| File name: | hytale.exe |
| Full analysis: | https://app.any.run/tasks/7f480f3a-913e-4c9d-a085-849f6b4806c9 |
| Verdict: | Malicious activity |
| Analysis date: | September 02, 2021, 18:47:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 15C6FF3060B98452D14C266BAD4A555F |
| SHA1: | 931C5CD439216DB1D07B832DB98B7720F3313C54 |
| SHA256: | 4D5334077FB53EDD67EA2DDC47E45900ADBF038A3754E6351C4DC563ACD4C394 |
| SSDEEP: | 98304:vqfr8qjV5REqFsCwv6mfin14F4AMbogmZMznOWE1tDxxZqv:igqjvwibF92x/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- hytale.exe (PID: 908)
- filezilla.exe (PID: 2032)
Reads the computer name
- hytale.exe (PID: 908)
- filezilla.exe (PID: 2032)
Creates files in the user directory
- filezilla.exe (PID: 2032)
INFO
Reads settings of System Certificates
- filezilla.exe (PID: 2032)
Manual execution by user
- filezilla.exe (PID: 2032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| ProductVersion: | 1.0.0.1 |
|---|---|
| ProductName: | TODO: <Product name> |
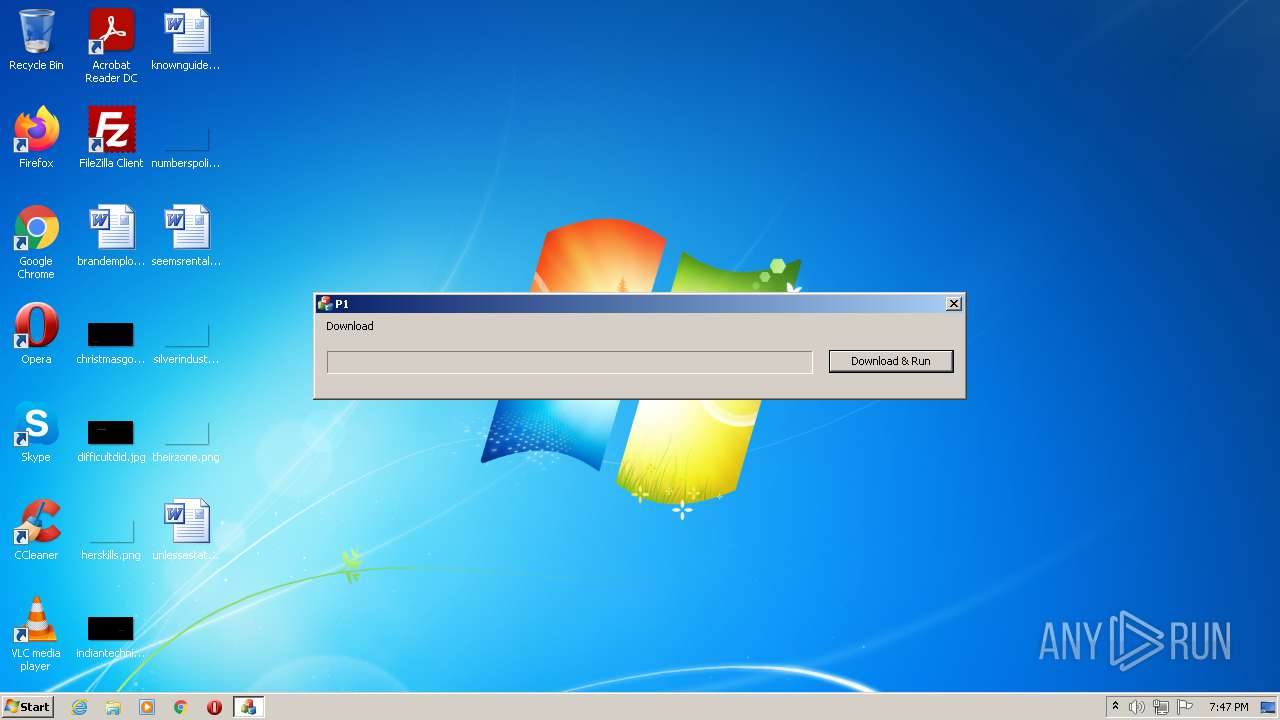
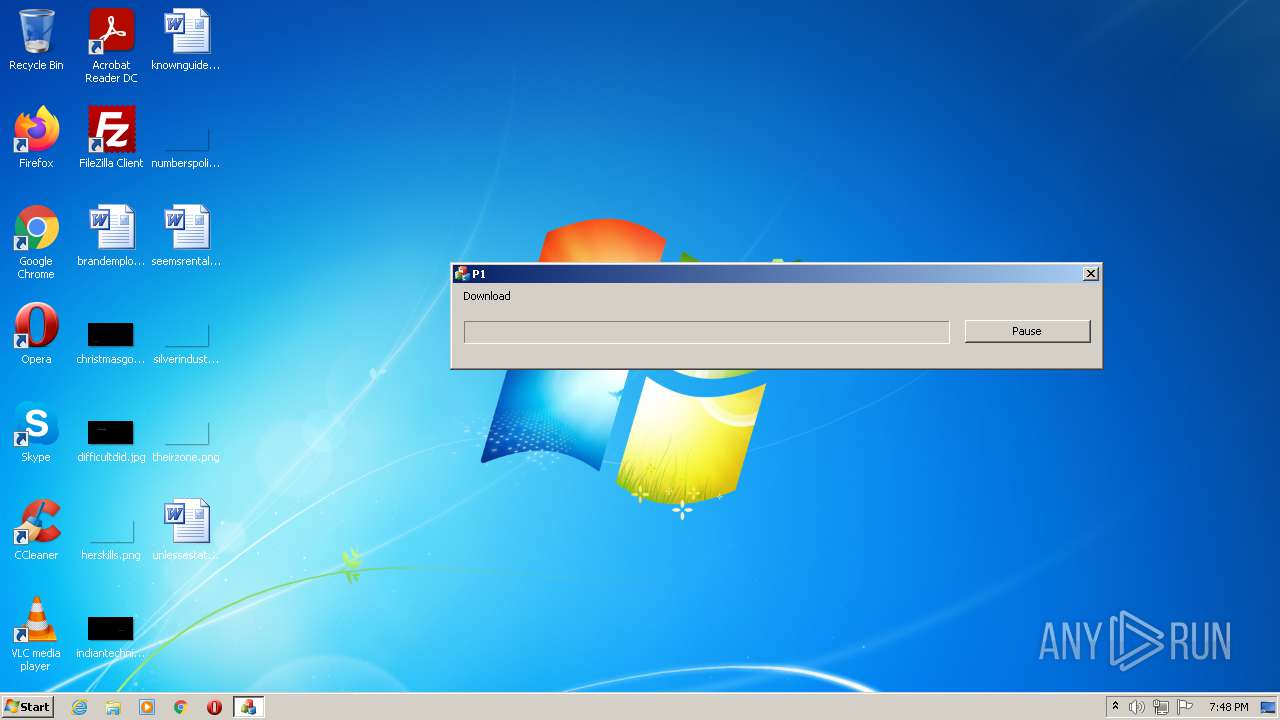
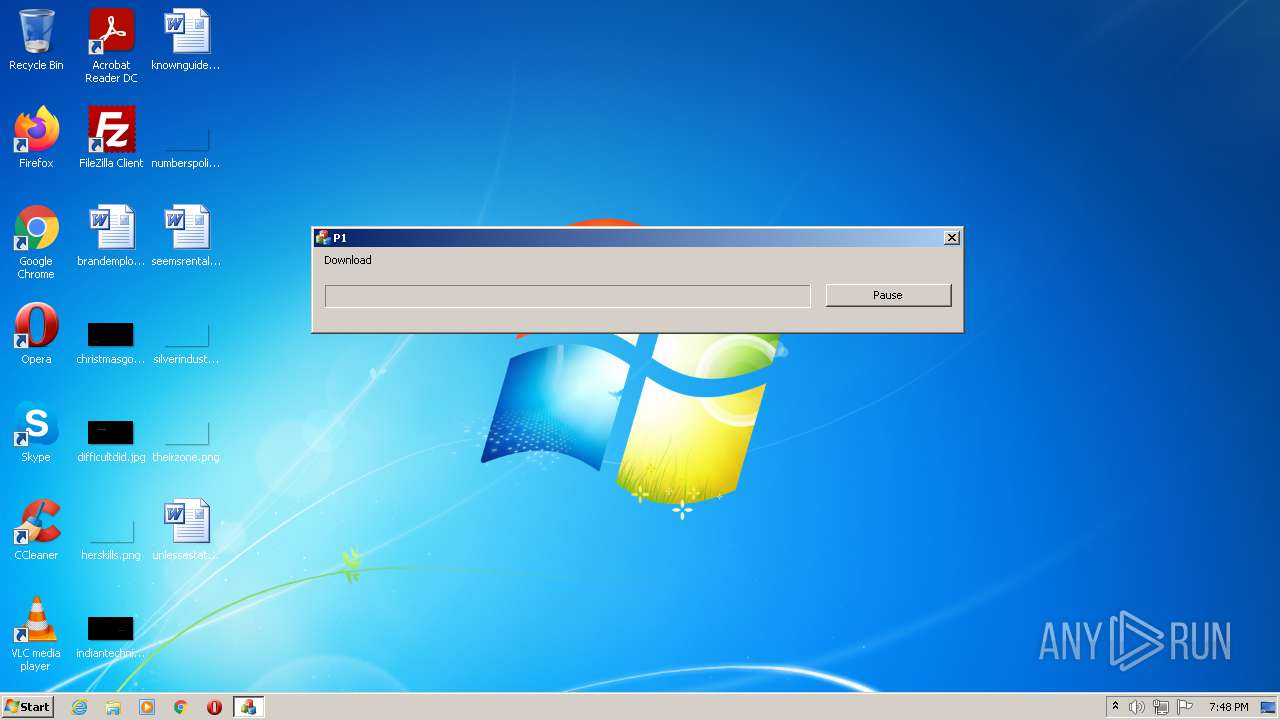
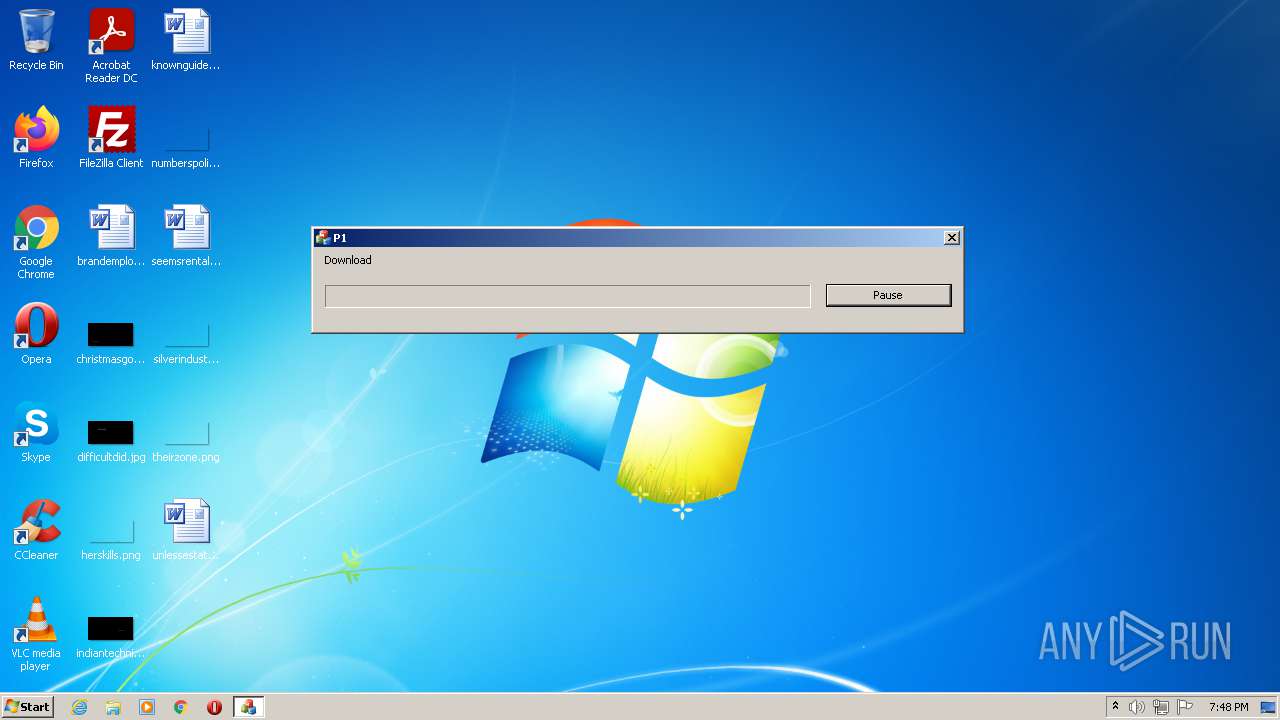
| OriginalFileName: | P1.exe |
| LegalCopyright: | TODO: (c) <Company name>. All rights reserved. |
| InternalName: | P1.exe |
| FileVersion: | 1.0.0.1 |
| FileDescription: | TODO: <File description> |
| CompanyName: | TODO: <Company name> |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.1 |
| FileVersionNumber: | 1.0.0.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x334542 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1218560 |
| CodeSize: | 3696640 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2016:11:21 17:18:07+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Nov-2016 16:18:07 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | TODO: <Company name> |
| FileDescription: | TODO: <File description> |
| FileVersion: | 1.0.0.1 |
| InternalName: | P1.exe |
| LegalCopyright: | TODO: (c) <Company name>. All rights reserved. |
| OriginalFilename: | P1.exe |
| ProductName: | TODO: <Product name> |
| ProductVersion: | 1.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Nov-2016 16:18:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x003866DE | 0x00386800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6297 |
.rdata | 0x00388000 | 0x000AF031 | 0x000AF200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.25412 |
.data | 0x00438000 | 0x0002C450 | 0x00021C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.19563 |
.rsrc | 0x00465000 | 0x00014B40 | 0x00014C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.69631 |
.reloc | 0x0047A000 | 0x00043C5C | 0x00043E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.40505 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02301 | 622 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.42849 | 744 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 4.16177 | 488 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 3.49987 | 296 | Latin 1 / Western European | Russian - Russia | RT_ICON |
5 | 5.77516 | 3752 | Latin 1 / Western European | Russian - Russia | RT_ICON |
6 | 6.154 | 2216 | Latin 1 / Western European | Russian - Russia | RT_ICON |
7 | 1.55585 | 56 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 4.98825 | 1384 | Latin 1 / Western European | Russian - Russia | RT_ICON |
9 | 7.95901 | 37835 | Latin 1 / Western European | Russian - Russia | RT_ICON |
10 | 5.35231 | 9640 | Latin 1 / Western European | Russian - Russia | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
MSWSOCK.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
??0context@ssl@asio@boost@@QAE@AAVio_service@23@W4method@context_base@123@@Z | 1 | 0x0011C530 |
??0context@ssl@asio@boost@@QAE@W4method@context_base@123@@Z | 2 | 0x0011C360 |
??0engine@detail@ssl@asio@boost@@QAE@PAUssl_ctx_st@@@Z | 3 | 0x00119EB0 |
??1context@ssl@asio@boost@@QAE@XZ | 4 | 0x00119CB0 |
??1engine@detail@ssl@asio@boost@@QAE@XZ | 5 | 0x001195A0 |
??Rrfc2818_verification@ssl@asio@boost@@QBE_N_NAAVverify_context@123@@Z | 6 | 0x0011A1E0 |
?accept_mutex@engine@detail@ssl@asio@boost@@CAAAUwin_static_mutex@245@XZ | 7 | 0x001196E0 |
?add_certificate_authority@context@ssl@asio@boost@@QAE?AVerror_code@system@4@ABVconst_buffer@34@AAV564@@Z | 8 | 0x0011A5E0 |
?add_certificate_authority@context@ssl@asio@boost@@QAEXABVconst_buffer@34@@Z | 9 | 0x0011B360 |
?add_verify_path@context@ssl@asio@boost@@QAE?AVerror_code@system@4@ABV?$basic_string@DU?$char_traits@D@std@@V?$allocator@D@2@@std@@AAV564@@Z | 10 | 0x0011A770 |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 908 | "C:\Users\admin\AppData\Local\Temp\hytale.exe" | C:\Users\admin\AppData\Local\Temp\hytale.exe | Explorer.EXE | ||||||||||||
User: admin Company: TODO: <Company name> Integrity Level: MEDIUM Description: TODO: <File description> Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
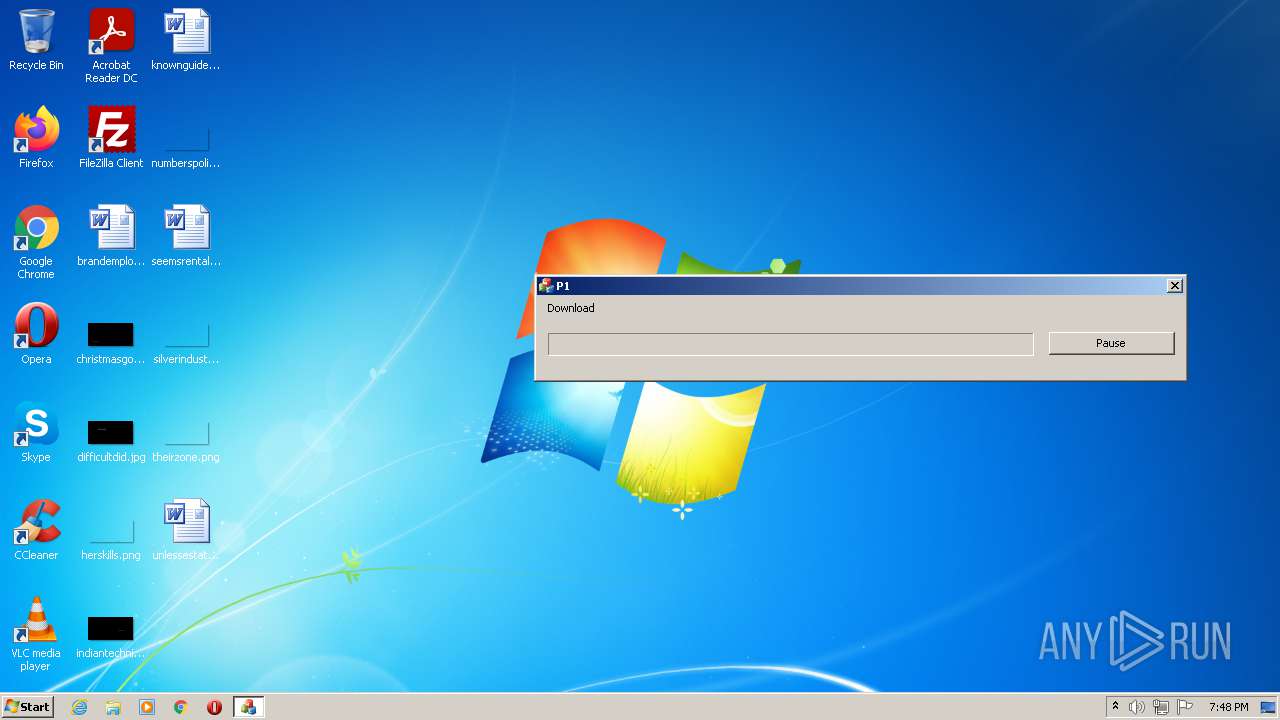
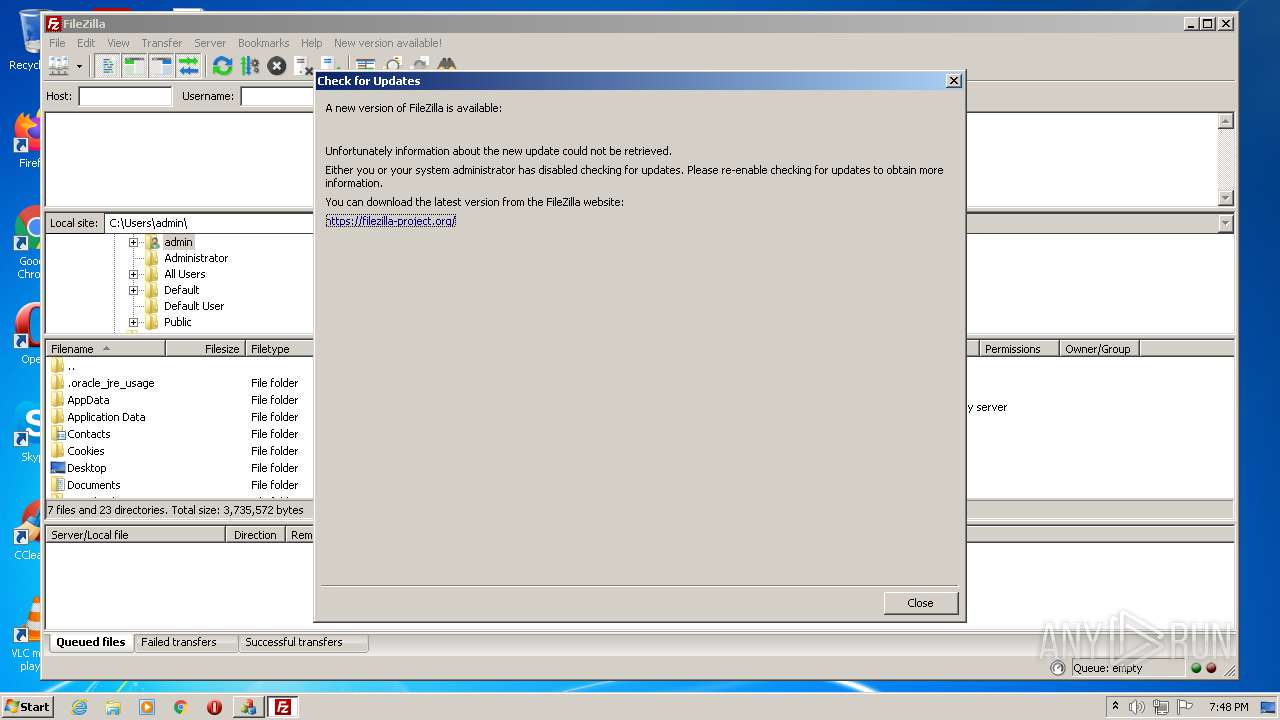
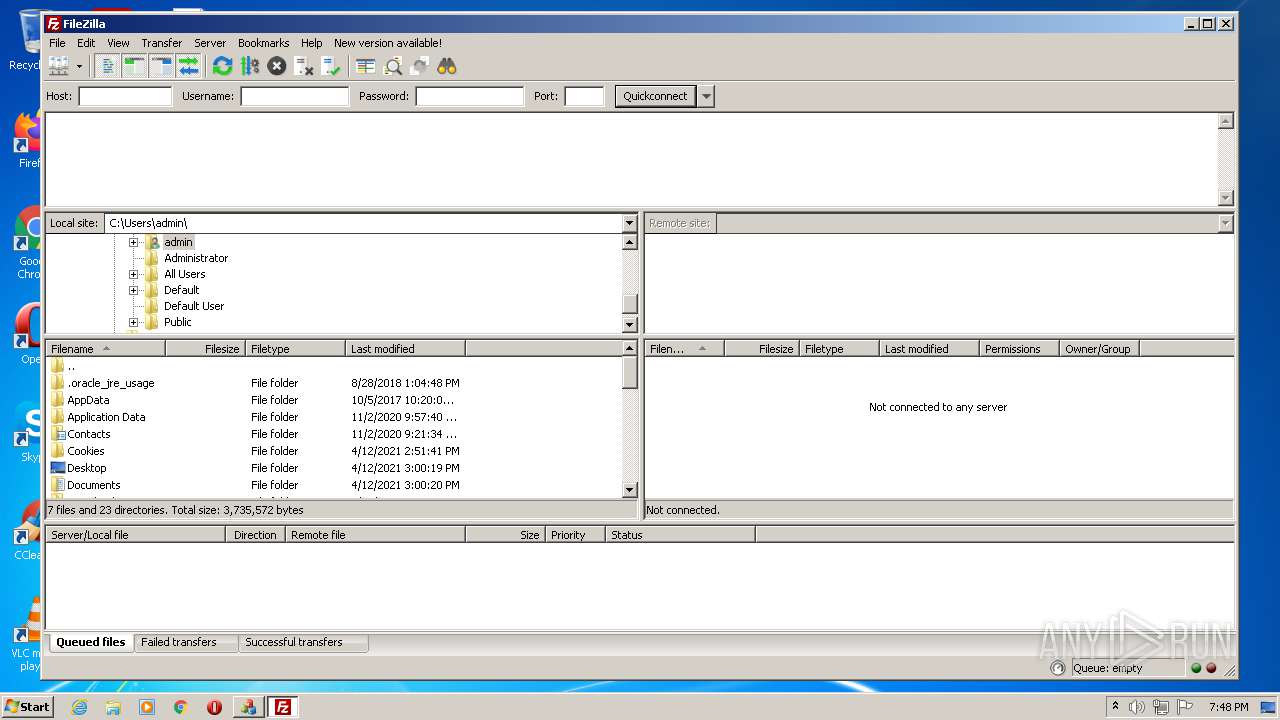
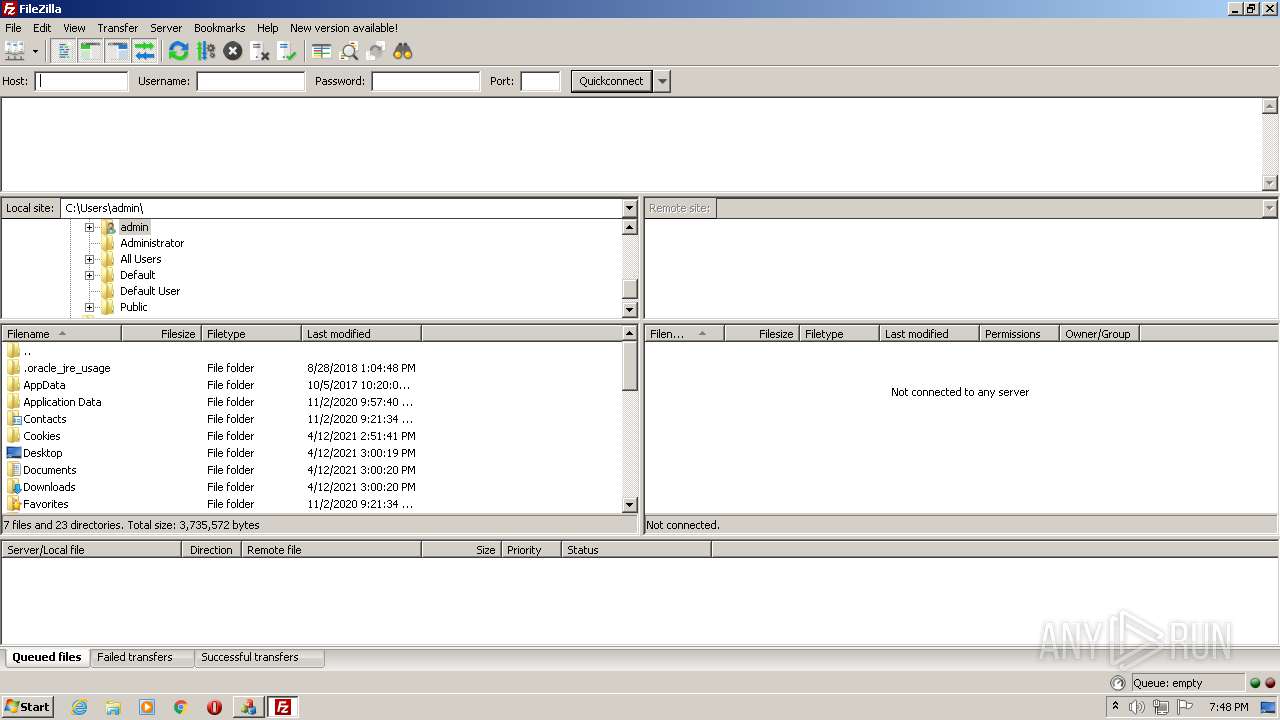
| 2032 | "C:\Program Files\FileZilla FTP Client\filezilla.exe" | C:\Program Files\FileZilla FTP Client\filezilla.exe | — | Explorer.EXE | |||||||||||
User: admin Company: FileZilla Project Integrity Level: MEDIUM Description: FileZilla FTP Client Exit code: 0 Version: 3, 51, 0, 0 Modules
| |||||||||||||||
Total events
2 321
Read events
2 321
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2032 | filezilla.exe | C:\Users\admin\AppData\Roaming\FileZilla\layout.xml | xml | |
MD5:F76334C9999EBFBFC0BAFE574784CDA6 | SHA256:62FD434F500CDE527D0C1CF2CEF956F896A48F8D2071DBCA1A505A11E08363D7 | |||
| 2032 | filezilla.exe | C:\Users\admin\AppData\Roaming\FileZilla\layout.xml~ | xml | |
MD5:F76334C9999EBFBFC0BAFE574784CDA6 | SHA256:62FD434F500CDE527D0C1CF2CEF956F896A48F8D2071DBCA1A505A11E08363D7 | |||
| 2032 | filezilla.exe | C:\Users\admin\AppData\Roaming\FileZilla\filezilla.xml~ | xml | |
MD5:AC690D623632CCC4D9660A534DBF61F0 | SHA256:4814FDBC8B68A7CFA3D880F8835391901A6A095F53CD1B8D5696EBBF6D39F224 | |||
| 2032 | filezilla.exe | C:\Users\admin\AppData\Roaming\FileZilla\filezilla.xml | xml | |
MD5:5D739F53DEDCB4EC857682F9F36B3BAA | SHA256:23C8CA3E620A33AC8584A465DA415F35E63C354AB68D8CB009A6AD739487A697 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
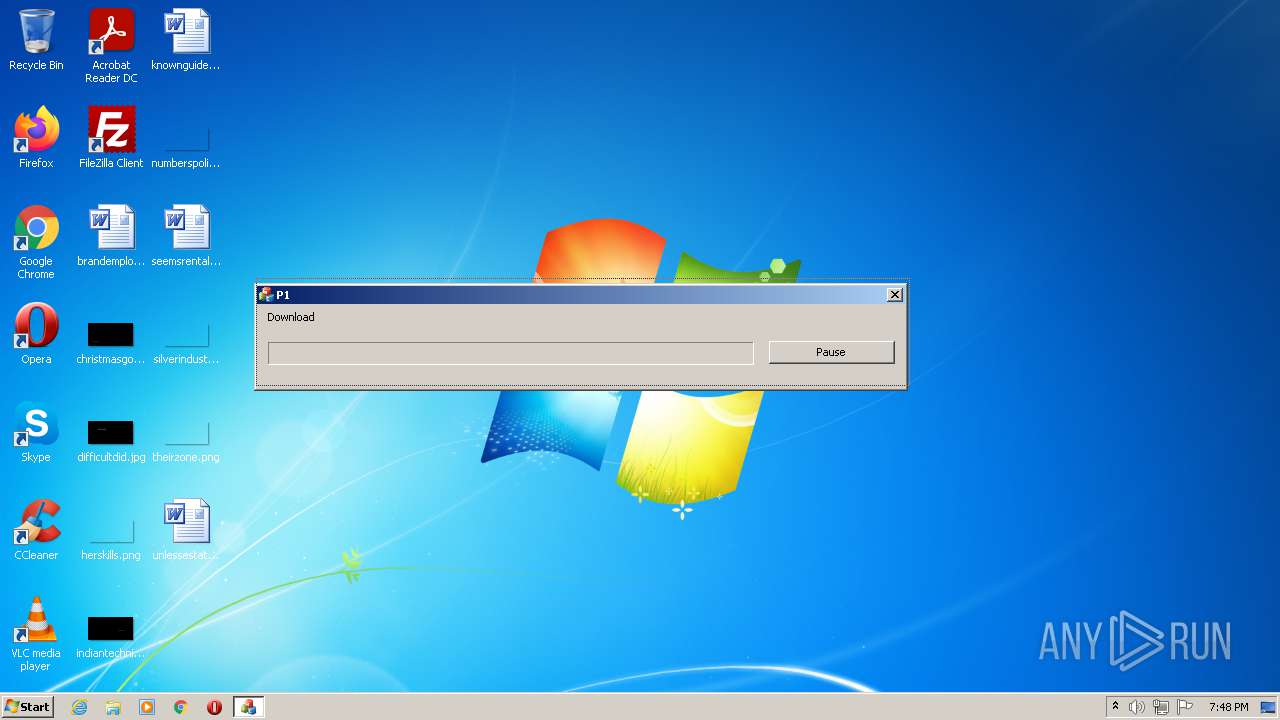
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
908 | hytale.exe | GET | 200 | 195.82.146.120:80 | http://bt.t-ru.org/ann?magnet&info_hash=%c1%87%14%5es%12%a6%da%9d%05Y%d4rI%8c%bat%26%12b&peer_id=-LT1000-NKnM5x)K1oiX&port=6881&uploaded=0&downloaded=0&left=16384&corrupt=0&key=1BDE96F9&event=started&numwant=200&compact=1&no_peer_id=1&supportcrypto=1&redundant=0 | RU | binary | 90 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
908 | hytale.exe | 195.82.146.120:80 | bt.t-ru.org | Dreamtorrent Corp | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
router.bittorrent.com |
| shared |
router.utorrent.com |
| whitelisted |
router.bitcomet.com |
| unknown |
bt.t-ru.org |
| malicious |