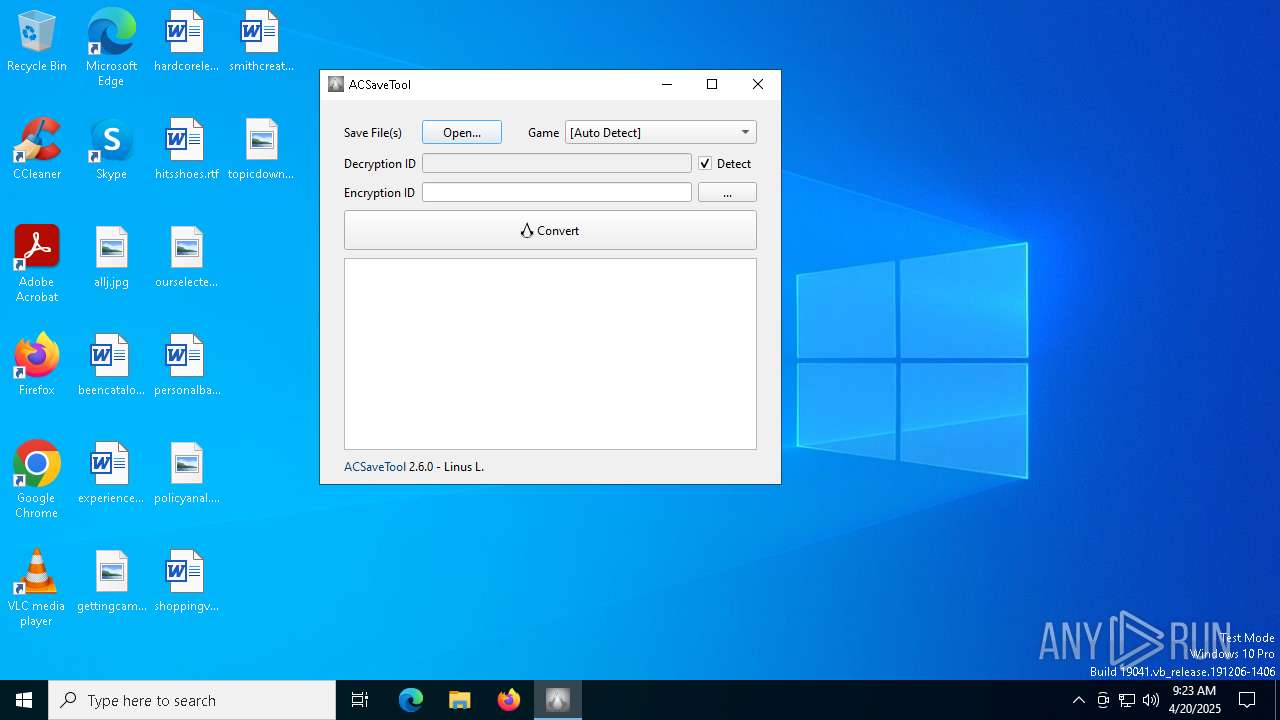
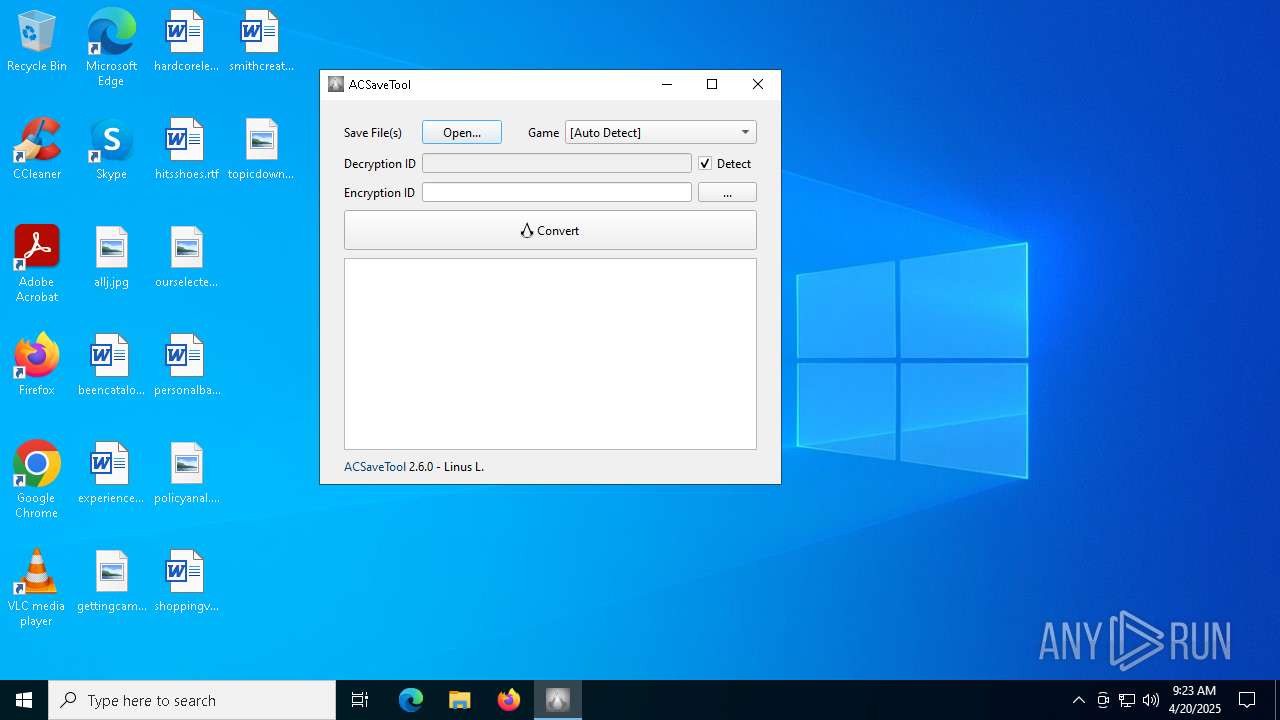
| File name: | ACSaveTool_x64.exe |
| Full analysis: | https://app.any.run/tasks/07e80a75-d6e8-4fc5-a1e2-5dcf11154d72 |
| Verdict: | Malicious activity |
| Analysis date: | April 20, 2025, 09:23:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 0BF7D2A2CA40538B8B02B393EAC995AF |
| SHA1: | BCB7C00E2F9EA3FF85D7092A00FC17536C9F8369 |
| SHA256: | 4CC25D80D1F4AEDEEA67EBE9DF48A346B25C81EB582421F4B8EAC29B3F2FEE68 |
| SSDEEP: | 98304:p1E4A+hpWar6pha+xXZzIODV+WP3C/T5HsWd8QNsynwuFaBIQLOUNHxpswPchnlm:339F3hfJbR+QJJb78e8q+7 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- ACSaveTool_x64.exe (PID: 4212)
Executable content was dropped or overwritten
- ACSaveTool_x64.exe (PID: 4212)
Reads security settings of Internet Explorer
- ACSaveTool_x64.exe (PID: 4212)
- ACSaveTool.exe (PID: 4812)
Reads the date of Windows installation
- ACSaveTool_x64.exe (PID: 4212)
There is functionality for taking screenshot (YARA)
- ACSaveTool_x64.exe (PID: 4212)
The process drops C-runtime libraries
- ACSaveTool_x64.exe (PID: 4212)
INFO
Reads the computer name
- ACSaveTool_x64.exe (PID: 4212)
- ACSaveTool.exe (PID: 4812)
The sample compiled with english language support
- ACSaveTool_x64.exe (PID: 4212)
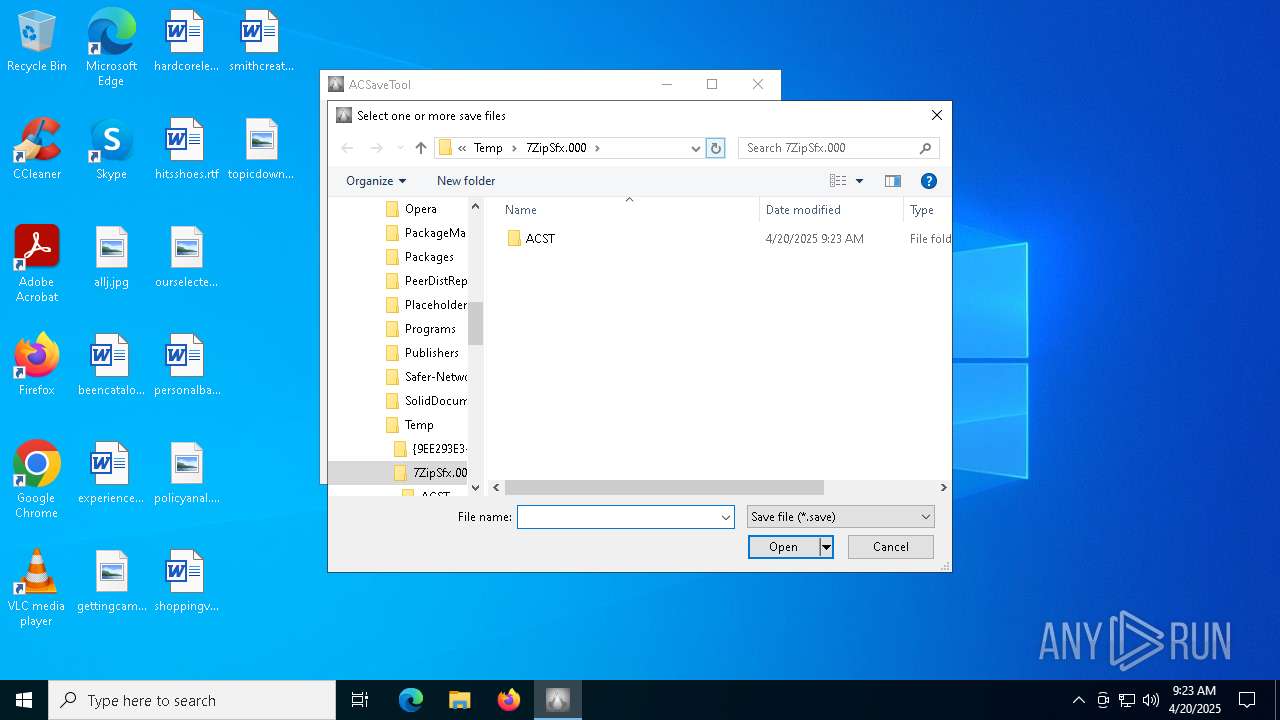
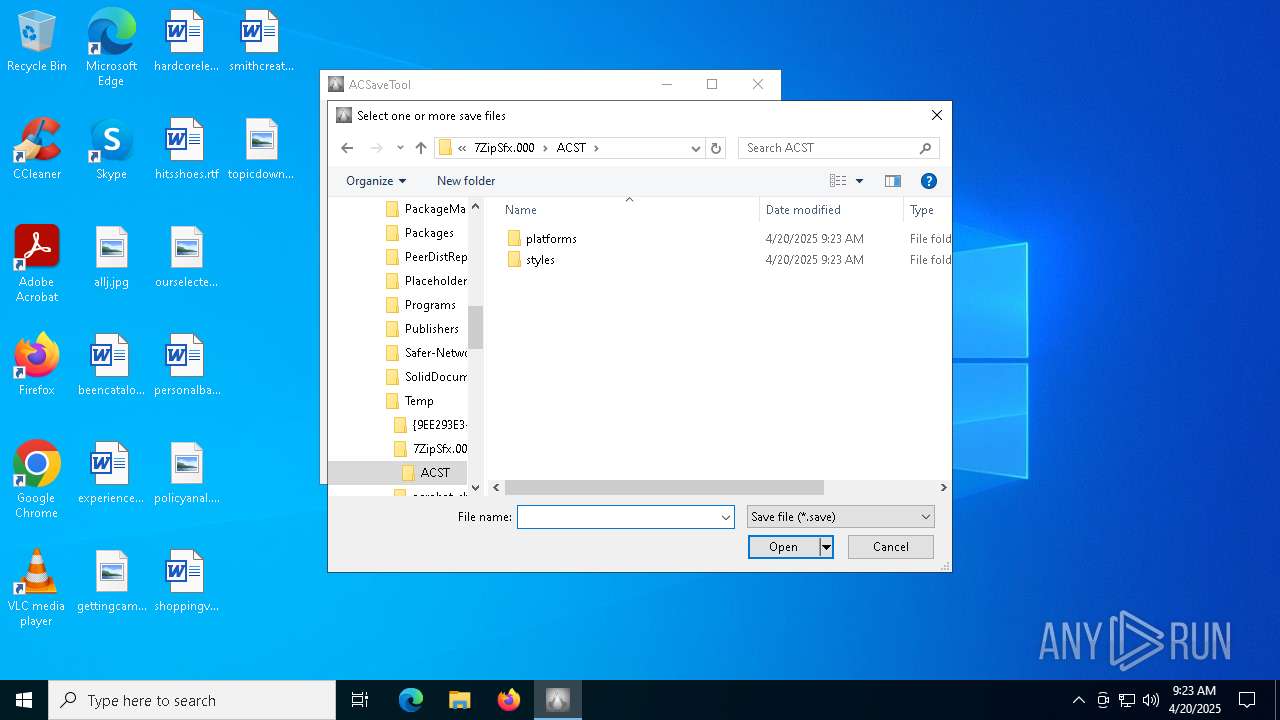
Create files in a temporary directory
- ACSaveTool_x64.exe (PID: 4212)
Process checks computer location settings
- ACSaveTool_x64.exe (PID: 4212)
Checks supported languages
- ACSaveTool_x64.exe (PID: 4212)
- ACSaveTool.exe (PID: 4812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2017:06:15 00:09:18+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 10 |
| CodeSize: | 131072 |
| InitializedDataSize: | 314880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x206bc |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.6.0.0 |
| ProductVersionNumber: | 2.6.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | ACSaveTool |
| FileVersion: | 2.6.0.0 |
| LegalCopyright: | Linus L. |
| OriginalFileName: | ACSaveTool.exe |
| ProductName: | ACST |
| ProductVersion: | 2.6.0 |
Total processes
130
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4024 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
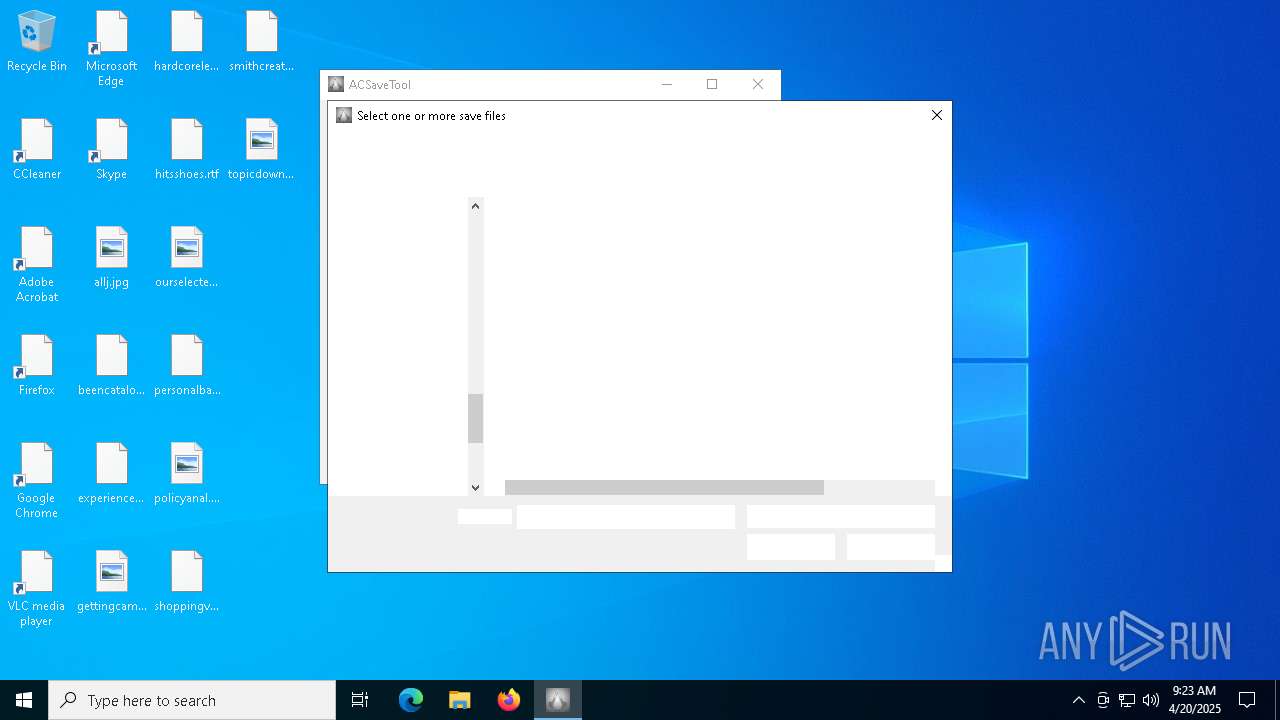
| 4212 | "C:\Users\admin\AppData\Local\Temp\ACSaveTool_x64.exe" | C:\Users\admin\AppData\Local\Temp\ACSaveTool_x64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4812 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ACST\ACSaveTool.exe" | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ACST\ACSaveTool.exe | — | ACSaveTool_x64.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
4 878
Read events
4 796
Write events
78
Delete events
4
Modification events
| (PID) Process: | (4812) ACSaveTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4812) ACSaveTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0E000000040000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (4812) ACSaveTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\14\0\0\0 |
| Operation: | write | Name: | 0 |
Value: 6200310000000000945AE54A1000375A69705366782E30303000480009000400EFBE945AE54A945AE54A2E000000B20F000000000C000000000000000000000000000000C5E6310037005A00690070005300660078002E0030003000300000001A000000 | |||
| (PID) Process: | (4812) ACSaveTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\14\0\0\0\0 |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (4812) ACSaveTool.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 114 | |||
| (PID) Process: | (4812) ACSaveTool.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 13BD046800000000 | |||
| (PID) Process: | (4812) ACSaveTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\14 |
| Operation: | write | Name: | MRUListEx |
Value: 00000000020000000300000001000000FFFFFFFF | |||
| (PID) Process: | (4812) ACSaveTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\14\0\0\0 |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (4812) ACSaveTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4812) ACSaveTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\14\0\0\0\0 |
| Operation: | write | Name: | NodeSlot |
Value: 254 | |||
Executable files
12
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4212 | ACSaveTool_x64.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ACST\ACSaveTool.exe | executable | |
MD5:454FFC3B929EE46EC39157D37C6A0DB5 | SHA256:5DD922B2E12FEB23D6DE4E2A90767E894AC87C7EC56B864747268CB7266A65D4 | |||
| 4212 | ACSaveTool_x64.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ACST\msvcp140_2.dll | executable | |
MD5:6FD1ABFC3BB7051F76502BED89AAD34F | SHA256:54D60E5B7A715192166A03DE9B0FF69E9ECF196713E728208F81D7BDF43C2EE8 | |||
| 4212 | ACSaveTool_x64.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ACST\msvcp140.dll | executable | |
MD5:7ACBC57D268A691247B4A94FECFA42B4 | SHA256:00E9BCDAA386942DFA7631079C450E702D6CE96E1D0A6ADED91D2F9436855320 | |||
| 4212 | ACSaveTool_x64.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ACST\acst_r2.dll | executable | |
MD5:ED265DD6E4DF02B22C453243DBE5C9CE | SHA256:8A92D3BA78C65BB33463F82D7785873DE7FA4D155229412C4F51D4B470C7994F | |||
| 4212 | ACSaveTool_x64.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ACST\vcruntime140.dll | executable | |
MD5:32DA96115C9D783A0769312C0482A62D | SHA256:8B10C53241726B0ACC9F513157E67FCB01C166FEC69E5E38CA6AADA8F9A3619F | |||
| 4212 | ACSaveTool_x64.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ACST\styles\qmodernwindowsstyle.dll | executable | |
MD5:C530EC3F535E240809312C791B414499 | SHA256:0B4925B59BFC864FB25688AC73A44C790B2162FED670602B922A74AB1FA07B51 | |||
| 4212 | ACSaveTool_x64.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ACST\vcruntime140_1.dll | executable | |
MD5:C0C0B4C611561F94798B62EB43097722 | SHA256:497A280550443E3E9F89E428E51CB795139CA8944D5DEDD54A7083C00E7164E5 | |||
| 4212 | ACSaveTool_x64.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ACST\Qt6Widgets.dll | executable | |
MD5:6532269DC53D121B4F5129FD96789D74 | SHA256:0D07A57F8FB298BC57FB66E49C6580094F8FE979D9F5DEAFCFC87FE1ED2E9F0F | |||
| 4212 | ACSaveTool_x64.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ACST\Qt6Core.dll | executable | |
MD5:8B1CE7C4AE80F5A2EF4D968E5A78B8D6 | SHA256:130C6EF3C126E97AAEC1A5CB1C638D7404473A3DDA837D6E161C69DB7A5BC339 | |||
| 4212 | ACSaveTool_x64.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\ACST\platforms\qwindows.dll | executable | |
MD5:CBB594A2C2708F51F83134D527A01CD5 | SHA256:87B2A5889A45B4DA2387B223B855E43D56CA30C90B18449553F8D756E7F2C681 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
18
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
864 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
864 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
864 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |