| File name: | 4ca8ac99b2416d8fae67a8b18a58c8d267b7e2b72af1ee0369f2470a030af8c7 |
| Full analysis: | https://app.any.run/tasks/d4fbfab7-afcf-44c6-84d5-53c96517ee2d |
| Verdict: | Malicious activity |
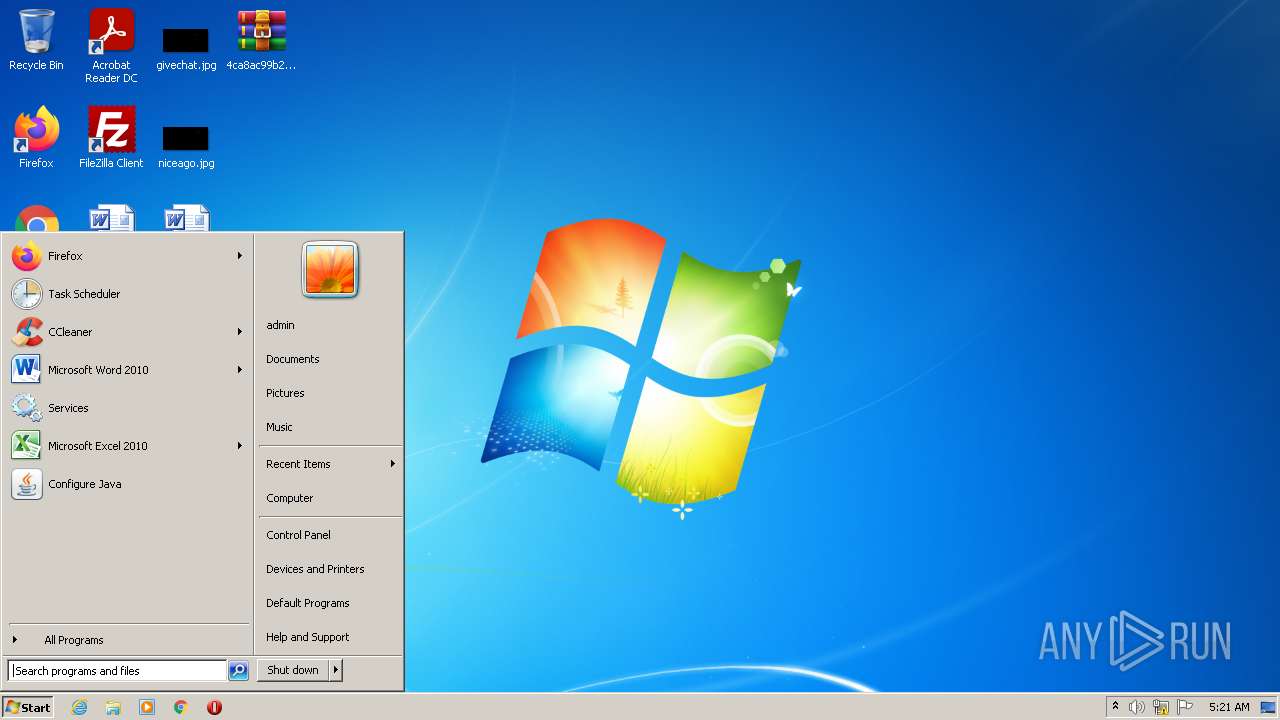
| Analysis date: | January 07, 2022, 05:20:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
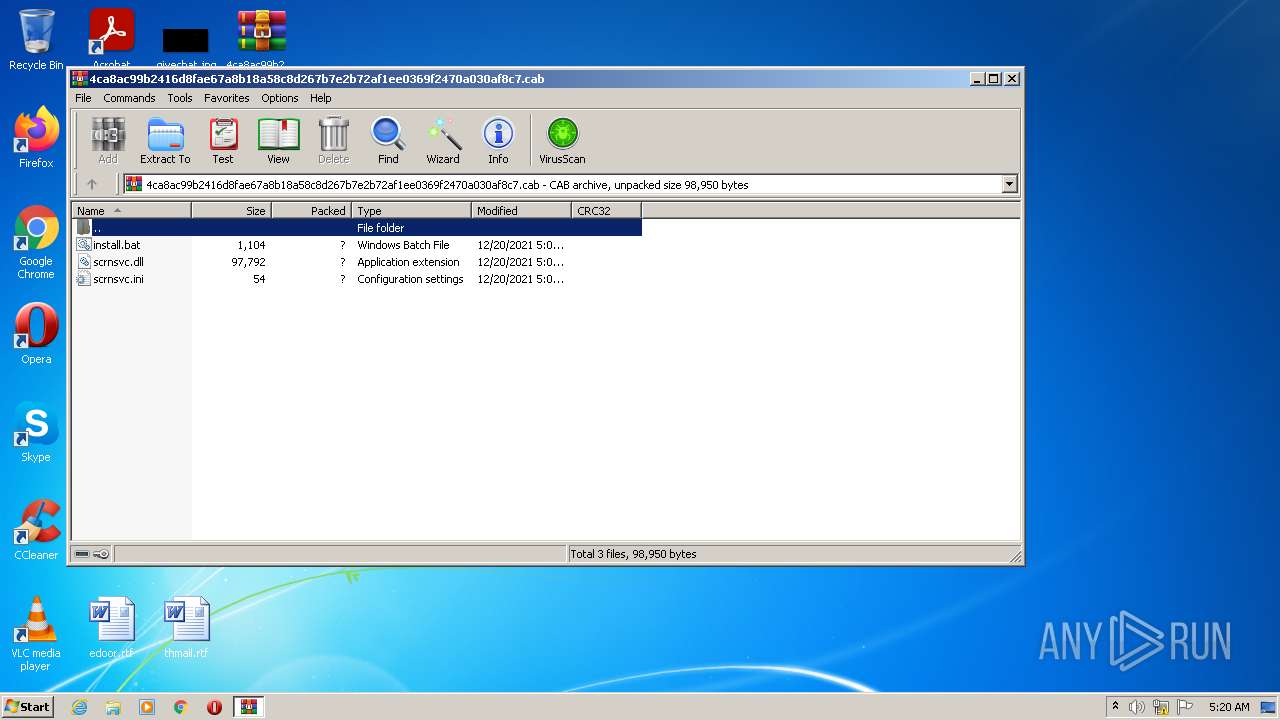
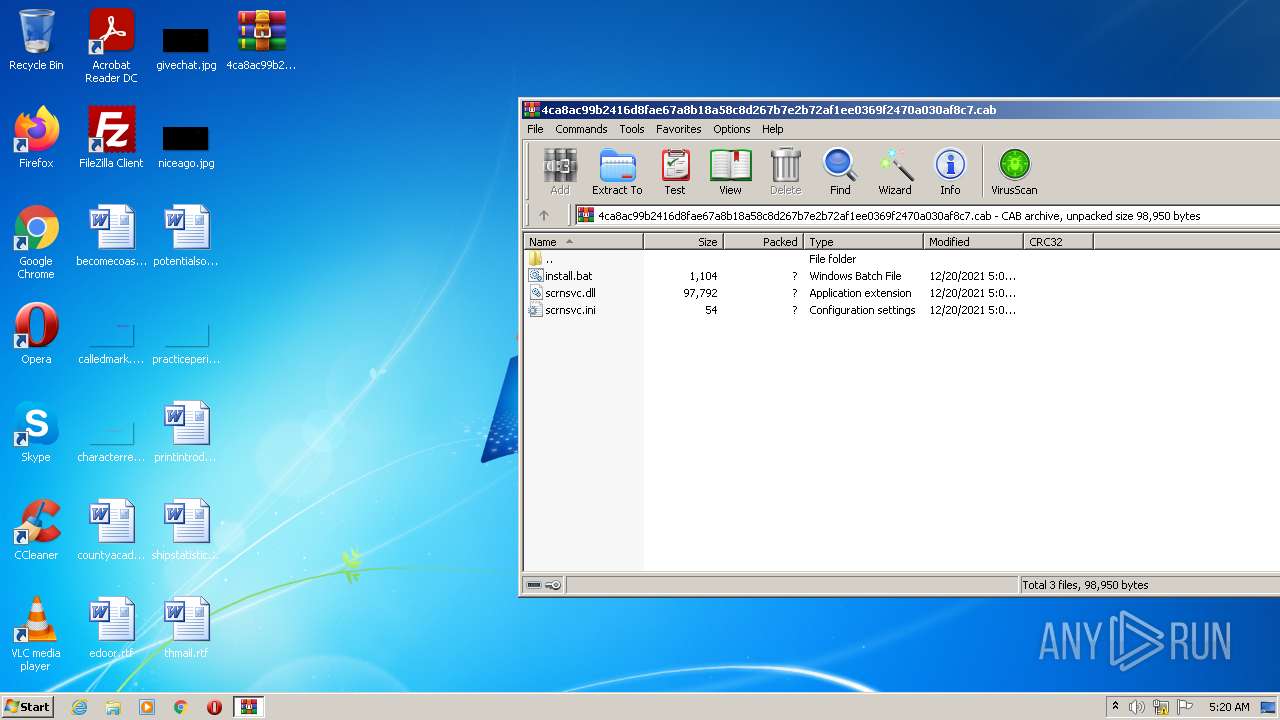
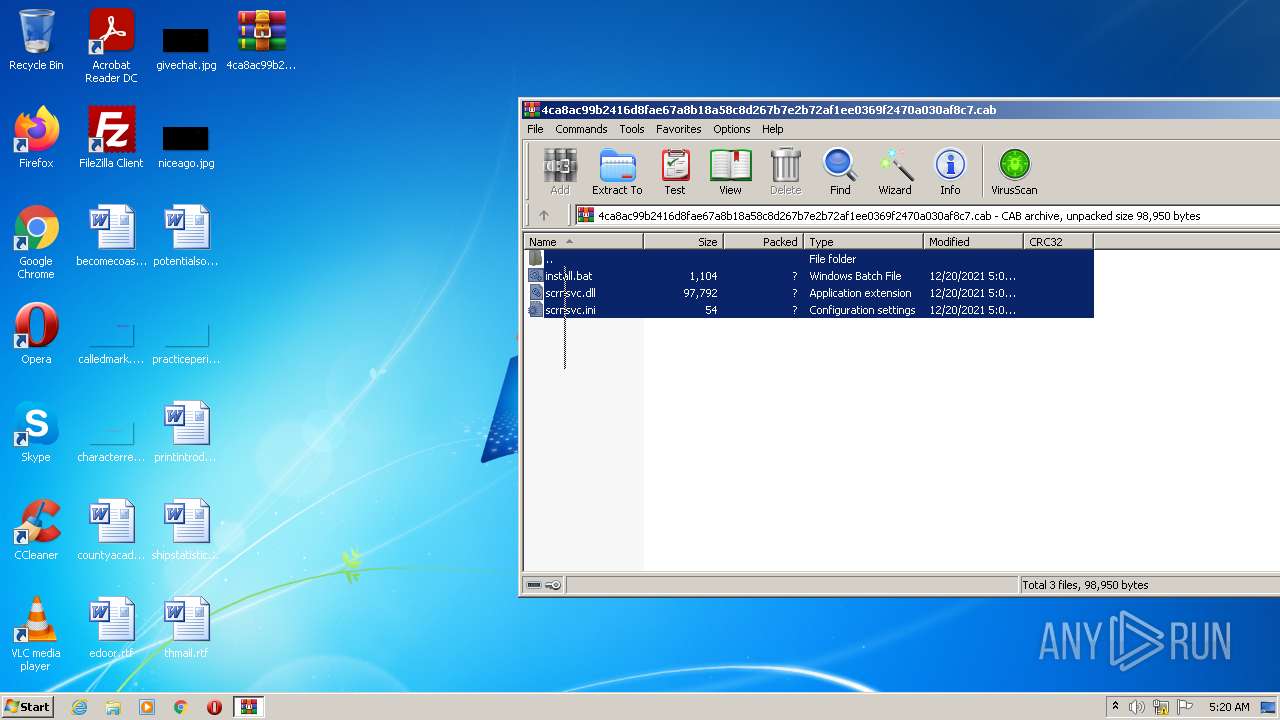
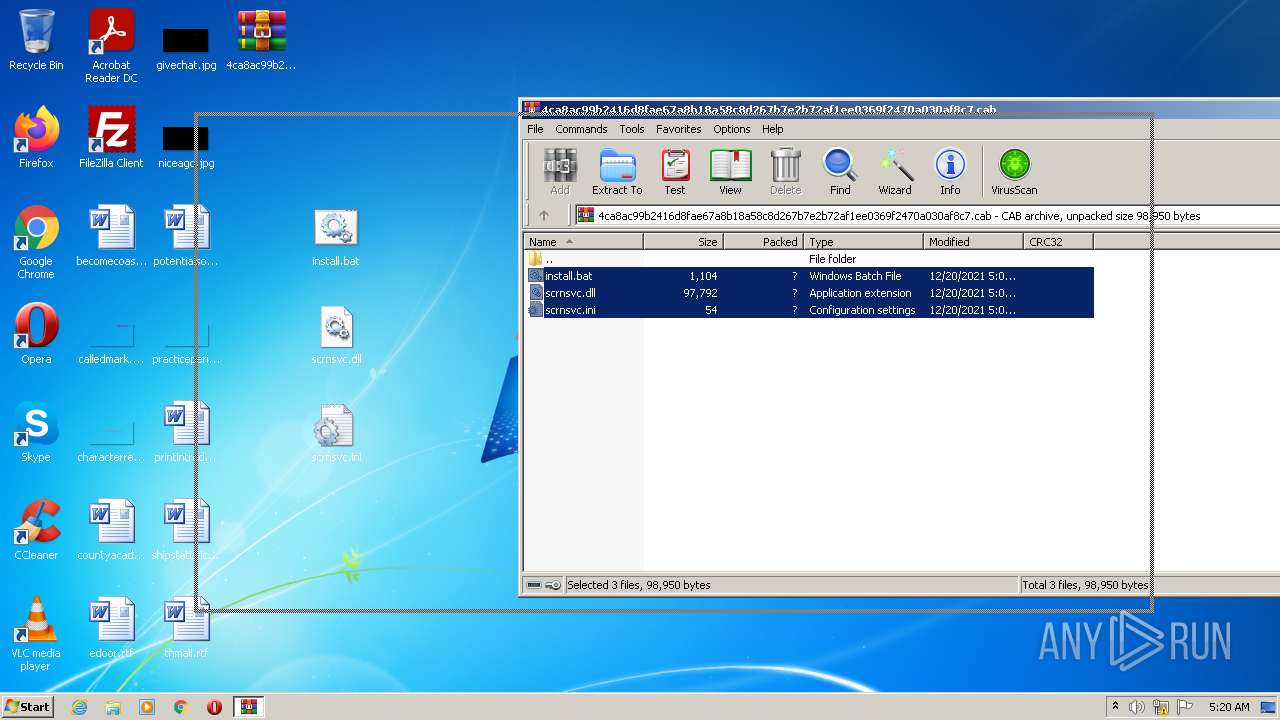
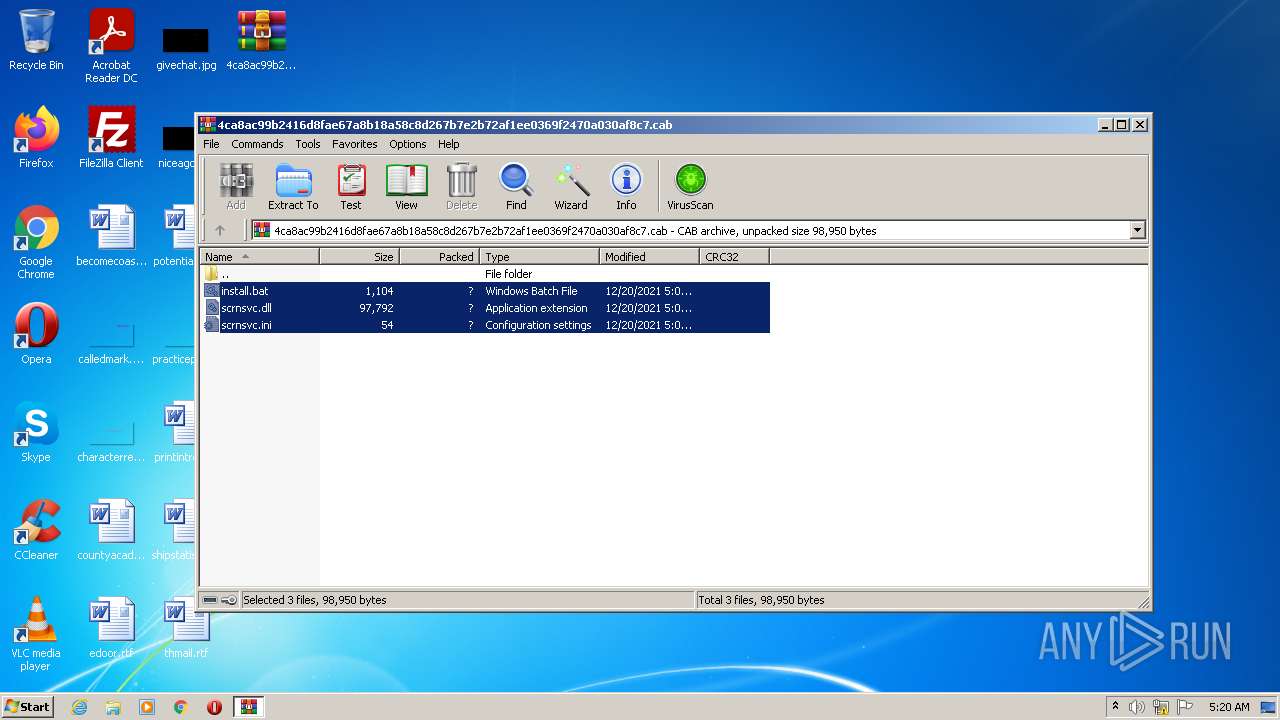
| MIME: | application/vnd.ms-cab-compressed |
| File info: | Microsoft Cabinet archive data, 46792 bytes, 3 files |
| MD5: | 446EA8033AE343971312745C79FCED2E |
| SHA1: | 6883E1C2C1F3656CB756264FDE77F88EBCDE541C |
| SHA256: | 4CA8AC99B2416D8FAE67A8B18A58C8D267B7E2B72AF1EE0369F2470A030AF8C7 |
| SSDEEP: | 768:I/QfC5FcGHcnR/dhdEg/DnKoKrafGLlvPjk8F9q8ViZbfFa18hUoJJ94ywxk1UZJ:IACV8n9dhdTi0KlvPj/z4bg18SoJAywR |
MALICIOUS
Drops executable file immediately after starts
- cmd.exe (PID: 3060)
- WinRAR.exe (PID: 3760)
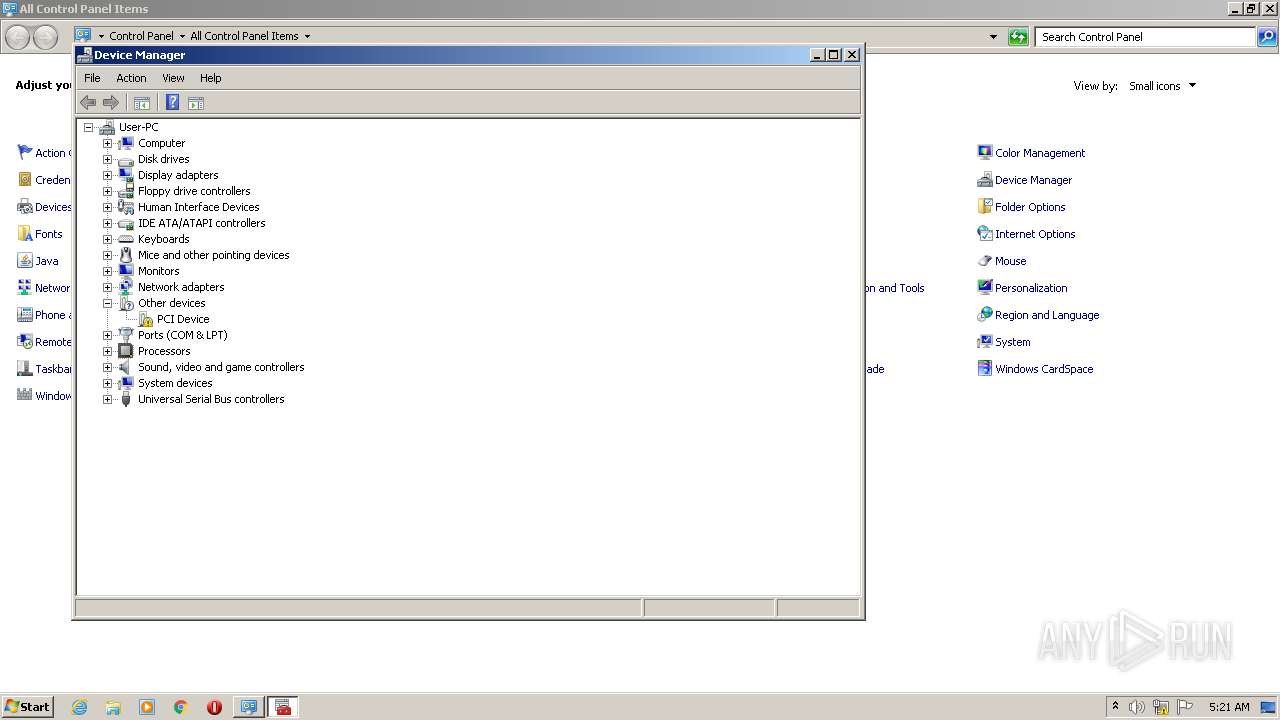
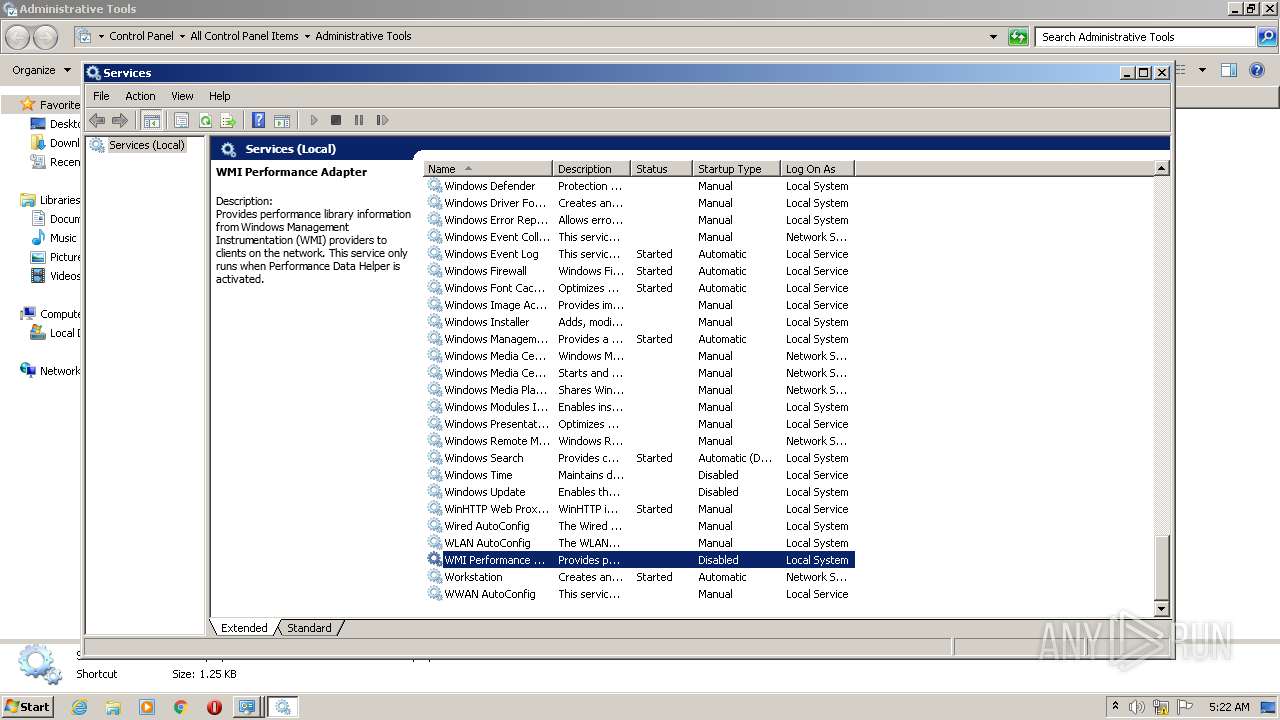
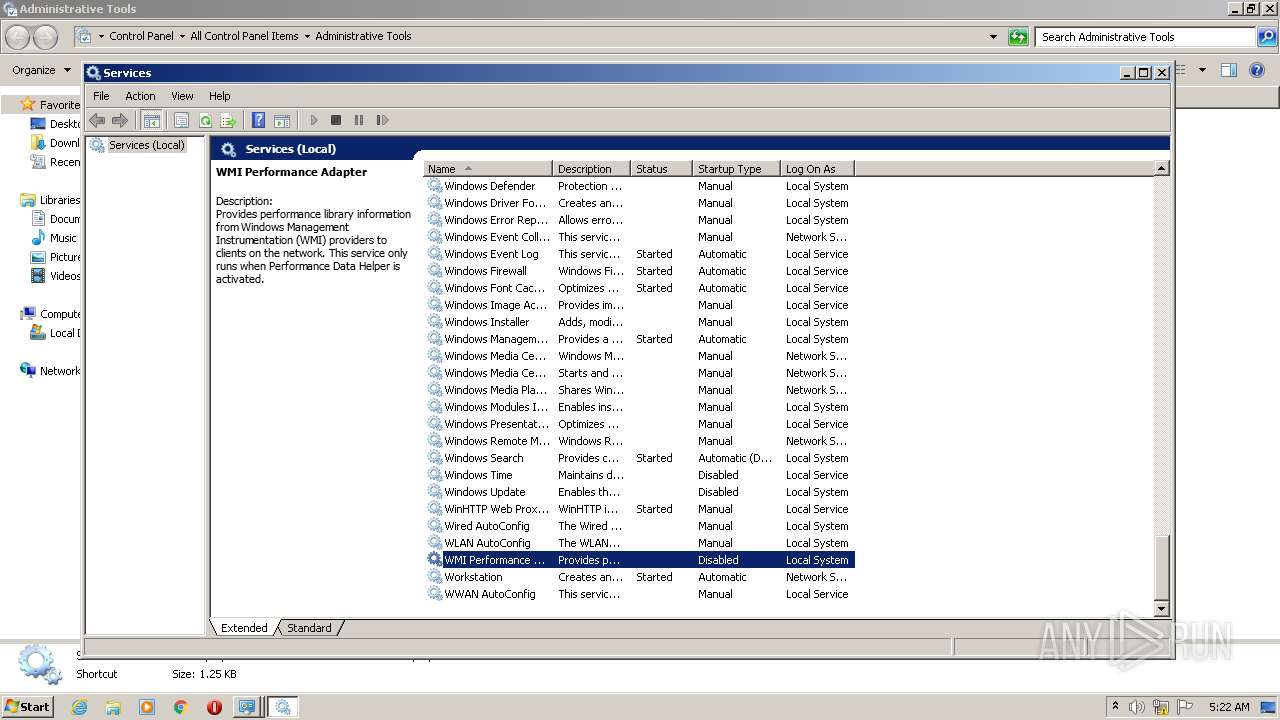
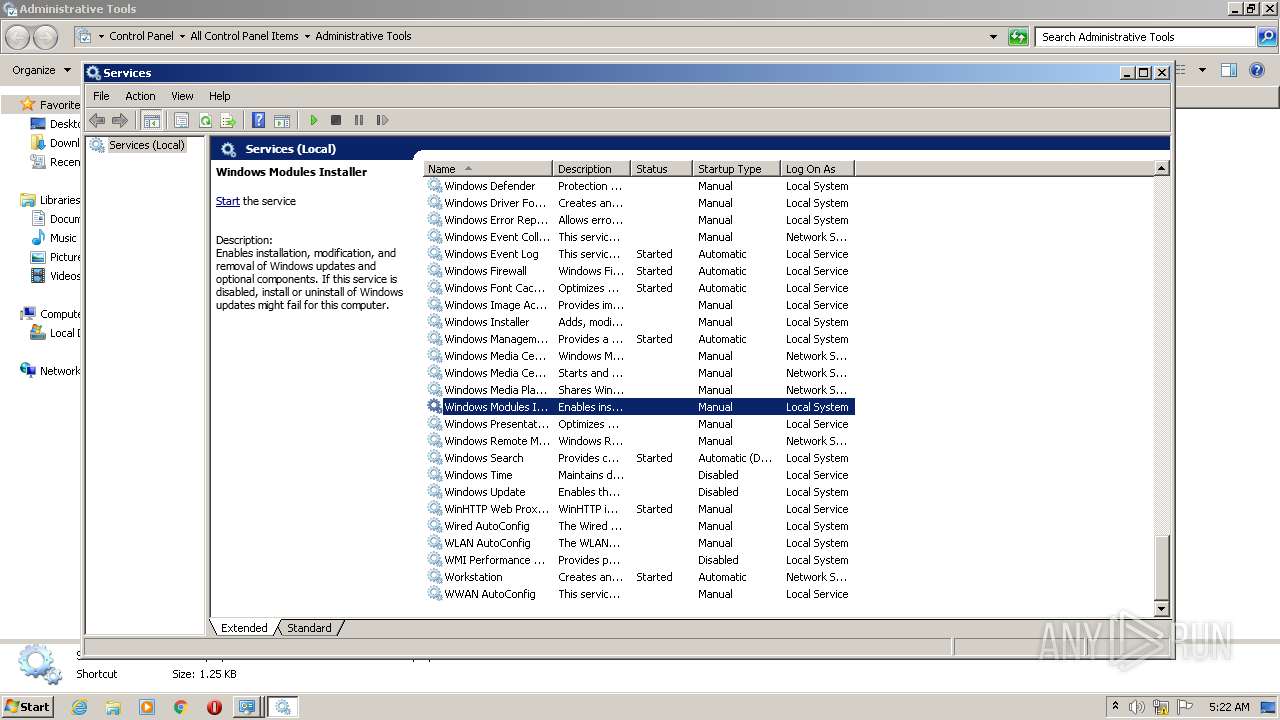
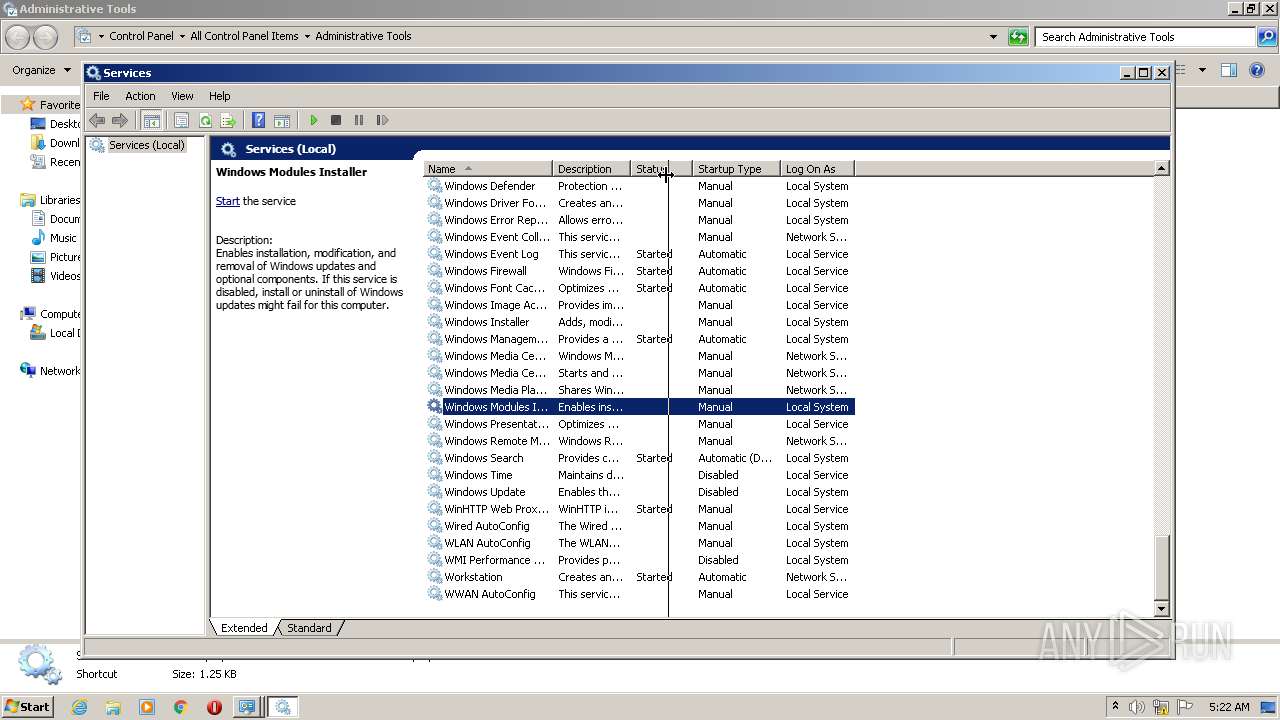
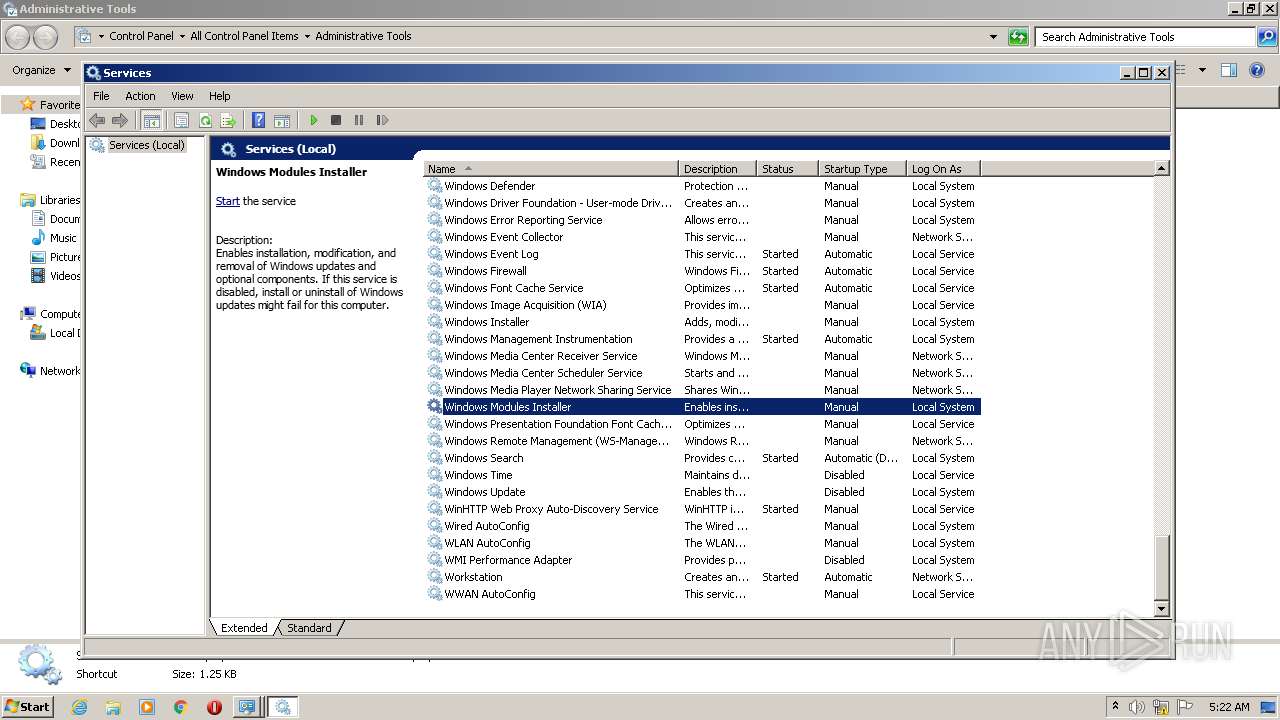
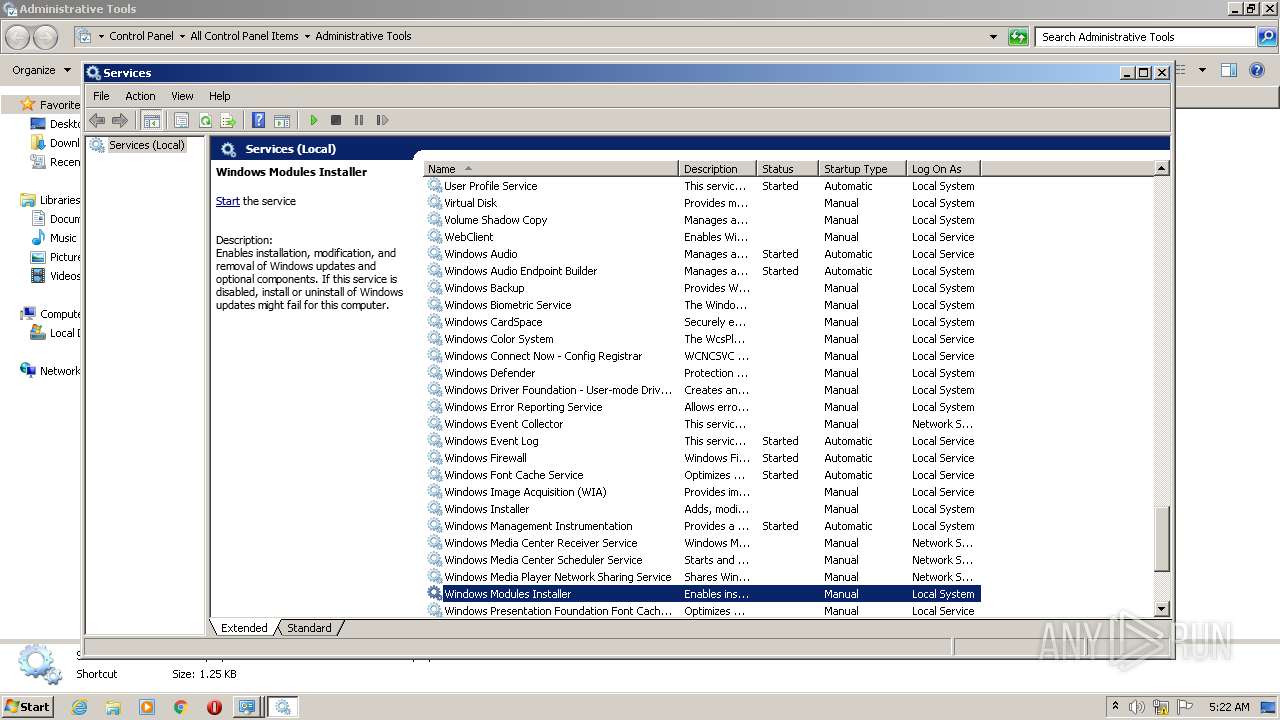
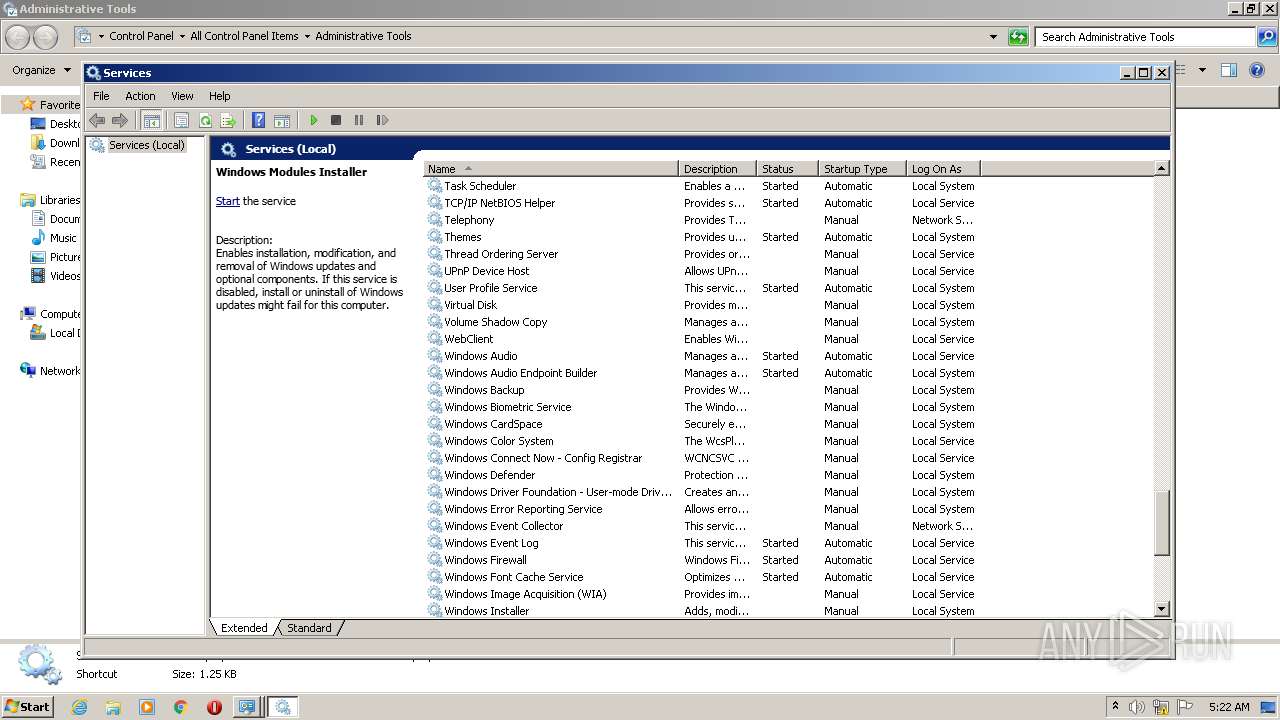
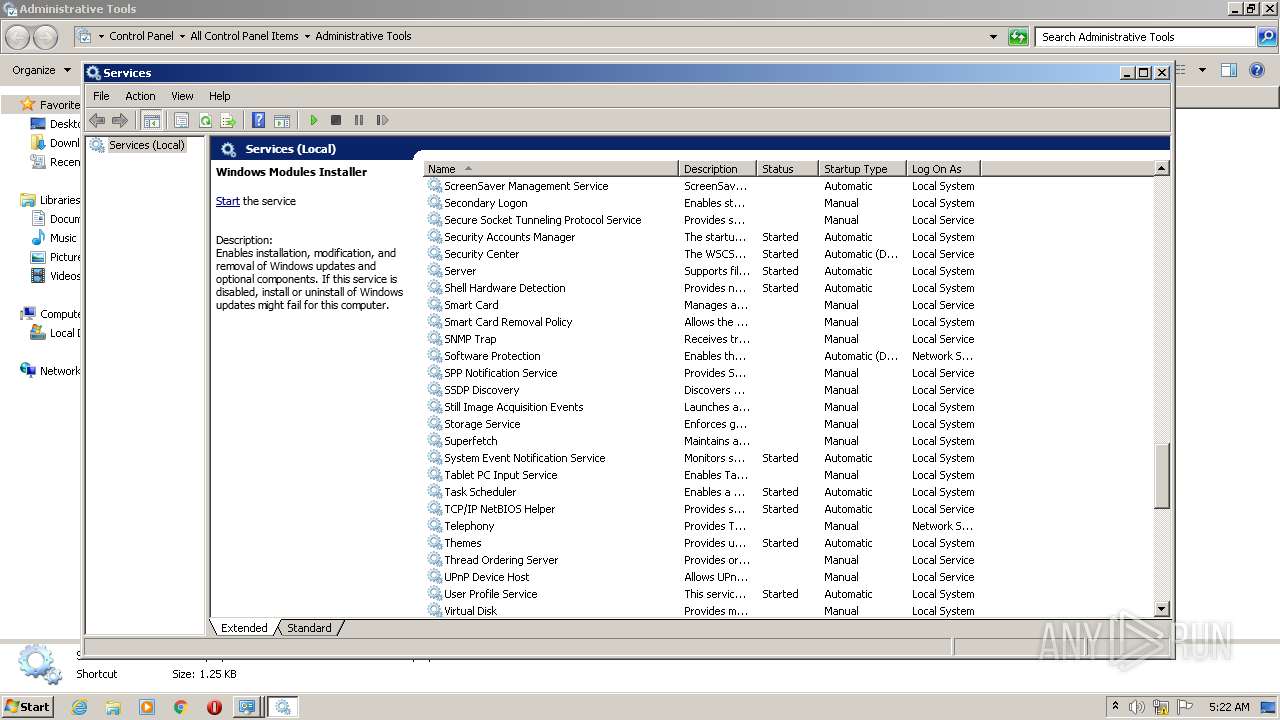
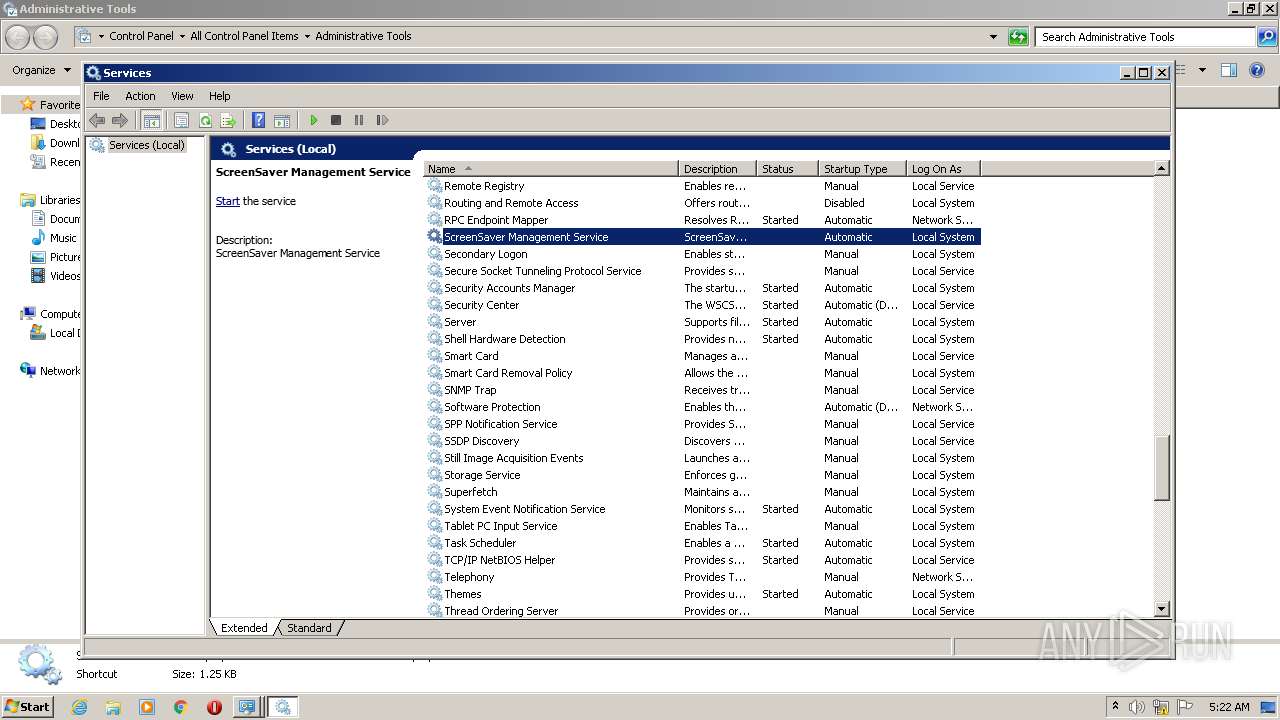
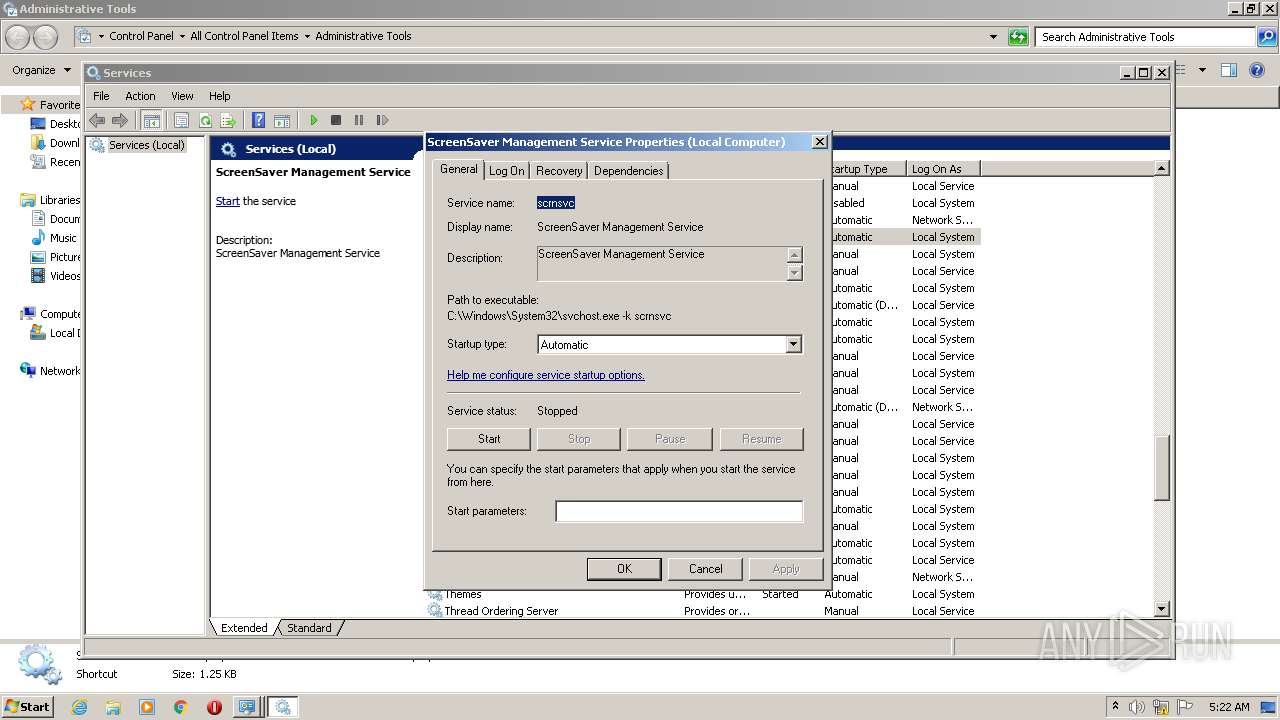
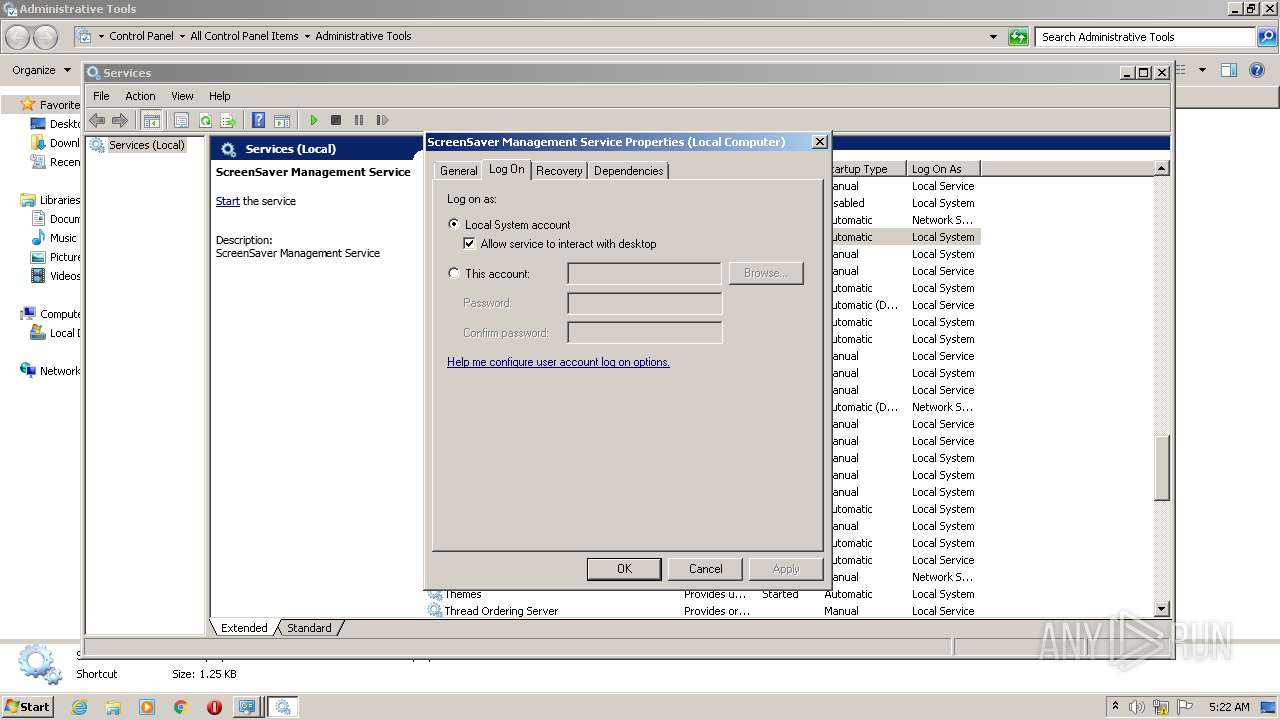
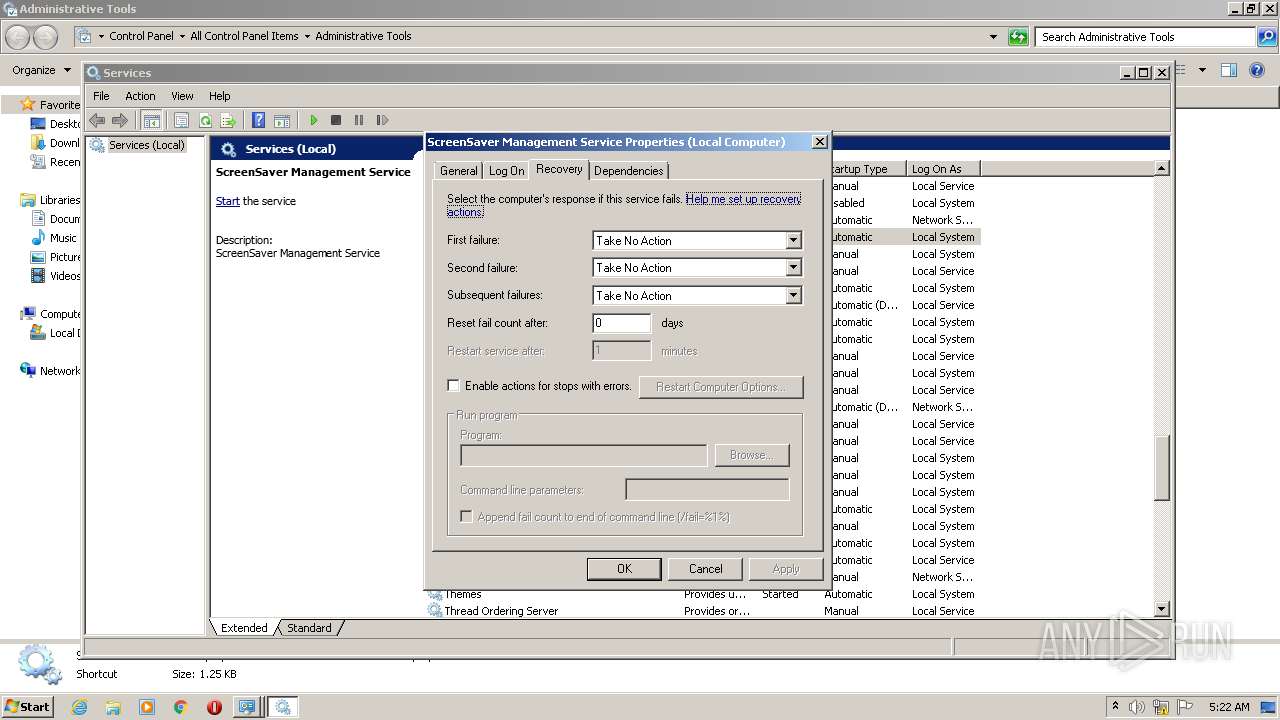
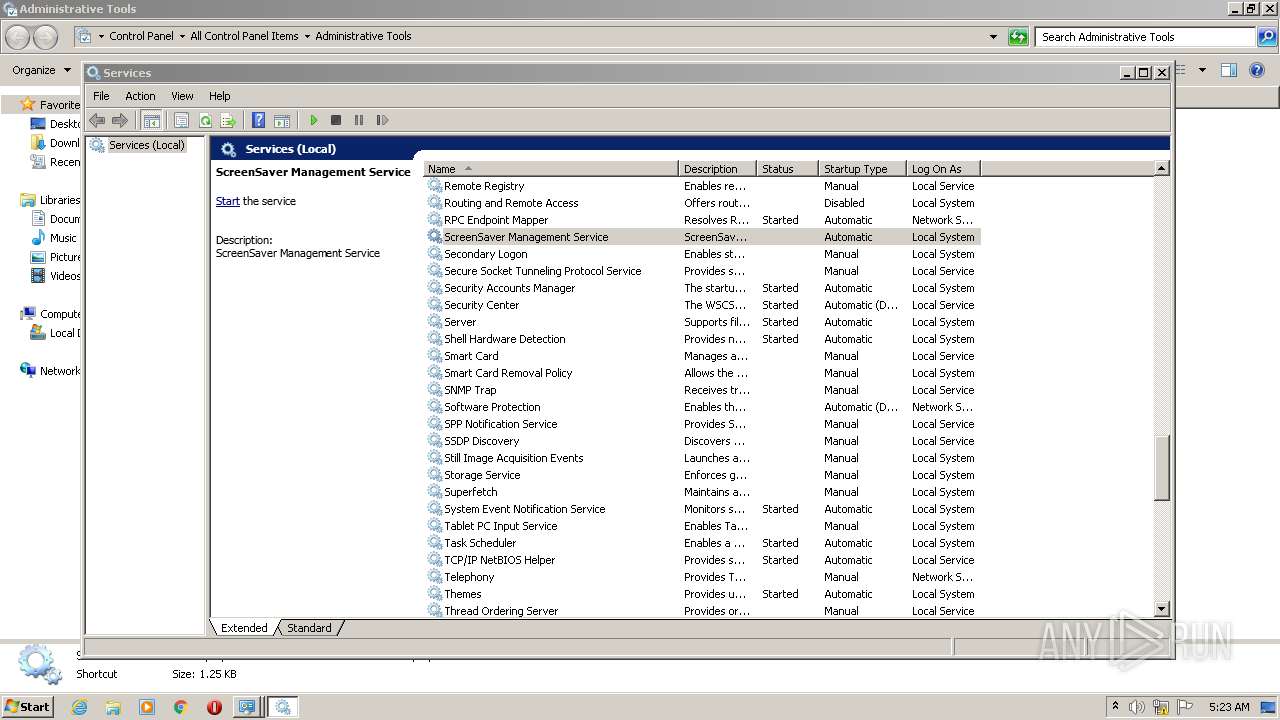
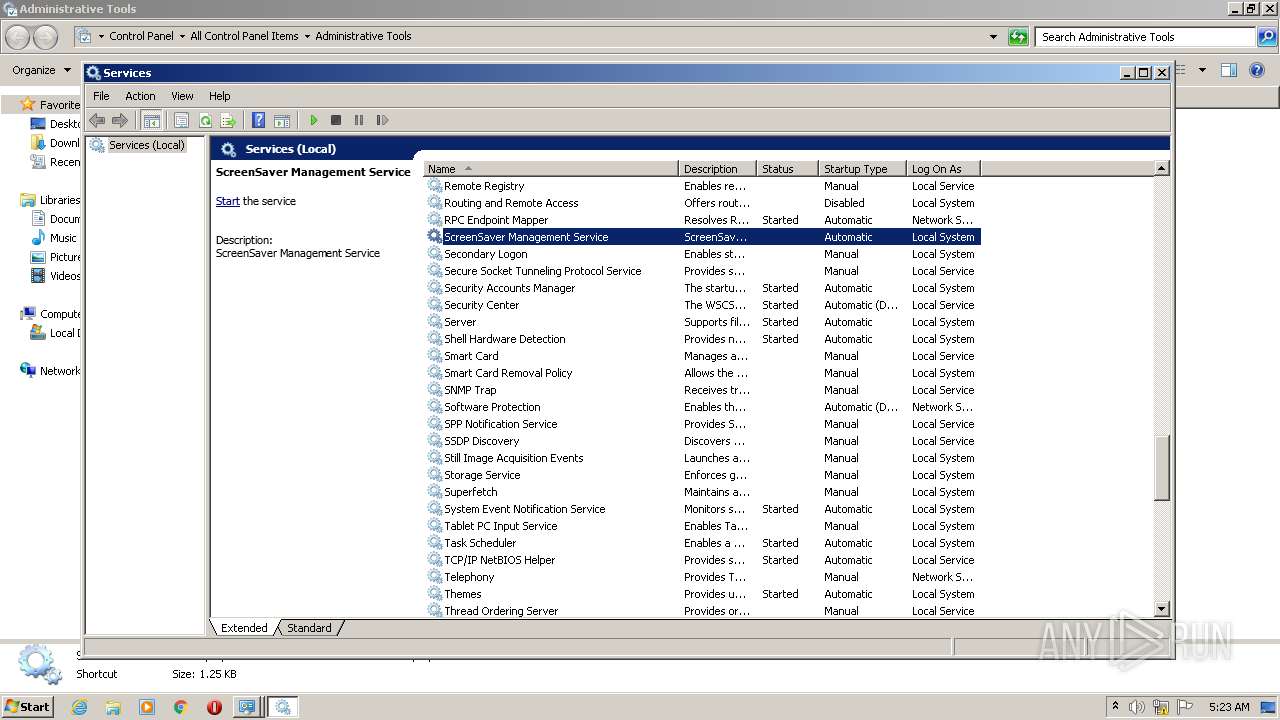
Creates or modifies windows services
- reg.exe (PID: 2372)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 1252)
- WinRAR.exe (PID: 3760)
Checks supported languages
- WinRAR.exe (PID: 1252)
- cmd.exe (PID: 3060)
- WinRAR.exe (PID: 3760)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 3736)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 1252)
- cmd.exe (PID: 3060)
- WinRAR.exe (PID: 3760)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1252)
- cmd.exe (PID: 3060)
- WinRAR.exe (PID: 3760)
Starts SC.EXE for service management
- cmd.exe (PID: 3060)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3060)
Reads Microsoft Outlook installation path
- mmc.exe (PID: 576)
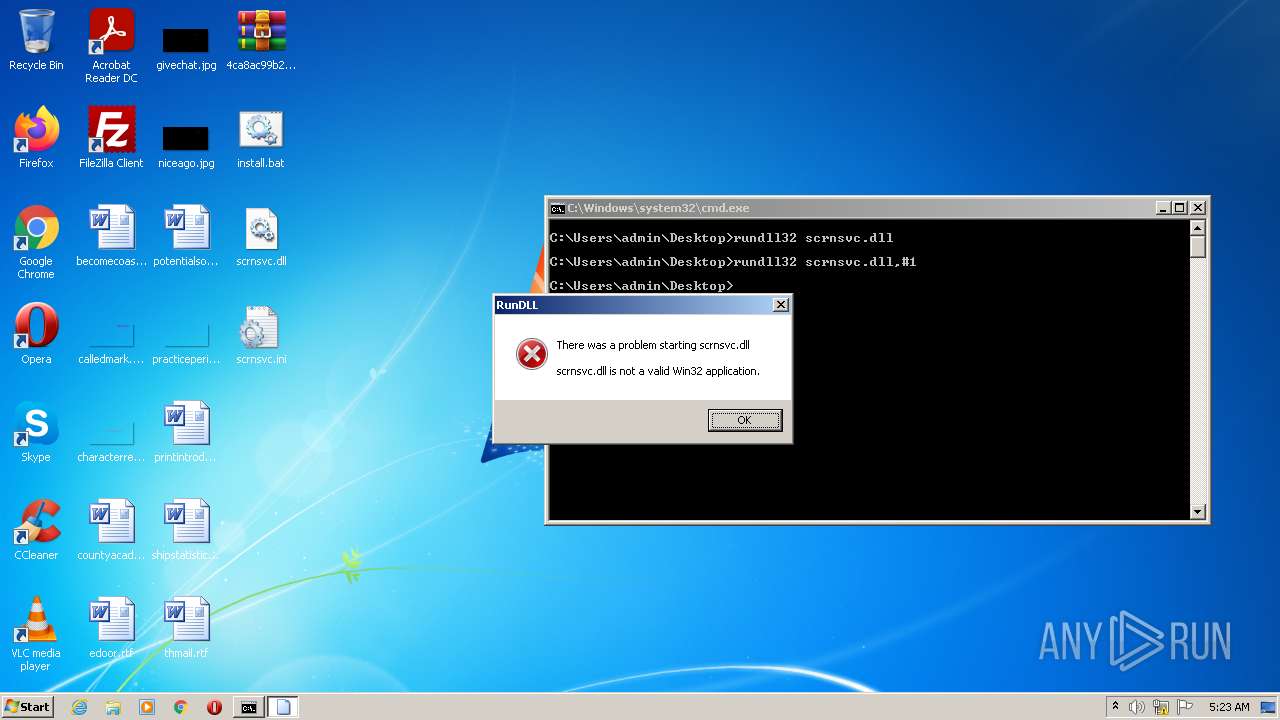
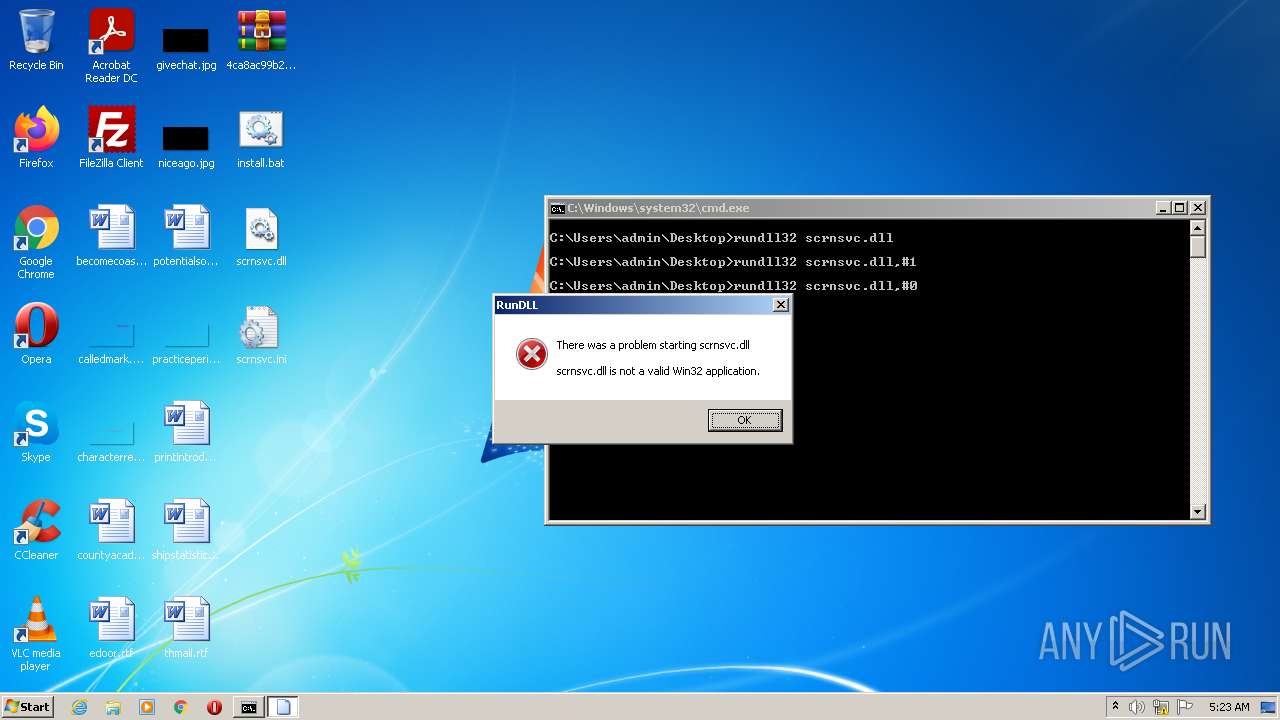
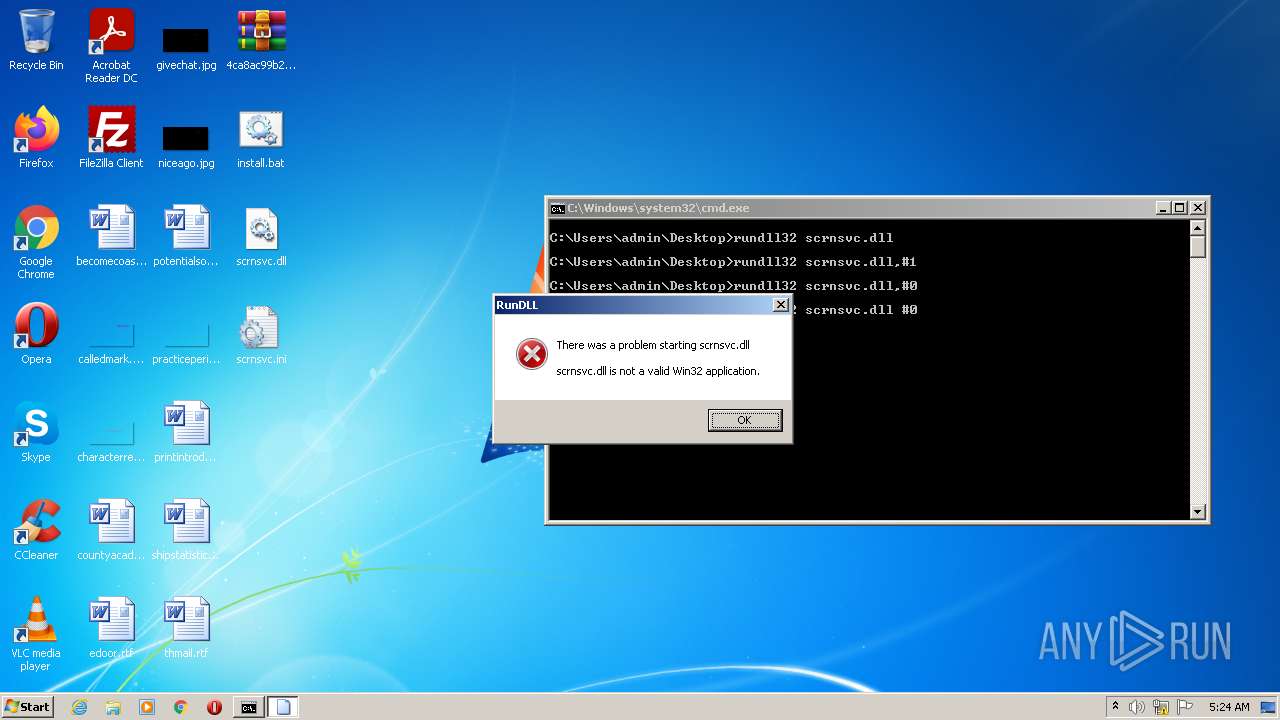
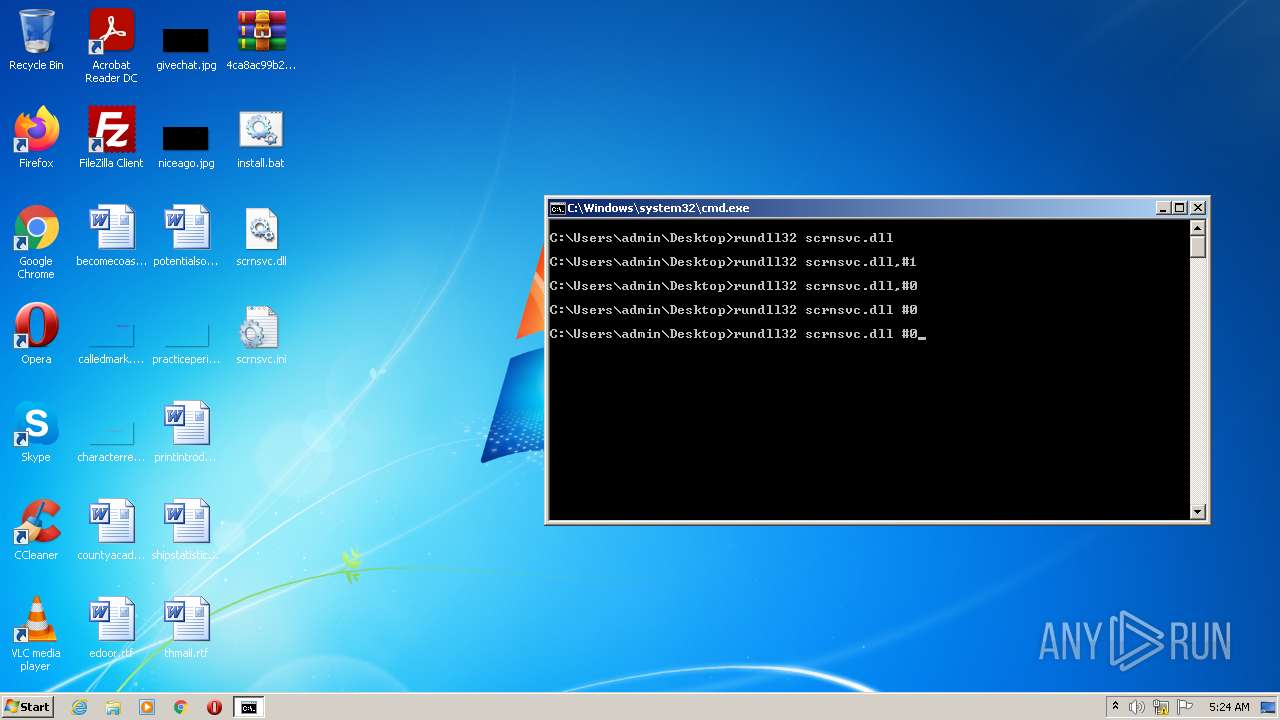
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 3008)
Reads internet explorer settings
- mmc.exe (PID: 576)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3060)
Application launched itself
- cmd.exe (PID: 3060)
Creates files in the Windows directory
- cmd.exe (PID: 3060)
INFO
Checks supported languages
- sc.exe (PID: 2972)
- sc.exe (PID: 1488)
- sc.exe (PID: 2104)
- sc.exe (PID: 3908)
- reg.exe (PID: 3476)
- sc.exe (PID: 1404)
- reg.exe (PID: 2372)
- mmc.exe (PID: 576)
- mmc.exe (PID: 3672)
- rundll32.exe (PID: 2272)
- rundll32.exe (PID: 3500)
- rundll32.exe (PID: 2496)
- rundll32.exe (PID: 1524)
- findstr.exe (PID: 832)
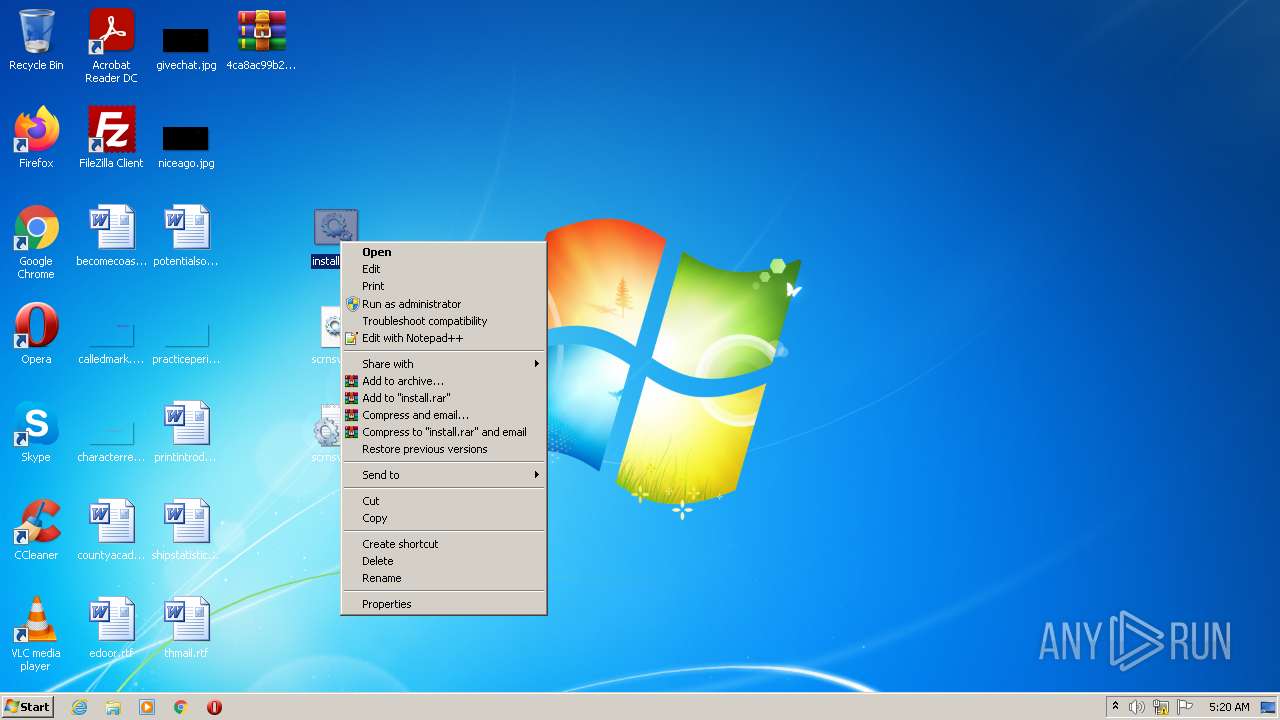
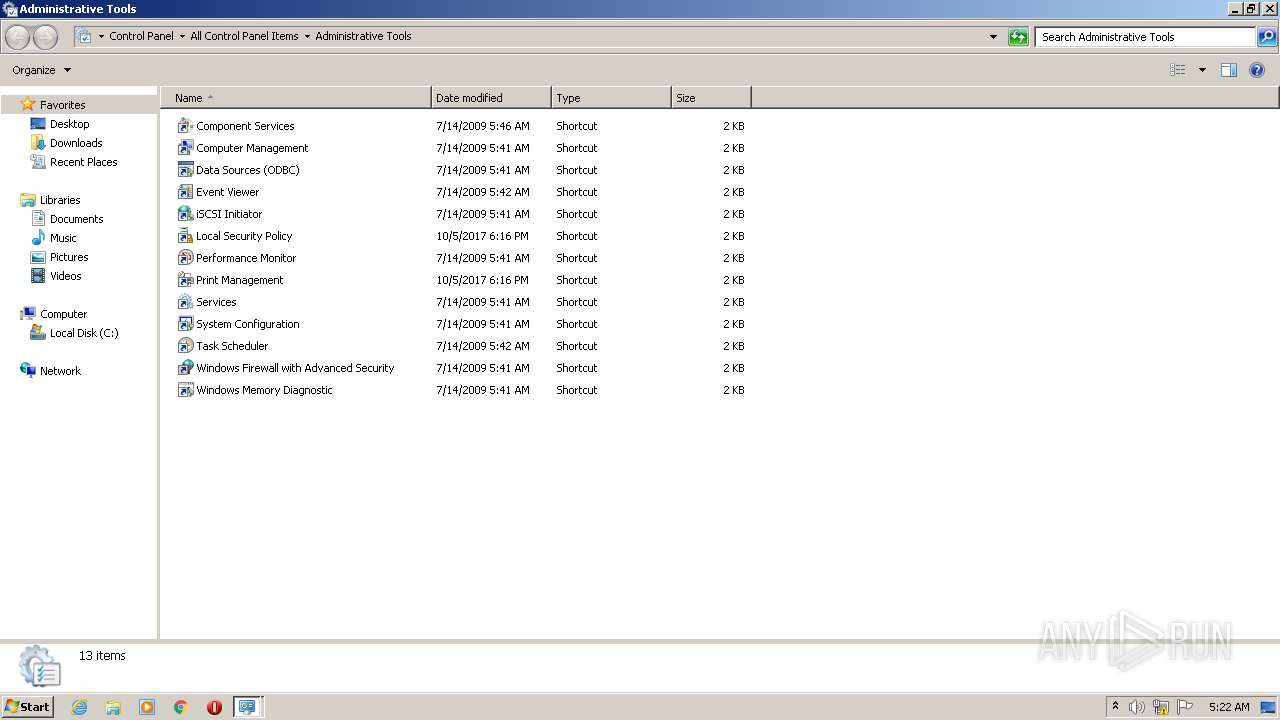
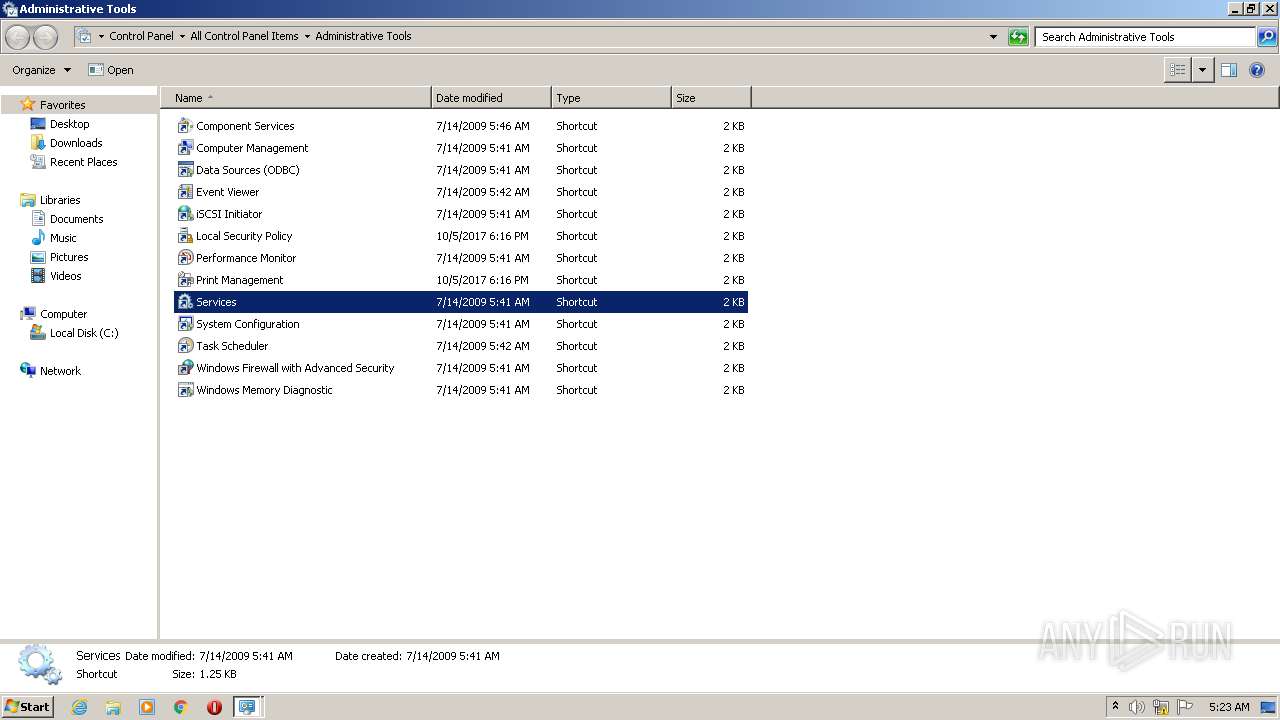
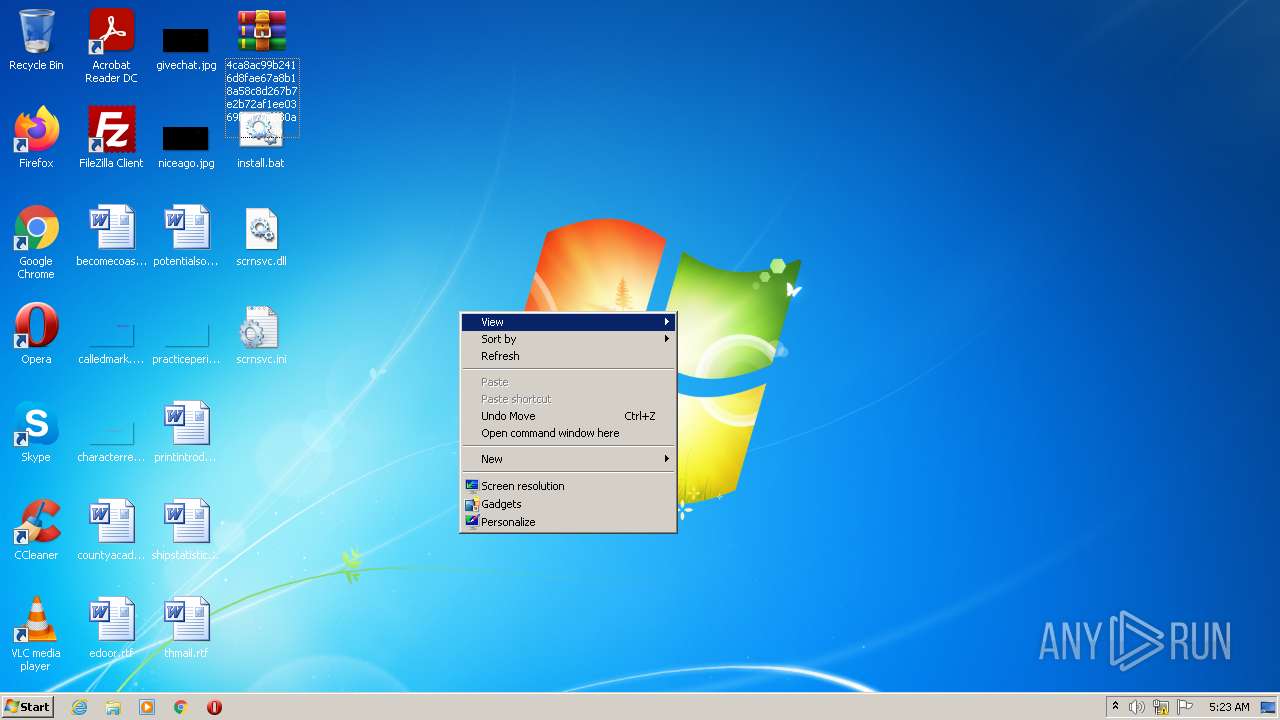
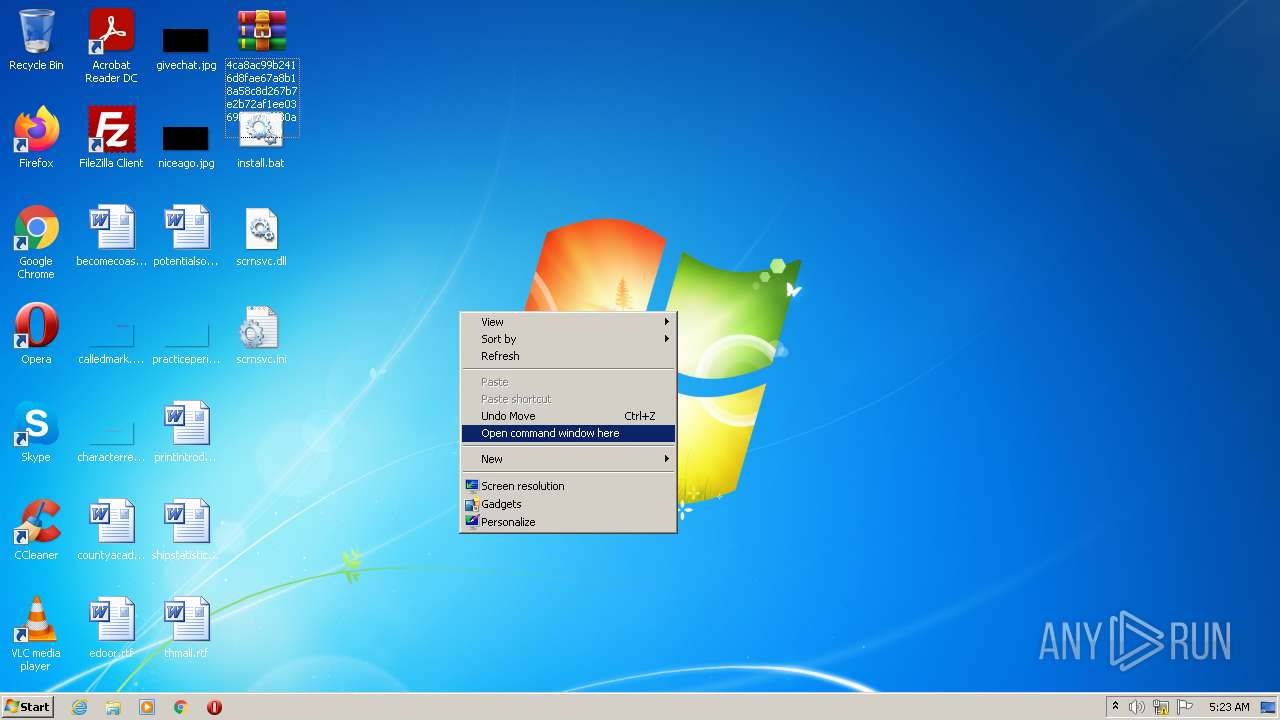
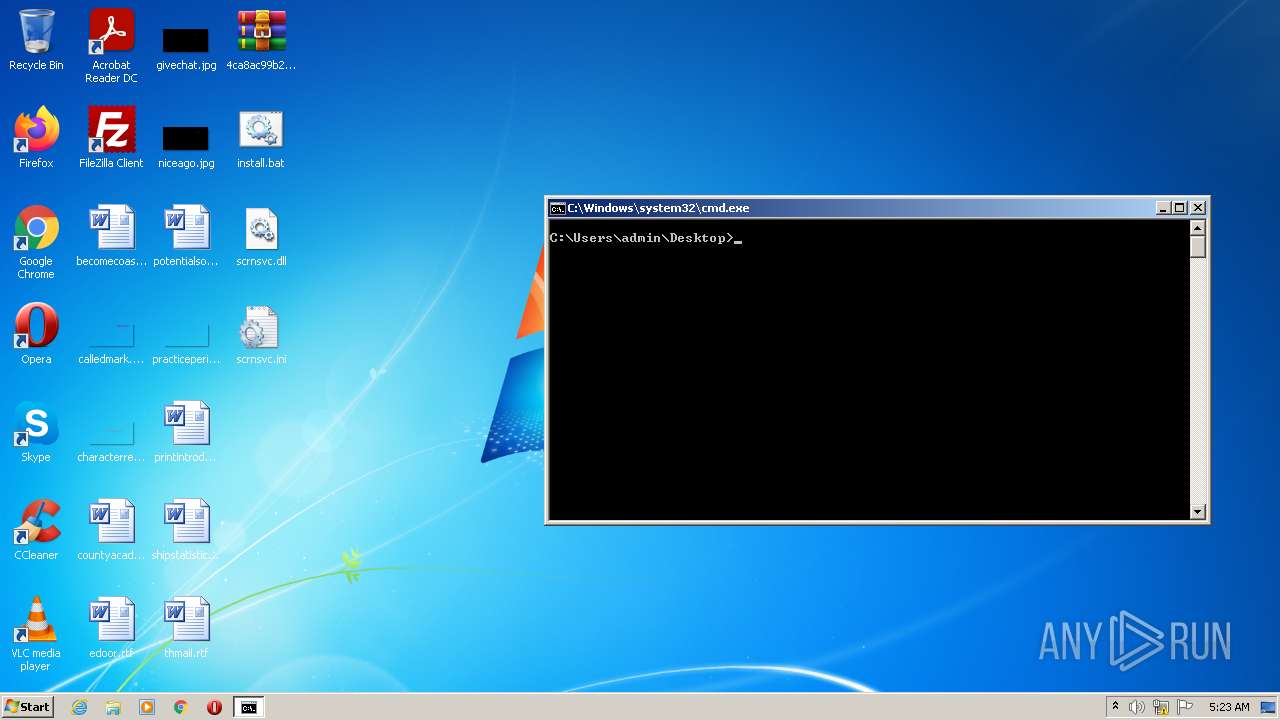
Manual execution by user
- cmd.exe (PID: 3060)
- mmc.exe (PID: 1292)
- WinRAR.exe (PID: 3760)
- mmc.exe (PID: 576)
- mmc.exe (PID: 3008)
- mmc.exe (PID: 3672)
- cmd.exe (PID: 3008)
Reads the computer name
- sc.exe (PID: 2104)
- sc.exe (PID: 3908)
- sc.exe (PID: 1488)
- sc.exe (PID: 1404)
- mmc.exe (PID: 3672)
- mmc.exe (PID: 576)
- sc.exe (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .cab | | | Microsoft Cabinet Archive (100) |
|---|
Total processes
73
Monitored processes
21
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
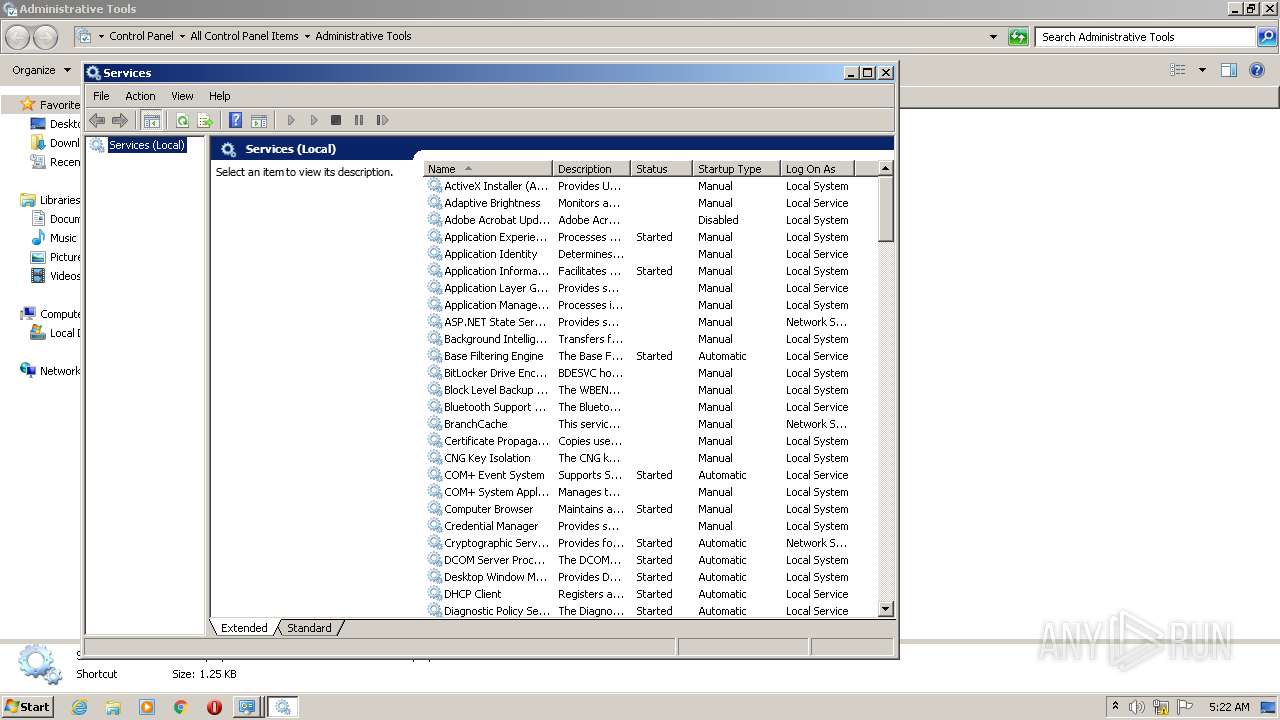
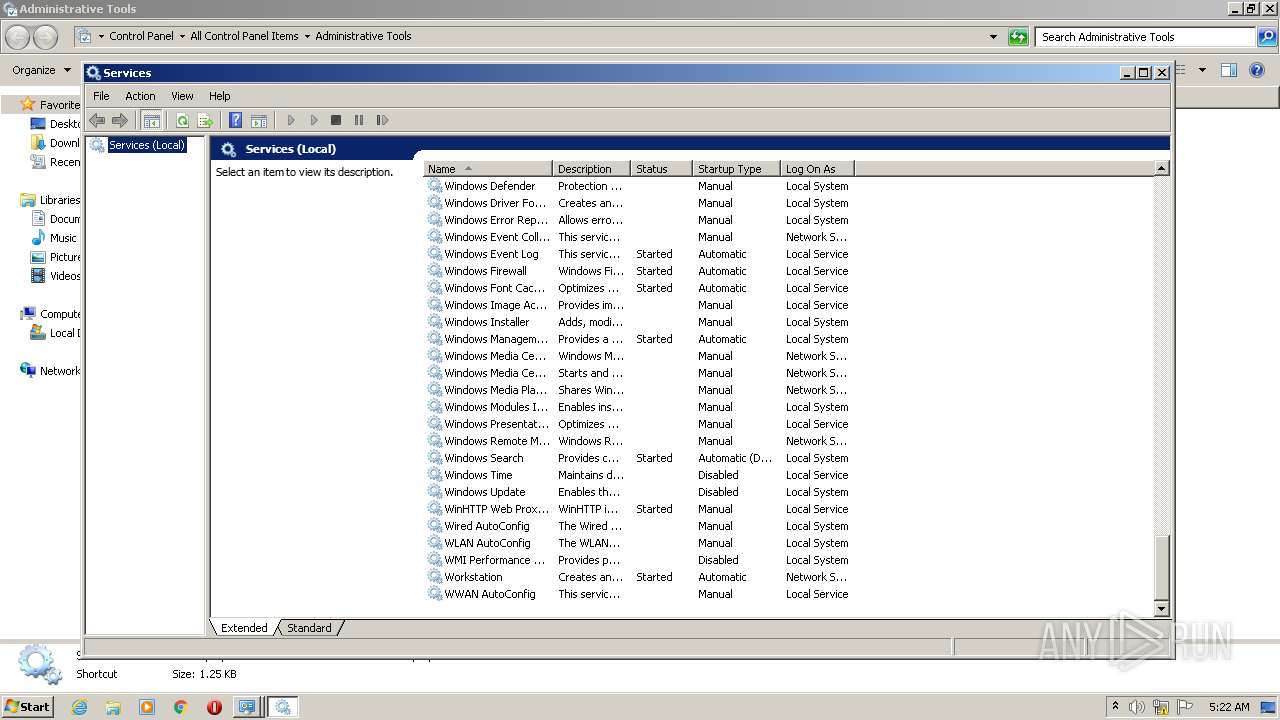
| 576 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\services.msc" | C:\Windows\system32\mmc.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 832 | findstr /i "system32" | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
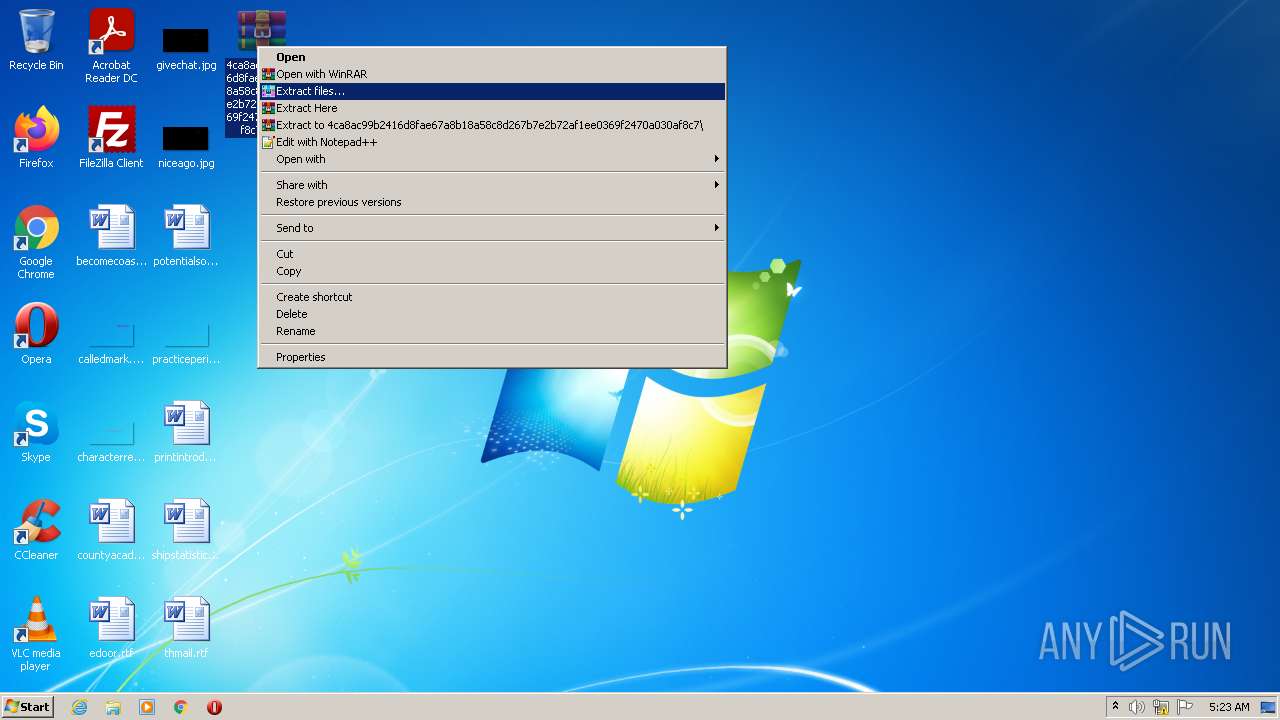
| 1252 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\4ca8ac99b2416d8fae67a8b18a58c8d267b7e2b72af1ee0369f2470a030af8c7.cab" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1292 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\services.msc" | C:\Windows\system32\mmc.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
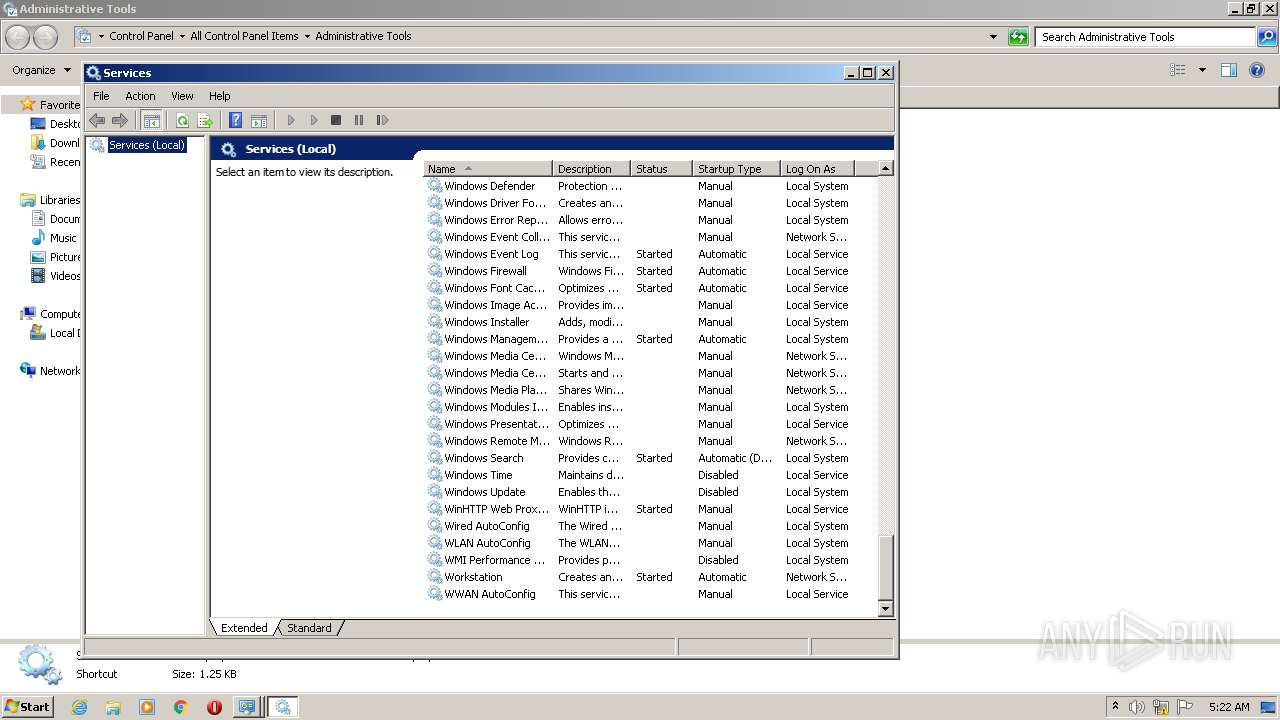
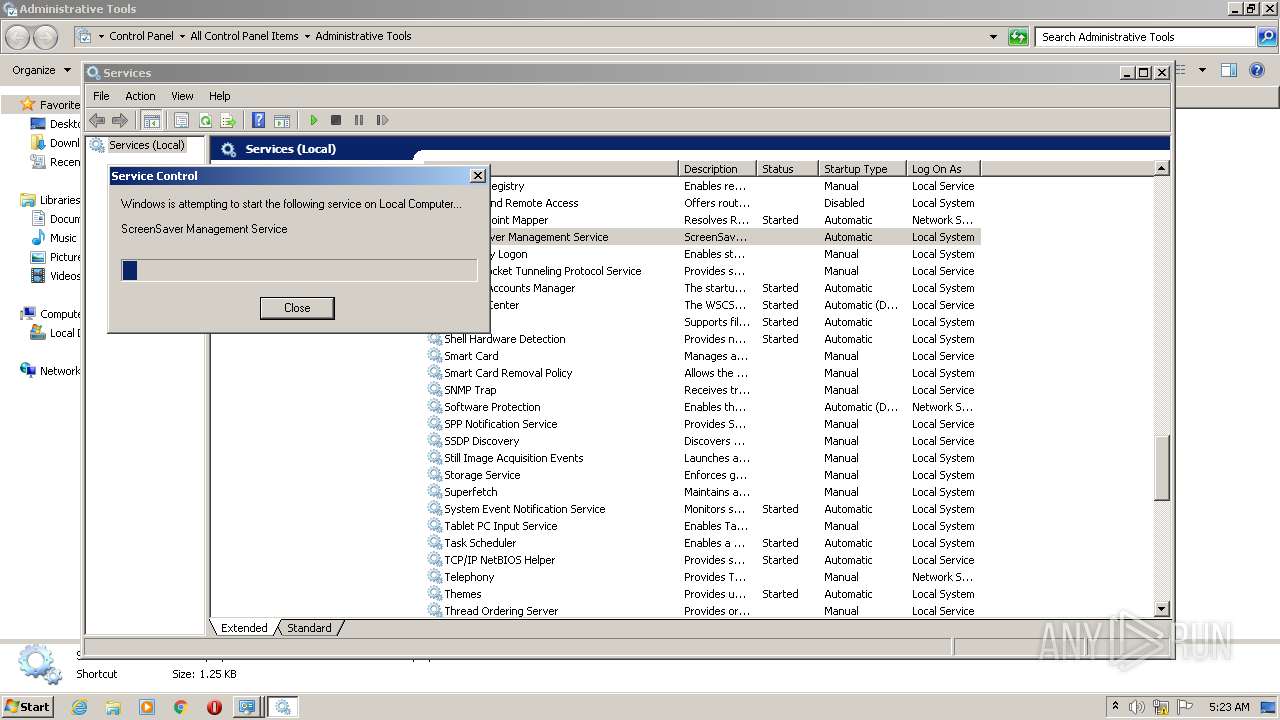
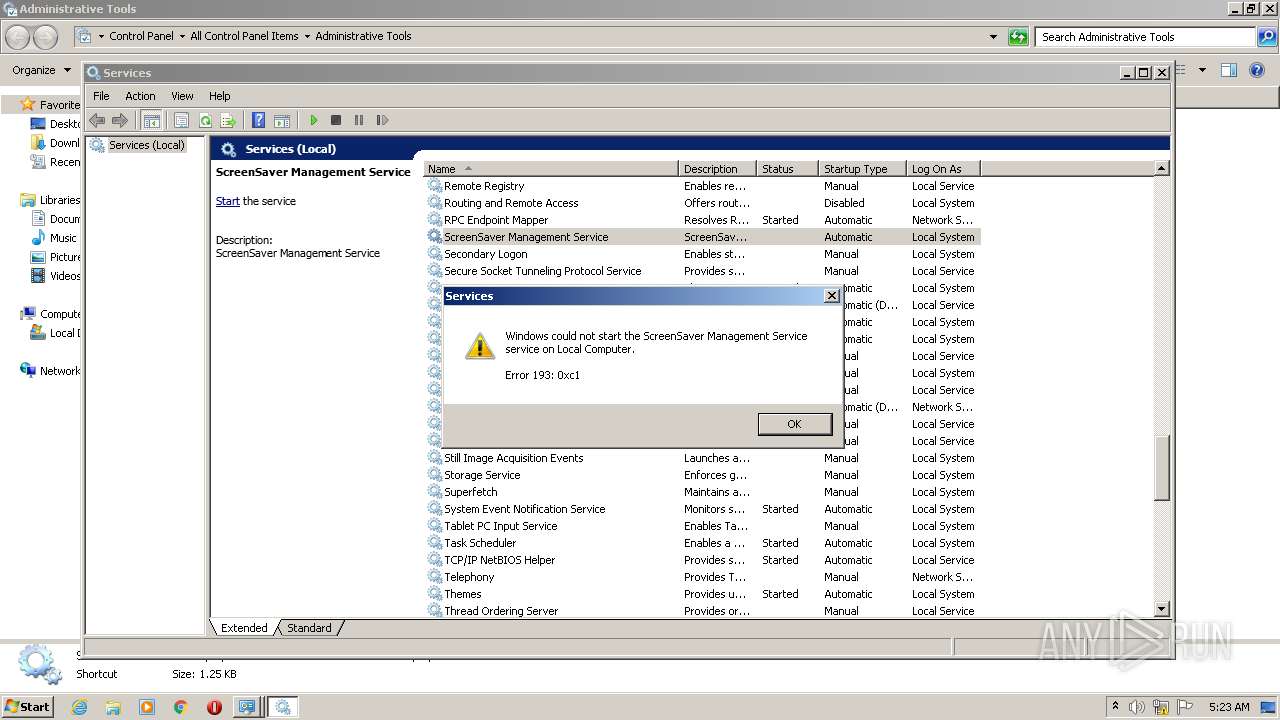
| 1404 | sc start scrnsvc | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
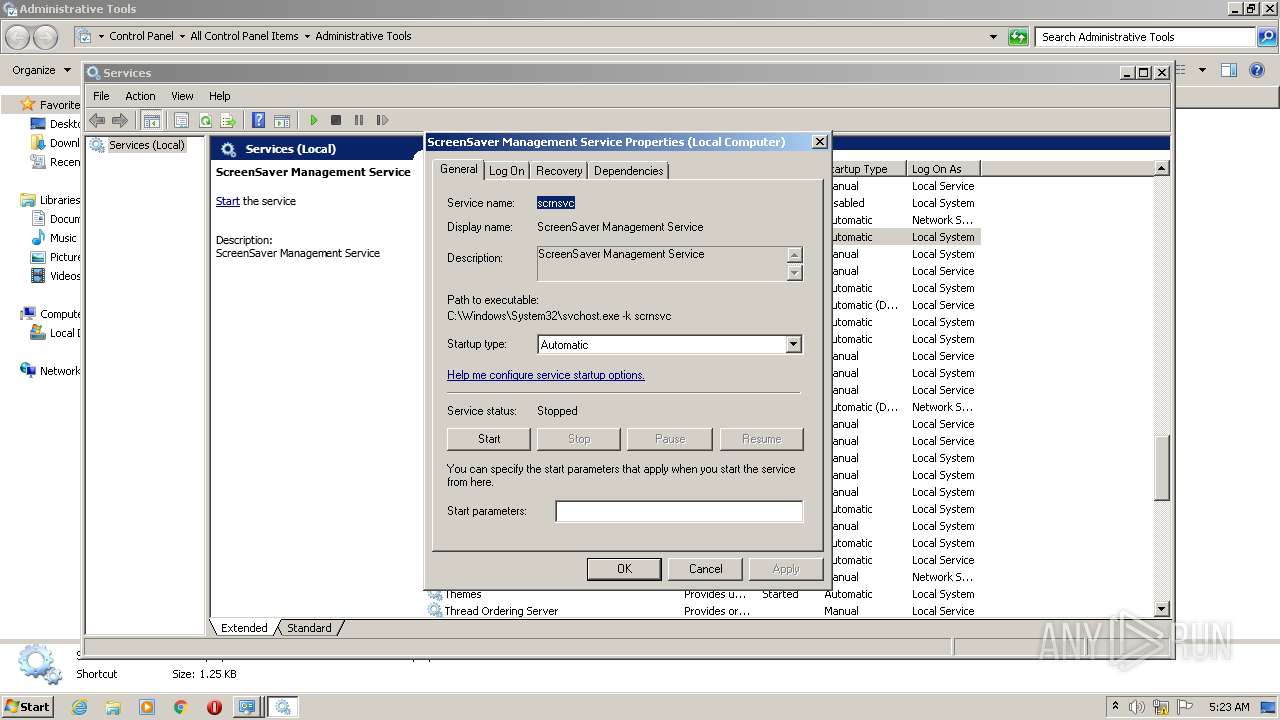
| 1488 | sc create scrnsvc binpath= "C:\Windows\System32\svchost.exe -k scrnsvc" DisplayName= "ScreenSaver Management Service" | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1524 | rundll32 scrnsvc.dll #0 | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2104 | sc description scrnsvc "ScreenSaver Management Service" | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | rundll32 scrnsvc.dll,#1 | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | reg add "HKLM\SYSTEM\CurrentControlSet\Services\scrnsvc\Parameters" /v ServiceDll /t REG_EXPAND_SZ /d "C:\Windows\System32\scrnsvc.dll" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 751
Read events
1 697
Write events
52
Delete events
2
Modification events
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\4ca8ac99b2416d8fae67a8b18a58c8d267b7e2b72af1ee0369f2470a030af8c7.cab | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1252) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3060 | cmd.exe | C:\Windows\System32\scrnsvc.ini | binary | |
MD5:— | SHA256:— | |||
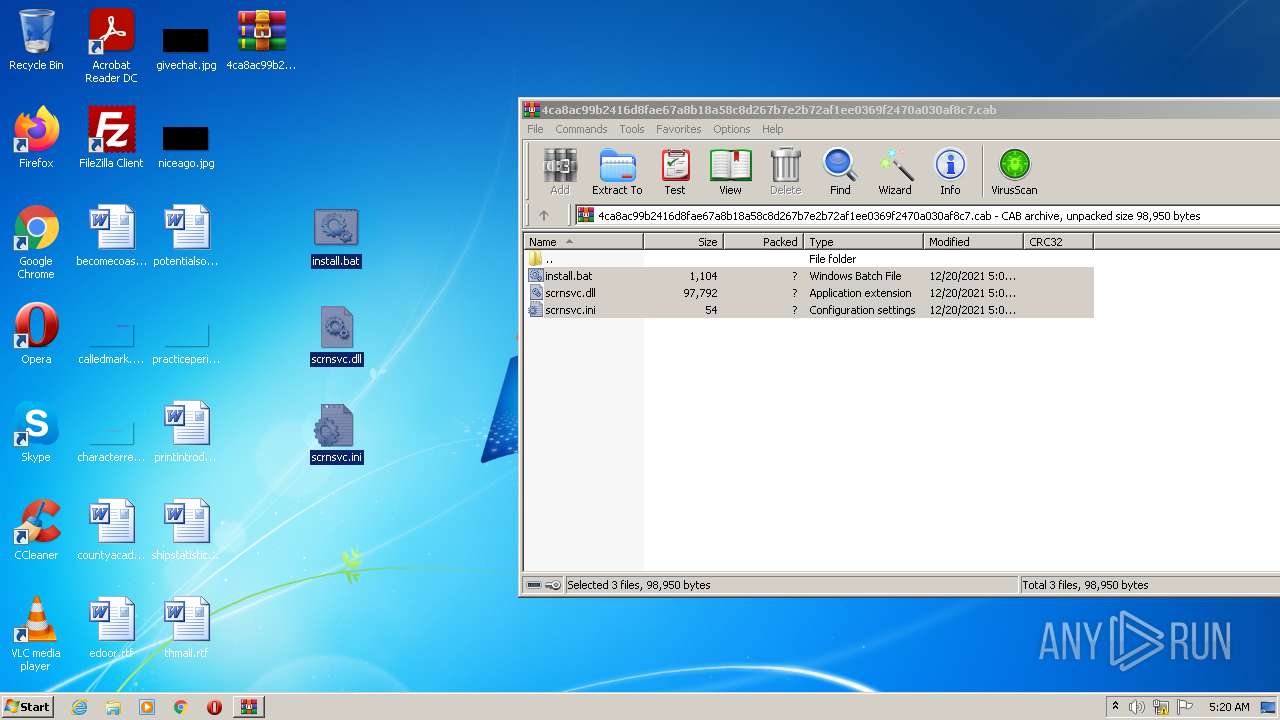
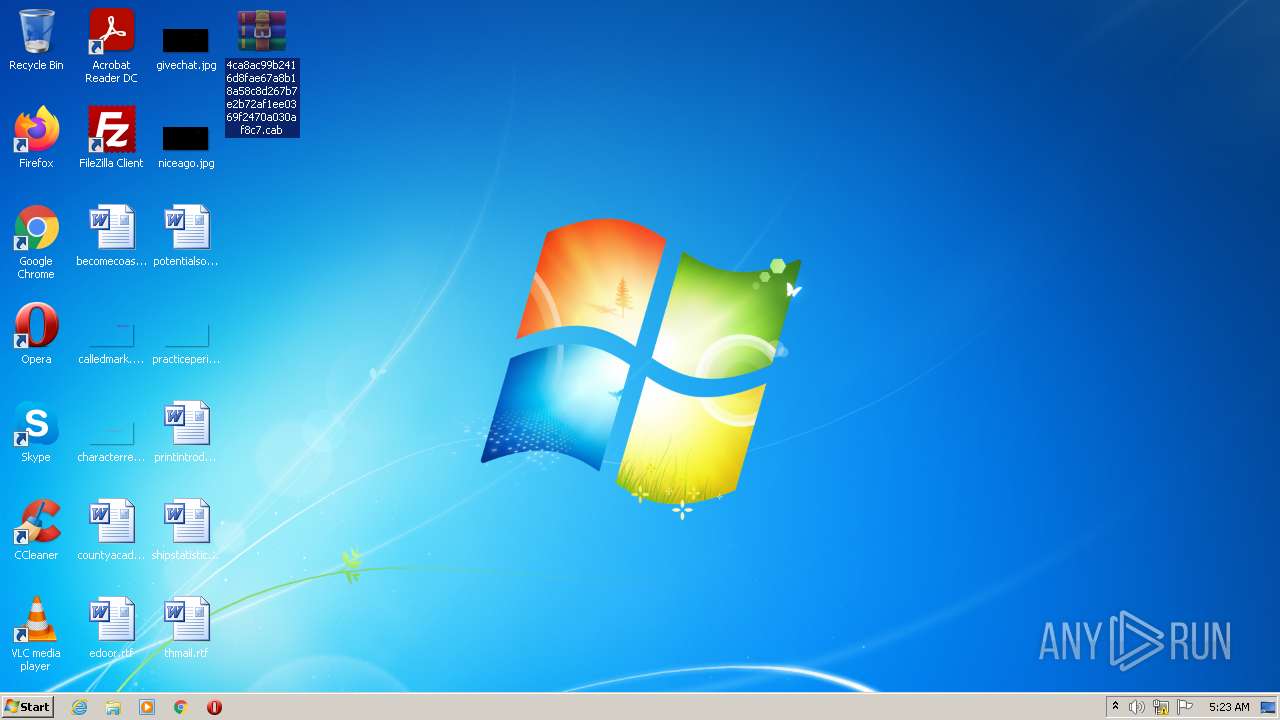
| 1252 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1252.49049\install.bat | text | |
MD5:— | SHA256:— | |||
| 3760 | WinRAR.exe | C:\Users\admin\Desktop\install.bat | text | |
MD5:— | SHA256:— | |||
| 3760 | WinRAR.exe | C:\Users\admin\Desktop\scrnsvc.ini | binary | |
MD5:— | SHA256:— | |||
| 3060 | cmd.exe | C:\Windows\System32\scrnsvc.dll | executable | |
MD5:57A22E74BA27B034613B0C6AC54A10D5 | SHA256:A3CD08AFD7317D1619FBA83C109F268B4B60429B4EB7C97FC274F92FF4FE17A2 | |||
| 3760 | WinRAR.exe | C:\Users\admin\Desktop\scrnsvc.dll | executable | |
MD5:57A22E74BA27B034613B0C6AC54A10D5 | SHA256:A3CD08AFD7317D1619FBA83C109F268B4B60429B4EB7C97FC274F92FF4FE17A2 | |||
| 1252 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1252.49049\scrnsvc.ini | binary | |
MD5:— | SHA256:— | |||
| 1252 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1252.49049\scrnsvc.dll | executable | |
MD5:57A22E74BA27B034613B0C6AC54A10D5 | SHA256:A3CD08AFD7317D1619FBA83C109F268B4B60429B4EB7C97FC274F92FF4FE17A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report