| File name: | covid19.doc |
| Full analysis: | https://app.any.run/tasks/642a1b8c-6232-41c0-8c74-0f4513a44599 |
| Verdict: | Suspicious activity |
| Analysis date: | March 24, 2020, 08:36:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Template: Normal.dotm, Revision Number: 7, Total Editing Time: 18:00, Create Time/Date: Thu Mar 19 08:06:00 2020, Last Saved Time/Date: Fri Mar 20 08:22:00 2020, Number of Pages: 3, Number of Words: 98, Number of Characters: 562, Security: 0 |
| MD5: | 555FE4685033CB33B6508ACB3F463BE9 |
| SHA1: | 7B3B5FAD119BB2A492385E9F98CFACDF94F9F09E |
| SHA256: | 4D71F1EAB01045DE9AE76EA248BE7746BAD70C12AD977EEB6E8F8E46BBCE6395 |
| SSDEEP: | 12288:GxKdcKUocIKuxr+bKZ1uQd65oStnzL4RTGbJ5l3:GxKdfH9xB15MoWX4RKb |
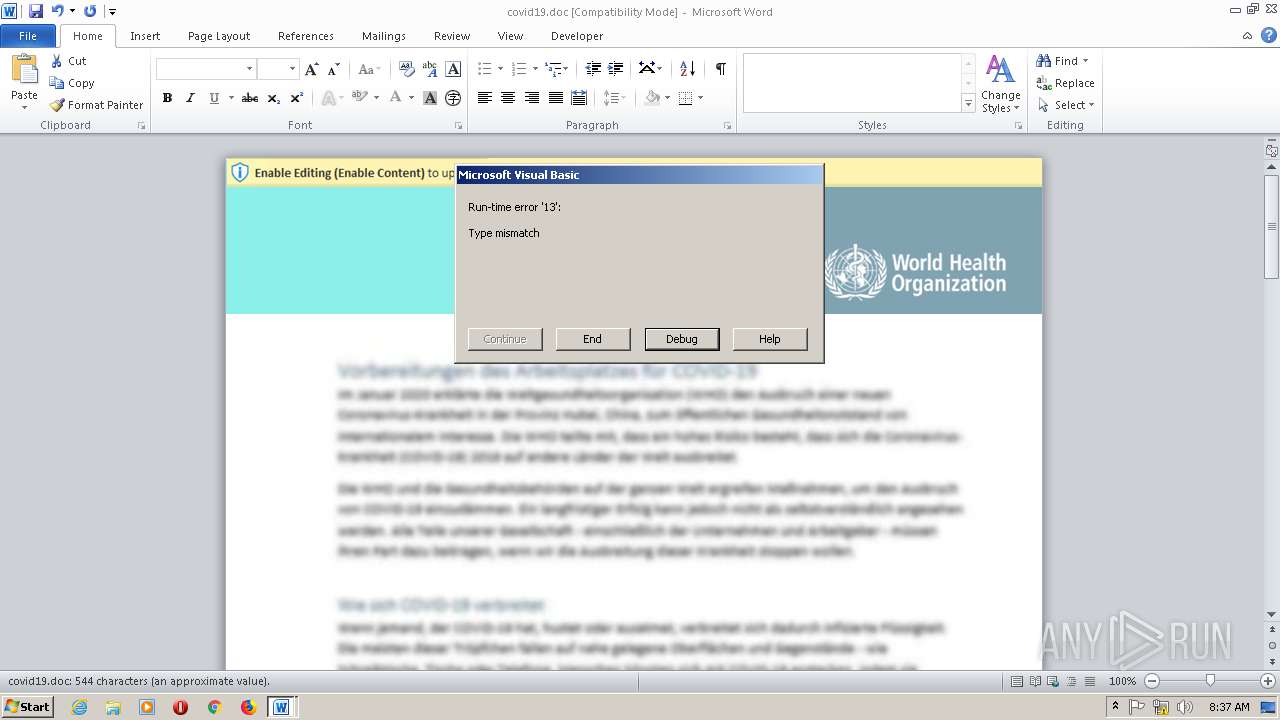
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2884)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- WINWORD.EXE (PID: 2884)
INFO
Reads settings of System Certificates
- WINWORD.EXE (PID: 2884)
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 2884)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (35.9) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (33.7) |
| .doc | | | Microsoft Word document (old ver.) (21.3) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| RevisionNumber: | 7 |
| TotalEditTime: | 18.0 minutes |
| CreateDate: | 2020:03:19 08:06:00 |
| ModifyDate: | 2020:03:20 08:22:00 |
| Pages: | 3 |
| Words: | 98 |
| Characters: | 562 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 4 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 659 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2136 | C:\Windows\\SysWOW64\\rundll32.exe | C:\Windows\SysWOW64\rundll32.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 2884 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\covid19.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.5123.5000 Modules
| |||||||||||||||
Total events
1 846
Read events
1 126
Write events
570
Delete events
150
Modification events
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | -<> |
Value: 2D3C3E00440B0000010000000000000000000000 | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2884) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD49E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2884 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ovid19.doc | pgc | |
MD5:0FF195F0C386FDBF7113AA5052A4F87C | SHA256:21E494EB047B4D1ED54C879A7F065D10DCF5677D2C4A311E8A4B3CBCA7B15CEB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2884 | WINWORD.EXE | 34.247.80.95:443 | cdn.javacon.eu | Amazon.com, Inc. | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.javacon.eu |
| unknown |