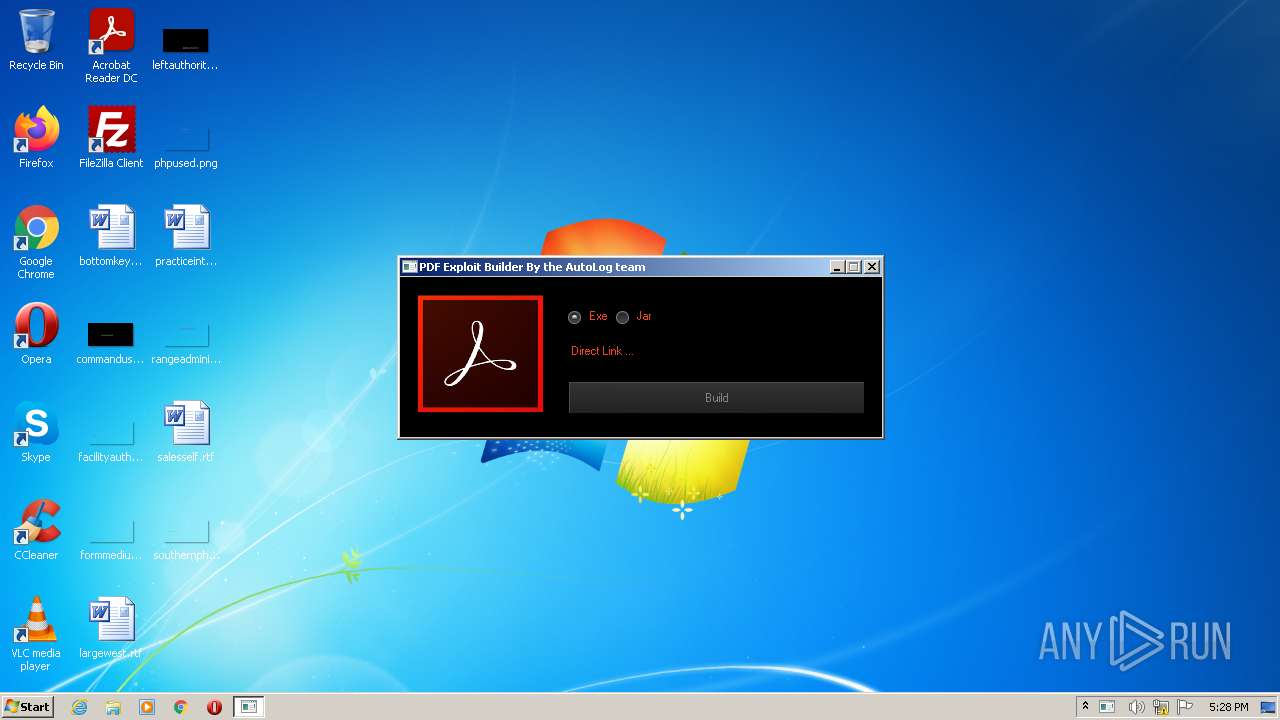
| File name: | PDFExploitBuilder.exe |
| Full analysis: | https://app.any.run/tasks/ce725151-6fd7-486d-832a-26b0c96ebaec |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 17:28:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 42C39D642A824E2D68384263E4F7A99A |
| SHA1: | 5EC51097CF3440AD7FC28B1E0F86F5491322A28C |
| SHA256: | 4D44E7D6BC3423672A623586196D0D6C7BF24DC82CE3EC7B2D800FDC64C16B15 |
| SSDEEP: | 49152:i7OKi1DaHy33jVWWmUkDd7snVJlXkZ8e43u:iKXaHyHjVWSkDd7sMrg |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- PDFExploitBuilder.exe (PID: 2972)
Reads mouse settings
- PDFExploitBuilder.exe (PID: 2972)
Reads the computer name
- PDFExploitBuilder.exe (PID: 2972)
Executable content was dropped or overwritten
- PDFExploitBuilder.exe (PID: 2972)
Drops a file with too old compile date
- PDFExploitBuilder.exe (PID: 2972)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| CharacterSet: | Unicode |
|---|---|
| LanguageCode: | English (British) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x3f9de2 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 730112 |
| CodeSize: | 581120 |
| LinkerVersion: | 12 |
| PEType: | PE32 |
| TimeStamp: | 2016:10:23 17:05:14+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Oct-2016 15:05:14 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 23-Oct-2016 15:05:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DD2E | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.rdata | 0x0008F000 | 0x0002E10E | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.data | 0x000BE000 | 0x00008F74 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.obf0 | 0x000C7000 | 0x00198BDB | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.tls | 0x00260000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.obf1 | 0x00261000 | 0x0021834C | 0x00218400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92044 |
.reloc | 0x0047A000 | 0x00000144 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.61414 |
.rsrc | 0x0047B000 | 0x00006817 | 0x00006A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.97189 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2972 | "C:\Users\admin\AppData\Local\Temp\PDFExploitBuilder.exe" | C:\Users\admin\AppData\Local\Temp\PDFExploitBuilder.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
619
Read events
619
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
2
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | PDFExploitBuilder.exe | C:\Users\admin\AppData\Local\Temp\skin.888.msstyles | executable | |
MD5:719C51F5637D922E8416E23D0978B8CB | SHA256:6CF0BF46C9EE98FDE7EB4DBC0B147E33BABEABF9B1F50A4722E29DD57E95EF09 | |||
| 2972 | PDFExploitBuilder.exe | C:\Users\admin\AppData\Local\Temp\aut3802.tmp | image | |
MD5:C5422CD3F57E8951414CB23564026B89 | SHA256:D7E2C5DCE7CF4588CB7019BF7C6F79A3BEF3CC71E1F7513D3EAD18896C3519A3 | |||
| 2972 | PDFExploitBuilder.exe | C:\Users\admin\AppData\Local\Temp\ccws.mp3 | mp3 | |
MD5:5D576E372446A31B0B487E53A971089D | SHA256:4B4AB8243ED3BE25A58EB4BEF6CD27992640AE106734B8489472D22C73988AB6 | |||
| 2972 | PDFExploitBuilder.exe | C:\Users\admin\AppData\Local\Temp\aut37C0.tmp | binary | |
MD5:01A0C1BD8DEFC2DF7796D1E9542A2EBB | SHA256:2FD19F4D0636BE9A381C399792073BD49E67E8715254239EFC3ED729FE824865 | |||
| 2972 | PDFExploitBuilder.exe | C:\Users\admin\AppData\Local\Temp\aut37B0.tmp | binary | |
MD5:F68775DF364BF3E53EA9A614E6A04850 | SHA256:902E8AB1AC00ABE0241AF4C112E17A6315763E1DB6D3B5BAFD7252C6E278CBCF | |||
| 2972 | PDFExploitBuilder.exe | C:\Users\admin\AppData\Local\Temp\fbhcyjo | text | |
MD5:B905723DF6A00F3ED696BC751D9DB4D5 | SHA256:64A47DD26BAFFF7DEE1D2EEBDDB03D0A6D50906F258187FE0988A663EE3D2117 | |||
| 2972 | PDFExploitBuilder.exe | C:\Users\admin\AppData\Local\Temp\ShowImage.jpg | image | |
MD5:C5422CD3F57E8951414CB23564026B89 | SHA256:D7E2C5DCE7CF4588CB7019BF7C6F79A3BEF3CC71E1F7513D3EAD18896C3519A3 | |||
| 2972 | PDFExploitBuilder.exe | C:\Users\admin\AppData\Local\Temp\aut37E1.tmp | executable | |
MD5:29E1D5770184BF45139084BCED50D306 | SHA256:794987C4069286F797631F936C73B925C663C42D552AECA821106DFC7C7BA307 | |||
| 2972 | PDFExploitBuilder.exe | C:\Users\admin\AppData\Local\Temp\aut3801.tmp | mp3 | |
MD5:5D576E372446A31B0B487E53A971089D | SHA256:4B4AB8243ED3BE25A58EB4BEF6CD27992640AE106734B8489472D22C73988AB6 | |||
| 2972 | PDFExploitBuilder.exe | C:\Users\admin\AppData\Local\Temp\skin.dll | executable | |
MD5:29E1D5770184BF45139084BCED50D306 | SHA256:794987C4069286F797631F936C73B925C663C42D552AECA821106DFC7C7BA307 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report