| File name: | DH398F23F32F23F23F23F23.exe |
| Full analysis: | https://app.any.run/tasks/dfc5d516-e529-494d-9548-59e45d2c49a0 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2025, 00:30:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 12 sections |
| MD5: | F9082704CDF8B1221D2FEE0261A81C3E |
| SHA1: | 495C3EB844EE9B86A3D7CFBE105B24E252398D8E |
| SHA256: | 4D7AEA61A056FBF046B2B304ED9EF83F5BF6E6E4766D38DD7798794843CC3240 |
| SSDEEP: | 98304:fFDFb7NALHsGsx26U/UVJ229vRdX37Z0DWvOL90YKTdDDiDv6zYYBgpGw4TD6HEc:CCEt3vEJaDyF3Ja |
MALICIOUS
Executing a file with an untrusted certificate
- DH398F23F32F23F23F23F23.exe (PID: 420)
- DH398F23F32F23F23F23F23.exe (PID: 3688)
Uses TASKKILL.EXE to kill security tools
- cmd.exe (PID: 5964)
- cmd.exe (PID: 5256)
- cmd.exe (PID: 1140)
- cmd.exe (PID: 3296)
SUSPICIOUS
Hides command output
- cmd.exe (PID: 5256)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 4144)
- cmd.exe (PID: 3436)
- cmd.exe (PID: 5096)
- cmd.exe (PID: 5256)
- cmd.exe (PID: 5236)
- cmd.exe (PID: 4628)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 5032)
- cmd.exe (PID: 1224)
- cmd.exe (PID: 5472)
- cmd.exe (PID: 6096)
- cmd.exe (PID: 4516)
- cmd.exe (PID: 5464)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 6012)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 5032)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 1448)
- cmd.exe (PID: 3692)
- cmd.exe (PID: 900)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 5684)
- cmd.exe (PID: 3836)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 4764)
- cmd.exe (PID: 4516)
- cmd.exe (PID: 5696)
- cmd.exe (PID: 3524)
- cmd.exe (PID: 5096)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 2992)
- cmd.exe (PID: 4716)
- cmd.exe (PID: 4164)
- cmd.exe (PID: 4952)
- cmd.exe (PID: 5472)
- cmd.exe (PID: 900)
- cmd.exe (PID: 4540)
- cmd.exe (PID: 3420)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 5032)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 1620)
- cmd.exe (PID: 3692)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 1412)
- cmd.exe (PID: 4516)
- cmd.exe (PID: 876)
- cmd.exe (PID: 4244)
- cmd.exe (PID: 5464)
- cmd.exe (PID: 624)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 1448)
- cmd.exe (PID: 4536)
- cmd.exe (PID: 440)
- cmd.exe (PID: 1224)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 5748)
- cmd.exe (PID: 4520)
- cmd.exe (PID: 1140)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 5684)
- cmd.exe (PID: 5748)
- cmd.exe (PID: 1448)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 2992)
- cmd.exe (PID: 3436)
- cmd.exe (PID: 1580)
- cmd.exe (PID: 4540)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 836)
- cmd.exe (PID: 2260)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 68)
- cmd.exe (PID: 4548)
- cmd.exe (PID: 4716)
- cmd.exe (PID: 4136)
- cmd.exe (PID: 1752)
- cmd.exe (PID: 3524)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 4540)
- cmd.exe (PID: 1580)
- cmd.exe (PID: 3420)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 3560)
- cmd.exe (PID: 1344)
- cmd.exe (PID: 4512)
- cmd.exe (PID: 4628)
- cmd.exe (PID: 444)
- cmd.exe (PID: 4640)
- cmd.exe (PID: 3436)
- cmd.exe (PID: 4244)
- cmd.exe (PID: 6012)
- cmd.exe (PID: 5696)
- cmd.exe (PID: 5156)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 1344)
- cmd.exe (PID: 5156)
- cmd.exe (PID: 5540)
- cmd.exe (PID: 4512)
- cmd.exe (PID: 1140)
- cmd.exe (PID: 4384)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 3836)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 4716)
- cmd.exe (PID: 1412)
- cmd.exe (PID: 2992)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 448)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 1224)
- cmd.exe (PID: 4596)
- cmd.exe (PID: 4628)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 2008)
- cmd.exe (PID: 5696)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 1200)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 624)
- cmd.exe (PID: 68)
- cmd.exe (PID: 4520)
Stops a currently running service
- sc.exe (PID: 2408)
- sc.exe (PID: 4708)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 5320)
- DH398F23F32F23F23F23F23.exe (PID: 420)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1852)
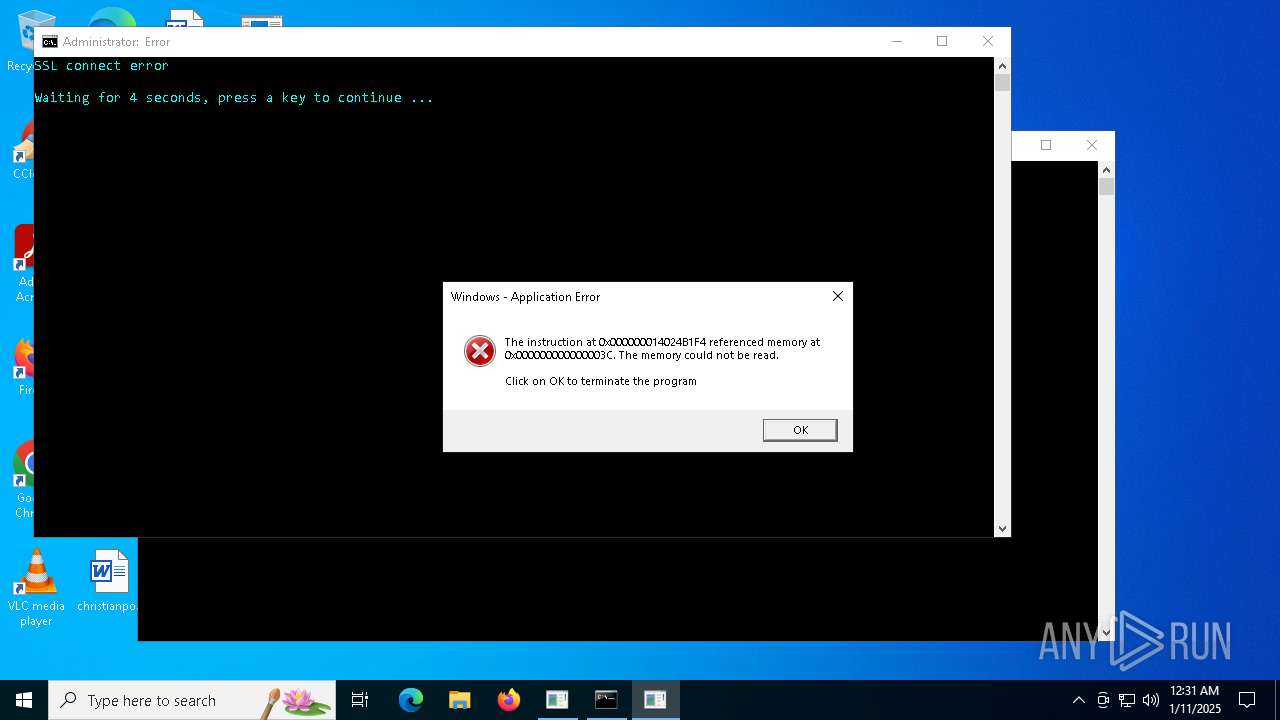
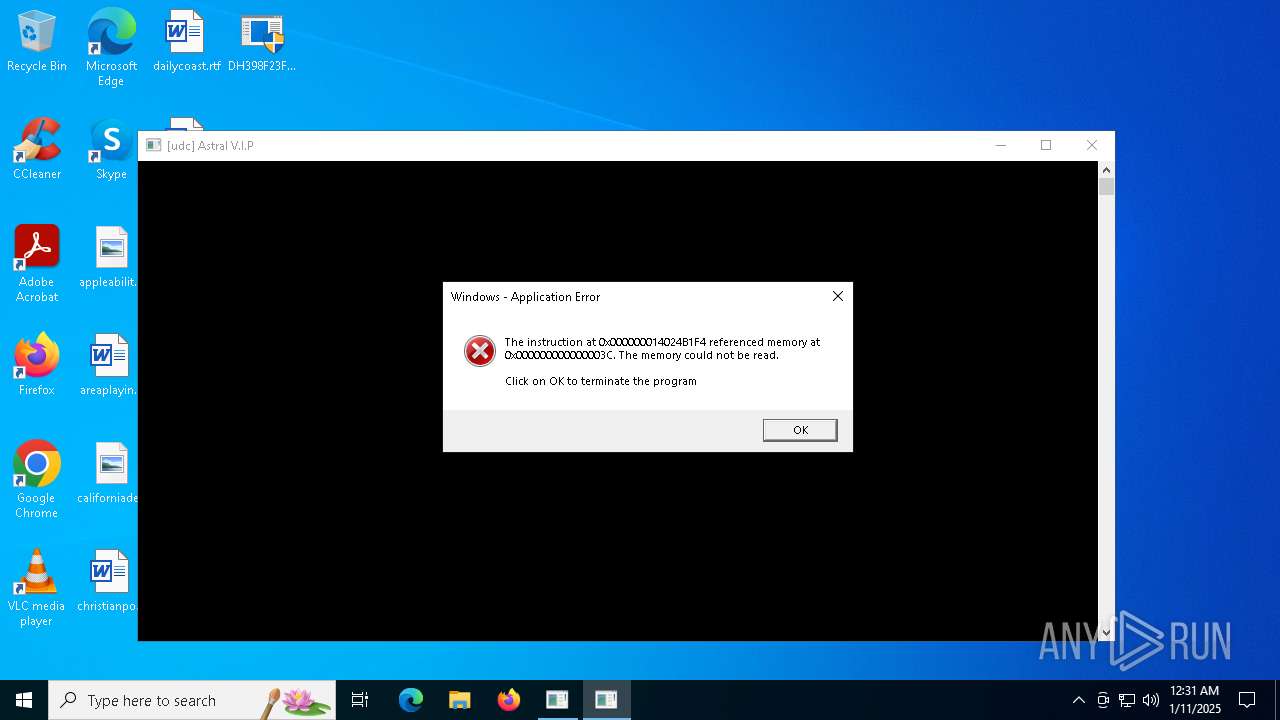
Executes application which crashes
- DH398F23F32F23F23F23F23.exe (PID: 420)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3436)
- cmd.exe (PID: 5096)
- cmd.exe (PID: 4144)
- cmd.exe (PID: 5256)
- cmd.exe (PID: 4628)
- cmd.exe (PID: 5032)
- cmd.exe (PID: 5236)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 6096)
- cmd.exe (PID: 1224)
- cmd.exe (PID: 5472)
- cmd.exe (PID: 4516)
- cmd.exe (PID: 5464)
- cmd.exe (PID: 6012)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 5032)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 3692)
- cmd.exe (PID: 5684)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 900)
- cmd.exe (PID: 3836)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 4764)
- cmd.exe (PID: 4516)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 5696)
- cmd.exe (PID: 3524)
- cmd.exe (PID: 5096)
- cmd.exe (PID: 4952)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 2992)
- cmd.exe (PID: 4716)
- cmd.exe (PID: 3420)
- cmd.exe (PID: 4540)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 4164)
- cmd.exe (PID: 900)
- cmd.exe (PID: 5472)
- cmd.exe (PID: 5032)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 1620)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 624)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 876)
- cmd.exe (PID: 1412)
- cmd.exe (PID: 5464)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 3692)
- cmd.exe (PID: 4516)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 1448)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 4536)
- cmd.exe (PID: 5696)
- cmd.exe (PID: 440)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 5748)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 5748)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 1448)
- cmd.exe (PID: 1448)
- cmd.exe (PID: 3436)
- cmd.exe (PID: 4540)
- cmd.exe (PID: 5548)
- cmd.exe (PID: 836)
- cmd.exe (PID: 2992)
- cmd.exe (PID: 2260)
- cmd.exe (PID: 4520)
- cmd.exe (PID: 1580)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 2804)
- cmd.exe (PID: 4716)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 68)
- cmd.exe (PID: 4548)
- cmd.exe (PID: 4136)
- cmd.exe (PID: 3524)
- cmd.exe (PID: 4540)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 3420)
- cmd.exe (PID: 1752)
- cmd.exe (PID: 1580)
- cmd.exe (PID: 3560)
- cmd.exe (PID: 1344)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 4512)
- cmd.exe (PID: 4244)
- cmd.exe (PID: 5156)
- cmd.exe (PID: 4640)
- cmd.exe (PID: 444)
- cmd.exe (PID: 4628)
- cmd.exe (PID: 4244)
- cmd.exe (PID: 3436)
- cmd.exe (PID: 1224)
- cmd.exe (PID: 1200)
- cmd.exe (PID: 6012)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 1344)
- cmd.exe (PID: 4512)
- cmd.exe (PID: 4384)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 5540)
- cmd.exe (PID: 5156)
- cmd.exe (PID: 3836)
- cmd.exe (PID: 1140)
- cmd.exe (PID: 5244)
- cmd.exe (PID: 5112)
- cmd.exe (PID: 5488)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 448)
- cmd.exe (PID: 1412)
- cmd.exe (PID: 2992)
- cmd.exe (PID: 4716)
- cmd.exe (PID: 2008)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 1224)
- cmd.exe (PID: 3928)
- cmd.exe (PID: 4596)
- cmd.exe (PID: 5696)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 624)
- cmd.exe (PID: 68)
- cmd.exe (PID: 4520)
- cmd.exe (PID: 5040)
- cmd.exe (PID: 4628)
- cmd.exe (PID: 5576)
Starts SC.EXE for service management
- cmd.exe (PID: 2796)
- cmd.exe (PID: 5684)
Application launched itself
- cmd.exe (PID: 5320)
Reads the BIOS version
- DH398F23F32F23F23F23F23.exe (PID: 420)
INFO
The sample compiled with english language support
- DH398F23F32F23F23F23F23.exe (PID: 420)
Process checks whether UAC notifications are on
- DH398F23F32F23F23F23F23.exe (PID: 420)
Checks supported languages
- DH398F23F32F23F23F23F23.exe (PID: 420)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 2408)
Reads the computer name
- DH398F23F32F23F23F23F23.exe (PID: 420)
Themida protector has been detected
- DH398F23F32F23F23F23F23.exe (PID: 420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:01:08 08:58:46+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 3090432 |
| InitializedDataSize: | 1432064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa97058 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 10.0.19041.4355 |
| ProductVersionNumber: | 10.0.19041.4355 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft |
| FileDescription: | Host Process for Windows Services |
| FileVersion: | 10.0.19041.4355 |
| InternalName: | injector.exe |
| LegalCopyright: | Copyright (C) 2024 |
| OriginalFileName: | svchost2 |
| ProductName: | Microsoft |
| ProductVersion: | 10.0.19041.4355 |
Total processes
420
Monitored processes
298
Malicious processes
1
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | taskkill /FI "IMAGENAME eq burpsuite*" /IM * /F /T | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 68 | C:\WINDOWS\system32\cmd.exe /c taskkill /FI "IMAGENAME eq anydesk*" /IM * /F /T >nul 2>&1 | C:\Windows\System32\cmd.exe | — | DH398F23F32F23F23F23F23.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 68 | C:\WINDOWS\system32\cmd.exe /c taskkill /FI "IMAGENAME eq zaproxy.exe*" /IM * /F /T >nul 2>&1 | C:\Windows\System32\cmd.exe | — | DH398F23F32F23F23F23F23.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | "C:\Users\admin\Desktop\DH398F23F32F23F23F23F23.exe" | C:\Users\admin\Desktop\DH398F23F32F23F23F23F23.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 3221225477 Version: 10.0.19041.4355 Modules
| |||||||||||||||
| 440 | taskkill /FI "IMAGENAME eq hxd*" /IM * /F /T | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 440 | C:\WINDOWS\system32\cmd.exe /c taskkill /FI "IMAGENAME eq immunitydebugger.exe*" /IM * /F /T >nul 2>&1 | C:\Windows\System32\cmd.exe | — | DH398F23F32F23F23F23F23.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 440 | taskkill /FI "IMAGENAME eq nomadnet*" /IM * /F /T | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | taskkill /FI "IMAGENAME eq fiddler*" /IM * /F /T | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | C:\WINDOWS\system32\cmd.exe /c taskkill /FI "IMAGENAME eq burpsuite32*" /IM * /F /T >nul 2>&1 | C:\Windows\System32\cmd.exe | — | DH398F23F32F23F23F23F23.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | C:\WINDOWS\system32\cmd.exe /c taskkill /FI "IMAGENAME eq thunar*" /IM * /F /T >nul 2>&1 | C:\Windows\System32\cmd.exe | — | DH398F23F32F23F23F23F23.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 789
Read events
15 786
Write events
3
Delete events
0
Modification events
| (PID) Process: | (2408) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.1!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_AUTO_UPDATE_CA_REVOCATION | |||
| (PID) Process: | (2408) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.2!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_AUTO_UPDATE_END_REVOCATION | |||
| (PID) Process: | (2408) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.3!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_NO_OCSP_FAILOVER_TO_CRL | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
19
DNS requests
9
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1140 | RUXIMICS.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1140 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5988 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
1140 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1140 | RUXIMICS.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1140 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
keyauth.win |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
420 | DH398F23F32F23F23F23F23.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |