| File name: | DumpIt.exe |
| Full analysis: | https://app.any.run/tasks/13bc8d06-be68-4877-8cce-79c78ebac86c |
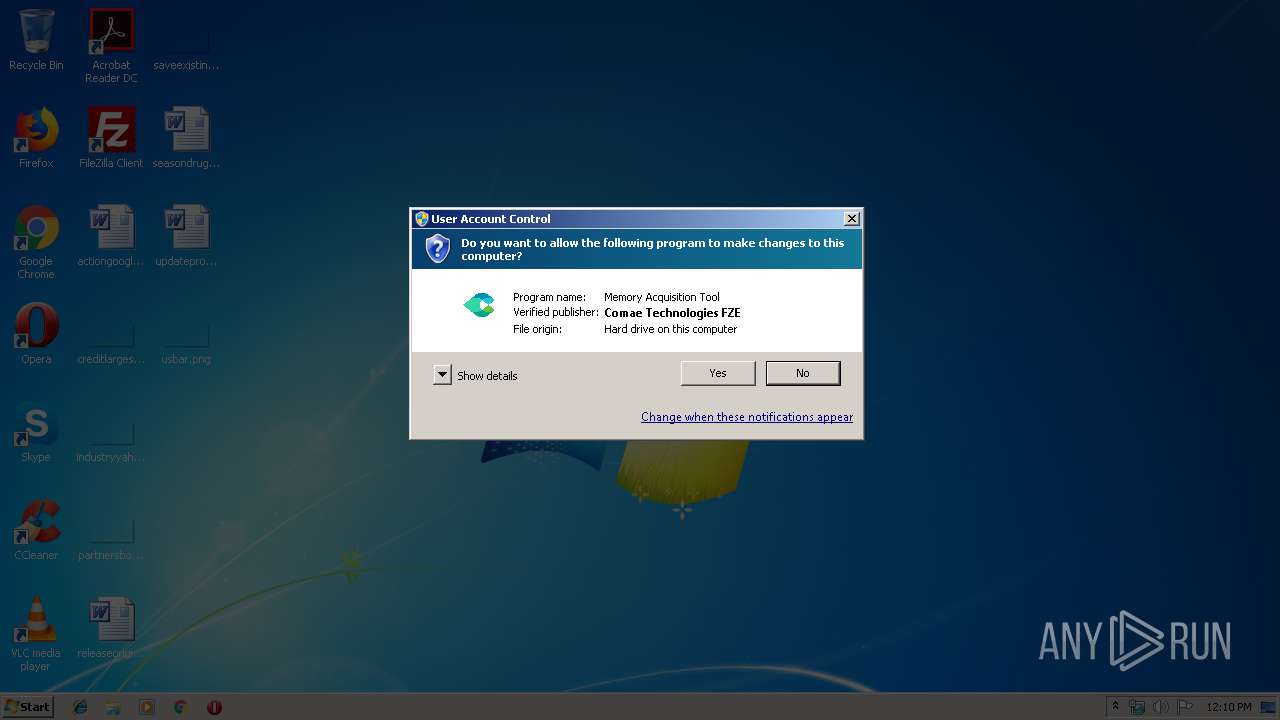
| Verdict: | No threats detected |
| Analysis date: | July 19, 2019, 11:09:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 2B5CEA63D21F275BAD67634E7BF9B68E |
| SHA1: | 6CEBFA8CDA8156A3EC96206D06CF45AB5D67AC4F |
| SHA256: | 4D2A26556E93302F8E57399042BB1CAC98E9B4A315D5685AE627CC5414C74E02 |
| SSDEEP: | 6144:A1XaqckmFENm2eK7mnoUSgpAY8ODcDcm7cIsRhm3MK3WsmvB+bcLDwUrAYdAOkbV:A1XIkOhdK3WsmJW+DFJ+QsO593Y |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the Windows directory
- DumpIt.exe (PID: 2924)
Creates files in the driver directory
- DumpIt.exe (PID: 2924)
Removes files from Windows directory
- DumpIt.exe (PID: 2924)
Creates or modifies windows services
- DumpIt.exe (PID: 2924)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:07 13:32:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.12 |
| CodeSize: | 251392 |
| InitializedDataSize: | 200192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x18050 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 3.0.0.0 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Comae Technologies FZE |
| FileDescription: | Memory Acquisition Tool |
| FileVersion: | 3.0.0.0 |
| InternalName: | DumpIt.exe |
| LegalCopyright: | Copyright (C) 2017 Comae Technologies FZE |
| OriginalFileName: | DumpIt.exe |
| ProductName: | Comae Toolkit |
| ProductVersion: | 3.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 07-Mar-2018 12:32:41 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Comae Technologies FZE |
| FileDescription: | Memory Acquisition Tool |
| FileVersion: | 3.0.0.0 |
| InternalName: | DumpIt.exe |
| LegalCopyright: | Copyright (C) 2017 Comae Technologies FZE |
| OriginalFilename: | DumpIt.exe |
| ProductName: | Comae Toolkit |
| ProductVersion: | 3.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 07-Mar-2018 12:32:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003D57C | 0x0003D600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62891 |
.rdata | 0x0003F000 | 0x0001651A | 0x00016600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.299 |
.data | 0x00056000 | 0x000023BC | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.49152 |
.rsrc | 0x00059000 | 0x00014EA0 | 0x00015000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.18635 |
.reloc | 0x0006E000 | 0x000033B0 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.63956 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.14302 | 78016 | UNKNOWN | English - United States | BIN |
Imports
ADVAPI32.dll |
KERNEL32.dll |
NETAPI32.dll |
OLEAUT32.dll |
SHLWAPI.dll |
WINHTTP.dll |
WS2_32.dll |
ole32.dll |
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
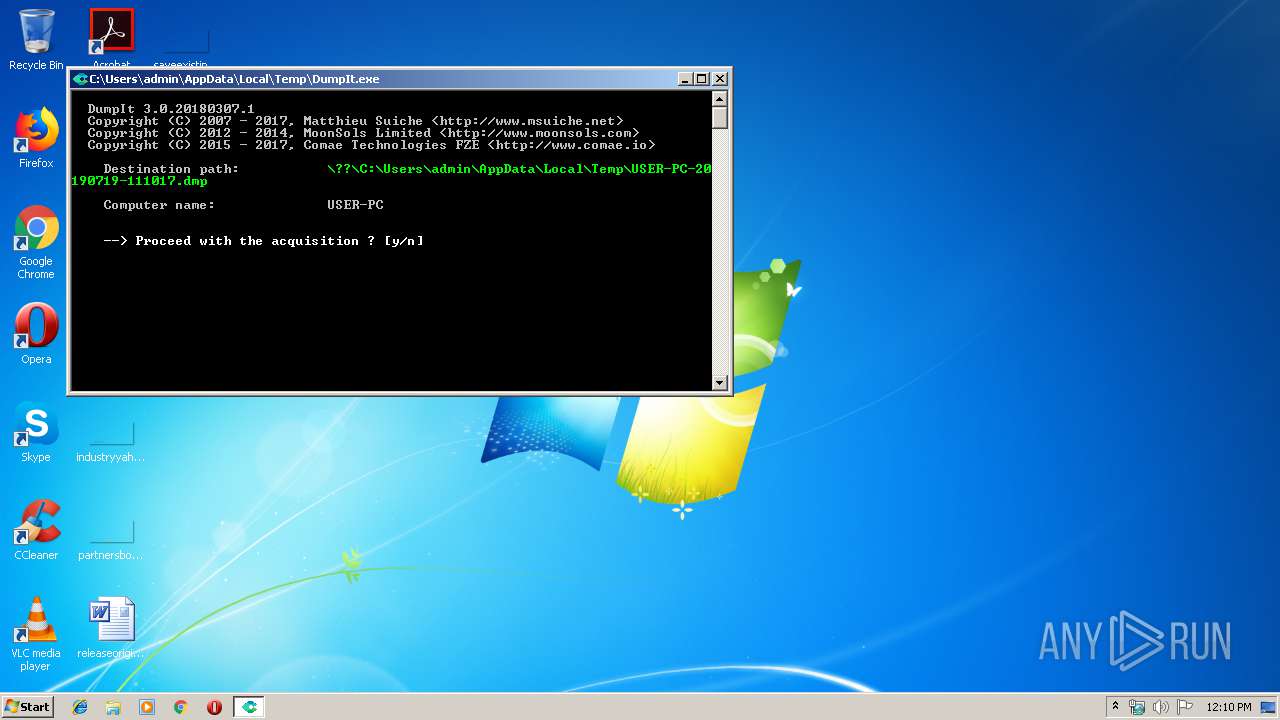
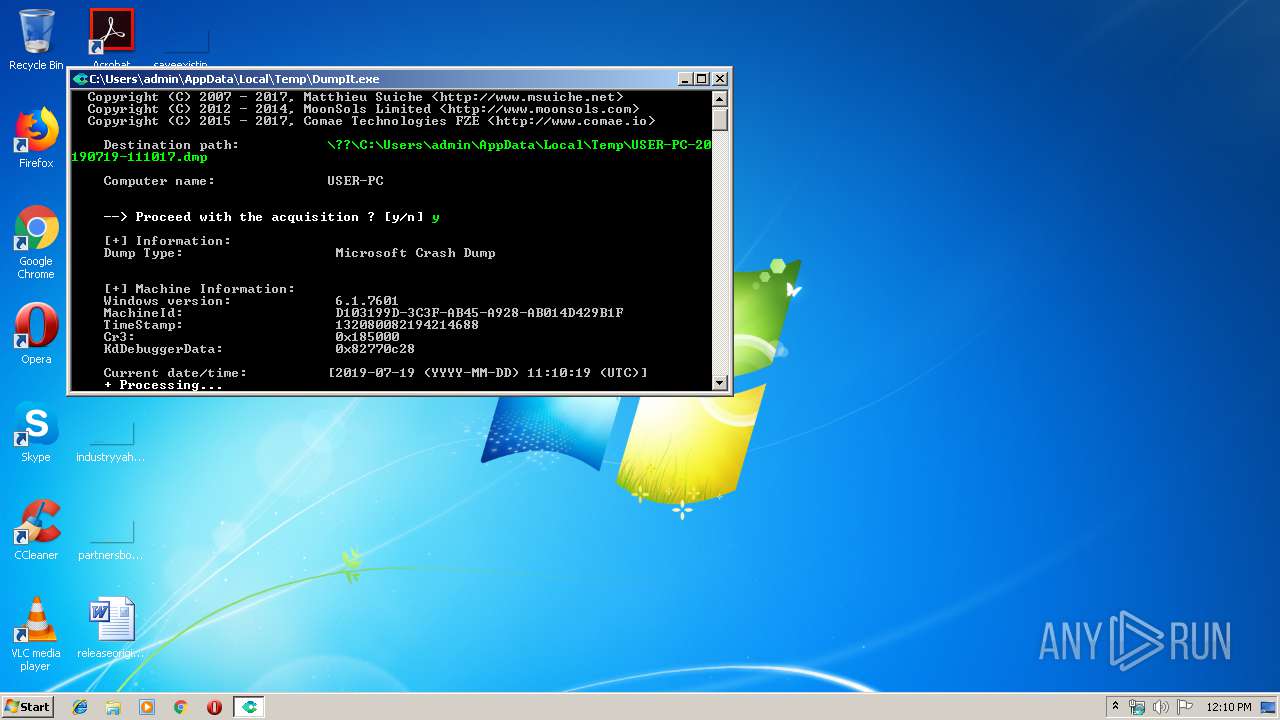
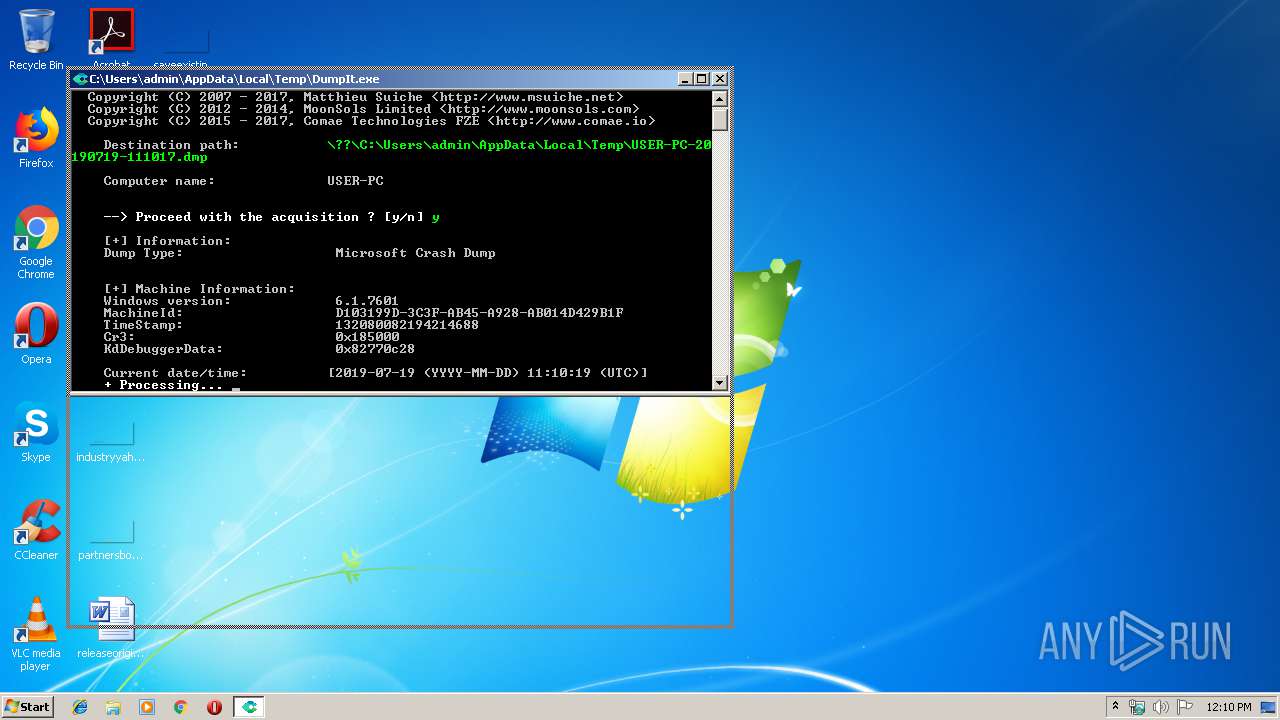
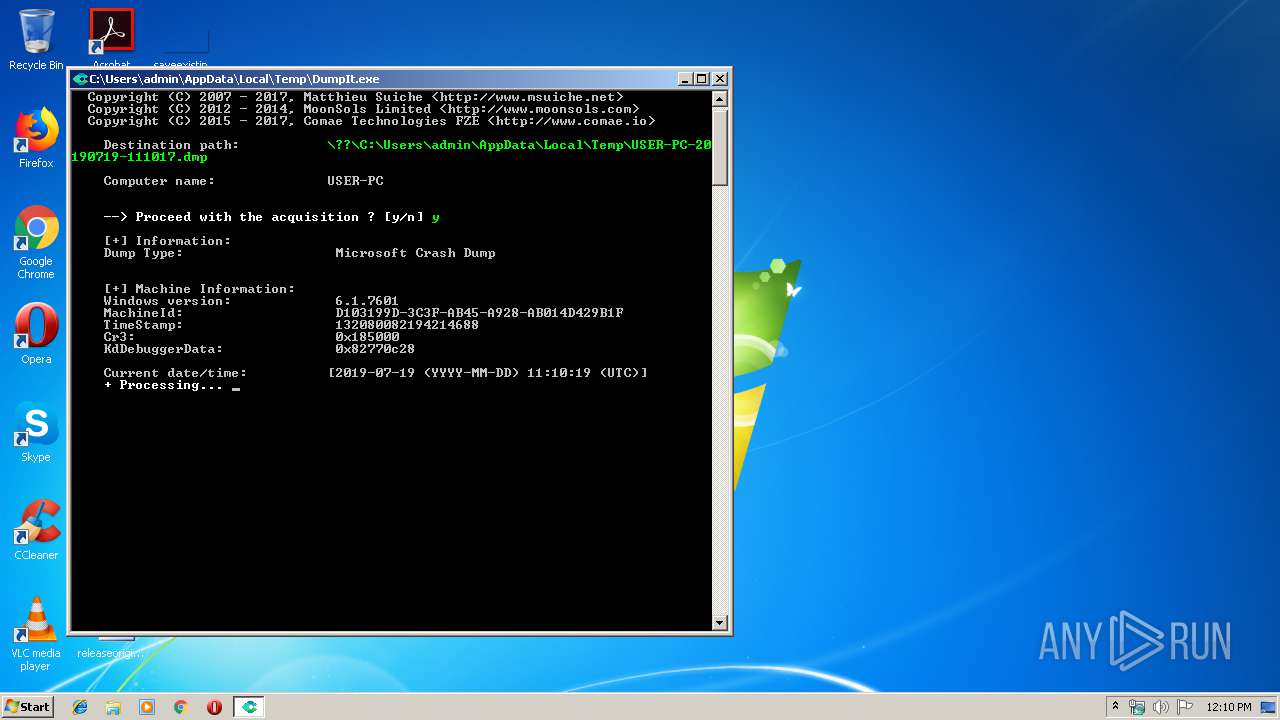
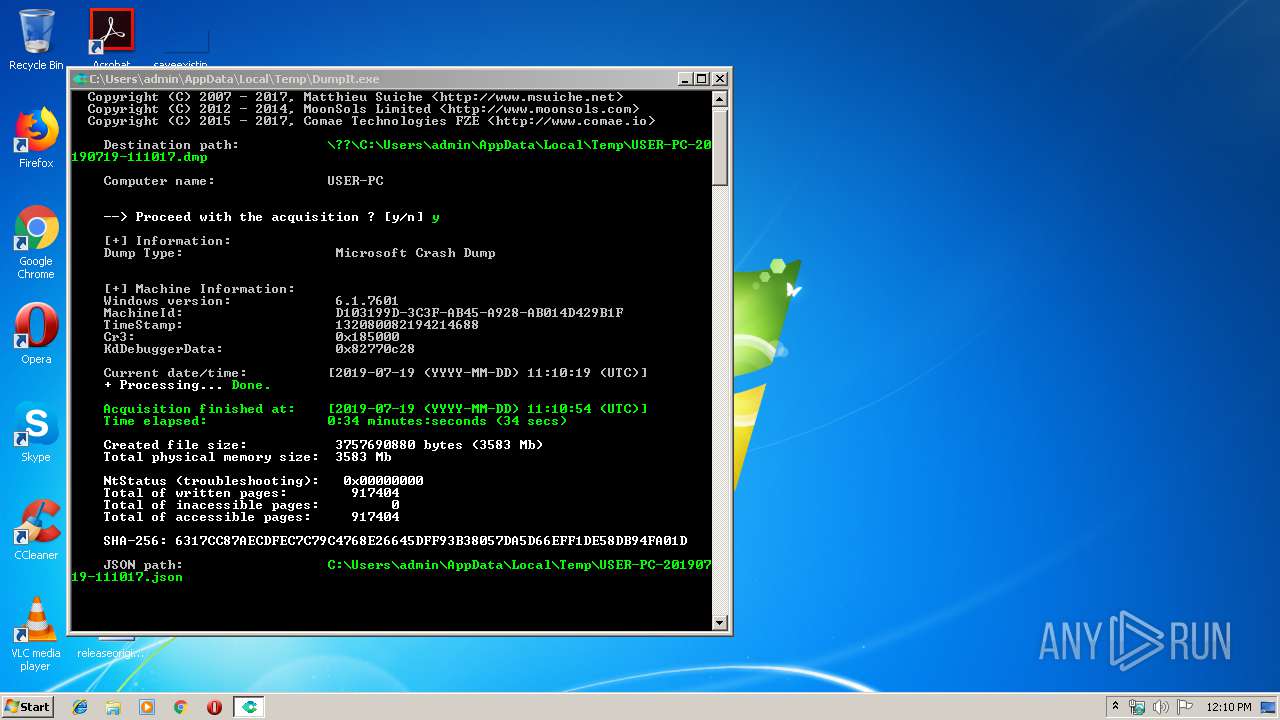
| 2924 | "C:\Users\admin\AppData\Local\Temp\DumpIt.exe" | C:\Users\admin\AppData\Local\Temp\DumpIt.exe | explorer.exe | ||||||||||||
User: admin Company: Comae Technologies FZE Integrity Level: HIGH Description: Memory Acquisition Tool Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 3616 | "C:\Users\admin\AppData\Local\Temp\DumpIt.exe" | C:\Users\admin\AppData\Local\Temp\DumpIt.exe | — | explorer.exe | |||||||||||
User: admin Company: Comae Technologies FZE Integrity Level: MEDIUM Description: Memory Acquisition Tool Exit code: 3221226540 Version: 3.0.0.0 Modules
| |||||||||||||||
Total events
45
Read events
23
Write events
18
Delete events
4
Modification events
| (PID) Process: | (2924) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | Type |
Value: 2 | |||
| (PID) Process: | (2924) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | ImagePath |
Value: \??\C:\Windows\system32\Drivers\DumpIt.sys | |||
| (PID) Process: | (2924) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (2924) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | DependOnService |
Value: FltMgr | |||
| (PID) Process: | (2924) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt |
| Operation: | write | Name: | Group |
Value: FSFilter Activity Monitor | |||
| (PID) Process: | (2924) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt\Instances |
| Operation: | write | Name: | DefaultInstance |
Value: DumpIt | |||
| (PID) Process: | (2924) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt\Instances\DumpIt |
| Operation: | write | Name: | Altitude |
Value: 389110 | |||
| (PID) Process: | (2924) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt\Instances\DumpIt |
| Operation: | write | Name: | Flags |
Value: 0 | |||
| (PID) Process: | (2924) DumpIt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2924) DumpIt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\DumpIt\Enum |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | DumpIt.exe | C:\Windows\system32\Drivers\DumpIt.sys | — | |
MD5:— | SHA256:— | |||
| 2924 | DumpIt.exe | C:\Users\admin\AppData\Local\Temp\USER-PC-20190719-111017.dmp | — | |
MD5:— | SHA256:— | |||
| 2924 | DumpIt.exe | C:\Users\admin\AppData\Local\Temp\USER-PC-20190719-111017.json | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2924 | DumpIt.exe | GET | 301 | 173.236.227.251:80 | http://www.comae.io/getip.php | US | html | 239 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2924 | DumpIt.exe | 173.236.227.251:80 | www.comae.io | New Dream Network, LLC | US | suspicious |
2924 | DumpIt.exe | 173.236.227.251:443 | www.comae.io | New Dream Network, LLC | US | suspicious |
2924 | DumpIt.exe | 52.174.3.80:443 | telemetry.comae.io | Microsoft Corporation | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.comae.io |
| suspicious |
www.comae.com |
| suspicious |
telemetry.comae.io |
| unknown |
Threats
Process | Message |
|---|---|
DumpIt.exe | [comae:1492] Error: WinHttpReceiveResponse failed with error code = 12175
|
DumpIt.exe | [comae:1492] -> totalUploadLength = 0x3e7
|