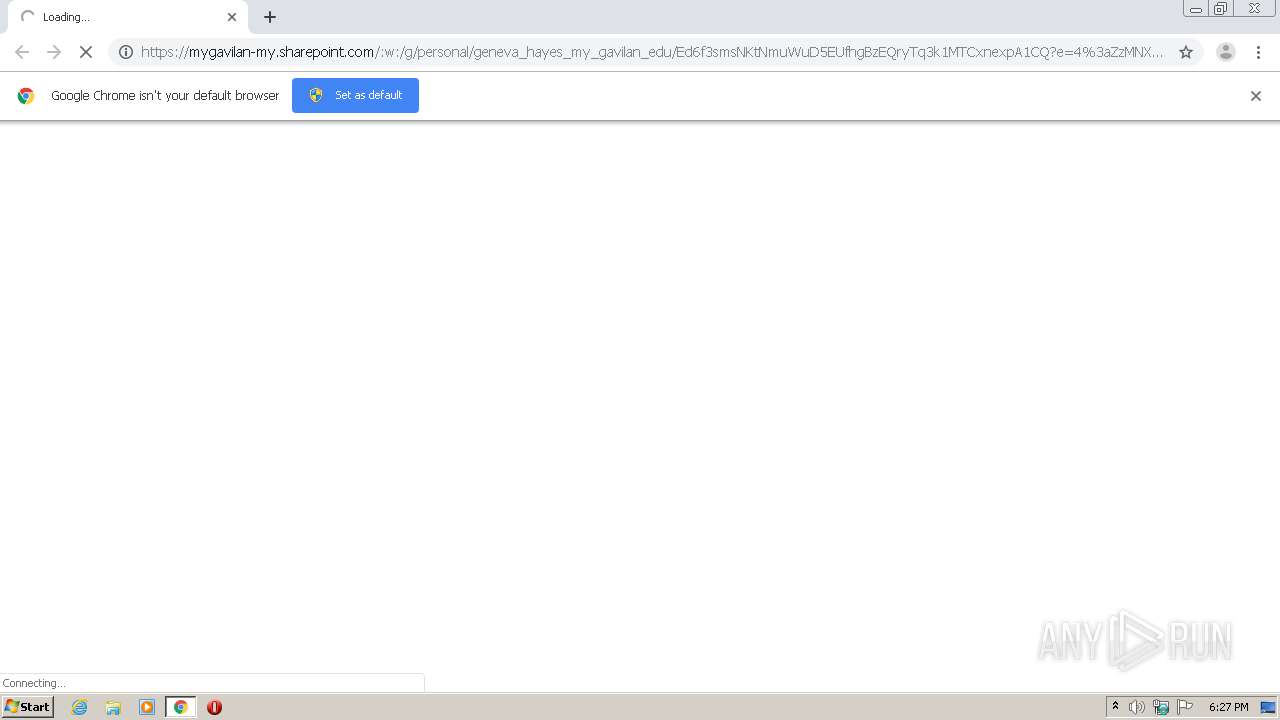
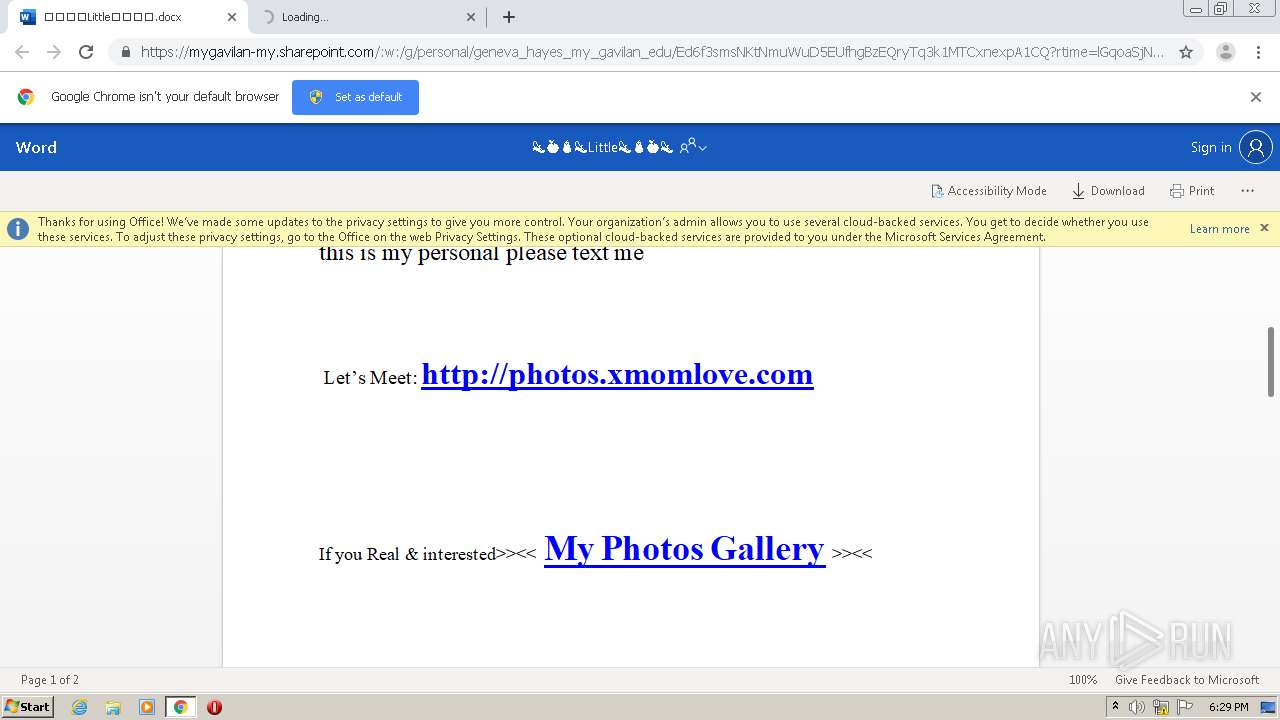
| URL: | https://mygavilan-my.sharepoint.com/:w:/g/personal/geneva_hayes_my_gavilan_edu/Ed6f3smsNKtNmuWuD5EUfhgBzEQryTq3k1MTCxnexpA1CQ?e=4%3aZzMNXE&at=9 |
| Full analysis: | https://app.any.run/tasks/302889da-5a61-47f3-86b6-9f8caa3d69a3 |
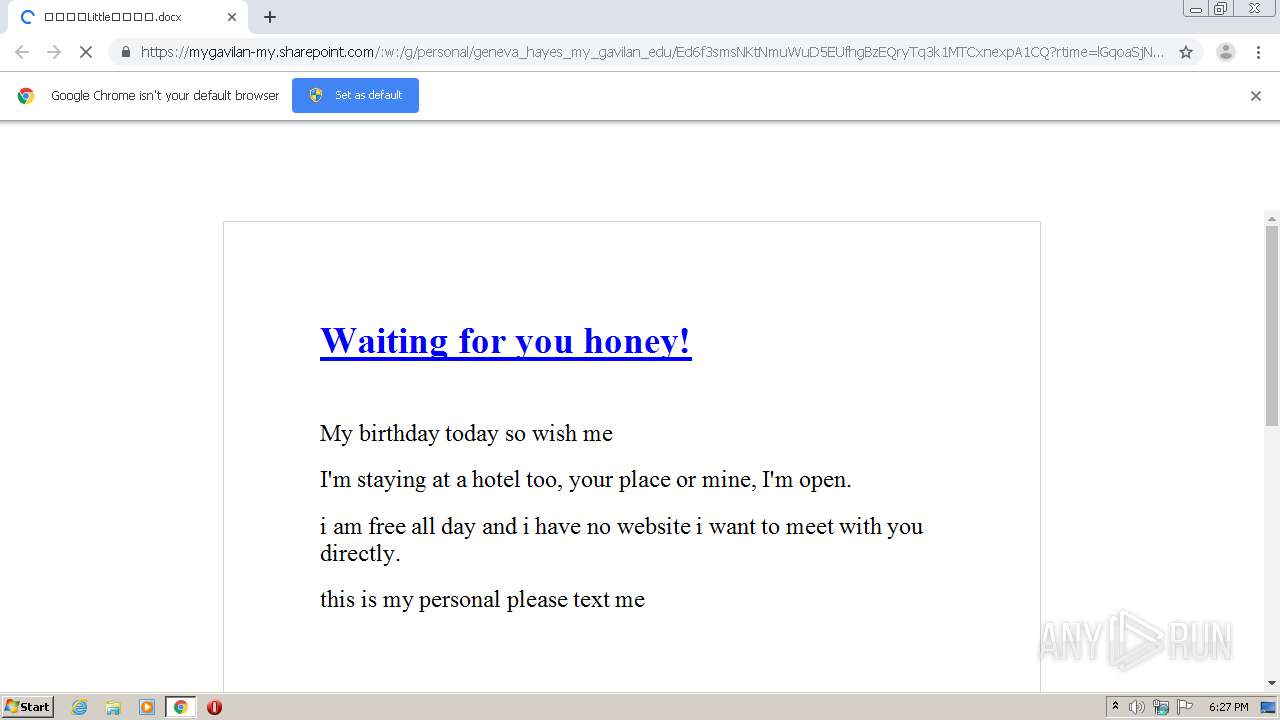
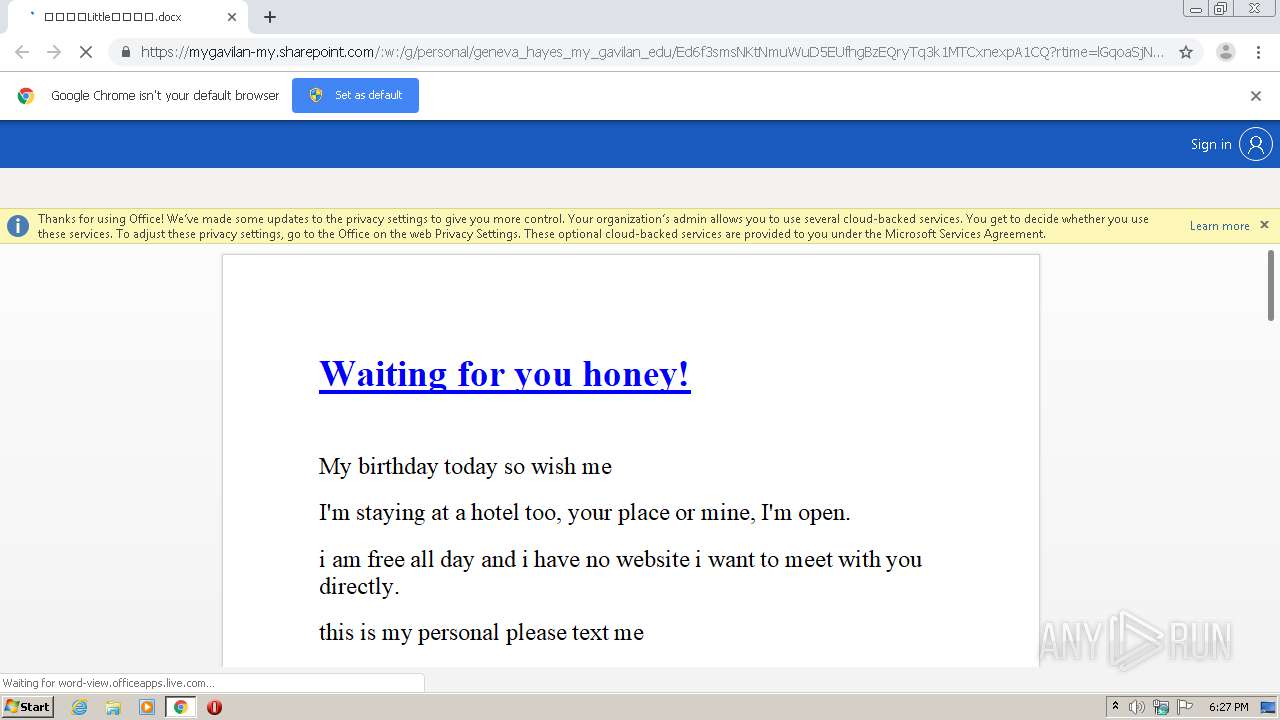
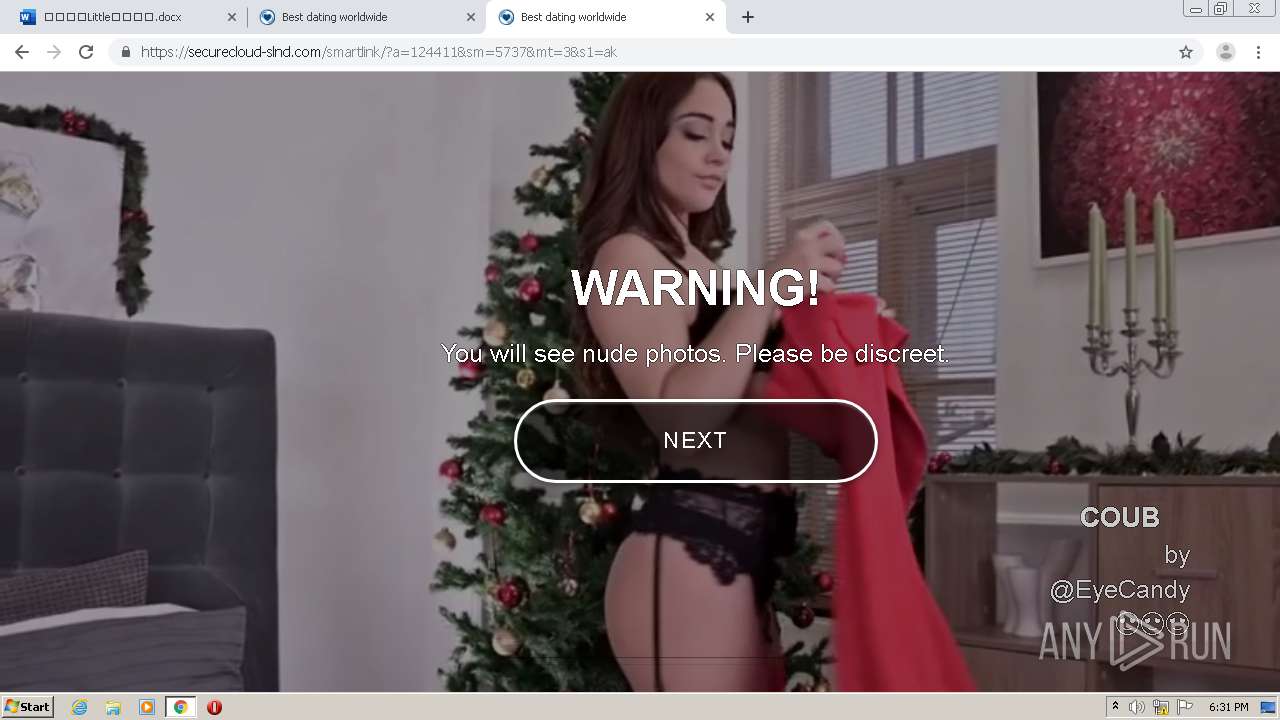
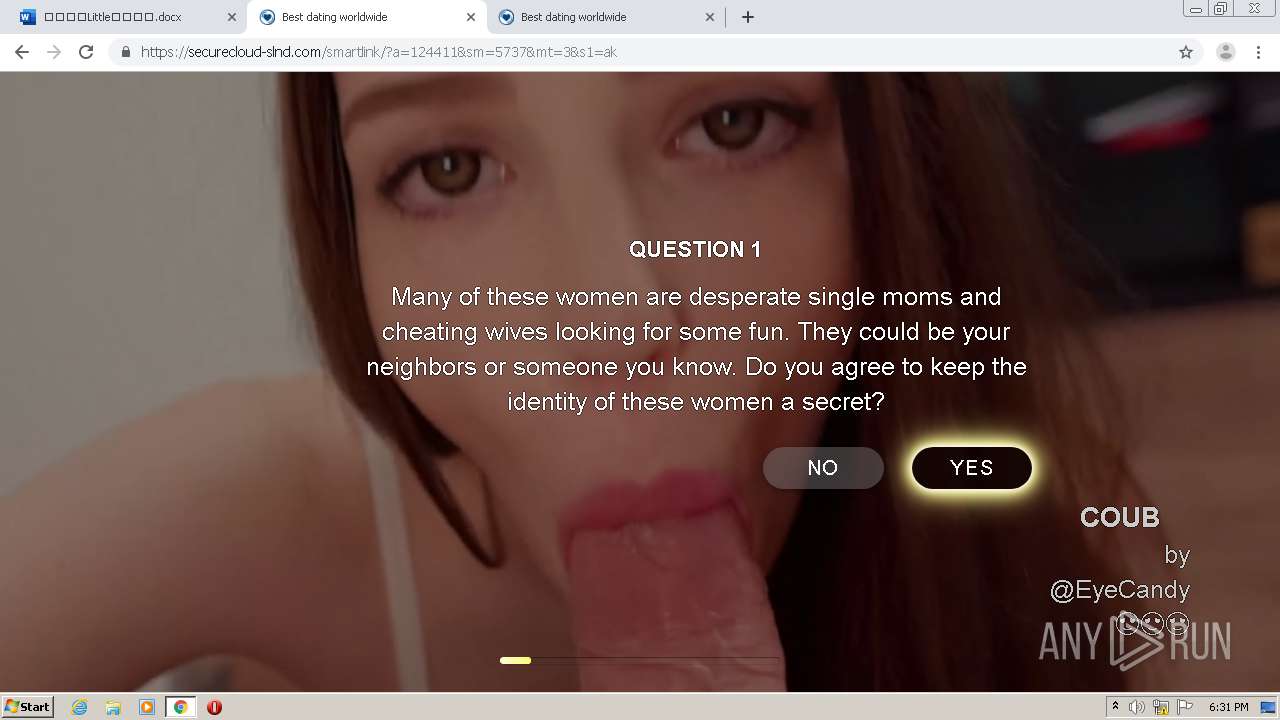
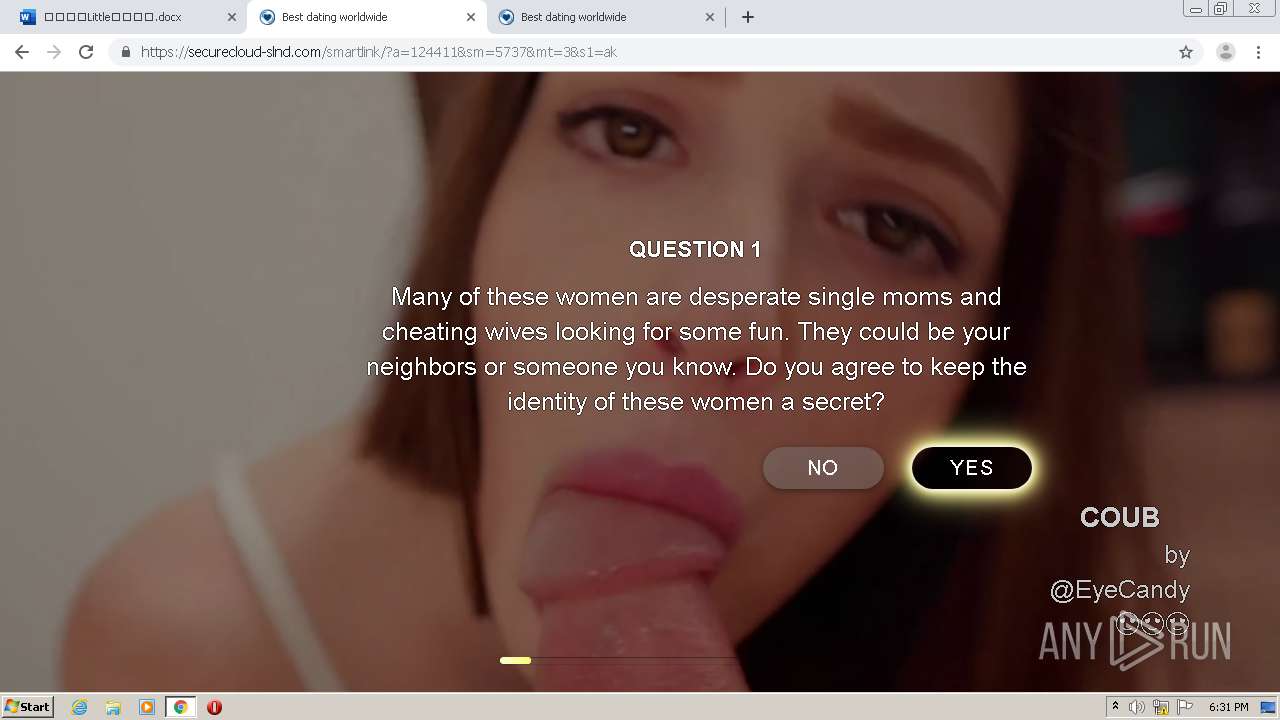
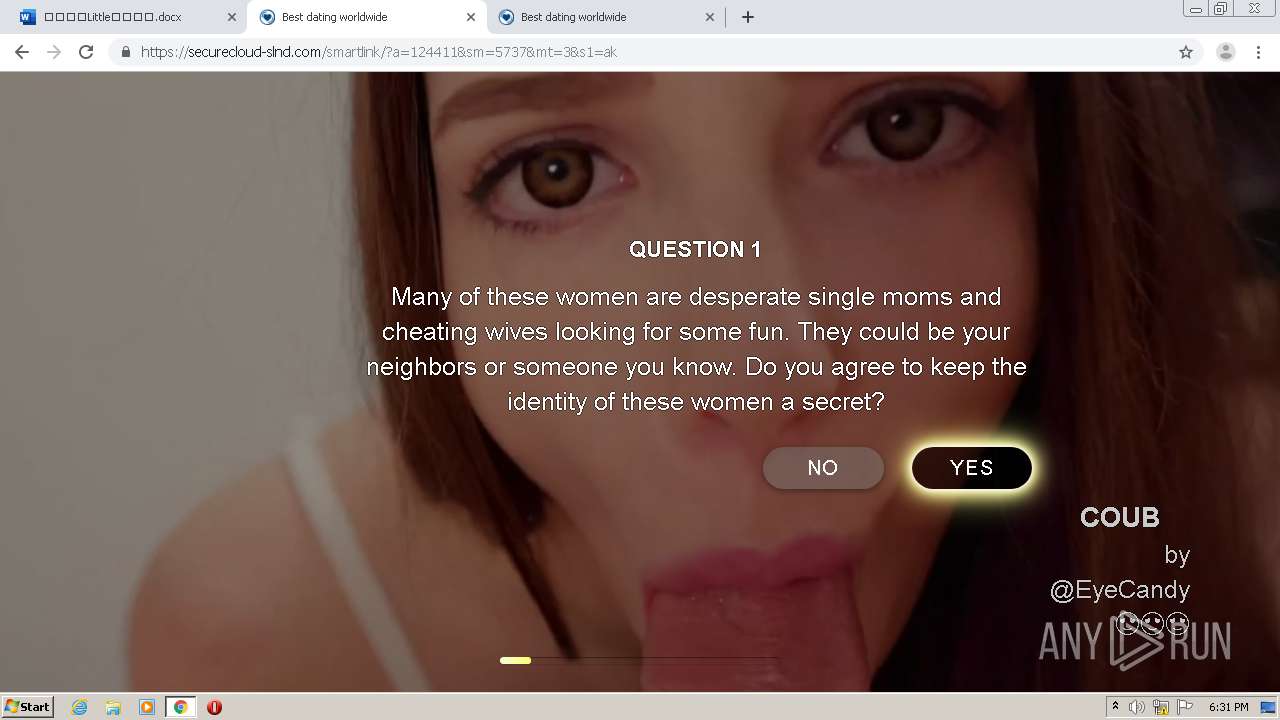
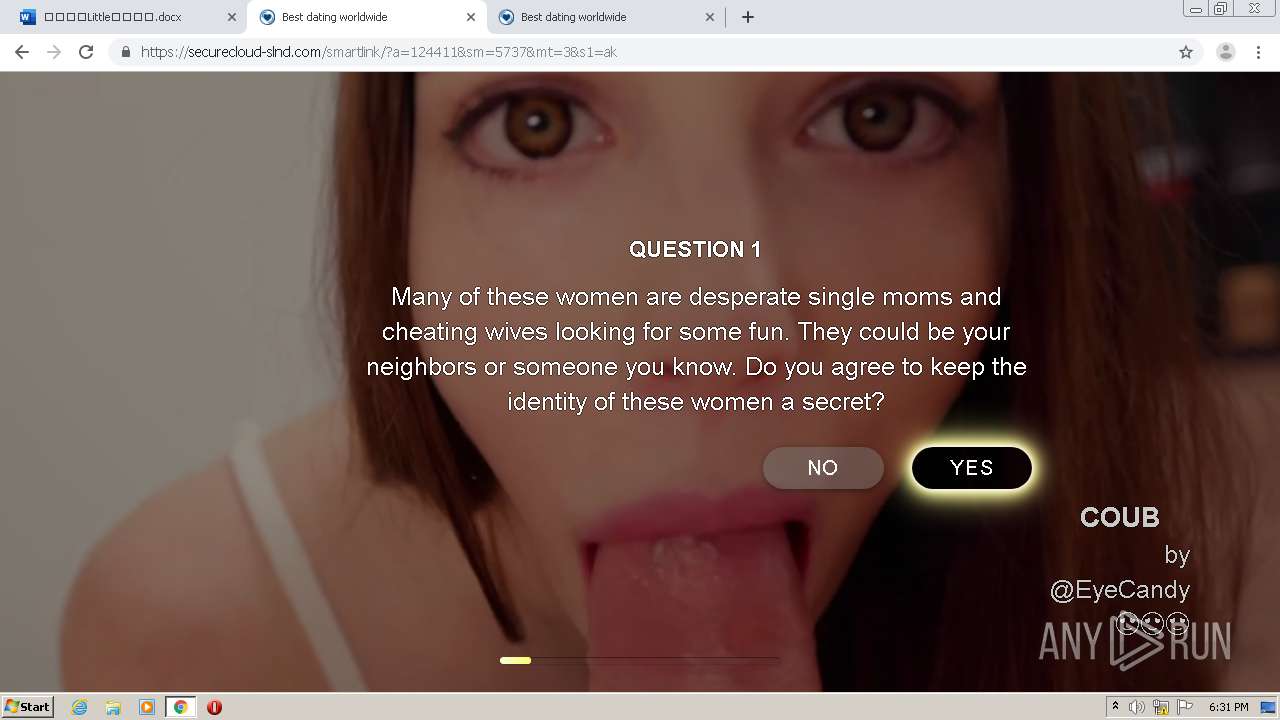
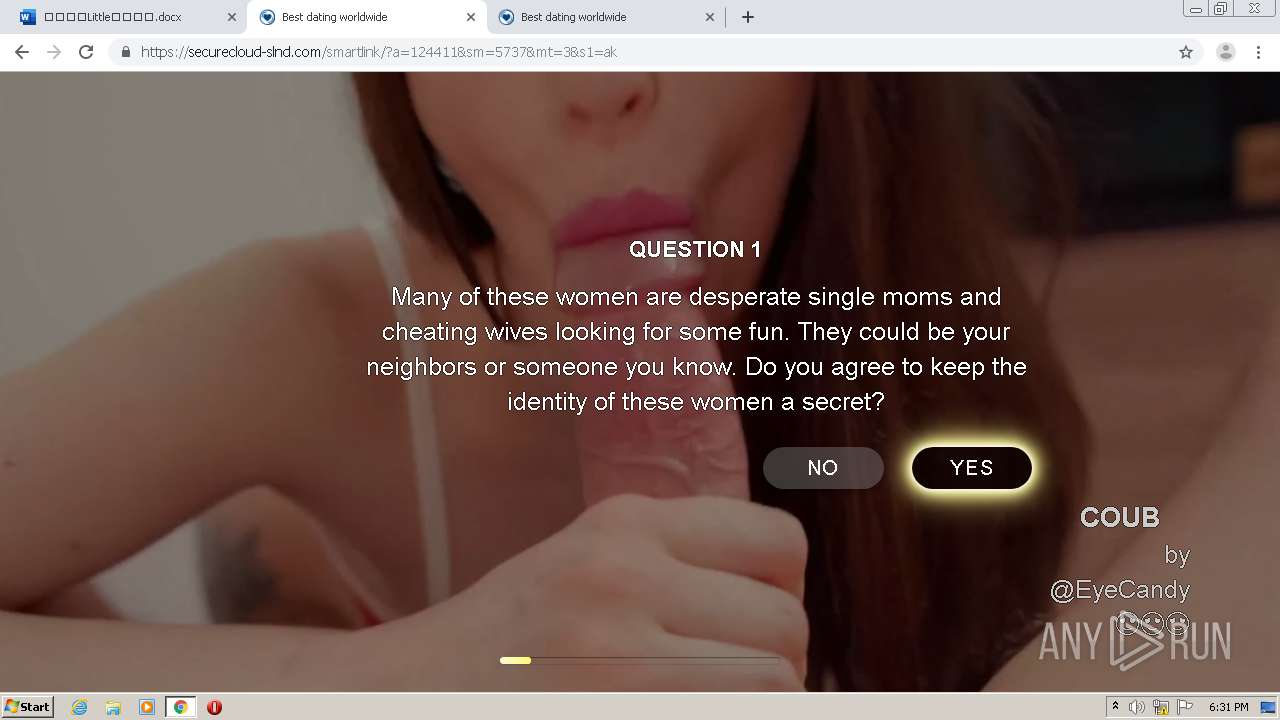
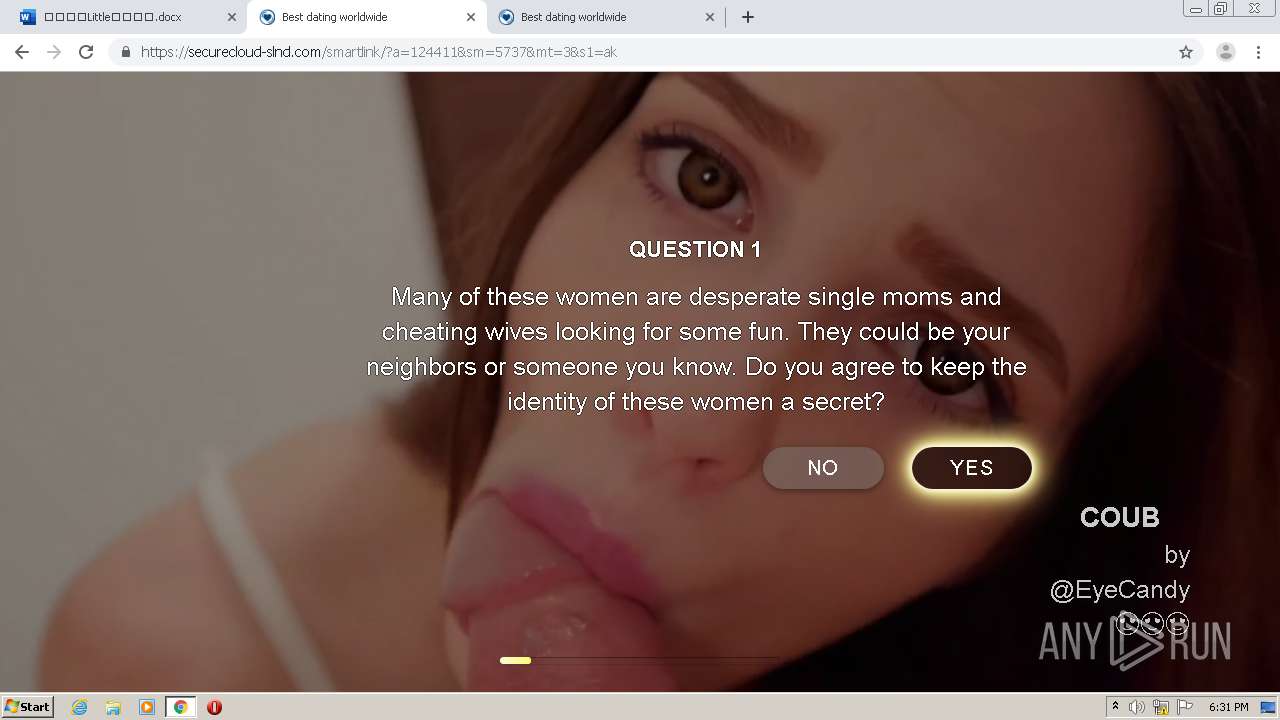
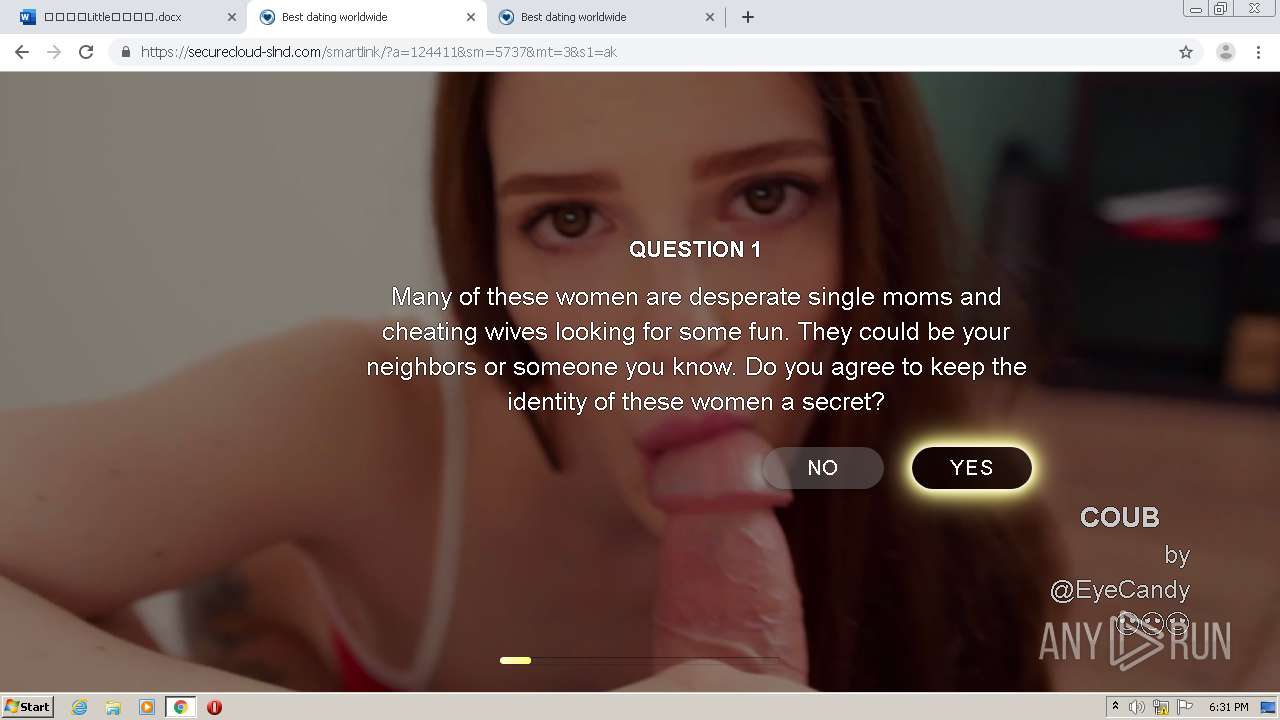
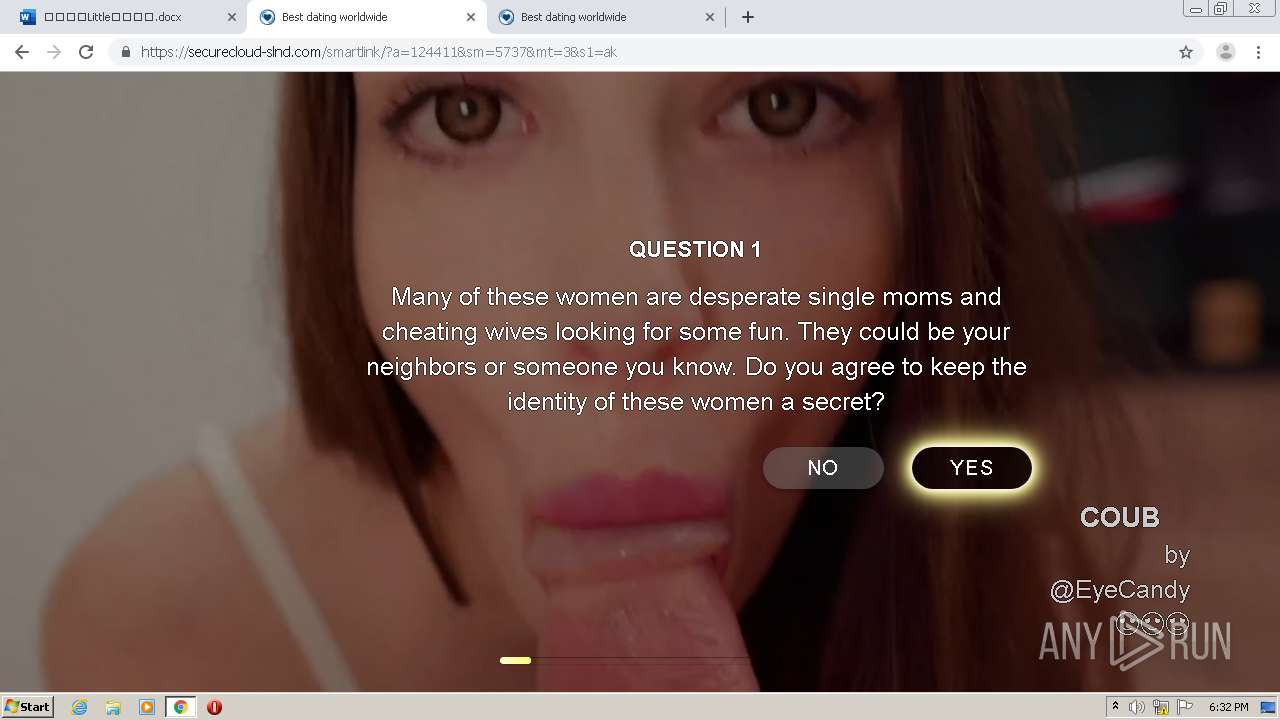
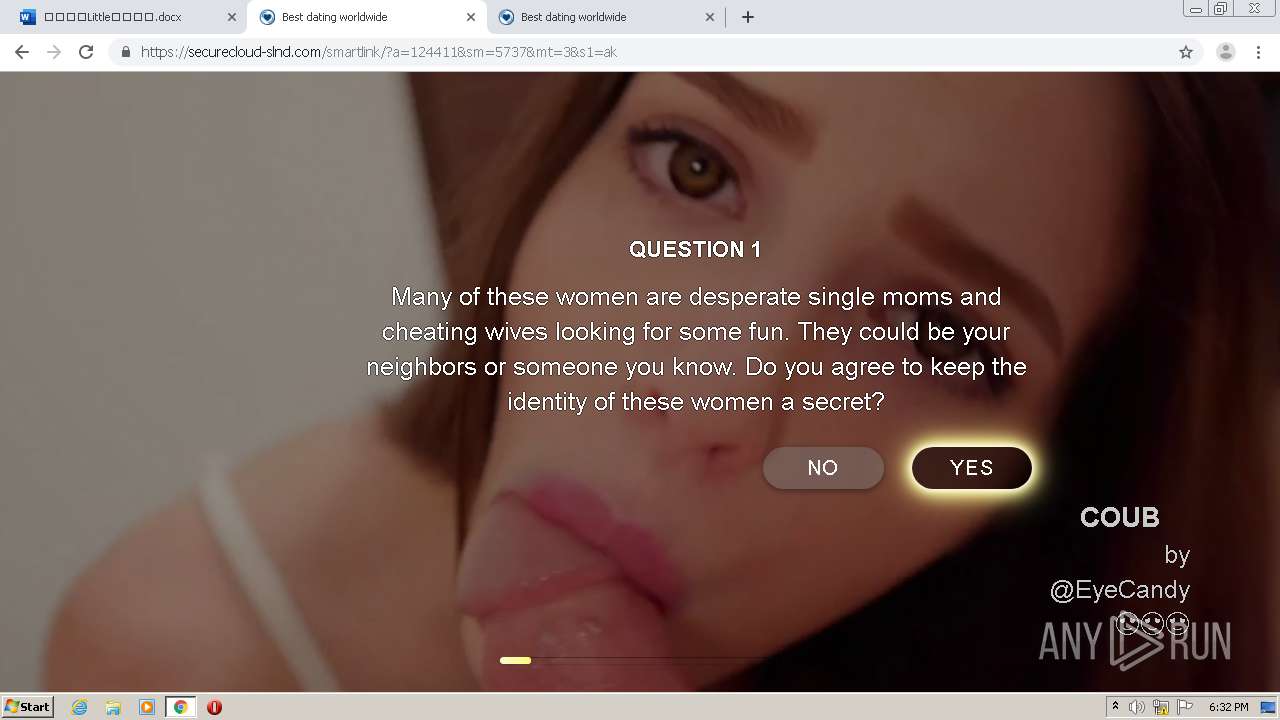
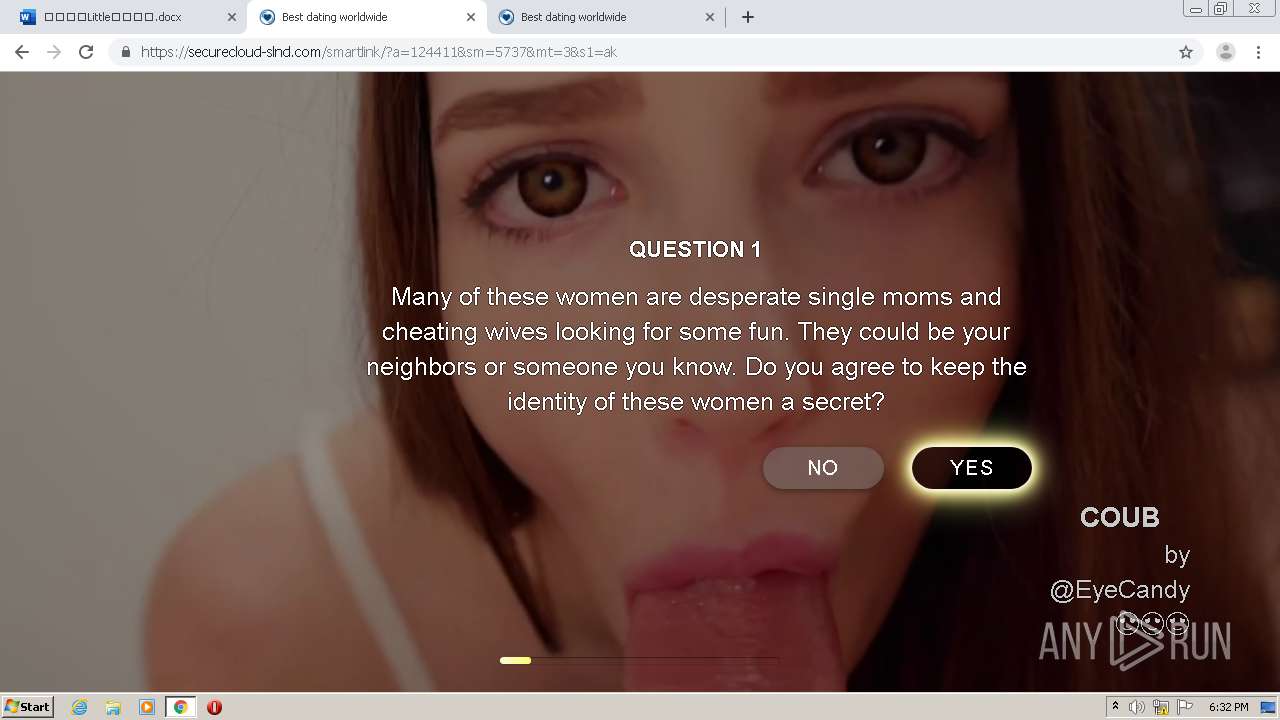
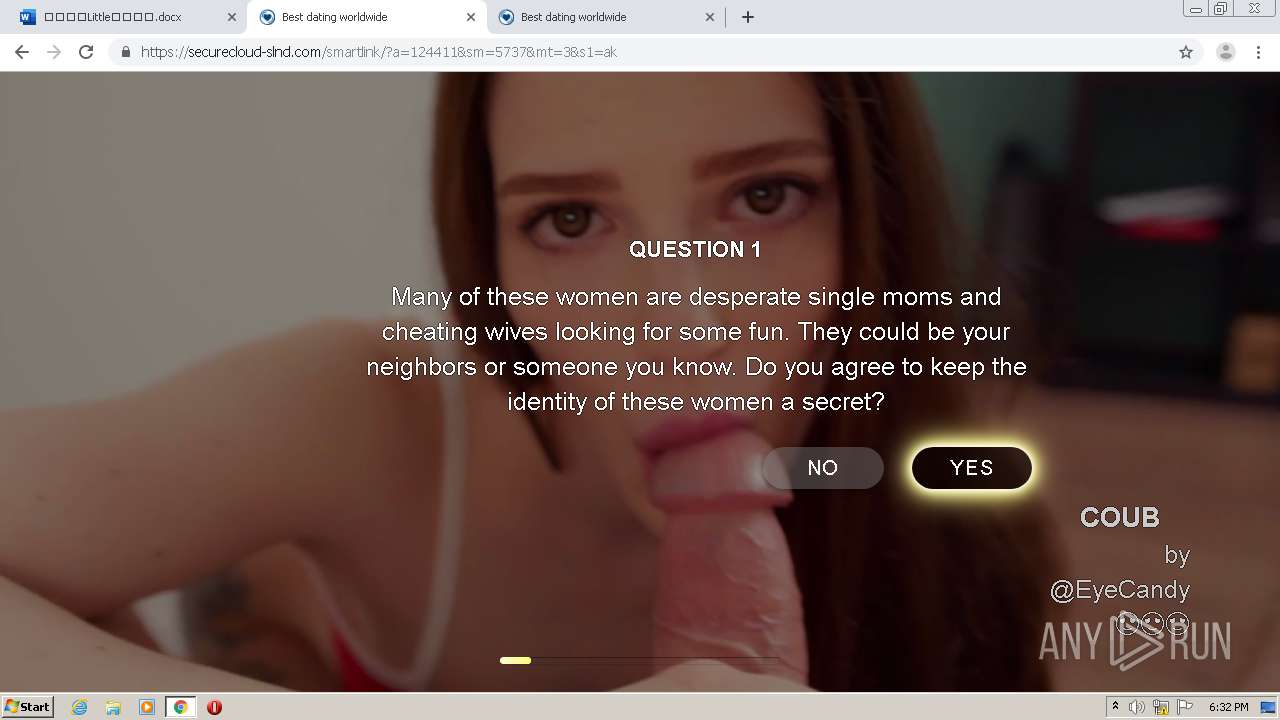
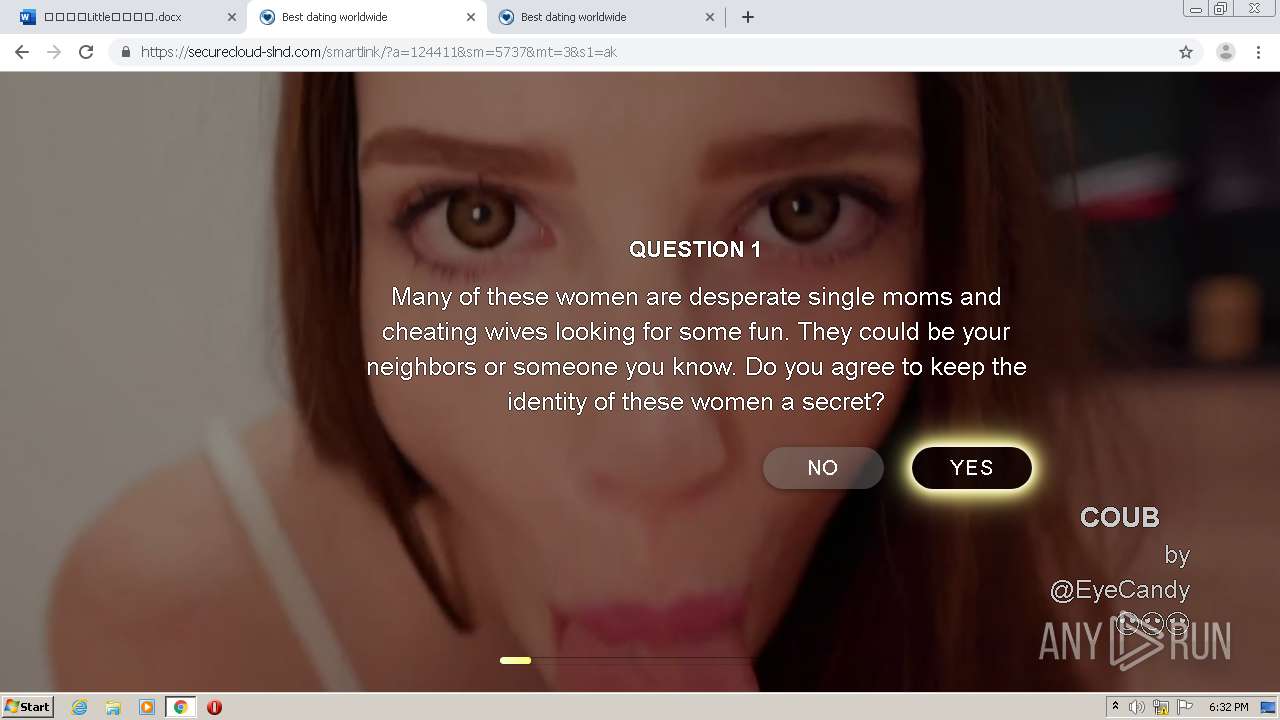
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2021, 18:27:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C24A0026FA63E52644CDFAD8BC9A4739 |
| SHA1: | F916012DB0852320AE8EACD59AFCCF304DA8A108 |
| SHA256: | 4CA0DDF3268754897467D4AACD95B75C12B6AE8701CBA70E12EEE41ABB0EFF22 |
| SSDEEP: | 3:N8NMK+ArL5rJSCukuEAJi60gBPWW/uNty0Q1Dh0XxWOxxmG9V2CDEjn:2NMK+Af8kMJi60gBZmNAp1DYxmG9VX2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2064)
Reads the hosts file
- chrome.exe (PID: 2064)
- chrome.exe (PID: 4000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,11711736722375004242,9601785972402356509,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13589267096697798531 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,11711736722375004242,9601785972402356509,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1683143549711661806 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,11711736722375004242,9601785972402356509,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17768043296783690556 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3860 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1520 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://mygavilan-my.sharepoint.com/:w:/g/personal/geneva_hayes_my_gavilan_edu/Ed6f3smsNKtNmuWuD5EUfhgBzEQryTq3k1MTCxnexpA1CQ?e=4%3aZzMNXE&at=9" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f94a9d0,0x6f94a9e0,0x6f94a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,11711736722375004242,9601785972402356509,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11156282850977967098 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,11711736722375004242,9601785972402356509,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2608436040985963112 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,11711736722375004242,9601785972402356509,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8964288859904177558 --mojo-platform-channel-handle=3608 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,11711736722375004242,9601785972402356509,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10228235437658166391 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
601
Read events
543
Write events
55
Delete events
3
Modification events
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2064-13257368868690000 |
Value: 259 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
77
Text files
103
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6022D425-810.pma | — | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bb65bc86-07c2-4812-83d3-0aad099f8663.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFdc515.TMP | text | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFdc498.TMP | text | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2064 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFdc786.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
66
DNS requests
28
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
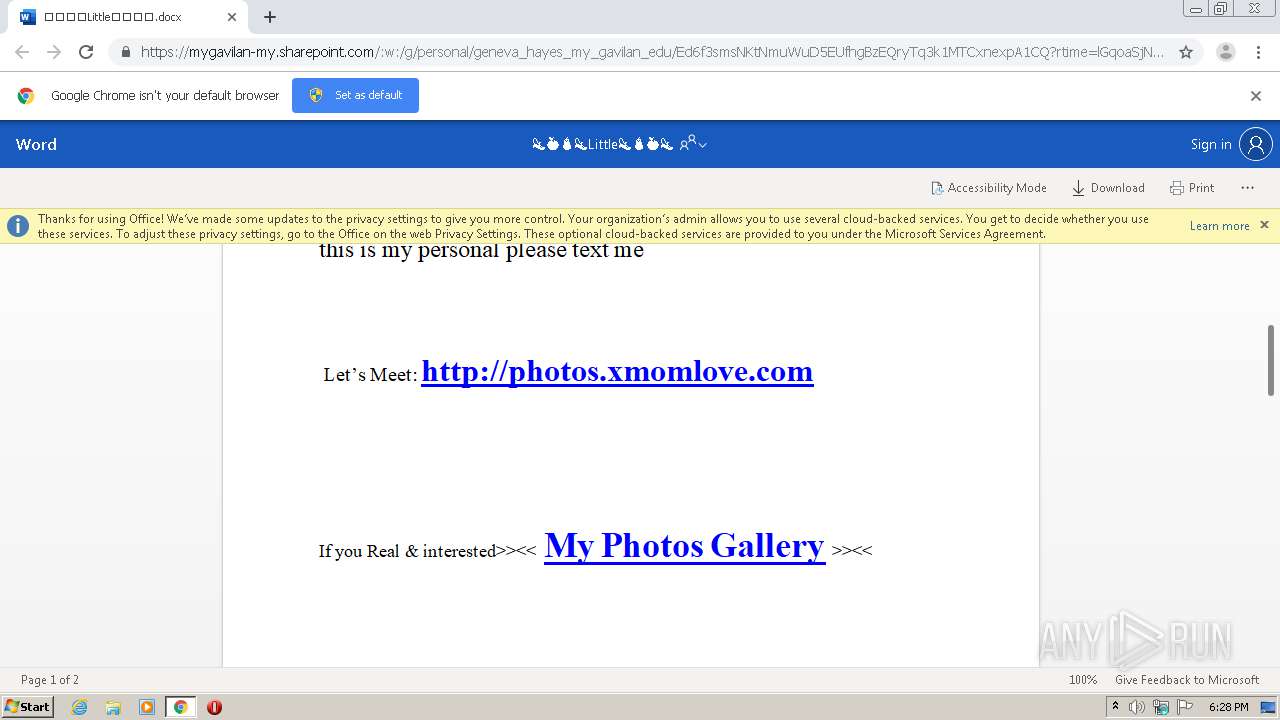
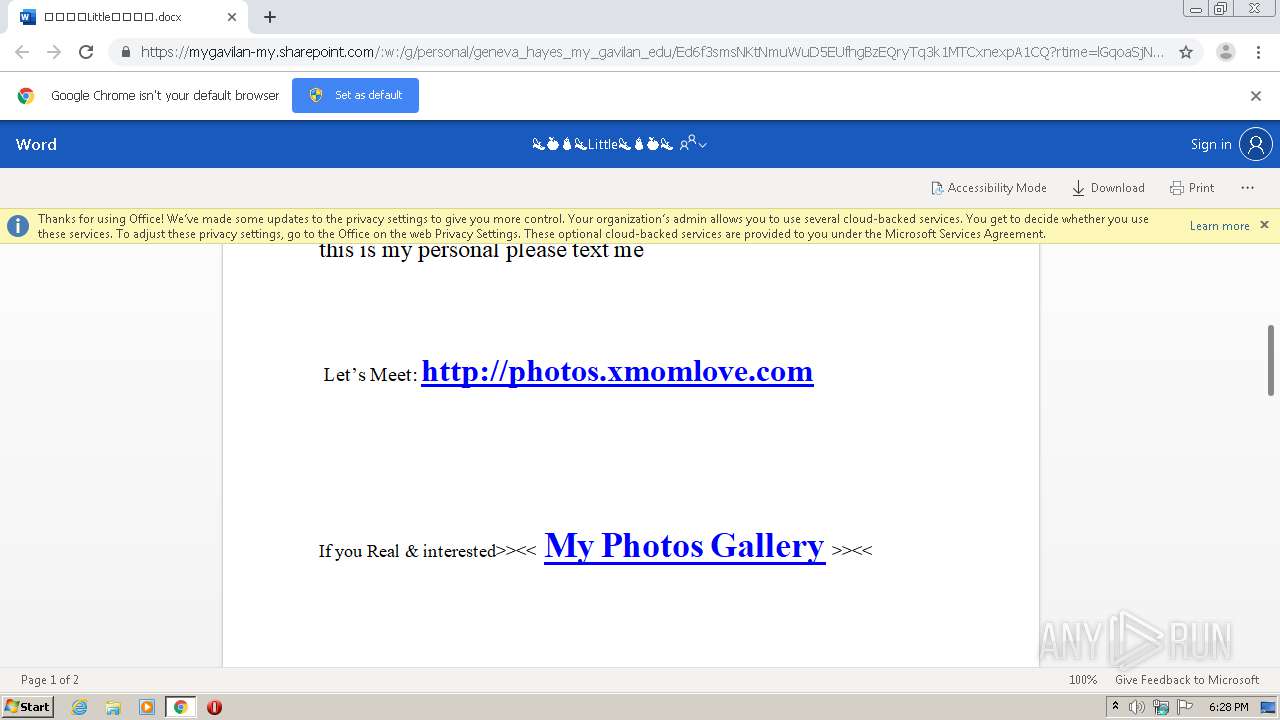
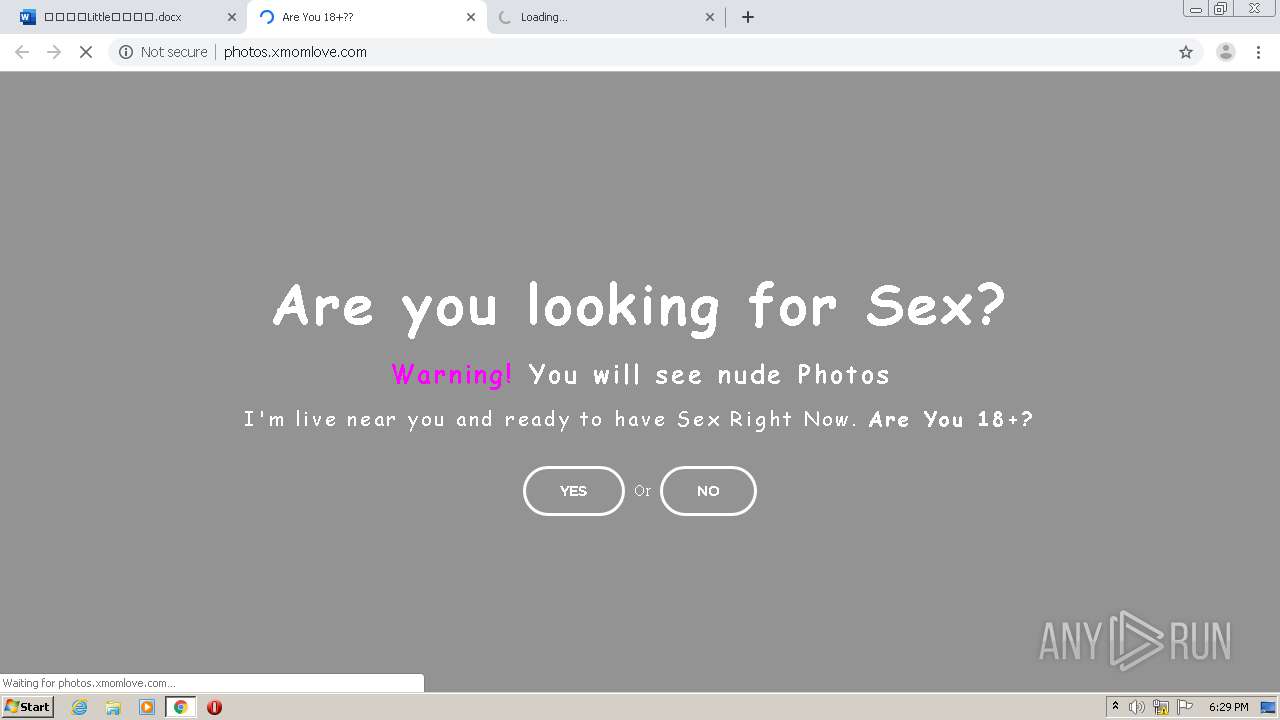
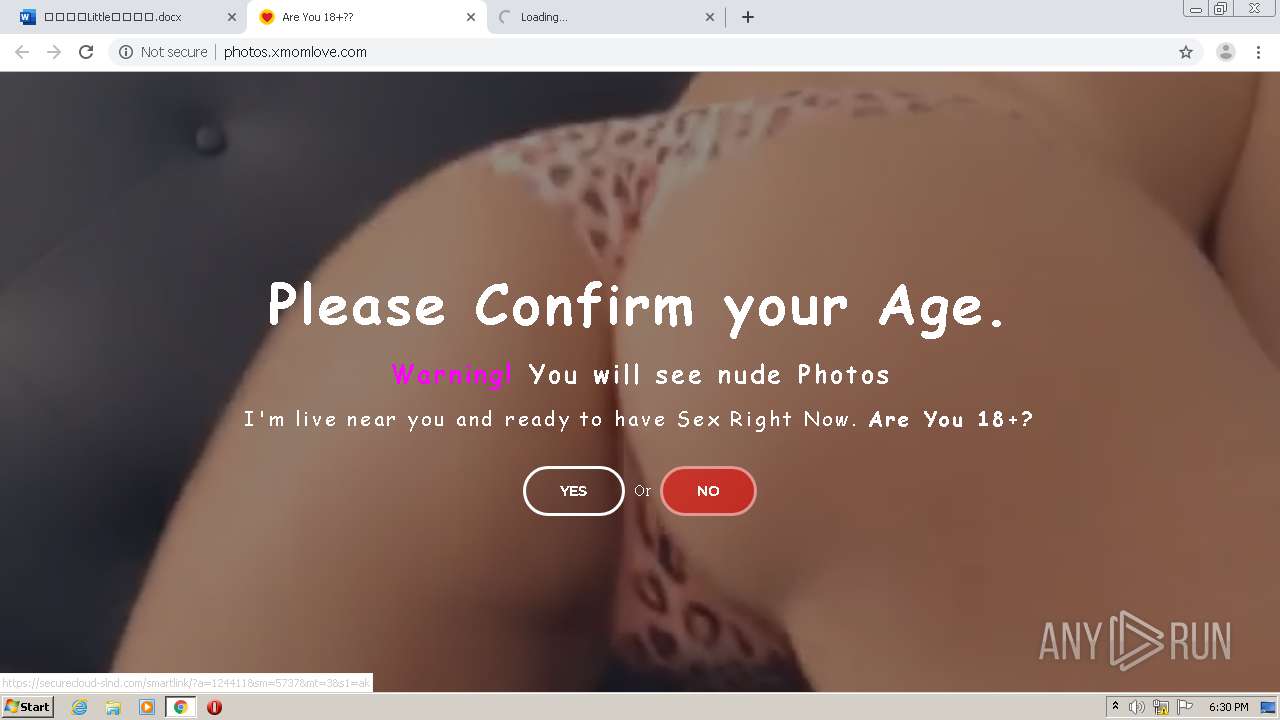
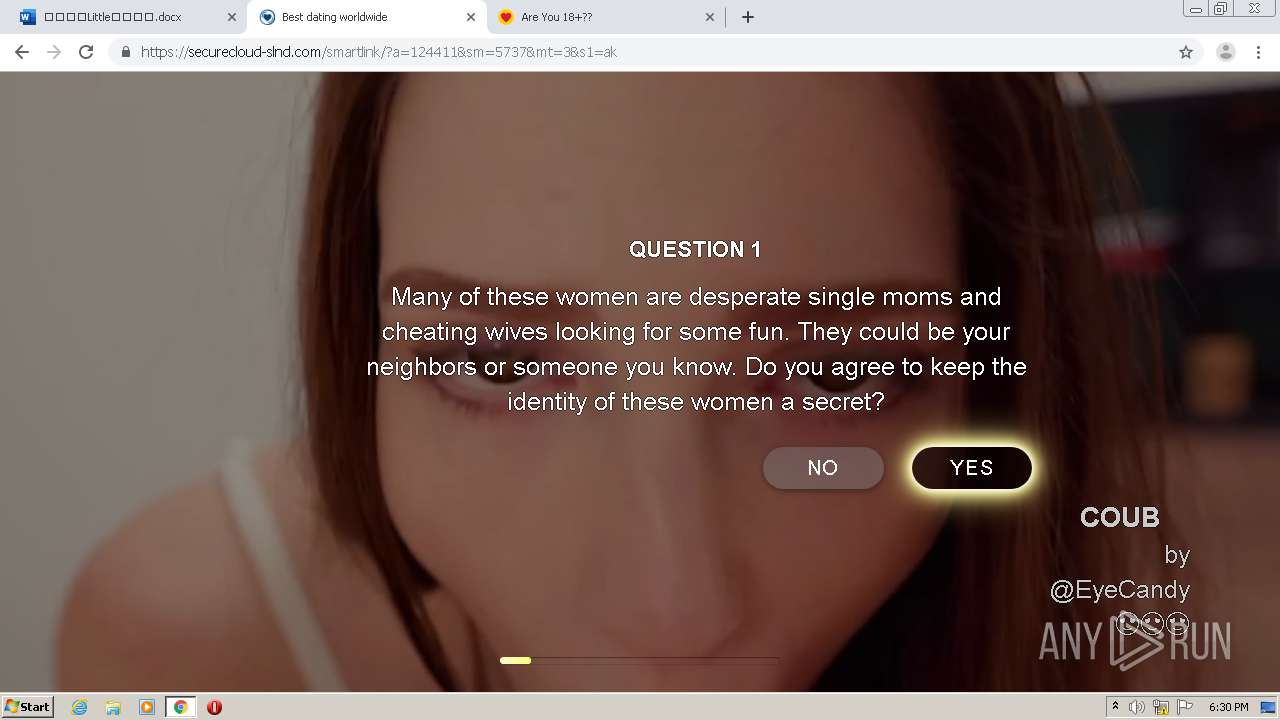
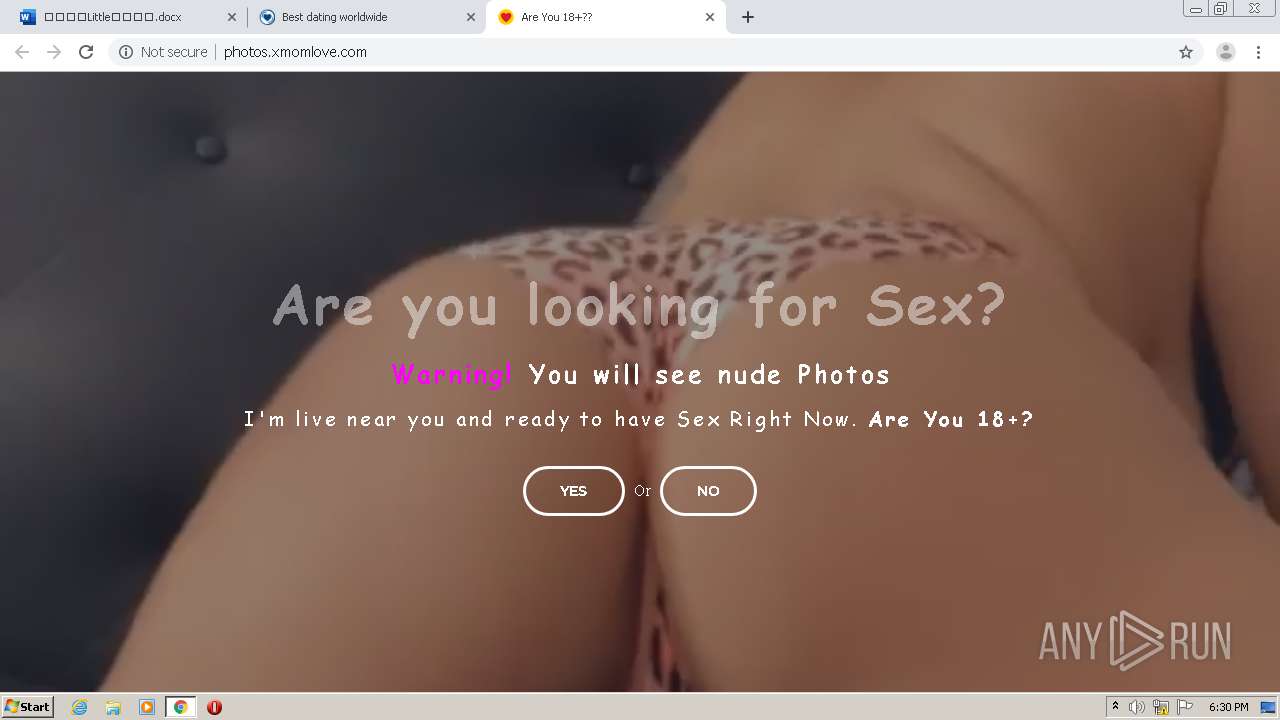
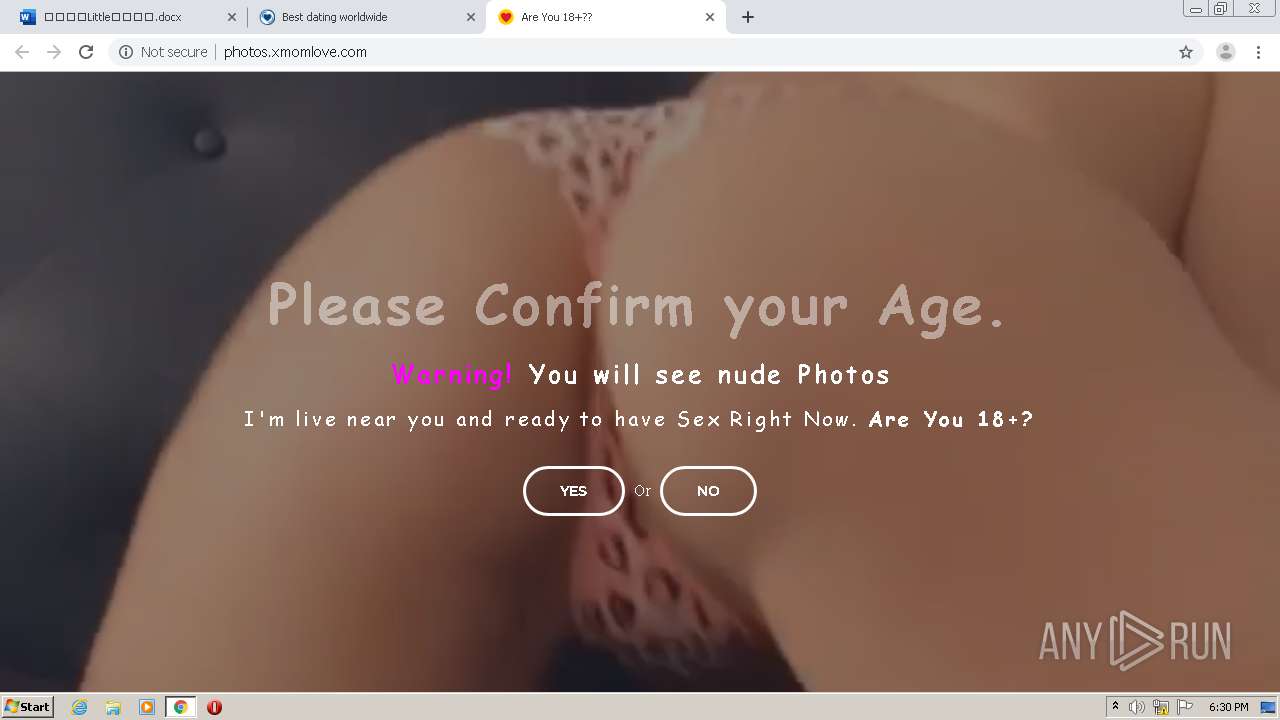
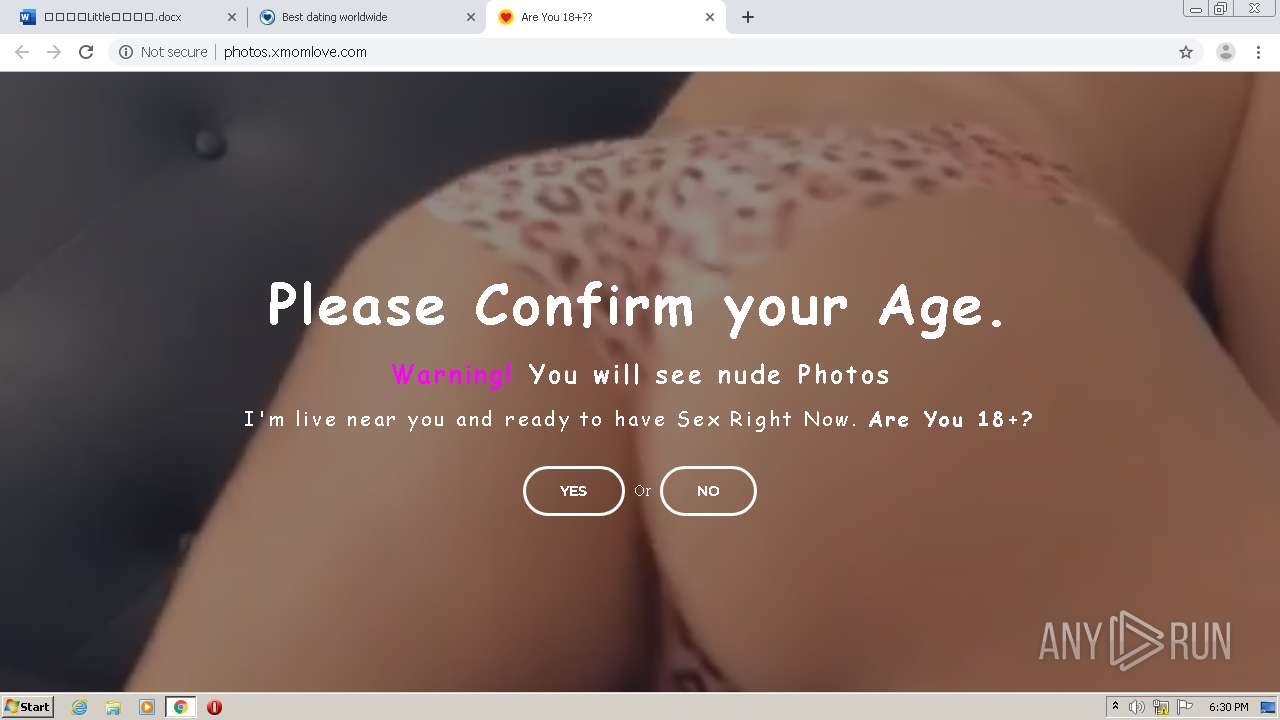
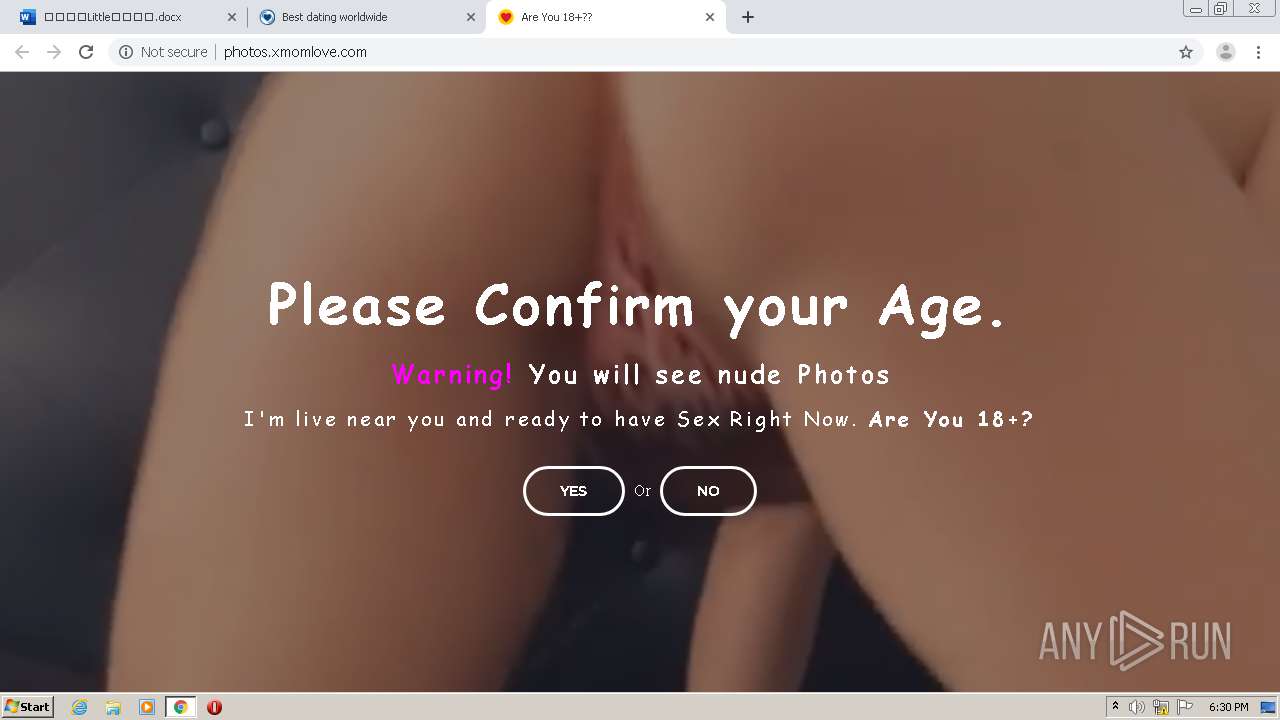
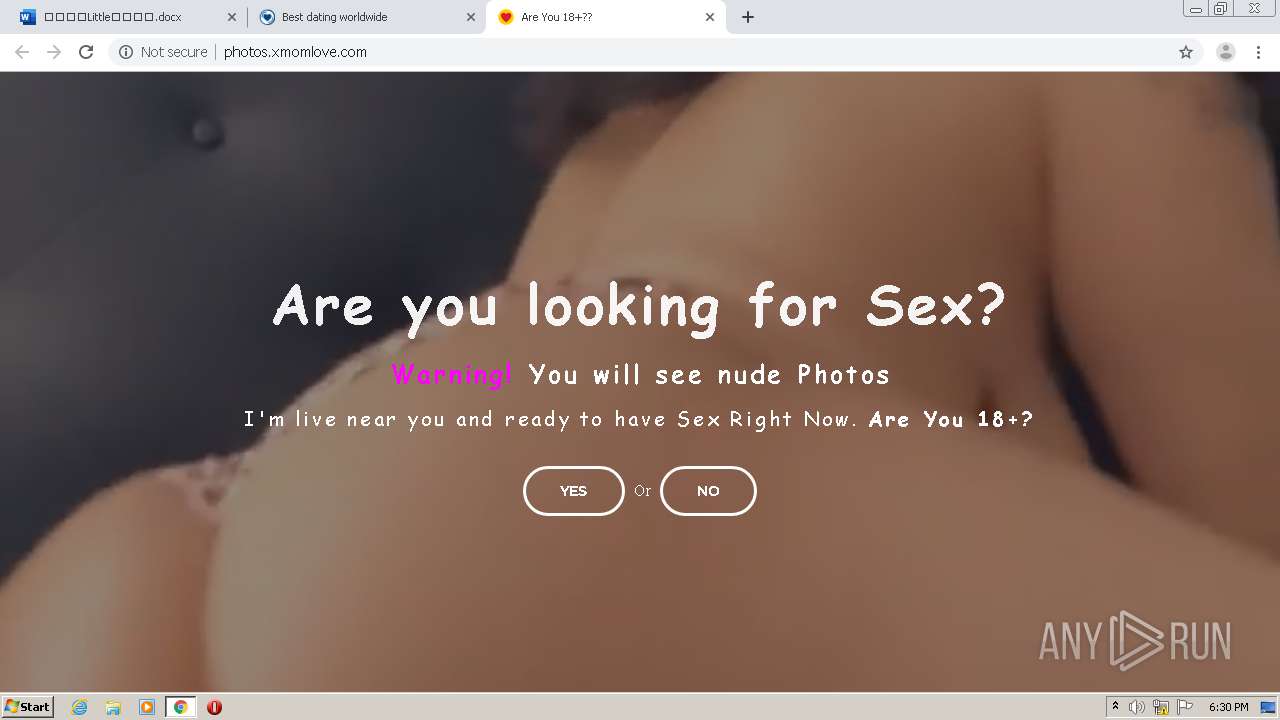
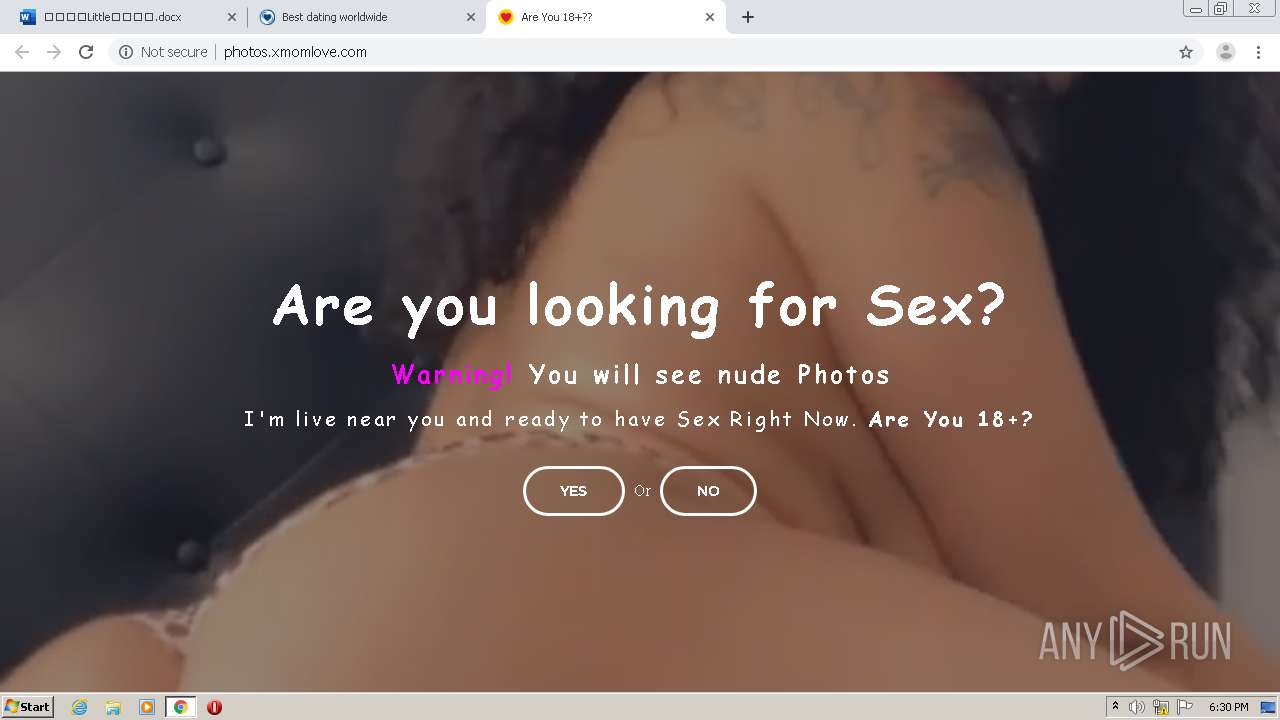
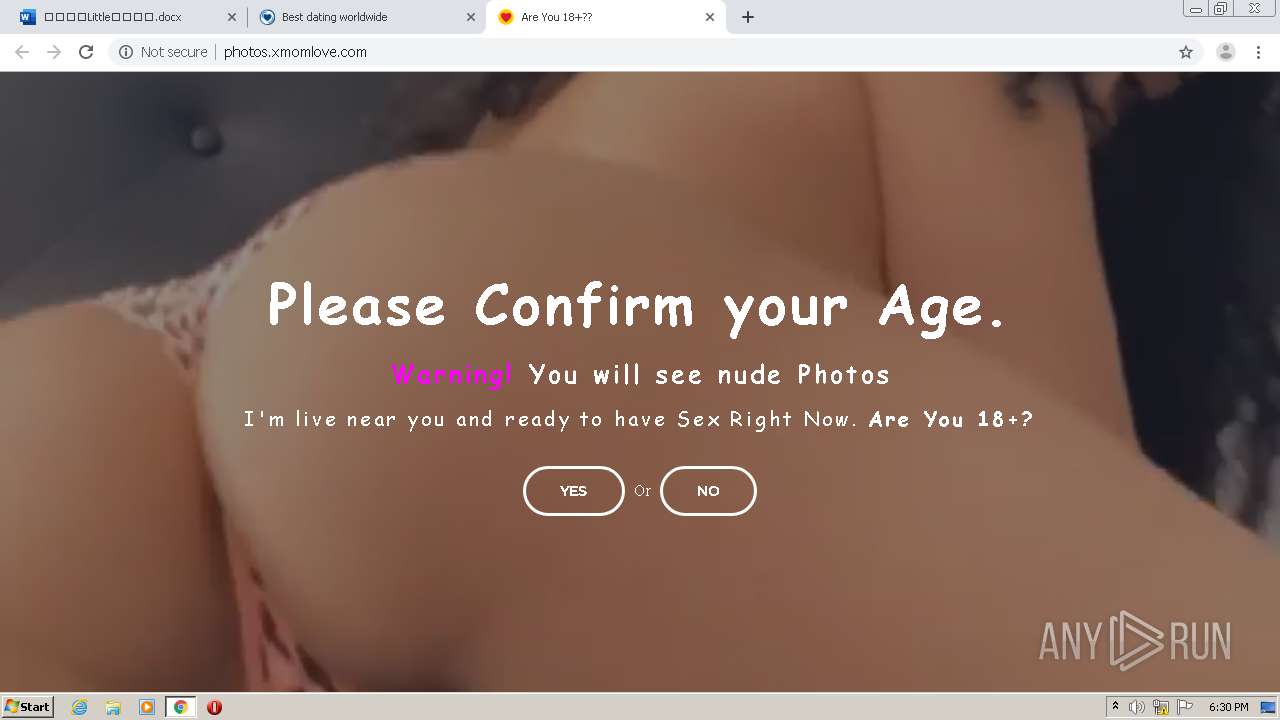
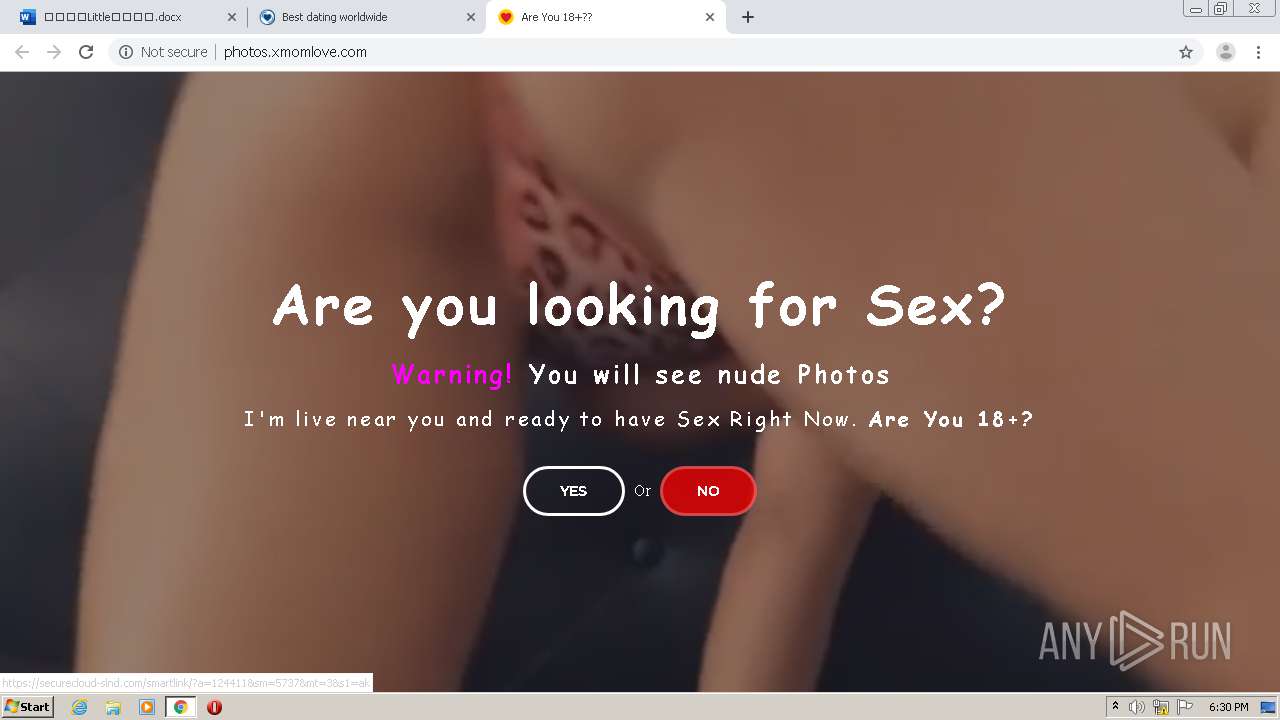
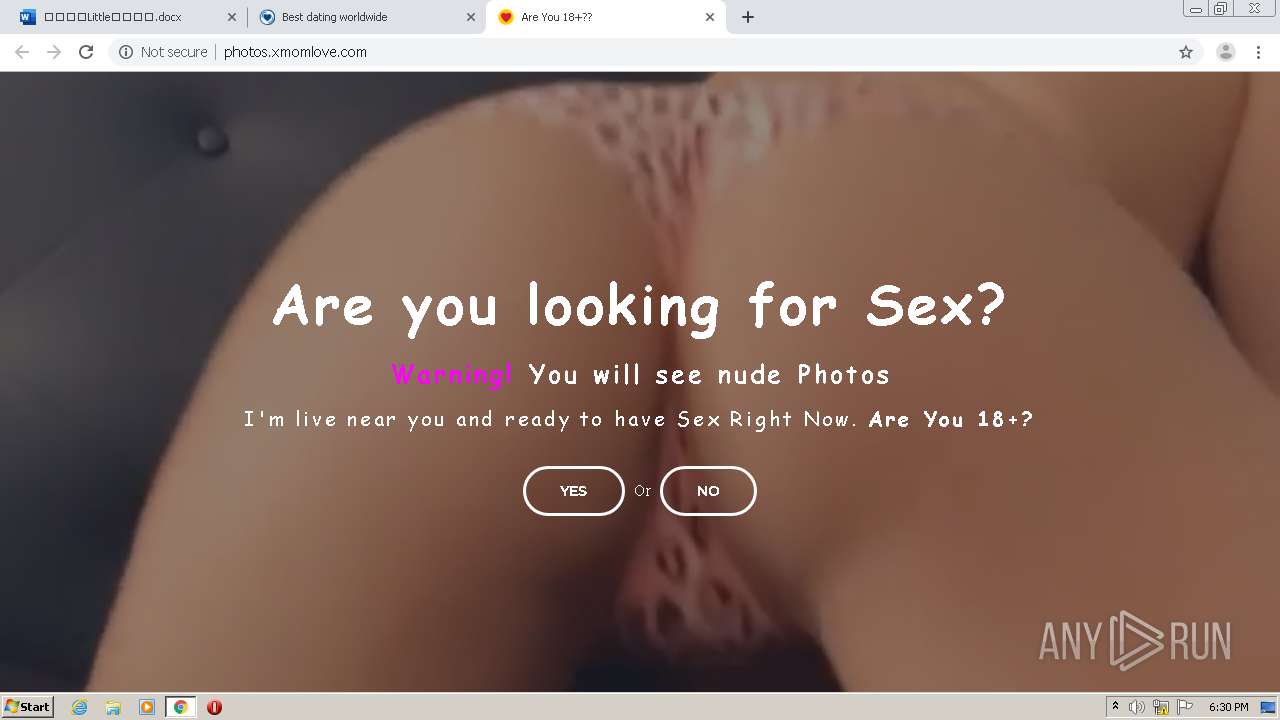
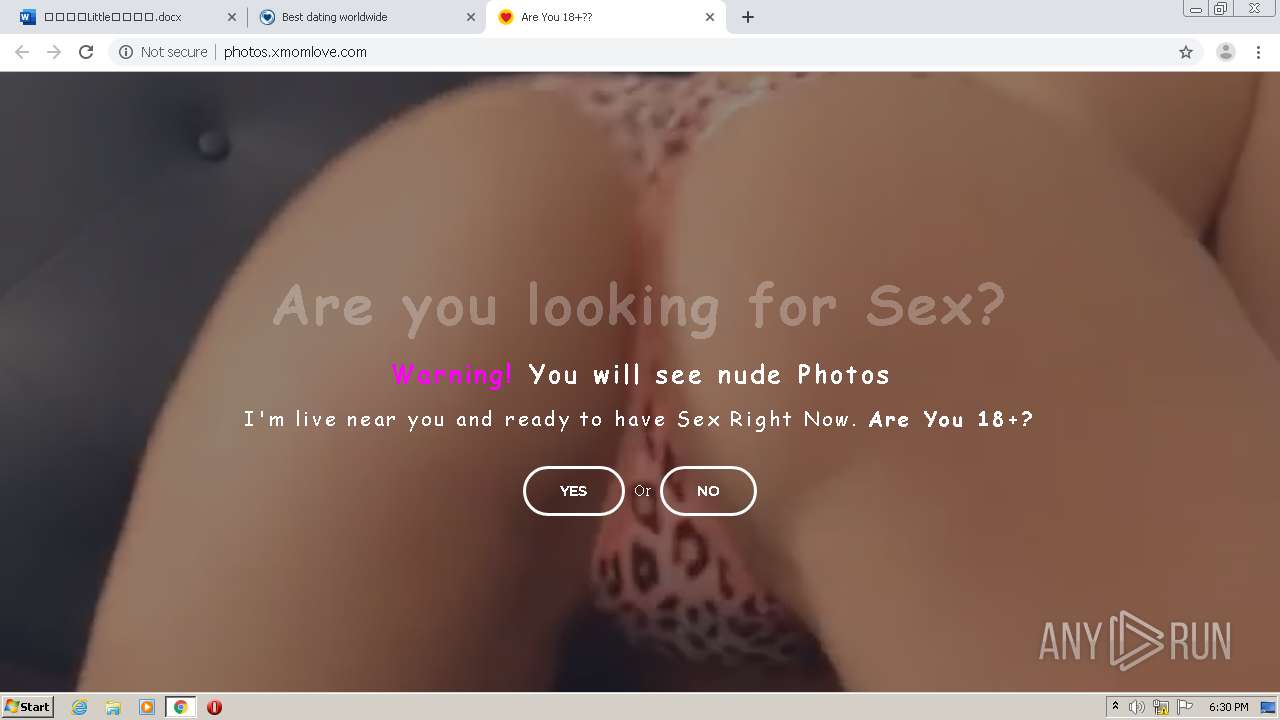
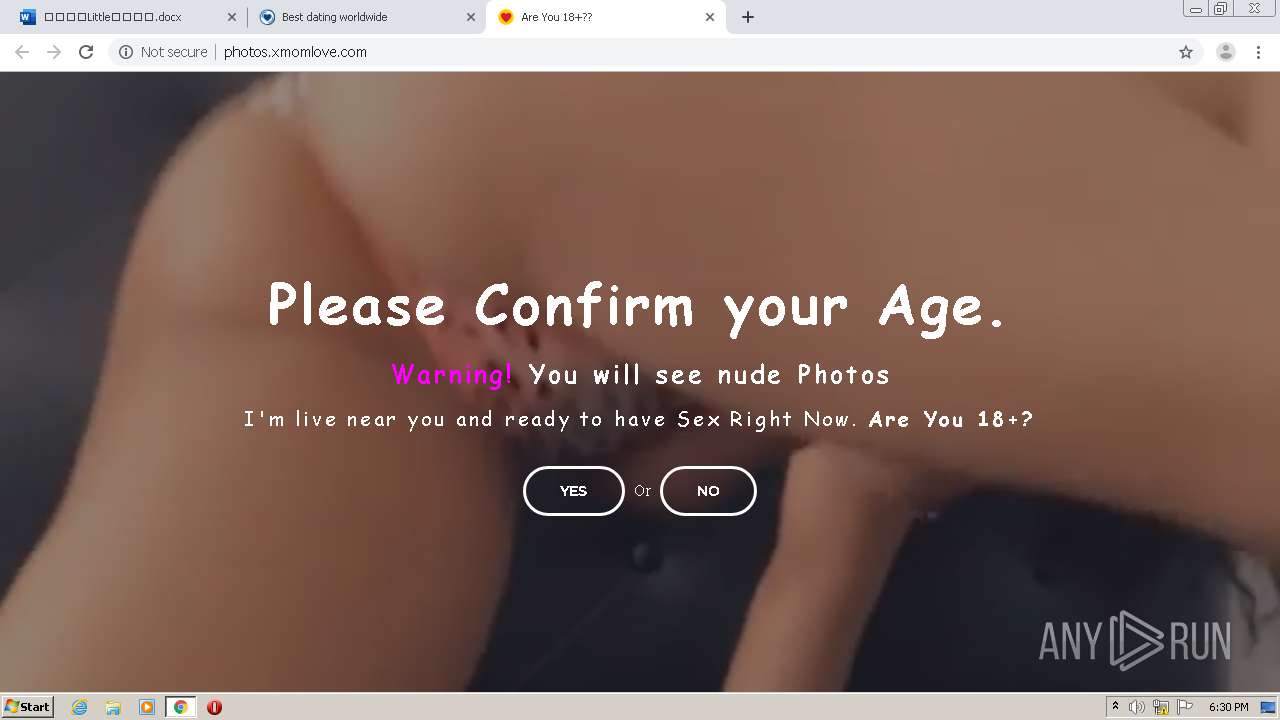
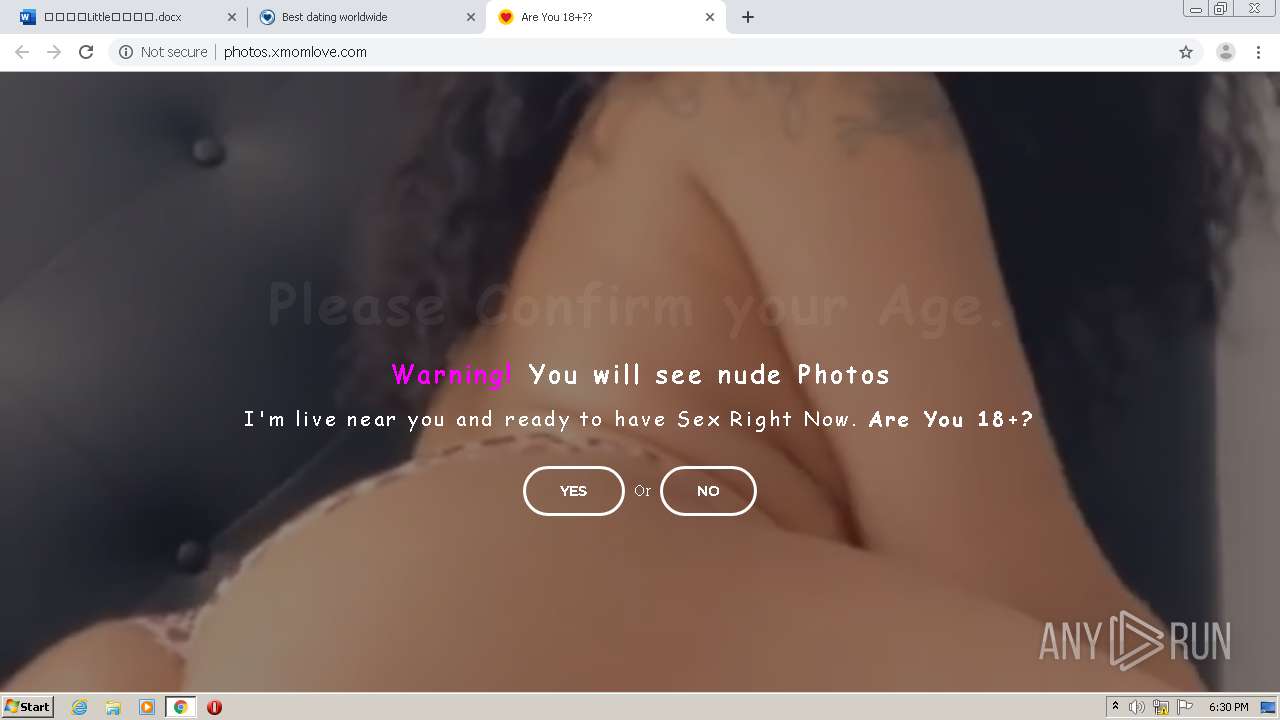
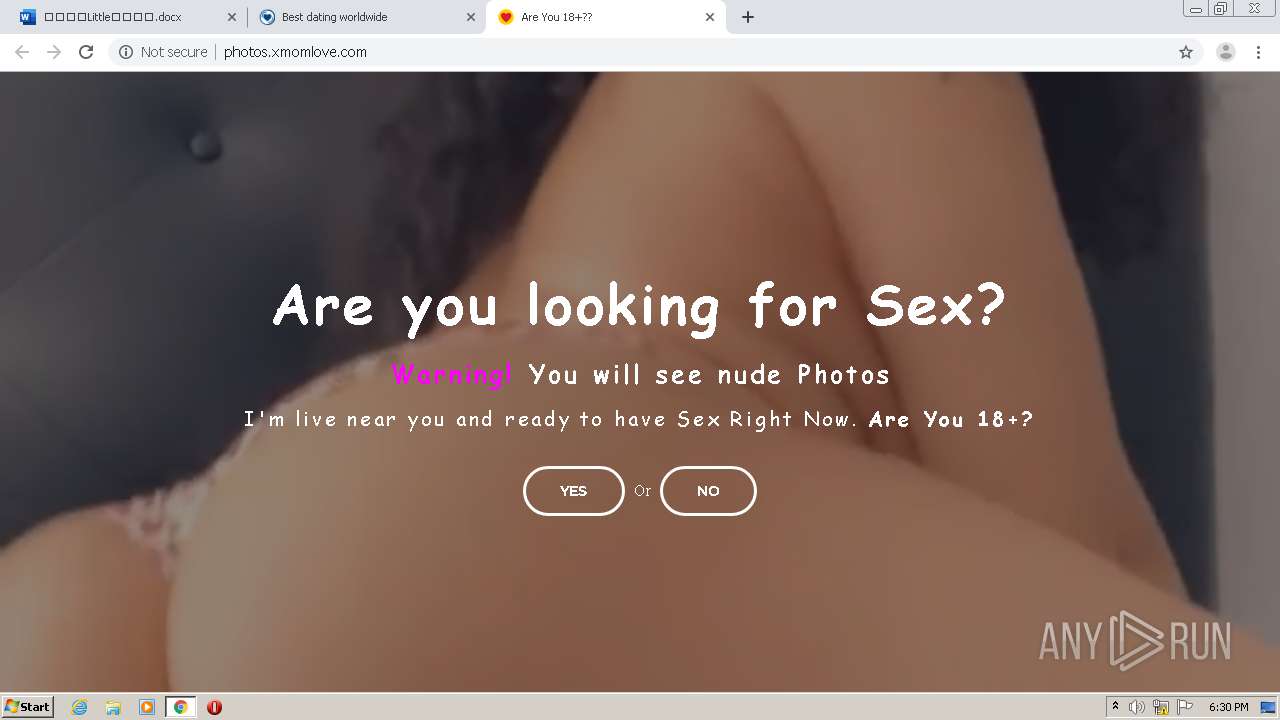
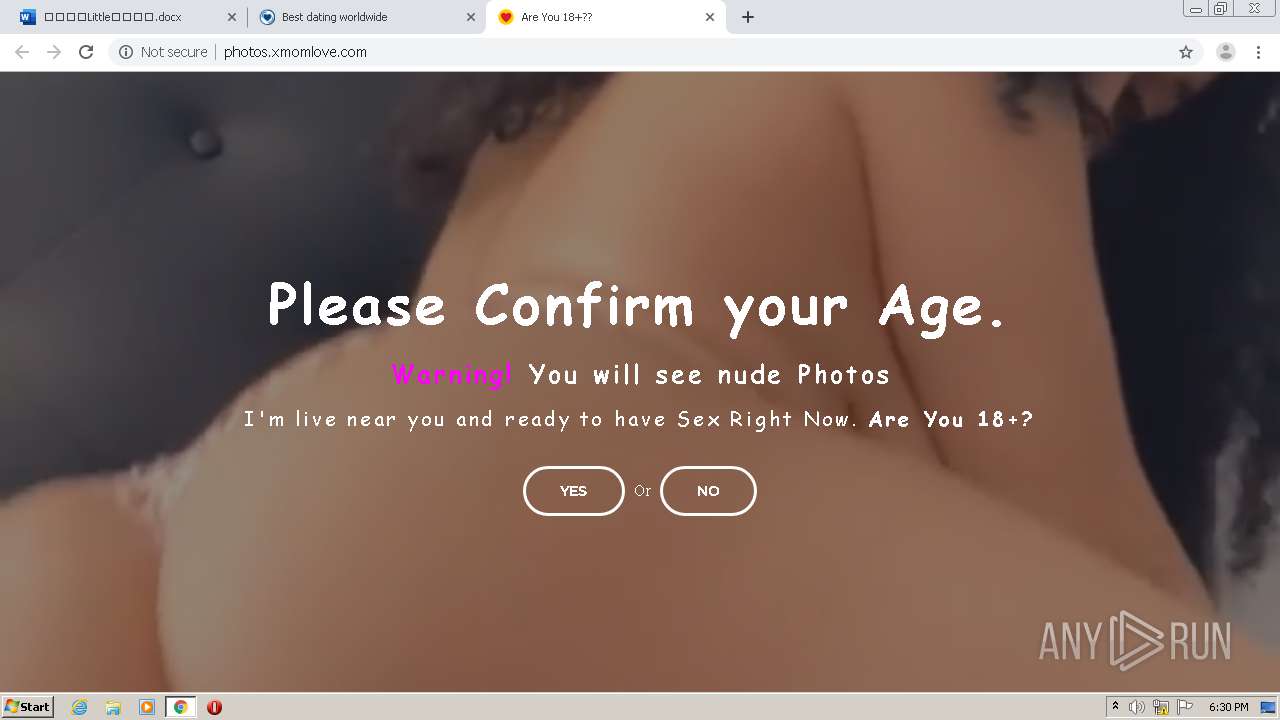
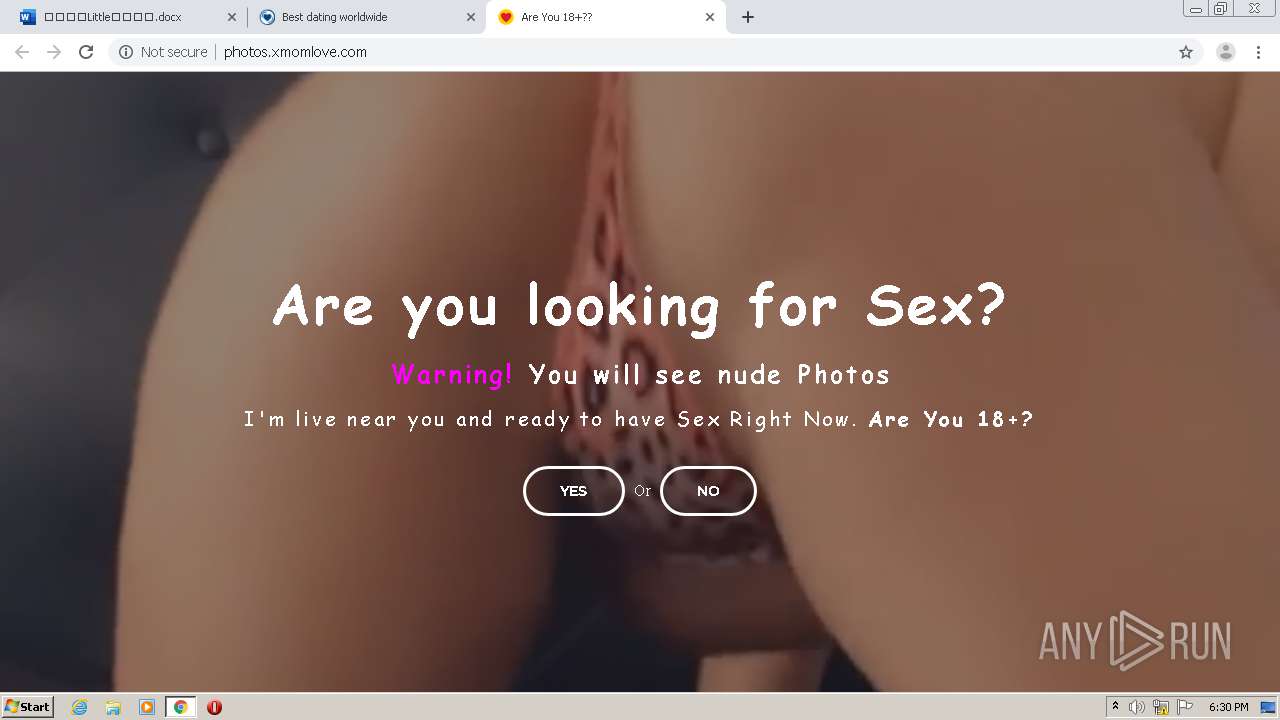
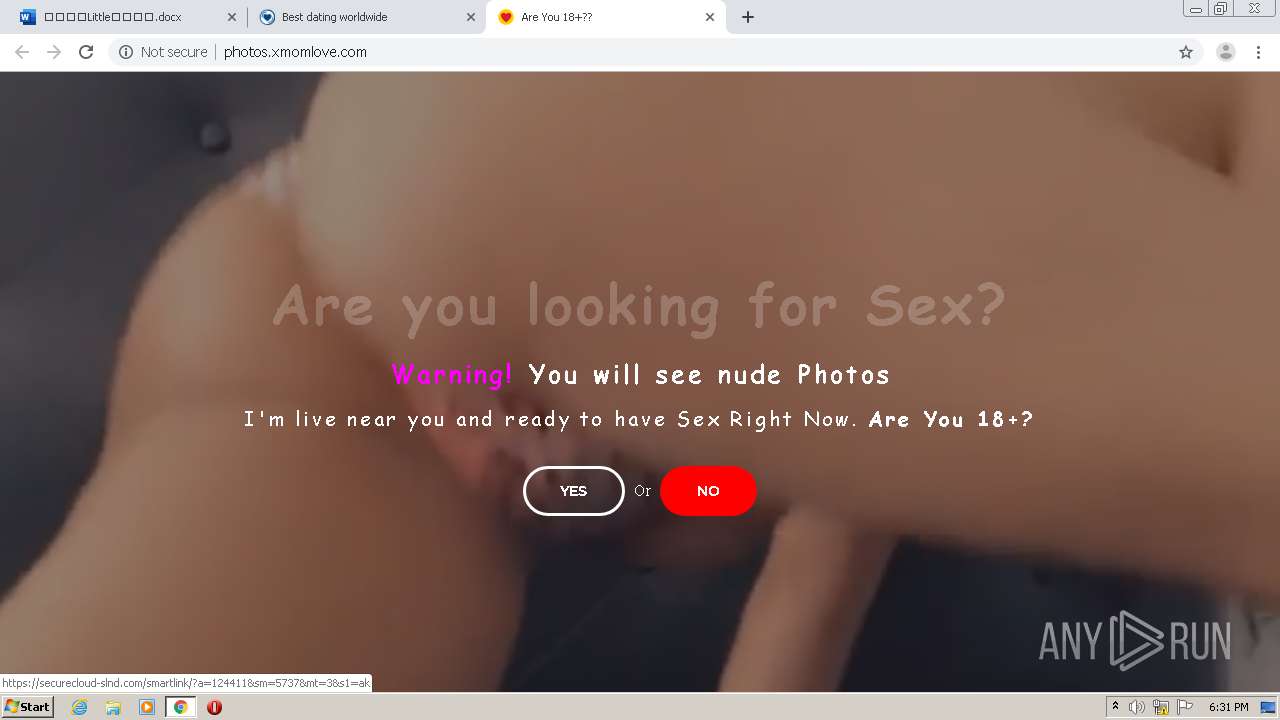
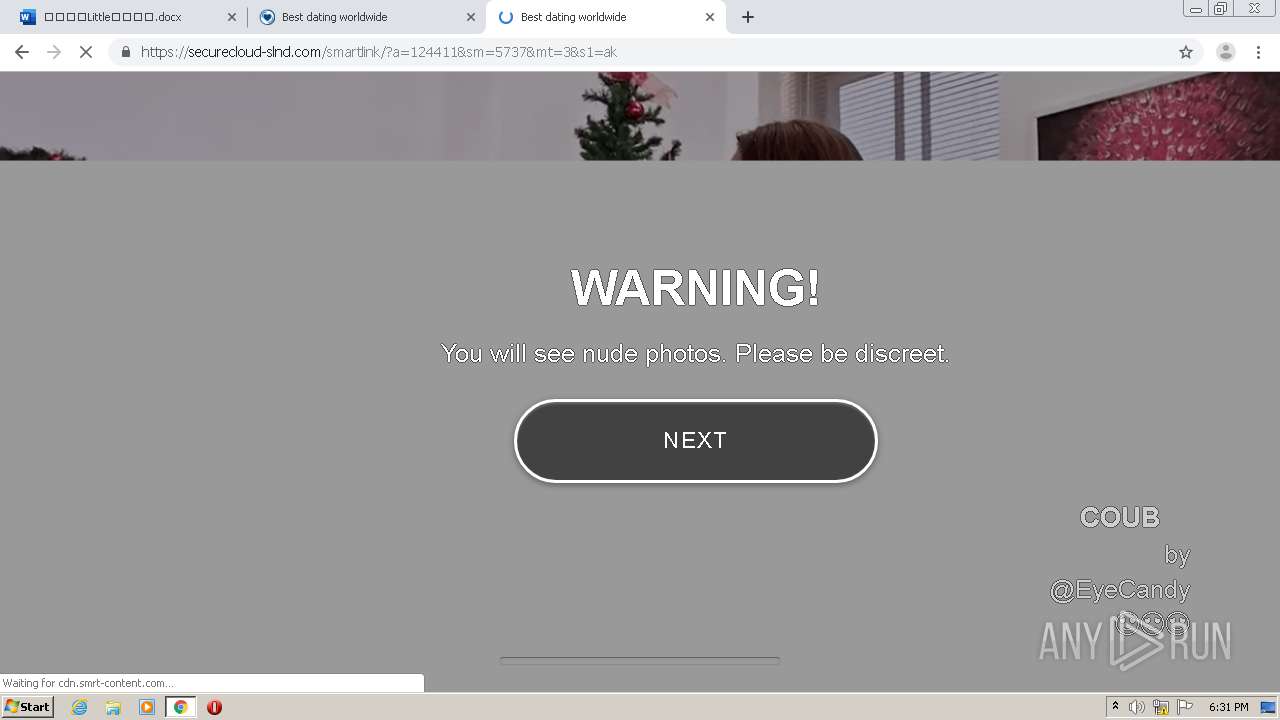
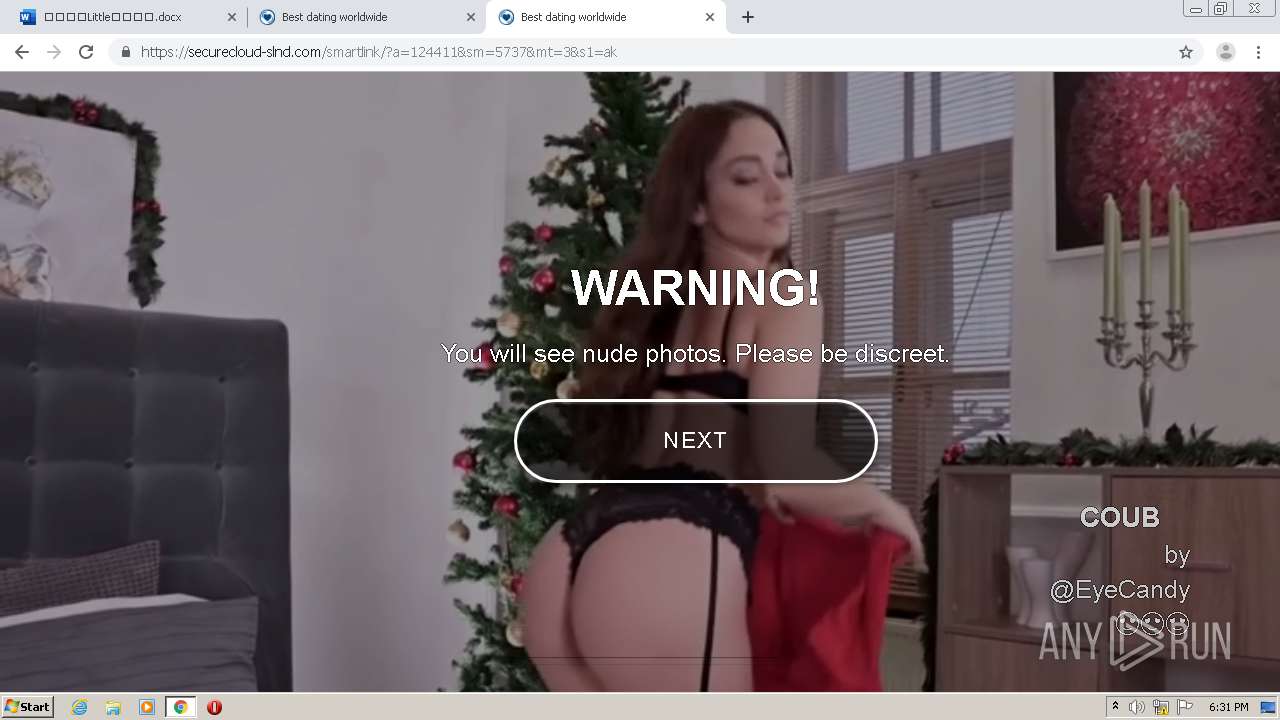
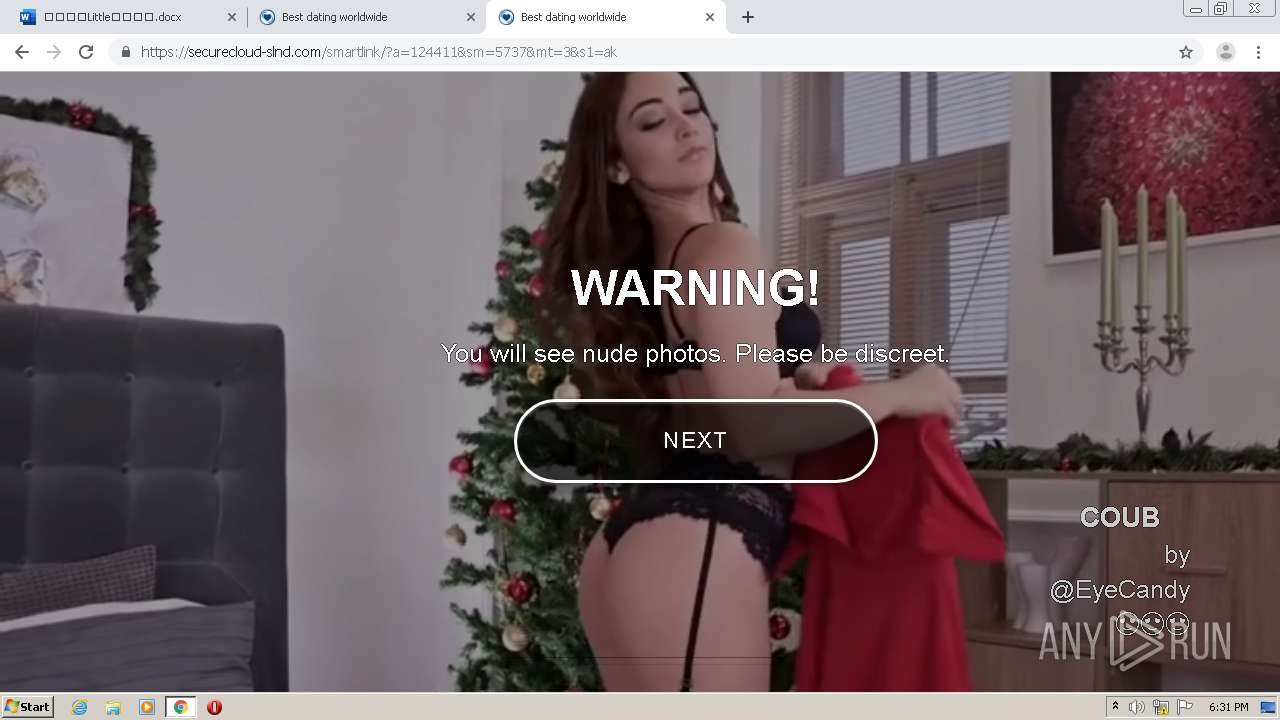
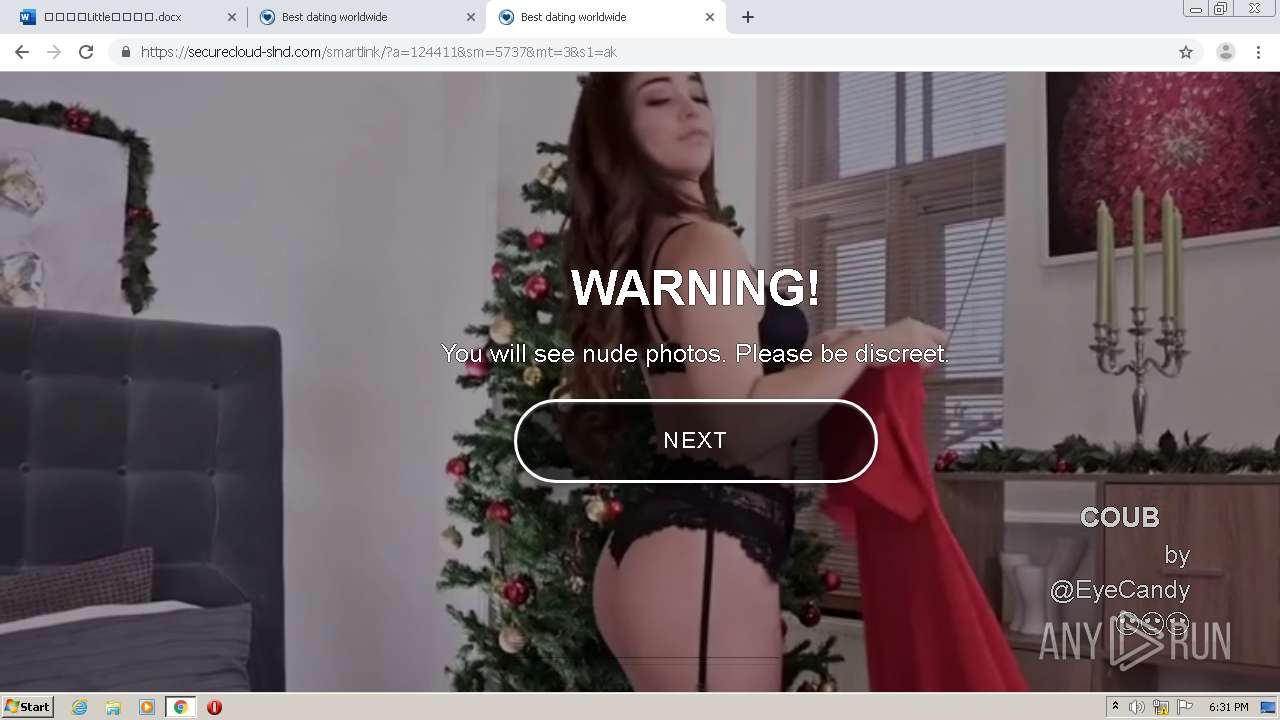
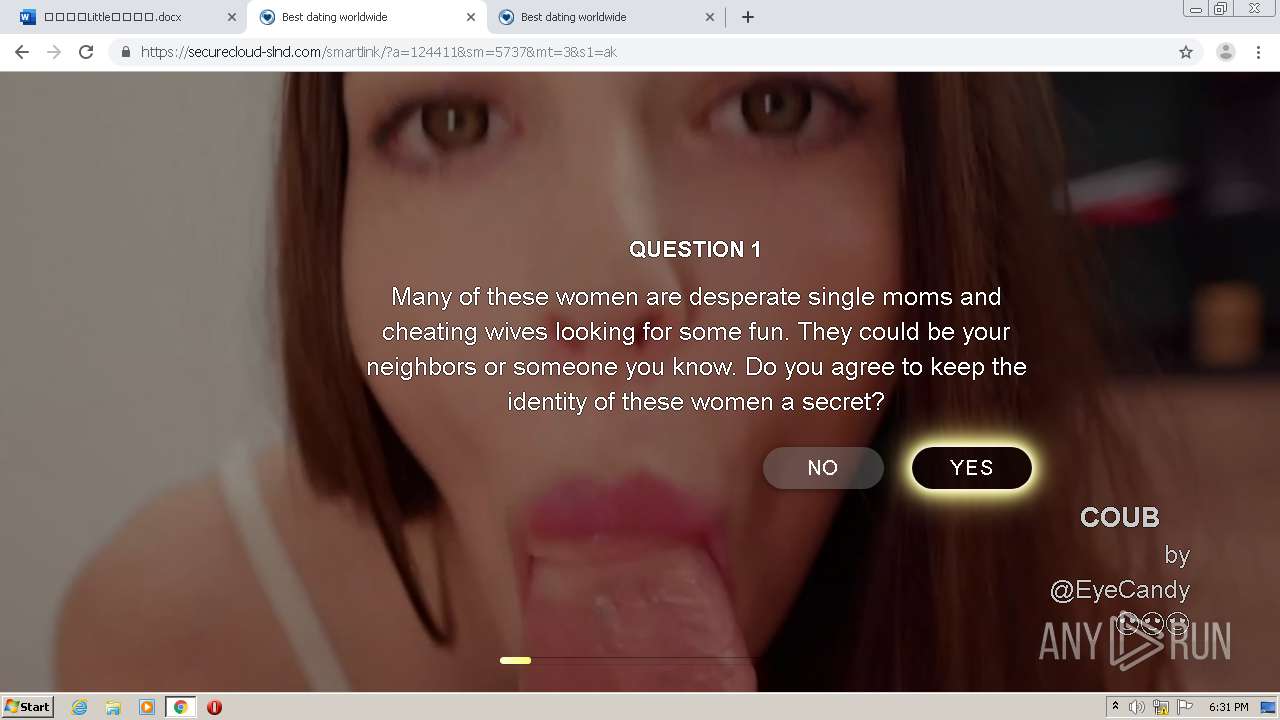
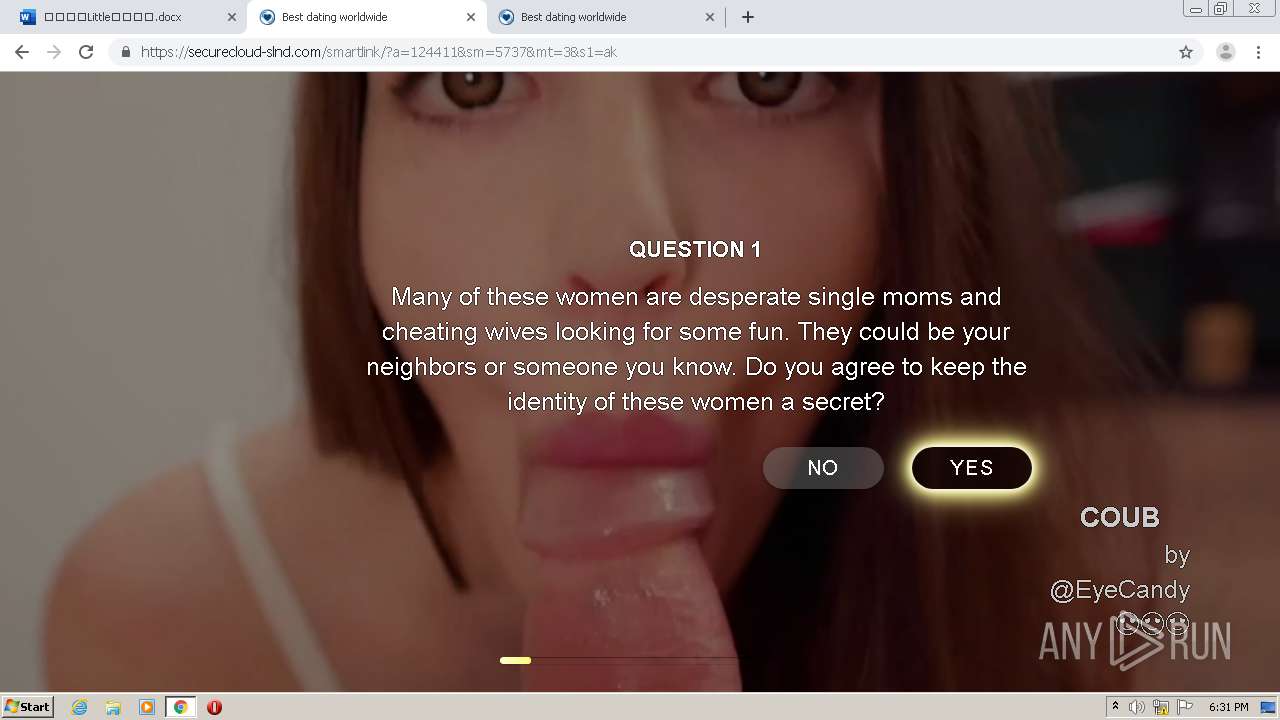
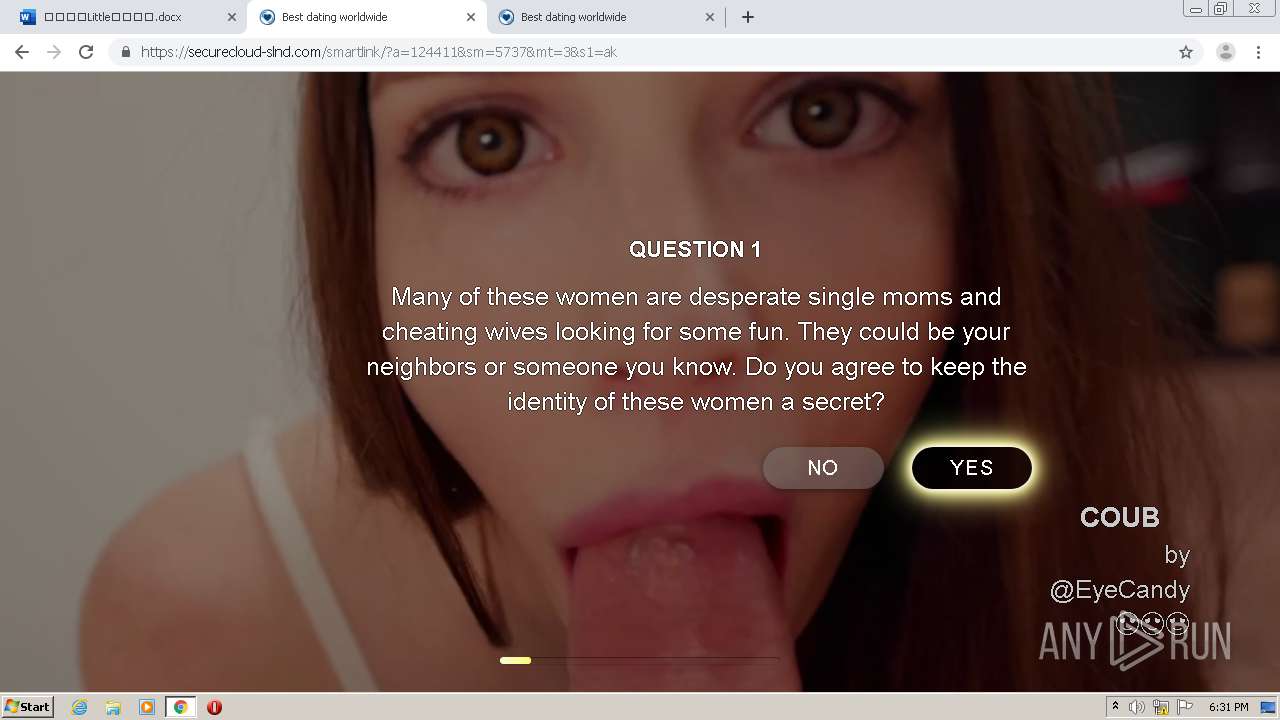
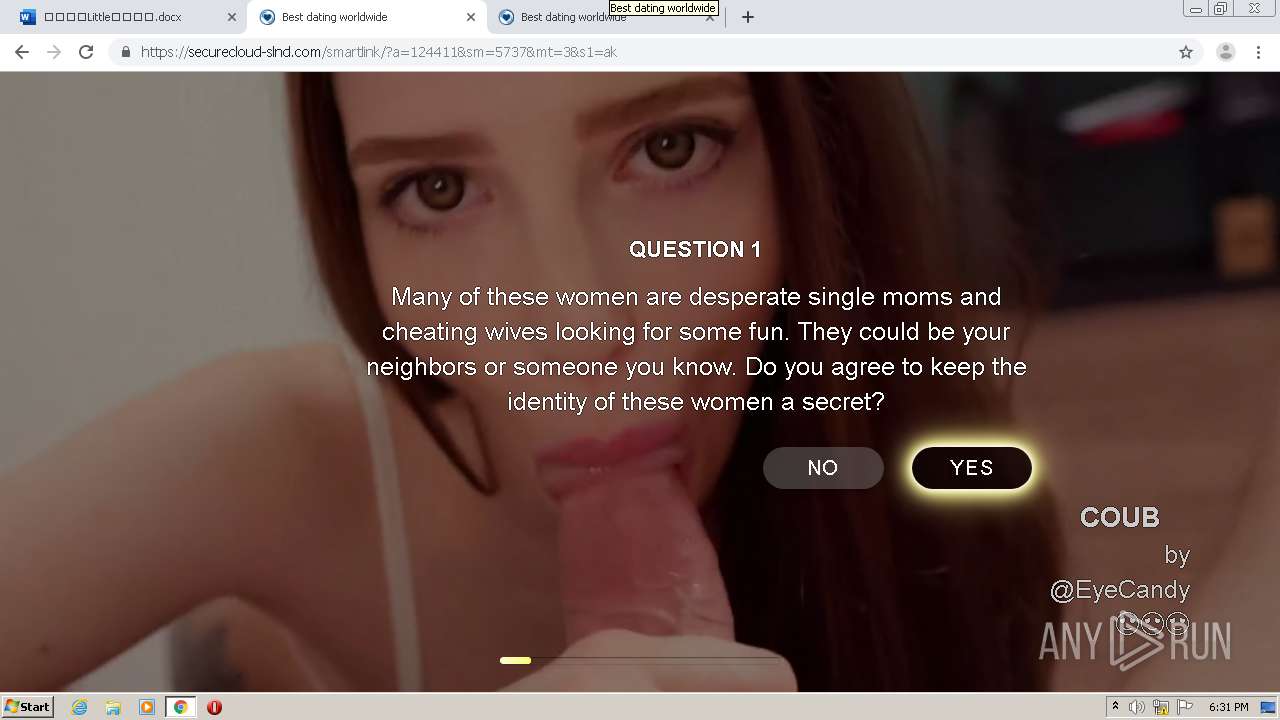
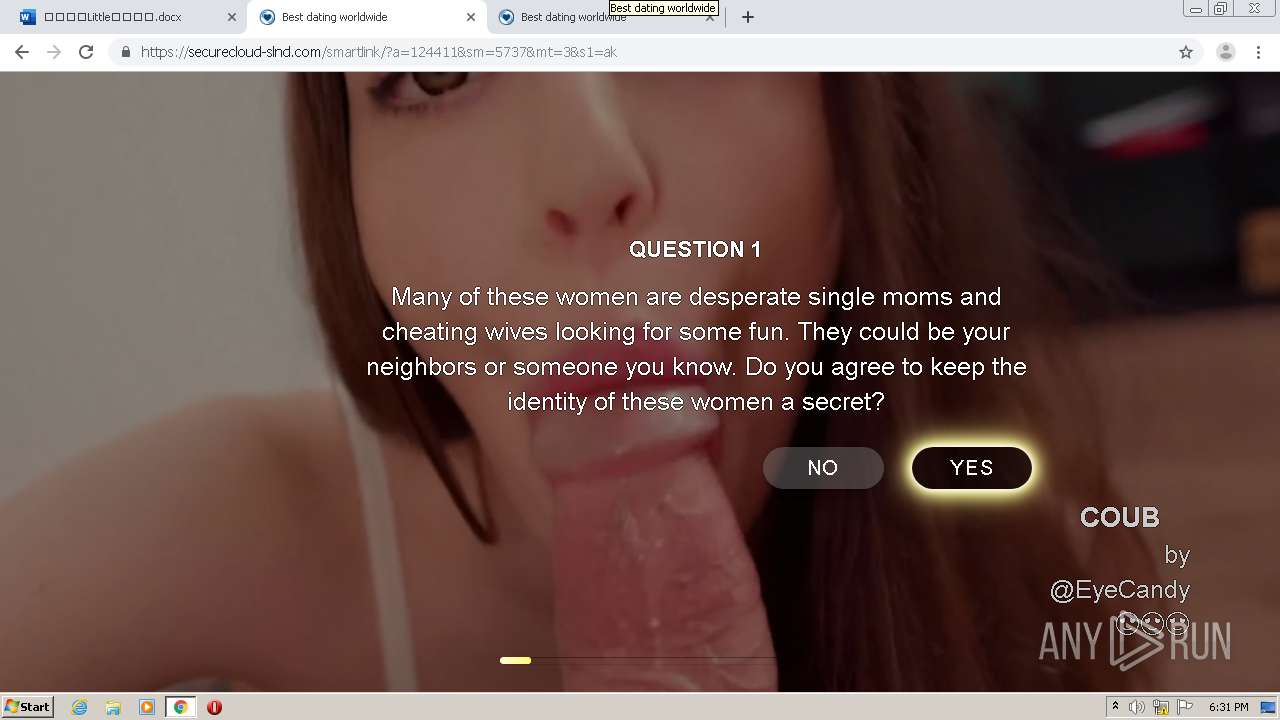
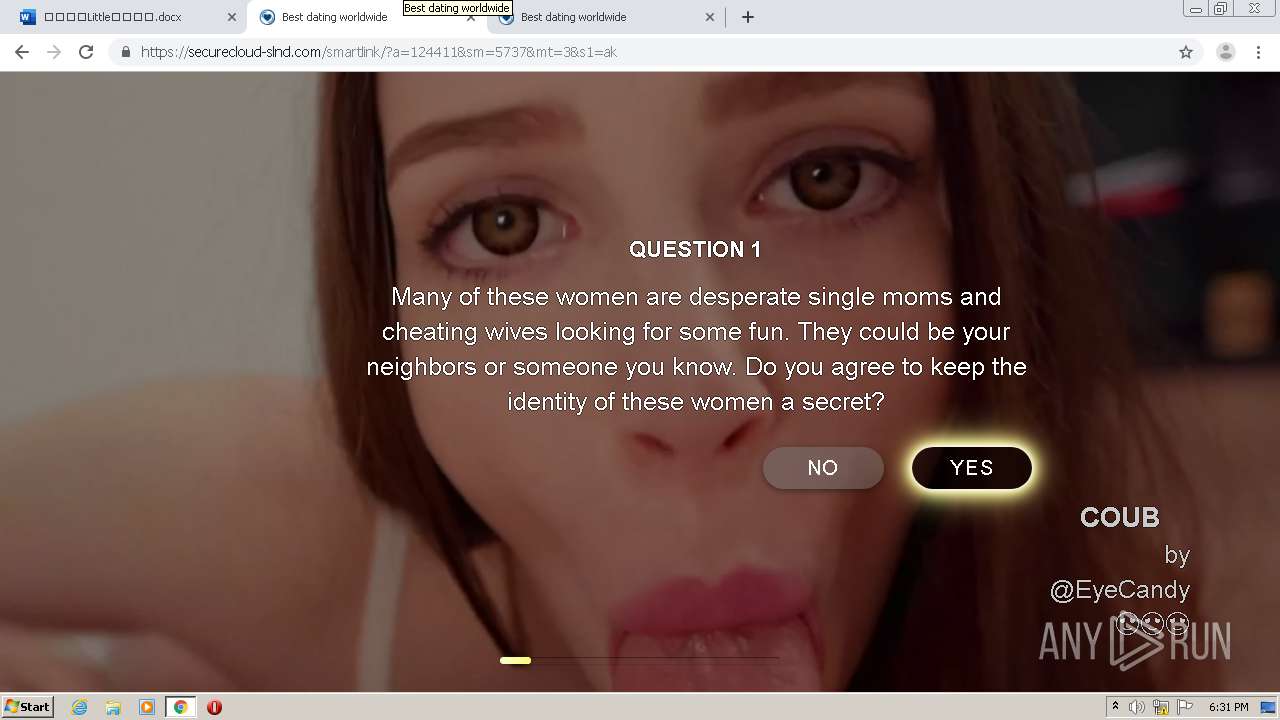
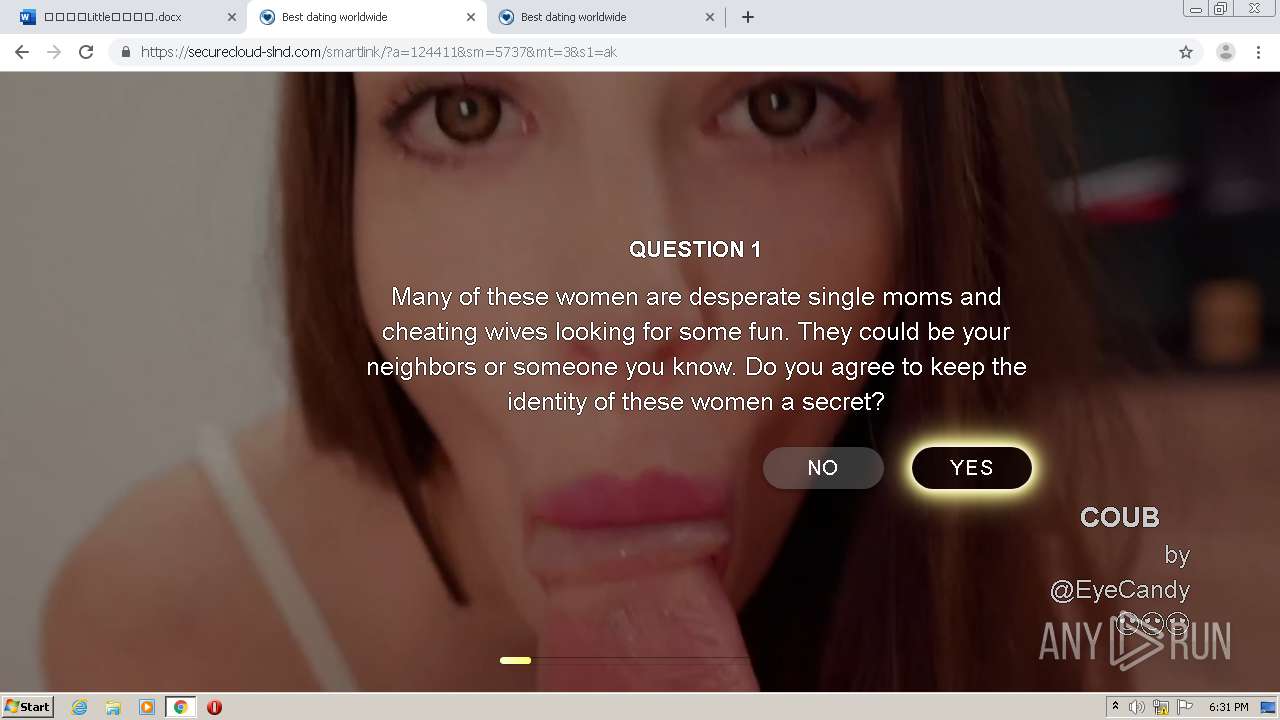
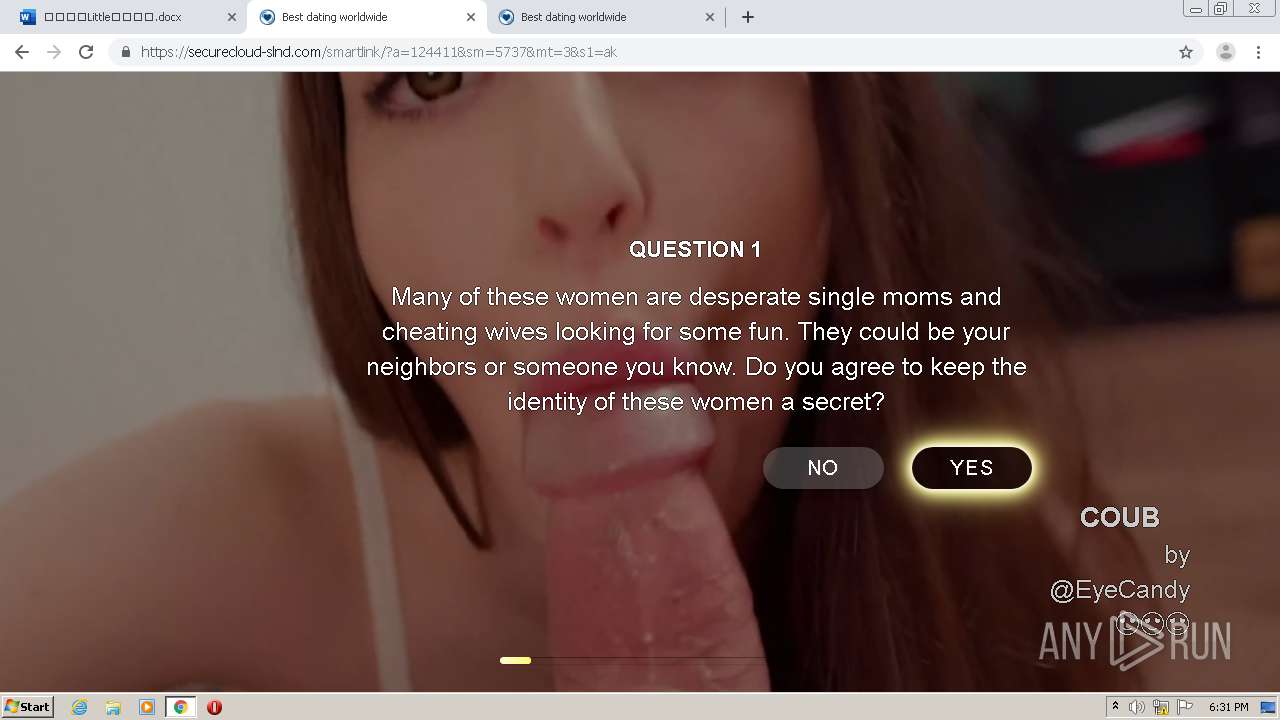
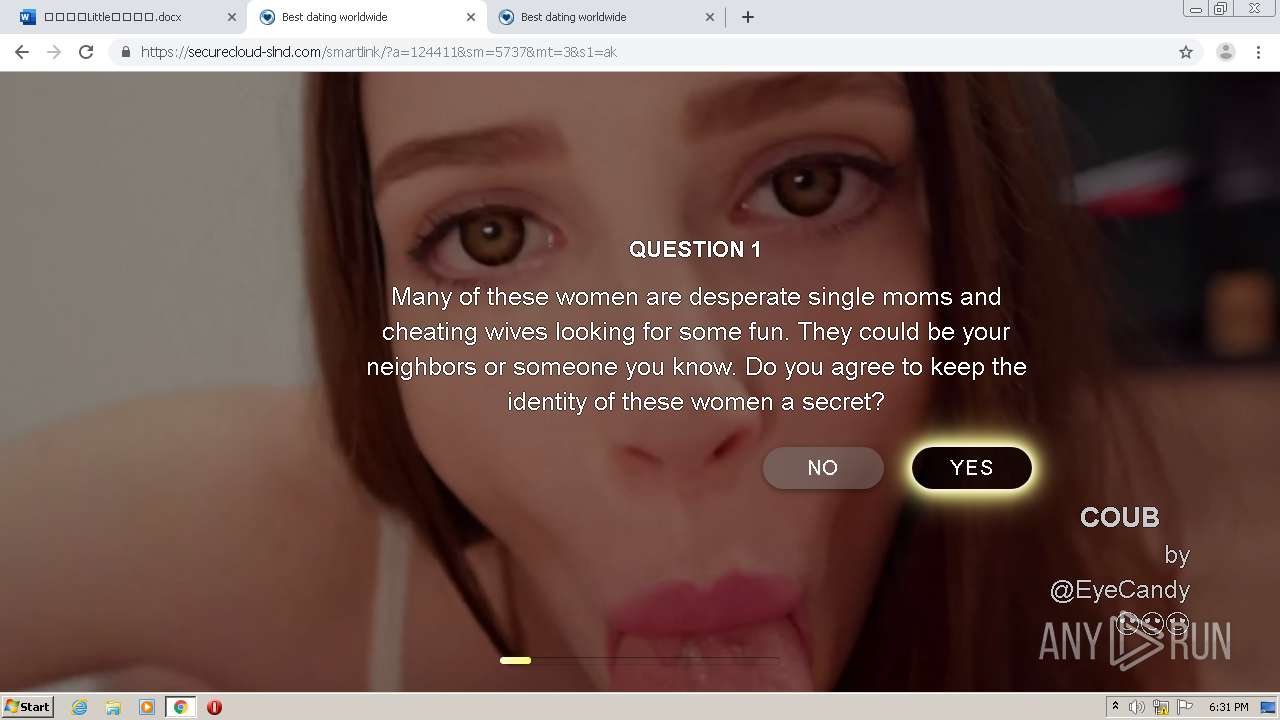
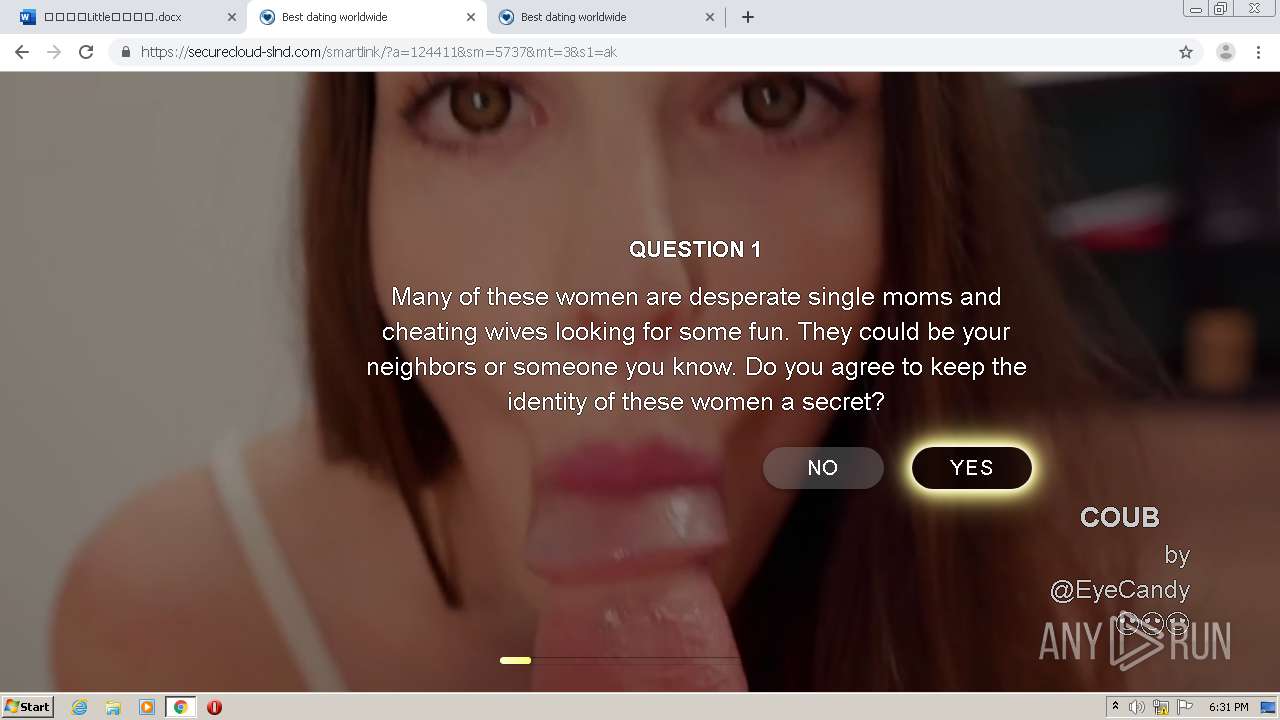
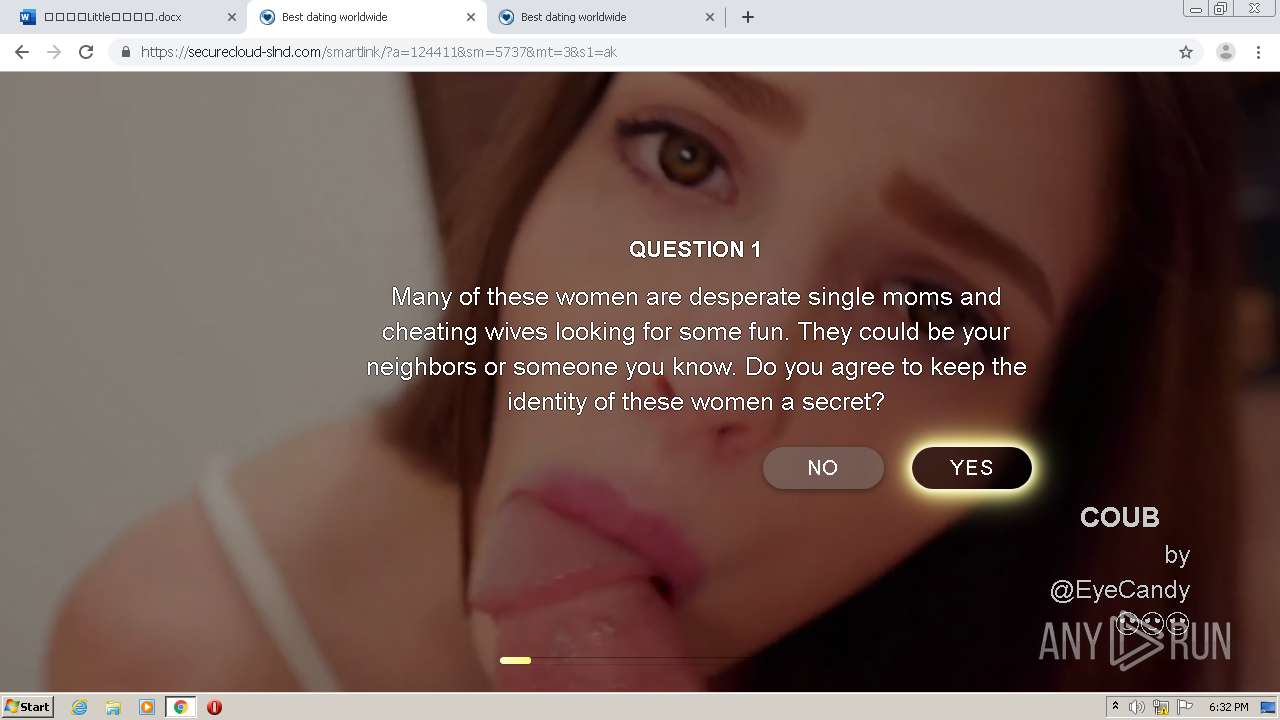
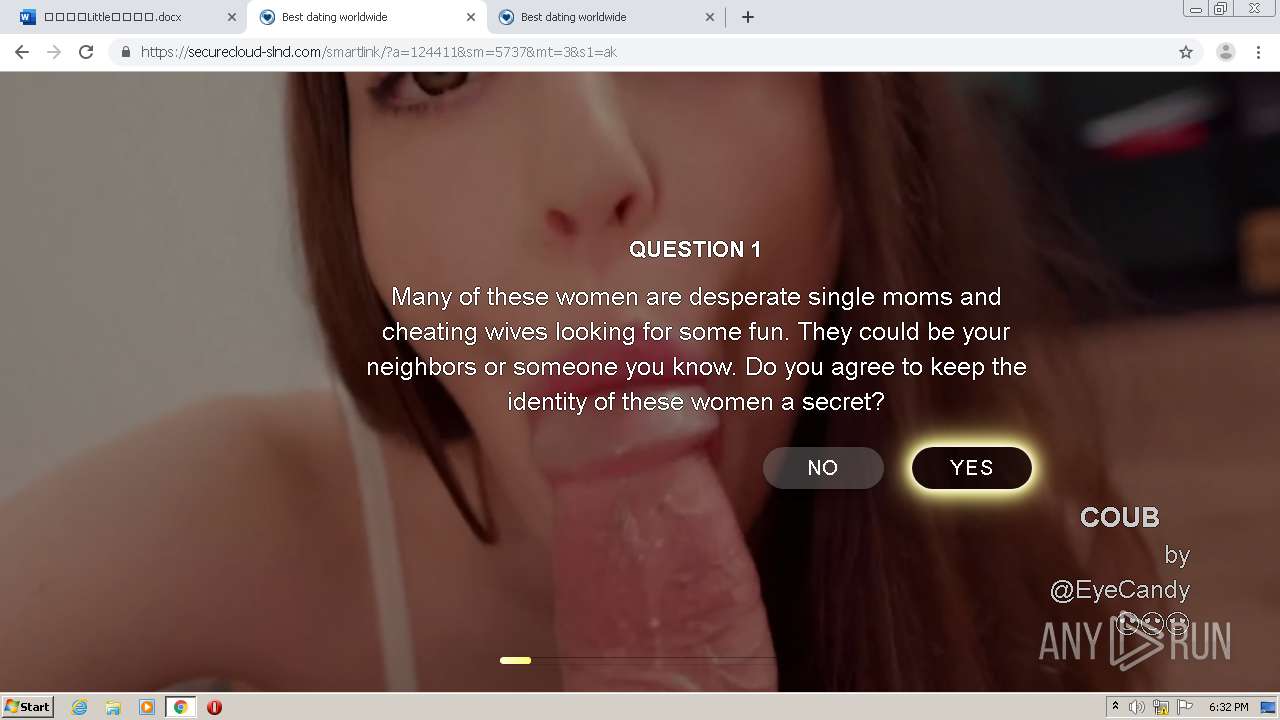
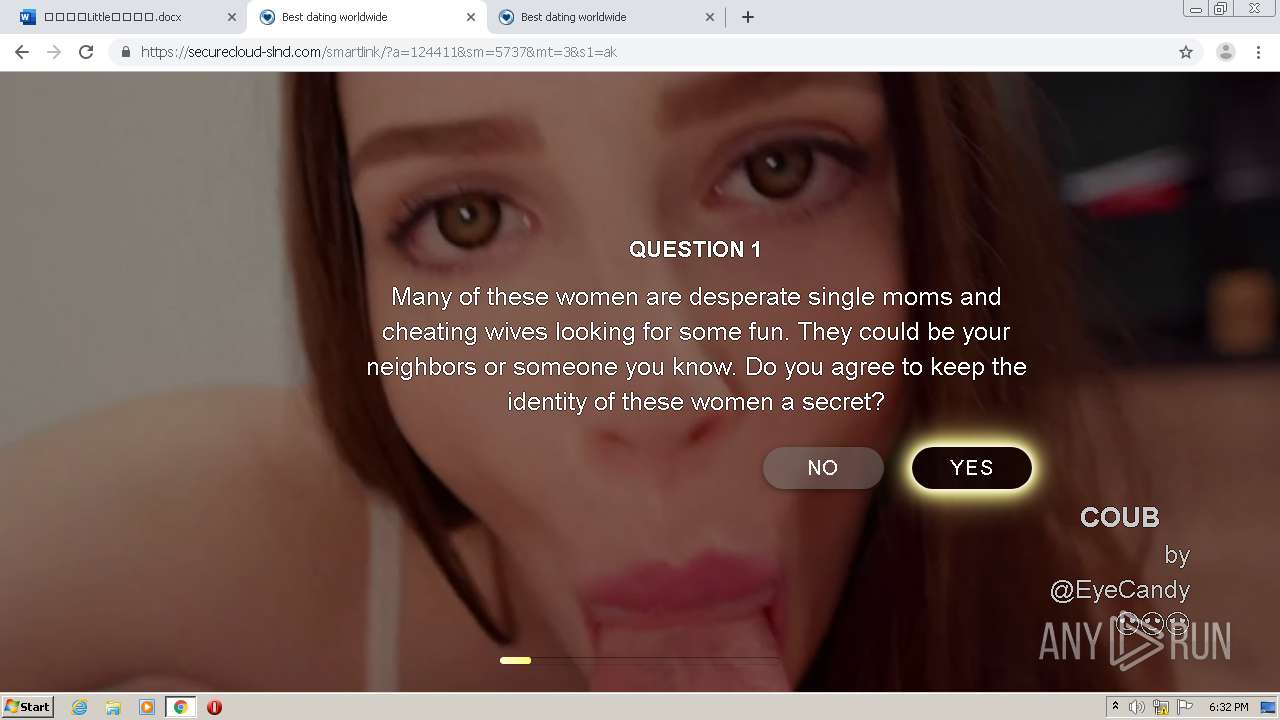
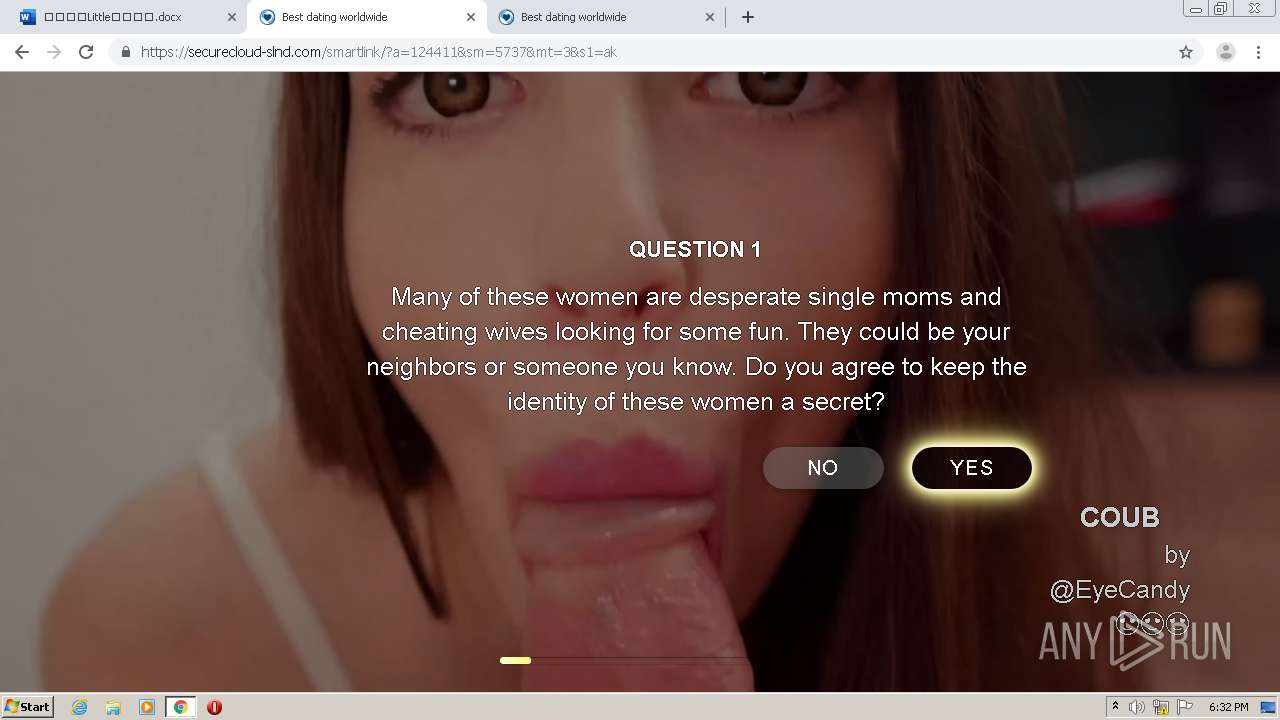
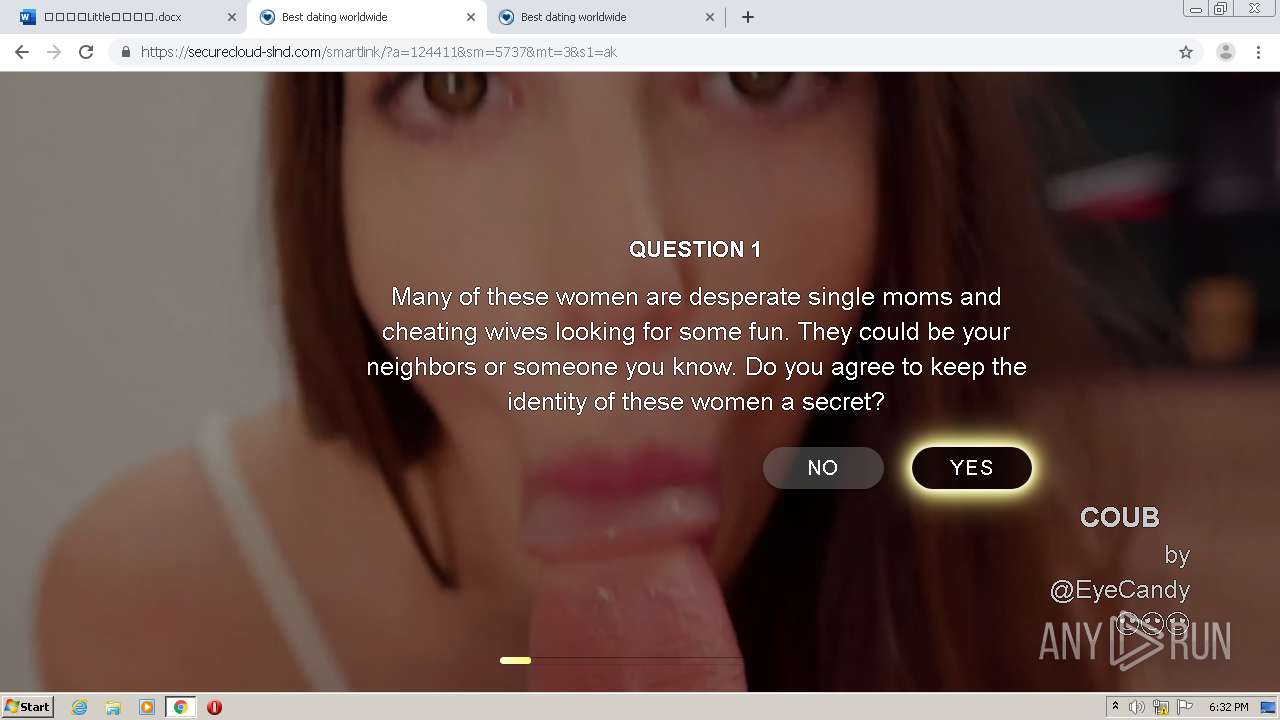
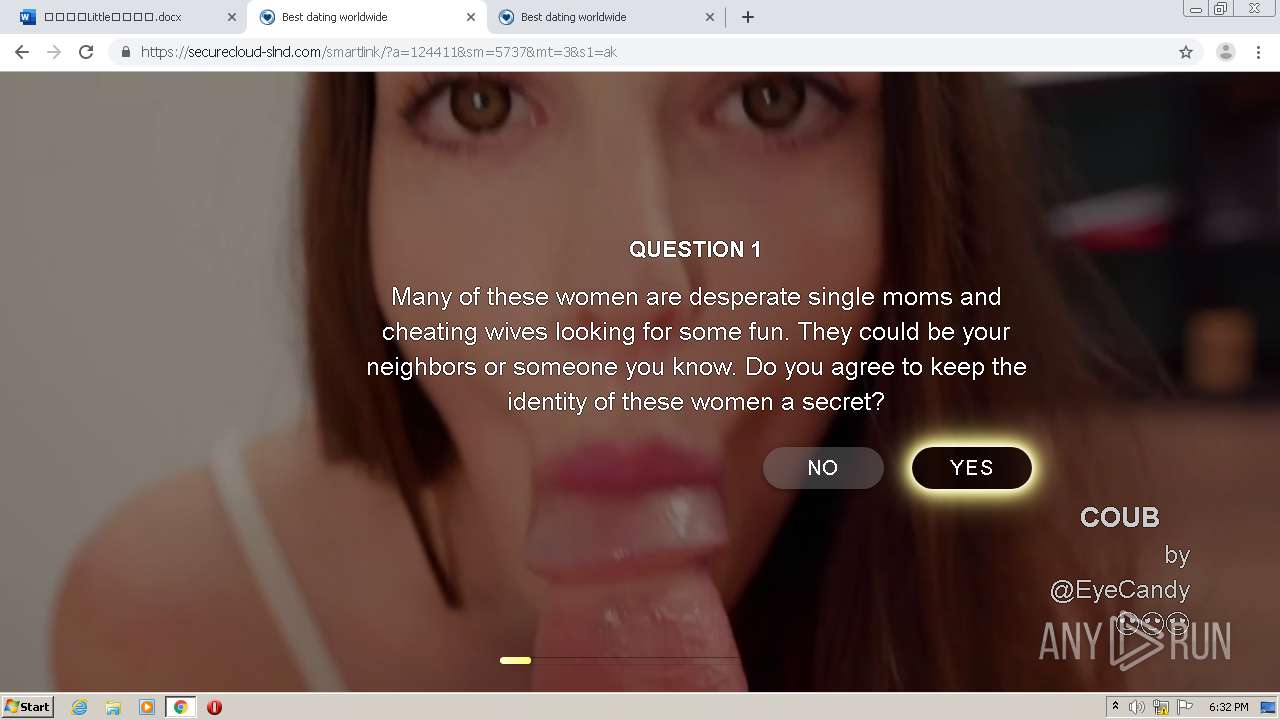
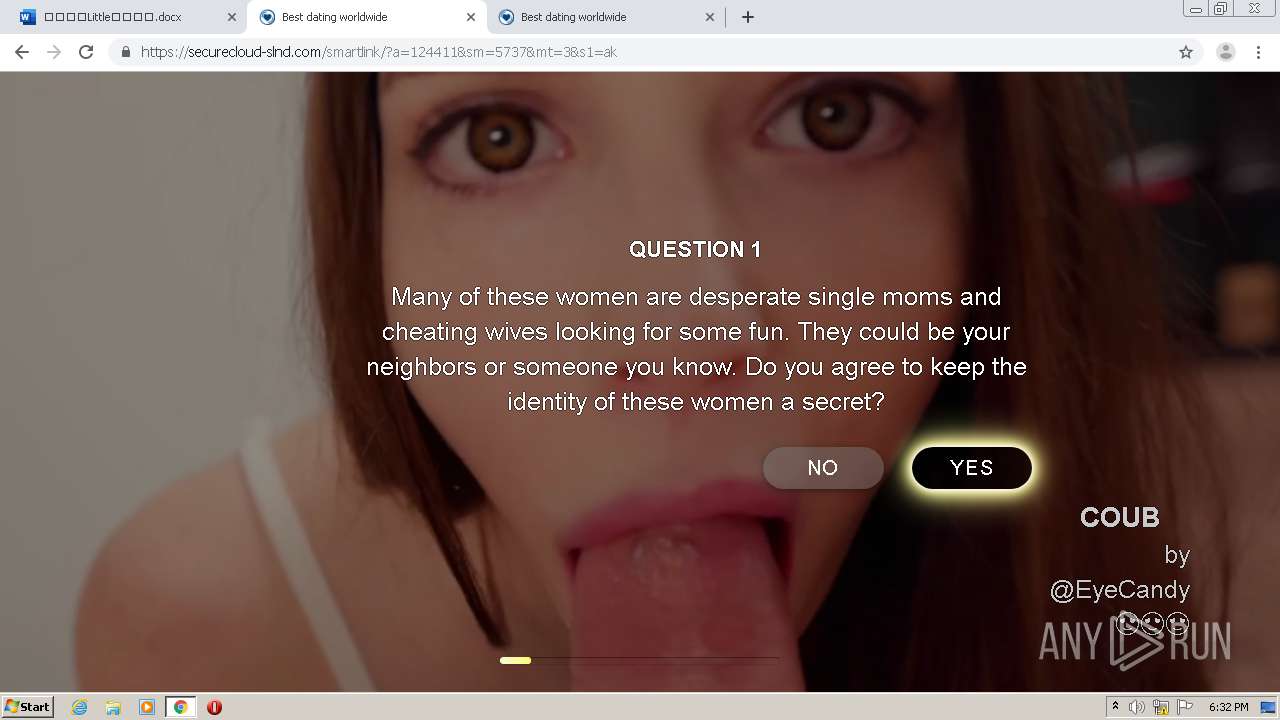
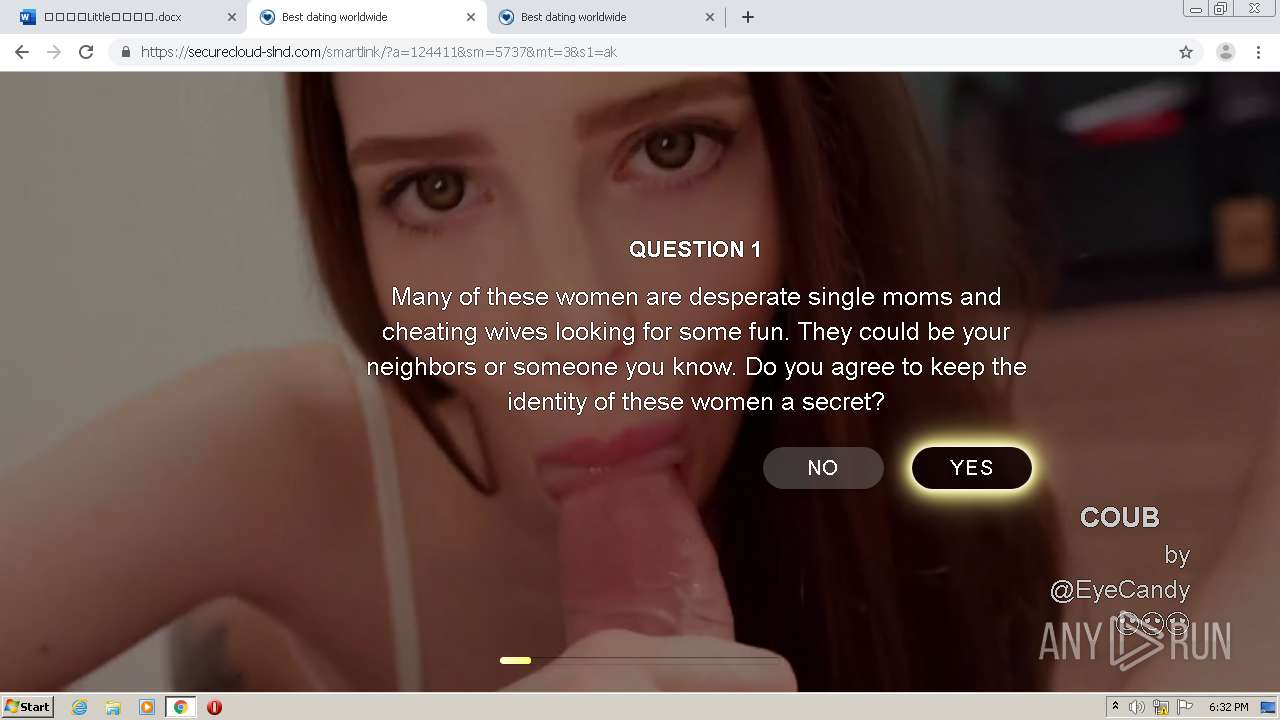
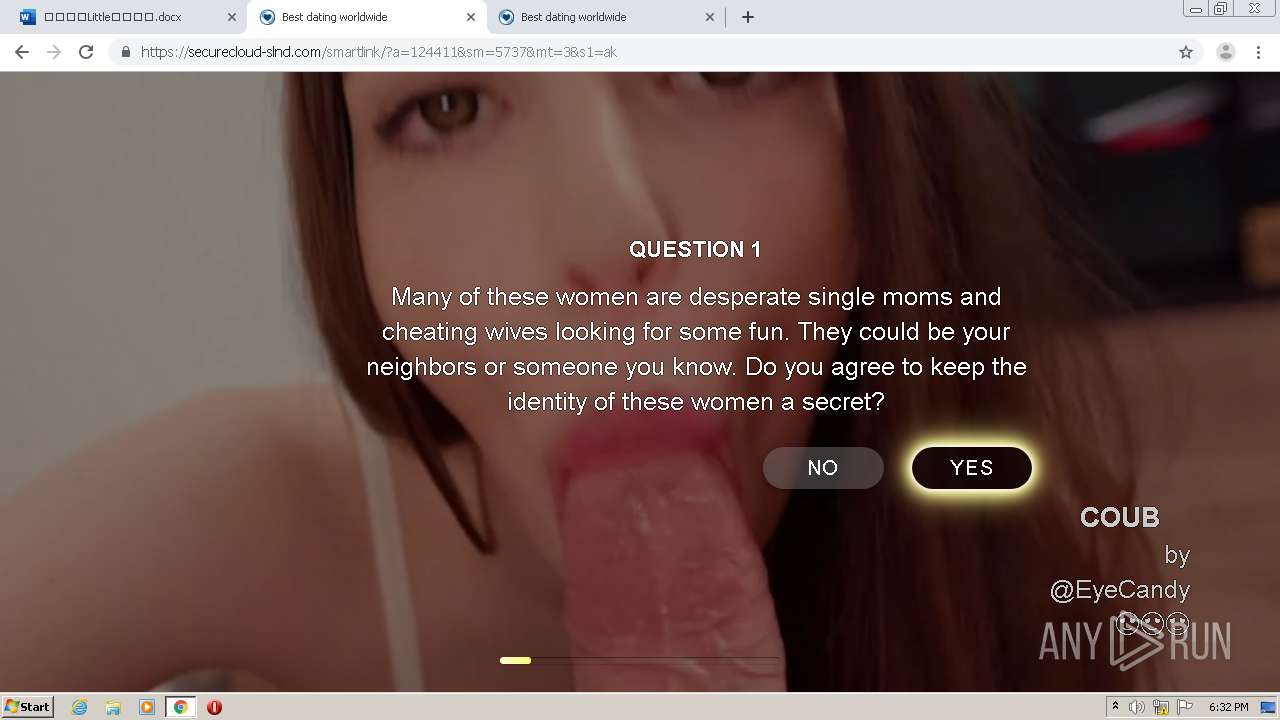
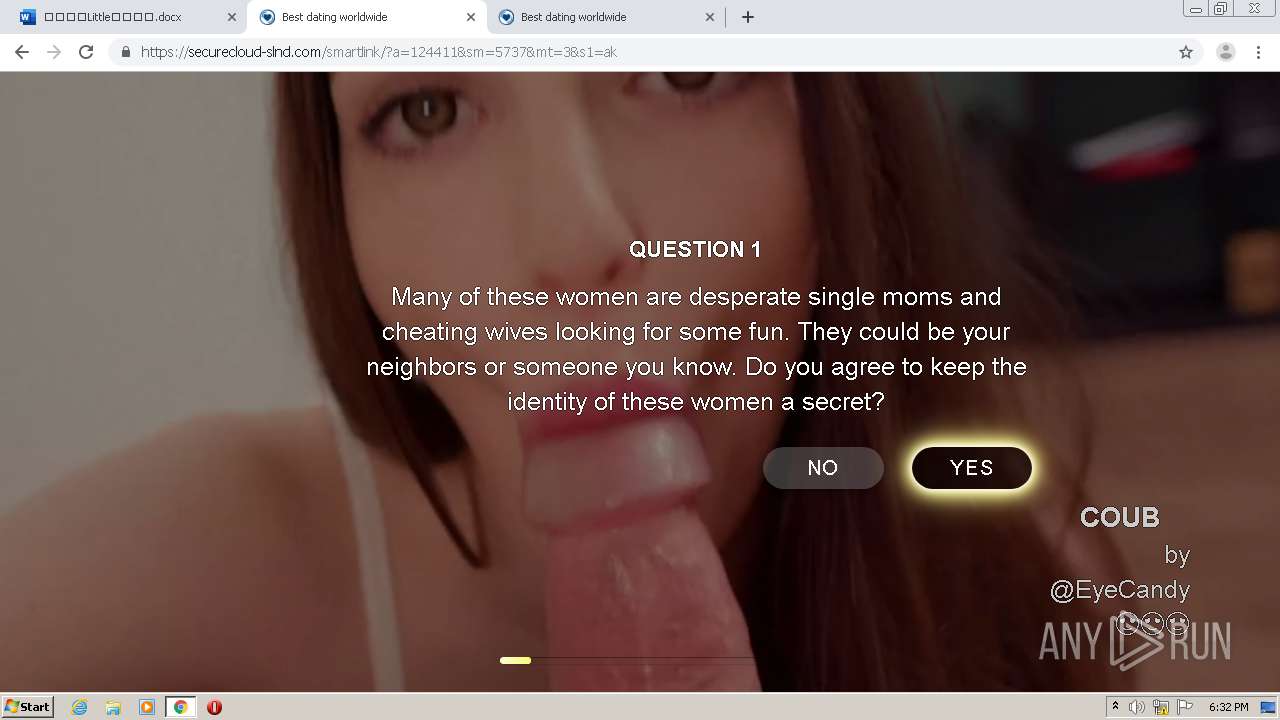
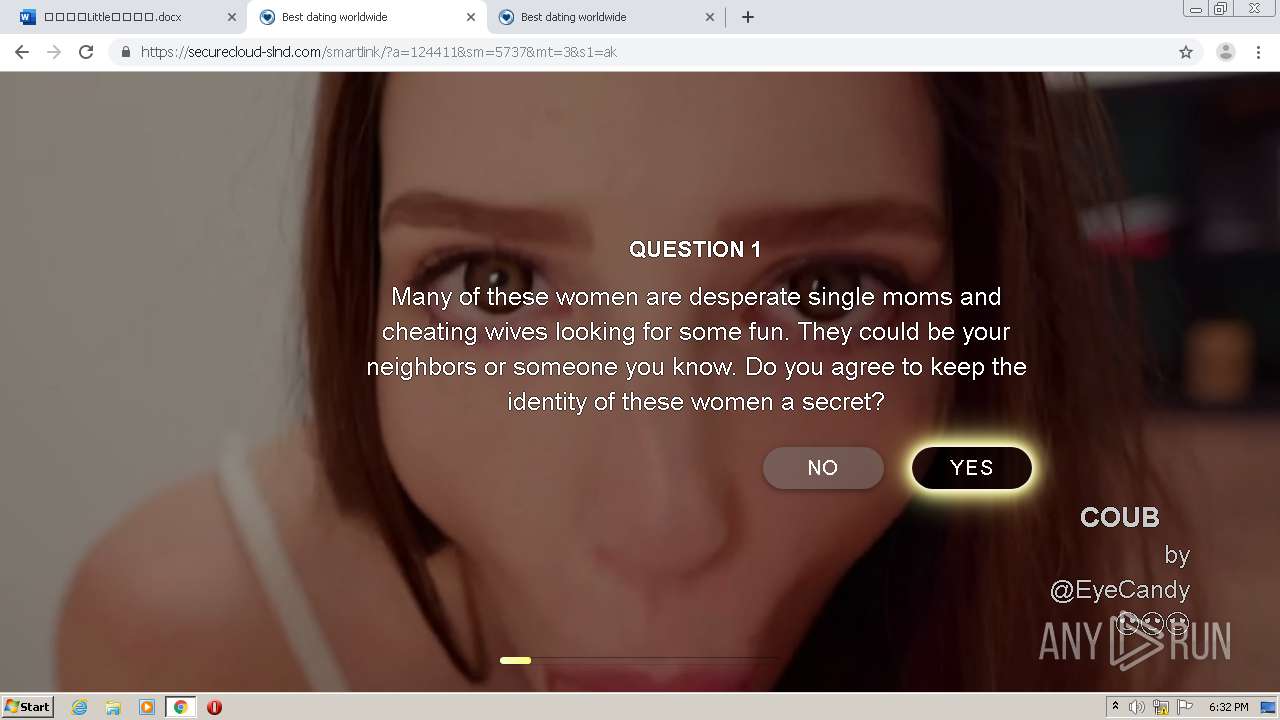
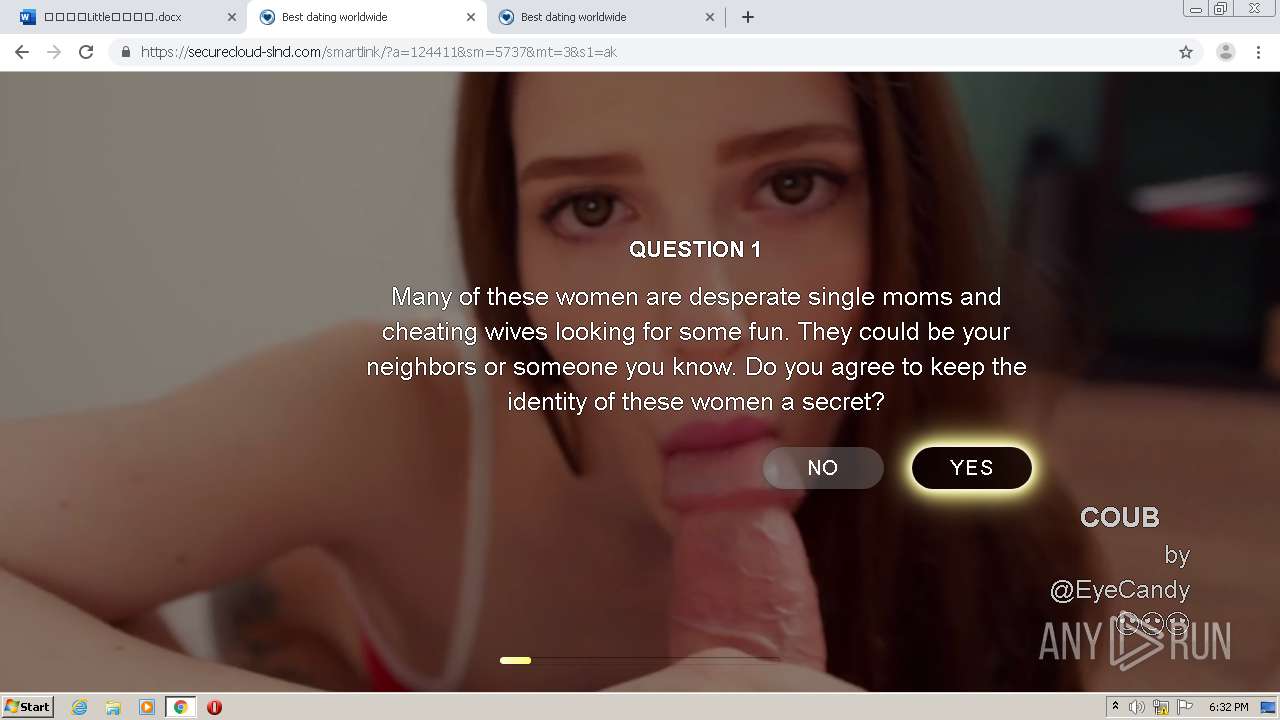
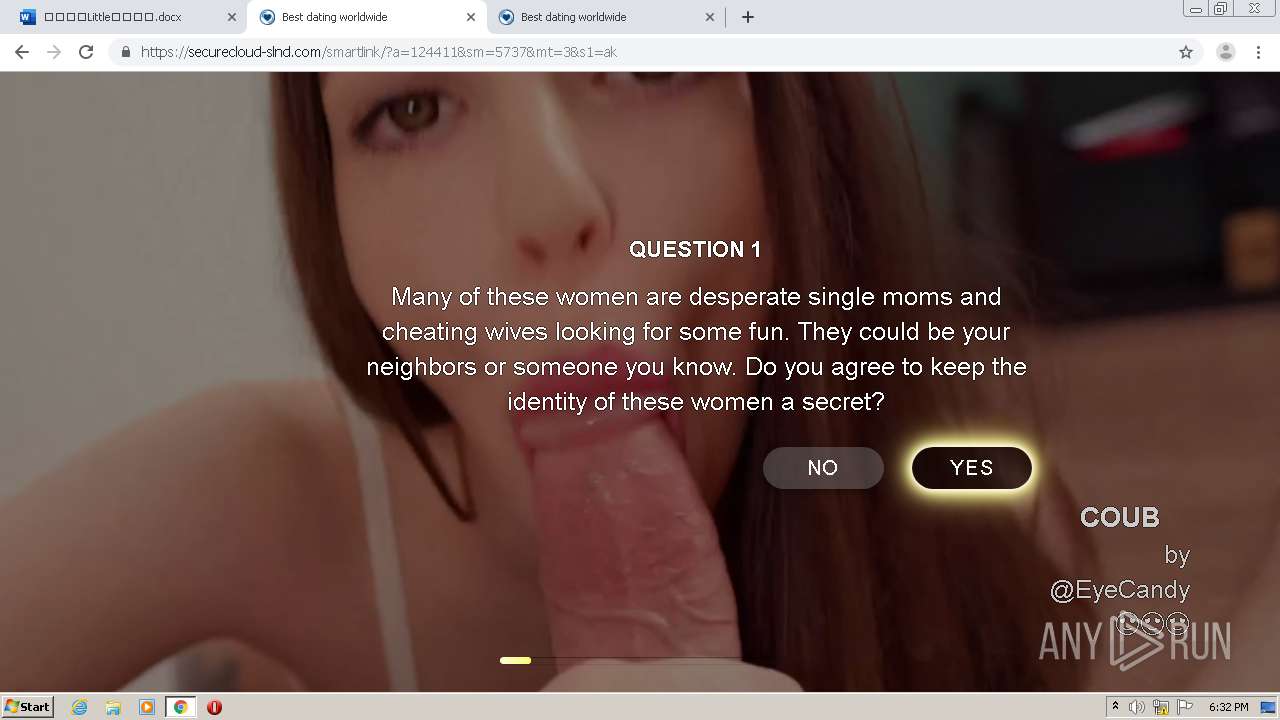
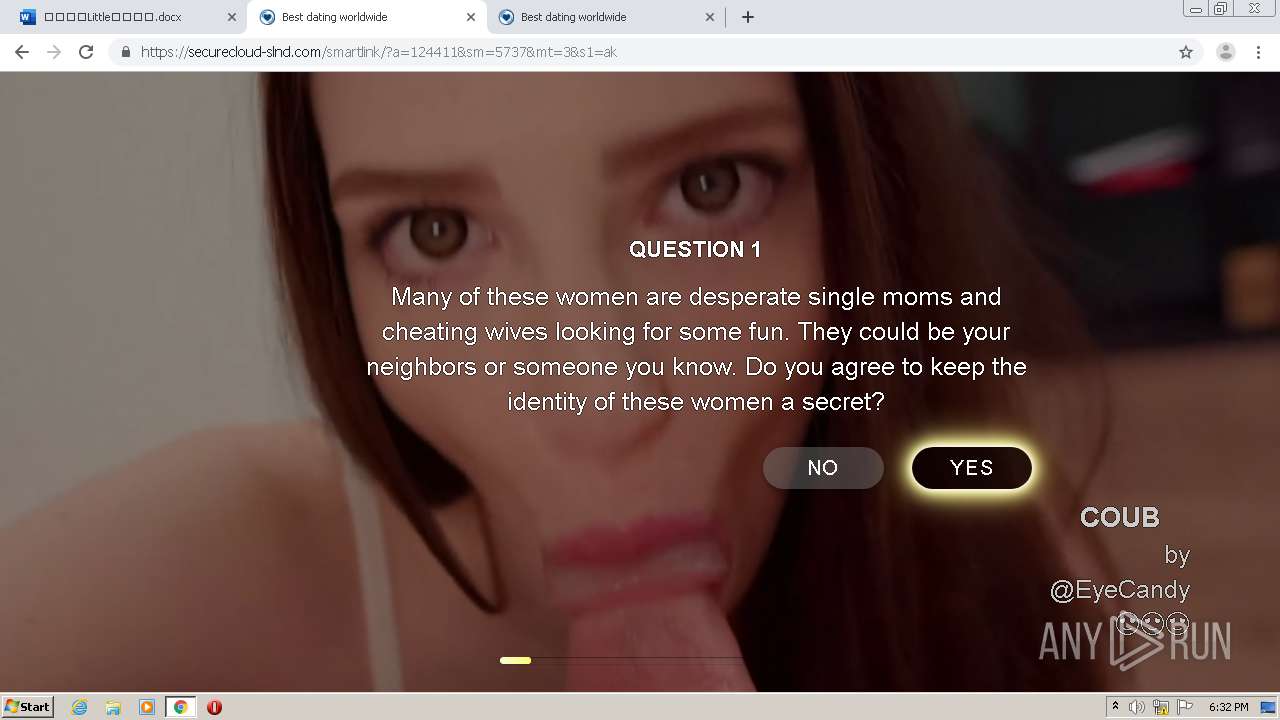
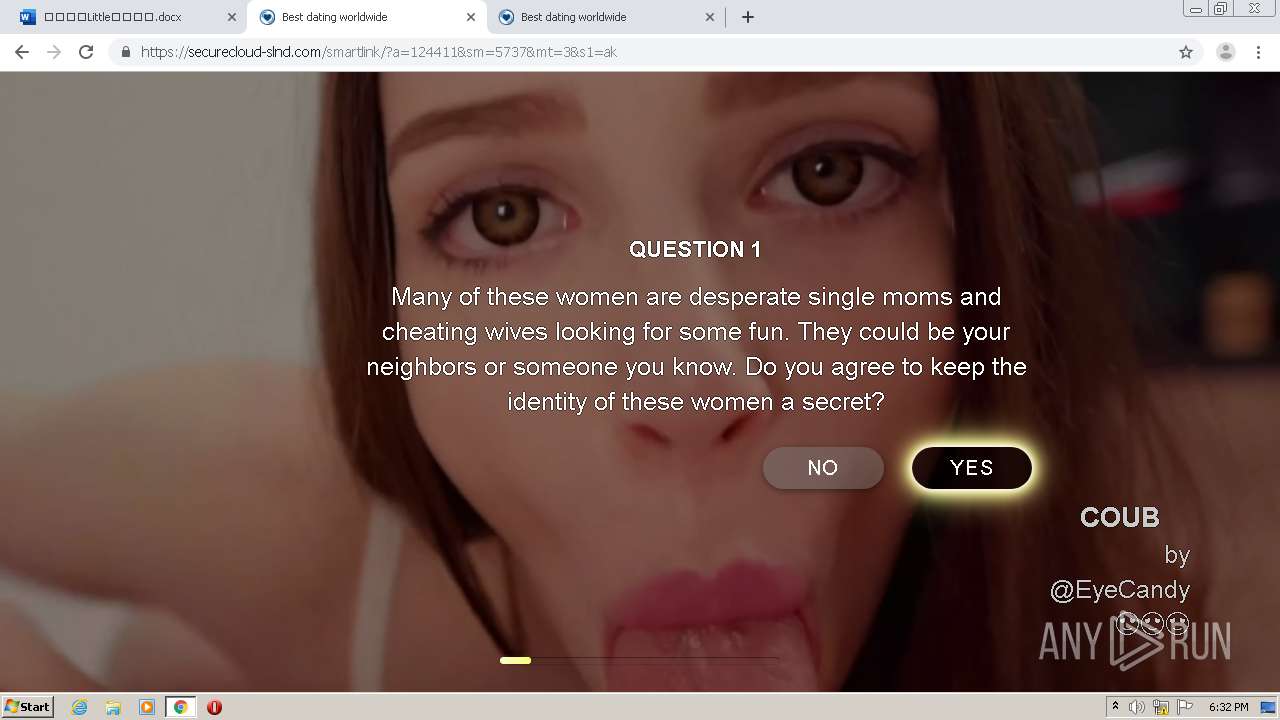
4000 | chrome.exe | GET | 200 | 198.54.116.191:80 | http://photos.xmomlove.com/ | US | compressed | 2.16 Kb | malicious |
4000 | chrome.exe | GET | 200 | 198.54.116.191:80 | http://photos.xmomlove.com/css/font-icons.css | US | compressed | 61.1 Kb | malicious |
4000 | chrome.exe | GET | 200 | 198.54.116.191:80 | http://photos.xmomlove.com/css/style.css | US | compressed | 12.3 Kb | malicious |
4000 | chrome.exe | GET | 200 | 198.54.116.191:80 | http://photos.xmomlove.com/css/magnific-popup.css | US | compressed | 1.91 Kb | malicious |
4000 | chrome.exe | GET | 200 | 198.54.116.191:80 | http://photos.xmomlove.com/css/spacings.css | US | compressed | 1.42 Kb | malicious |
4000 | chrome.exe | GET | 200 | 198.54.116.191:80 | http://photos.xmomlove.com/css/rev-slider.css | US | compressed | 12.0 Kb | malicious |
4000 | chrome.exe | GET | 200 | 198.54.116.191:80 | http://photos.xmomlove.com/css/sliders.css | US | compressed | 1.79 Kb | malicious |
4000 | chrome.exe | GET | 200 | 198.54.116.191:80 | http://photos.xmomlove.com/css/animate.css | US | compressed | 4.05 Kb | malicious |
4000 | chrome.exe | GET | 200 | 198.54.116.191:80 | http://photos.xmomlove.com/css/responsive.css | US | compressed | 1.65 Kb | malicious |
4000 | chrome.exe | GET | 200 | 198.54.116.191:80 | http://photos.xmomlove.com/ | US | compressed | 2.16 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4000 | chrome.exe | 13.107.6.171:443 | word-view.officeapps.live.com | Microsoft Corporation | US | whitelisted |
4000 | chrome.exe | 216.58.212.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
4000 | chrome.exe | 52.114.159.34:443 | browser.events.data.microsoft.com | Microsoft Corporation | US | unknown |
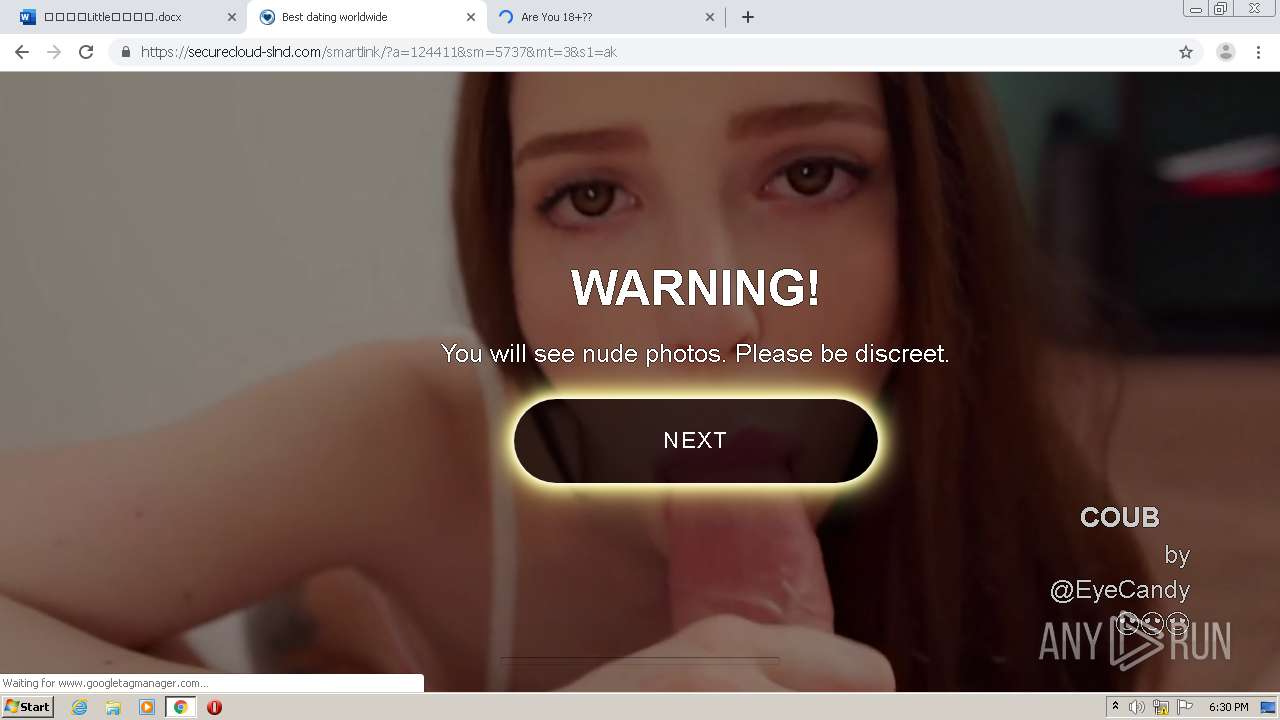
4000 | chrome.exe | 13.107.246.13:443 | amcdn.msftauth.net | Microsoft Corporation | US | suspicious |
4000 | chrome.exe | 52.109.124.71:443 | messaging.office.com | Microsoft Corporation | SG | suspicious |
4000 | chrome.exe | 13.104.158.179:443 | storage.live.com | Microsoft Corporation | US | unknown |
4000 | chrome.exe | 40.126.31.137:443 | login.live.com | Microsoft Corporation | US | suspicious |
4000 | chrome.exe | 172.217.23.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
4000 | chrome.exe | 198.54.116.191:80 | photos.xmomlove.com | Namecheap, Inc. | US | malicious |
4000 | chrome.exe | 40.122.160.14:443 | browser.pipe.aria.microsoft.com | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mygavilan-my.sharepoint.com |
| suspicious |
accounts.google.com |
| shared |
c1-word-view-15.cdn.office.net |
| whitelisted |
modern.akamai.odsp.cdn.office.net |
| whitelisted |
word-view.officeapps.live.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
clients1.google.com |
| whitelisted |
browser.events.data.microsoft.com |
| whitelisted |
messaging.office.com |
| whitelisted |
amcdn.msftauth.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4000 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
4000 | chrome.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |
4000 | chrome.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |