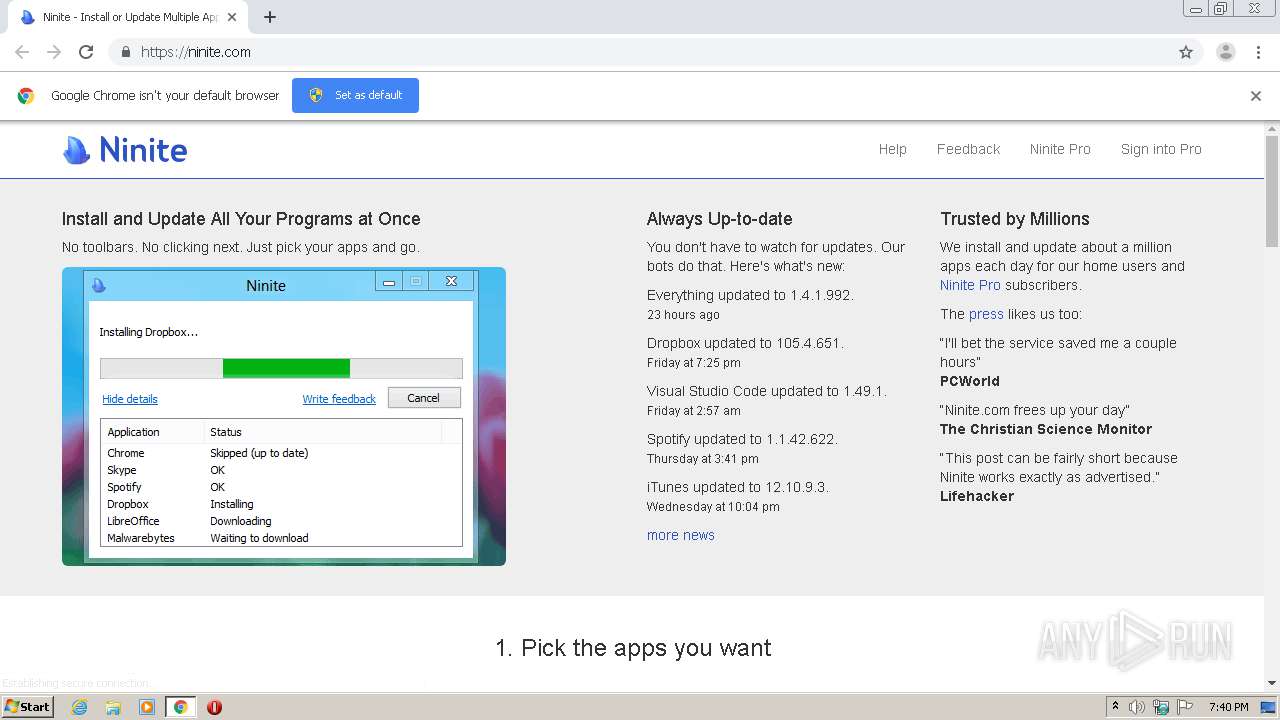
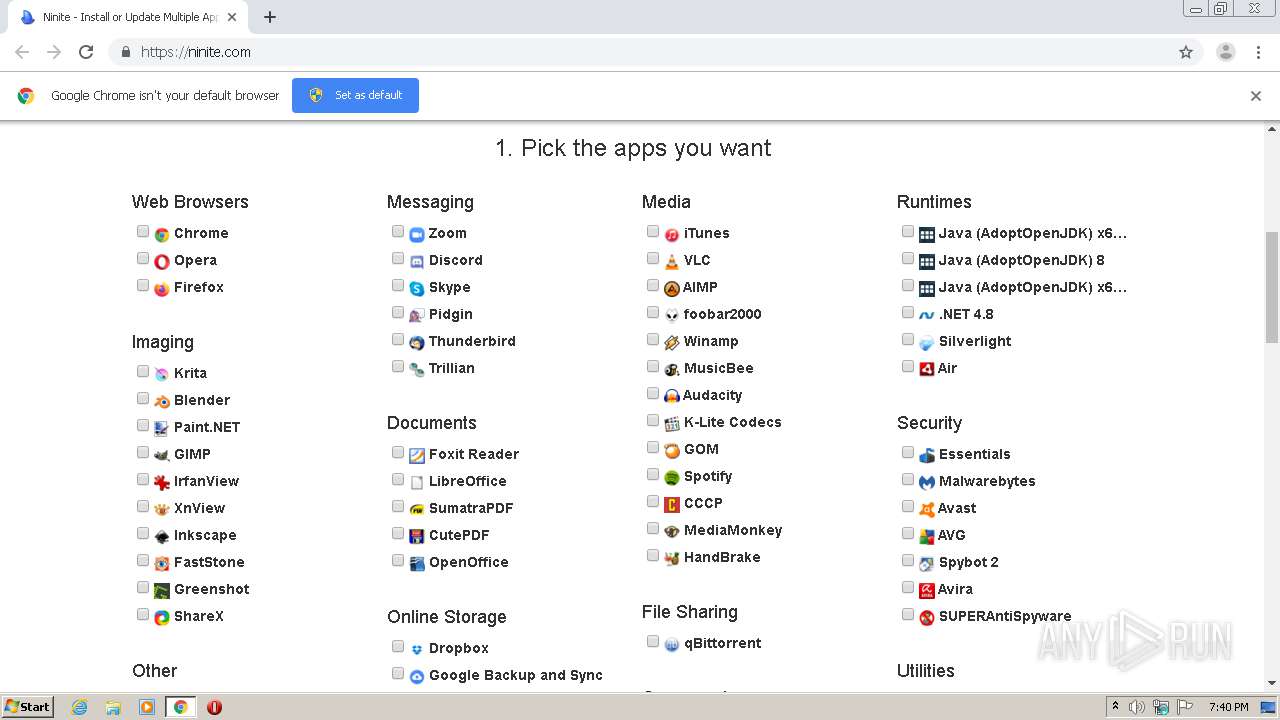
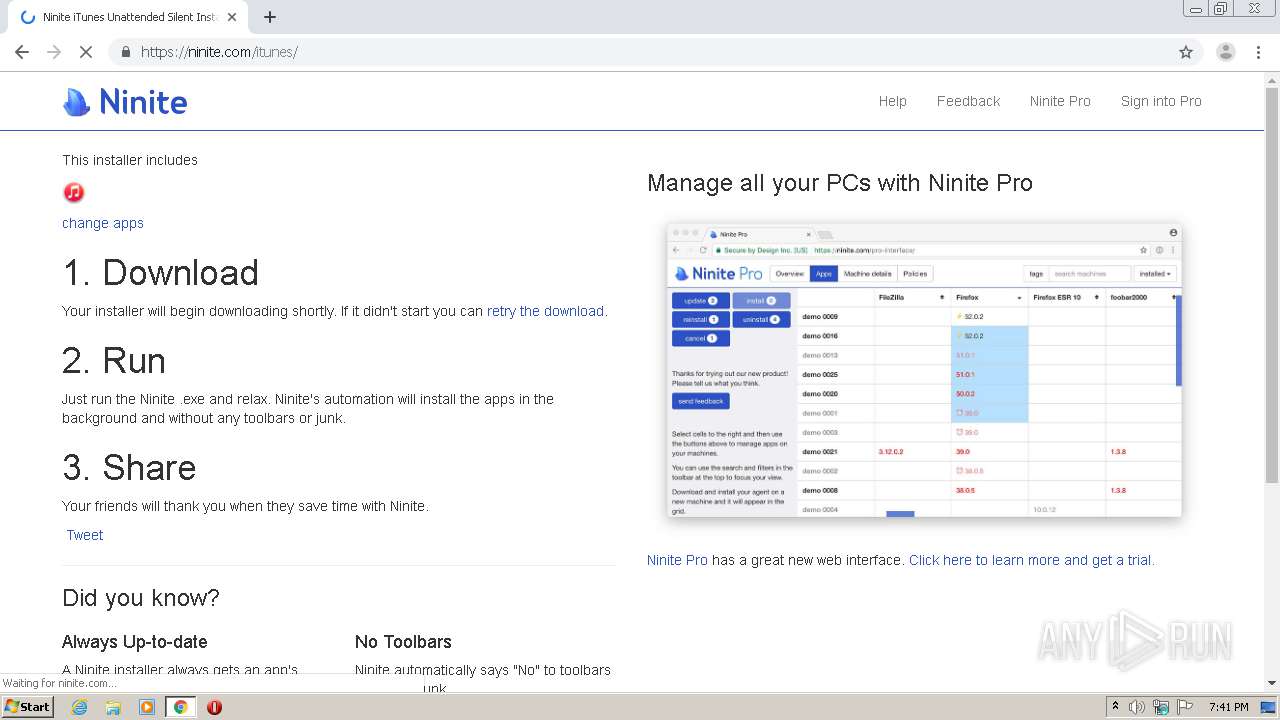
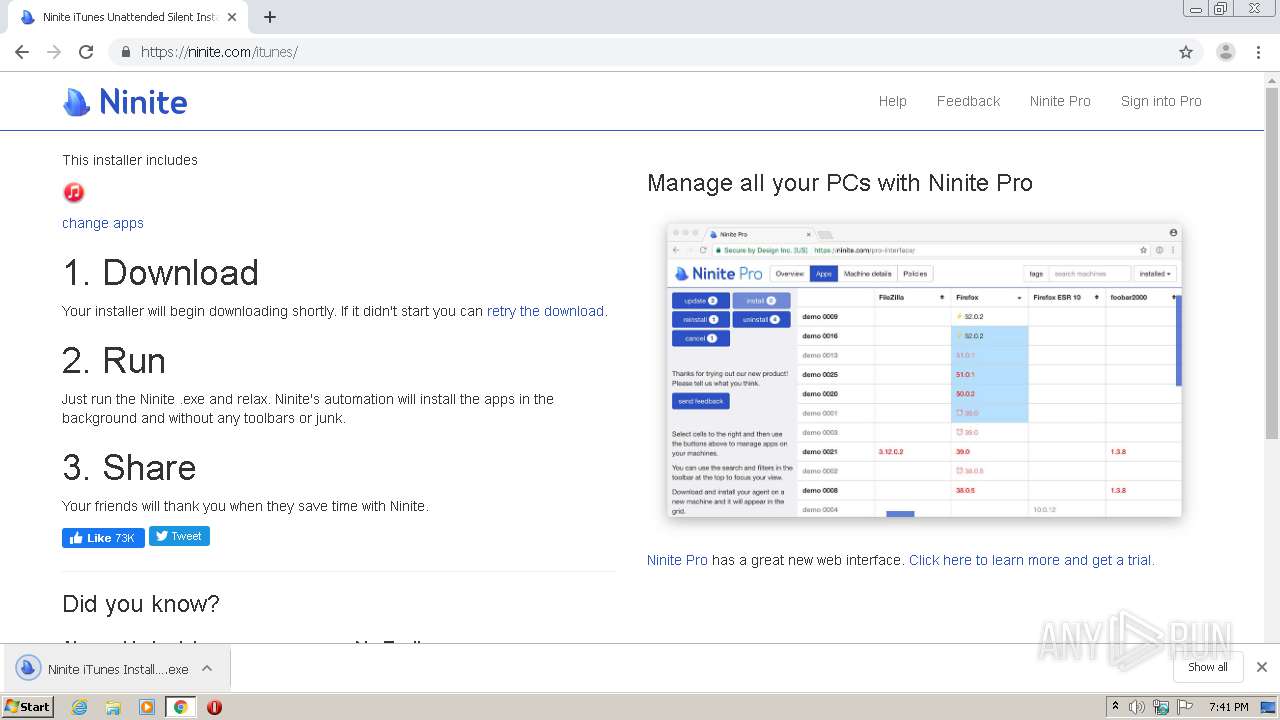
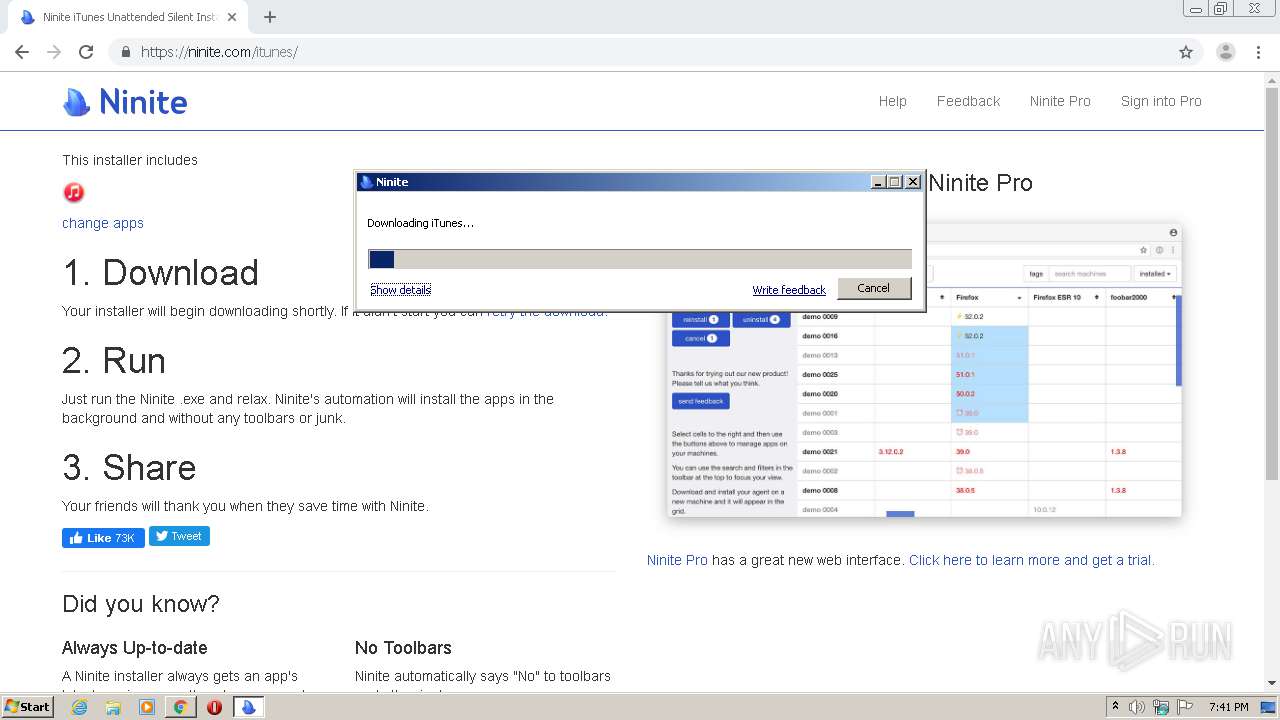
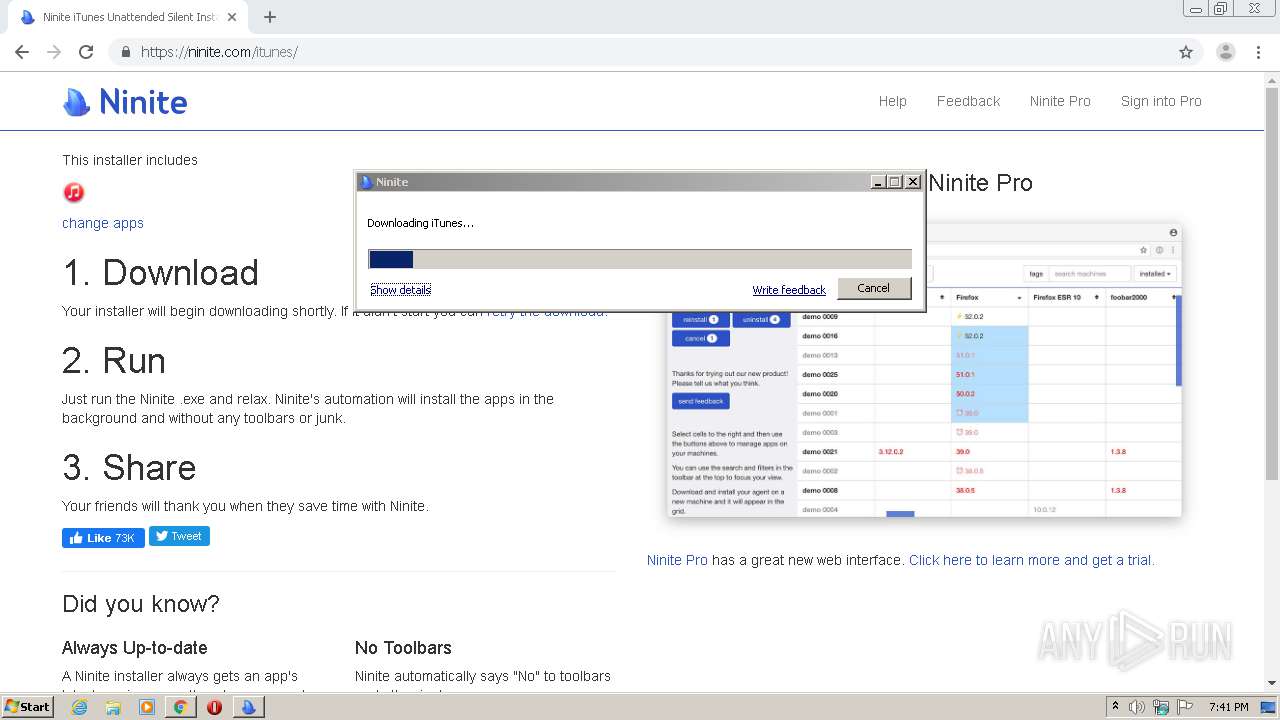
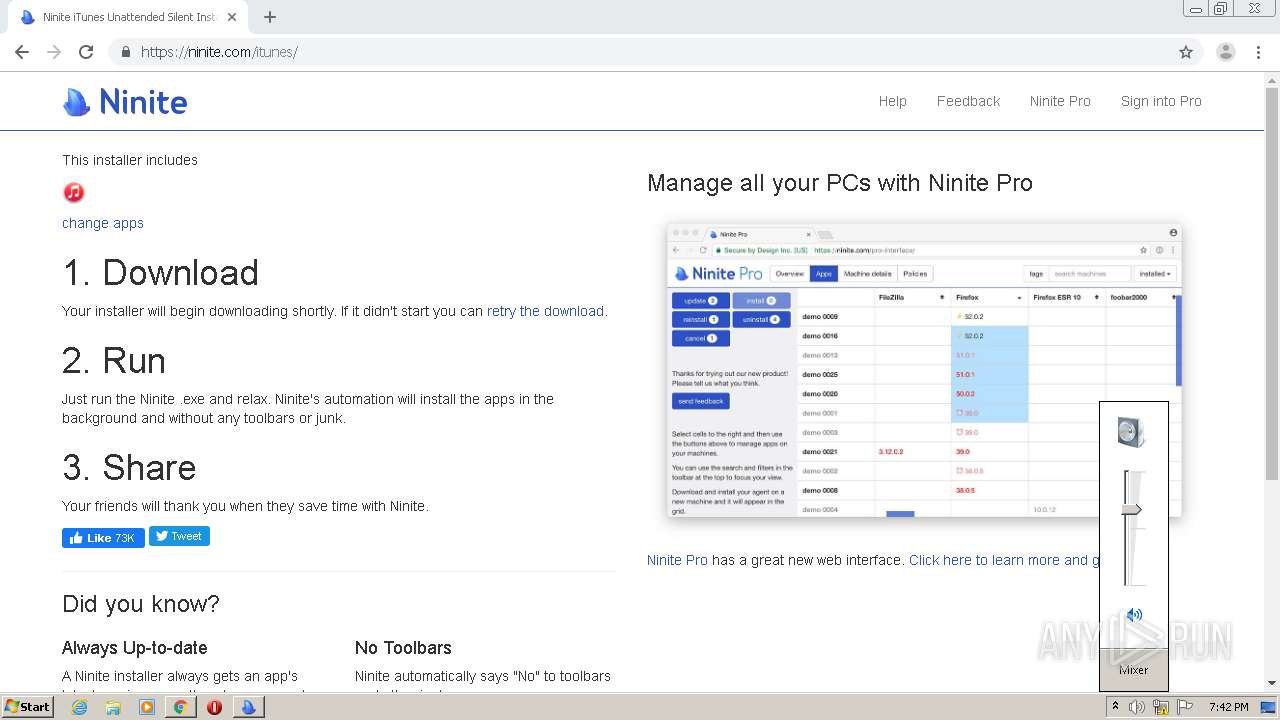
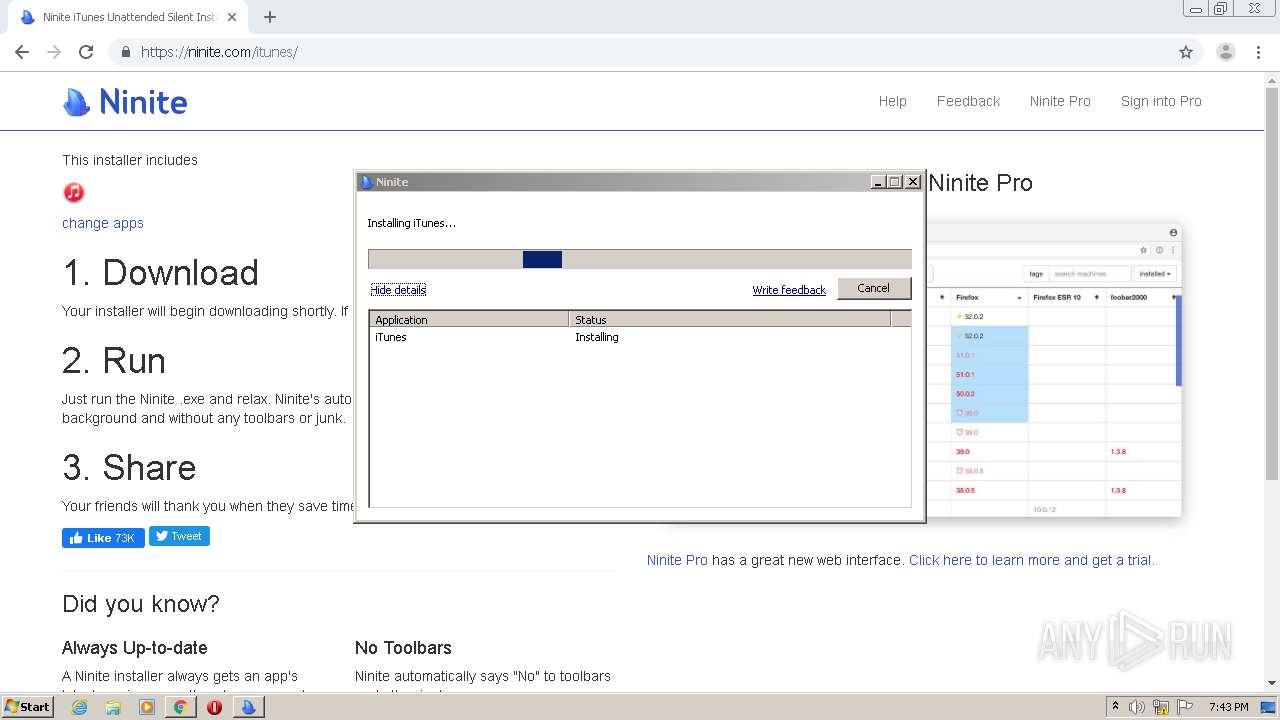
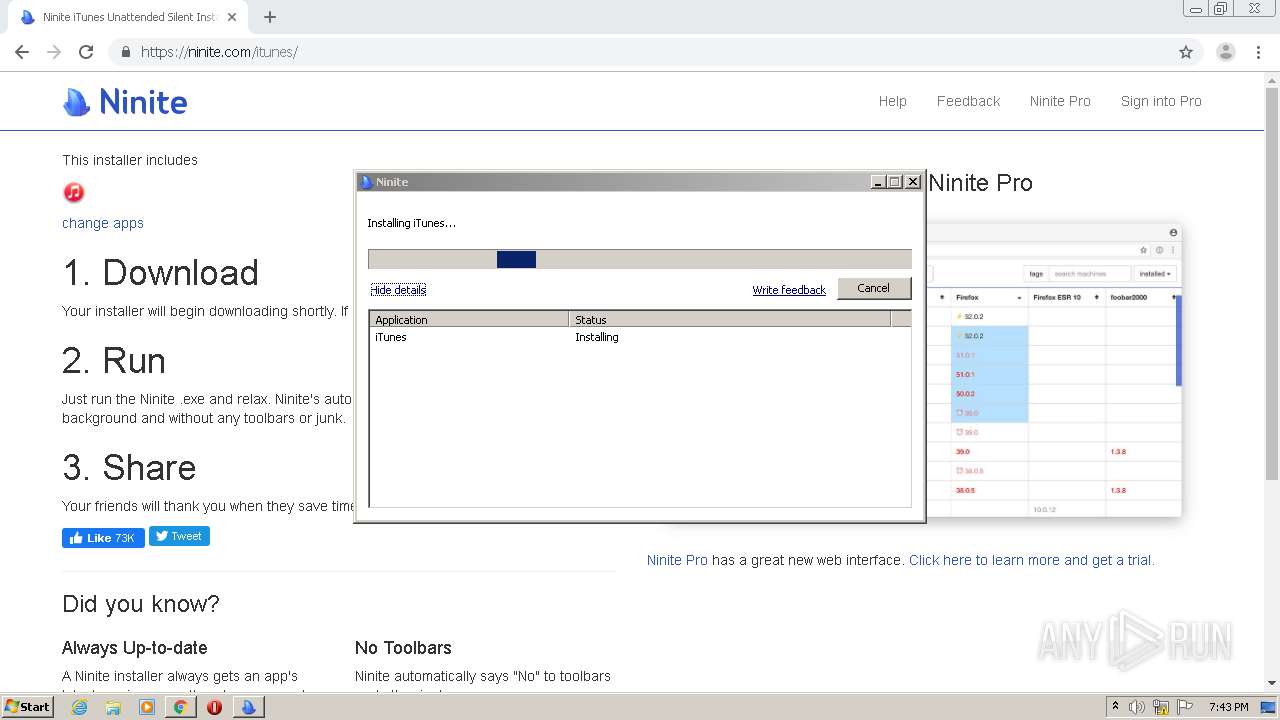
| URL: | https://ninite.com/ |
| Full analysis: | https://app.any.run/tasks/4cb82371-f869-4749-8722-2200db2c587e |
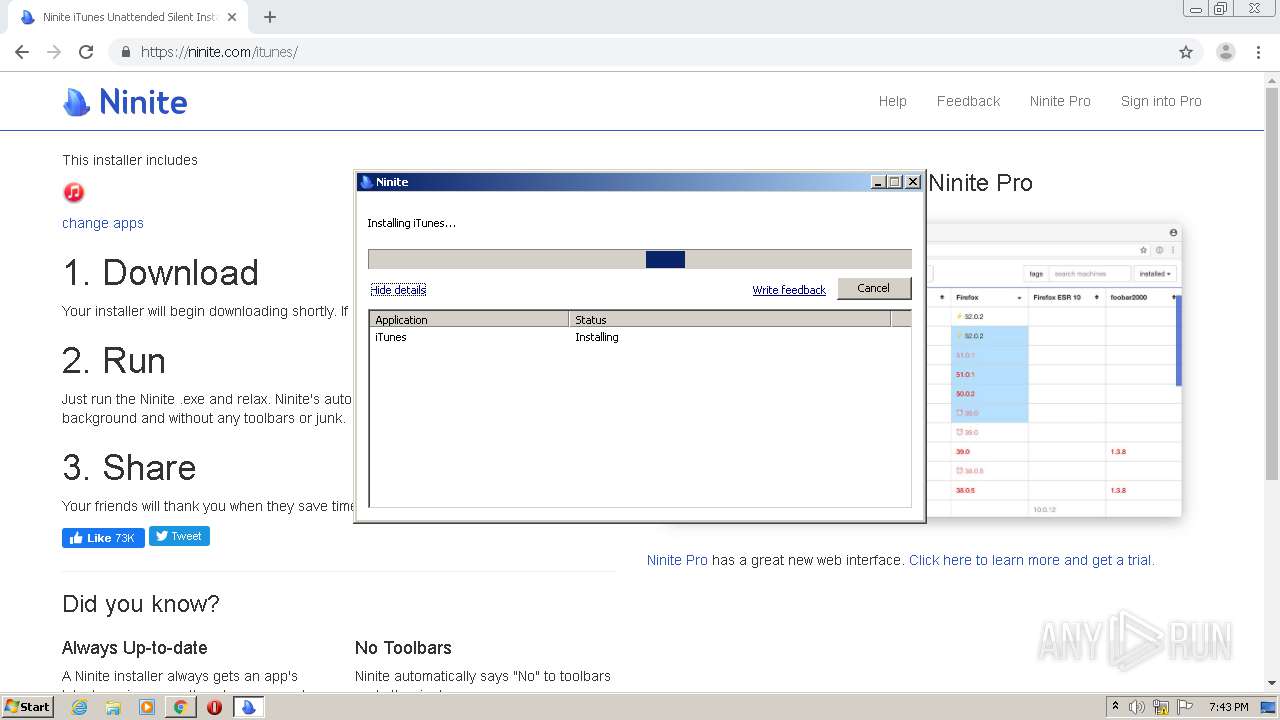
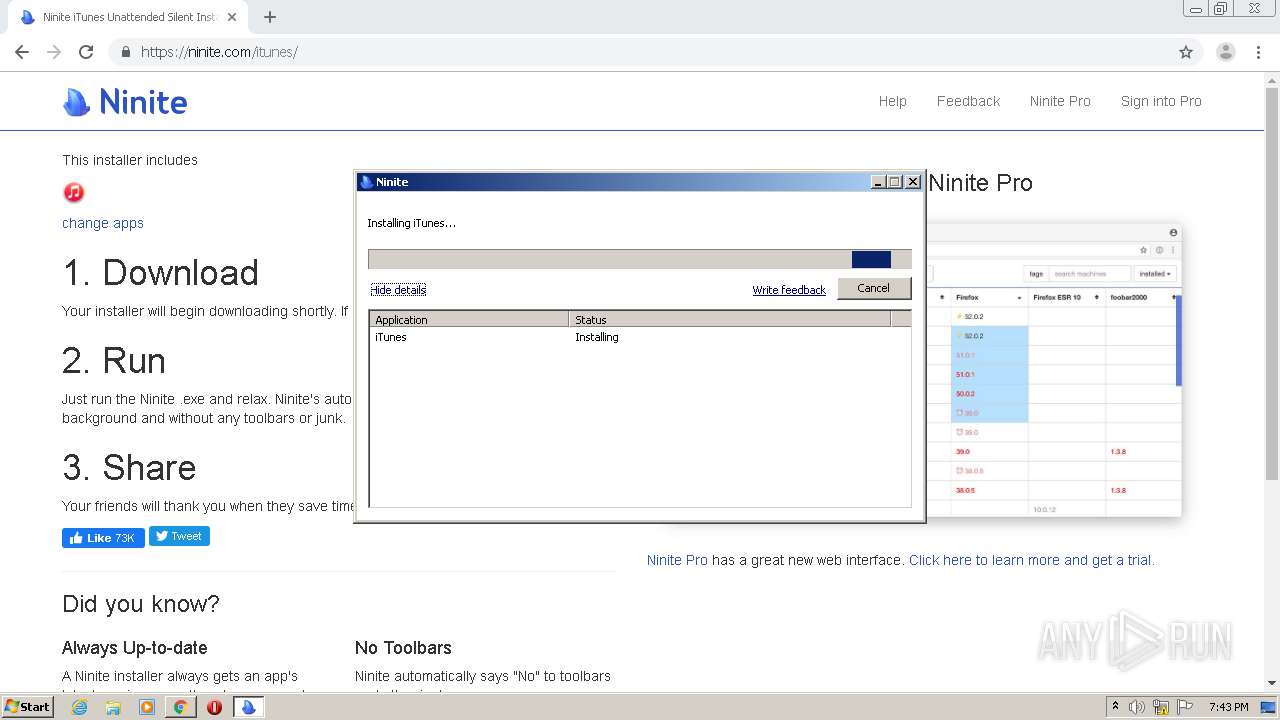
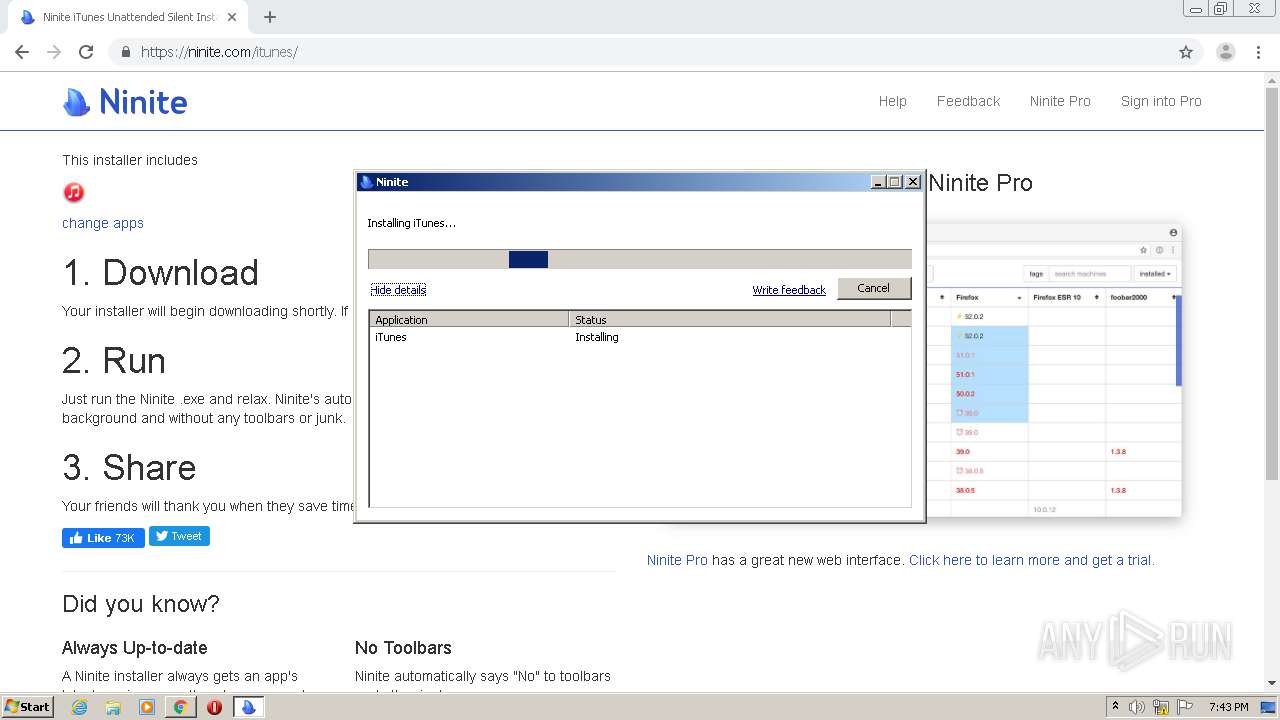
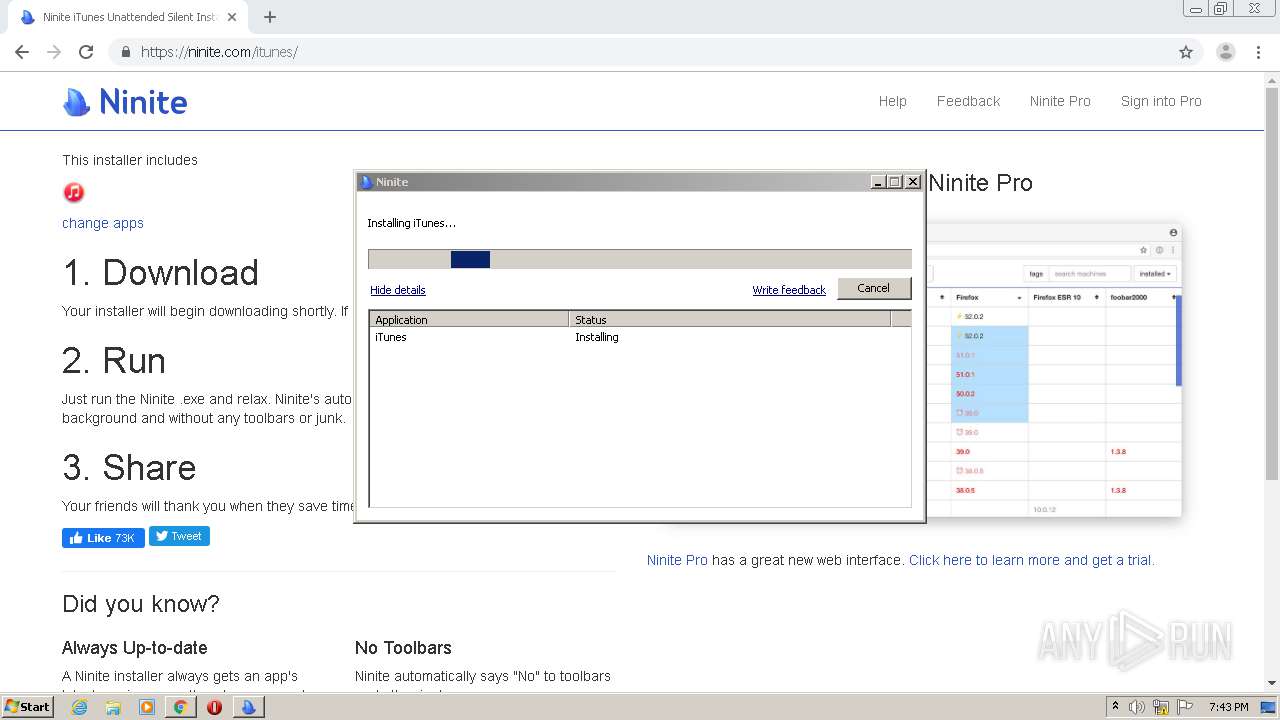
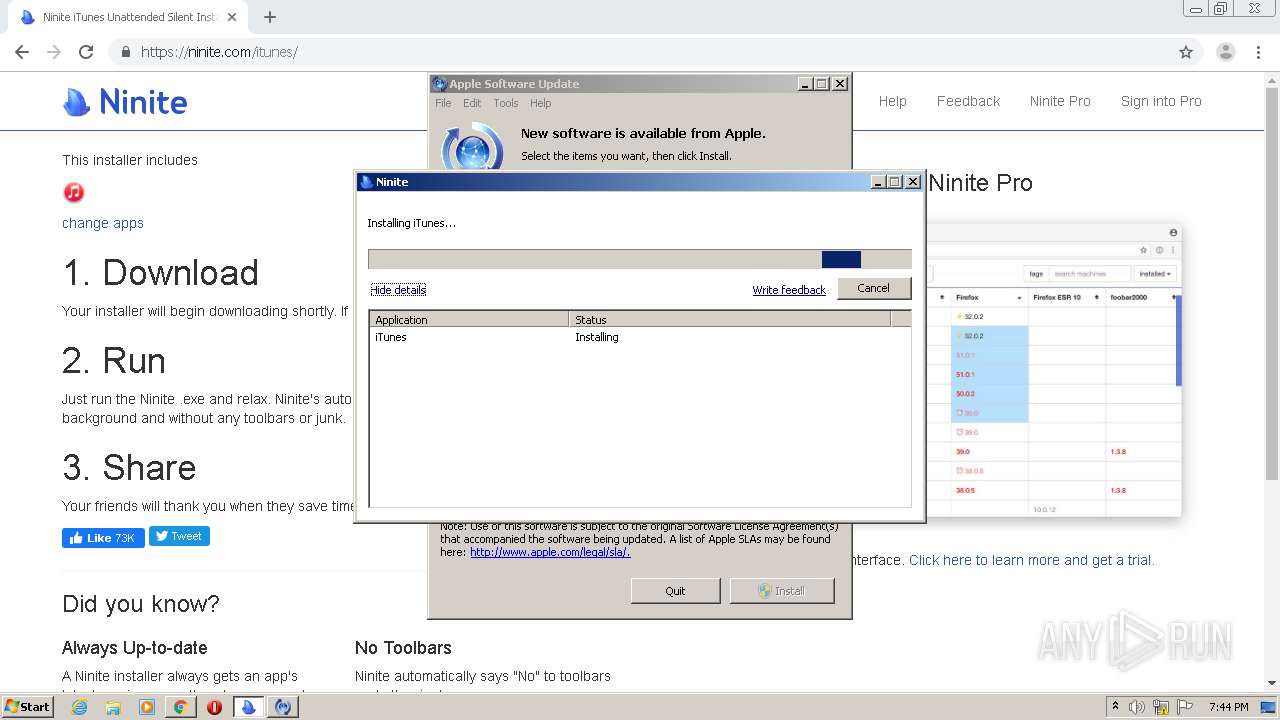
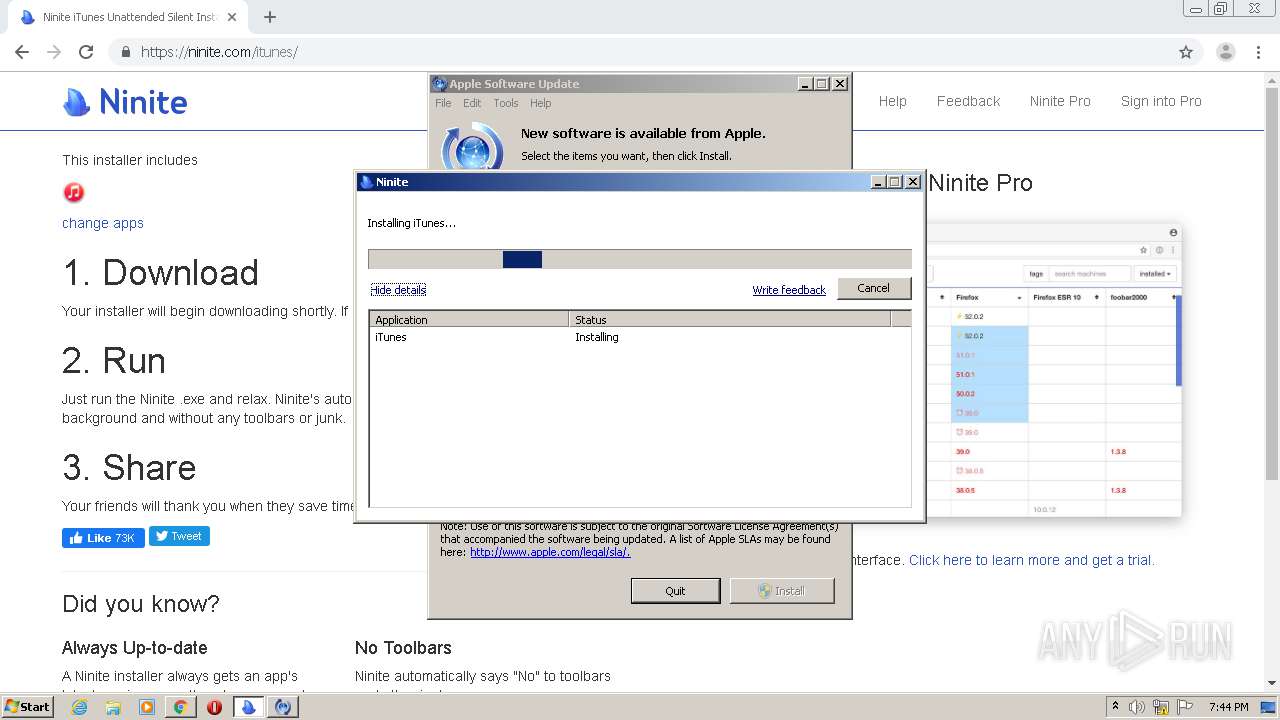
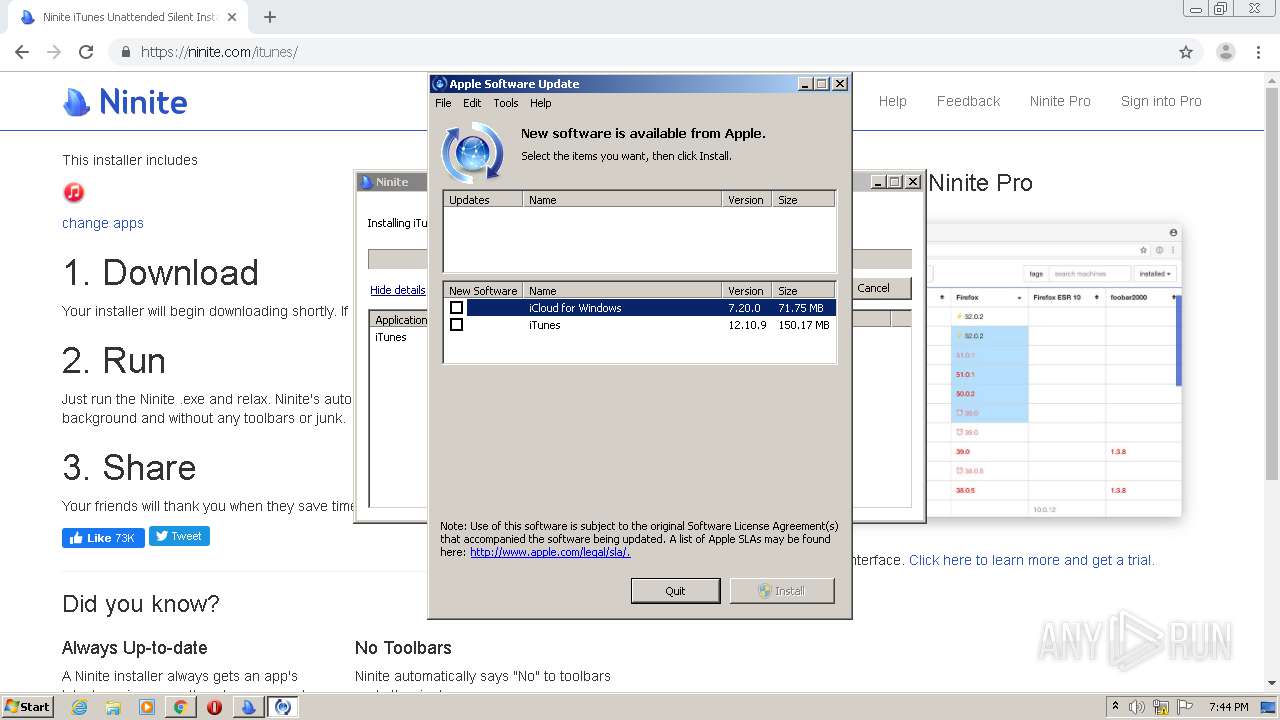
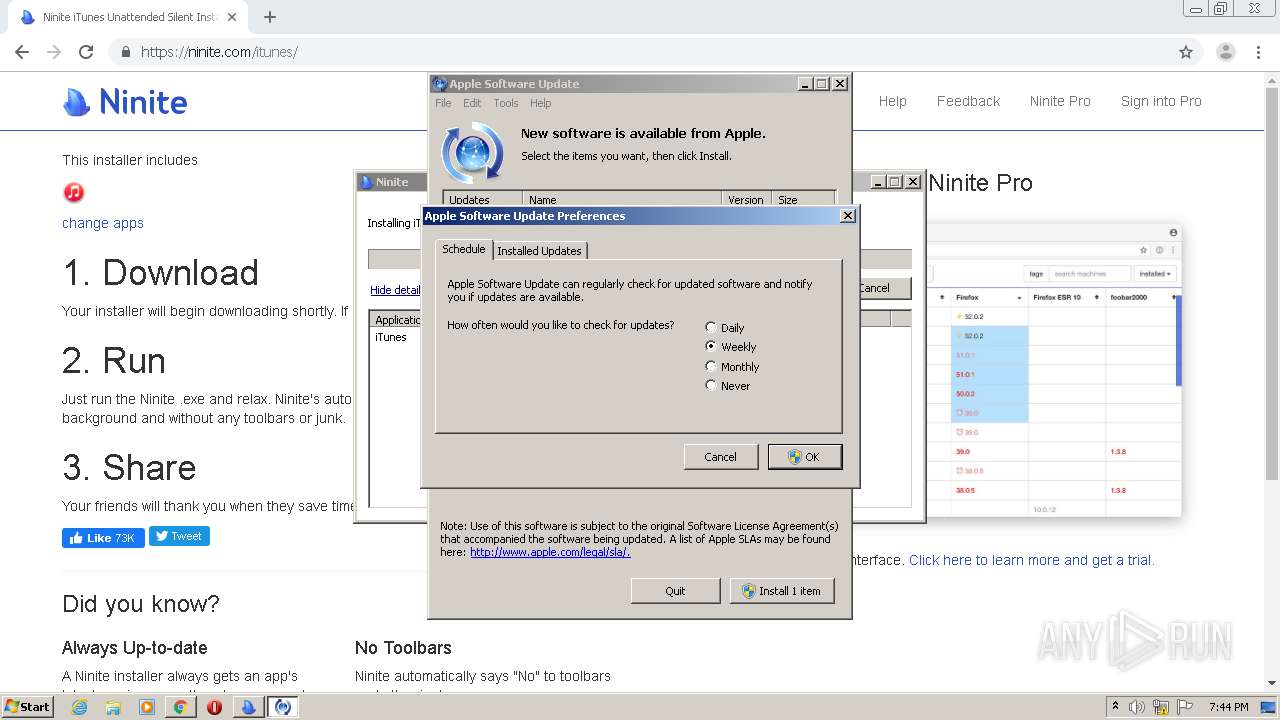
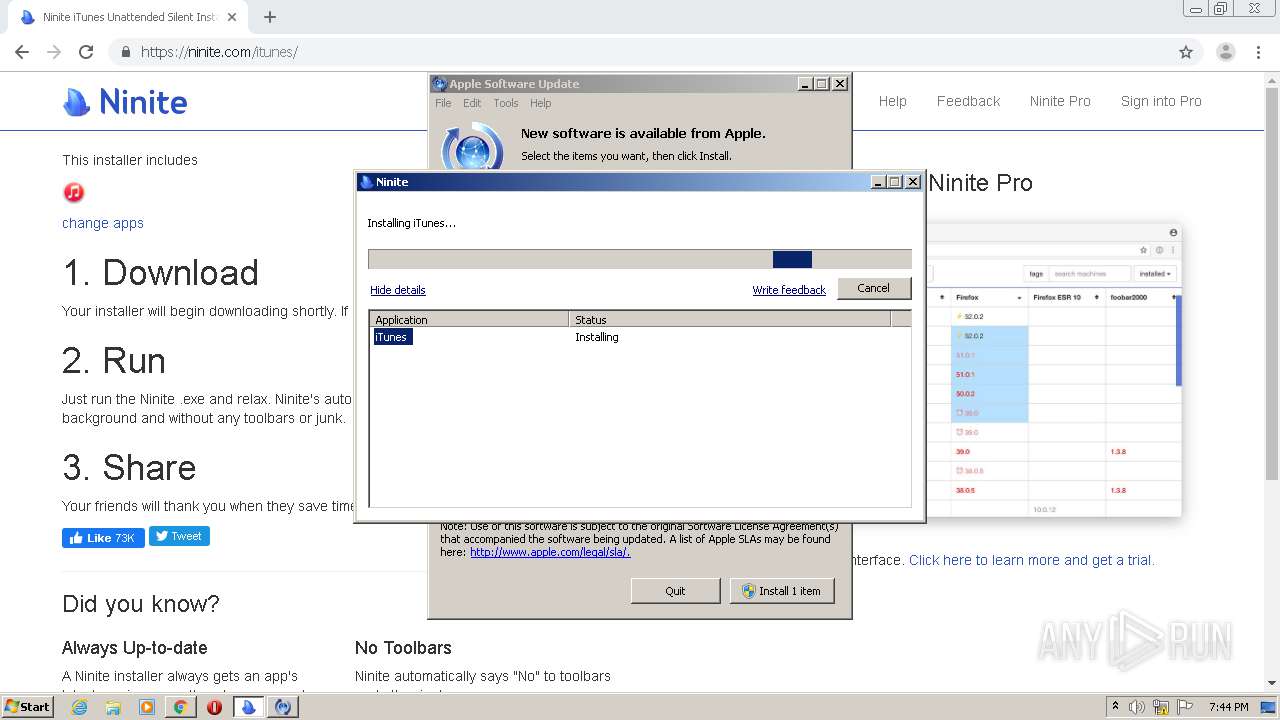
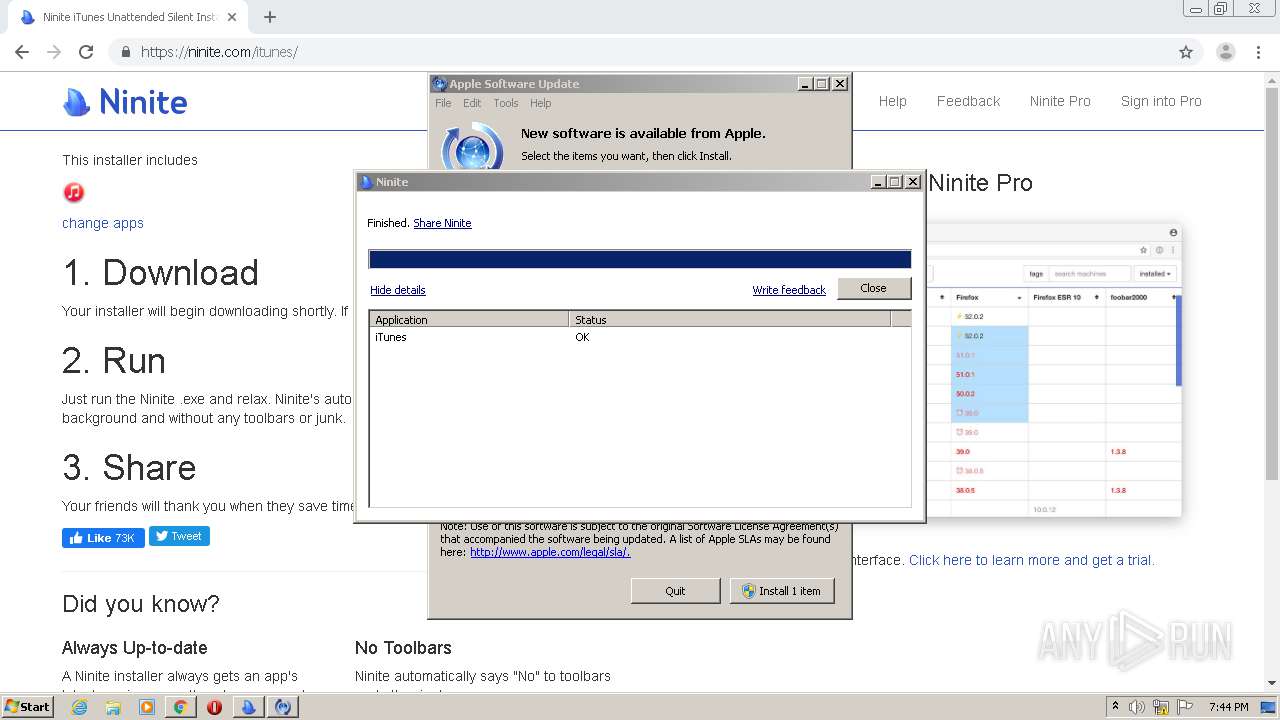
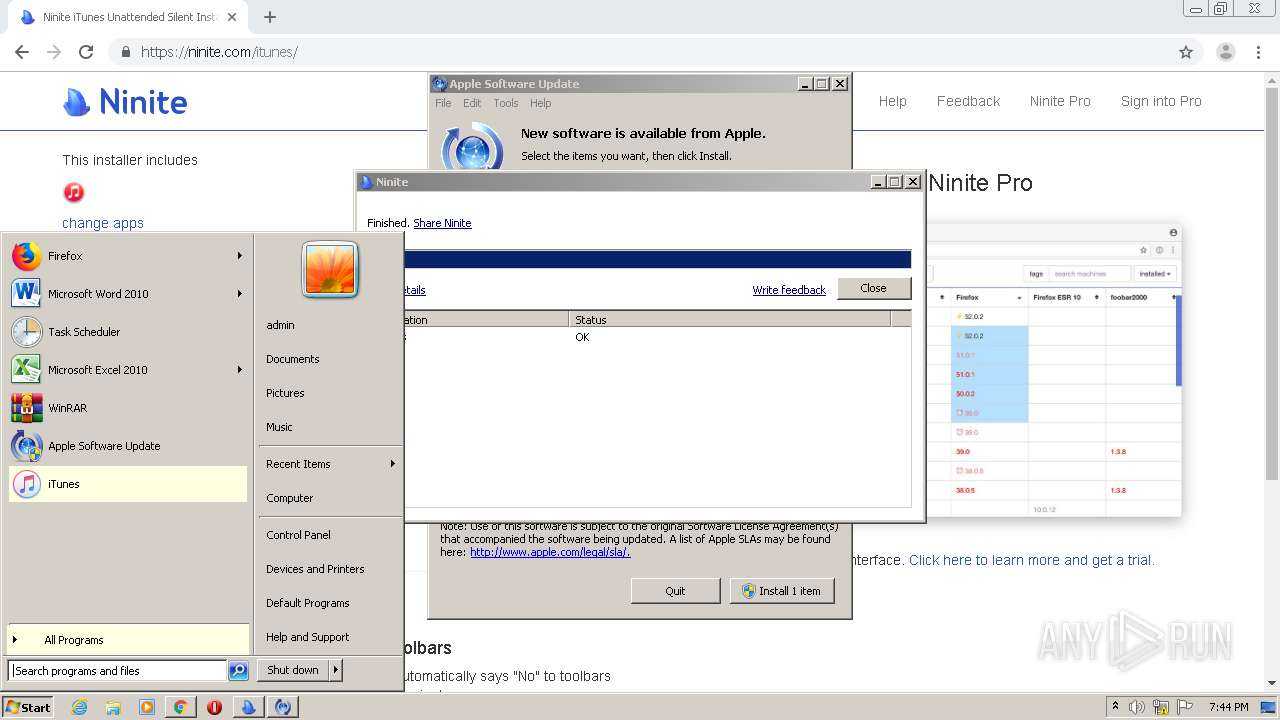
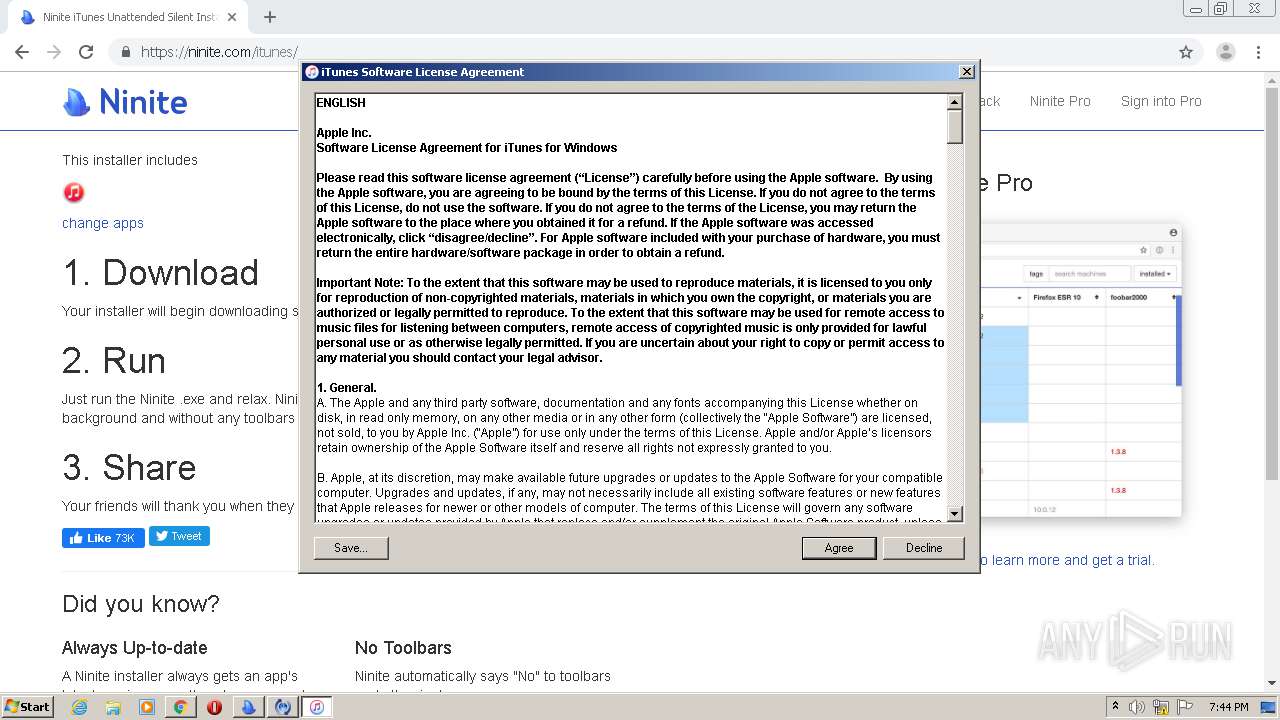
| Verdict: | Malicious activity |
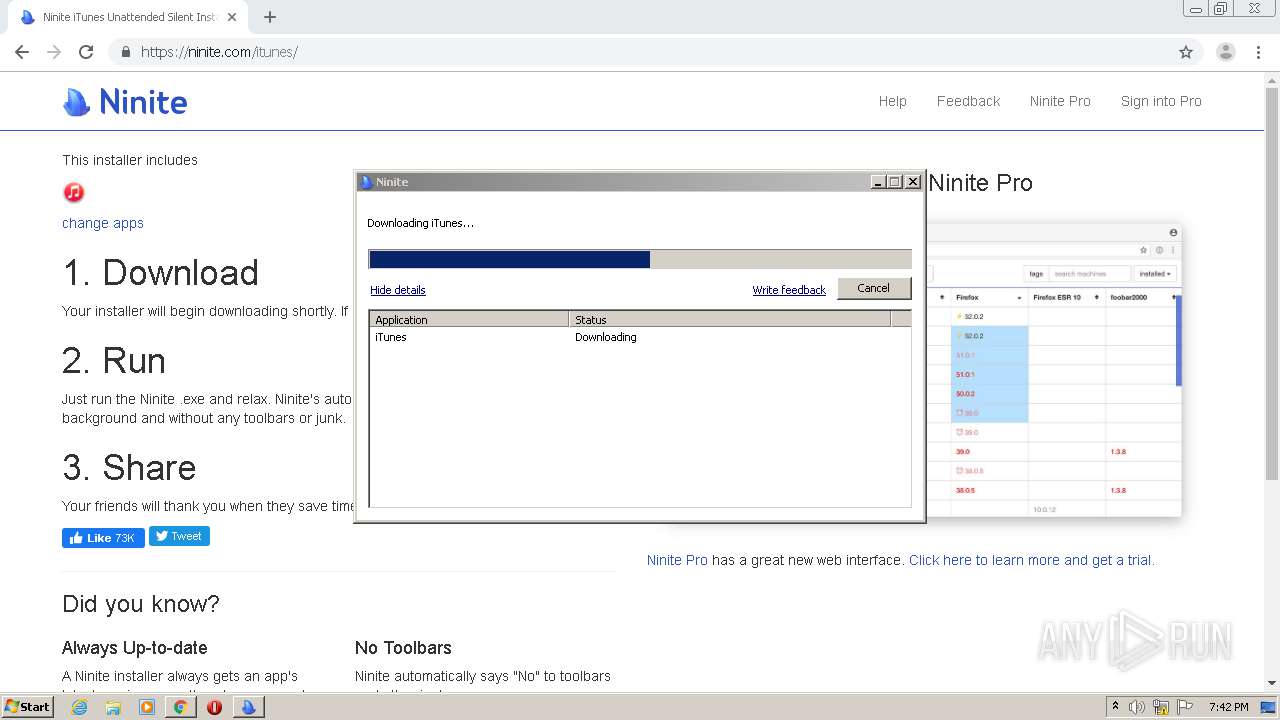
| Analysis date: | September 20, 2020, 18:40:27 |
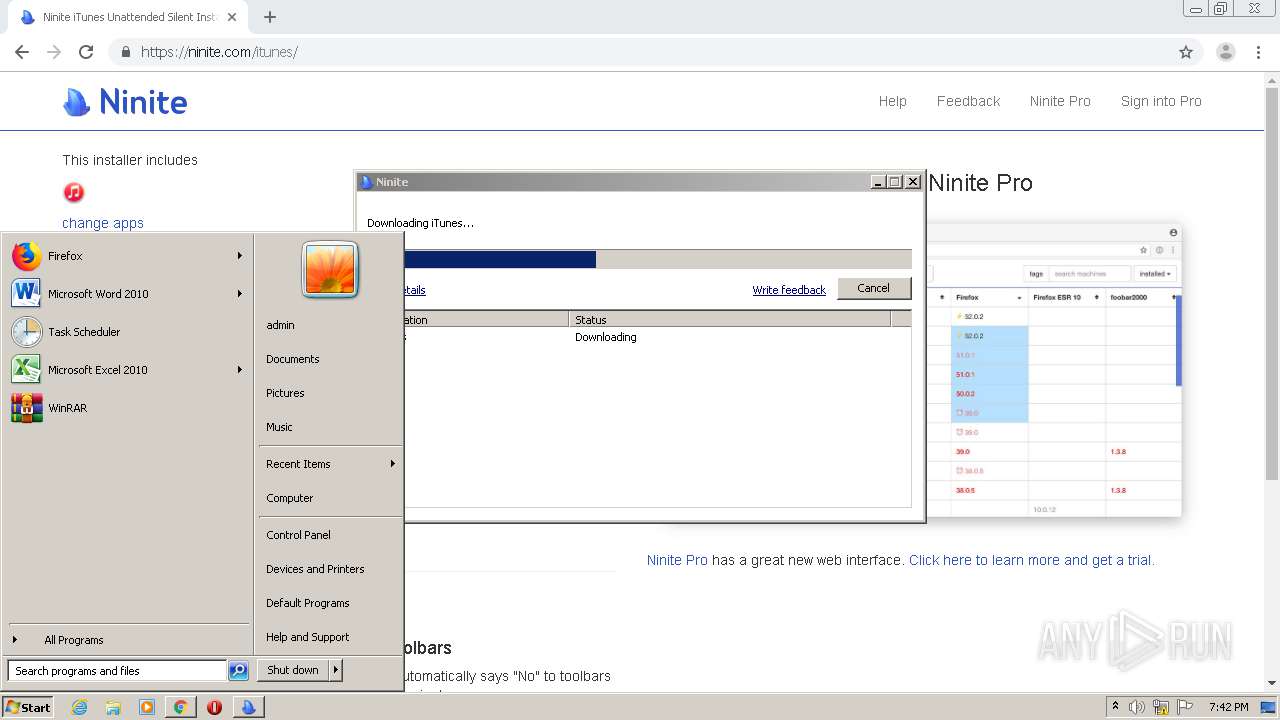
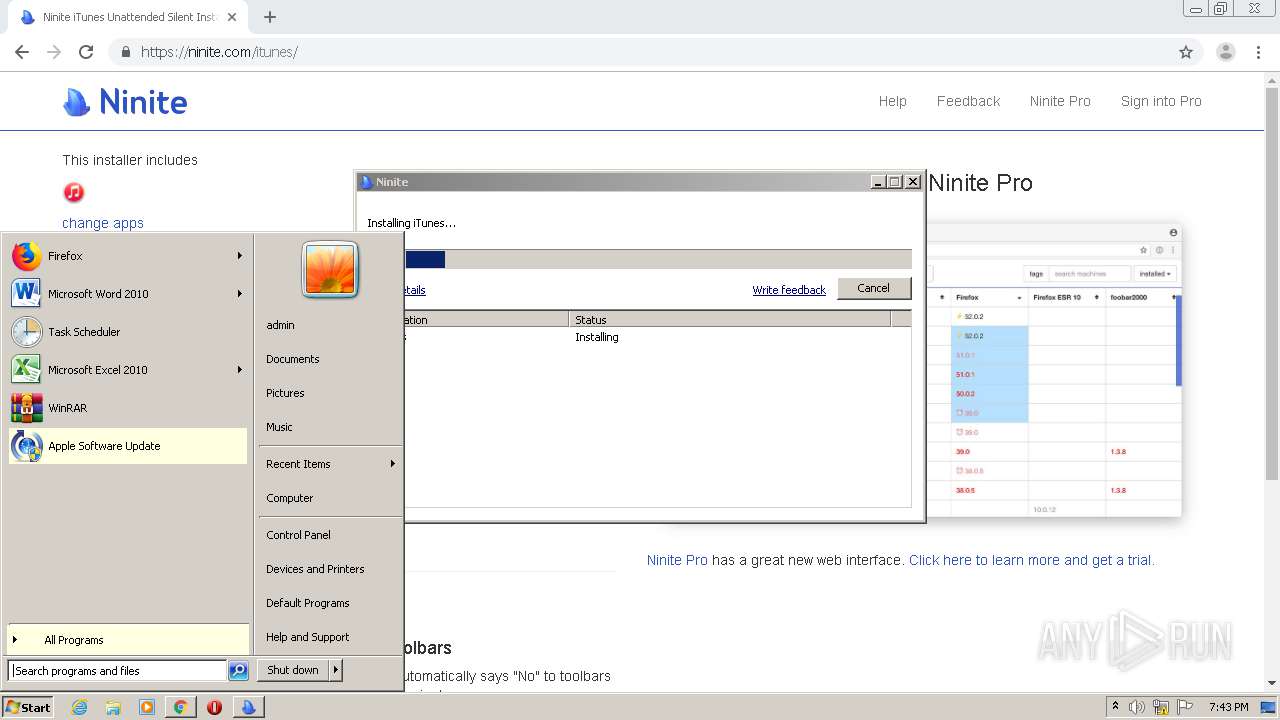
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FBA9CD5600FC68022E9955C42AC087F9 |
| SHA1: | 2696566521ACAC62F7C2923CD14FC11AF6F089ED |
| SHA256: | 4D19A8D5FD40E37AC9B73A0E75684EF424B14D1555F960FE024B4857570FA389 |
| SSDEEP: | 3:N8DAyG:2DAyG |
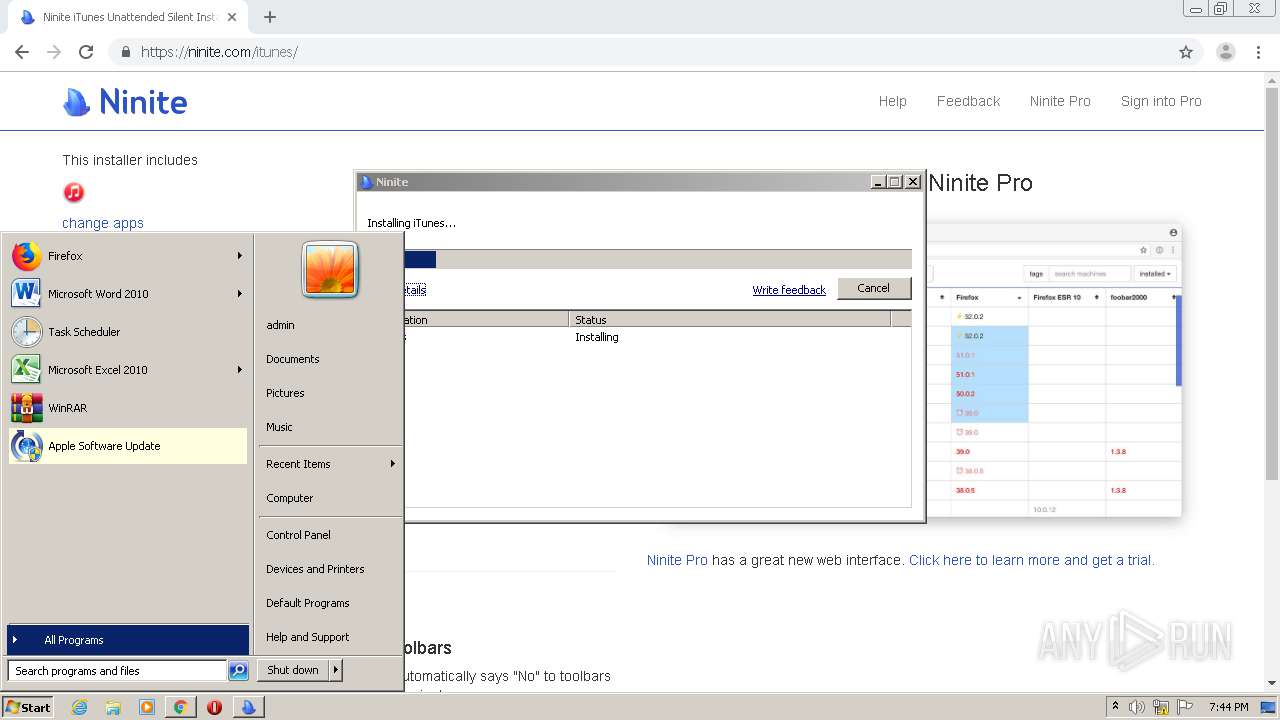
MALICIOUS
Changes settings of System certificates
- svchost.exe (PID: 1048)
- Ninite.exe (PID: 3024)
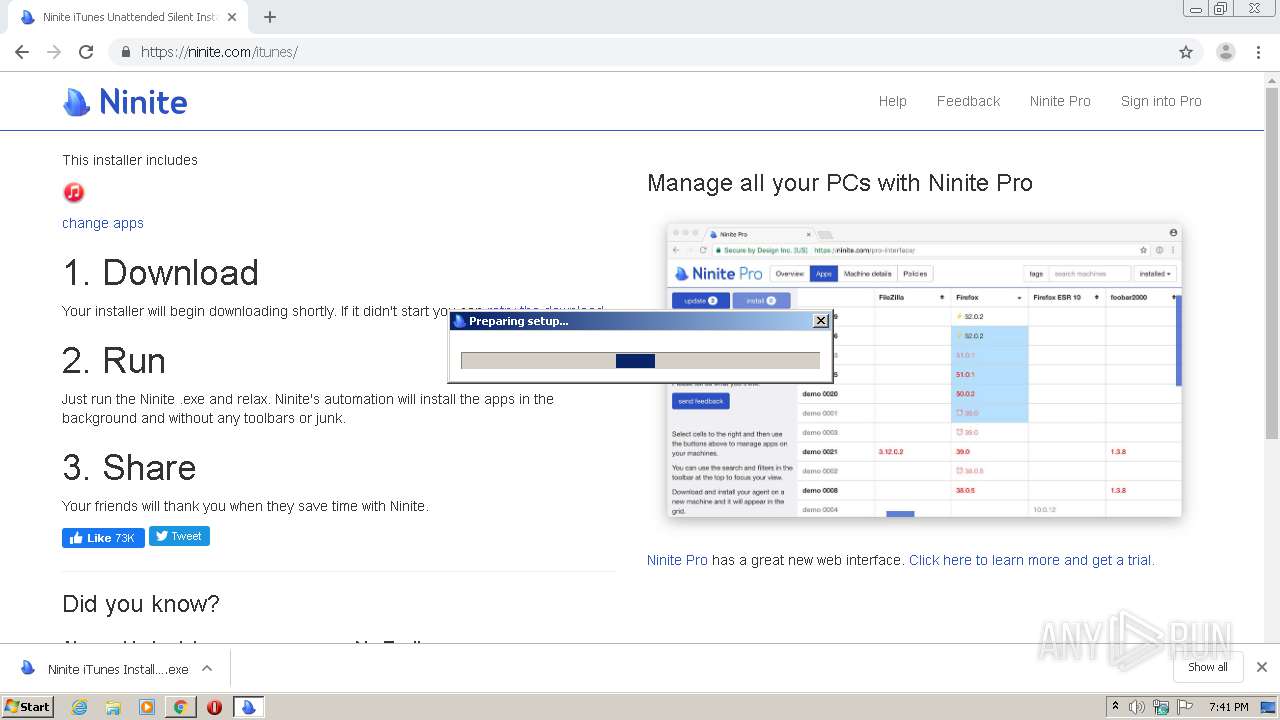
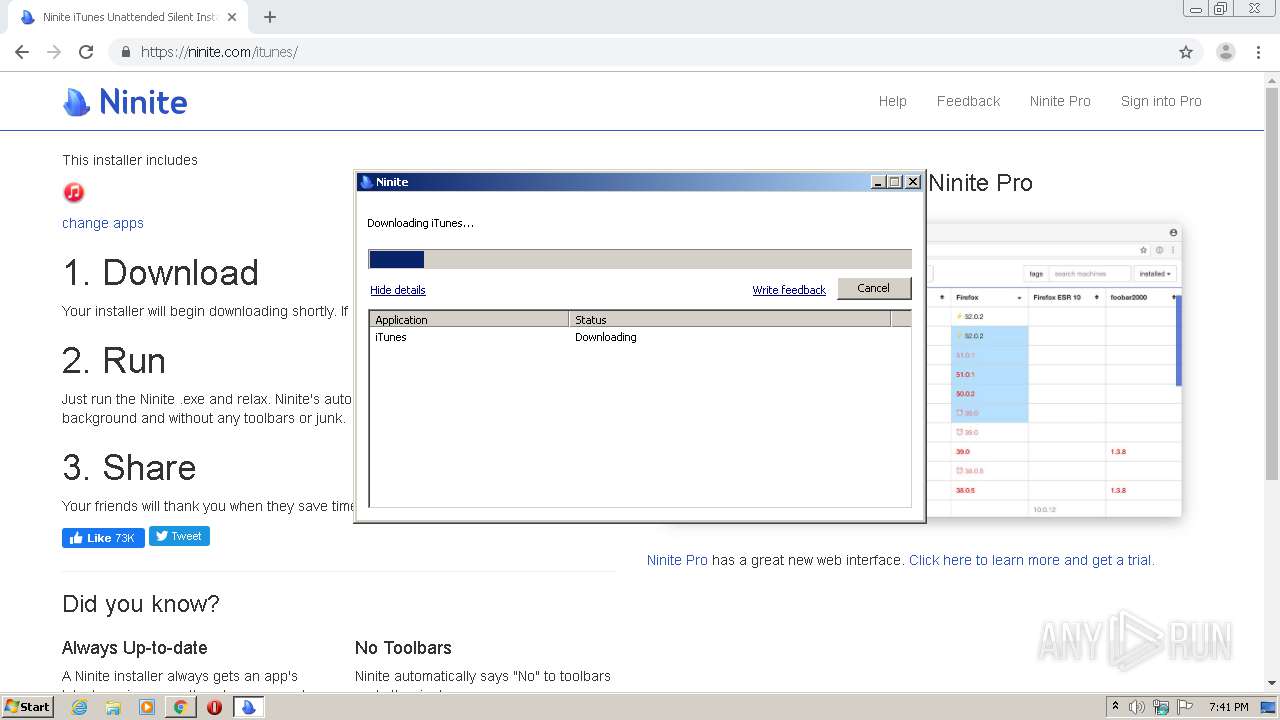
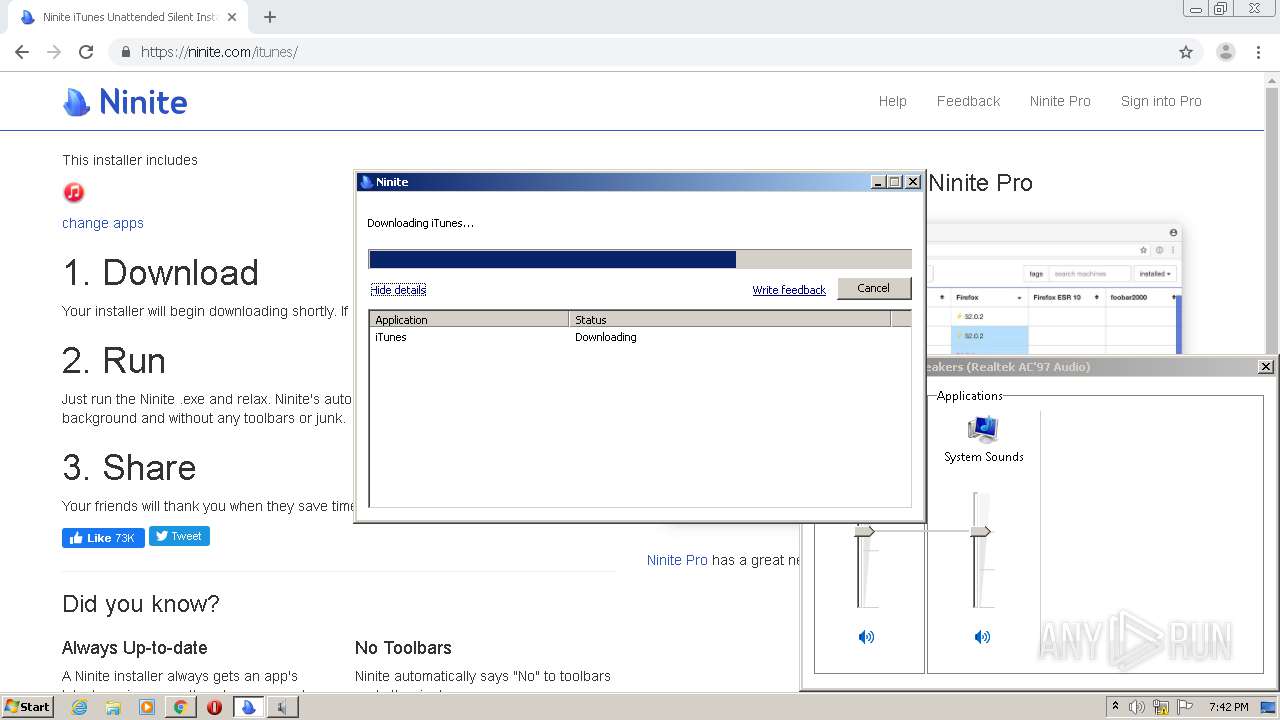
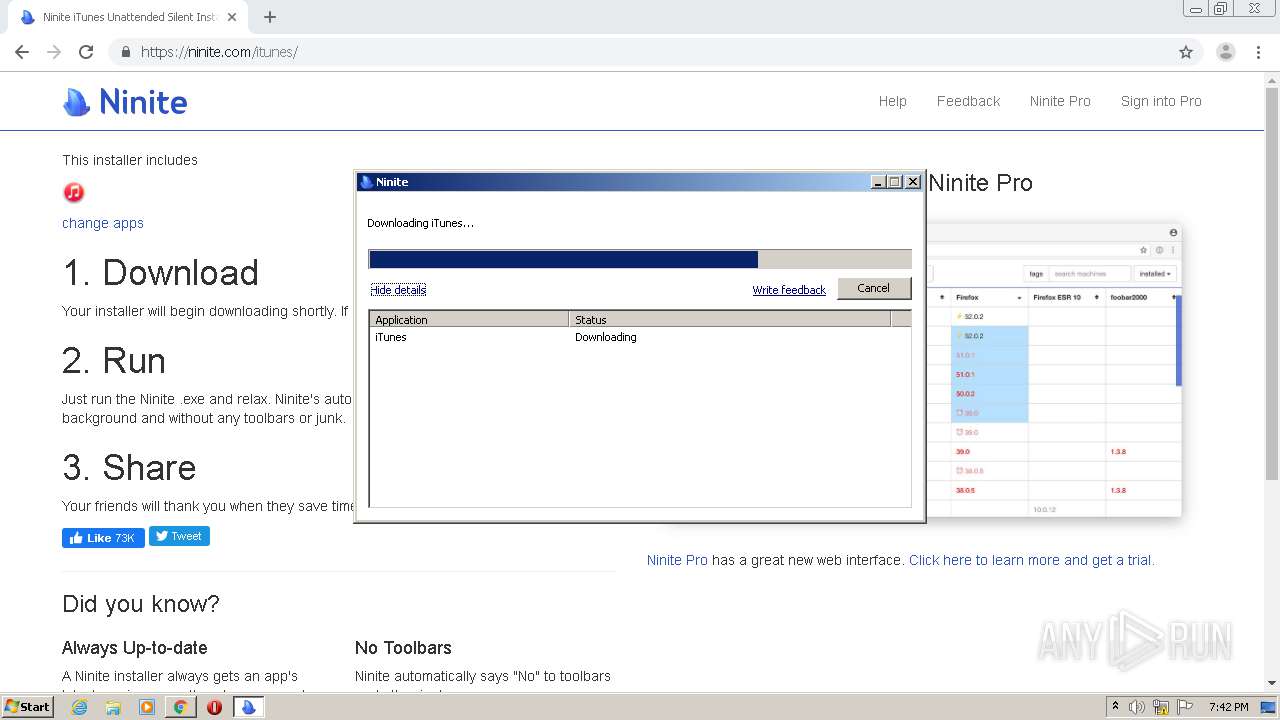
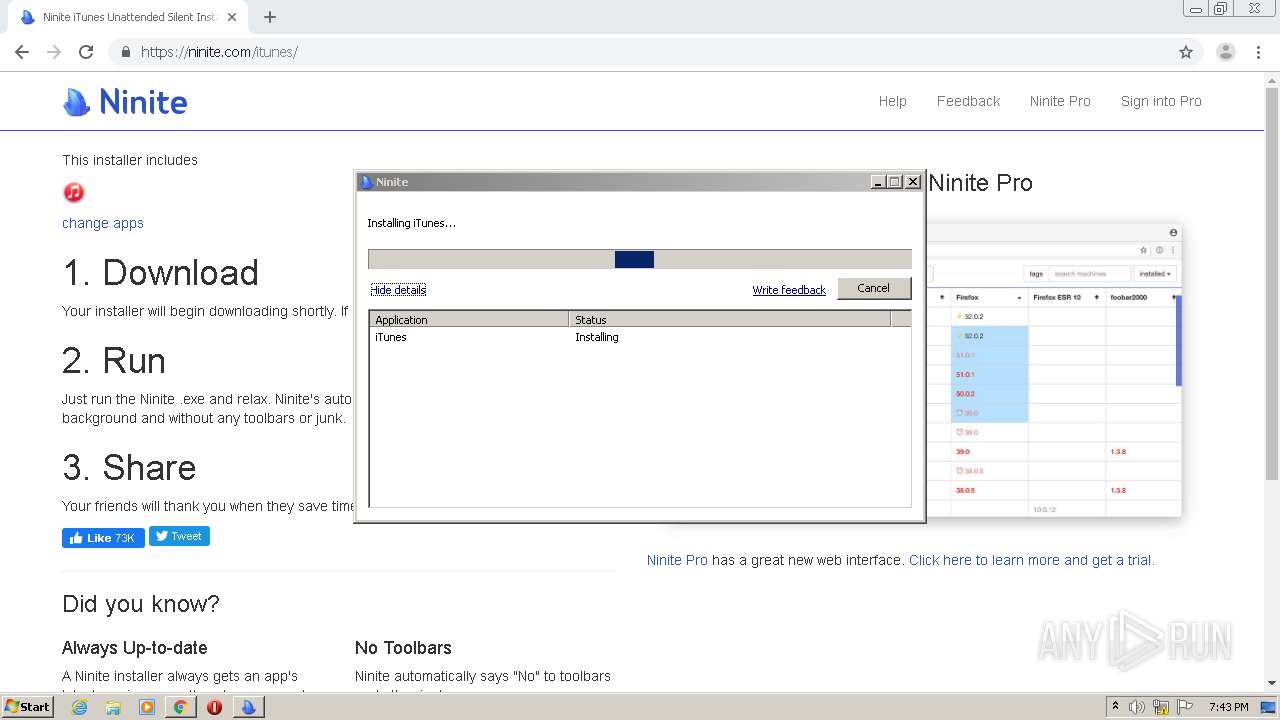
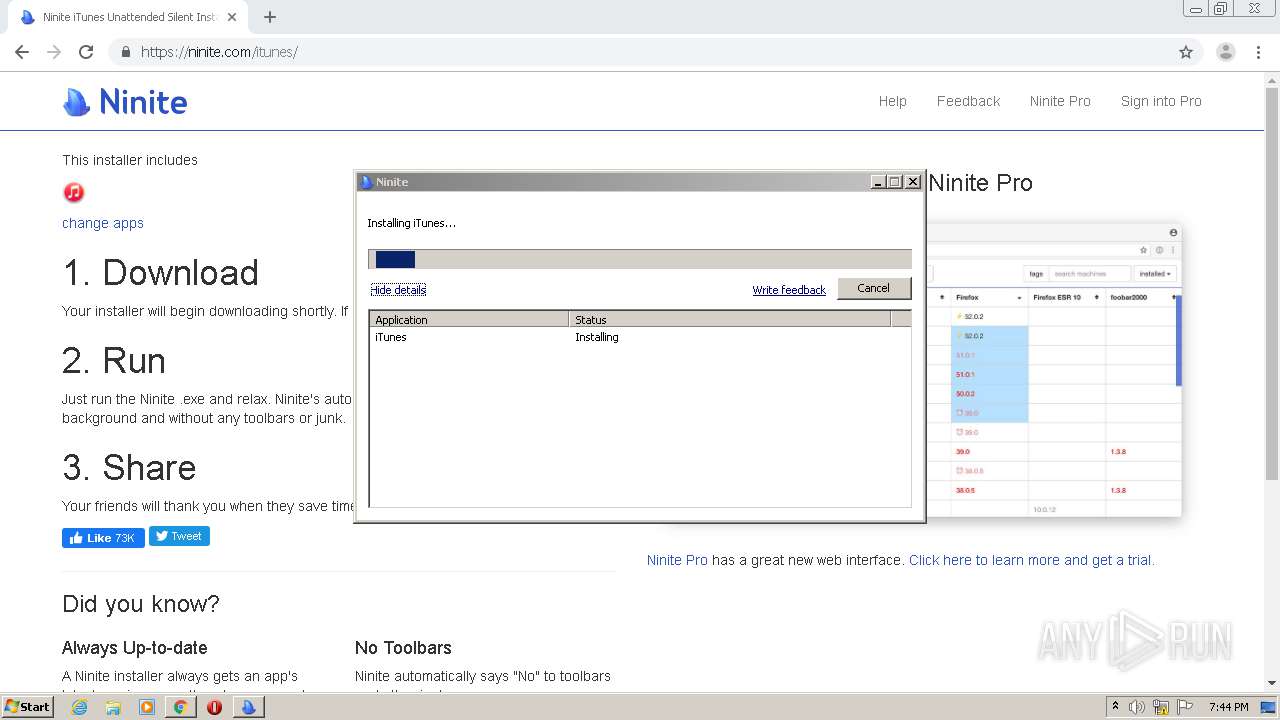
Application was dropped or rewritten from another process
- Ninite iTunes Installer.exe (PID: 3928)
- Ninite.exe (PID: 2360)
- Ninite.exe (PID: 3024)
- 7za.exe (PID: 3464)
- mDNSResponder.exe (PID: 2496)
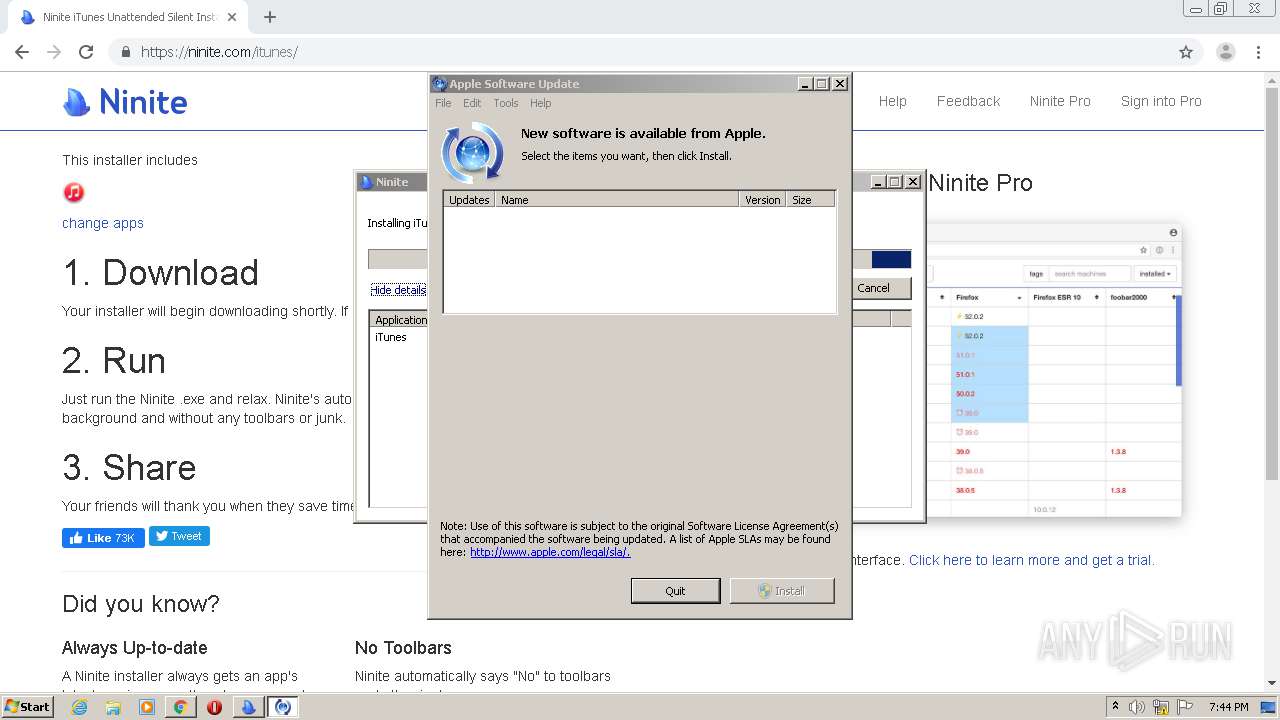
- SoftwareUpdate.exe (PID: 1064)
- AppleMobileDeviceService.exe (PID: 576)
- SoftwareUpdate.exe (PID: 2112)
- iTunesHelper.exe (PID: 2368)
- iTunes.exe (PID: 3244)
- AppleMobileDeviceHelper.exe (PID: 2176)
- iTunesVisualizerHost.exe (PID: 2460)
- distnoted.exe (PID: 3588)
- distnoted.exe (PID: 2344)
- iPodService.exe (PID: 1236)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 4060)
- explorer.exe (PID: 352)
- MsiExec.exe (PID: 392)
- SoftwareUpdate.exe (PID: 1064)
- svchost.exe (PID: 856)
- MsiExec.exe (PID: 3416)
- svchost.exe (PID: 676)
- DllHost.exe (PID: 2196)
- AppleMobileDeviceService.exe (PID: 576)
- SoftwareUpdate.exe (PID: 2112)
- DllHost.exe (PID: 2556)
- consent.exe (PID: 1800)
- svchost.exe (PID: 1048)
- iTunesHelper.exe (PID: 2368)
- iTunes.exe (PID: 3244)
- iTunesVisualizerHost.exe (PID: 2460)
- AppleMobileDeviceHelper.exe (PID: 2176)
- distnoted.exe (PID: 3588)
- distnoted.exe (PID: 2344)
- lsass.exe (PID: 488)
- SearchProtocolHost.exe (PID: 3808)
- chrome.exe (PID: 956)
Loads the Task Scheduler COM API
- DllHost.exe (PID: 2196)
- DllHost.exe (PID: 2556)
- DllHost.exe (PID: 2608)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 956)
- chrome.exe (PID: 292)
- Ninite iTunes Installer.exe (PID: 3928)
- 7za.exe (PID: 3464)
- Ninite.exe (PID: 3024)
- MsiExec.exe (PID: 2204)
- DrvInst.exe (PID: 1504)
Modifies files in Chrome extension folder
- chrome.exe (PID: 292)
Adds / modifies Windows certificates
- svchost.exe (PID: 1048)
- Ninite.exe (PID: 3024)
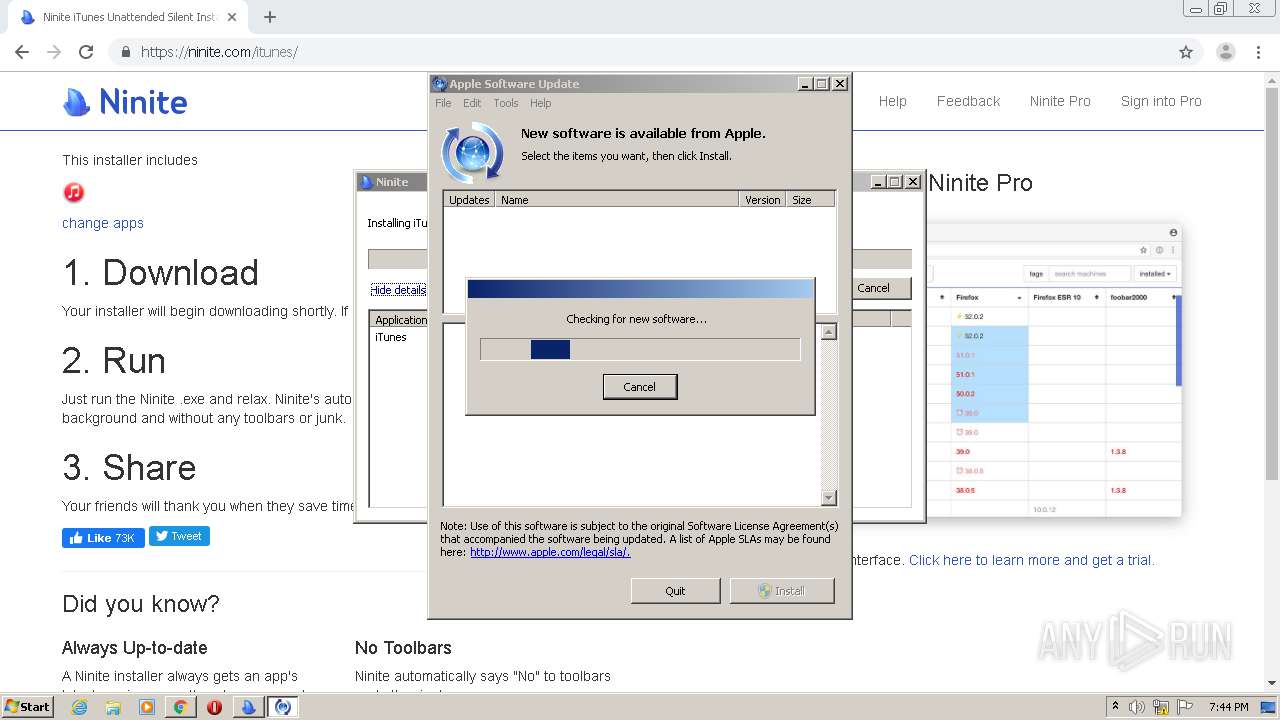
Reads Internet Cache Settings
- Ninite iTunes Installer.exe (PID: 3928)
- Ninite.exe (PID: 3024)
- SoftwareUpdate.exe (PID: 2112)
- DllHost.exe (PID: 2332)
- iTunes.exe (PID: 3244)
Application launched itself
- Ninite.exe (PID: 2360)
- SndVol.exe (PID: 3736)
Cleans NTFS data-stream (Zone Identifier)
- Ninite.exe (PID: 3024)
Starts Microsoft Installer
- Ninite.exe (PID: 3024)
Executed as Windows Service
- mDNSResponder.exe (PID: 2496)
- AppleMobileDeviceService.exe (PID: 576)
- iPodService.exe (PID: 1236)
Creates COM task schedule object
- MsiExec.exe (PID: 3416)
Executed via COM
- DllHost.exe (PID: 2196)
- DrvInst.exe (PID: 2724)
- DrvInst.exe (PID: 1504)
- DllHost.exe (PID: 2556)
- DllHost.exe (PID: 2332)
- DllHost.exe (PID: 2608)
Removes files from Windows directory
- DrvInst.exe (PID: 2724)
- svchost.exe (PID: 1048)
- DrvInst.exe (PID: 1504)
- svchost.exe (PID: 856)
- lsass.exe (PID: 488)
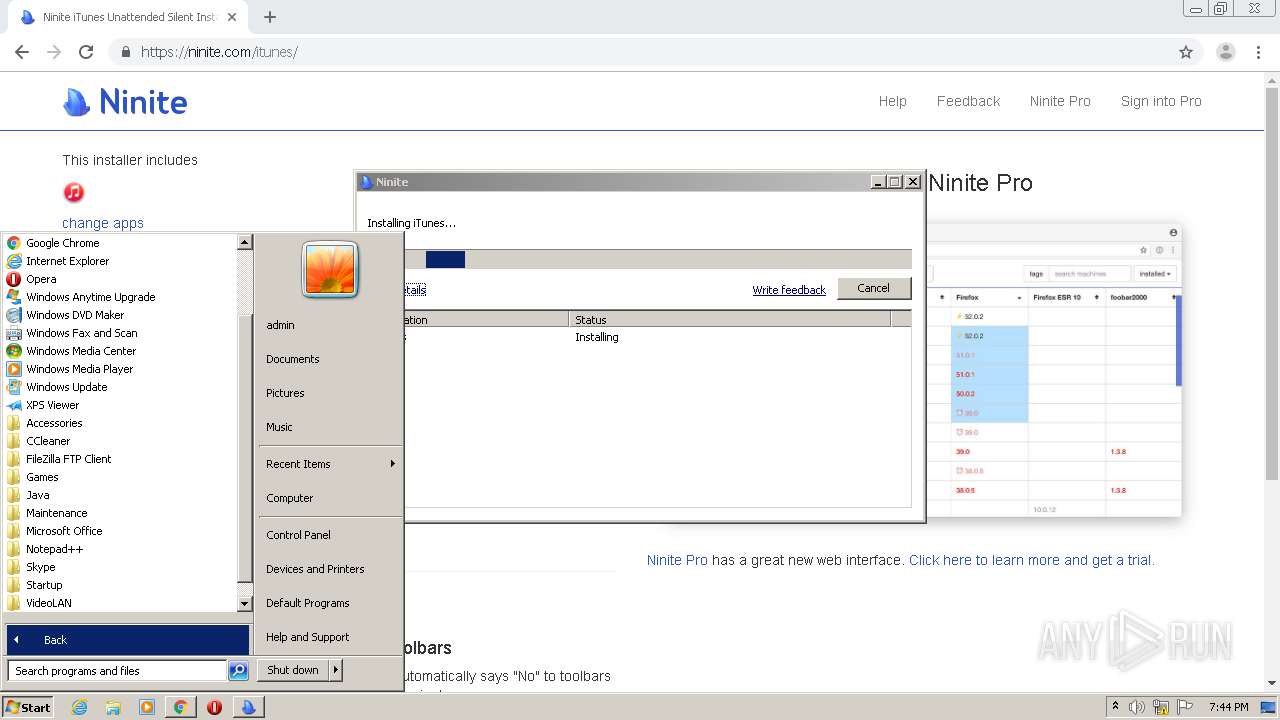
Searches for installed software
- Ninite.exe (PID: 3024)
Creates files in the Windows directory
- DrvInst.exe (PID: 2724)
- svchost.exe (PID: 856)
- svchost.exe (PID: 1048)
- DrvInst.exe (PID: 1504)
- lsass.exe (PID: 488)
Creates files in the driver directory
- DrvInst.exe (PID: 2724)
- DrvInst.exe (PID: 1504)
Creates files in the program directory
- AppleMobileDeviceService.exe (PID: 576)
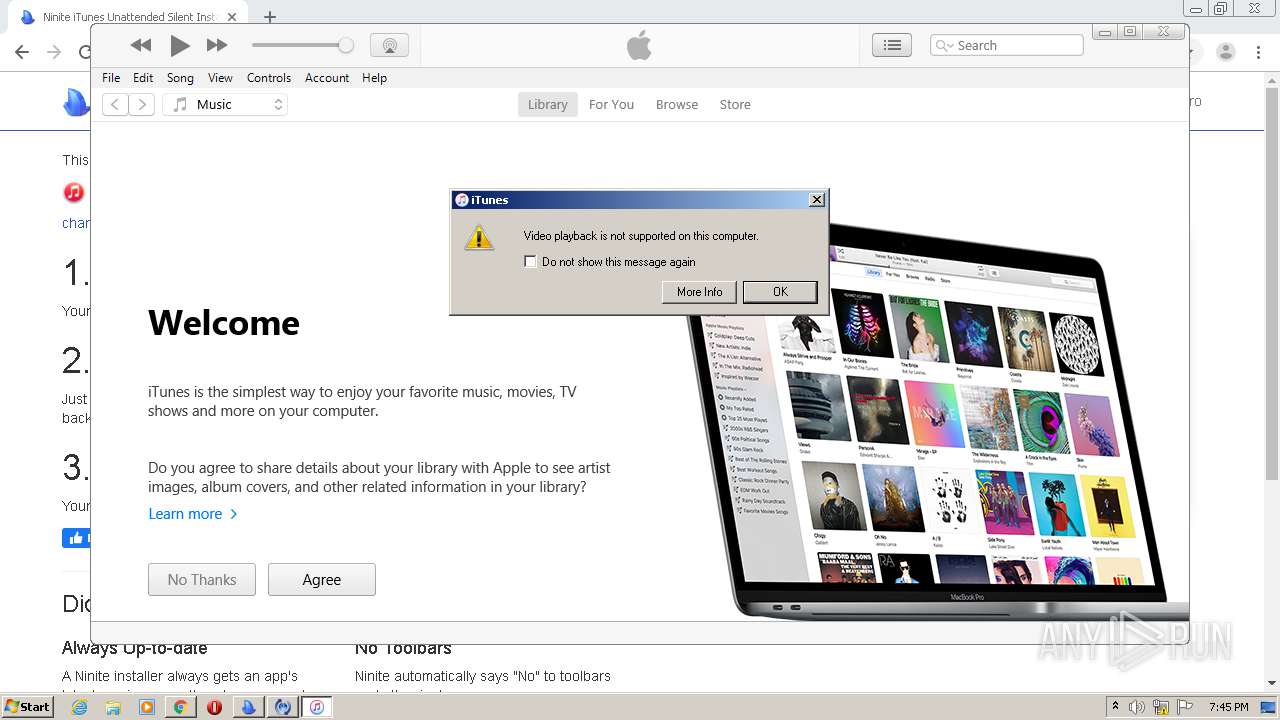
- iTunes.exe (PID: 3244)
Reads internet explorer settings
- SoftwareUpdate.exe (PID: 2112)
Reads the BIOS version
- iTunes.exe (PID: 3244)
Creates files in the user directory
- iTunes.exe (PID: 3244)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 956)
- chrome.exe (PID: 292)
- svchost.exe (PID: 1048)
- iTunes.exe (PID: 3244)
- lsass.exe (PID: 488)
Reads the hosts file
- chrome.exe (PID: 956)
- chrome.exe (PID: 292)
Reads Internet Cache Settings
- chrome.exe (PID: 292)
Application launched itself
- chrome.exe (PID: 292)
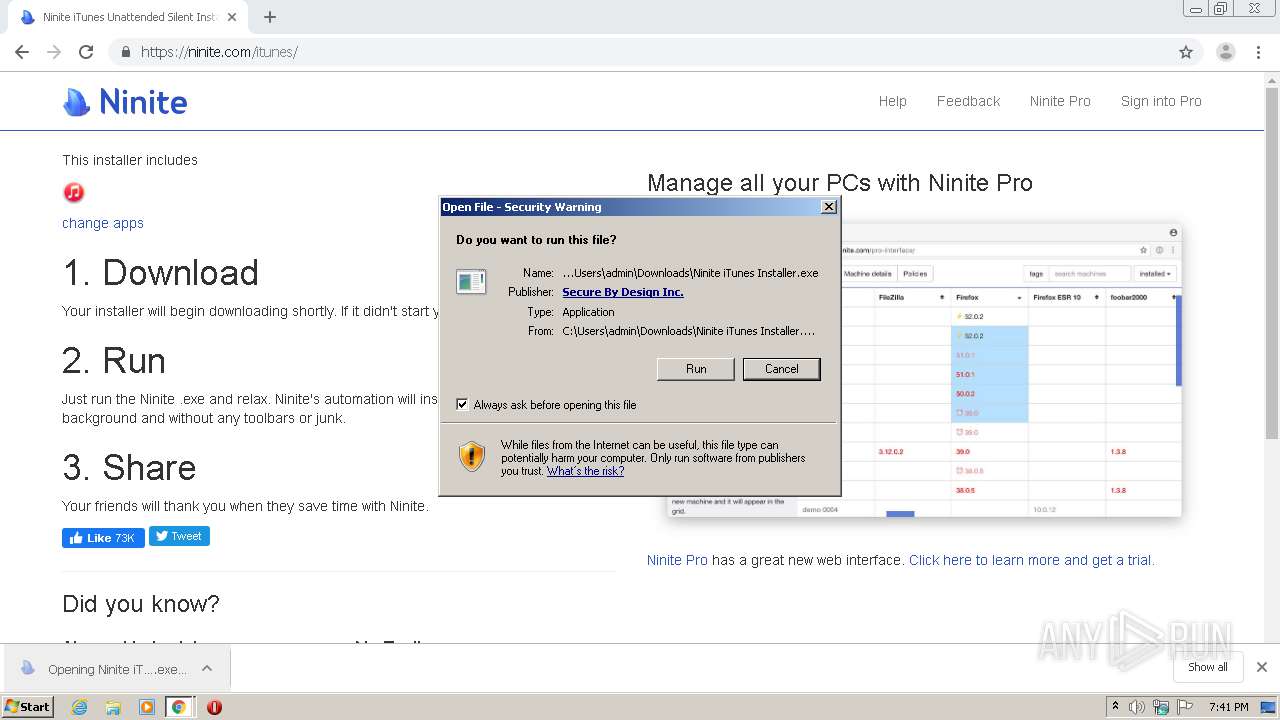
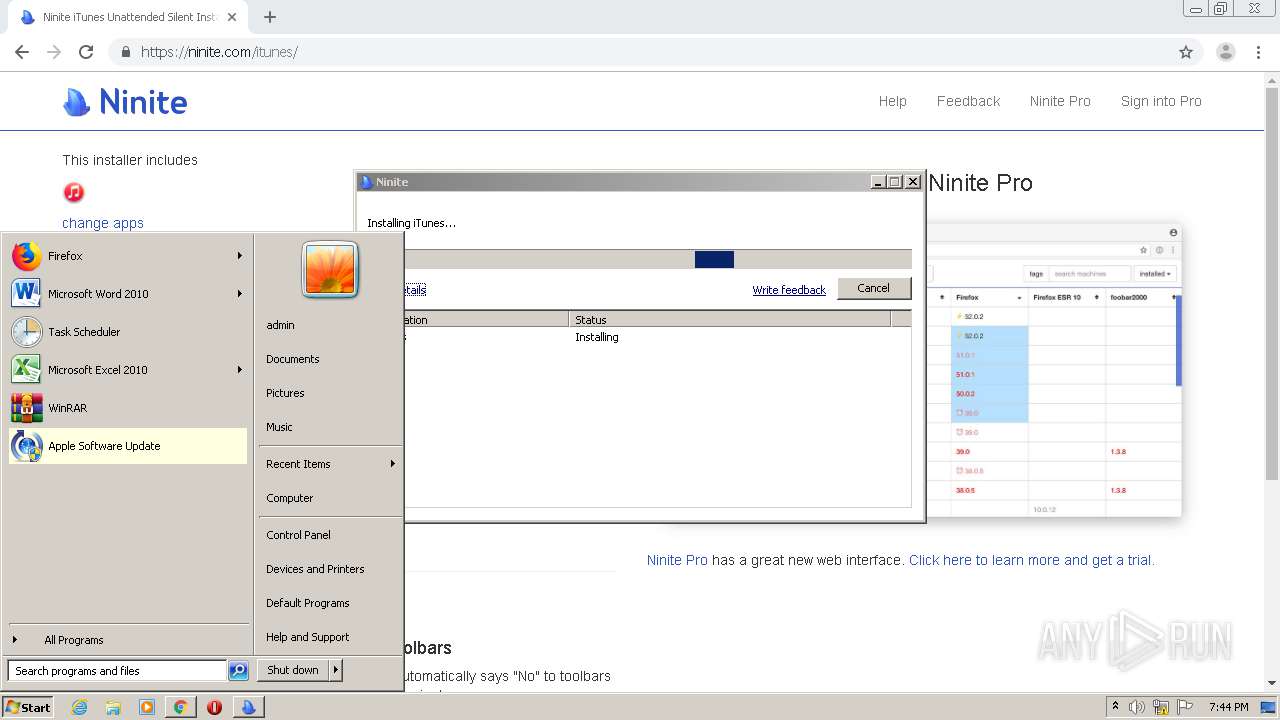
Manual execution by user
- SndVol.exe (PID: 3736)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
109
Monitored processes
57
Malicious processes
18
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,2479698327166396154,12763720859575232041,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5682931108007710621 --mojo-platform-channel-handle=1132 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://ninite.com/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | "C:\Windows\system32\MsiExec.exe" /Y "C:\Program Files\Bonjour\mdnsNSP.dll" | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,2479698327166396154,12763720859575232041,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15404166441621920478 --mojo-platform-channel-handle=3460 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 488 | C:\Windows\system32\lsass.exe | C:\Windows\System32\lsass.exe | — | wininit.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | "C:\Program Files\Common Files\Apple\Mobile Device Support\AppleMobileDeviceService.exe" | C:\Program Files\Common Files\Apple\Mobile Device Support\AppleMobileDeviceService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Apple Inc. Integrity Level: SYSTEM Description: MobileDeviceService Exit code: 0 Version: 486.0.2.16 Modules
| |||||||||||||||
| 676 | C:\Windows\system32\svchost.exe -k RPCSS | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 856 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | msiexec.exe /i "C:\Users\admin\AppData\Local\Temp\DD80BC~1\AppleSoftwareUpdate.msi" /qn /norestart REBOOT=ReallySuppress ALLUSERS=1 /Le "C:\Users\admin\AppData\Local\Temp\DD80BC~1\22f860bf-fb71-11ea-8c46-12a9866c77de" | C:\Windows\system32\msiexec.exe | — | Ninite.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 187
Read events
6 354
Write events
806
Delete events
27
Modification events
| (PID) Process: | (292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 292-13245100841920500 |
Value: 259 | |||
| (PID) Process: | (292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (292) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 292-13245100841920500 |
Value: 259 | |||
Executable files
17
Suspicious files
118
Text files
228
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2d602470-d448-4a91-8fe5-aef66ef7be51.tmp | — | |
MD5:— | SHA256:— | |||
| 856 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFed628.TMP | text | |
MD5:— | SHA256:— | |||
| 292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFed685.TMP | text | |
MD5:— | SHA256:— | |||
| 292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFed7ed.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
59
DNS requests
48
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3928 | Ninite iTunes Installer.exe | GET | 304 | 8.253.207.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3244 | iTunes.exe | POST | 200 | 208.72.242.165:80 | http://c12850432.mgr.gcsp.cddbp.net/gcsp/2.0 | US | — | — | unknown |
956 | chrome.exe | GET | 200 | 176.126.58.209:80 | http://r6---sn-x2pm-3ufk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=sX&mip=84.17.55.74&mm=28&mn=sn-x2pm-3ufk&ms=nvh&mt=1600627152&mv=m&mvi=6&pl=23&shardbypass=yes | PL | crx | 834 Kb | whitelisted |
956 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWFjQUFXV2lsMkZVdjR5Vk5VZHJTM3E1dw/7919.1028.0.0_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
292 | chrome.exe | GET | 200 | 8.253.207.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
3928 | Ninite iTunes Installer.exe | GET | 200 | 13.35.253.185:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3928 | Ninite iTunes Installer.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAGC%2BAmOouYmuRo7J4Qfua8%3D | US | der | 1.47 Kb | whitelisted |
3928 | Ninite iTunes Installer.exe | GET | 200 | 143.204.208.165:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3024 | Ninite.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAgRQFZLq86Uy%2B4JCiho9J0%3D | US | der | 471 b | whitelisted |
292 | chrome.exe | GET | 304 | 8.253.207.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
956 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
956 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
956 | chrome.exe | 52.7.124.208:443 | ninite.com | Amazon.com, Inc. | US | unknown |
956 | chrome.exe | 216.58.207.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
956 | chrome.exe | 13.35.253.204:443 | d8f7mp21btv4f.cloudfront.net | — | US | malicious |
956 | chrome.exe | 142.250.74.196:443 | www.google.com | Google Inc. | US | whitelisted |
956 | chrome.exe | 172.217.18.104:443 | ssl.google-analytics.com | Google Inc. | US | suspicious |
956 | chrome.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
956 | chrome.exe | 93.184.220.66:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
956 | chrome.exe | 185.60.216.35:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
ninite.com |
| whitelisted |
accounts.google.com |
| shared |
d8f7mp21btv4f.cloudfront.net |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r6---sn-x2pm-3ufk.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
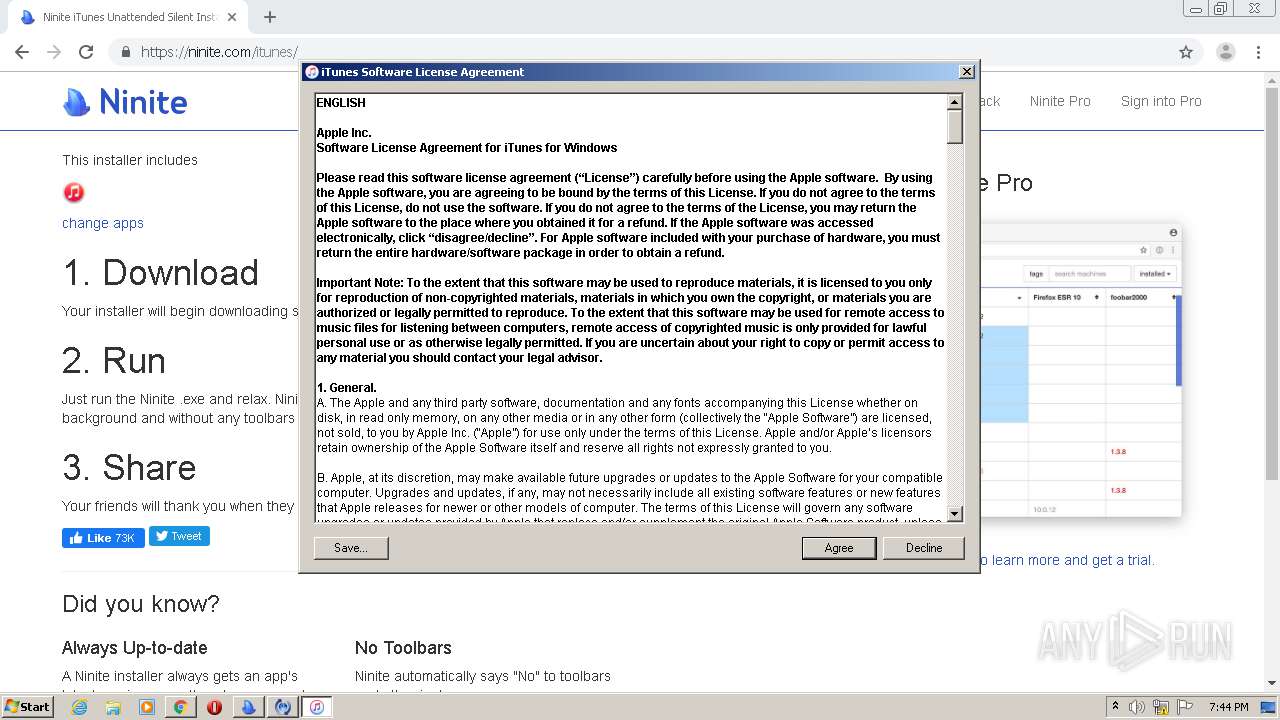
3244 | iTunes.exe | Potential Corporate Privacy Violation | ET POLICY iTunes User Agent |
Process | Message |
|---|---|
AppleMobileDeviceService.exe | ASL checking for logging parameters in environment variable "asl.log"
|
AppleMobileDeviceService.exe | ASL checking for logging parameters in environment variable "AppleMobileDeviceService.exe.log"
|
iTunesHelper.exe | ASL checking for logging parameters in environment variable "asl.log"
|
iTunesHelper.exe | ASL checking for logging parameters in environment variable "iTunesHelper.exe.log"
|
iTunes.exe | |
iTunes.exe | Couldn't load our private device map. Device identification will be limited. |
iTunes.exe | |
iTunes.exe | |
iTunes.exe | ASL checking for logging parameters in environment variable "asl.log"
|
iTunes.exe | ASL logging to file "C:\Users\admin\AppData\Roaming\Apple Computer\Logs\asl.194448_20Sep20.log"
|