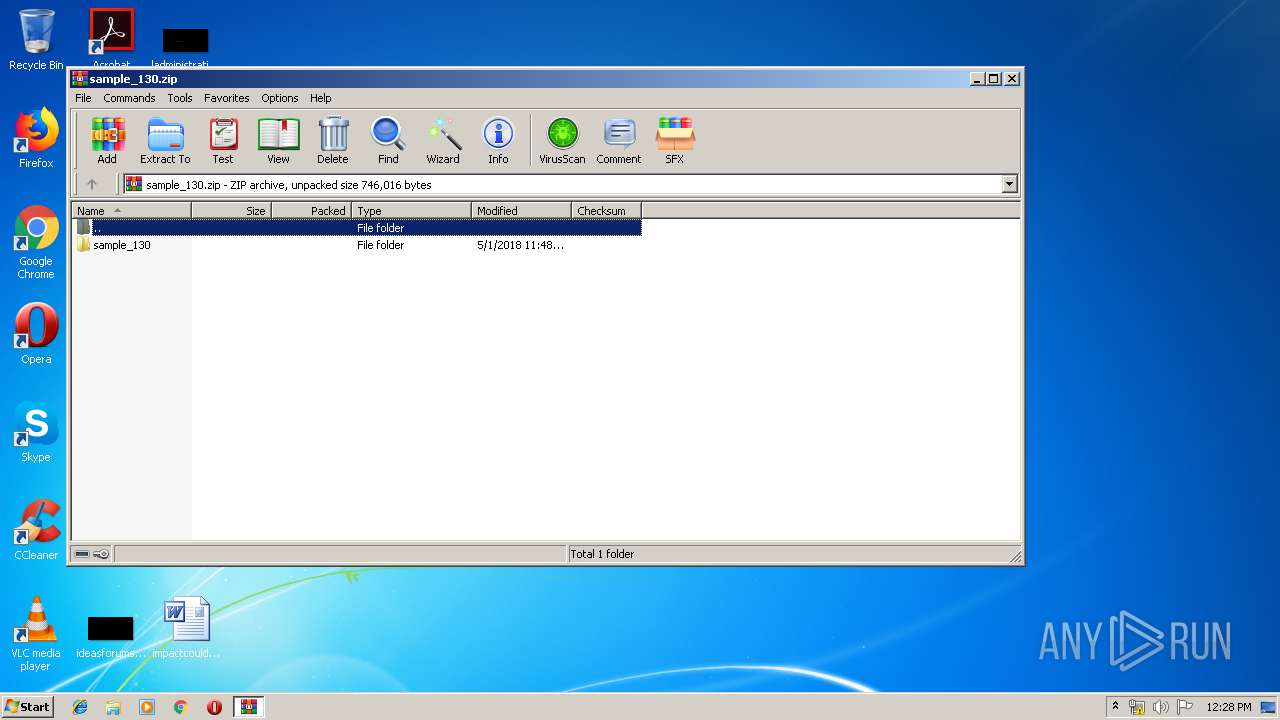
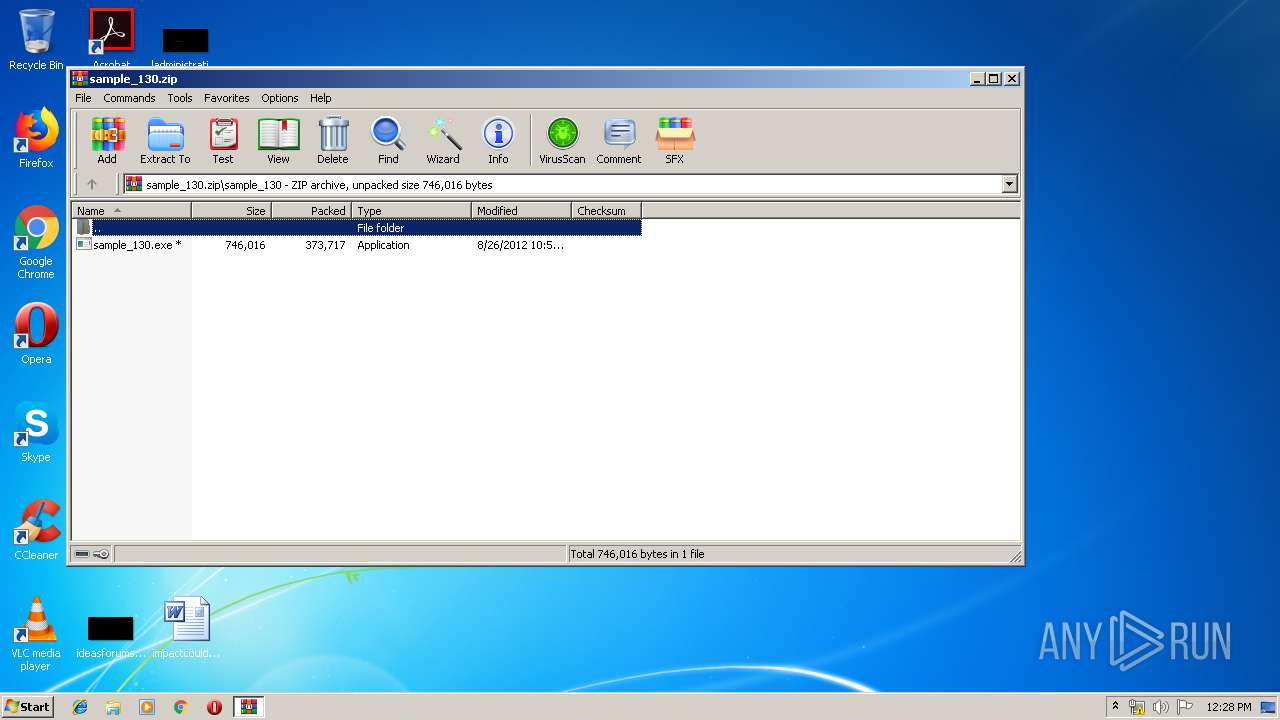
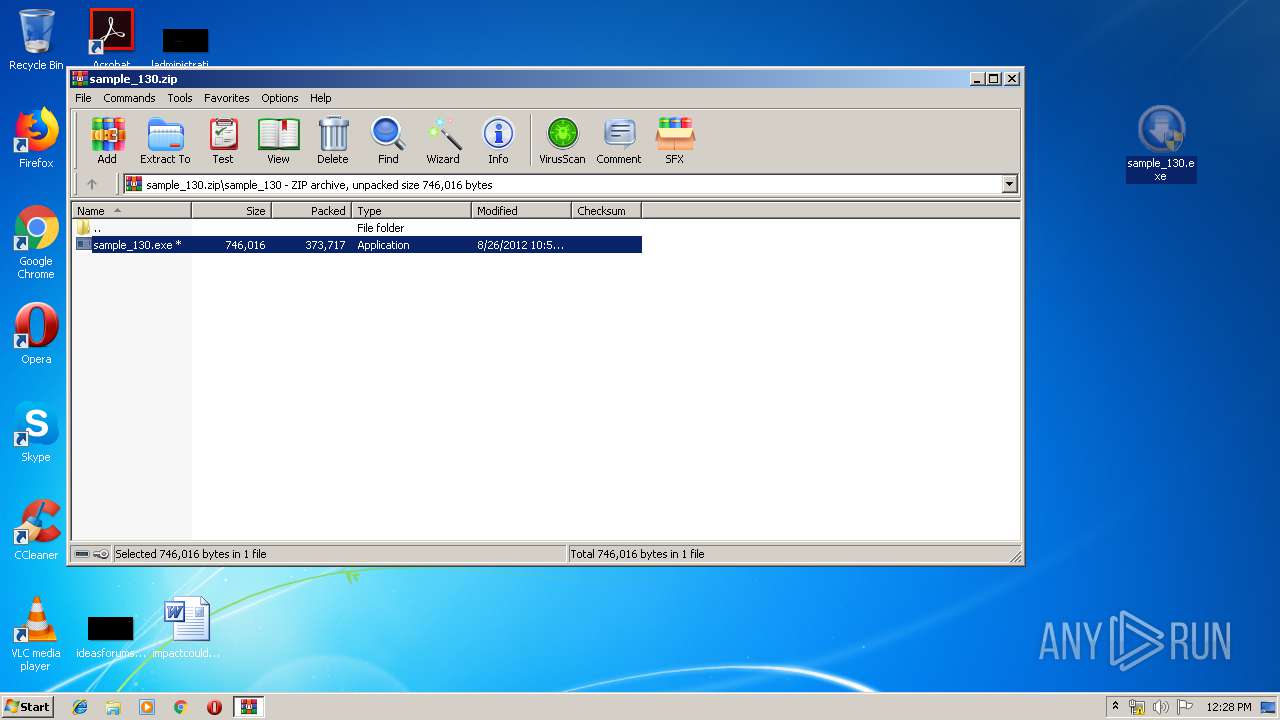
| File name: | sample_130.zip |
| Full analysis: | https://app.any.run/tasks/0e5560e2-3cb1-49c7-9fb2-aca50f0831c5 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 11:27:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 394DE60DC4B7D0F78DFE1210260CA2D9 |
| SHA1: | 098CBEA7E4F27843F8F1555F8C757AEE21A2AC57 |
| SHA256: | 4D2993CE62AB82DD3A59C367F46E0D04683CC706B4A3FDC991C2B4C1A2AA2000 |
| SSDEEP: | 6144:kpRgHfSSHZOuNEuIxmh5AVFrtco6JIPX0VwA62Mrip/iEpBC4+E3acZ89VvDfkS3:0Rq35fN+csxtZ6/562MgiEpacZ4VvDft |
MALICIOUS
Application was dropped or rewritten from another process
- sample_130.exe (PID: 2176)
- sample_130.exe (PID: 2044)
Connects to CnC server
- sample_130.exe (PID: 2044)
Changes settings of System certificates
- sample_130.exe (PID: 2044)
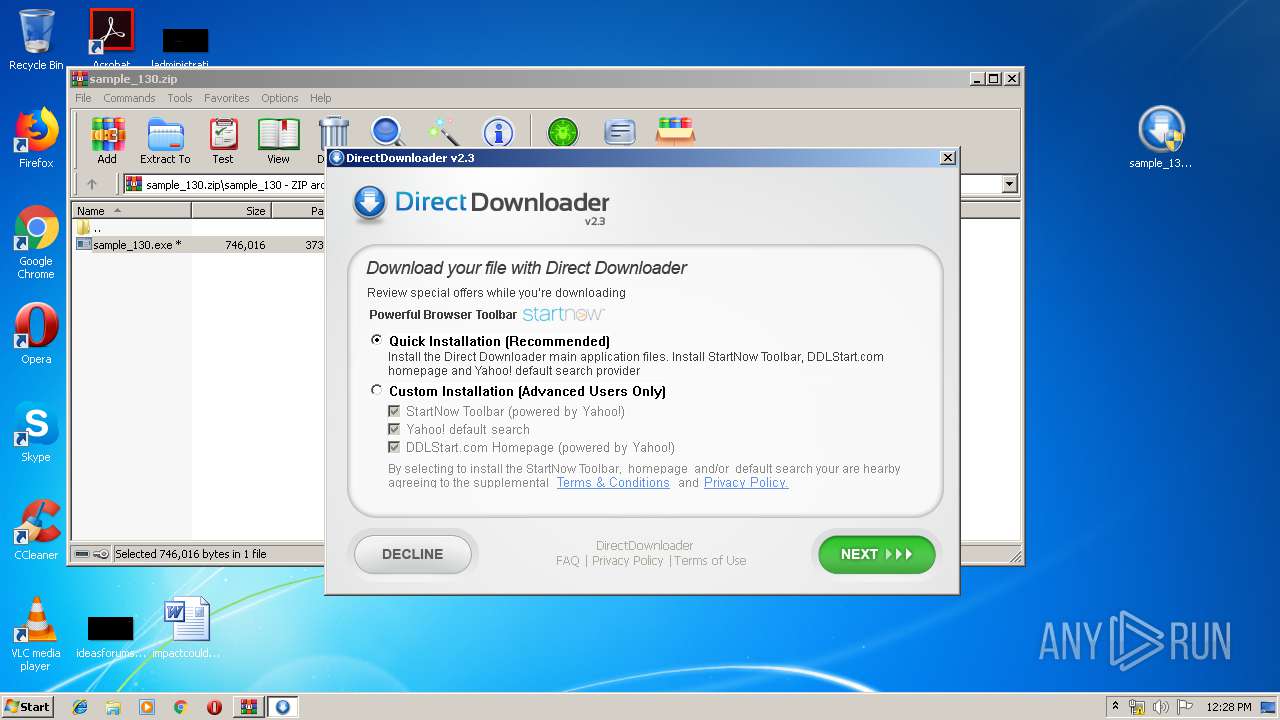
SUSPICIOUS
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2836)
- cmd.exe (PID: 2280)
Adds / modifies Windows certificates
- sample_130.exe (PID: 2044)
Starts CMD.EXE for commands execution
- sample_130.exe (PID: 2044)
Creates files in the user directory
- sample_130.exe (PID: 2044)
Executes application which crashes
- sample_130.exe (PID: 2044)
INFO
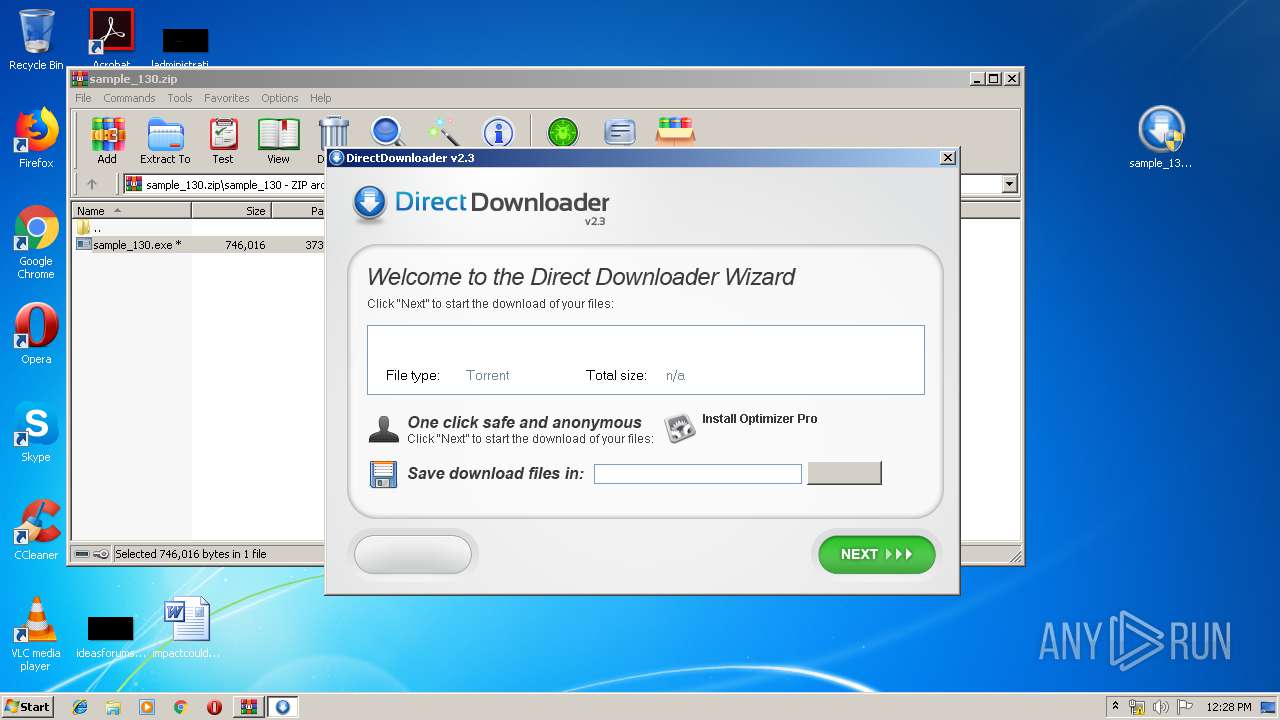
Manual execution by user
- sample_130.exe (PID: 2044)
- sample_130.exe (PID: 2176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:05:01 18:48:23 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_130/ |
Total processes
52
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | "C:\Windows\System32\cmd.exe" /C mkdir "C:\Users\admin\AppData\Local\DirectDownloader" | C:\Windows\System32\cmd.exe | — | sample_130.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 912 | netsh firewall add allowedprogram "C:\Users\admin\AppData\Local\DirectDownloader\directdownloader.exe" "DirectDownloader" ENABLE | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2044 | "C:\Users\admin\Desktop\sample_130.exe" | C:\Users\admin\Desktop\sample_130.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2104 | netsh firewall delete allowedprogram "C:\Users\admin\AppData\Local\DirectDownloader\directdownloader.exe" | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\Desktop\sample_130.exe" | C:\Users\admin\Desktop\sample_130.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2280 | "C:\Windows\System32\cmd.exe" /C netsh firewall delete allowedprogram "C:\Users\admin\AppData\Local\DirectDownloader\directdownloader.exe" | C:\Windows\System32\cmd.exe | — | sample_130.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2640 | "C:\Windows\system32\ntvdm.exe" -i2 | C:\Windows\system32\ntvdm.exe | — | sample_130.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2836 | "C:\Windows\System32\cmd.exe" /C netsh firewall add allowedprogram "C:\Users\admin\AppData\Local\DirectDownloader\directdownloader.exe" "DirectDownloader" ENABLE | C:\Windows\System32\cmd.exe | — | sample_130.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2900 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | sample_130.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3256 | "C:\Windows\System32\cmd.exe" /C echo ifms > "C:\Users\admin\AppData\Local\DirectDownloader\directdownloader.exe" | C:\Windows\System32\cmd.exe | — | sample_130.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 007
Read events
867
Write events
140
Delete events
0
Modification events
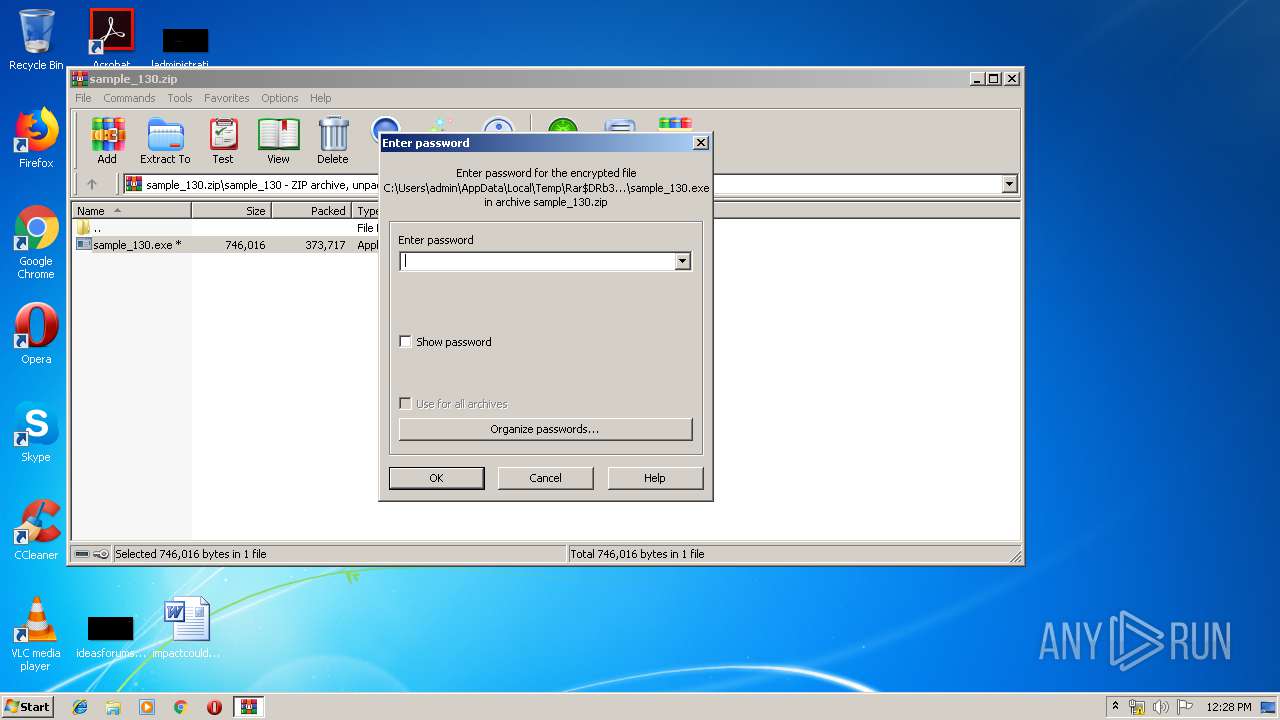
| (PID) Process: | (3372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3372) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_130.zip | |||
| (PID) Process: | (3372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2044) sample_130.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3372 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3372.39387\sample_130\sample_130.exe | — | |
MD5:— | SHA256:— | |||
| 2044 | sample_130.exe | C:\Users\admin\AppData\Local\Temp\DirectDownloaderInstaller.exe | html | |
MD5:— | SHA256:— | |||
| 2044 | sample_130.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[1].txt | text | |
MD5:— | SHA256:— | |||
| 3256 | cmd.exe | C:\Users\admin\AppData\Local\DirectDownloader\directdownloader.exe | text | |
MD5:— | SHA256:— | |||
| 2044 | sample_130.exe | C:\Users\admin\AppData\Local\Temp\optimizer.exe | html | |
MD5:— | SHA256:— | |||
| 2044 | sample_130.exe | C:\Users\admin\AppData\Local\Temp\ddlr-directdownloader-sntb.exe | html | |
MD5:— | SHA256:— | |||
| 2640 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs6EB1.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
| 2900 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs6AD9.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
| 2900 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs6AC8.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
| 2640 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs6EB0.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
4
DNS requests
4
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2044 | sample_130.exe | GET | 302 | 162.255.119.249:80 | http://www.directdownloader.com/check.php?v=2.3a&os=windows&version=7%20Service%20Pack%201&lang=English&referer=&offer_pre=no&type=custom&homepage=no&search=no&toolbar=no&install=yes | US | html | 228 b | malicious |
2044 | sample_130.exe | GET | 302 | 162.255.119.249:80 | http://www.directdownloader.com/toolbars/ddlr-directdownloader-sntb.exe | US | html | 123 b | malicious |
2044 | sample_130.exe | GET | 301 | 172.217.22.68:80 | http://www.google.com/enterprise/apps/business/products.html/toolbars/ddlr-directdownloader-sntb.exe | US | html | 294 b | malicious |
2044 | sample_130.exe | GET | 302 | 162.255.119.249:80 | http://www.directdownloader.com/toolbars/optimizer.exe | US | html | 106 b | malicious |
2044 | sample_130.exe | GET | 302 | 162.255.119.249:80 | http://www.directdownloader.com/DirectDownloaderInstaller.exe | US | html | 113 b | malicious |
2044 | sample_130.exe | GET | 301 | 172.217.22.68:80 | http://www.google.com/enterprise/apps/business/products.html/check.php?homepage=no&install=yes&lang=English&offer_pre=no&os=windows&referer=&search=no&toolbar=no&type=custom&v=2.3a&version=7+Service+Pack+1 | US | html | 439 b | malicious |
2044 | sample_130.exe | GET | 301 | 172.217.22.68:80 | http://www.google.com/enterprise/apps/business/products.html/DirectDownloaderInstaller.exe | US | html | 284 b | malicious |
2044 | sample_130.exe | GET | 301 | 172.217.22.68:80 | http://www.google.com/enterprise/apps/business/products.html/toolbars/optimizer.exe | US | html | 277 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2044 | sample_130.exe | 162.255.119.249:80 | www.directdownloader.com | Namecheap, Inc. | US | malicious |
2044 | sample_130.exe | 172.217.22.68:80 | www.google.com | Google Inc. | US | whitelisted |
2044 | sample_130.exe | 216.58.205.238:443 | enterprise.google.com | Google Inc. | US | whitelisted |
2044 | sample_130.exe | 172.217.21.238:443 | gsuite.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.directdownloader.com |
| malicious |
www.google.com |
| malicious |
enterprise.google.com |
| whitelisted |
gsuite.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2044 | sample_130.exe | A Network Trojan was detected | ET MALWARE Suspicious User-Agent (downloader) |
2044 | sample_130.exe | A Network Trojan was detected | ET MALWARE Suspicious User-Agent (downloader) |
2044 | sample_130.exe | A Network Trojan was detected | ET MALWARE Suspicious User-Agent (downloader) |
2044 | sample_130.exe | A Network Trojan was detected | ET MALWARE Suspicious User-Agent (downloader) |
2044 | sample_130.exe | A Network Trojan was detected | ET MALWARE Suspicious User-Agent (downloader) |
2044 | sample_130.exe | A Network Trojan was detected | ET MALWARE Suspicious User-Agent (downloader) |
3 ETPRO signatures available at the full report