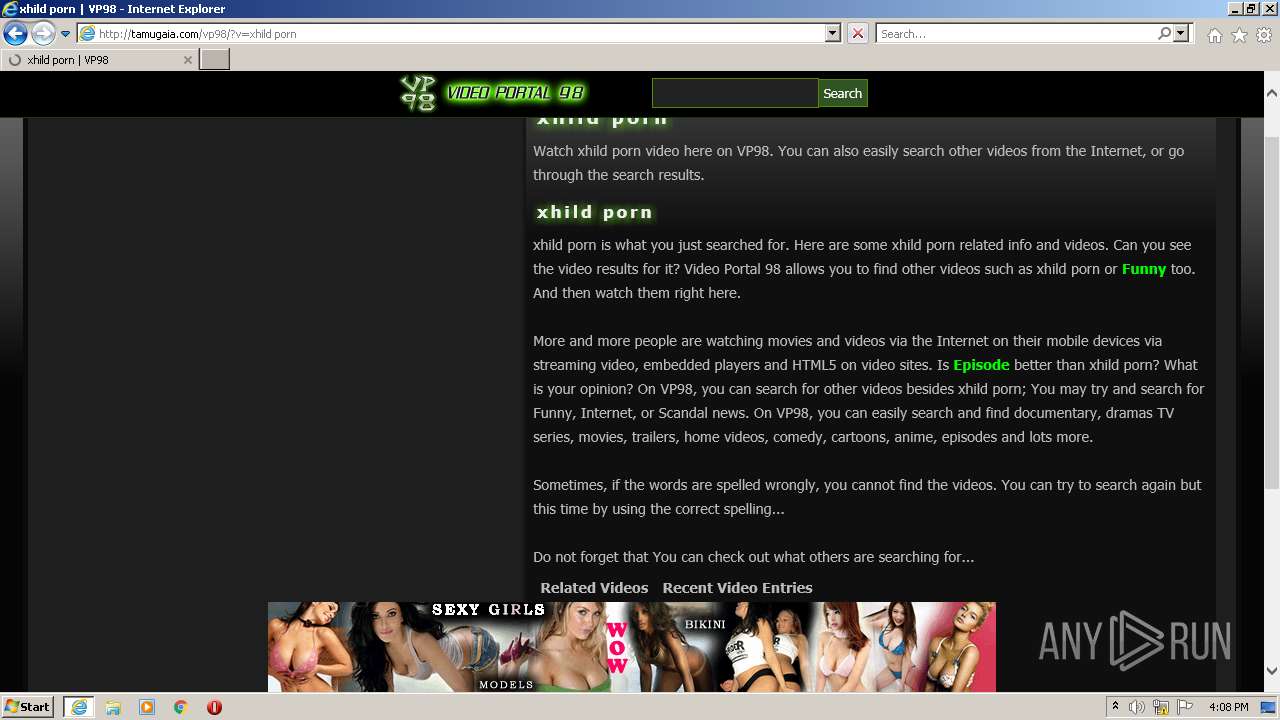
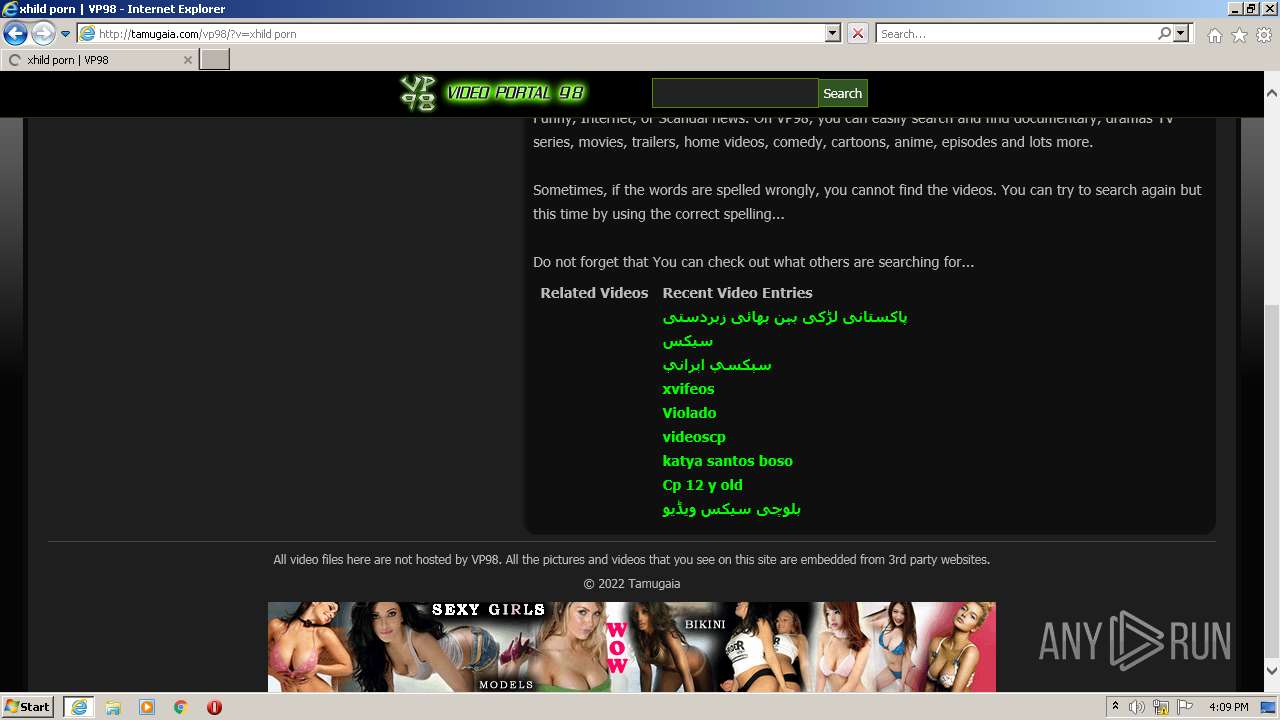
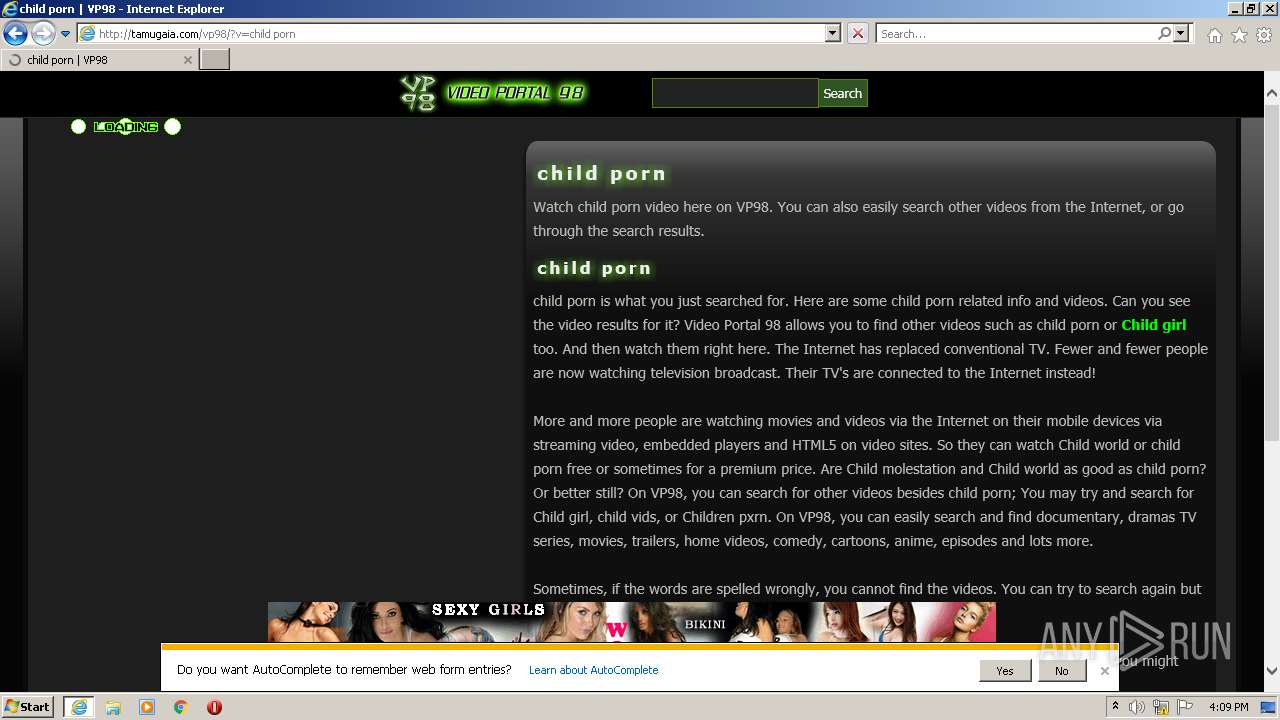
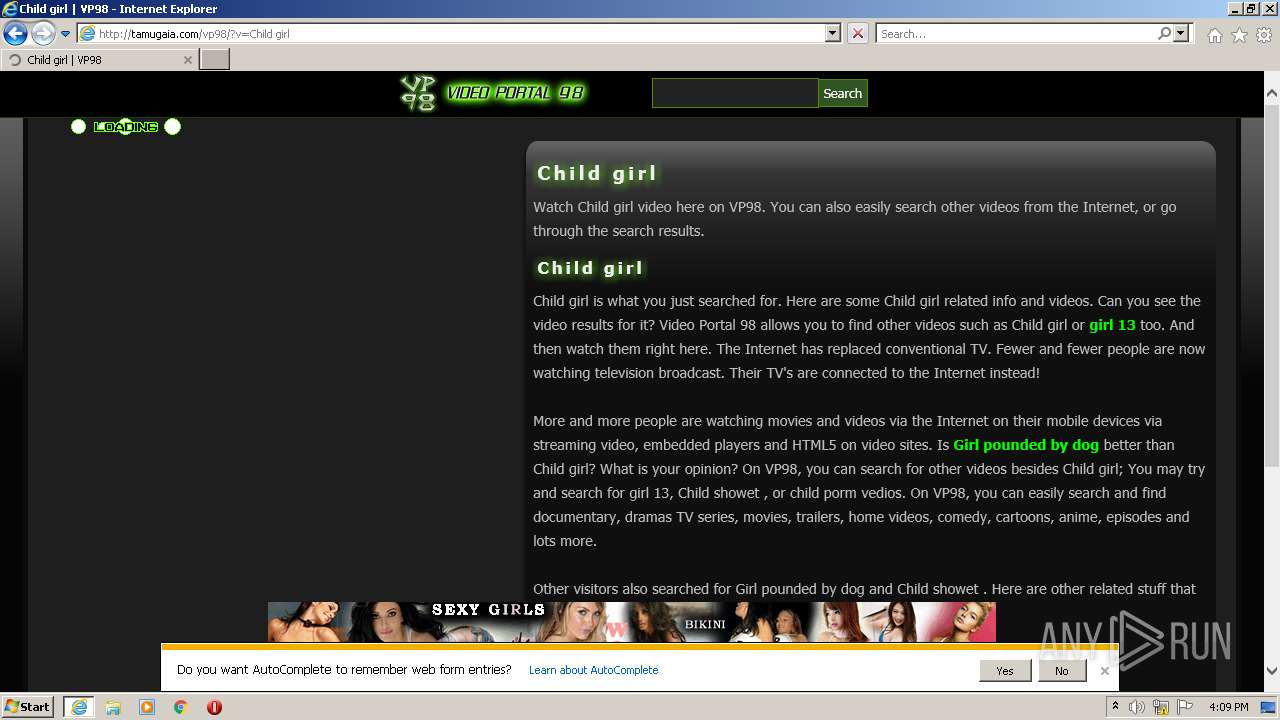
| URL: | http://tamugaia.com/vp98/?v=Child%20prn |
| Full analysis: | https://app.any.run/tasks/12e182d9-f47a-4100-bd42-94abfb020d72 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2022, 16:08:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7EBC020E3DD0C31D32669C72008B4C12 |
| SHA1: | 3F011C23D1A8CFE2F32A8028F5710623CAA5B407 |
| SHA256: | 4D028318FC55FEA35DEF0BC6A0D32A76D87C5505DA2694169ADD243084146DA6 |
| SSDEEP: | 3:N1KKEtCeLKBIYqAz:CKGRKBTqAz |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3632)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2544)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2544)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2544)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2544)
INFO
Checks supported languages
- iexplore.exe (PID: 1820)
- iexplore.exe (PID: 3632)
Reads the computer name
- iexplore.exe (PID: 1820)
- iexplore.exe (PID: 3632)
Changes internet zones settings
- iexplore.exe (PID: 1820)
Application launched itself
- iexplore.exe (PID: 1820)
Reads internet explorer settings
- iexplore.exe (PID: 3632)
Reads settings of System Certificates
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 1820)
Checks Windows Trust Settings
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 1820)
Reads CPU info
- iexplore.exe (PID: 3632)
Creates files in the user directory
- iexplore.exe (PID: 3632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1820 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://tamugaia.com/vp98/?v=Child%20prn" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2544 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3632 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1820 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
14 584
Read events
14 444
Write events
140
Delete events
0
Modification events
| (PID) Process: | (1820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30934588 | |||
| (PID) Process: | (1820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30934588 | |||
| (PID) Process: | (1820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1820) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
11
Text files
48
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\vp98[1].htm | html | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\stylos[1].css | text | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\vp98[1].svg | text | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ads[1].js | html | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\v6[1].js | text | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\vp98head[1].png | image | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\lod[1].gif | image | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\unsemantic-grid-responsive[1].css | text | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\s1x2[1].gif | image | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\counter[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
69
DNS requests
20
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3632 | iexplore.exe | GET | 403 | 192.243.59.13:80 | http://pl5052.puhtml.com/72/03/6e/72036e1b166bd3fe72c0723194d06125.js | US | — | — | malicious |
3632 | iexplore.exe | GET | 200 | 91.121.251.65:80 | http://tamugaia.com/vp98/?v=Child%20prn | GB | html | 3.33 Kb | unknown |
3632 | iexplore.exe | GET | 200 | 91.121.251.65:80 | http://tamugaia.com/vp98/stylos.css | GB | text | 2.02 Kb | unknown |
3632 | iexplore.exe | GET | 200 | 91.121.251.65:80 | http://tamugaia.com/vp98/unsemantic-grid-responsive.css | GB | text | 2.68 Kb | unknown |
3632 | iexplore.exe | GET | 200 | 91.121.251.65:80 | http://tamugaia.com/vp98/p/vp98head.png | GB | image | 8.22 Kb | unknown |
3632 | iexplore.exe | GET | 200 | 91.121.251.65:80 | http://tamugaia.com/vp98/v6.js | GB | text | 33.2 Kb | unknown |
3632 | iexplore.exe | GET | 200 | 91.121.251.65:80 | http://tamugaia.com/vp98/ads.js | GB | html | 156 b | unknown |
3632 | iexplore.exe | GET | 200 | 91.121.251.65:80 | http://tamugaia.com/vp98/p/lod.gif | GB | image | 663 b | unknown |
3632 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
3632 | iexplore.exe | GET | 200 | 91.121.251.65:80 | http://tamugaia.com/vp98/p/s1x2.gif | GB | image | 51.8 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3632 | iexplore.exe | 91.121.251.65:80 | tamugaia.com | OVH SAS | GB | unknown |
3632 | iexplore.exe | 192.243.59.13:80 | pl5052.puhtml.com | DataWeb Global Group B.V. | US | malicious |
3632 | iexplore.exe | 151.139.242.3:80 | cdn.ad4game.com | netDNA | US | unknown |
— | — | 104.20.228.67:80 | www.statcounter.com | Cloudflare Inc | US | unknown |
1820 | iexplore.exe | 2.16.106.171:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1820 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3632 | iexplore.exe | 184.31.84.150:443 | htlb.casalemedia.com | Akamai International B.V. | NL | whitelisted |
3632 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1820 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3632 | iexplore.exe | 104.18.30.182:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tamugaia.com |
| unknown |
pl5052.puhtml.com |
| malicious |
cdn.ad4game.com |
| whitelisted |
www.statcounter.com |
| whitelisted |
c.statcounter.com |
| whitelisted |
api.dailymotion.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ads.ad4game.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3632 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3632 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3632 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3632 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3632 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
— | — | Potentially Bad Traffic | ET INFO TLS Handshake Failure |