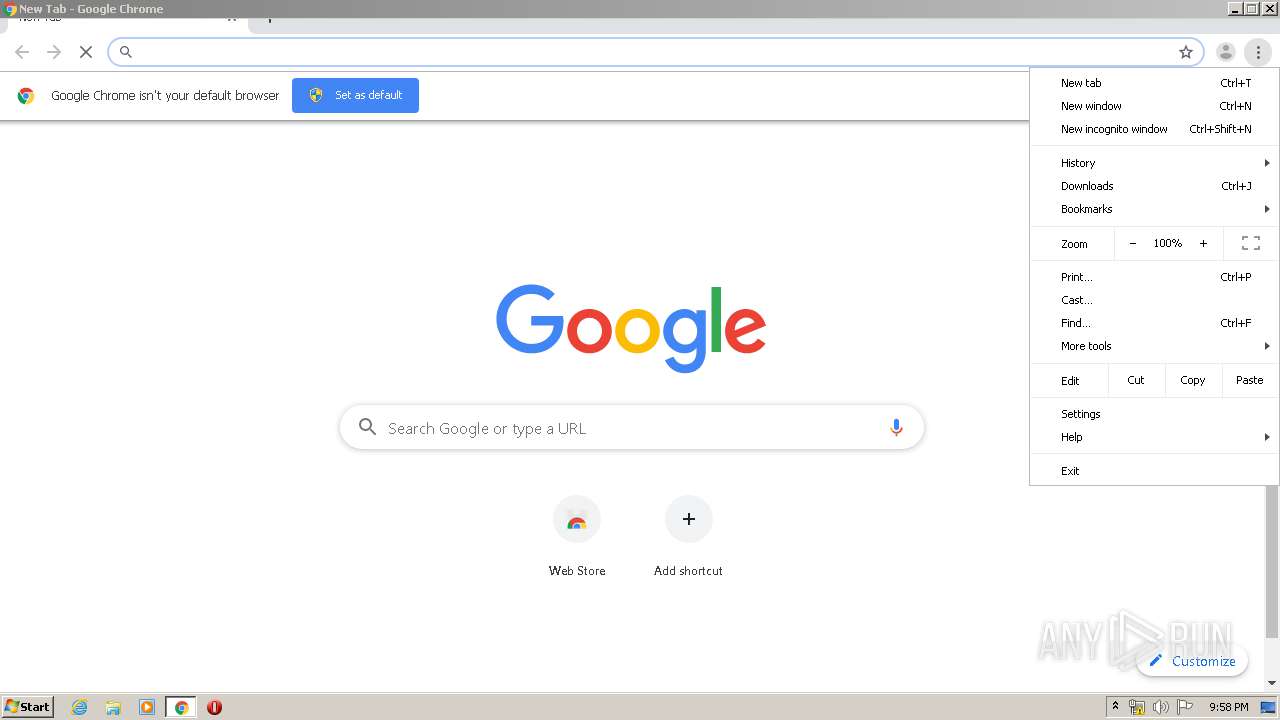
Application launched itself
- chrome.exe (PID: 3248)
- chrome.exe (PID: 2804)
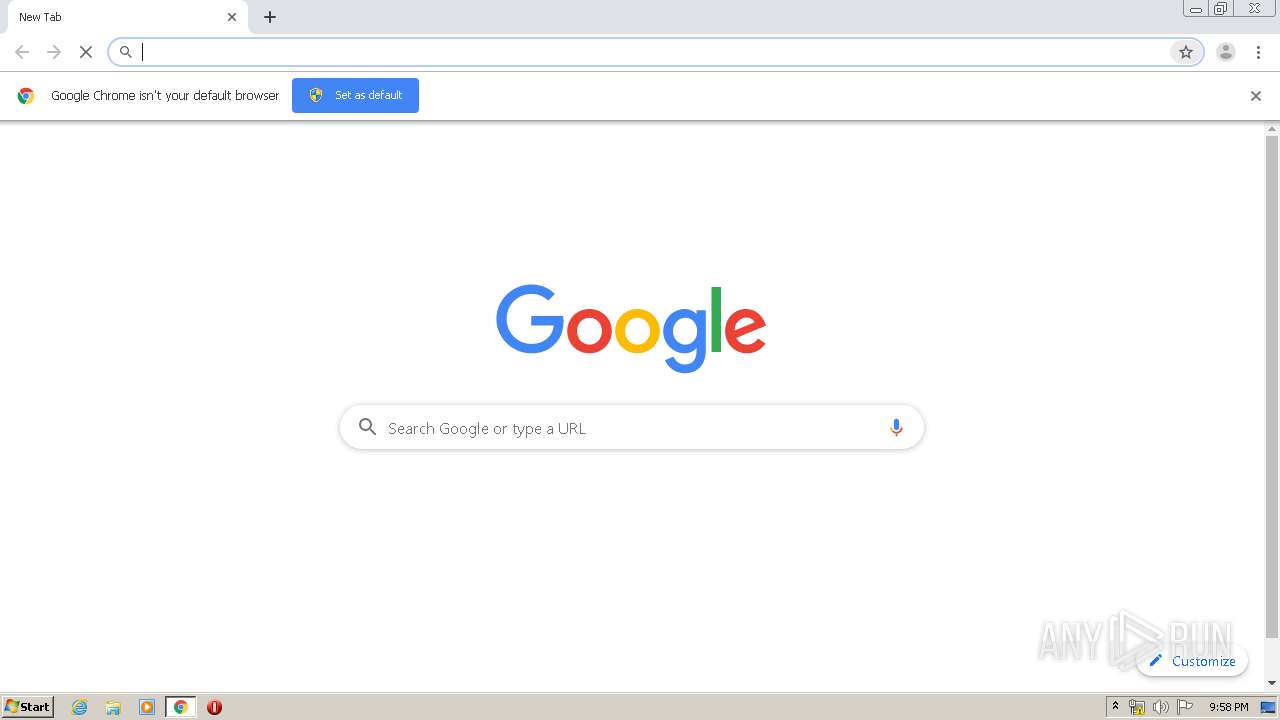
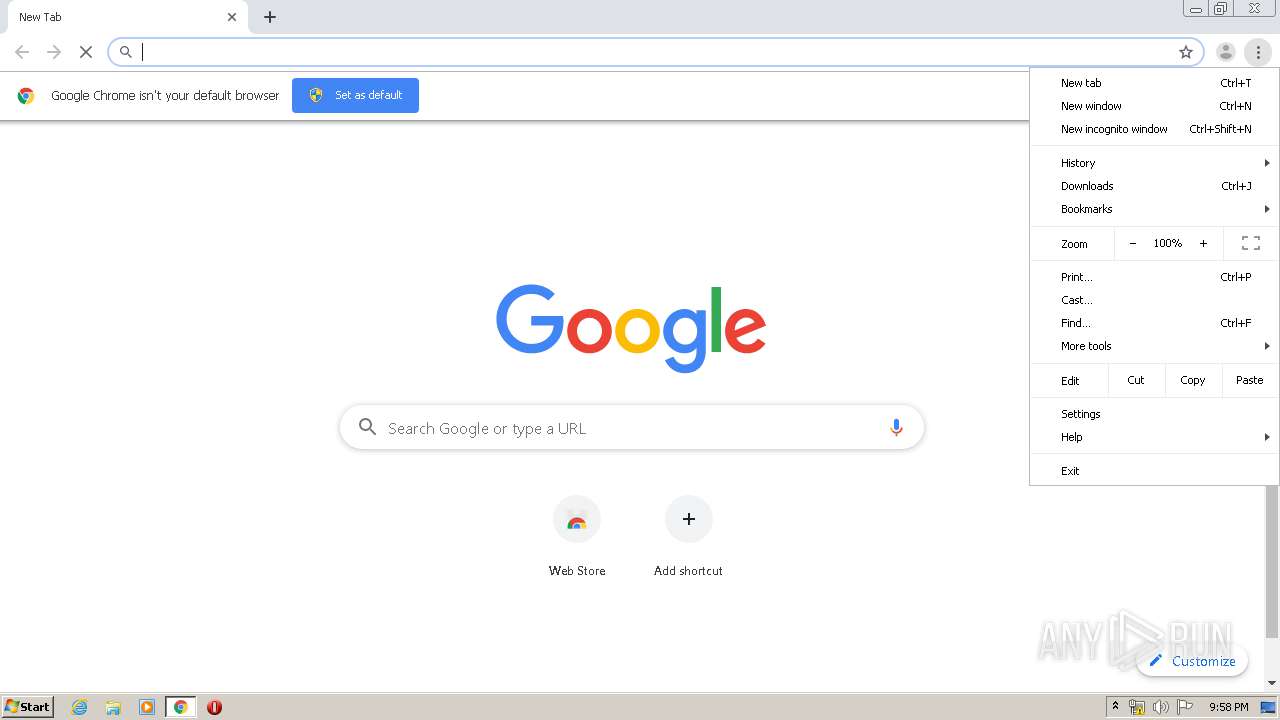
Manual execution by user
- chrome.exe (PID: 3248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
28
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,12665795242614146256,16957560209056292568,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14991113926228044536 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11378337207423122489 --mojo-platform-channel-handle=3544 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Common Files\McAfee\SystemCore\mfemms.exe" | C:\Program Files\Common Files\McAfee\SystemCore\mfemms.exe | services.exe | ||||||||||||
User: SYSTEM Company: McAfee, LLC Integrity Level: SYSTEM Description: McAfee Management Service Exit code: 0 Version: SYSCORE.20.1.0.177 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,12665795242614146256,16957560209056292568,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14738473022719764399 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2540 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2212 | C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\VSCore\mfehidin.exe -i -g {308C1AD7-765B-4A17-B25B-D415F07357F3} -mfetrust_killbit -etl C:\ProgramData\McAfee\MCLOGS\mfehidin001.etl -l C:\ProgramData\McAfee\MCLOGS\mfehidin001.log | C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\VSCore\mfehidin.exe | McVscIns.exe | ||||||||||||
User: admin Company: McAfee, LLC Integrity Level: HIGH Description: McAfee System Core Installer Exit code: 0 Version: SYSCORE.20.1.0.184 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,12665795242614146256,16957560209056292568,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=947356341005080532 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5444575908759735061 --mojo-platform-channel-handle=976 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16927237434041628048 --mojo-platform-channel-handle=1088 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2688 | "C:\Users\admin\Downloads\McAfee_Installer_serial_gb6zgTKdYRuHc-ucVEU3cw2_key_affid_532_akey.exe" | C:\Users\admin\Downloads\McAfee_Installer_serial_gb6zgTKdYRuHc-ucVEU3cw2_key_affid_532_akey.exe | — | chrome.exe | |||||||||||
User: admin Company: McAfee, LLC. Integrity Level: MEDIUM Description: McAfee CSIS Installer Exit code: 3221226540 Version: 18.4.134.0 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8362181689479168979 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 534
Read events
1 731
Write events
1 756
Delete events
47
Modification events
| (PID) Process: | (2804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2804-13229301421408750 |
Value: 259 | |||
| (PID) Process: | (2804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2804) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2804-13229301421408750 |
Value: 259 | |||
Executable files
159
Suspicious files
74
Text files
238
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E768DAD-AF4.pma | — | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c662f721-fd3a-4c7a-967d-b4724579b30b.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa66ceb.TMP | text | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66c4f.TMP | text | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66e62.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
26
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3696 | delegate.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3696 | delegate.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3696 | delegate.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
2212 | mfehidin.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3296 | Install.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.7 Kb | whitelisted |
3296 | Install.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.7 Kb | whitelisted |
3296 | Install.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
2212 | mfehidin.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3296 | Install.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEQCu%2F8JZxQ3BalXFvP7Nih9m | US | der | 728 b | whitelisted |
3696 | delegate.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2752 | chrome.exe | 95.101.184.108:443 | download.mcafee.com | CW Vodafone Group PLC | — | unknown |
2752 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 216.239.38.117:443 | www.google.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3296 | Install.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3296 | Install.exe | 95.101.185.24:443 | sadownload.mcafee.com | CW Vodafone Group PLC | — | unknown |
3696 | delegate.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3296 | Install.exe | 95.101.184.108:443 | download.mcafee.com | CW Vodafone Group PLC | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.mcafee.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
sadownload.mcafee.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
prd-mcafee-mosaic-pub.azurewebsites.net |
| suspicious |
Threats
Process | Message |
|---|---|
McVscIns.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\McVscIns.exe loading C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
McVscIns.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory
|
McVscIns.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\McVscIns.exe loading C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
McVscIns.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory
|
McVscIns.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory
|
McVscIns.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\McVscIns.exe loading C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
McVscIns.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory
|
McVscIns.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\McVscIns.exe loading C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
McVscIns.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\McVscIns.exe loading C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
McVscIns.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\McVscIns.exe loading C:\Users\admin\AppData\Local\Temp\McInstallTemp\SelfProtect\Win32\mfeaaca.dll, WinVerifyTrust failed with 80092003
|