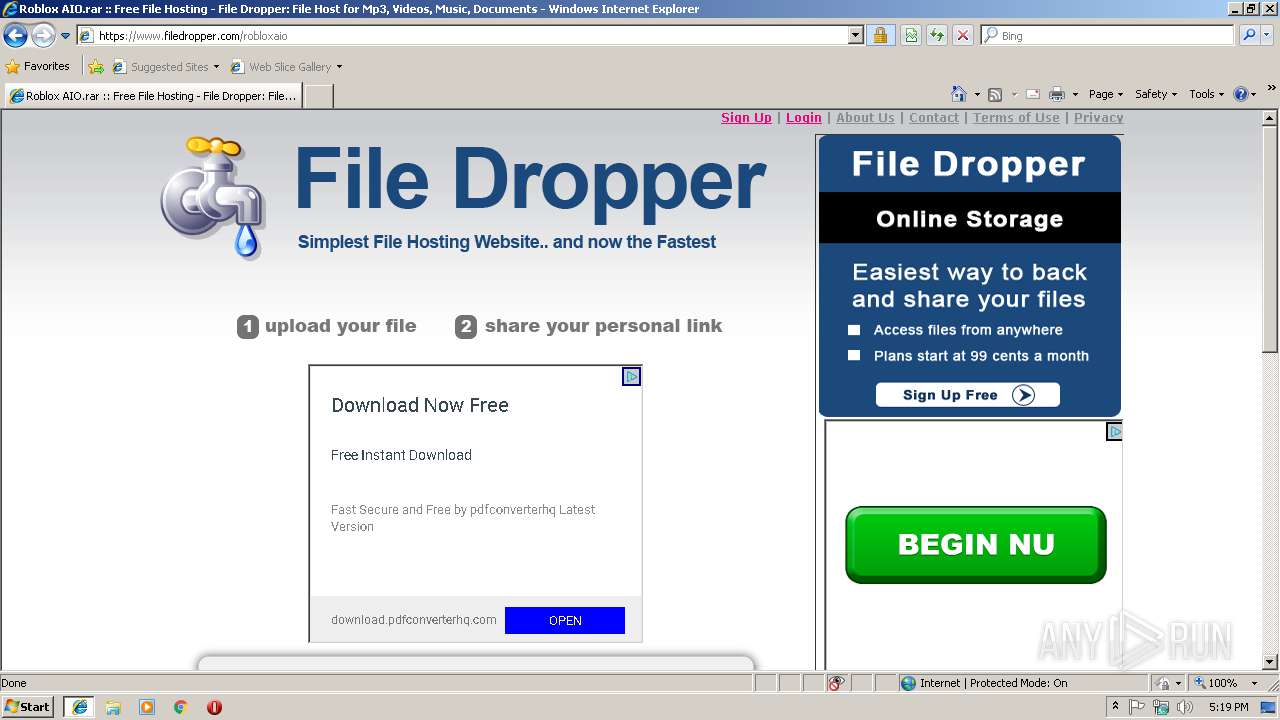
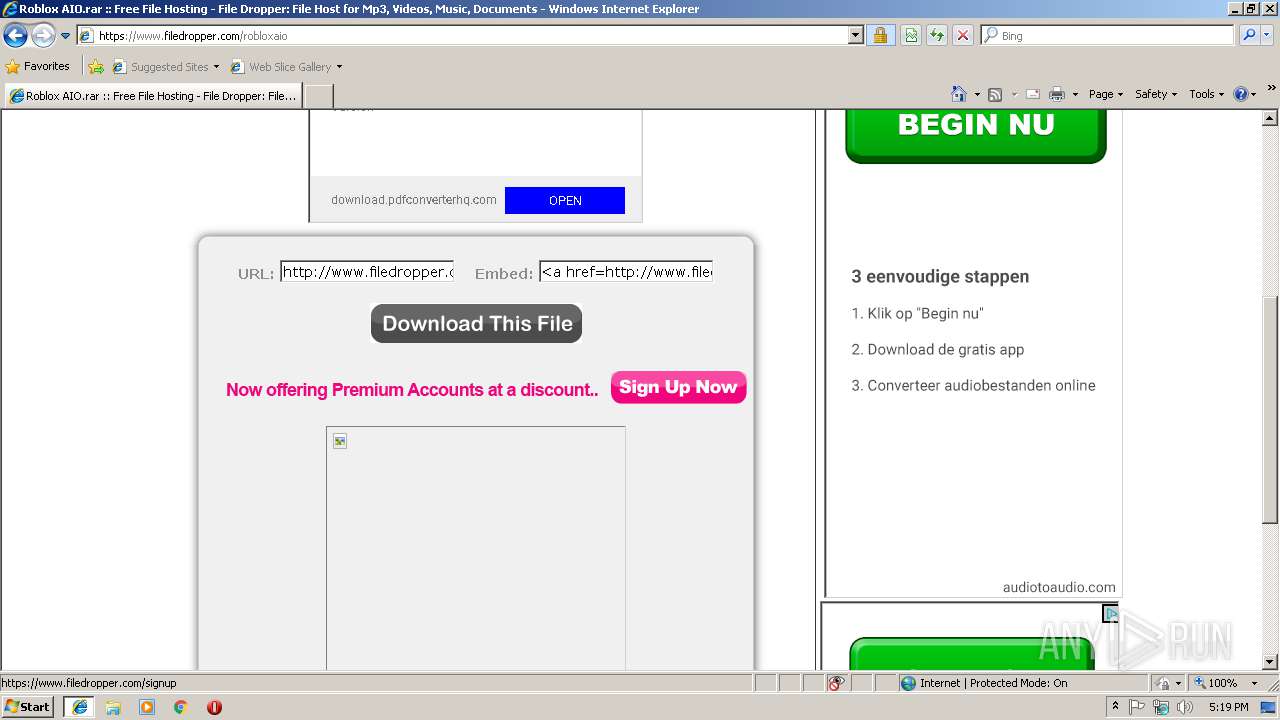
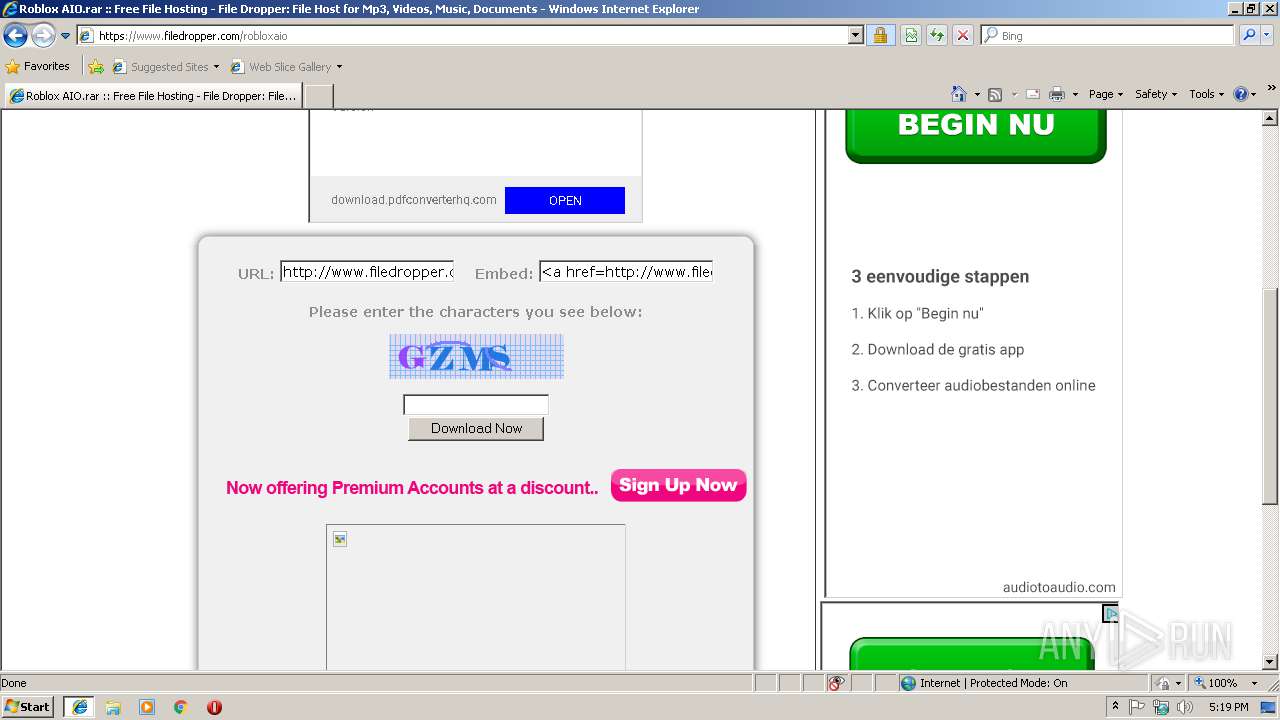
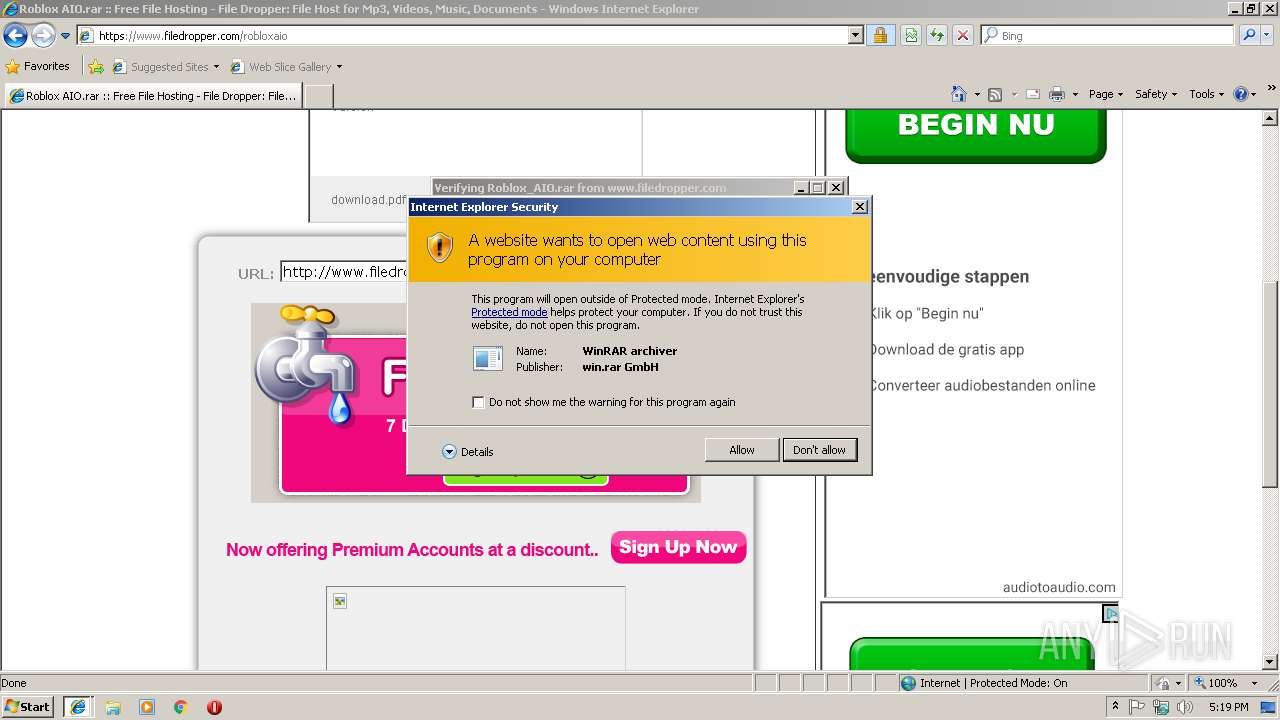
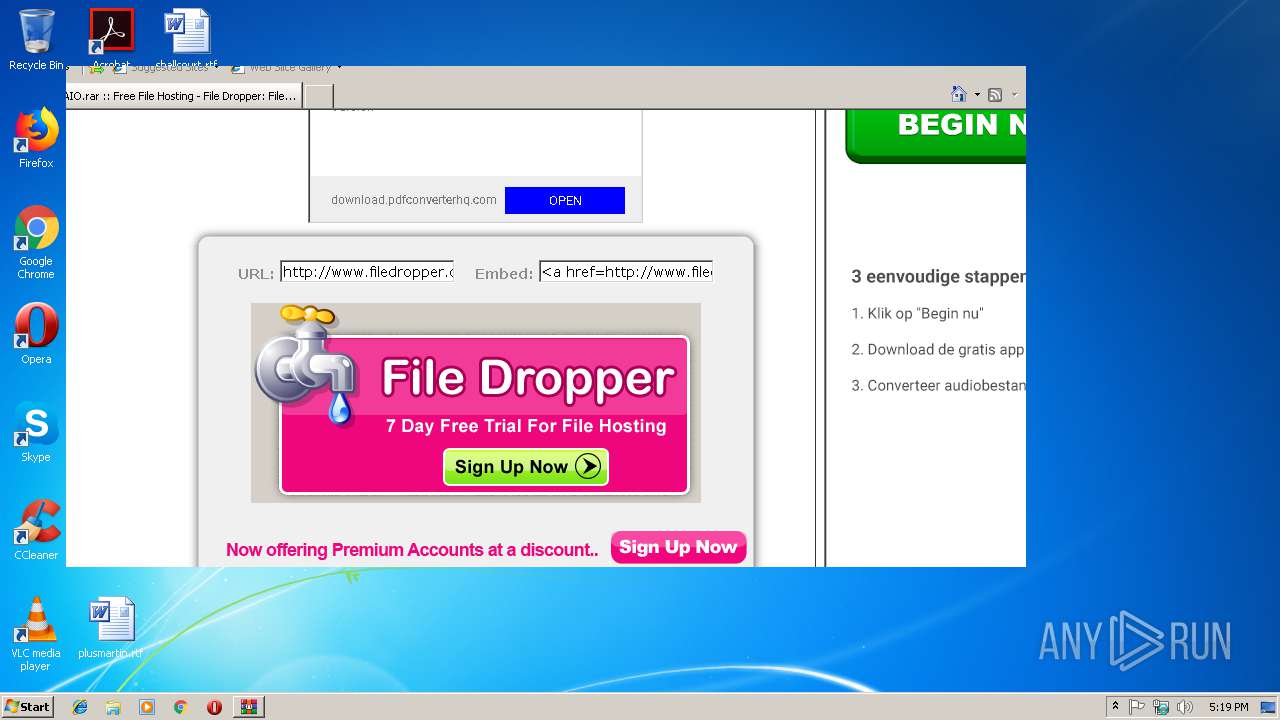
| URL: | https://www.filedropper.com/robloxaio |
| Full analysis: | https://app.any.run/tasks/28dd7192-74dd-4822-a763-52f84881e2e6 |
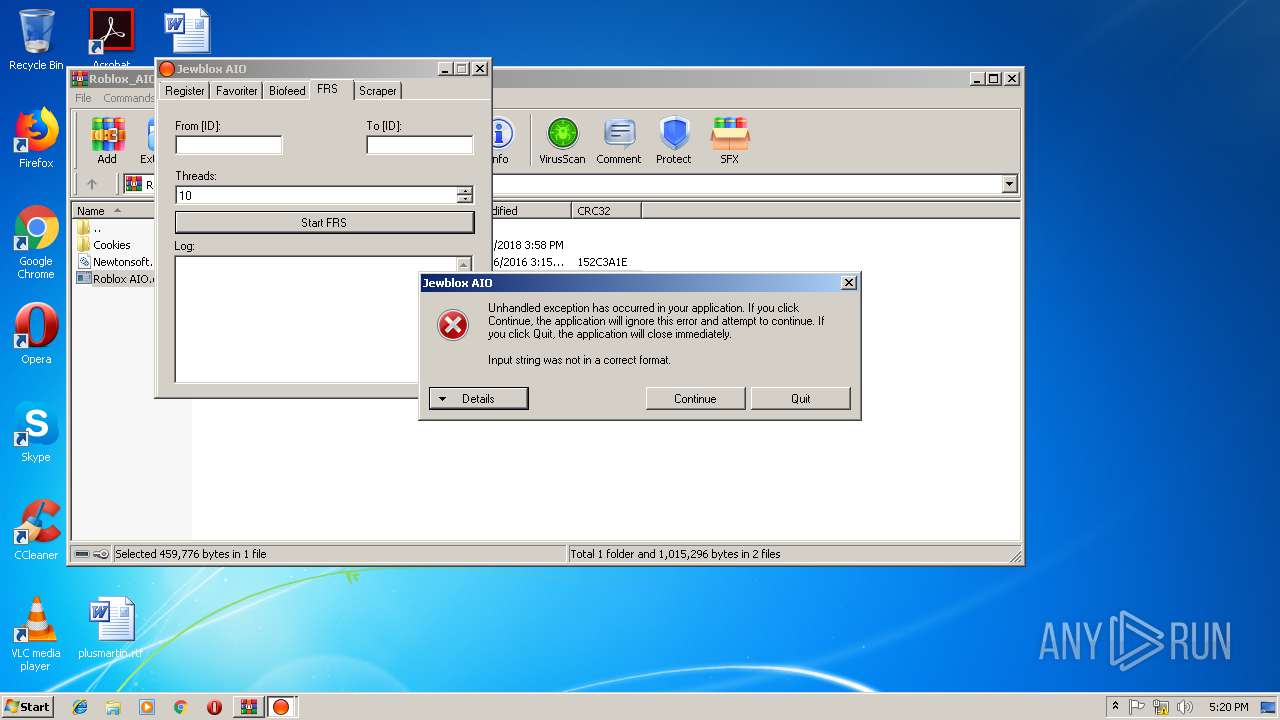
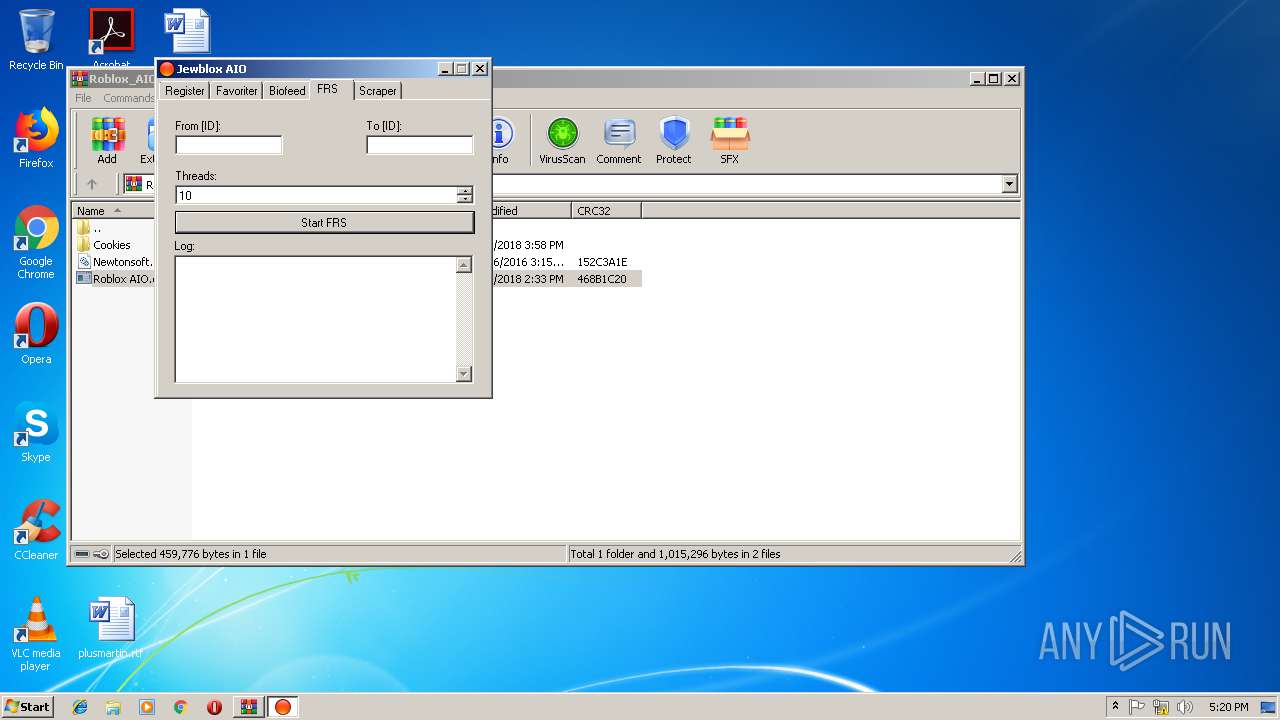
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2019, 17:18:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CB85BE2995D0DF70F6A23B79E8917FE3 |
| SHA1: | 5989EA0FE8ECD29E393FB4B2F95302D30DE18725 |
| SHA256: | 4D079336CA665ED4832DAD81B354771017BA46397ACC41A262B055CE145BB025 |
| SSDEEP: | 3:N8DSLQuXrxdQ:2OLQodQ |
MALICIOUS
Application was dropped or rewritten from another process
- Roblox AIO.exe (PID: 2684)
- ROBLOX AIO.EXE (PID: 3652)
- SYSTEM.EXE (PID: 2456)
- SYSTEM.EXE (PID: 2284)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2668)
- Roblox AIO.exe (PID: 2684)
- SYSTEM.EXE (PID: 2456)
Application launched itself
- SYSTEM.EXE (PID: 2284)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 3732)
Creates files in the user directory
- iexplore.exe (PID: 3732)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3084)
Changes internet zones settings
- iexplore.exe (PID: 3488)
Reads Internet Cache Settings
- iexplore.exe (PID: 3732)
Reads settings of System Certificates
- iexplore.exe (PID: 3488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
8
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2284 | "C:\Users\admin\AppData\Local\Temp\SYSTEM.EXE" | C:\Users\admin\AppData\Local\Temp\SYSTEM.EXE | — | Roblox AIO.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2456 | "C:\Users\admin\AppData\Local\Temp\SYSTEM.EXE" | C:\Users\admin\AppData\Local\Temp\SYSTEM.EXE | SYSTEM.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
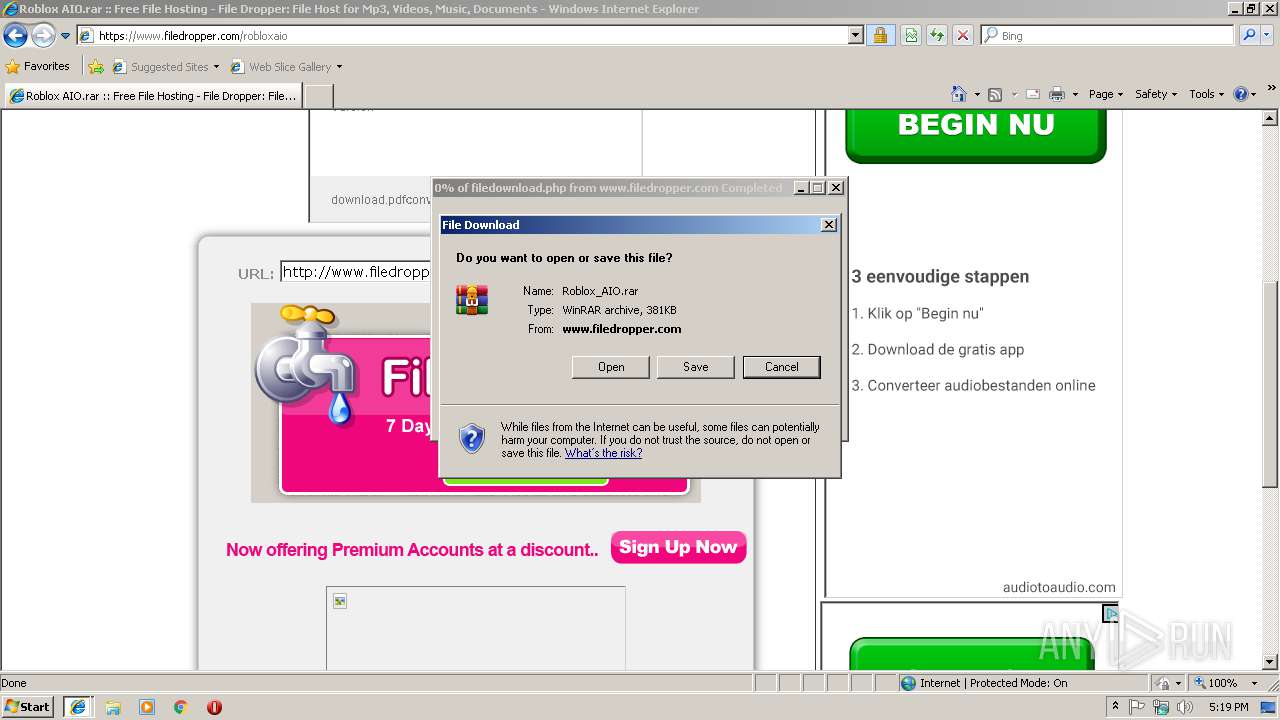
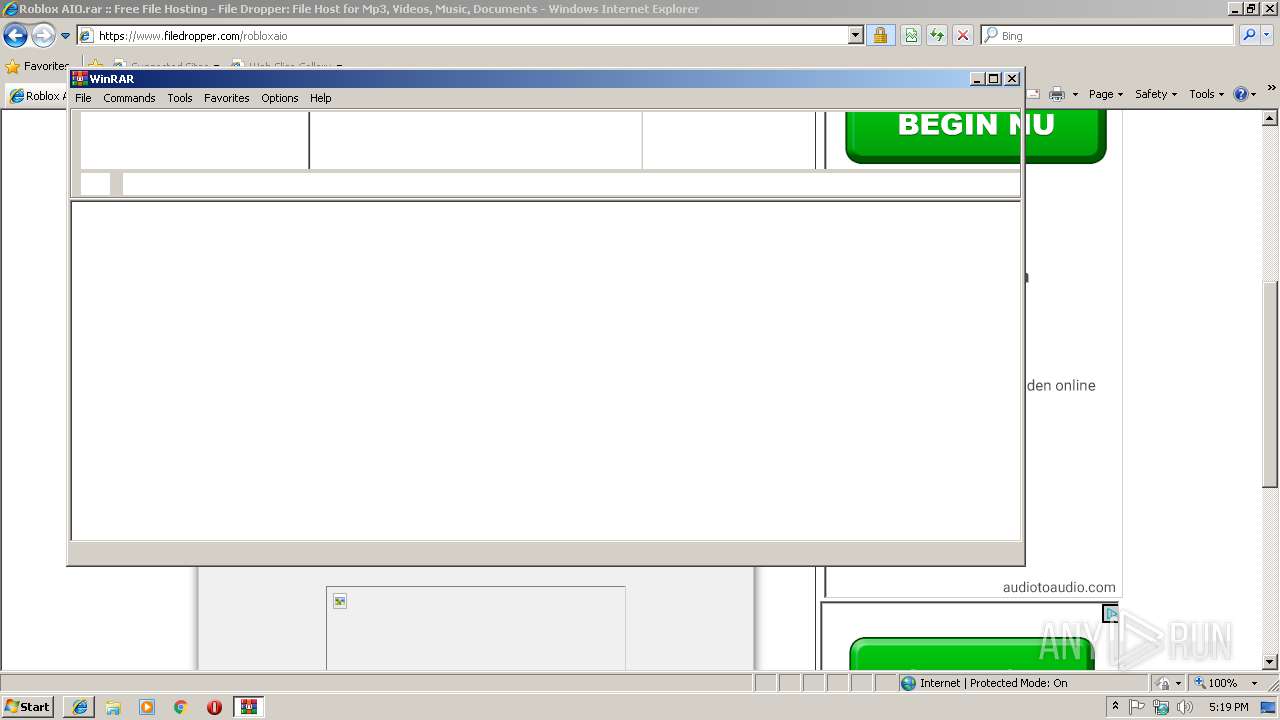
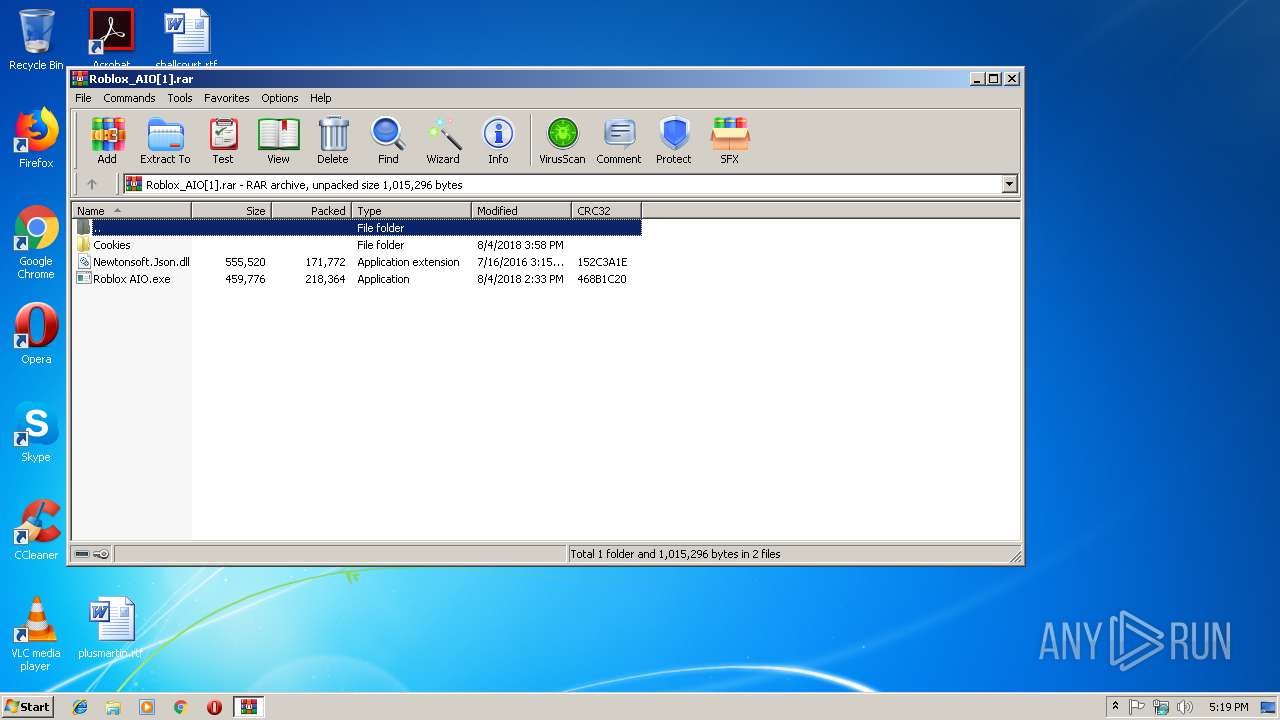
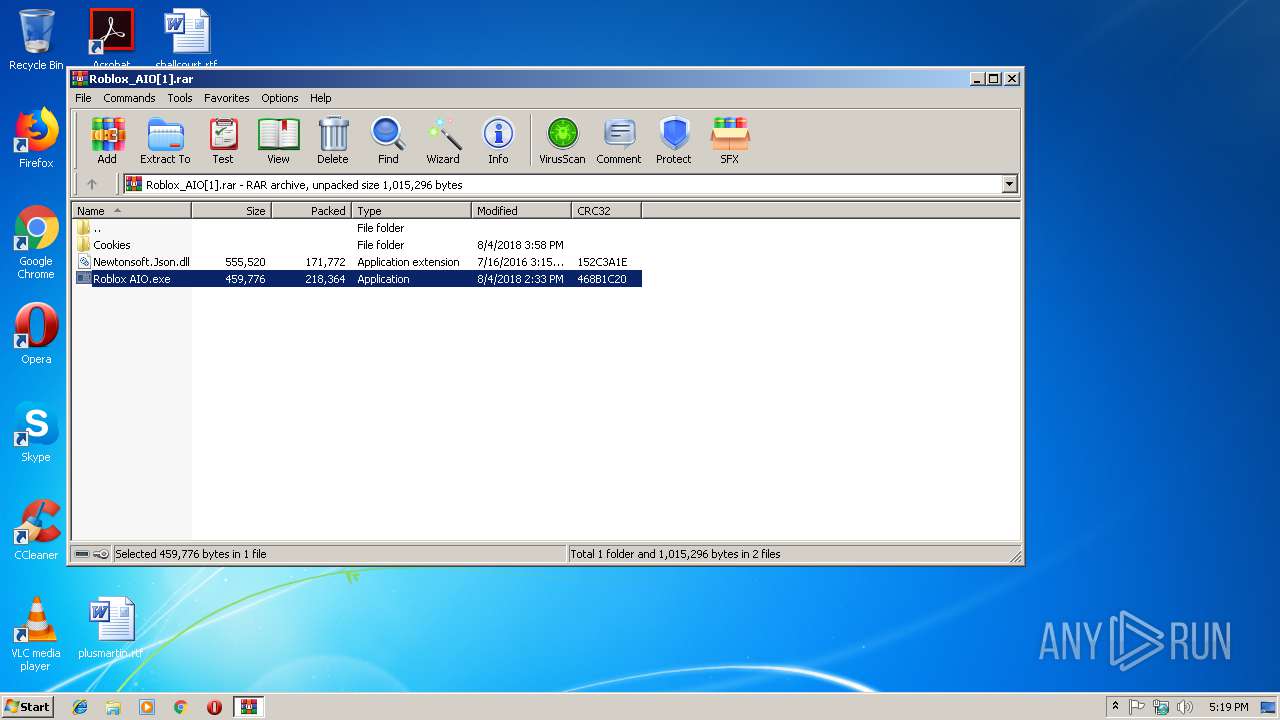
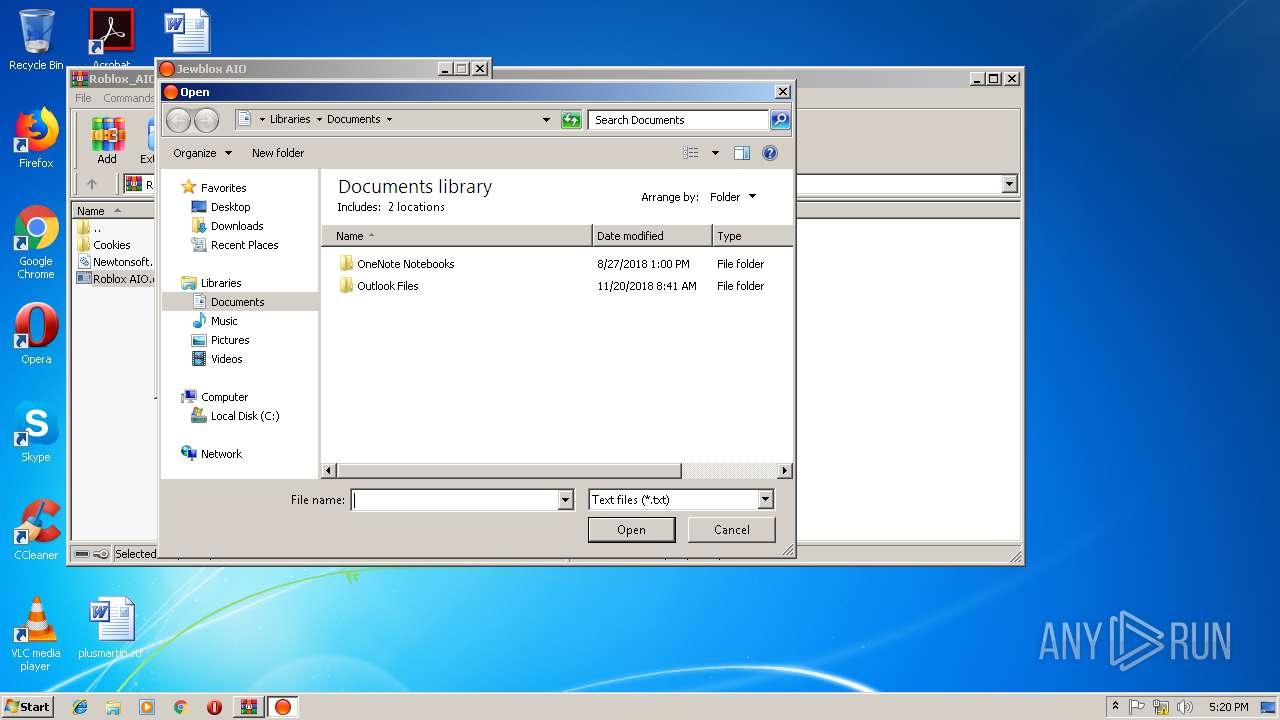
| 2668 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\Roblox_AIO[1].rar" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2684 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2668.7449\Roblox AIO.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2668.7449\Roblox AIO.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3084 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3488 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\AppData\Local\Temp\ROBLOX AIO.EXE" | C:\Users\admin\AppData\Local\Temp\ROBLOX AIO.EXE | Roblox AIO.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Roblox AIO Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3732 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3488 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 336
Read events
2 122
Write events
212
Delete events
2
Modification events
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {452A9763-41C6-11E9-BEEC-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3488) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307030005000800110013000400CF02 | |||
Executable files
5
Suspicious files
4
Text files
55
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3488 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3488 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3732 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\logo[1].png | image | |
MD5:— | SHA256:— | |||
| 3732 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\f[1].txt | text | |
MD5:— | SHA256:— | |||
| 3732 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\spacer[1].png | image | |
MD5:— | SHA256:— | |||
| 3732 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\f[2].txt | text | |
MD5:— | SHA256:— | |||
| 3732 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\ca-pub-8541837862733769[1].js | text | |
MD5:— | SHA256:— | |||
| 3732 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\steps_wide[1].png | image | |
MD5:— | SHA256:— | |||
| 3732 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\bg[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3732 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@filedropper[1].txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
61
DNS requests
29
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3732 | iexplore.exe | GET | — | 104.20.2.47:80 | http://c.statcounter.com/3541212/0/872cdcc5/1/ | US | — | — | whitelisted |
3732 | iexplore.exe | GET | 301 | 144.76.226.41:80 | http://www.filedropper.com/images/filedropper_banner.png | DE | html | 265 b | suspicious |
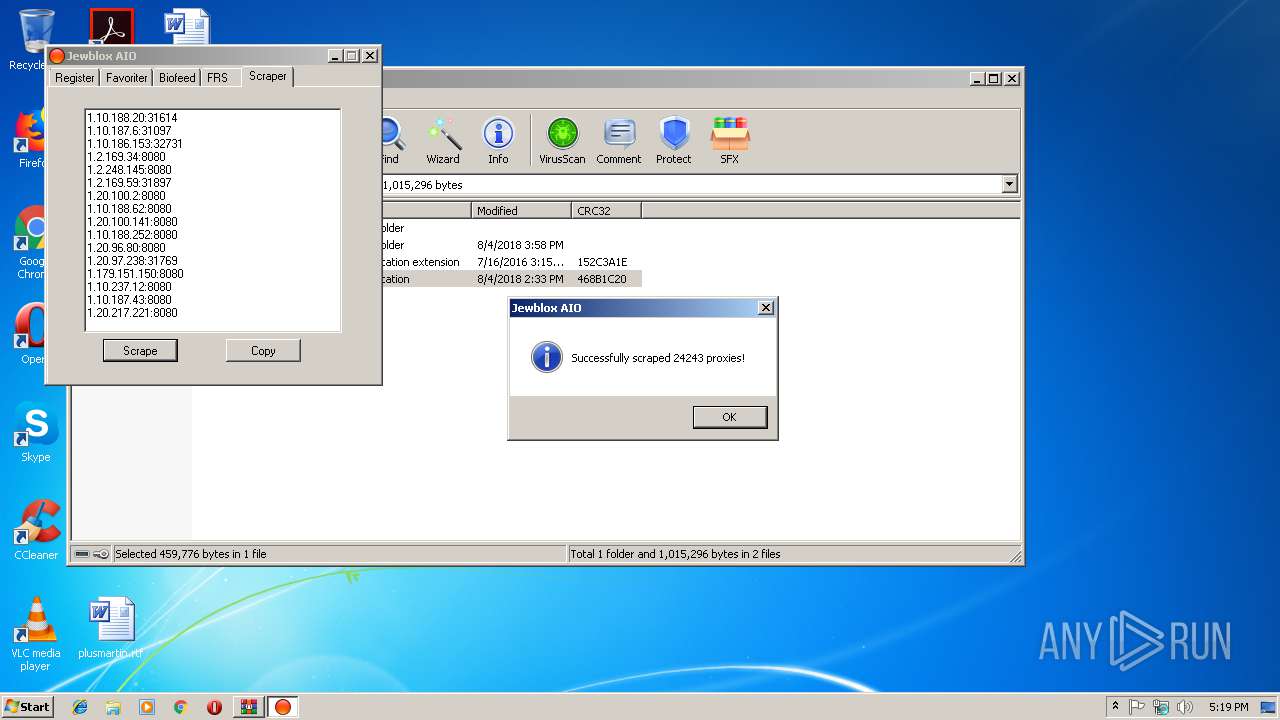
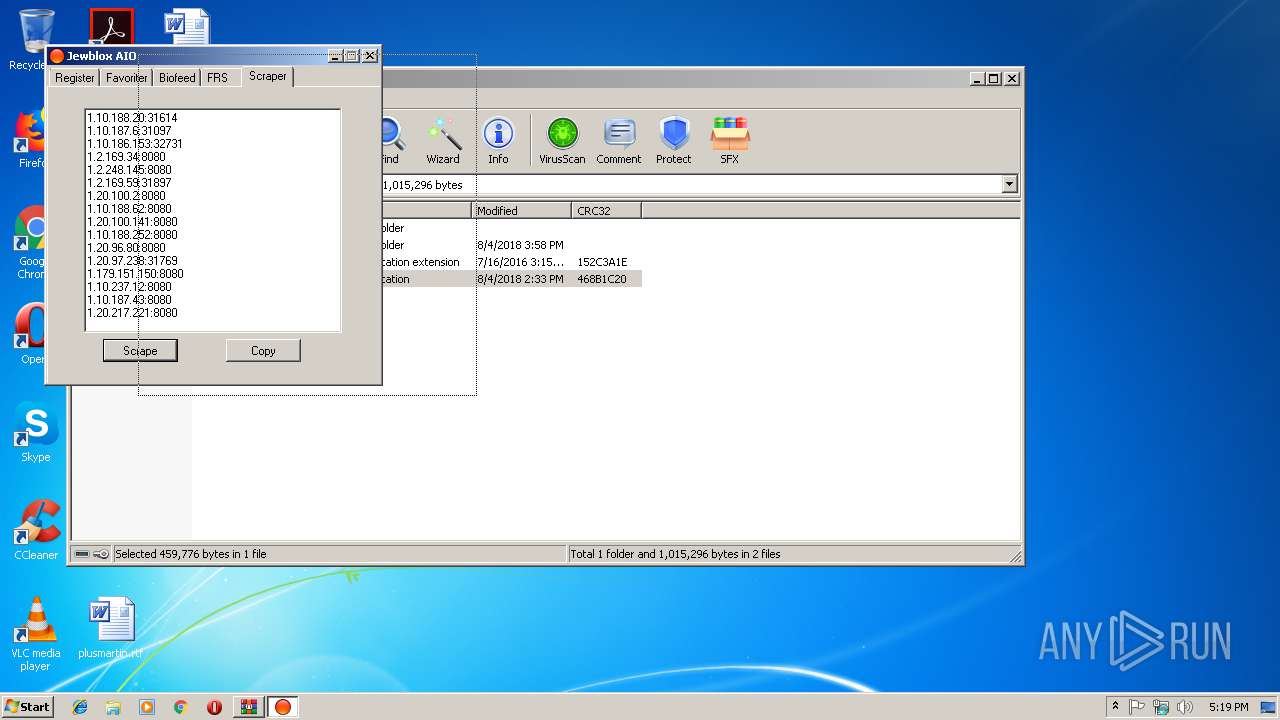
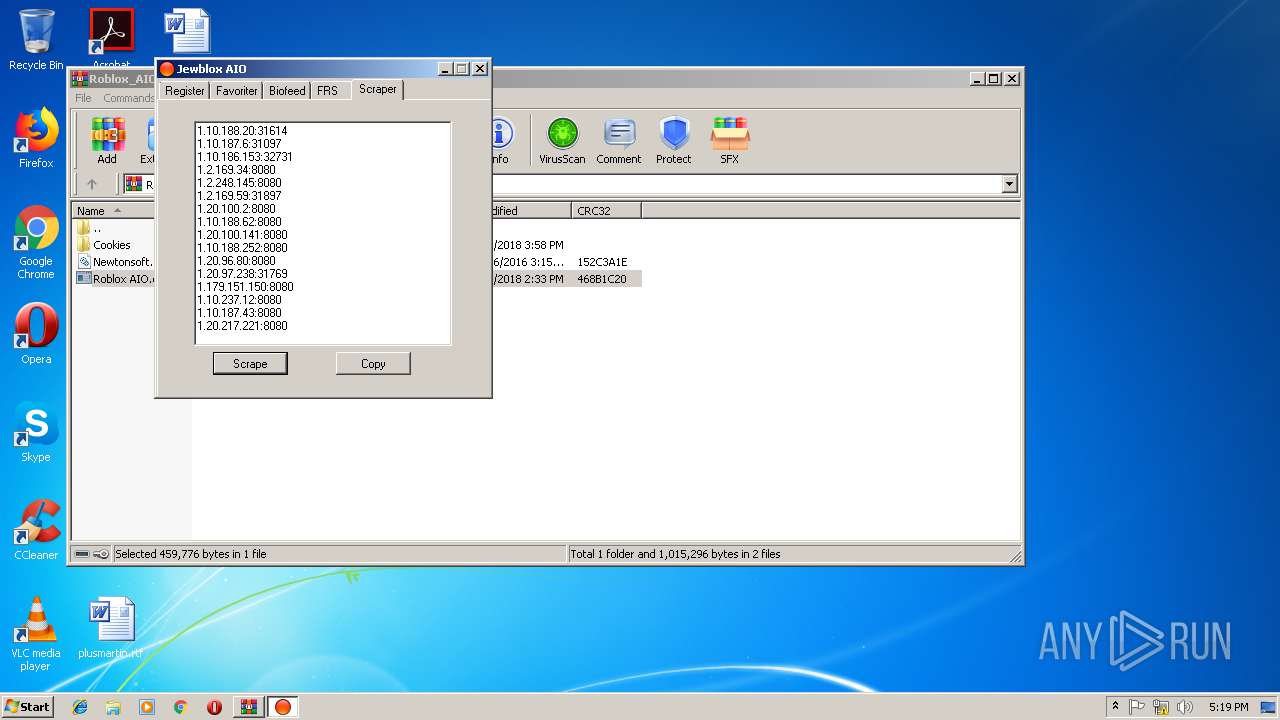
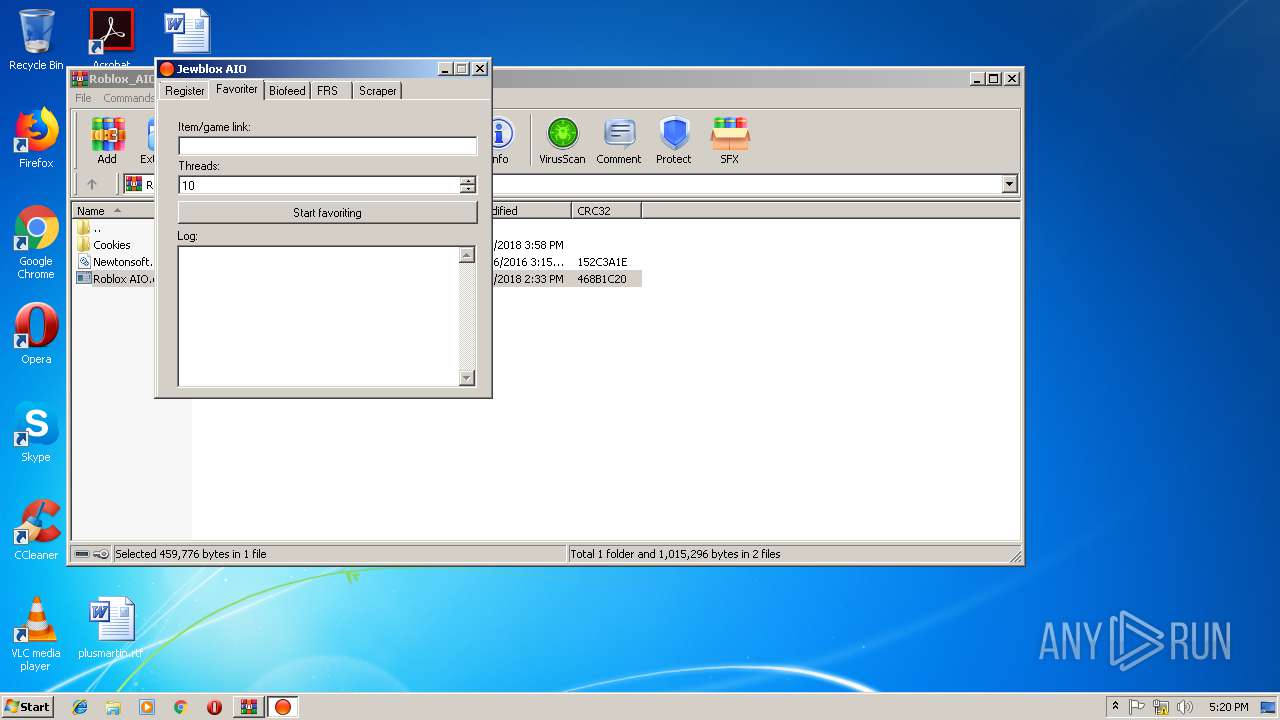
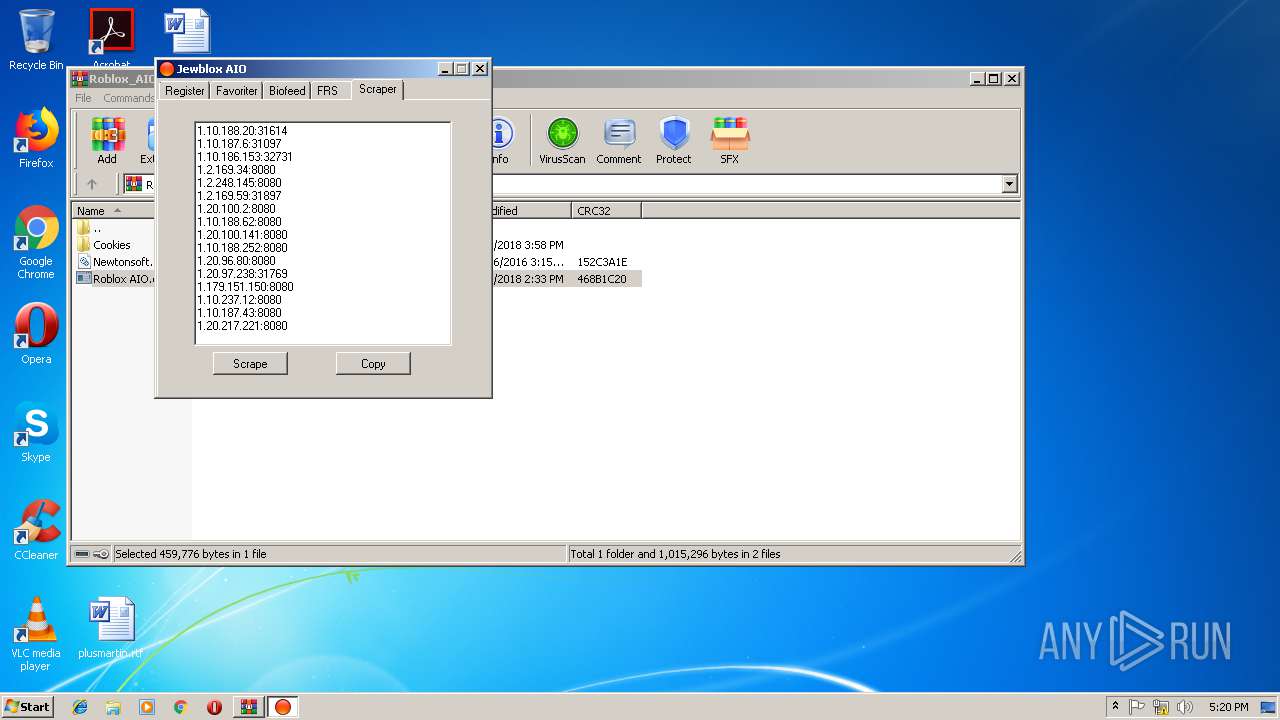
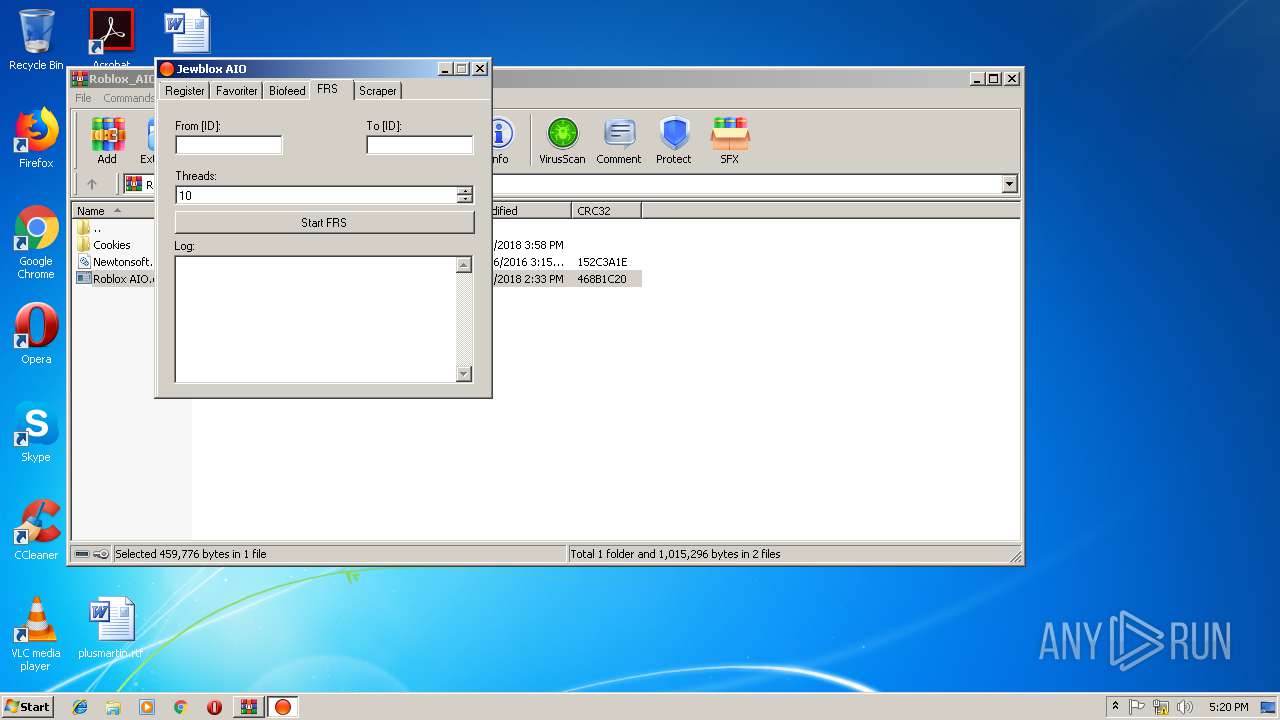
3652 | ROBLOX AIO.EXE | GET | 404 | 172.217.18.161:80 | http://proxieslounge.blogspot.com/ | US | html | 41.9 Kb | whitelisted |
3652 | ROBLOX AIO.EXE | GET | 301 | 172.217.18.161:80 | http://proxyserverlist-24.blogspot.com/feeds/posts/default | US | html | 234 b | whitelisted |
3652 | ROBLOX AIO.EXE | GET | 200 | 172.217.16.147:80 | http://www.proxyserverlist24.top/feeds/posts/default | US | xml | 1.30 Mb | whitelisted |
3652 | ROBLOX AIO.EXE | GET | 200 | 172.217.16.147:80 | http://www.sslproxies24.top/feeds/posts/default | US | xml | 44.5 Kb | whitelisted |
3652 | ROBLOX AIO.EXE | GET | 301 | 172.217.18.161:80 | http://sslproxies24.blogspot.com/feeds/posts/default | US | html | 229 b | whitelisted |
3488 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3732 | iexplore.exe | 52.41.88.59:443 | e.dlx.addthis.com | Amazon.com, Inc. | US | unknown |
3488 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3732 | iexplore.exe | 144.76.226.41:443 | www.filedropper.com | Hetzner Online GmbH | DE | unknown |
3732 | iexplore.exe | 216.58.205.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3732 | iexplore.exe | 216.58.206.2:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3732 | iexplore.exe | 172.217.21.194:443 | adservice.google.nl | Google Inc. | US | whitelisted |
3732 | iexplore.exe | 144.76.226.41:80 | www.filedropper.com | Hetzner Online GmbH | DE | unknown |
3732 | iexplore.exe | 172.217.22.66:443 | adservice.google.com | Google Inc. | US | whitelisted |
3732 | iexplore.exe | 172.217.16.130:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
3732 | iexplore.exe | 104.20.2.47:80 | c.statcounter.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.filedropper.com |
| suspicious |
pagead2.googlesyndication.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
adservice.google.nl |
| whitelisted |
adservice.google.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
c.statcounter.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
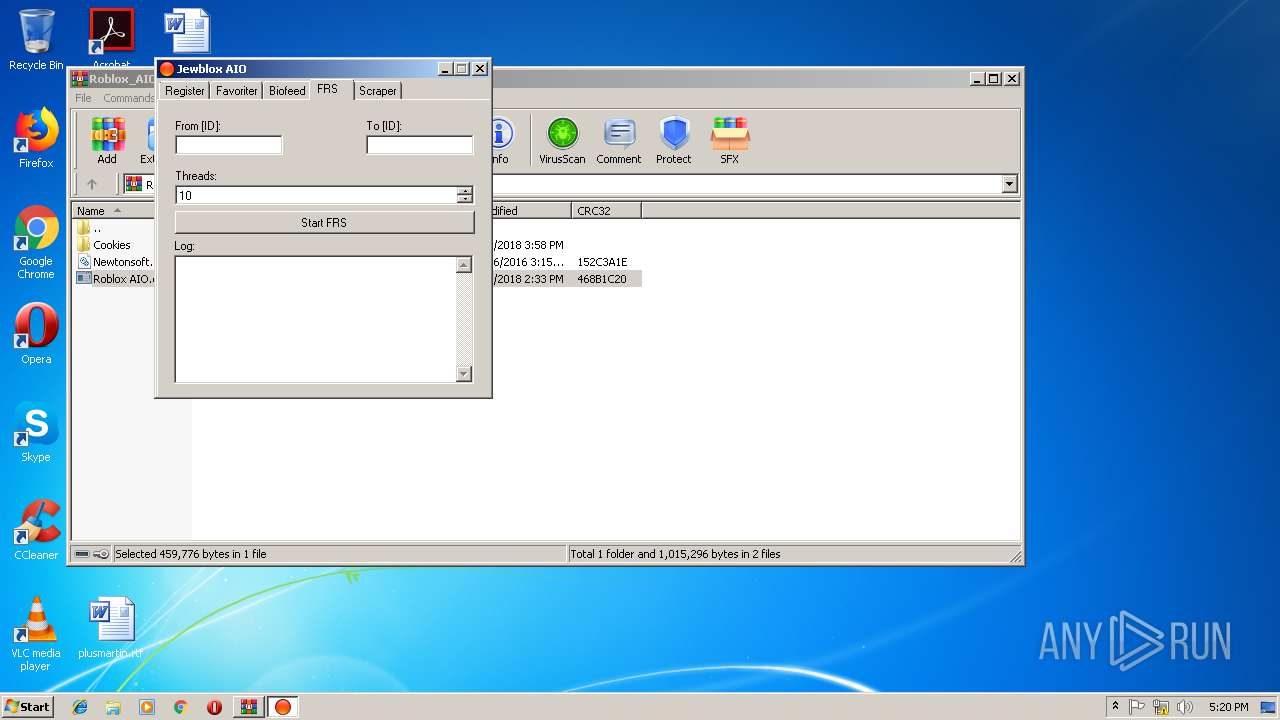
1064 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3652 | ROBLOX AIO.EXE | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
Process | Message |
|---|---|
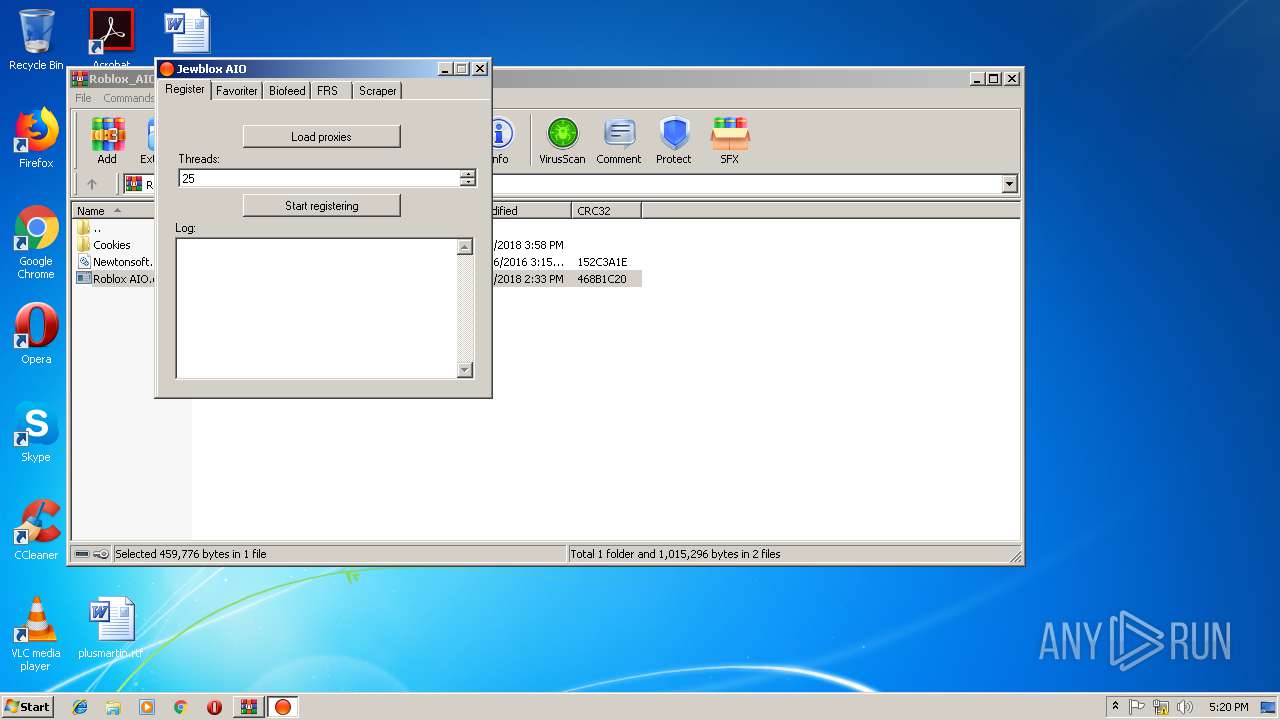
Roblox AIO.exe | C:\Users\admin\AppData\Local\Temp\ROBLOX AIO.EXE |
Roblox AIO.exe | C:\Users\admin\AppData\Local\Temp\SYSTEM.EXE |