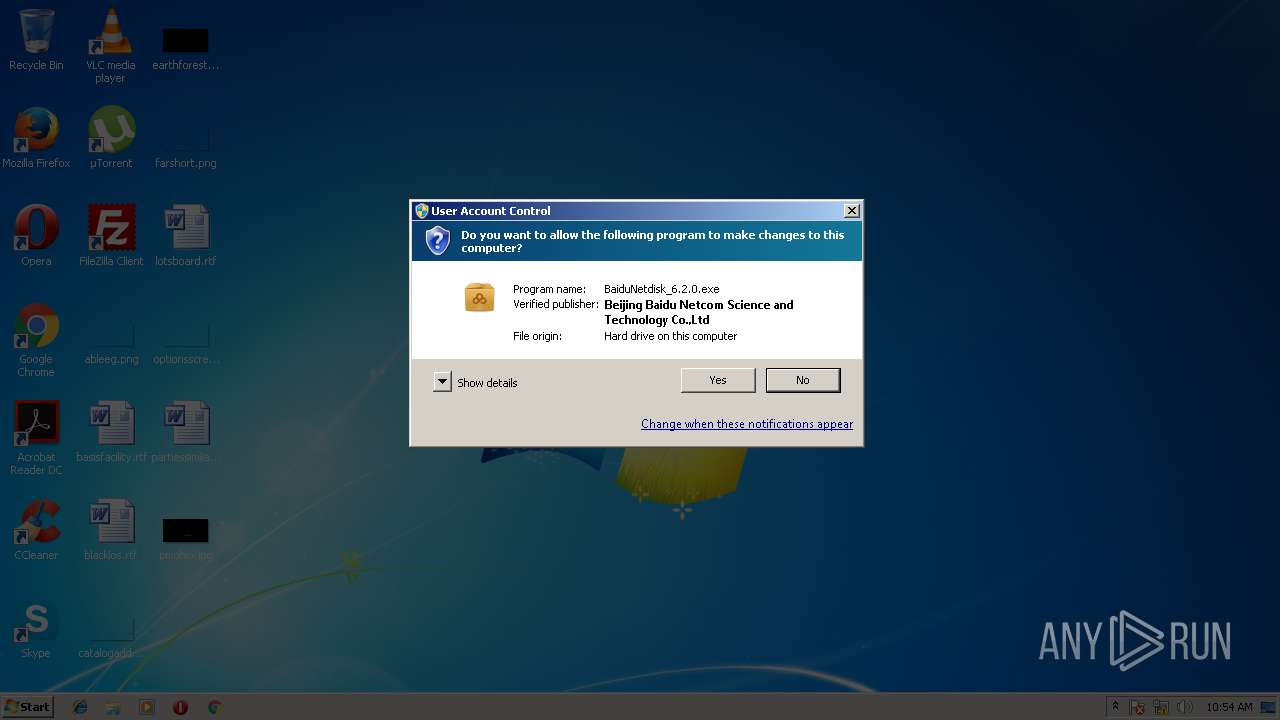
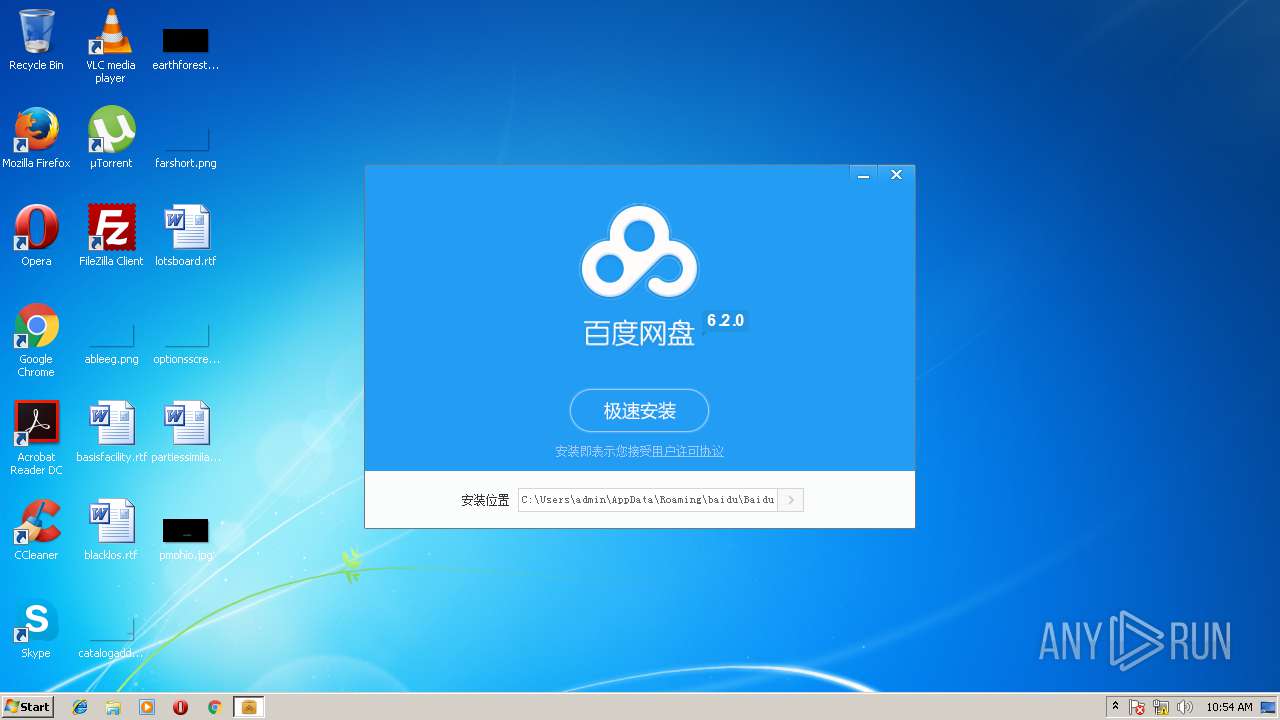
| download: | BaiduNetdisk_6.2.0.exe |
| Full analysis: | https://app.any.run/tasks/0f0b9017-defa-4748-b42a-3ead3f5b418c |
| Verdict: | Malicious activity |
| Analysis date: | May 31, 2018, 09:51:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DEA2742F83E1C12D45C87ADFF5BFF330 |
| SHA1: | B445D9532FD10331A3FAB6B67A1D2DEEAA8EB7D7 |
| SHA256: | 4D0045FA3319BA58FED293488C523261585CCE89843D95E621EE7BCA99DF16BC |
| SSDEEP: | 393216:lVJYOuuIBobPWgDmcgvby9sd+FaTzXu5GVMC9/0ULGzZr1QWW/a4jDLuFdELWh+w:R2ozyFzlOGVMw0UqzZr1+WTEKkw |
MALICIOUS
Loads dropped or rewritten executable
- BaiduNetdisk_6.2.0.exe (PID: 3912)
SUSPICIOUS
Executable content was dropped or overwritten
- BaiduNetdisk_6.2.0.exe (PID: 3912)
Creates files in the user directory
- BaiduNetdisk_6.2.0.exe (PID: 3912)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x39e3 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:59 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006F10 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49788 |
.rdata | 0x00008000 | 0x00002A92 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39389 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47278 |
.ndata | 0x00073000 | 0x000E1000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00154000 | 0x0005AF90 | 0x0005B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.80149 |
.reloc | 0x001AF000 | 0x00000F8A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.41359 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21698 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.80323 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 5.94822 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 6.14 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 6.20708 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 6.66261 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.55883 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68733 | 494 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.86626 | 228 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.9304 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2148 | "C:\Users\admin\AppData\Local\Temp\BaiduNetdisk_6.2.0.exe" | C:\Users\admin\AppData\Local\Temp\BaiduNetdisk_6.2.0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3912 | "C:\Users\admin\AppData\Local\Temp\BaiduNetdisk_6.2.0.exe" | C:\Users\admin\AppData\Local\Temp\BaiduNetdisk_6.2.0.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
333
Read events
333
Write events
0
Delete events
0
Modification events
Executable files
5
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3912 | BaiduNetdisk_6.2.0.exe | C:\Users\admin\AppData\Roaming\baidu\BaiduNetdisk\YunLogic.dll | — | |
MD5:— | SHA256:— | |||
| 3912 | BaiduNetdisk_6.2.0.exe | C:\Users\admin\AppData\Roaming\baidu\BaiduNetdisk\module\CyberPlayer\CyberPlayer.dll | — | |
MD5:— | SHA256:— | |||
| 3912 | BaiduNetdisk_6.2.0.exe | C:\Users\admin\AppData\Local\Temp\nshF1D3.tmp\SetupCfg.ini | text | |
MD5:AC0835CA6CC22EB3547391CD28BABD84 | SHA256:FE2E95678FBD1A8B6609EB95F3E9941F67018EBAB32149CF0B94B0A200354A54 | |||
| 3912 | BaiduNetdisk_6.2.0.exe | C:\Users\admin\AppData\Local\Temp\nshF1D3.tmp\VersionInfo.xml | xml | |
MD5:— | SHA256:— | |||
| 3912 | BaiduNetdisk_6.2.0.exe | C:\Users\admin\AppData\Local\Temp\nshF1D3.tmp\NsisInstallUI.dll | executable | |
MD5:— | SHA256:— | |||
| 3912 | BaiduNetdisk_6.2.0.exe | C:\Users\admin\AppData\Roaming\baidu\BaiduNetdisk\logonbdext.dll | executable | |
MD5:— | SHA256:— | |||
| 3912 | BaiduNetdisk_6.2.0.exe | C:\Users\admin\AppData\Roaming\baidu\BaiduNetdisk\Bull140U.dll | executable | |
MD5:— | SHA256:— | |||
| 3912 | BaiduNetdisk_6.2.0.exe | C:\Users\admin\AppData\Local\Temp\nshF1D3.tmp\nsProcessW.dll | executable | |
MD5:F0438A894F3A7E01A4AAE8D1B5DD0289 | SHA256:30C6C3DD3CC7FCEA6E6081CE821ADC7B2888542DAE30BF00E881C0A105EB4D11 | |||
| 3912 | BaiduNetdisk_6.2.0.exe | C:\Users\admin\AppData\Local\Temp\nshF1D3.tmp\System.dll | executable | |
MD5:BF712F32249029466FA86756F5546950 | SHA256:7851CB12FA4131F1FEE5DE390D650EF65CAC561279F1CFE70AD16CC9780210AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report