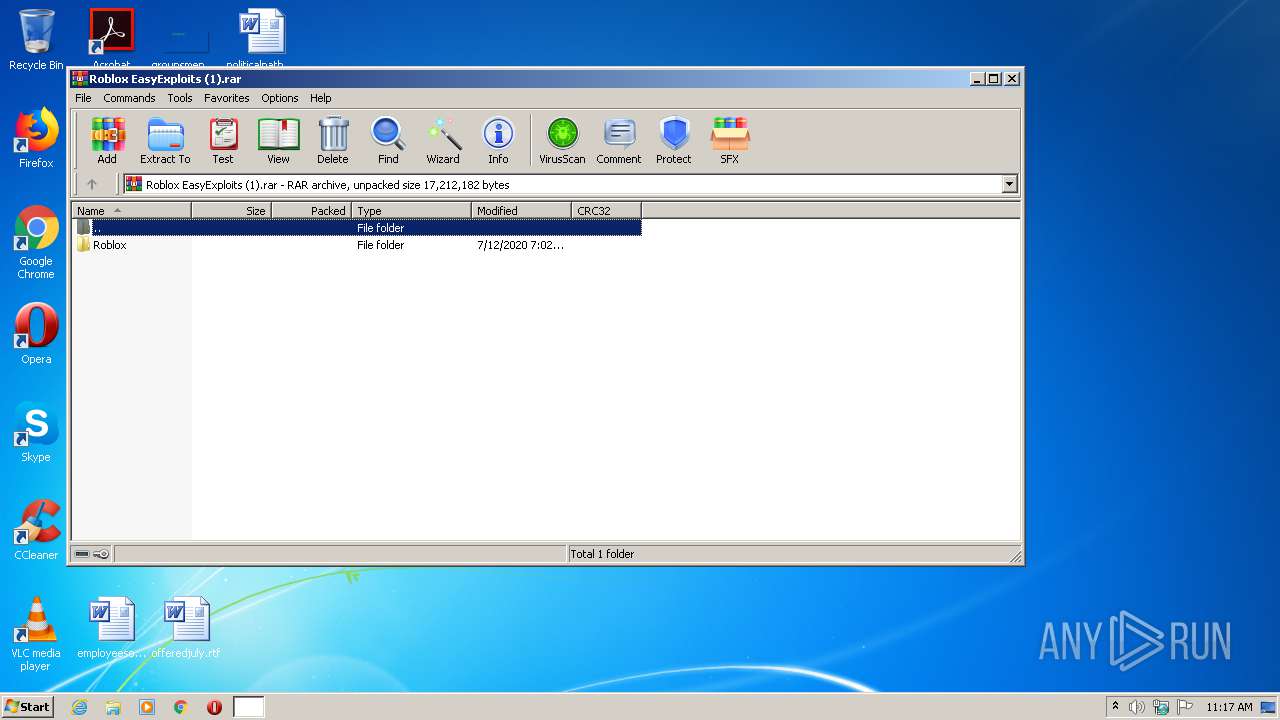
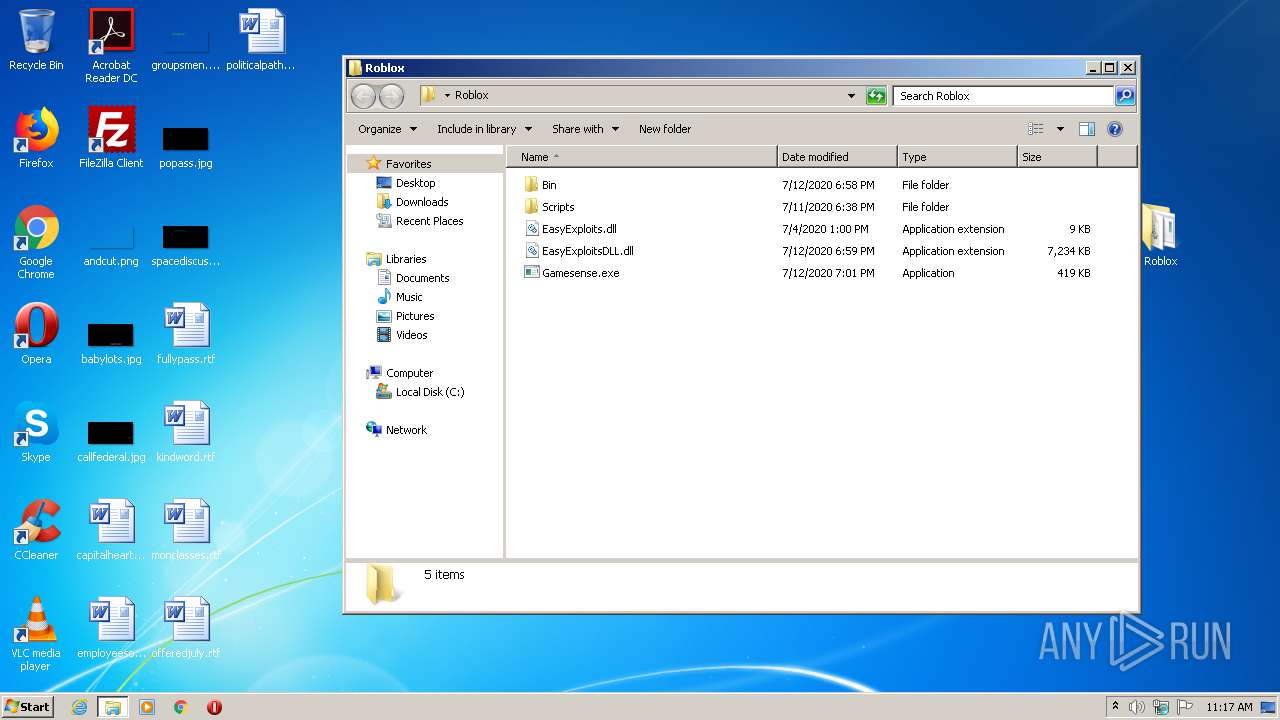
| File name: | Roblox EasyExploits (1).rar |
| Full analysis: | https://app.any.run/tasks/cc826e7d-1f2a-40ed-934d-bde85dc97cb0 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2020, 10:17:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5AD305309EEDEB4F33EF7963020C5FC3 |
| SHA1: | B642B77843B4756298DAFE91E2461741DB13B13B |
| SHA256: | 4CA7885FA203EC8C24078EC63305DFD128D12B068AA39F14E6DF885B5A1B2317 |
| SSDEEP: | 196608:DybiYQRaK7/Tg4+4vBtXp2XYBw+FFY92YtsbTNCx:DyQYY/Tgav3XpvBwmmXGg |
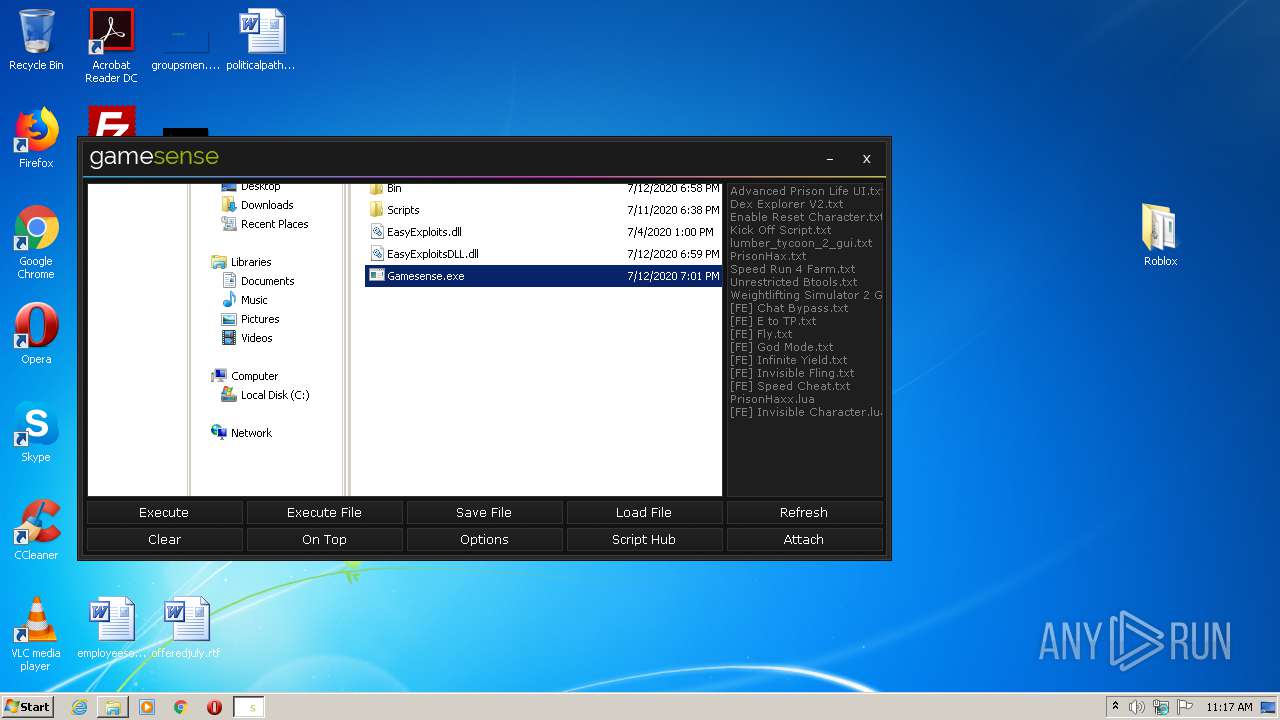
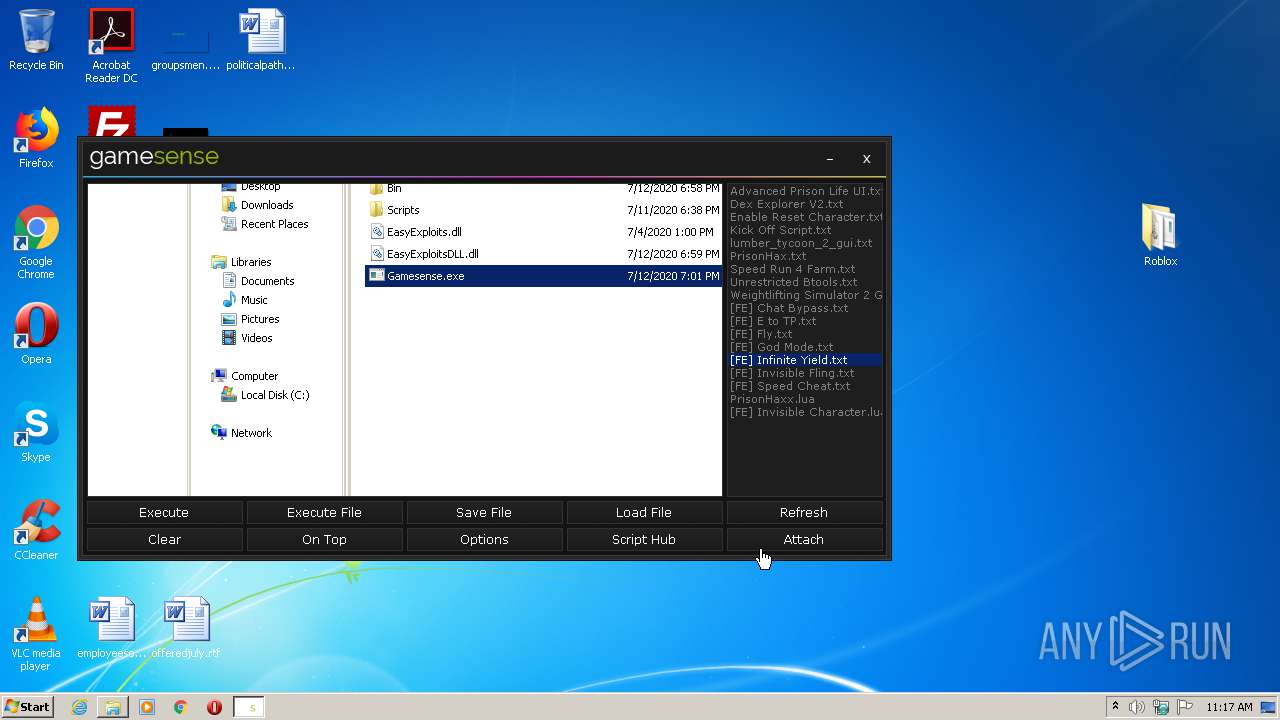
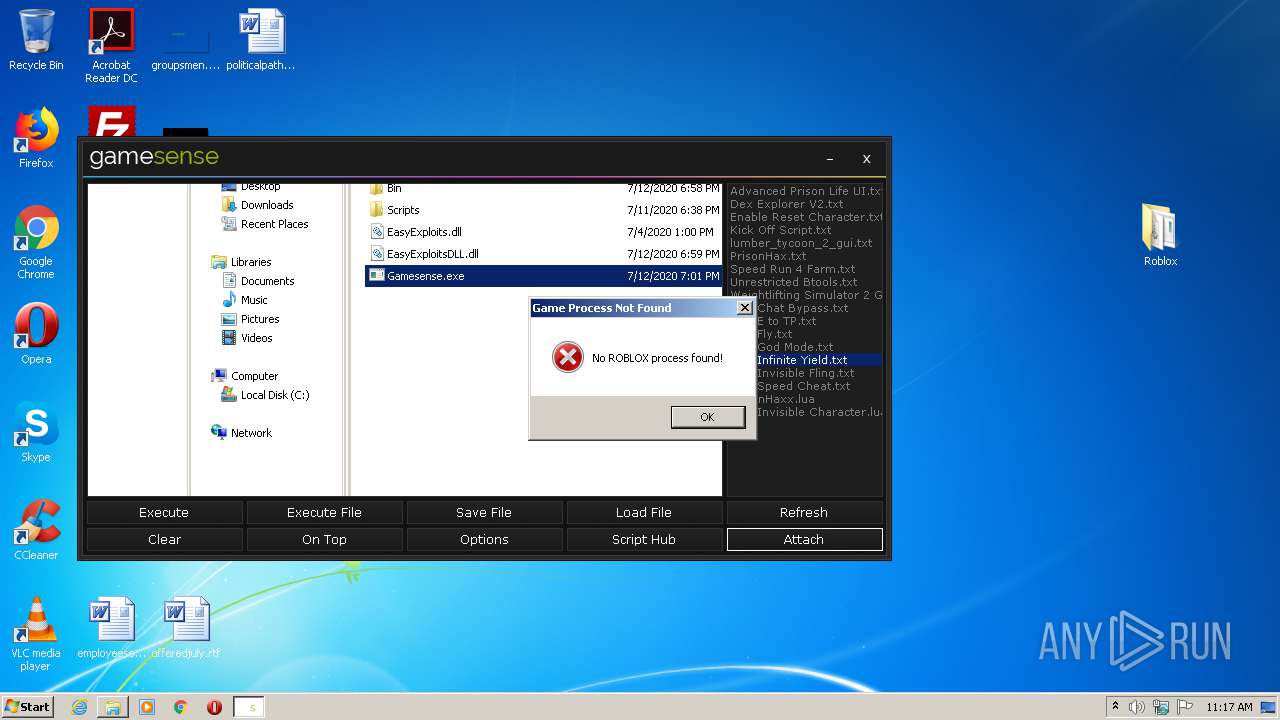
MALICIOUS
Application was dropped or rewritten from another process
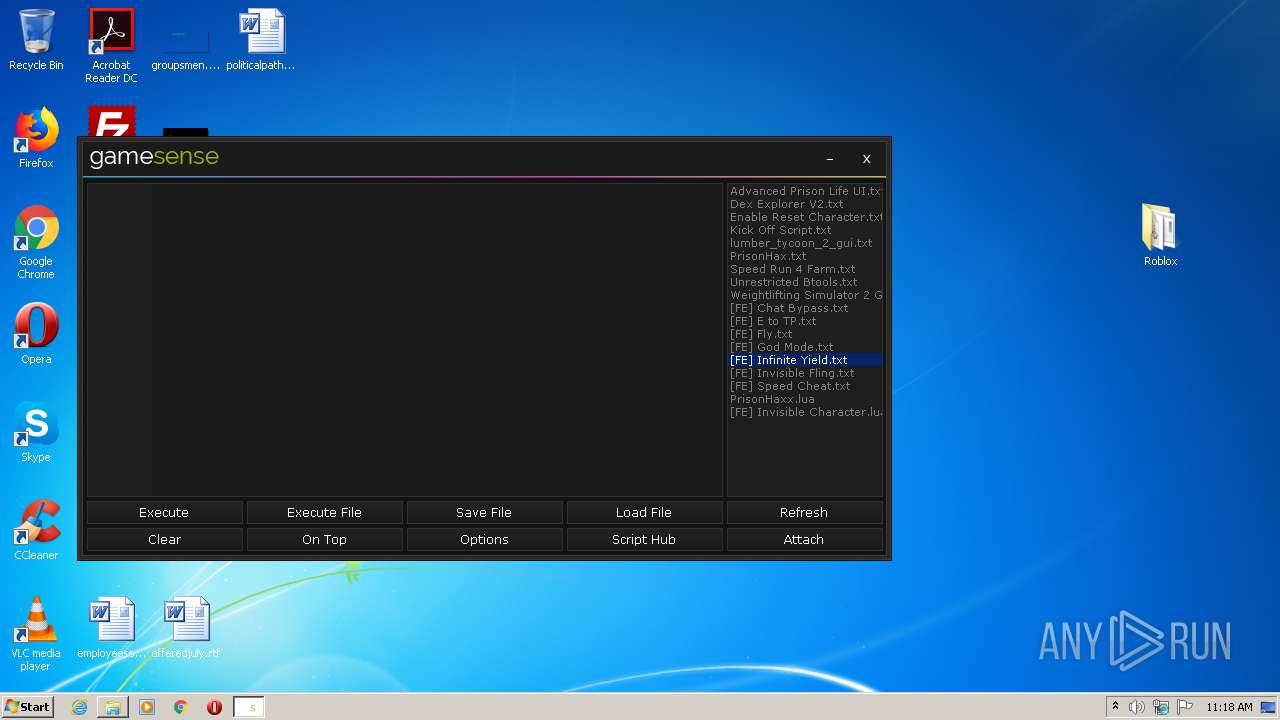
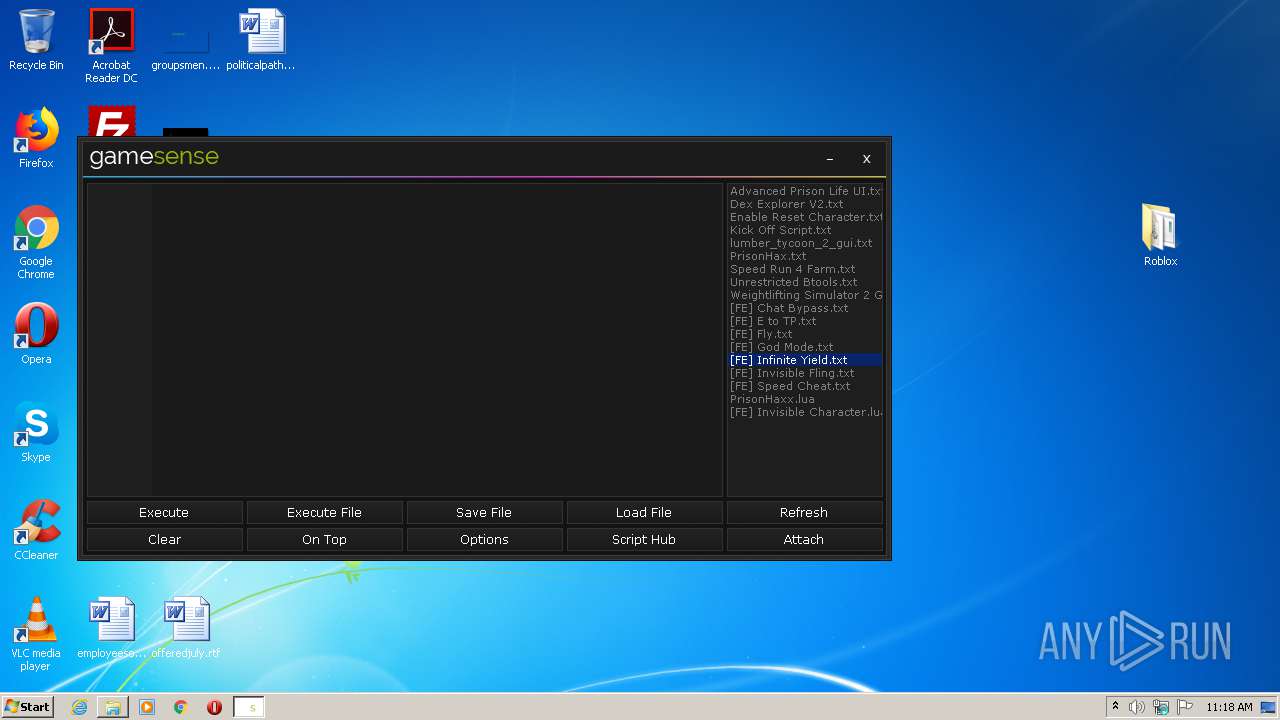
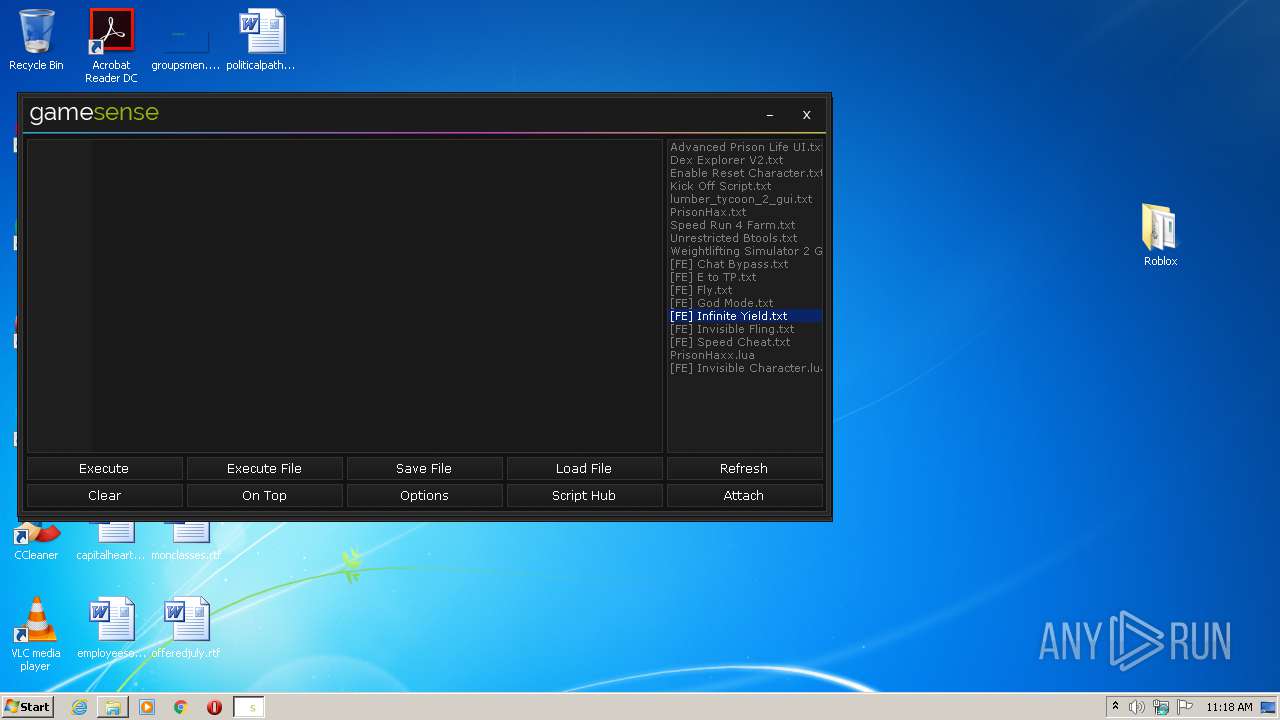
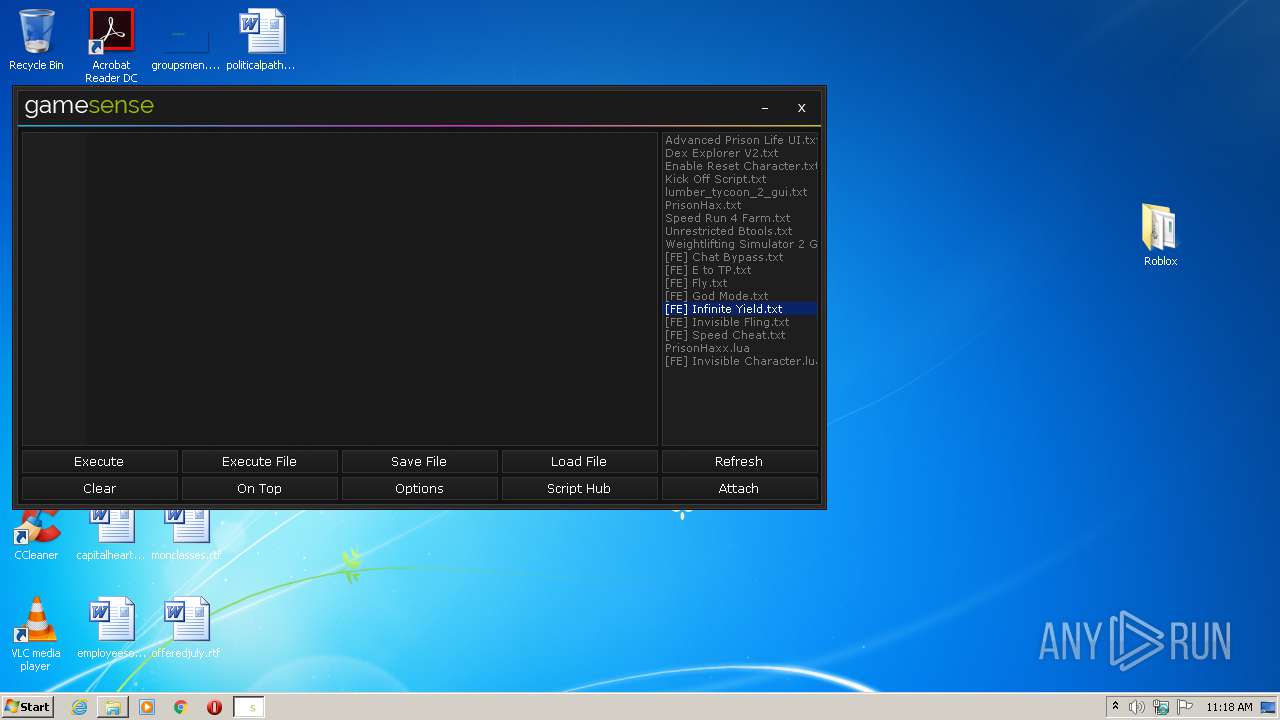
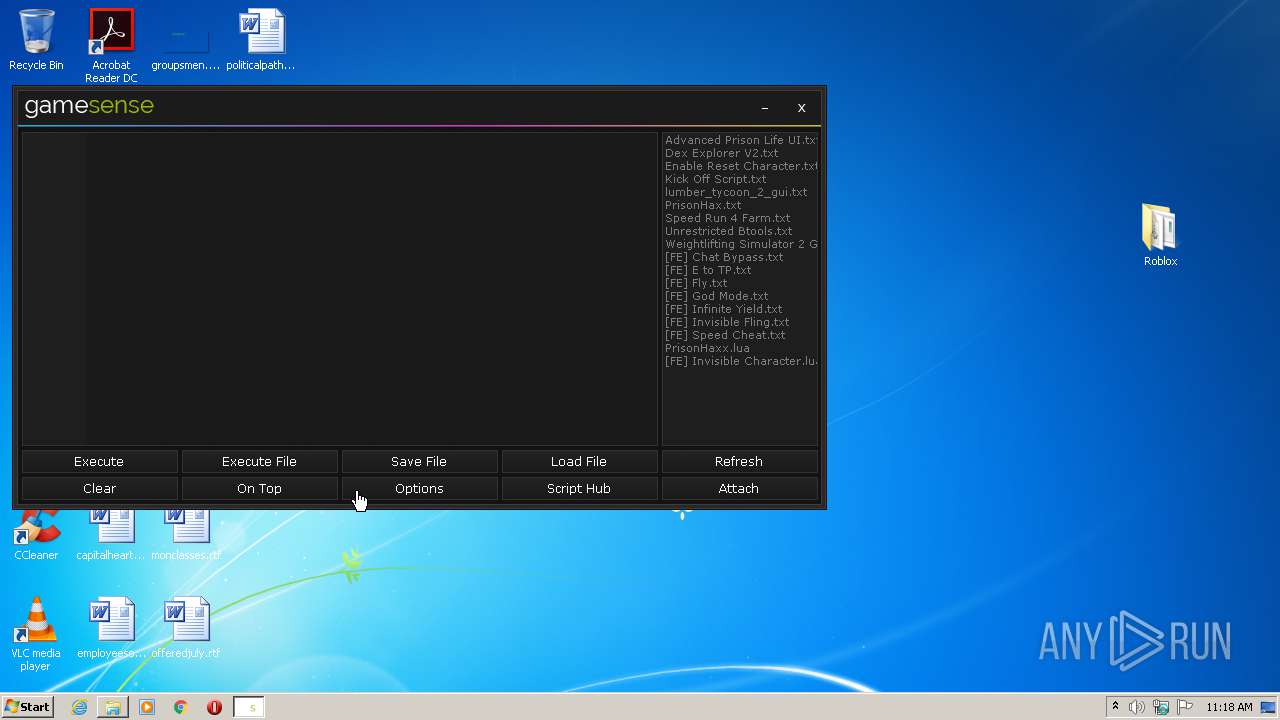
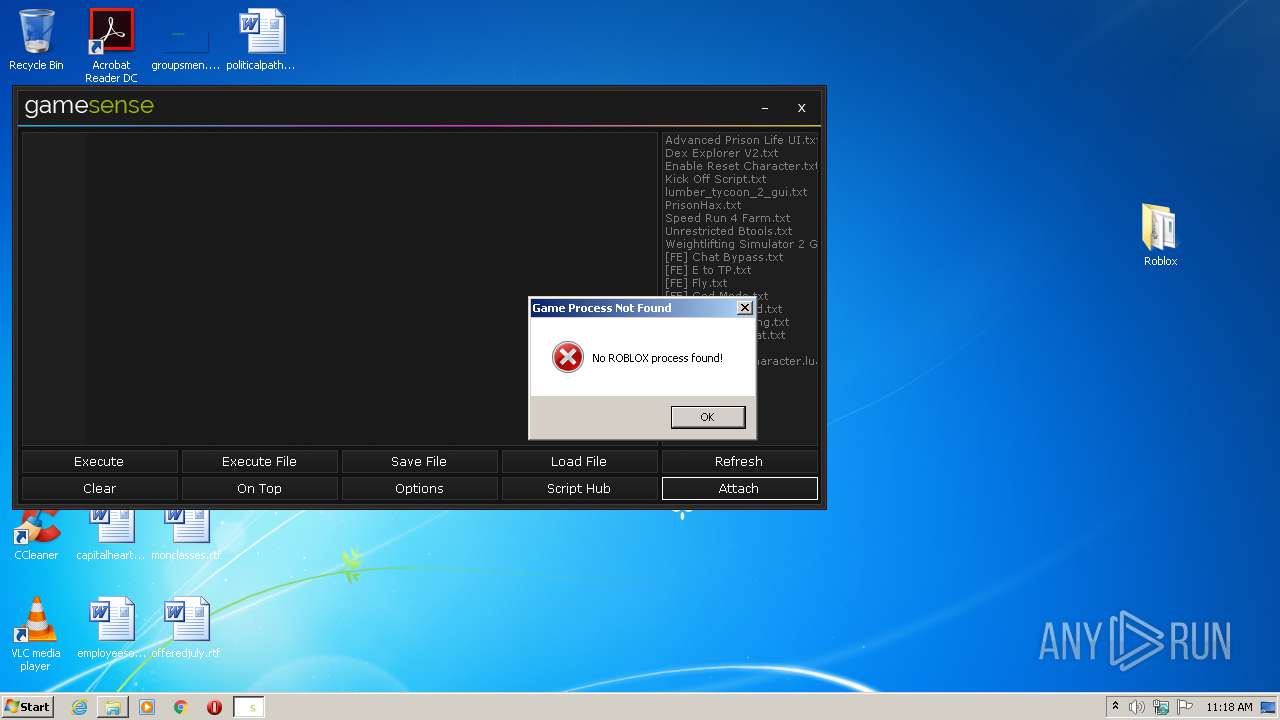
- Gamesense.exe (PID: 3868)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3460)
SUSPICIOUS
Reads internet explorer settings
- Gamesense.exe (PID: 3868)
Changes IE settings (feature browser emulation)
- Gamesense.exe (PID: 3868)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1008)
- Gamesense.exe (PID: 3868)
Reads Internet Cache Settings
- Gamesense.exe (PID: 3868)
INFO
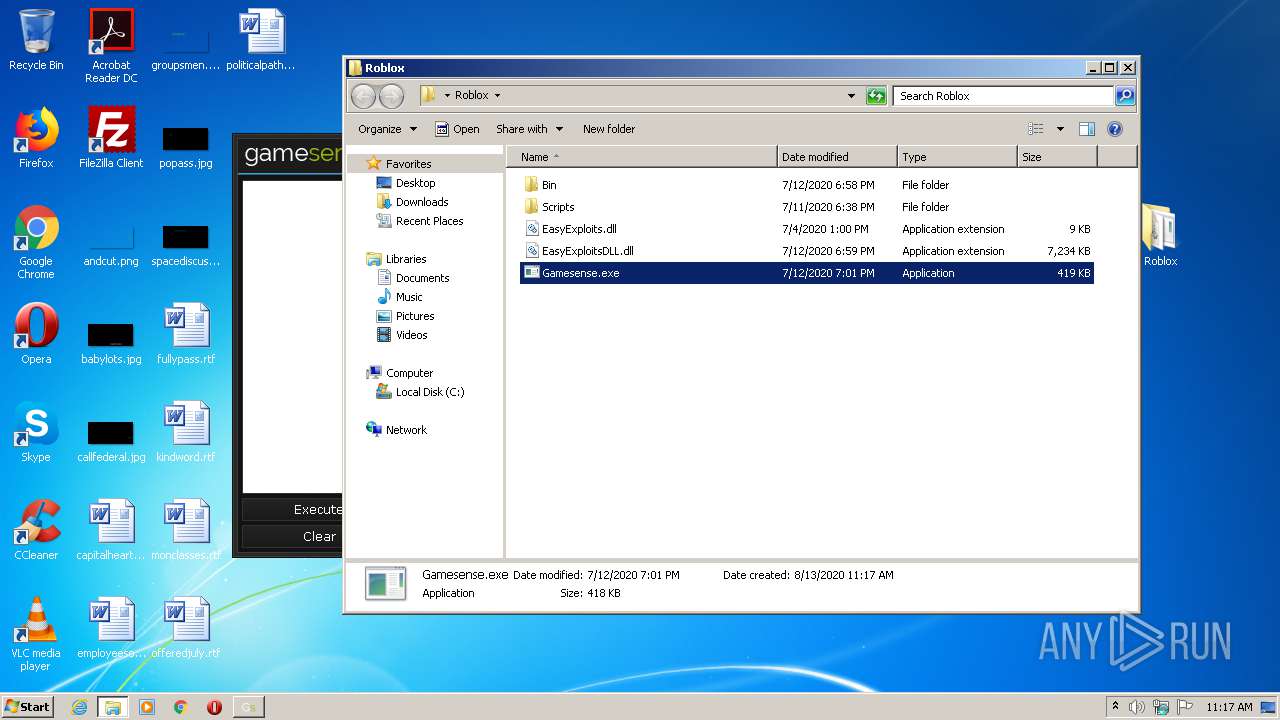
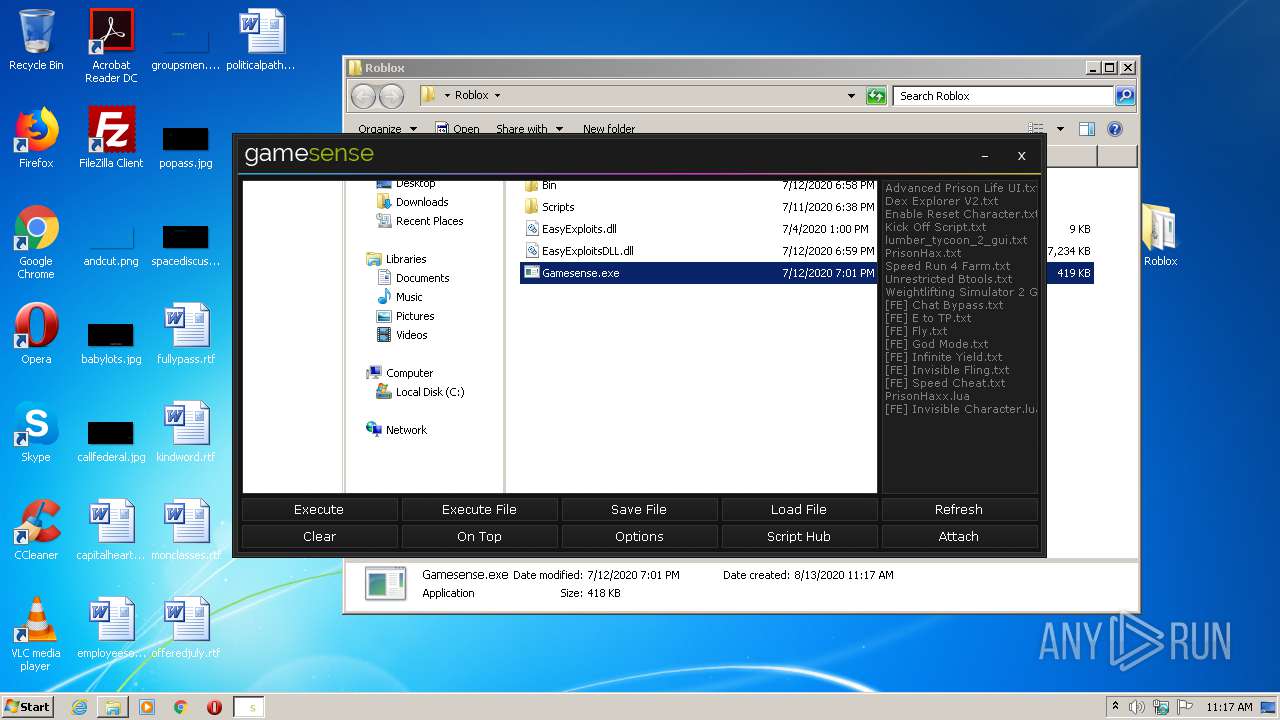
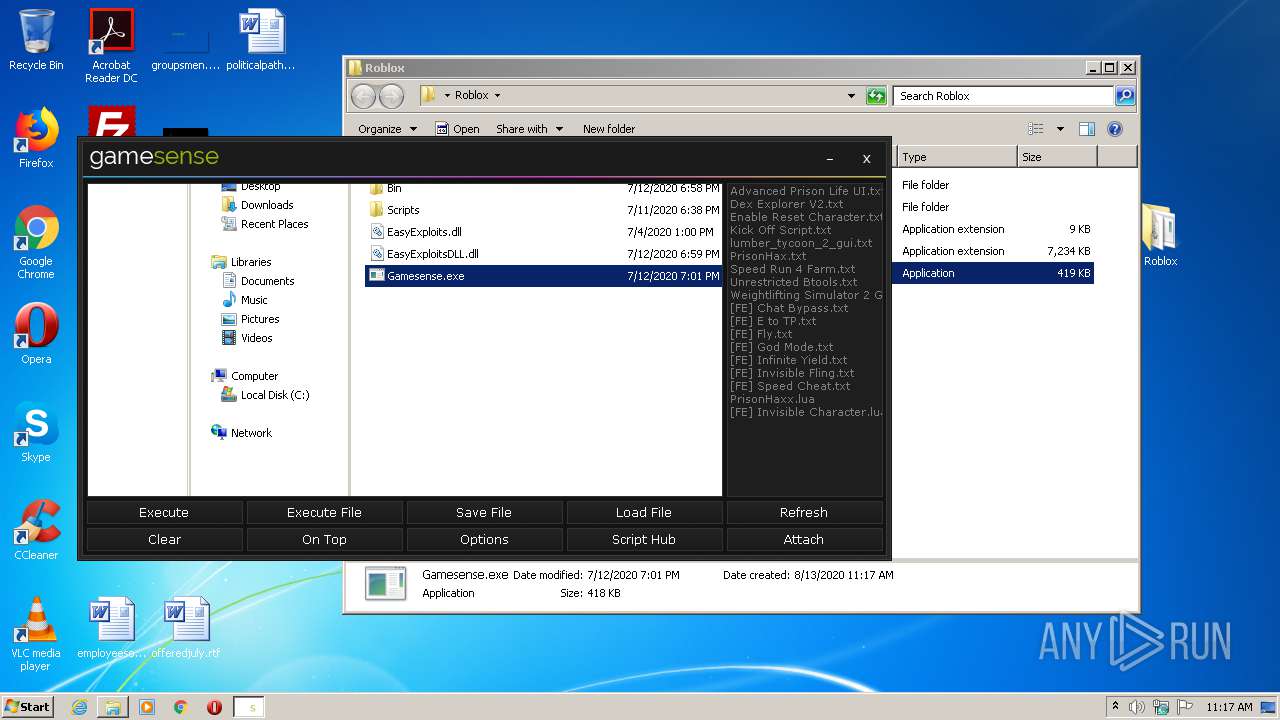
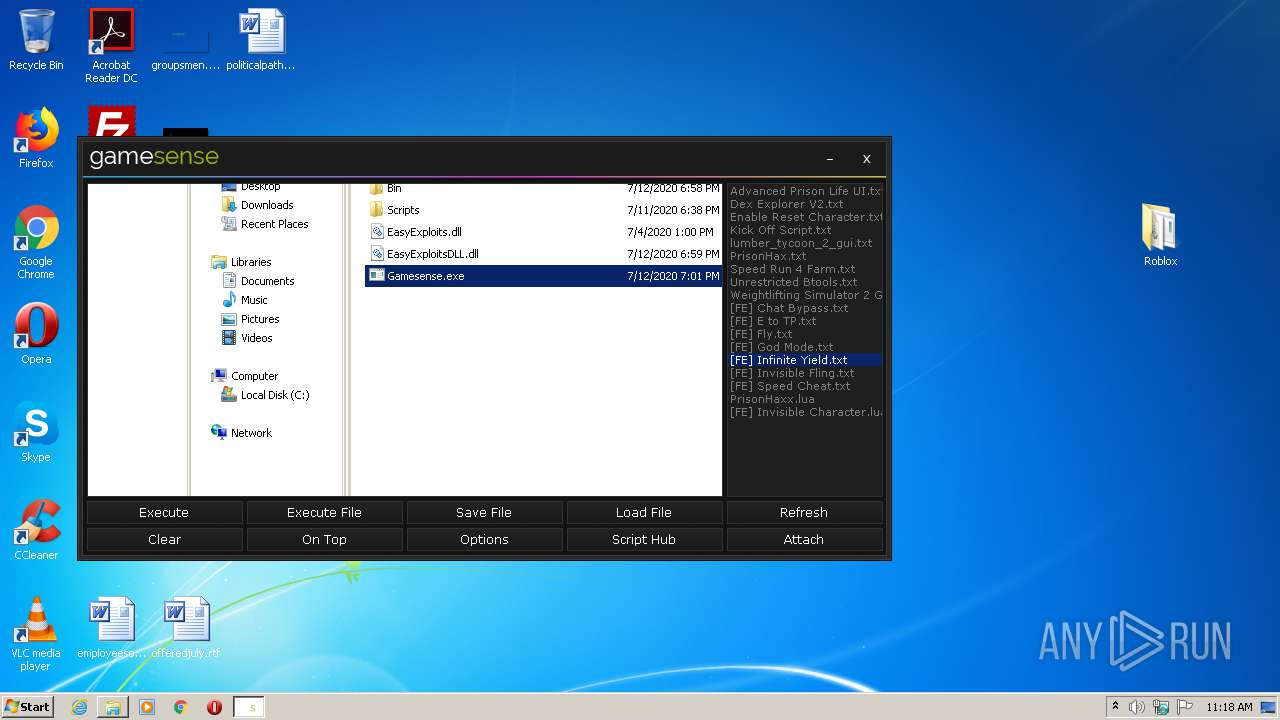
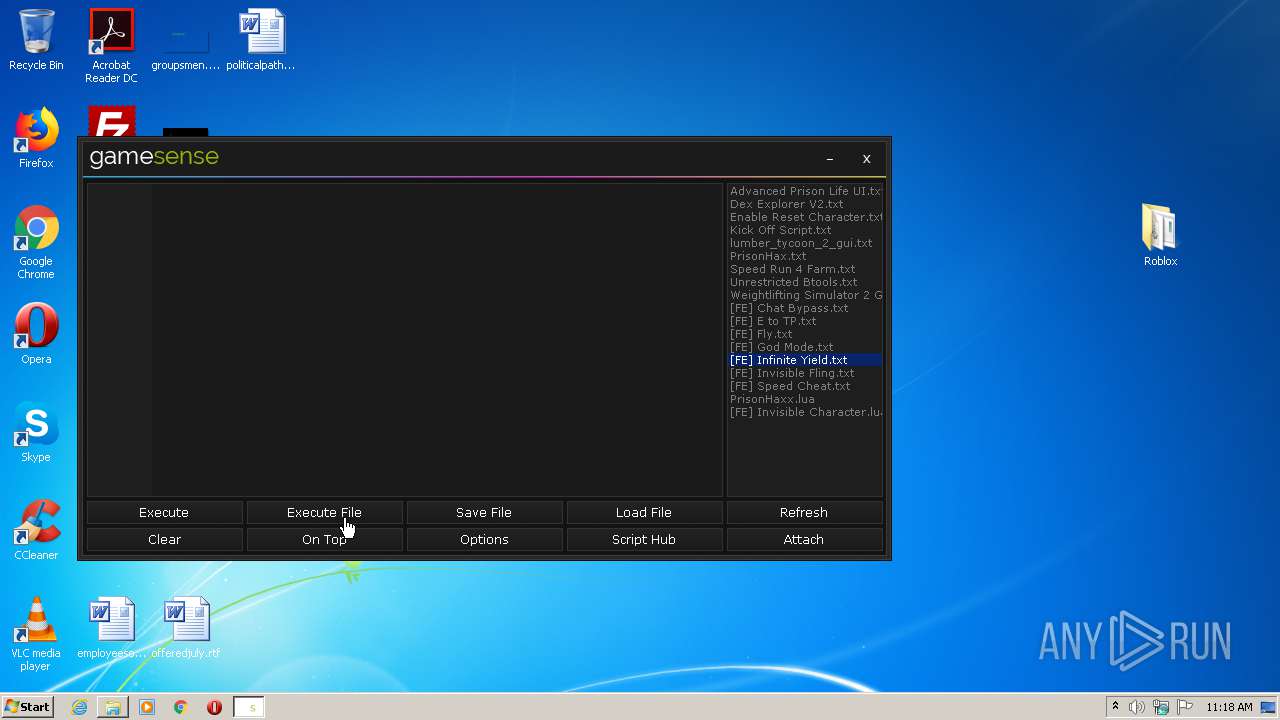
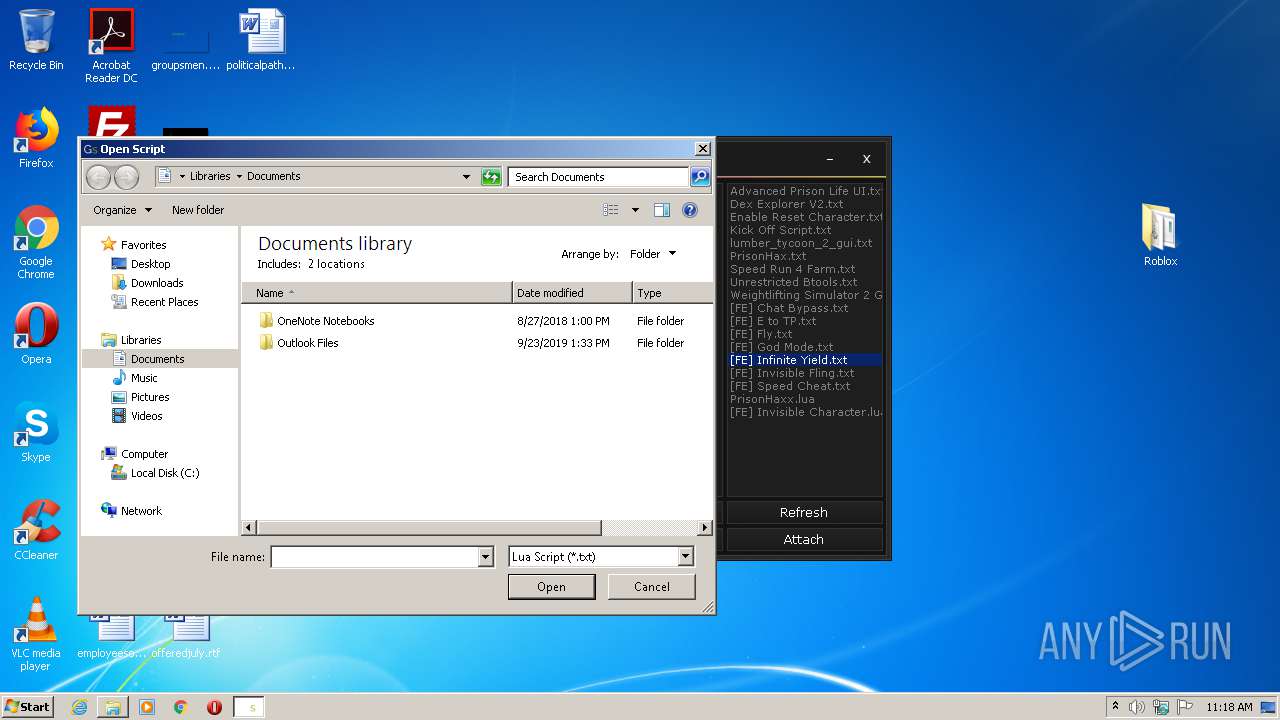
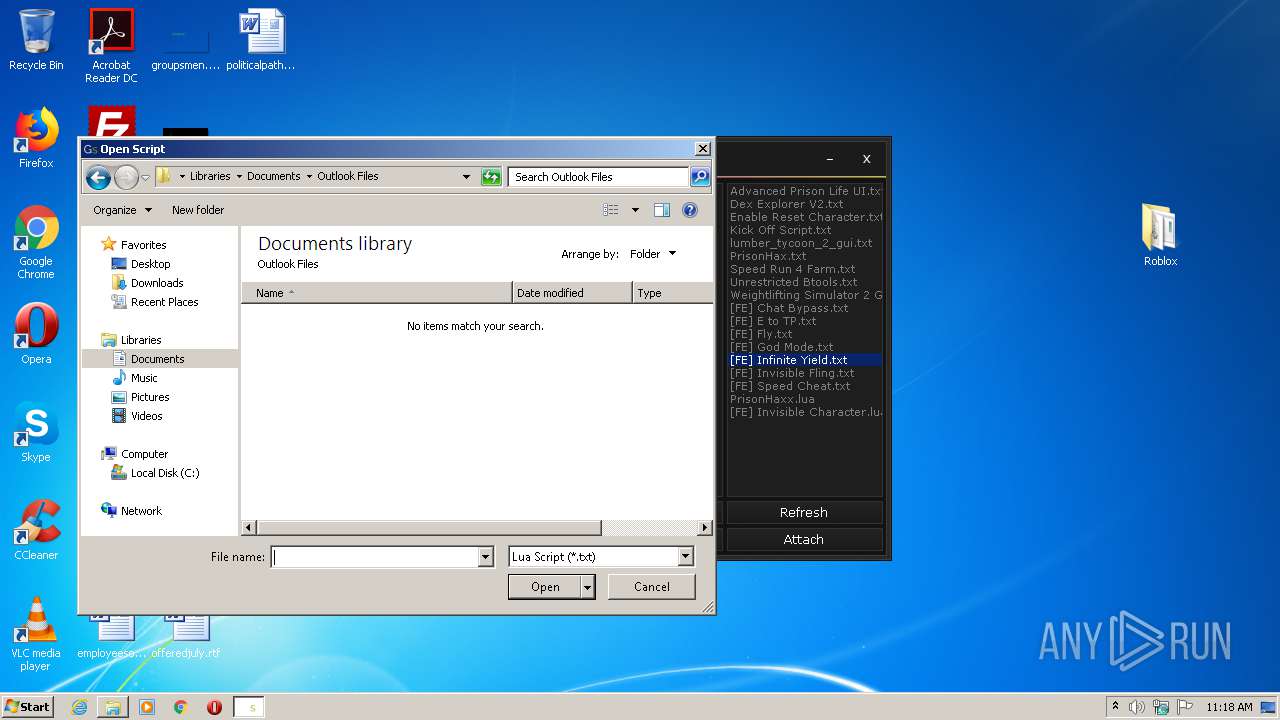
Manual execution by user
- Gamesense.exe (PID: 3868)
Reads settings of System Certificates
- Gamesense.exe (PID: 3868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
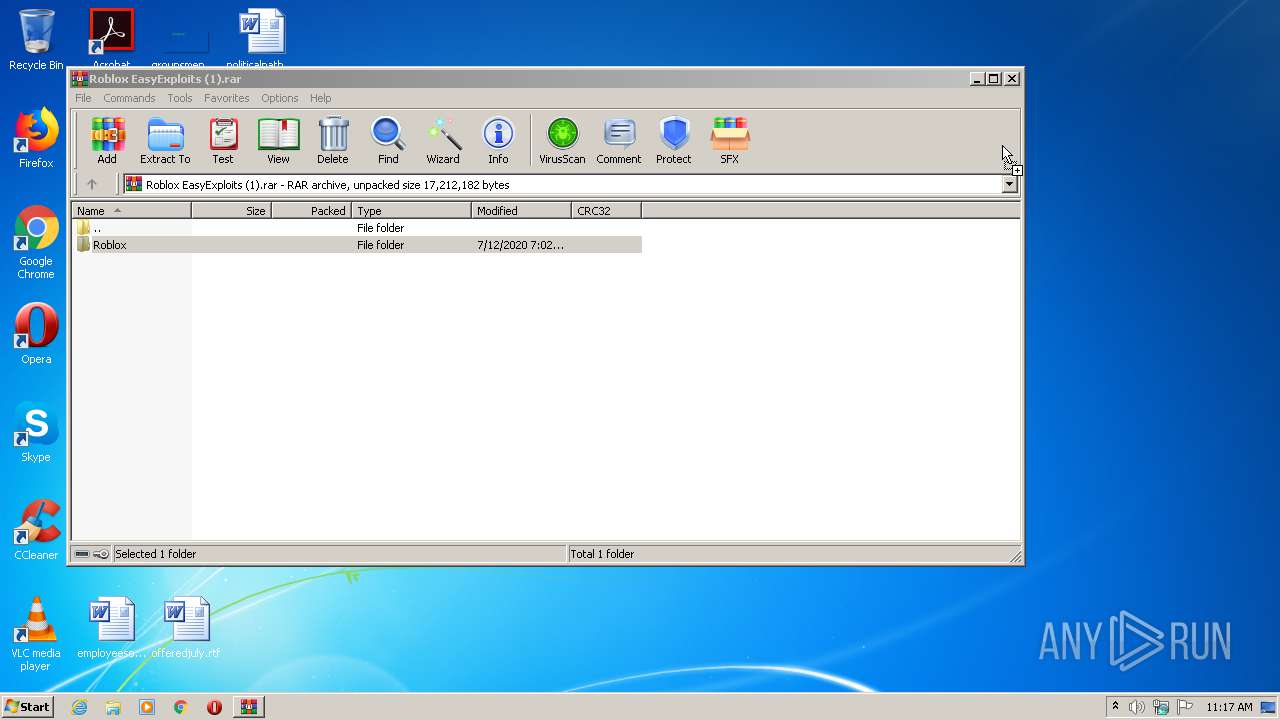
| 1008 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Roblox EasyExploits (1).rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3460 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3868 | "C:\Users\admin\Desktop\Roblox\Gamesense.exe" | C:\Users\admin\Desktop\Roblox\Gamesense.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Gamesense Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 548
Read events
1 393
Write events
152
Delete events
3
Modification events
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Roblox EasyExploits (1).rar | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
5
Suspicious files
6
Text files
87
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.18141\Roblox\Bin\FpsUnlocker.exe | executable | |
MD5:— | SHA256:— | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.18141\Roblox\Bin\Monaco\vs\basic-languages\cpp\cpp.js | text | |
MD5:0A16509E6CD0155FB622E785CFE976C7 | SHA256:A7C2BEA7CA3D9E203A3A286735945FE010C8F4F8D46620386EE8BEFC6A78B32B | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.18141\Roblox\Bin\Monaco\vs\basic-languages\coffee\coffee.js | text | |
MD5:9D0C4AC1691EED0A480C3E9246490D29 | SHA256:E706C9F8E5C5A0CB01B2F4E4879EC34A050D6EB2A8840284EB7BADD9D78099F9 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.18141\Roblox\Bin\Monaco\Monaco.html | html | |
MD5:— | SHA256:— | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.18141\Roblox\Bin\Monaco\vs\basic-languages\markdown\markdown.js | text | |
MD5:CAF4799639D5DF40DFB1B979ED68AF9C | SHA256:EAAF453E0A9F9A604547E564A24E682503189CB9B85C87715BC9B5B6492B6F62 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.18141\Roblox\Bin\Monaco\vs\basic-languages\lua\lua.js | text | |
MD5:8706D861294E09A1F2F7E63D19E5FCB7 | SHA256:FC2D6FB52A524A56CD8AC53BFE4BAD733F246E76DC73CBEC4C61BE32D282AC42 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.18141\Roblox\Bin\Monaco\vs\basic-languages\csharp\csharp.js | text | |
MD5:F8F841D13C9220E15DCD6BC386B37BA2 | SHA256:6B3BE9A86EE8E3202F51745D94D24CC1EEFBCF7D9E6D94FBAF70146B084E835F | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.18141\Roblox\Bin\Monaco\vs\basic-languages\java\java.js | text | |
MD5:826546E08F178D68E8AA2AB29194C03A | SHA256:44BE702CAE05D5844DC1C452F9BD94020007B9E543A765DB4E6649278607D218 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.18141\Roblox\Bin\Monaco\vs\basic-languages\ini\ini.js | text | |
MD5:B9252B74381FE17565D494711F4C9093 | SHA256:1F0FEEAE58C32F6E1F31B78F7E2AAB3C91DA387E464234C0F55EBFF0E77444A2 | |||
| 1008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1008.18141\Roblox\Bin\Monaco\vs\basic-languages\msdax\msdax.js | text | |
MD5:EAA7BFF8662633AEC211D57FD17CB8CE | SHA256:6AB13356E083C4334E93D3167BDD17D02552508BFD11EA044C880AF3A1DD94F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
6
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3868 | Gamesense.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
3868 | Gamesense.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 313 b | whitelisted |
3868 | Gamesense.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEDJAnJQUGG0bwuno3m2vDJ8%3D | US | der | 280 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3868 | Gamesense.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
3868 | Gamesense.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
— | — | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
3868 | Gamesense.exe | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
ocsp.comodoca.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |
raw.githubusercontent.com |
| shared |