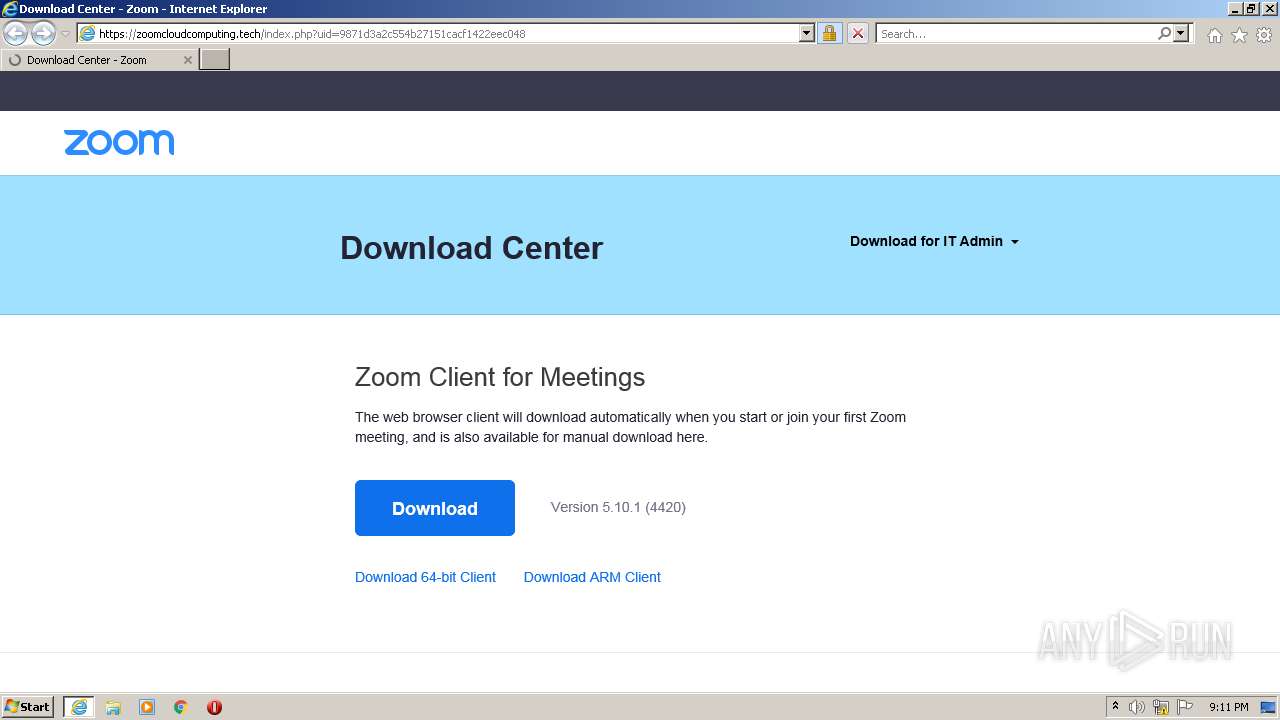
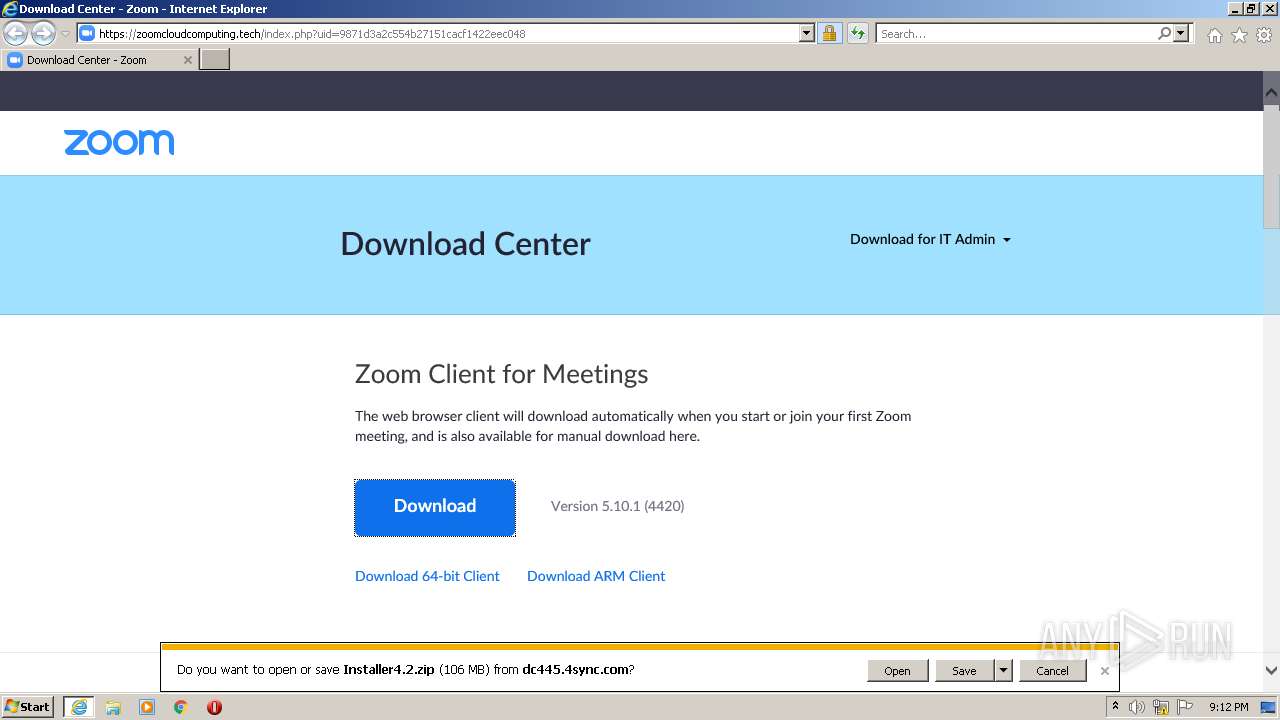
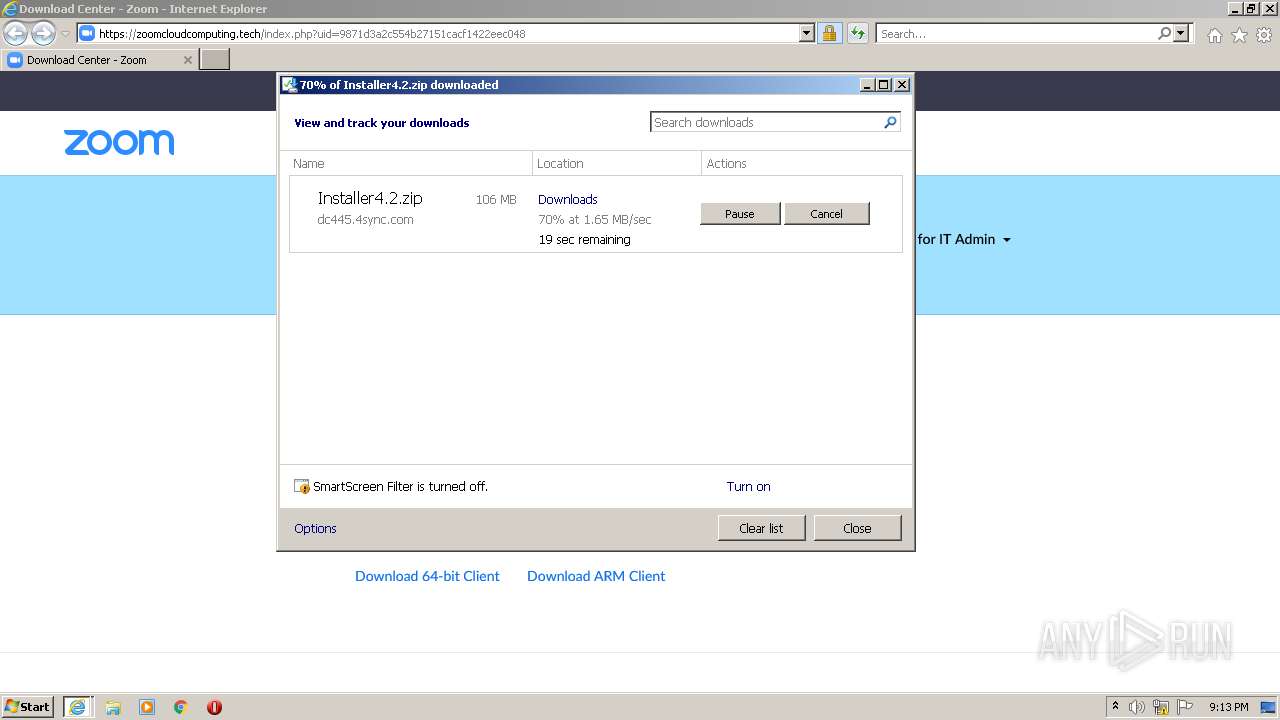
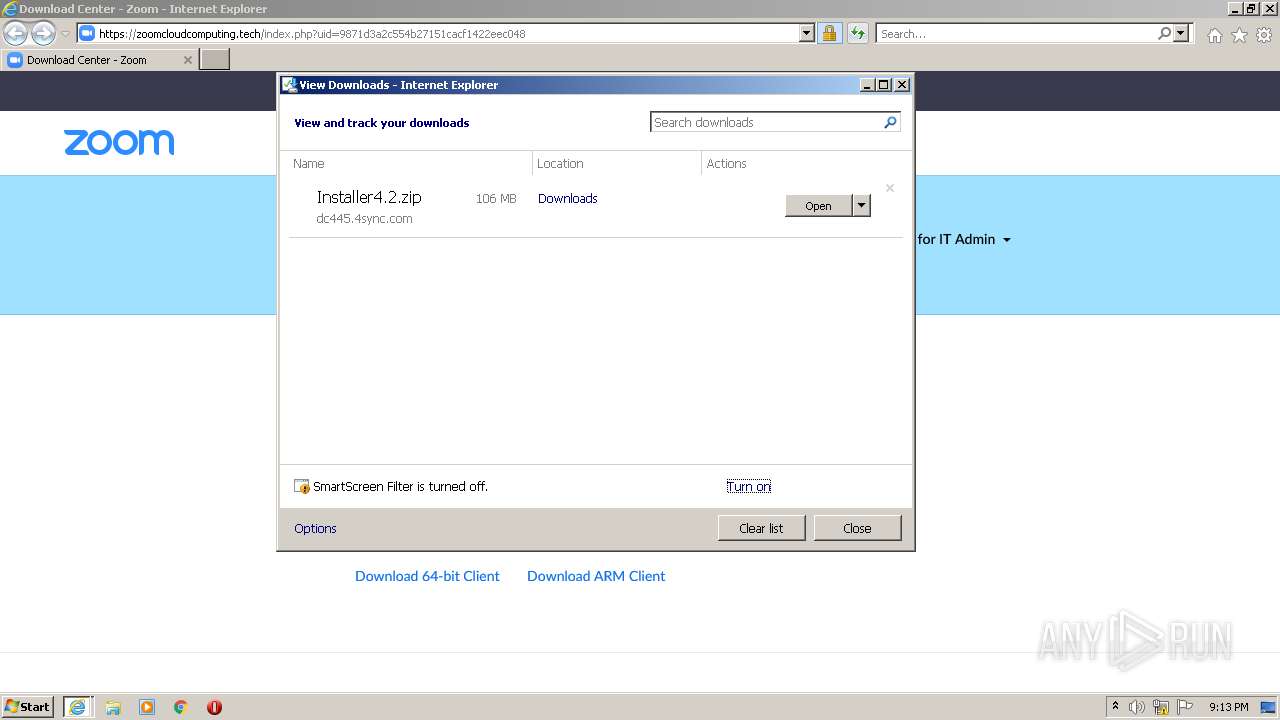
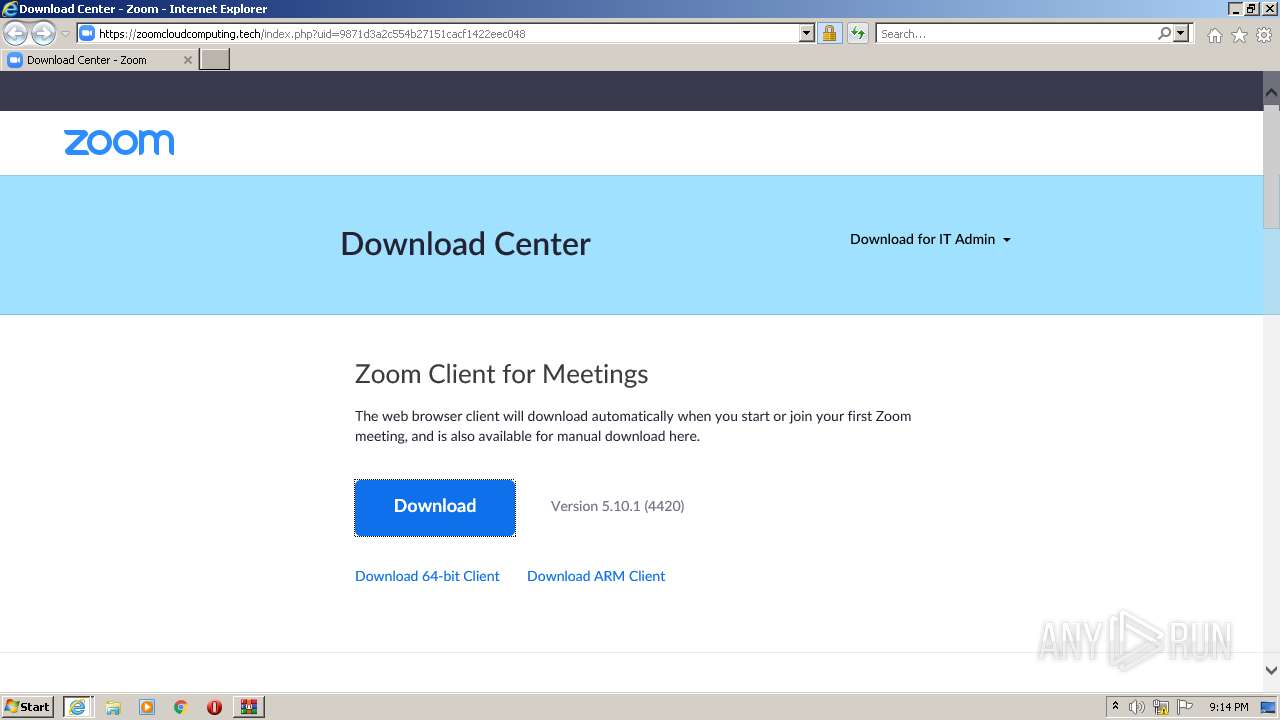
| URL: | https://zoomcloudcomputing.tech/index.php?uid=9871d3a2c554b27151cacf1422eec048 |
| Full analysis: | https://app.any.run/tasks/ae954e42-561b-4e82-85a4-474114c417fb |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 20:11:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BB20D1802E29F7BE68F9912101CB0A19 |
| SHA1: | 79781CF7242E654CD8F880147F91C37859B50D85 |
| SHA256: | 4D8B4F6C4C354305618E540C9EDAA94A62199A71EEDA4CBC7D85553A8E51D5B9 |
| SSDEEP: | 3:N88GJKfT6M2iM1AbHbAxdhwRHXnBKww:28VfT6ZvkHNRHXBI |
MALICIOUS
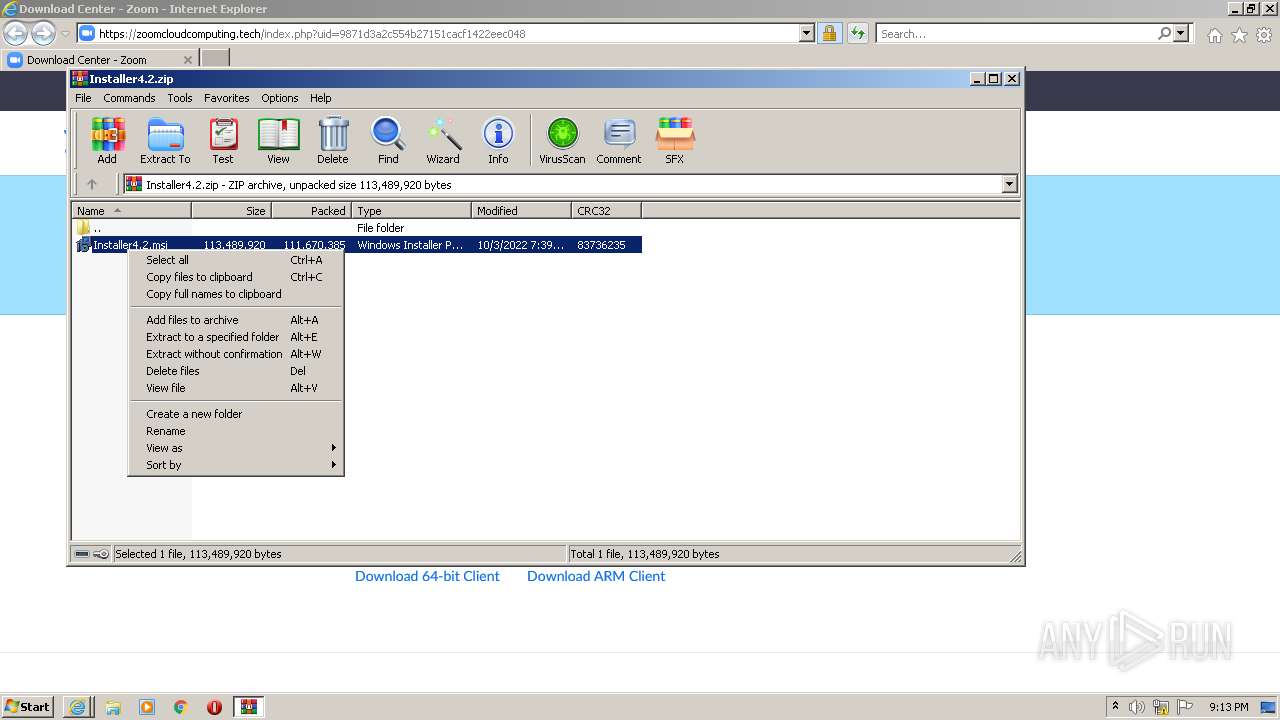
Drops executable file immediately after starts
- msiexec.exe (PID: 2784)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2088)
- msiexec.exe (PID: 2784)
- MsiExec.exe (PID: 2676)
Reads the computer name
- WinRAR.exe (PID: 2088)
- MsiExec.exe (PID: 2676)
- msiexec.exe (PID: 2784)
Reads the Windows organization settings
- msiexec.exe (PID: 3608)
- msiexec.exe (PID: 2784)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3608)
- msiexec.exe (PID: 2784)
Executed as Windows Service
- vssvc.exe (PID: 3820)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1180)
Reads Environment values
- powershell.exe (PID: 1844)
- vssvc.exe (PID: 3820)
- MsiExec.exe (PID: 2676)
Creates a directory in Program Files
- msiexec.exe (PID: 2784)
Executes PowerShell scripts
- MsiExec.exe (PID: 2676)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2784)
Drops a file with a compile date too recent
- msiexec.exe (PID: 2784)
INFO
Reads the computer name
- iexplore.exe (PID: 3068)
- iexplore.exe (PID: 1180)
- msiexec.exe (PID: 3608)
- vssvc.exe (PID: 3820)
- powershell.exe (PID: 1844)
Application launched itself
- iexplore.exe (PID: 3068)
- msiexec.exe (PID: 2784)
Checks supported languages
- iexplore.exe (PID: 3068)
- iexplore.exe (PID: 1180)
- msiexec.exe (PID: 3608)
- vssvc.exe (PID: 3820)
- powershell.exe (PID: 1844)
Changes internet zones settings
- iexplore.exe (PID: 3068)
Reads settings of System Certificates
- iexplore.exe (PID: 1180)
- iexplore.exe (PID: 3068)
- msiexec.exe (PID: 3608)
- msiexec.exe (PID: 2784)
- powershell.exe (PID: 1844)
Reads internet explorer settings
- iexplore.exe (PID: 1180)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3068)
Checks Windows Trust Settings
- iexplore.exe (PID: 3068)
- iexplore.exe (PID: 1180)
- msiexec.exe (PID: 2784)
- msiexec.exe (PID: 3608)
- powershell.exe (PID: 1844)
Changes settings of System certificates
- iexplore.exe (PID: 3068)
Creates files in the user directory
- iexplore.exe (PID: 1180)
- iexplore.exe (PID: 3068)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3068)
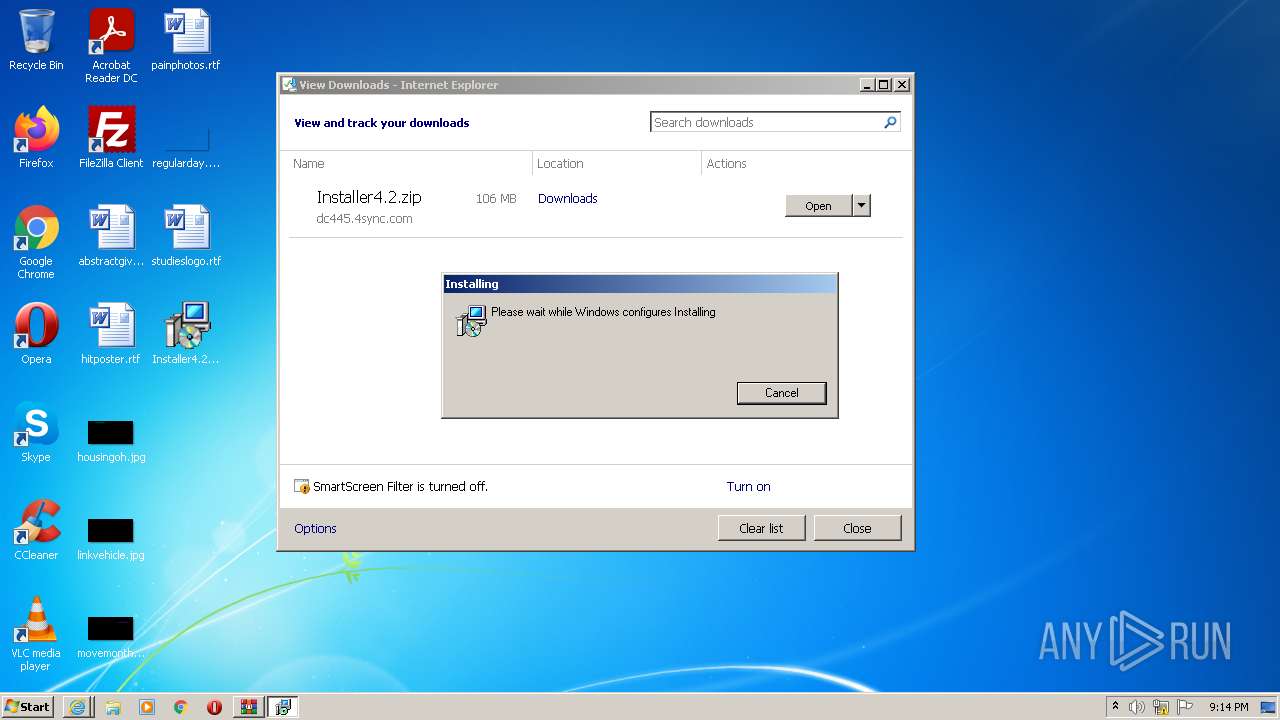
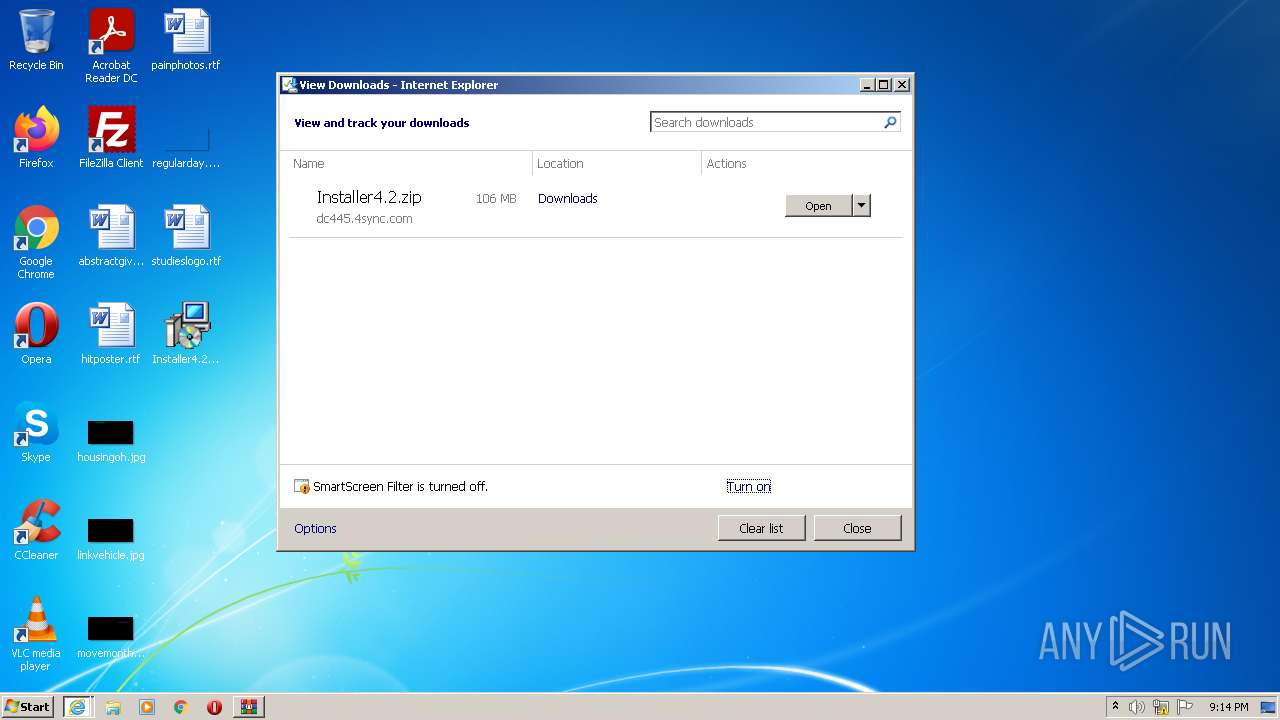
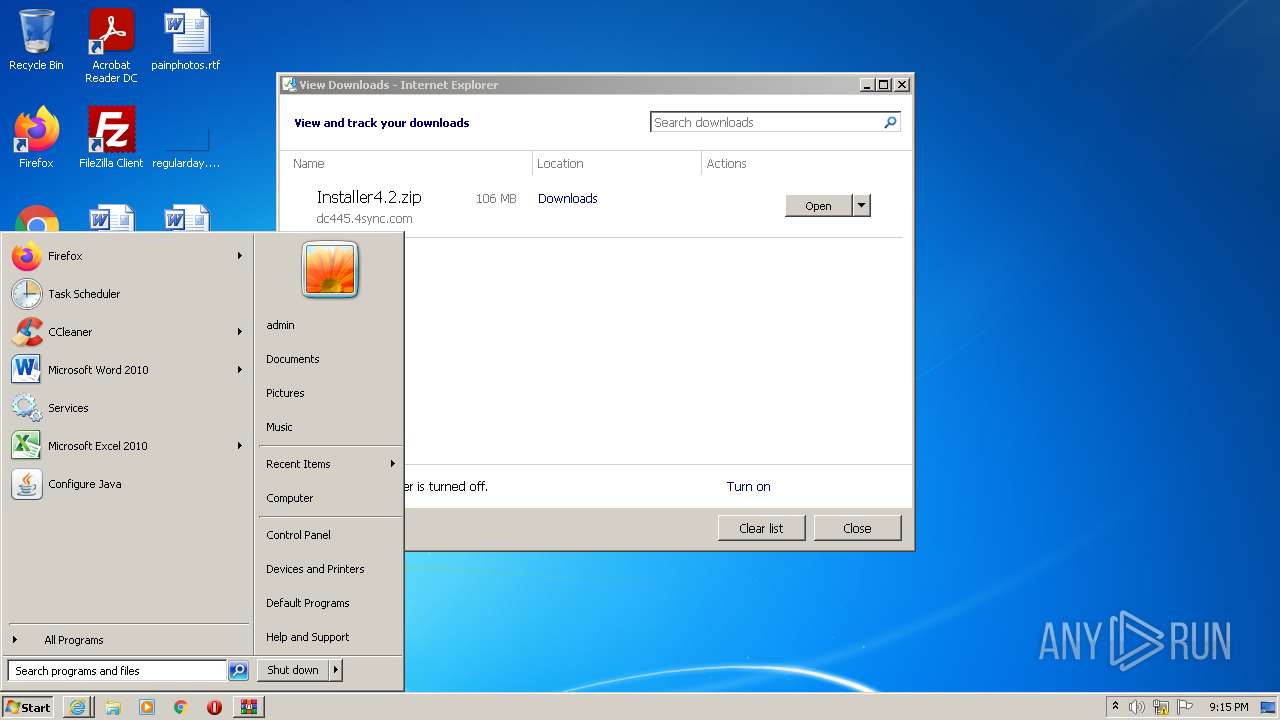
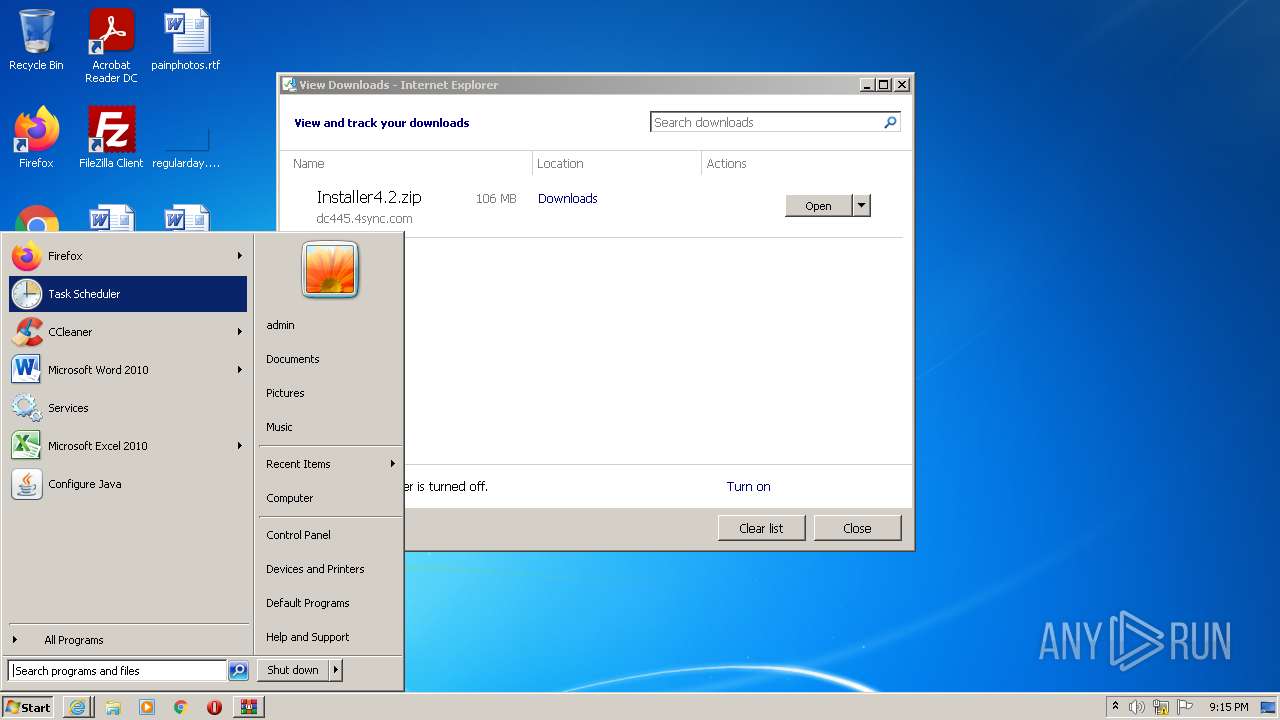
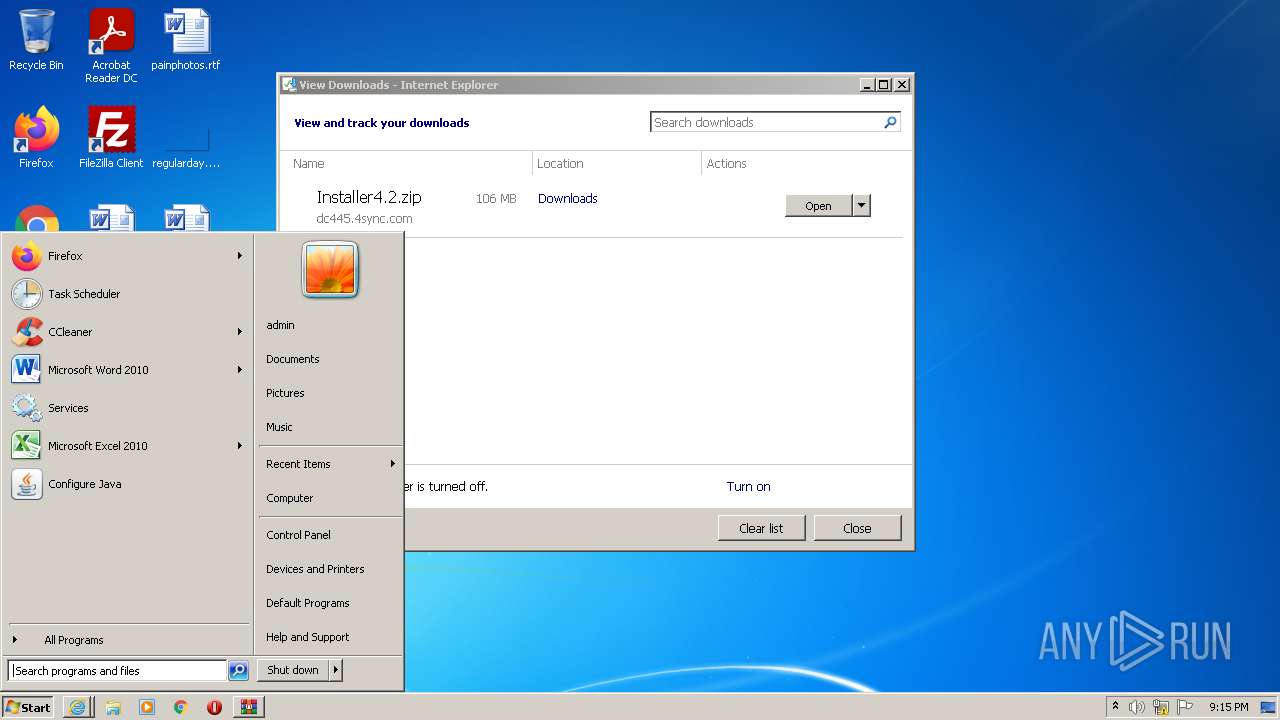
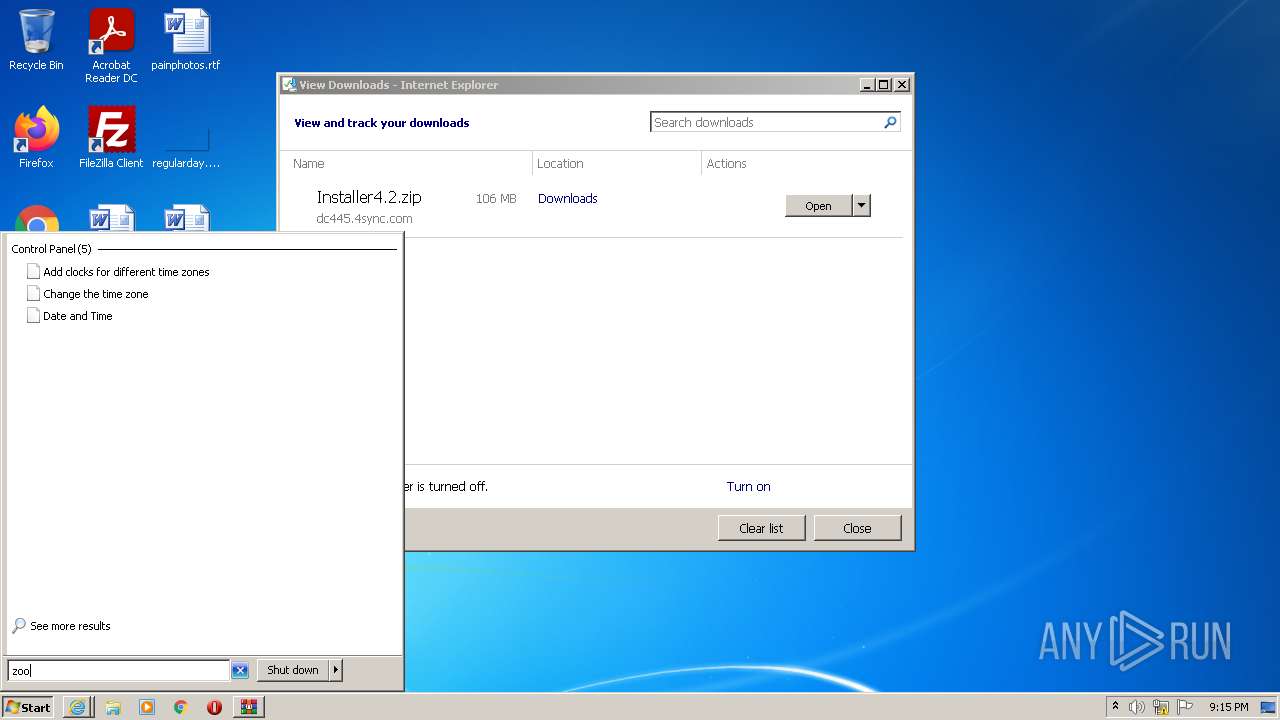
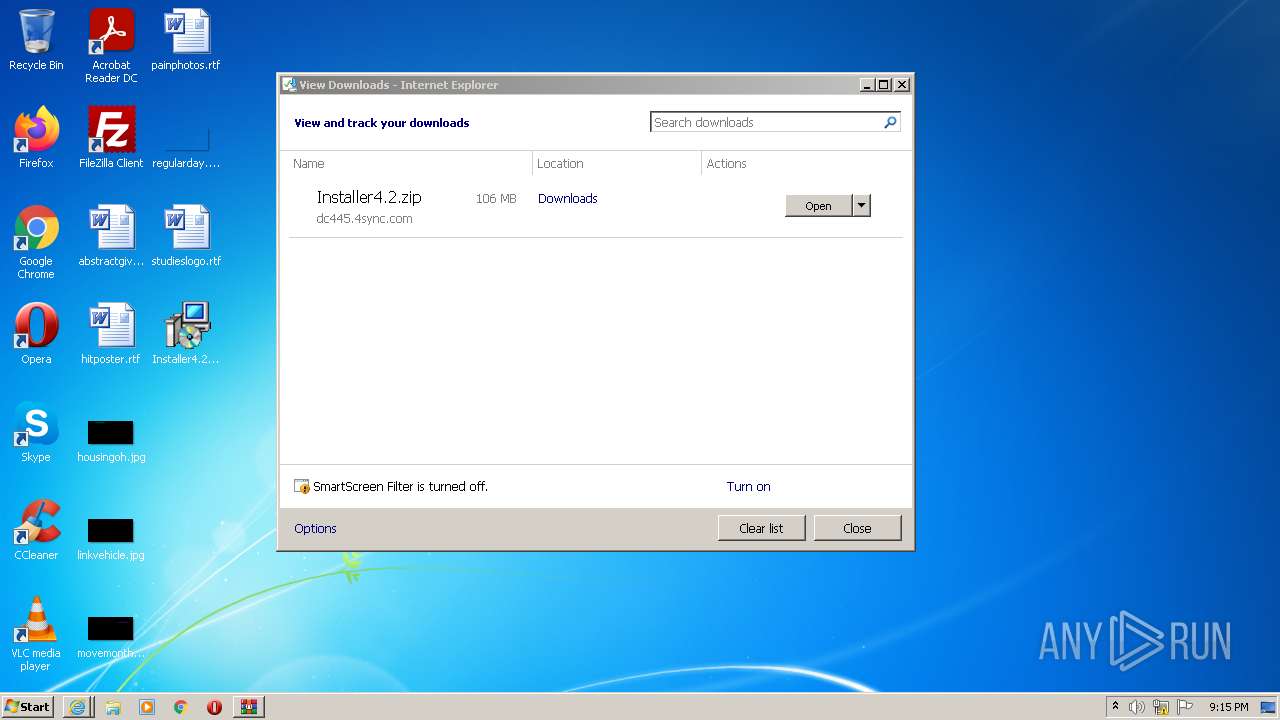
Manual execution by user
- msiexec.exe (PID: 3608)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2784)
Searches for installed software
- msiexec.exe (PID: 2784)
Creates files in the program directory
- msiexec.exe (PID: 2784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3068 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1844 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssF2F8.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msiF2F5.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scrF2F6.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scrF2F7.txt" -propSep " :<->: " -testPrefix "_testValue." | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
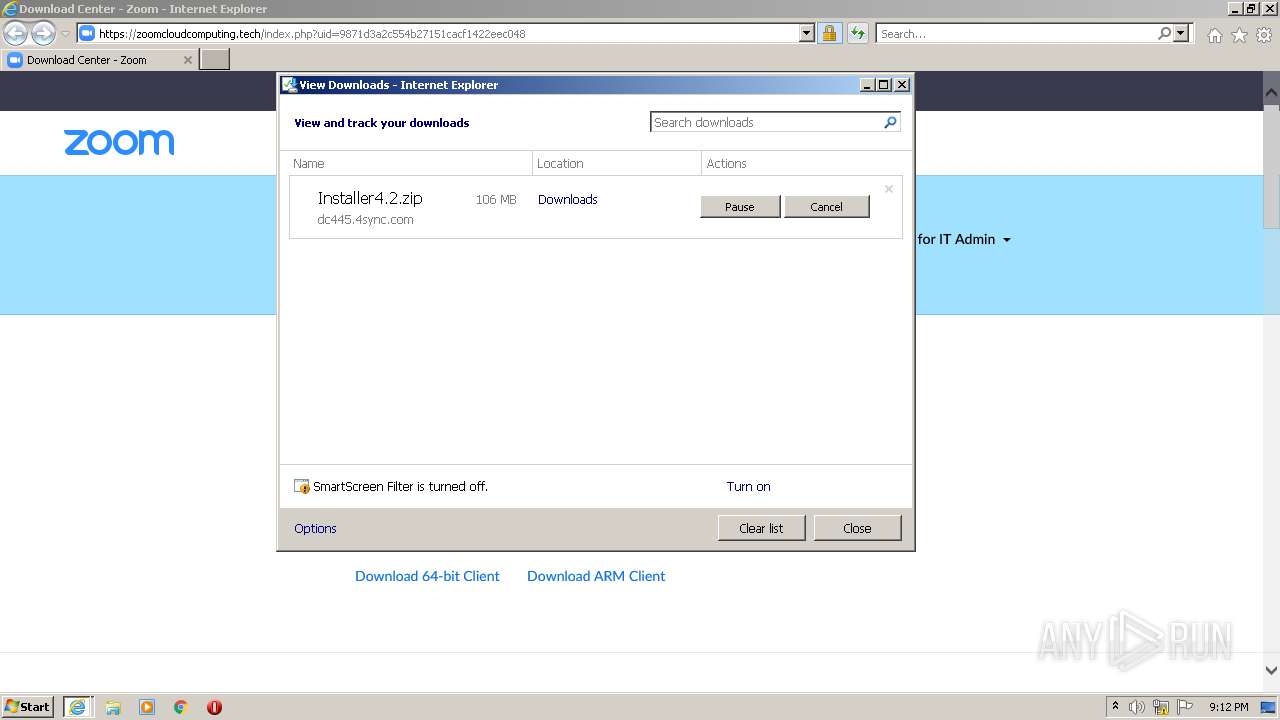
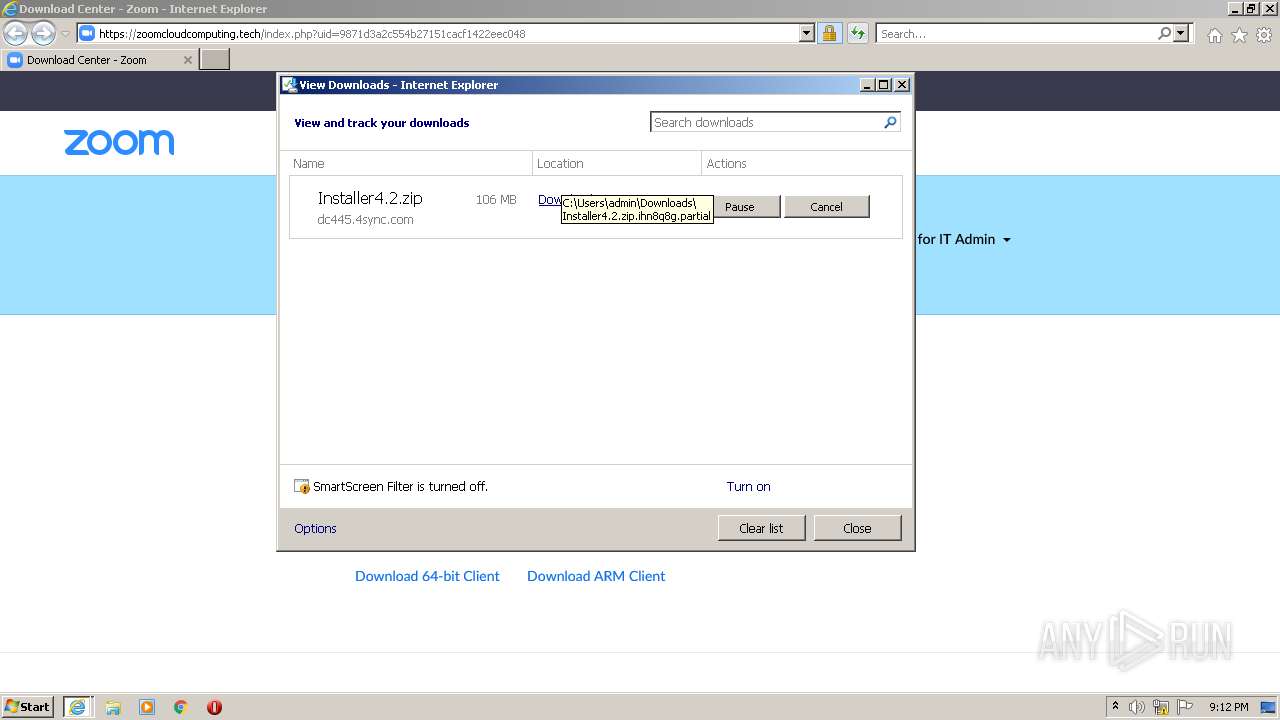
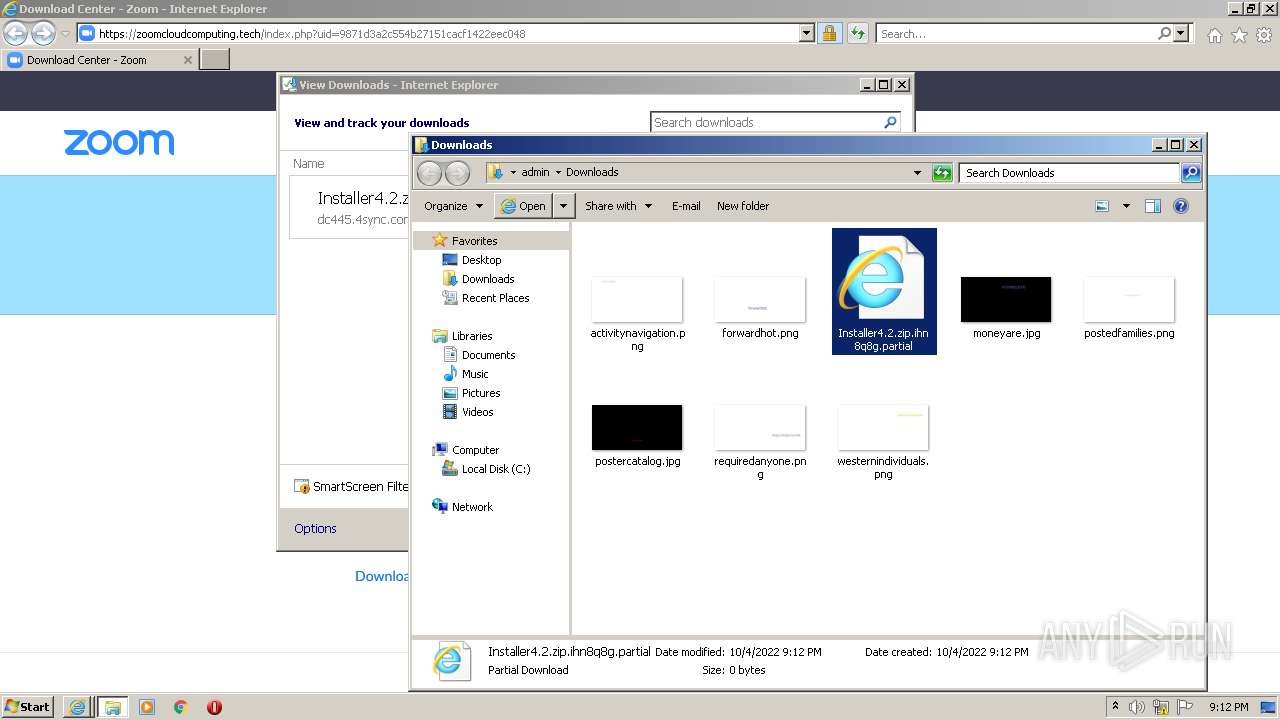
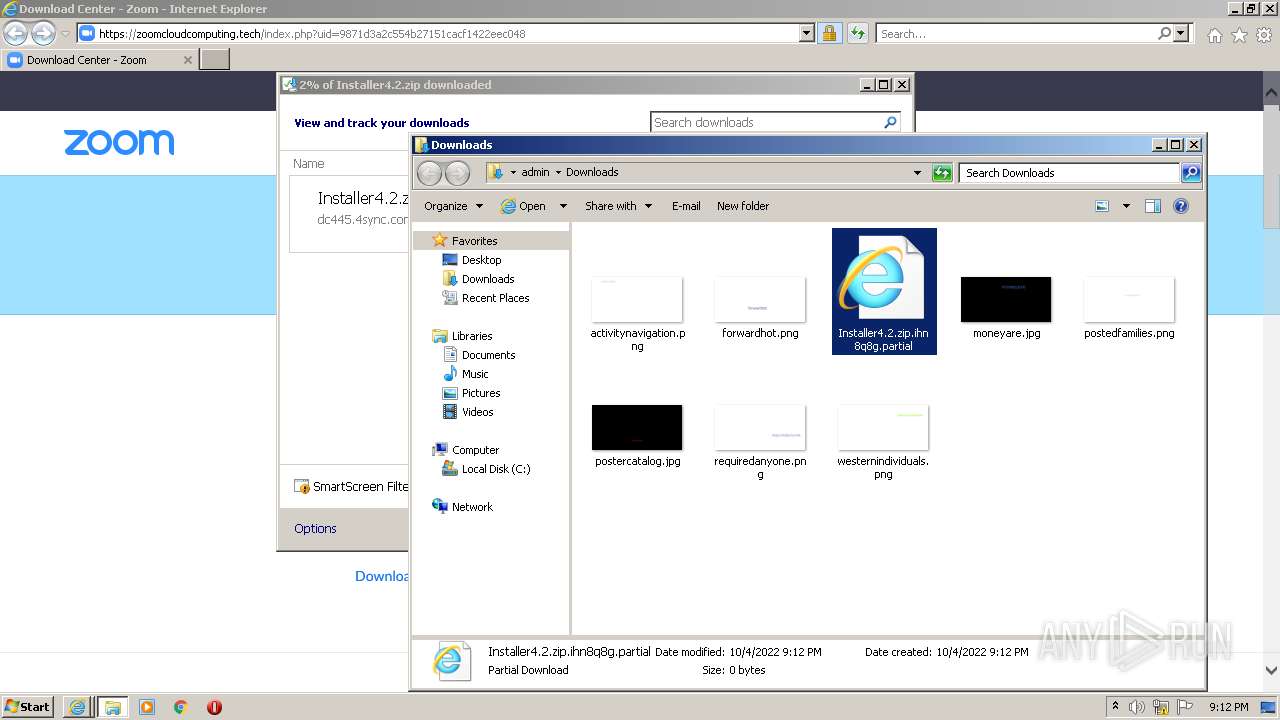
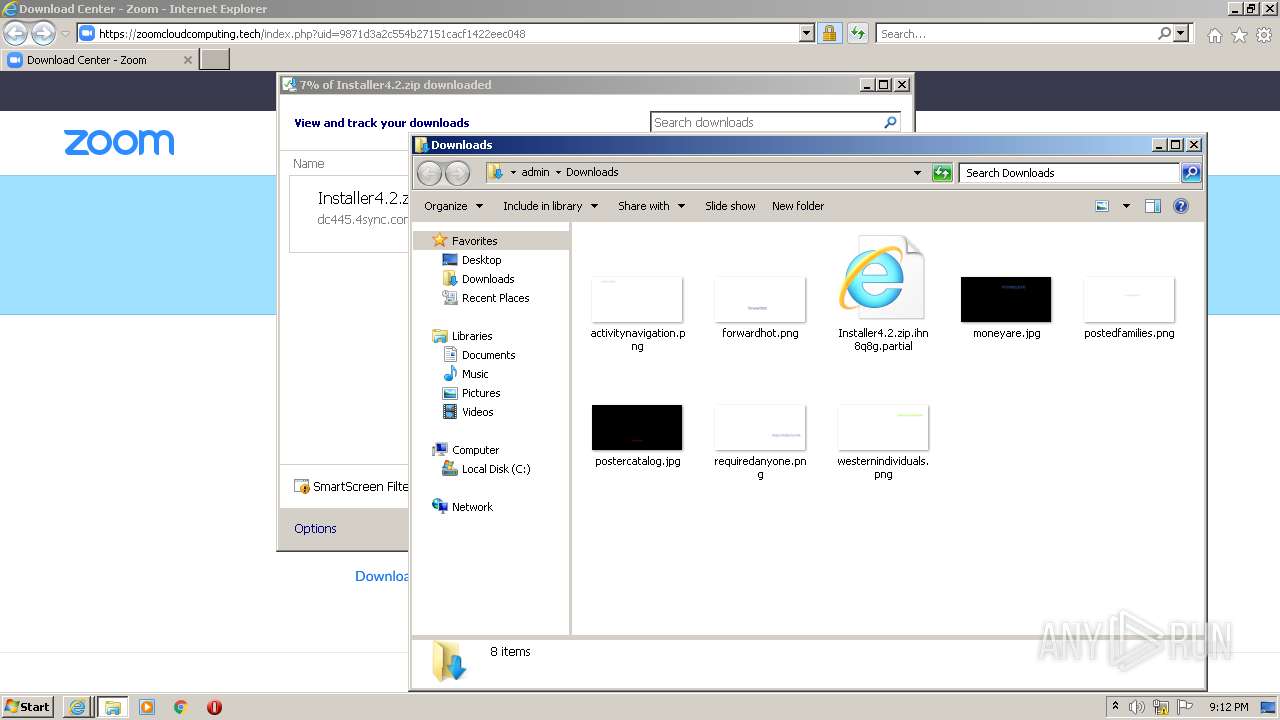
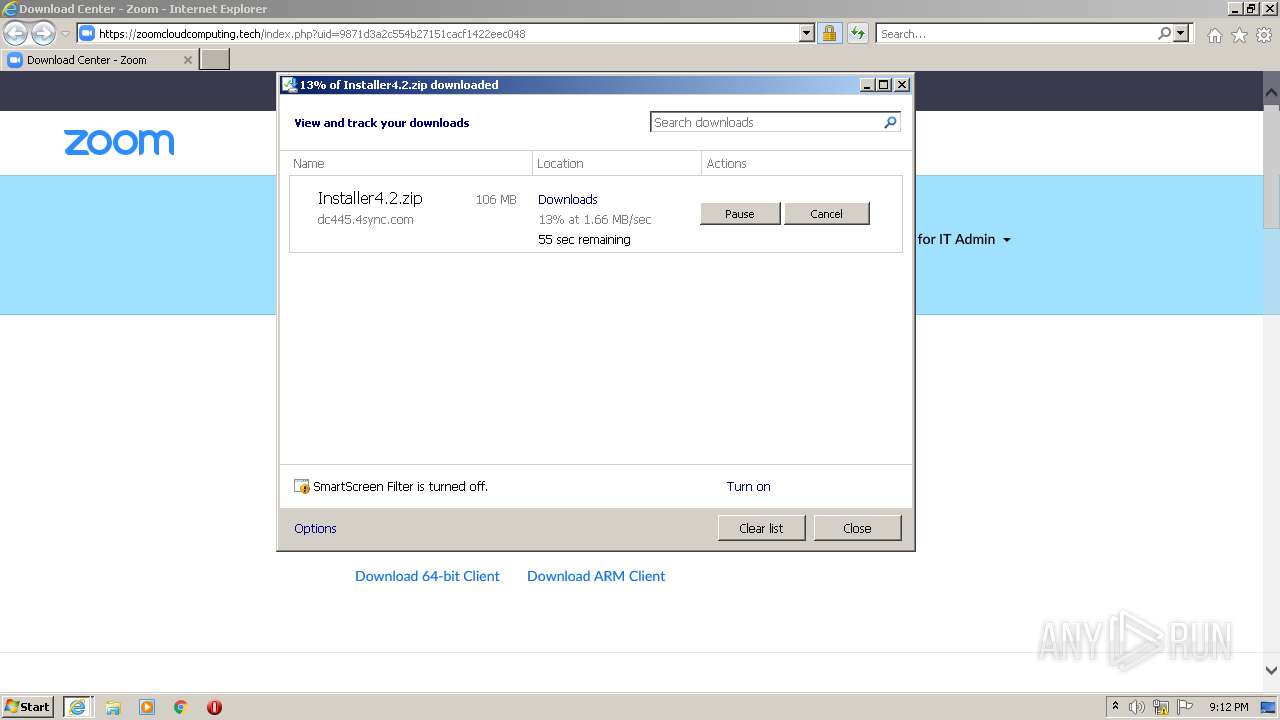
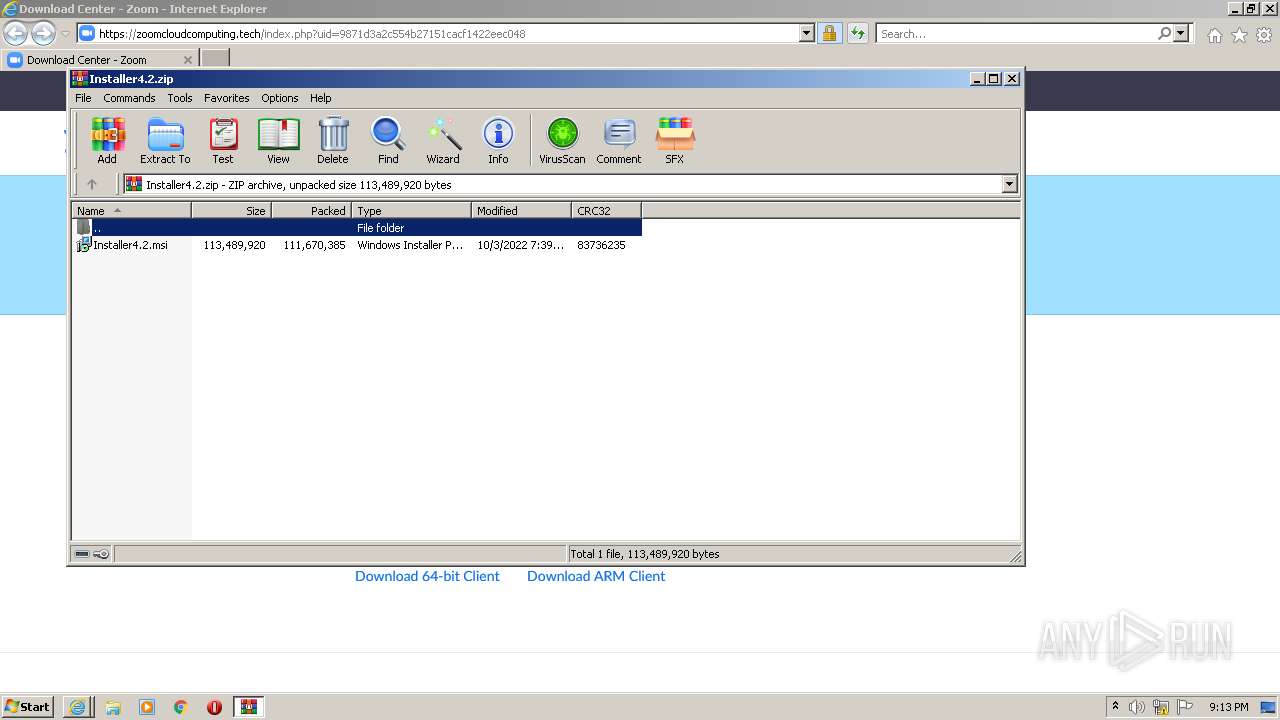
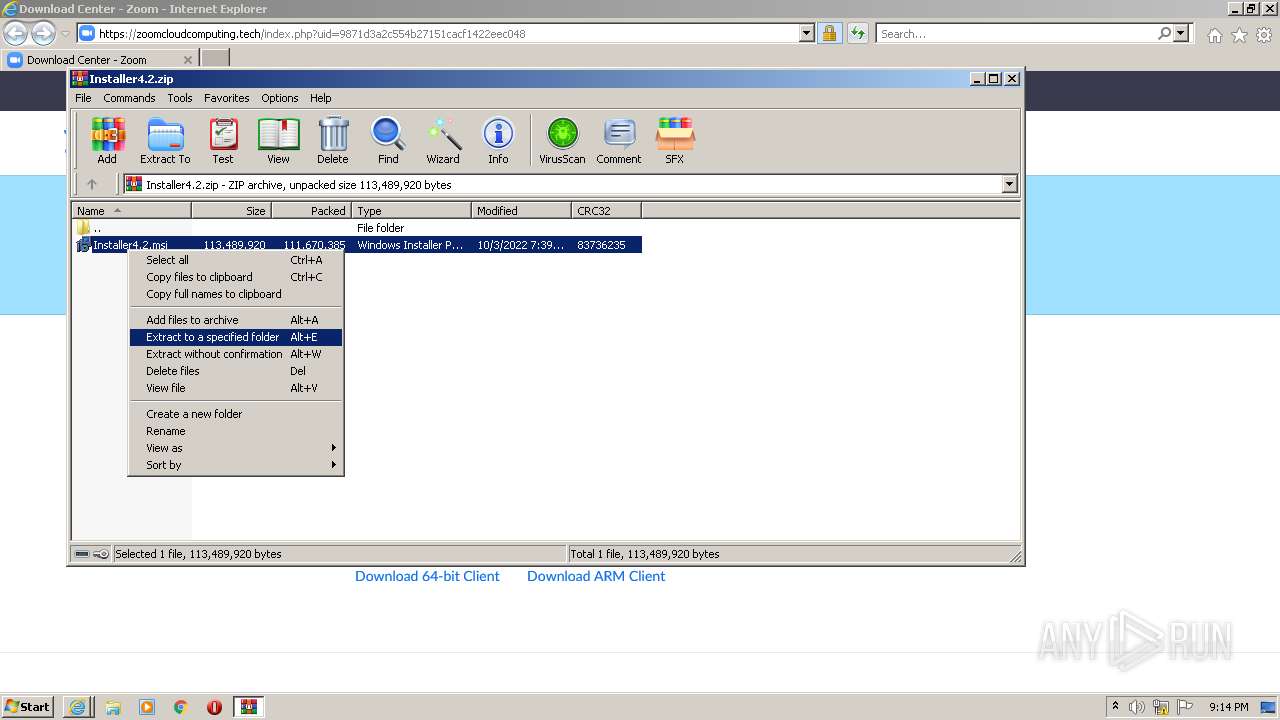
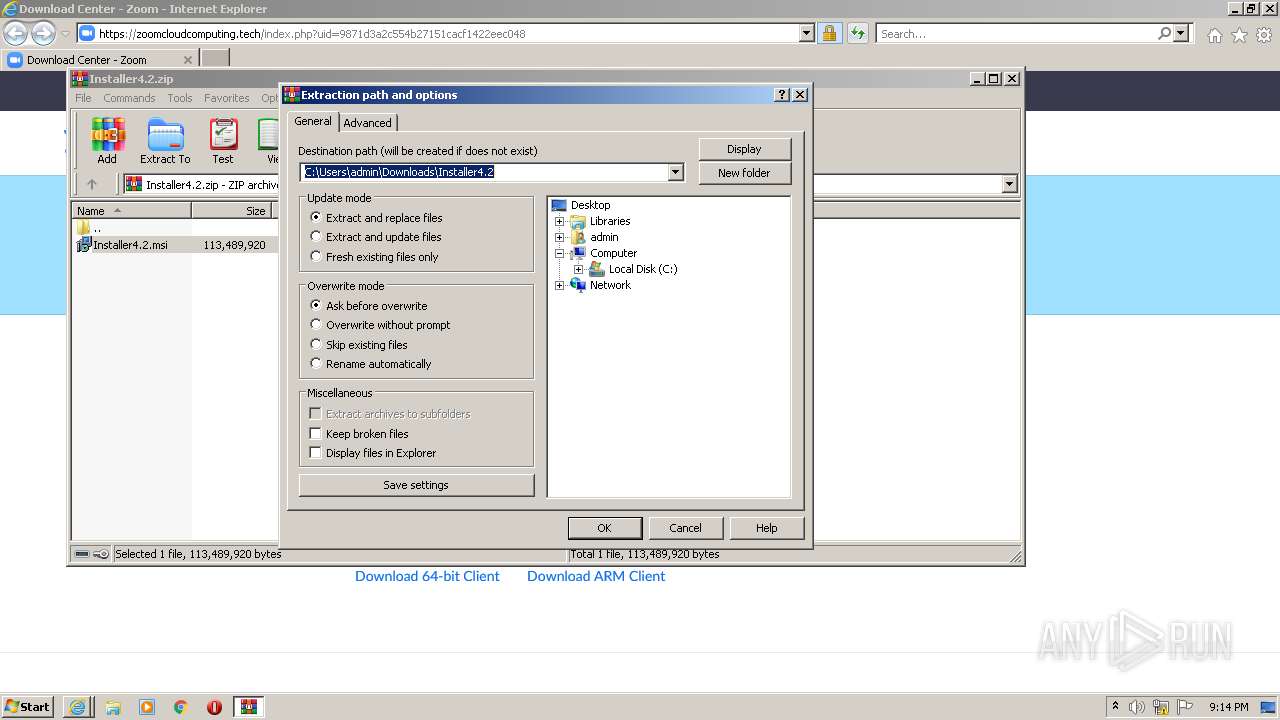
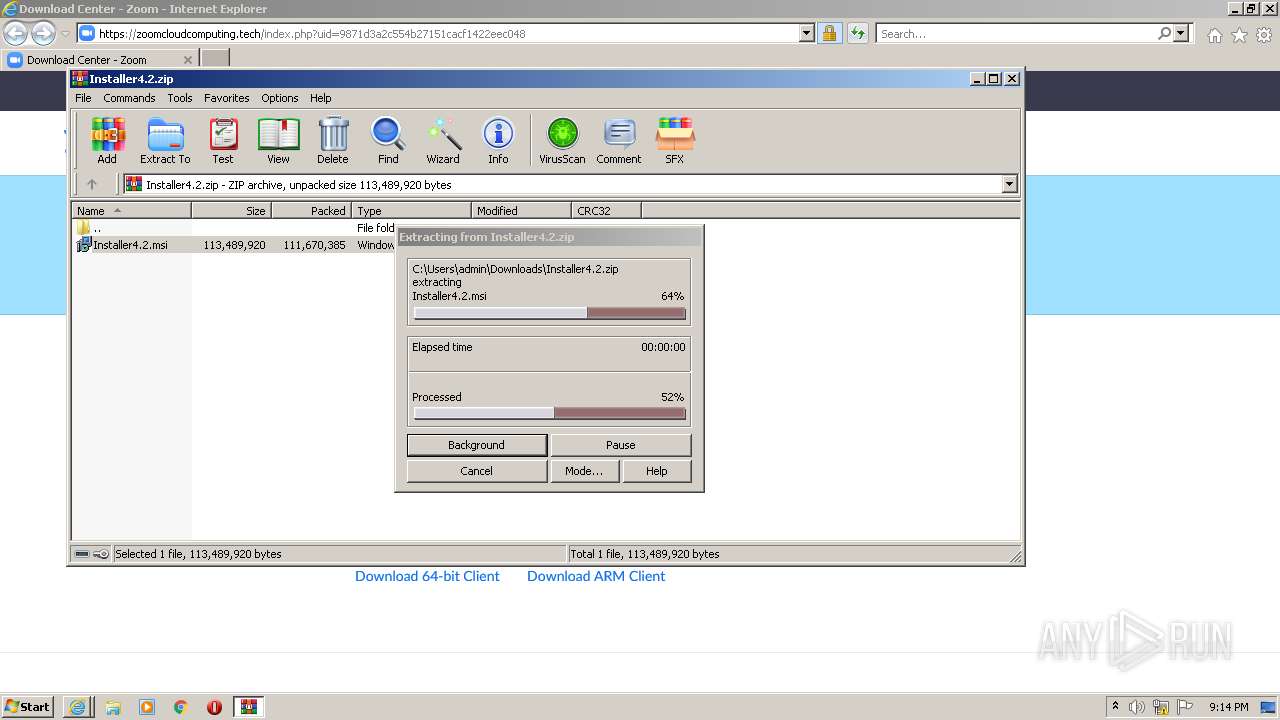
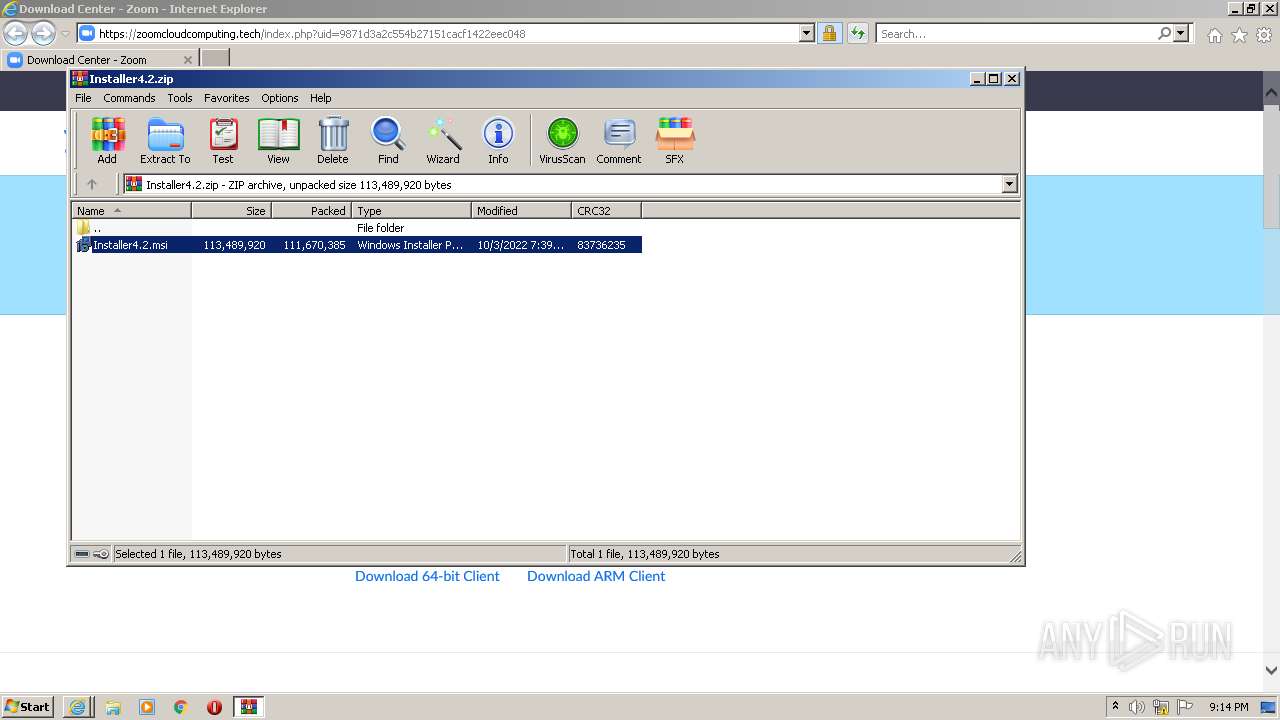
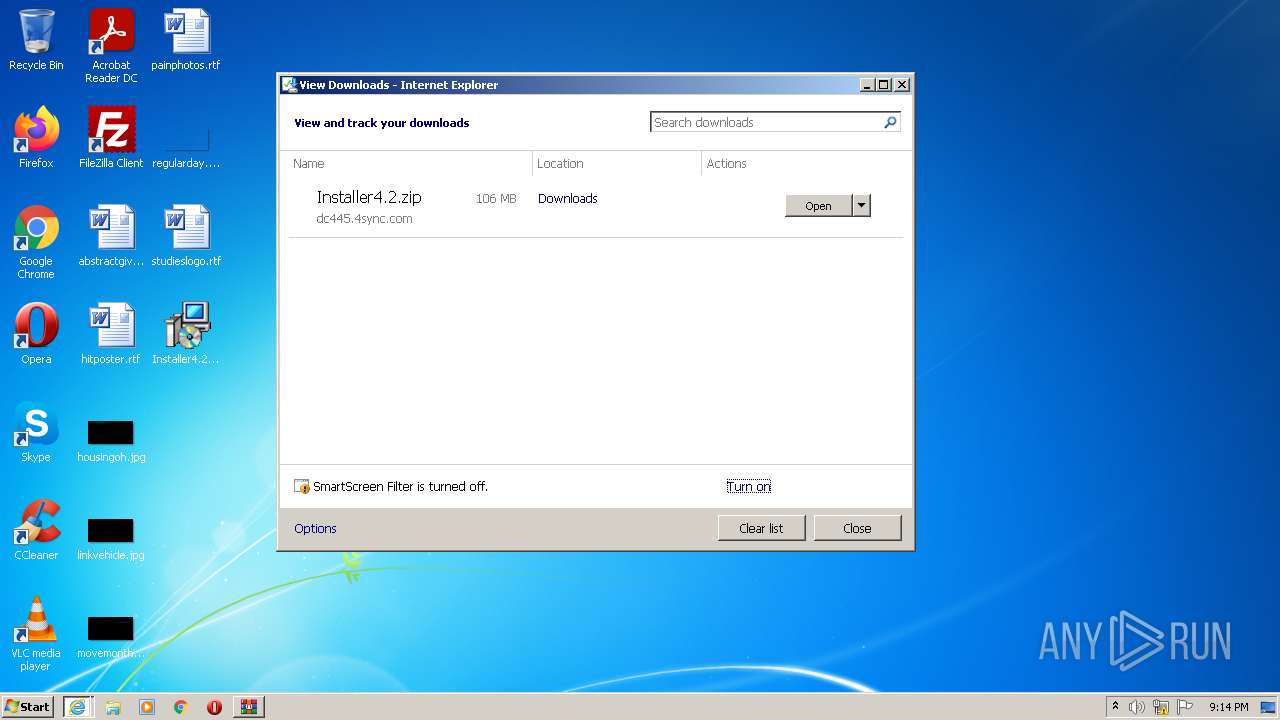
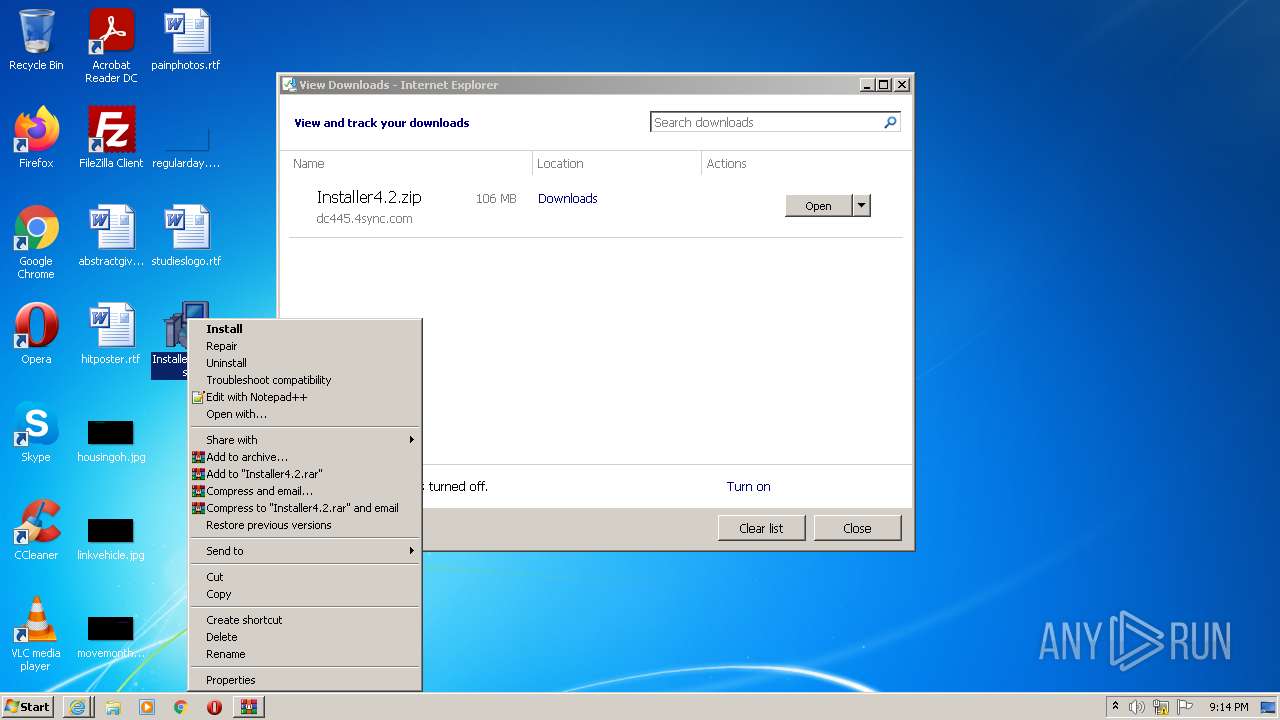
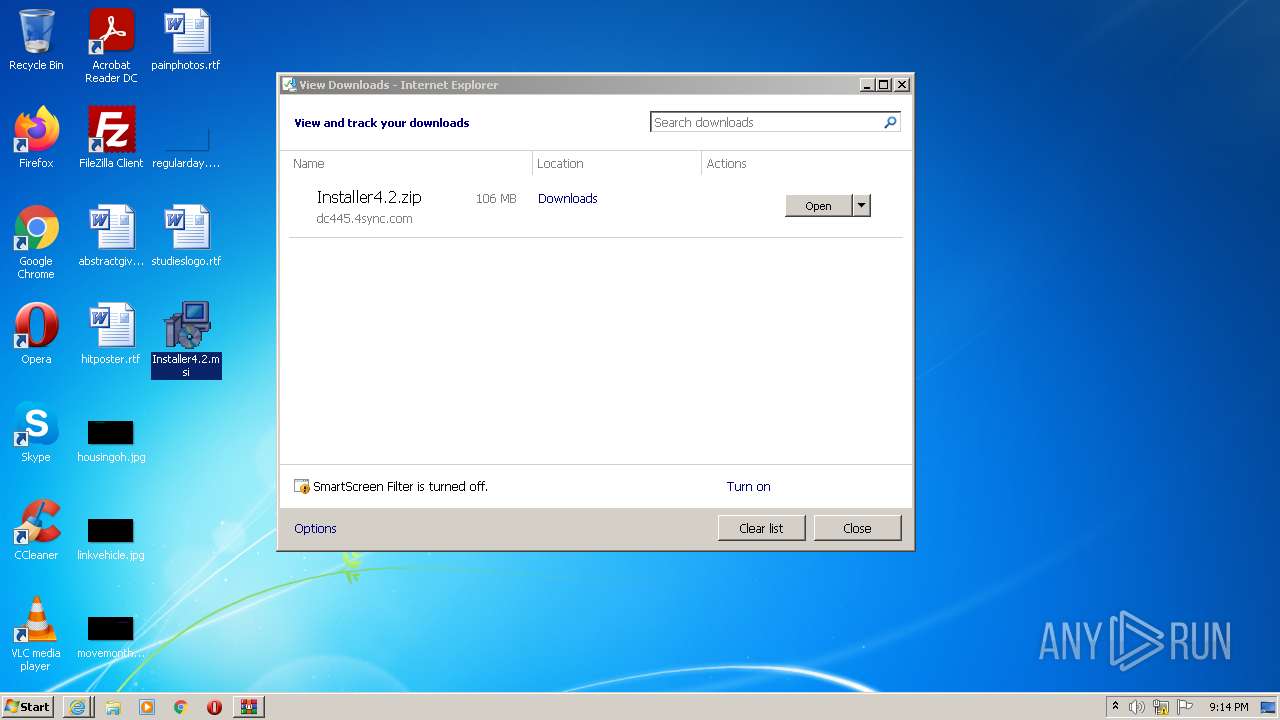
| 2088 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Installer4.2.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2676 | C:\Windows\system32\MsiExec.exe -Embedding 0ECE9653ADA4A7562424DC54D0B26EBA | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2784 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3068 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://zoomcloudcomputing.tech/index.php?uid=9871d3a2c554b27151cacf1422eec048" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3608 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Desktop\Installer4.2.msi" | C:\Windows\System32\msiexec.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3820 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
30 814
Read events
30 377
Write events
421
Delete events
16
Modification events
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30988333 | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30988333 | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
311
Suspicious files
104
Text files
76
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1180 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab5C4C.tmp | compressed | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar5C4D.tmp | cat | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35A6FDB69457C123C3C0C51920D8B1B6 | der | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\35A6FDB69457C123C3C0C51920D8B1B6 | binary | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\all.min[1].css | text | |
MD5:25D67B9CD15DF77F5C3F174ECC671803 | SHA256:31EEBBA0249114FC28BDE3BEA5D0230578EC08FD4DD5E70EE3A0D39E24713652 | |||
| 1180 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
42
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3068 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1180 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
1180 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCBjVsTUeA9f8 | US | der | 1.74 Kb | whitelisted |
3068 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
1180 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?930d7671152f423d | US | compressed | 60.9 Kb | whitelisted |
3068 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
1180 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3ee1327b1814a2ea | US | compressed | 4.70 Kb | whitelisted |
1180 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
1180 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?00ebef62d5cb671e | US | compressed | 4.70 Kb | whitelisted |
1180 | iexplore.exe | GET | 200 | 184.24.77.51:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPGMUg%2F6Q1vF6szrD1IrCGcBg%3D%3D | US | der | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1180 | iexplore.exe | 37.140.192.70:443 | zoomcloudcomputing.tech | Domain names registrar REG.RU, Ltd | RU | malicious |
3068 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3068 | iexplore.exe | 204.79.197.203:443 | www.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | malicious |
3068 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1180 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1180 | iexplore.exe | 184.24.77.51:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
3068 | iexplore.exe | 37.140.192.70:443 | zoomcloudcomputing.tech | Domain names registrar REG.RU, Ltd | RU | malicious |
1844 | powershell.exe | 194.67.119.190:443 | cloudupdatesss.com | Domain names registrar REG.RU, Ltd | RU | unknown |
1180 | iexplore.exe | 204.155.149.140:443 | www.4sync.com | WZCOM | US | unknown |
1180 | iexplore.exe | 192.124.249.36:80 | ocsp.godaddy.com | SUCURI-SEC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zoomcloudcomputing.tech |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
r3.o.lencr.org |
| shared |
ocsp.digicert.com |
| whitelisted |
www.4sync.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
Threats
Process | Message |
|---|---|
MsiExec.exe | 2022-10-04 21:14:27 DetectPrinters dll started
|
MsiExec.exe | 2022-10-04 21:14:27 SetVersionNT - start
|
MsiExec.exe | 2022-10-04 21:14:27 ReadProcessIdVariable - CustomActionData:
|
MsiExec.exe | 2022-10-04 21:14:27 GetKeyData - RegQueryValueEx error: 2
|
MsiExec.exe | 2022-10-04 21:14:27 GetKeyData - RegQueryValueEx error: 2
|
MsiExec.exe | 2022-10-04 21:14:27 SetVersionNT - end
|