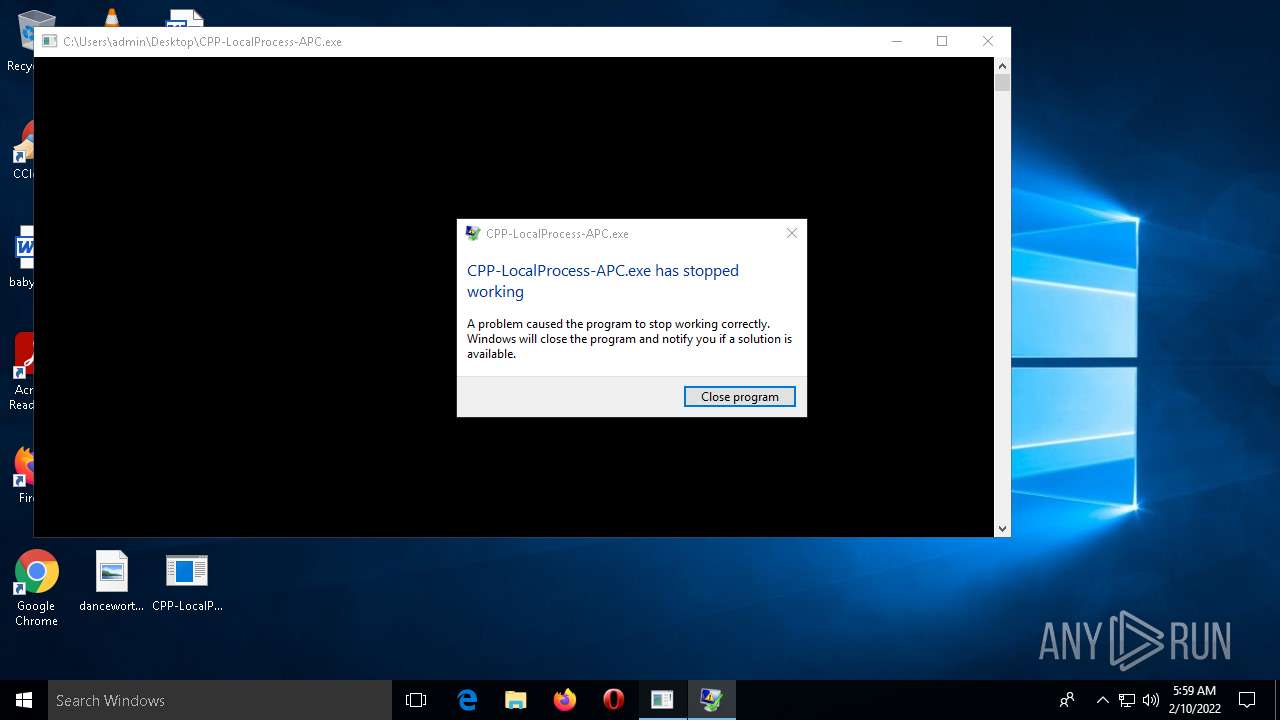
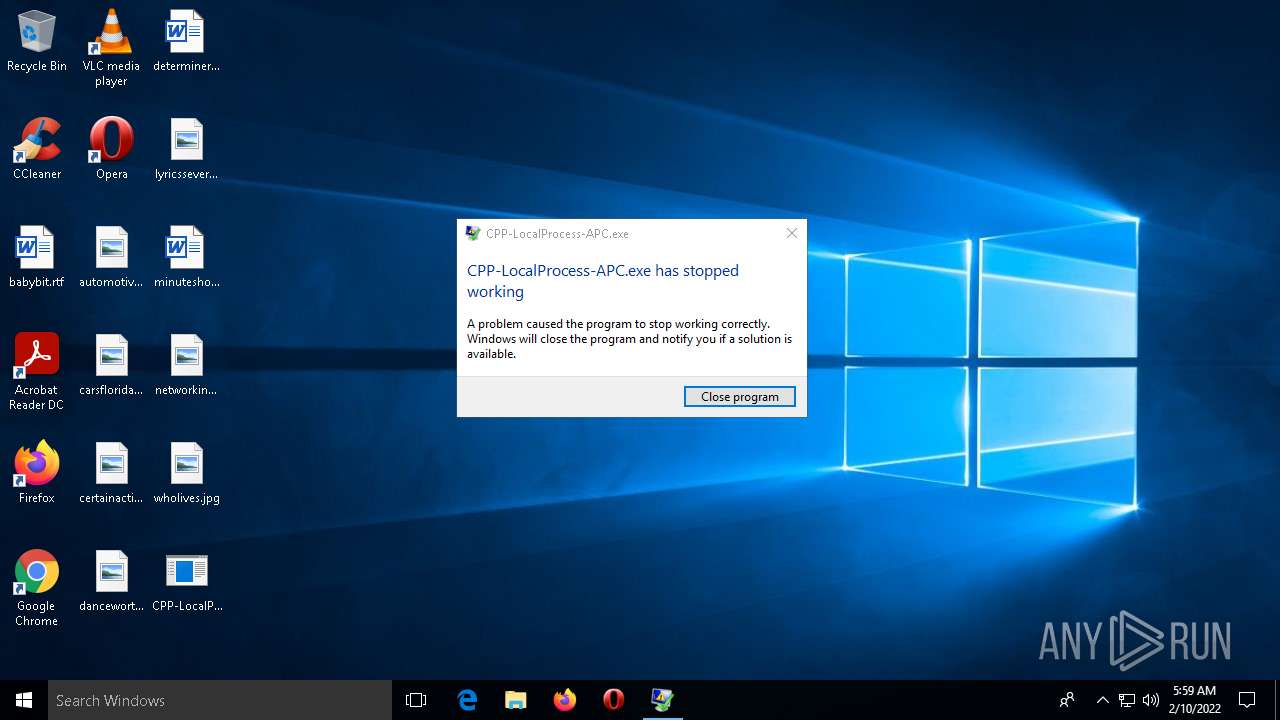
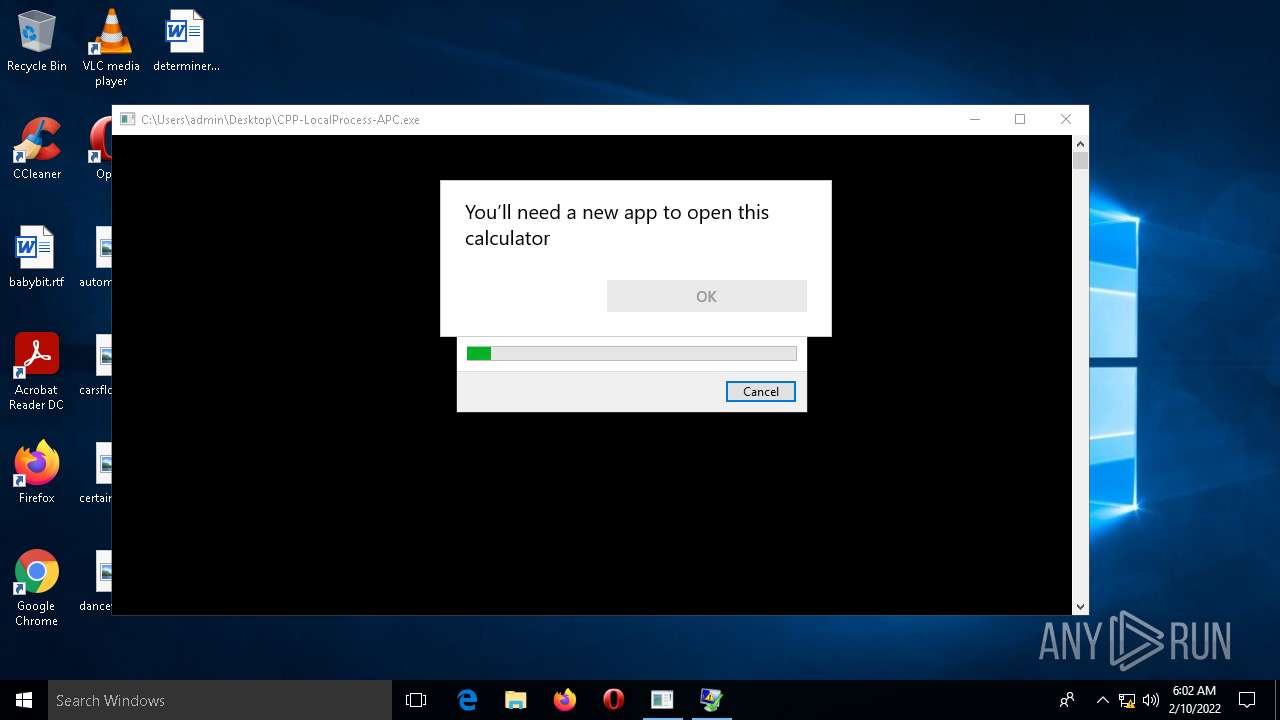
| File name: | CPP-LocalProcess-APC.exe |
| Full analysis: | https://app.any.run/tasks/4fcb68a8-30b3-4514-844f-a7cf54e2a53c |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2022, 05:58:54 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | C0BB2741052FE7832B8772FE0B8E7163 |
| SHA1: | BD52F17BBFA4F7BCC914408CFBA80668088AF212 |
| SHA256: | 4D6E64E6AEAD13350FAB7DC950D07EF7FE008F67C47B9EE39C493C5D47053F0A |
| SSDEEP: | 192:FqeNQlpOP3mOy7iFOb+ci3Q5tfBDieIZX:FDQlpKymO+F3neIZX |
MALICIOUS
Scans artifacts that could help determine the target
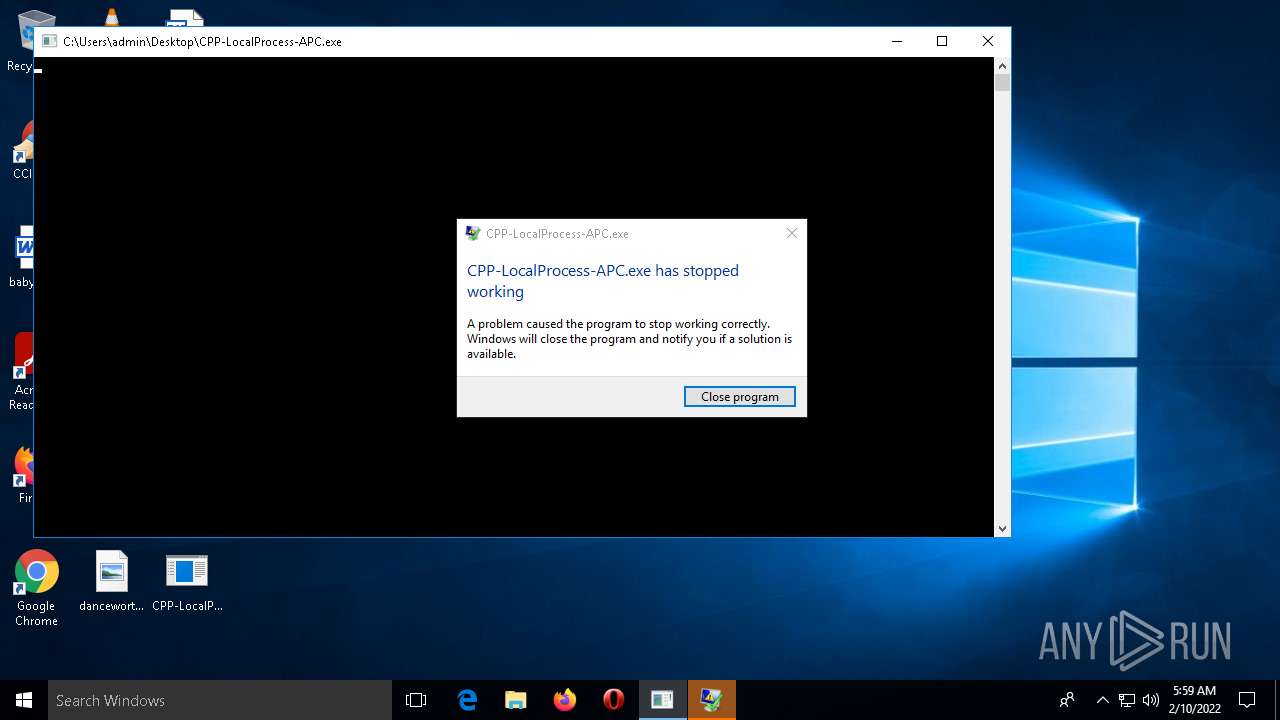
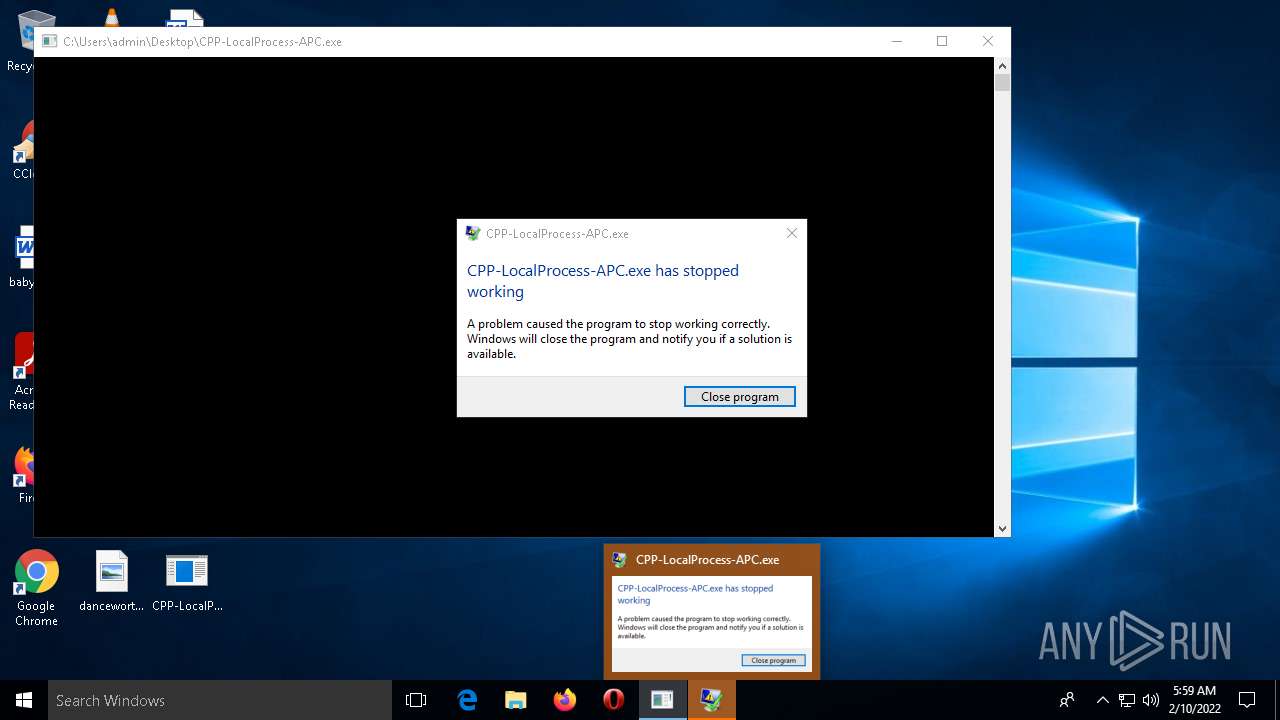
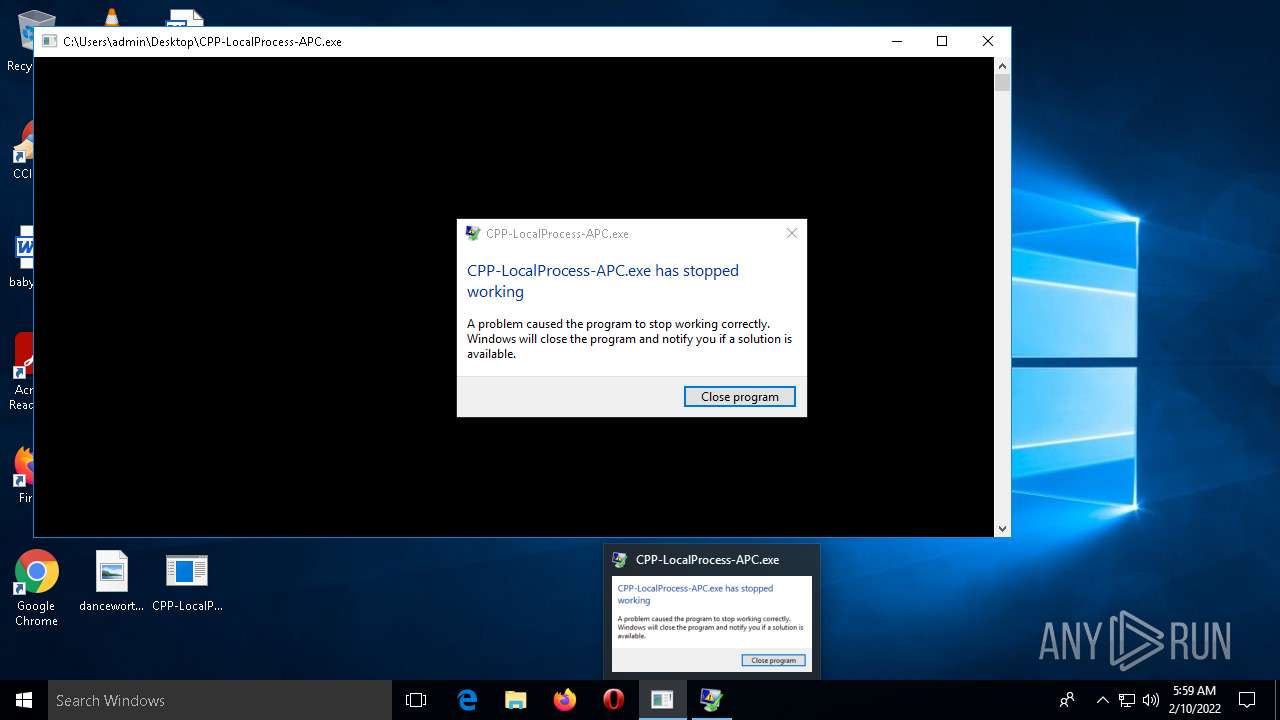
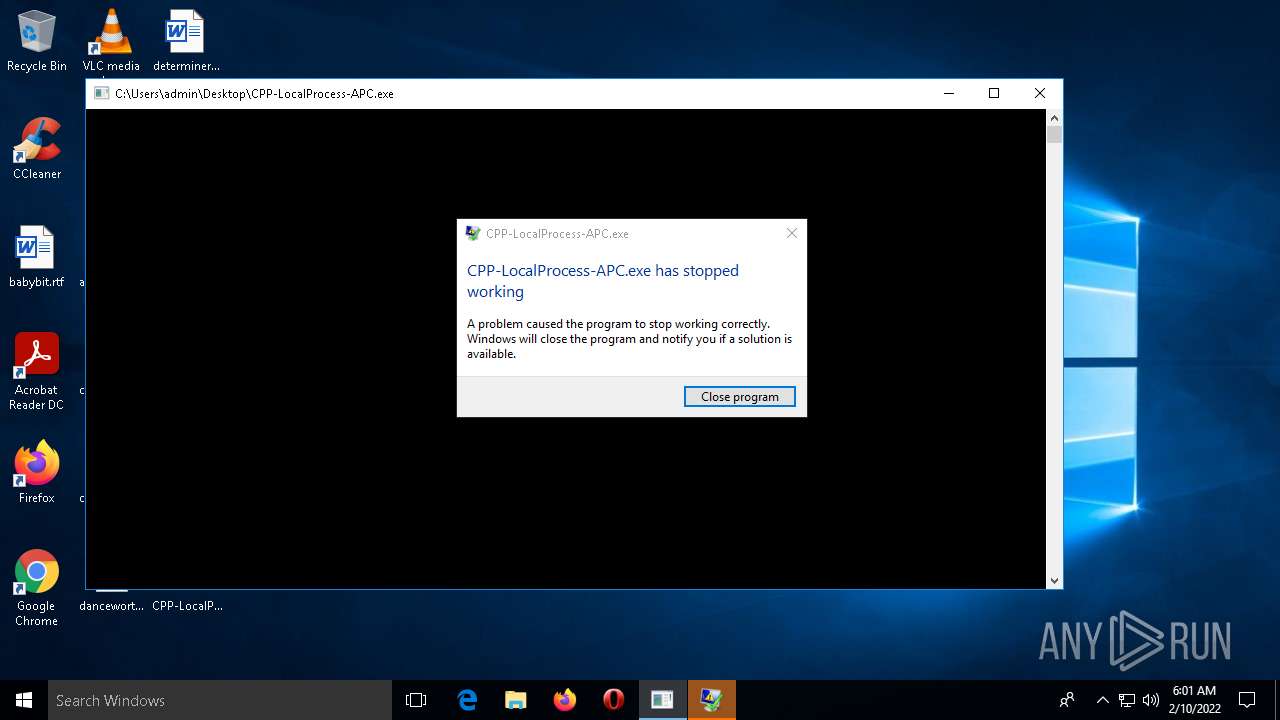
- WerFault.exe (PID: 4512)
- WerFault.exe (PID: 4540)
SUSPICIOUS
Checks supported languages
- conhost.exe (PID: 488)
- conhost.exe (PID: 408)
Reads the computer name
- conhost.exe (PID: 488)
- CPP-LocalProcess-APC.exe (PID: 1580)
- CPP-LocalProcess-APC.exe (PID: 3272)
- conhost.exe (PID: 408)
Creates files in the program directory
- WerFault.exe (PID: 4512)
- WerFault.exe (PID: 4540)
Reads Environment values
- WerFault.exe (PID: 4512)
- WerFault.exe (PID: 4540)
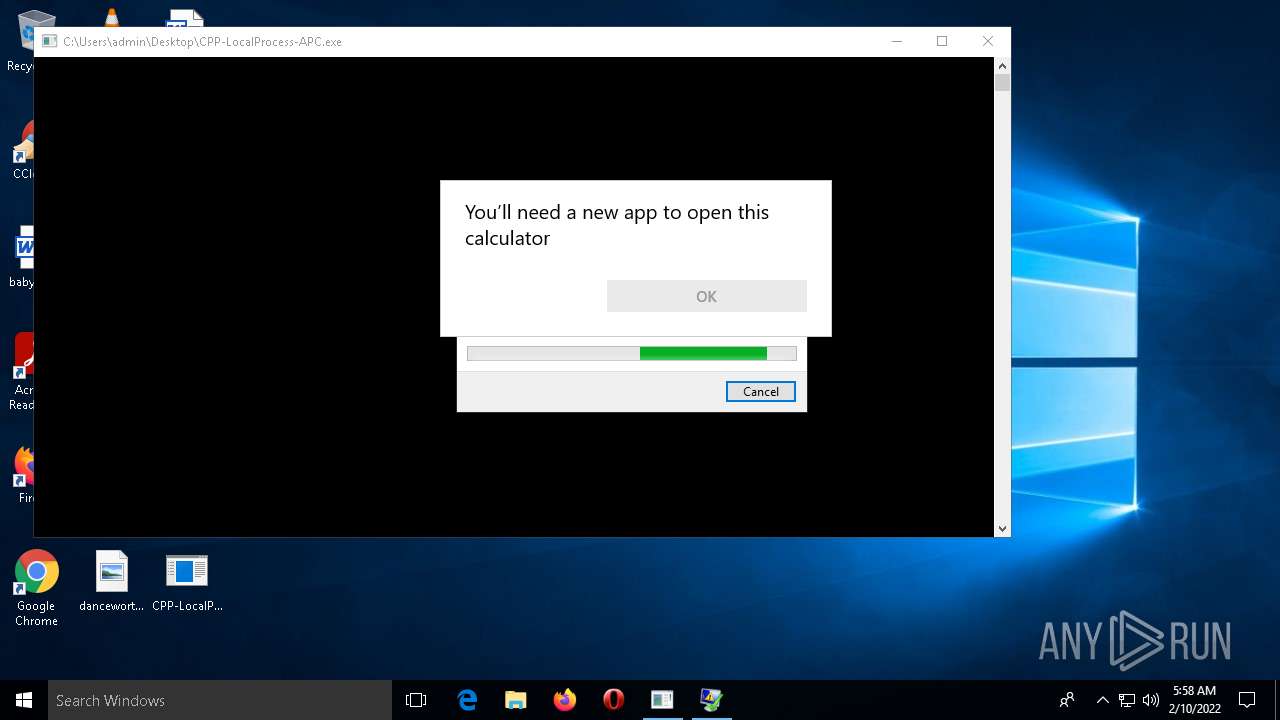
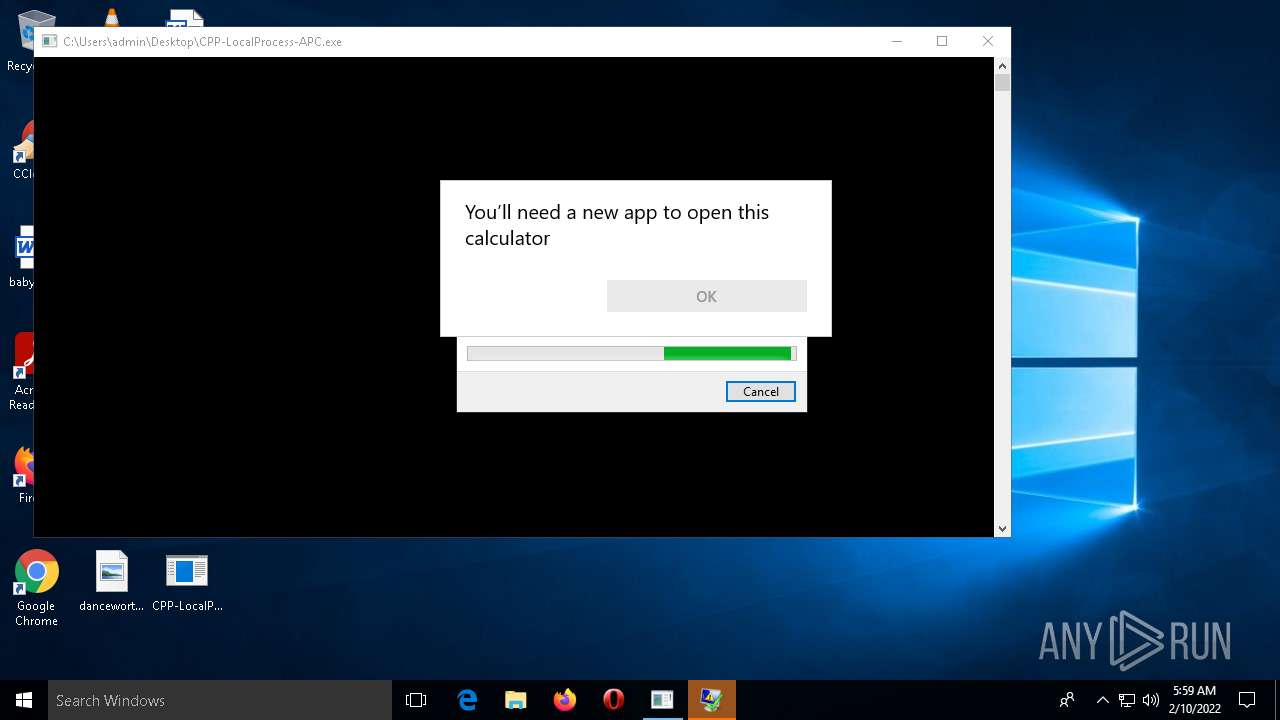
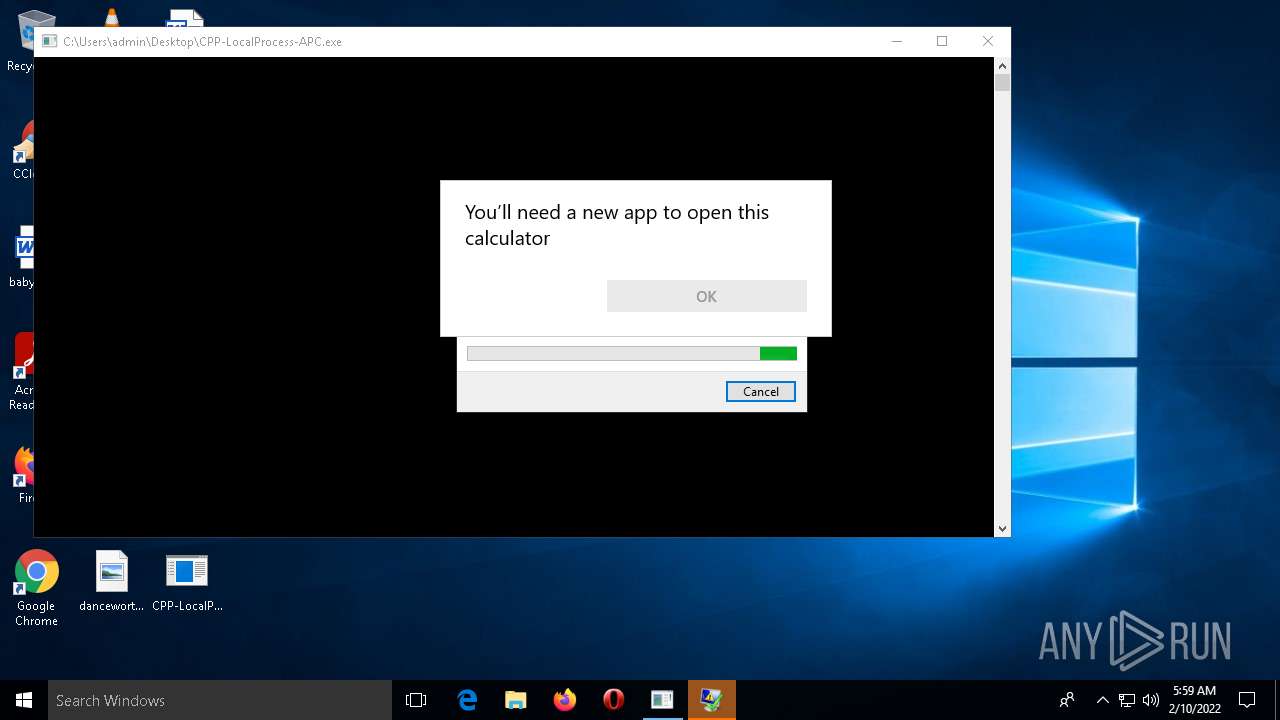
Executed via COM
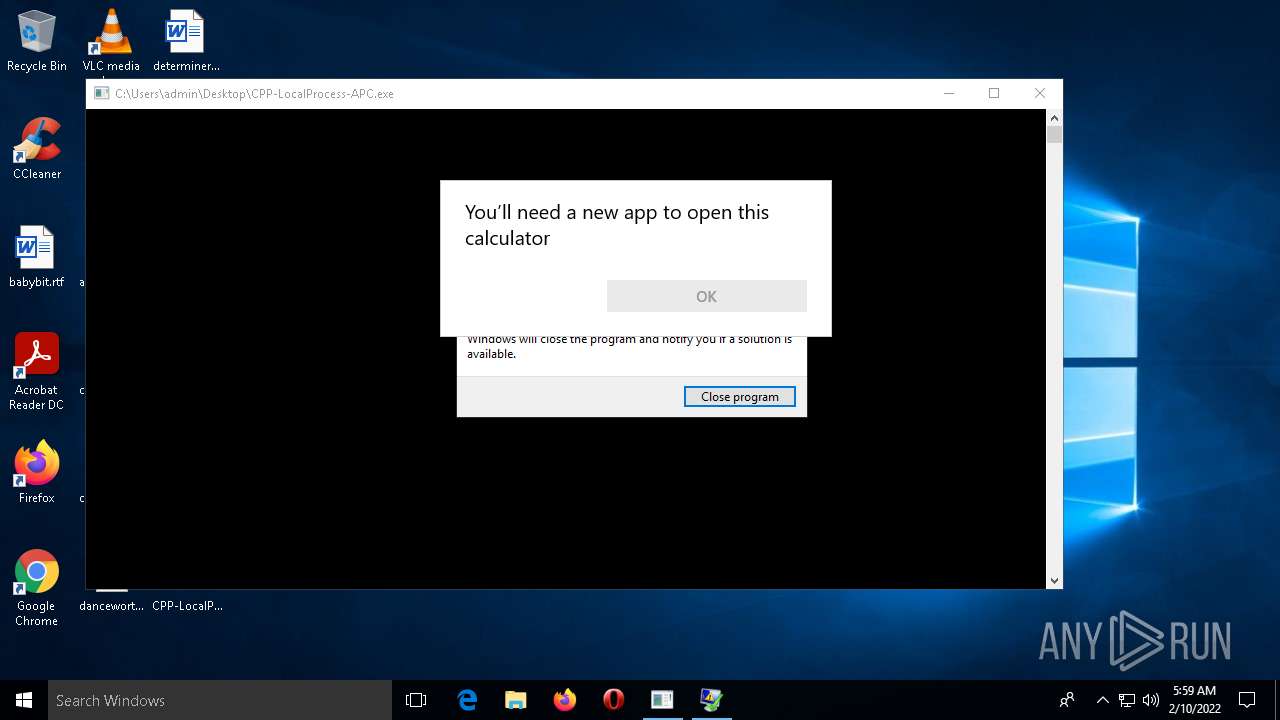
- OpenWith.exe (PID: 4324)
- OpenWith.exe (PID: 2220)
Reads the date of Windows installation
- WerFault.exe (PID: 4512)
- WerFault.exe (PID: 4540)
Executable content was dropped or overwritten
- WerFault.exe (PID: 4512)
- WerFault.exe (PID: 4540)
Drops a file with a compile date too recent
- WerFault.exe (PID: 4512)
- WerFault.exe (PID: 4540)
INFO
Checks supported languages
- calc.exe (PID: 5068)
- WerFault.exe (PID: 4512)
- OpenWith.exe (PID: 4324)
- calc.exe (PID: 1436)
- WerFault.exe (PID: 4540)
- OpenWith.exe (PID: 2220)
Reads the computer name
- calc.exe (PID: 5068)
- OpenWith.exe (PID: 4324)
- WerFault.exe (PID: 4512)
- calc.exe (PID: 1436)
- WerFault.exe (PID: 4540)
- OpenWith.exe (PID: 2220)
Reads settings of System Certificates
- WerFault.exe (PID: 4512)
- WerFault.exe (PID: 4540)
Reads CPU info
- WerFault.exe (PID: 4512)
- WerFault.exe (PID: 4540)
Reads the software policy settings
- WerFault.exe (PID: 4512)
- WerFault.exe (PID: 4540)
Manual execution by user
- CPP-LocalProcess-APC.exe (PID: 3272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x17d0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 12800 |
| CodeSize: | 5120 |
| LinkerVersion: | 14.29 |
| PEType: | PE32+ |
| TimeStamp: | 2022:02:07 01:23:43+01:00 |
| MachineType: | AMD AMD64 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 07-Feb-2022 00:23:43 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 6 |
| Time date stamp: | 07-Feb-2022 00:23:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000123C | 0x00001400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.8158 |
.rdata | 0x00003000 | 0x000012B0 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.37013 |
.data | 0x00005000 | 0x00001698 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47974 |
.pdata | 0x00007000 | 0x000001C8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.41172 |
.rsrc | 0x00008000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.69612 |
.reloc | 0x00009000 | 0x00000058 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 1.19829 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
KERNEL32.dll |
RPCRT4.dll |
VCRUNTIME140.dll |
api-ms-win-crt-heap-l1-1-0.dll |
api-ms-win-crt-locale-l1-1-0.dll |
api-ms-win-crt-math-l1-1-0.dll |
api-ms-win-crt-runtime-l1-1-0.dll |
api-ms-win-crt-stdio-l1-1-0.dll |
Total processes
196
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | \??\C:\WINDOWS\system32\conhost.exe | CPP-LocalProcess-APC.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 488 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | \??\C:\WINDOWS\system32\conhost.exe | CPP-LocalProcess-APC.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1436 | calc.exe | C:\WINDOWS\SYSTEM32\calc.exe | — | CPP-LocalProcess-APC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Calculator Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1580 | "C:\Users\admin\Desktop\CPP-LocalProcess-APC.exe" | C:\Users\admin\Desktop\CPP-LocalProcess-APC.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 2220 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\WINDOWS\system32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Pick an app Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3272 | "C:\Users\admin\Desktop\CPP-LocalProcess-APC.exe" | C:\Users\admin\Desktop\CPP-LocalProcess-APC.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 4324 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\WINDOWS\system32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4512 | C:\WINDOWS\system32\WerFault.exe -u -p 1580 -s 412 | C:\WINDOWS\system32\WerFault.exe | CPP-LocalProcess-APC.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4540 | C:\WINDOWS\system32\WerFault.exe -u -p 3272 -s 416 | C:\WINDOWS\system32\WerFault.exe | CPP-LocalProcess-APC.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5068 | calc.exe | C:\WINDOWS\SYSTEM32\calc.exe | — | CPP-LocalProcess-APC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 672
Read events
2 621
Write events
48
Delete events
3
Modification events
| (PID) Process: | (5068) calc.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\61\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (5068) calc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5068) calc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5068) calc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4324) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4324) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4324) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4512) WerFault.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\61\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1436) calc.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\61\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1436) calc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
2
Suspicious files
2
Text files
4
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4512 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERA6C2.tmp.dmp | dmp | |
MD5:— | SHA256:— | |||
| 4512 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERA751.tmp.WERInternalMetadata.xml | xml | |
MD5:— | SHA256:— | |||
| 4512 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:— | SHA256:— | |||
| 4512 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | der | |
MD5:— | SHA256:— | |||
| 4512 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_CPP-LocalProcess_1932bd3dc598deddc6525eed2ecae8421f4e7093_465b7fb9_11be1ee0\Report.wer | text | |
MD5:— | SHA256:— | |||
| 4512 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | der | |
MD5:— | SHA256:— | |||
| 4540 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER781C.tmp.dmp | dmp | |
MD5:— | SHA256:— | |||
| 4512 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:— | SHA256:— | |||
| 4512 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WAXA6C3.tmp | executable | |
MD5:— | SHA256:— | |||
| 4540 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\CPP-LocalProcess-APC.exe.3272.dmp | dmp | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
23
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2040 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3636 | svchost.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | der | 814 b | whitelisted |
4512 | WerFault.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | der | 814 b | whitelisted |
3636 | svchost.exe | GET | 200 | 178.18.231.171:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | der | 1.11 Kb | whitelisted |
4512 | WerFault.exe | GET | 200 | 178.18.231.171:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | der | 1.11 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2040 | svchost.exe | 20.190.154.17:443 | login.live.com | Microsoft Corporation | US | suspicious |
2040 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4512 | WerFault.exe | 52.182.143.212:443 | watson.telemetry.microsoft.com | Microsoft Corporation | US | suspicious |
4512 | WerFault.exe | 2.18.233.62:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
4540 | WerFault.exe | 20.189.173.21:443 | watson.telemetry.microsoft.com | Microsoft Corporation | US | suspicious |
3636 | svchost.exe | 178.18.231.171:80 | crl.microsoft.com | Peering Ltd | RU | suspicious |
3636 | svchost.exe | 20.189.173.21:443 | watson.telemetry.microsoft.com | Microsoft Corporation | US | suspicious |
2876 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | — | US | whitelisted |
3636 | svchost.exe | 2.18.233.62:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
4512 | WerFault.exe | 178.18.231.171:80 | crl.microsoft.com | Peering Ltd | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
watson.telemetry.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
config.edge.skype.com |
| malicious |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |