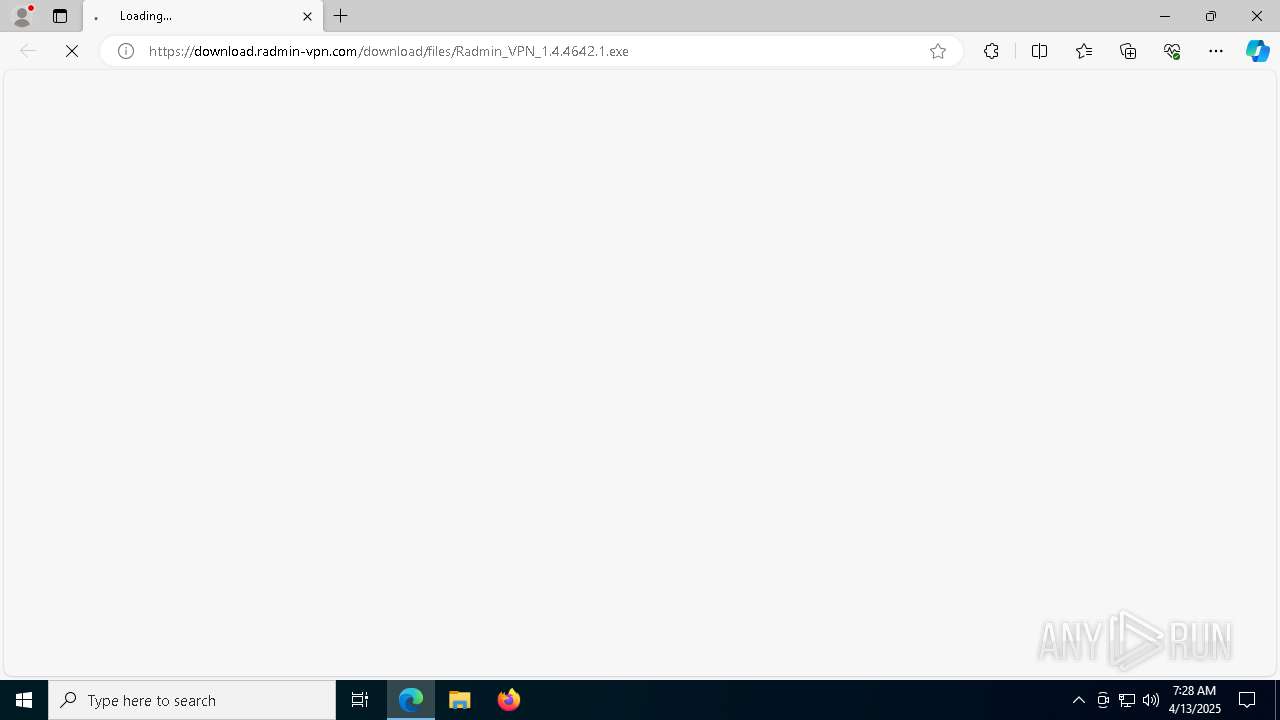
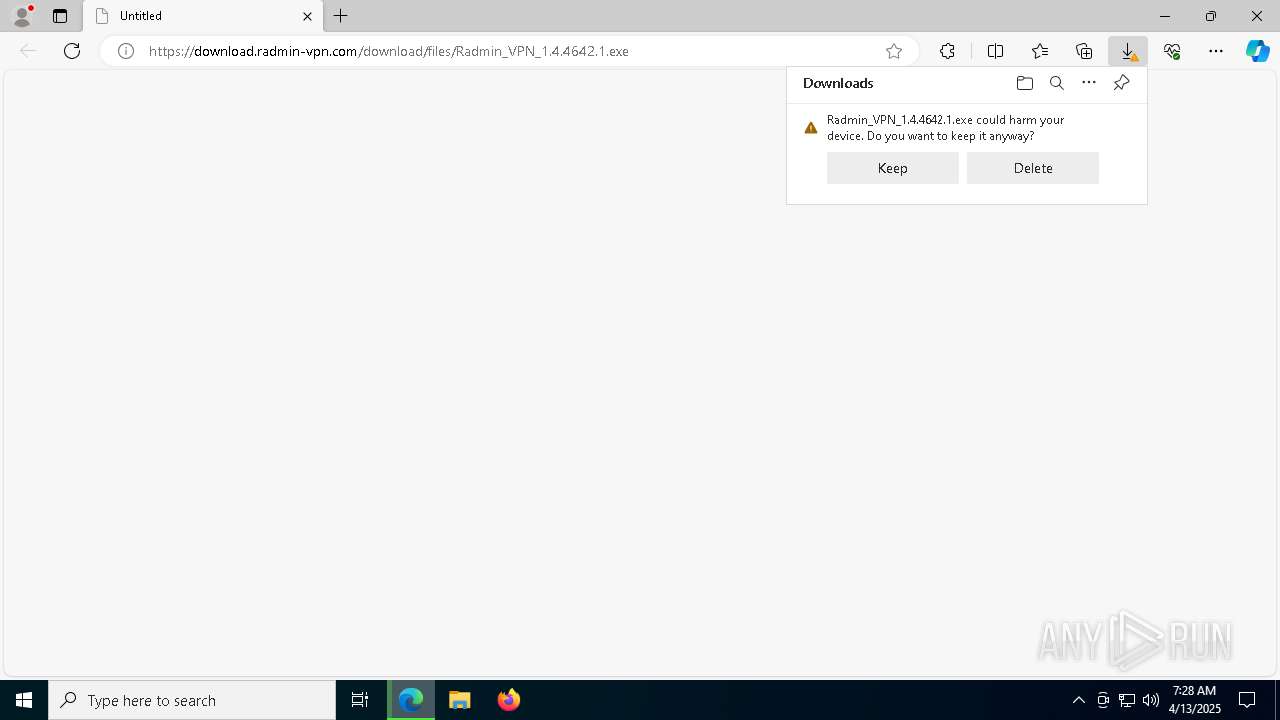
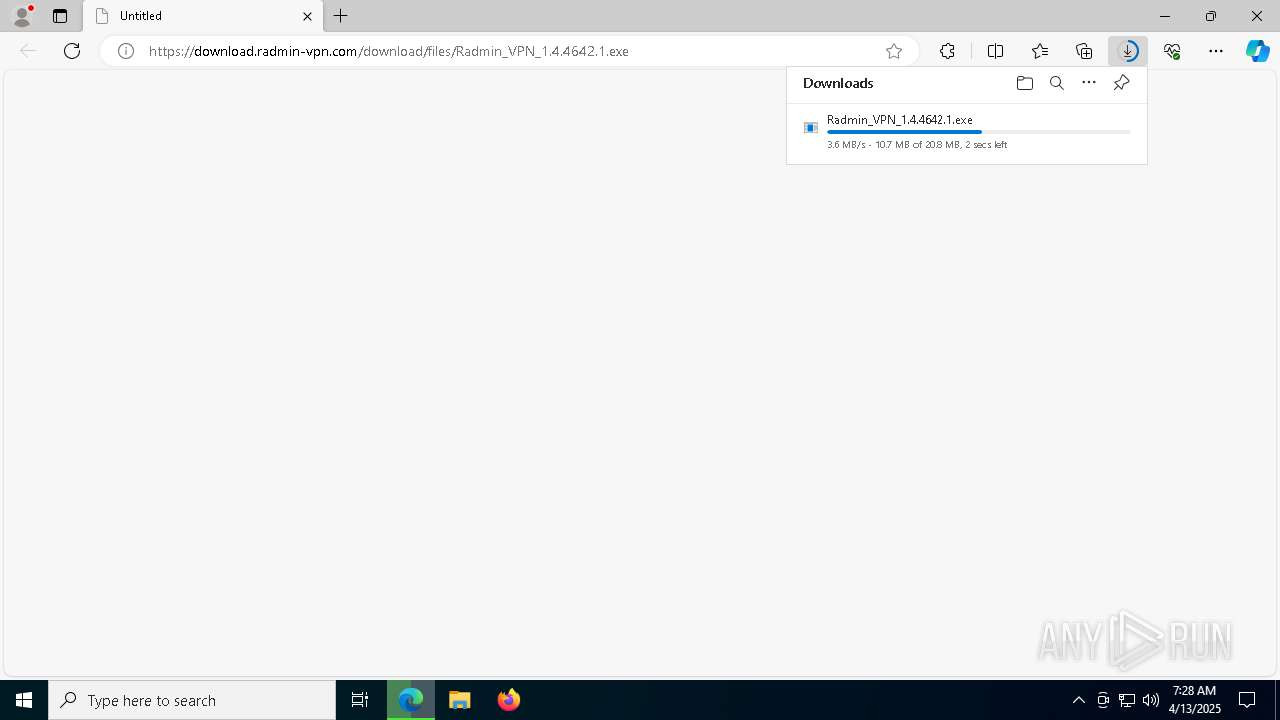
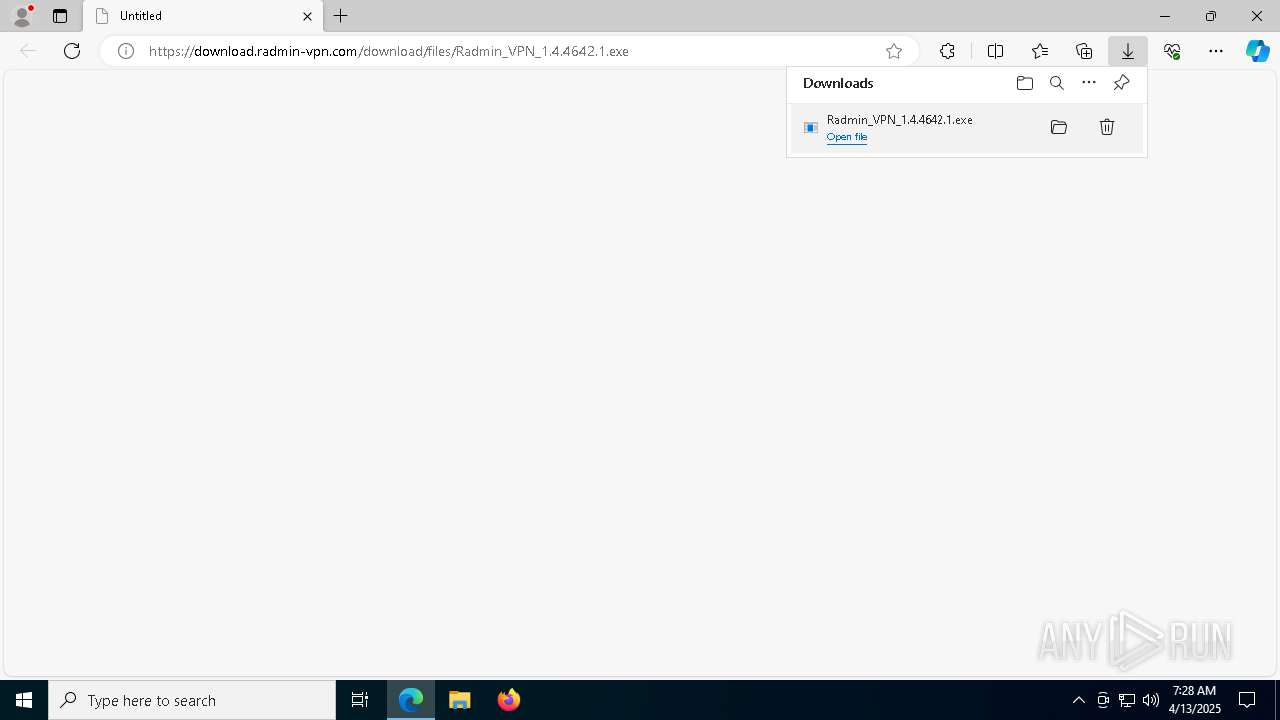
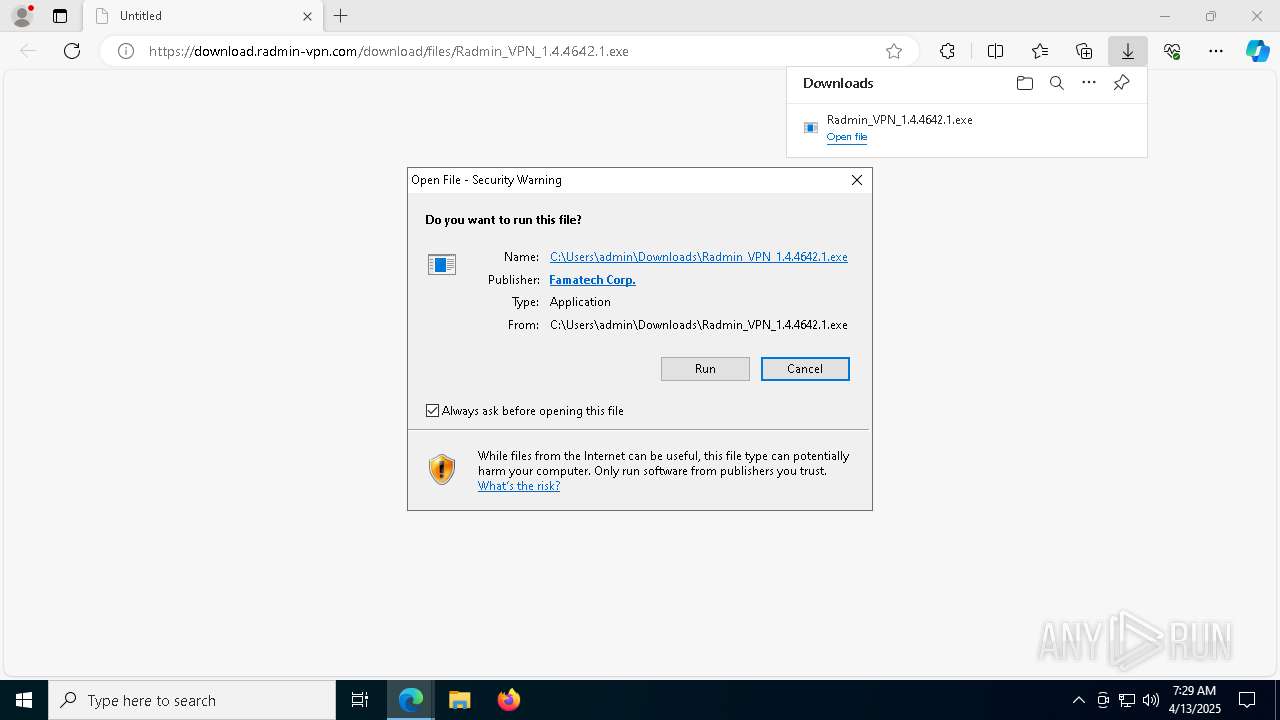
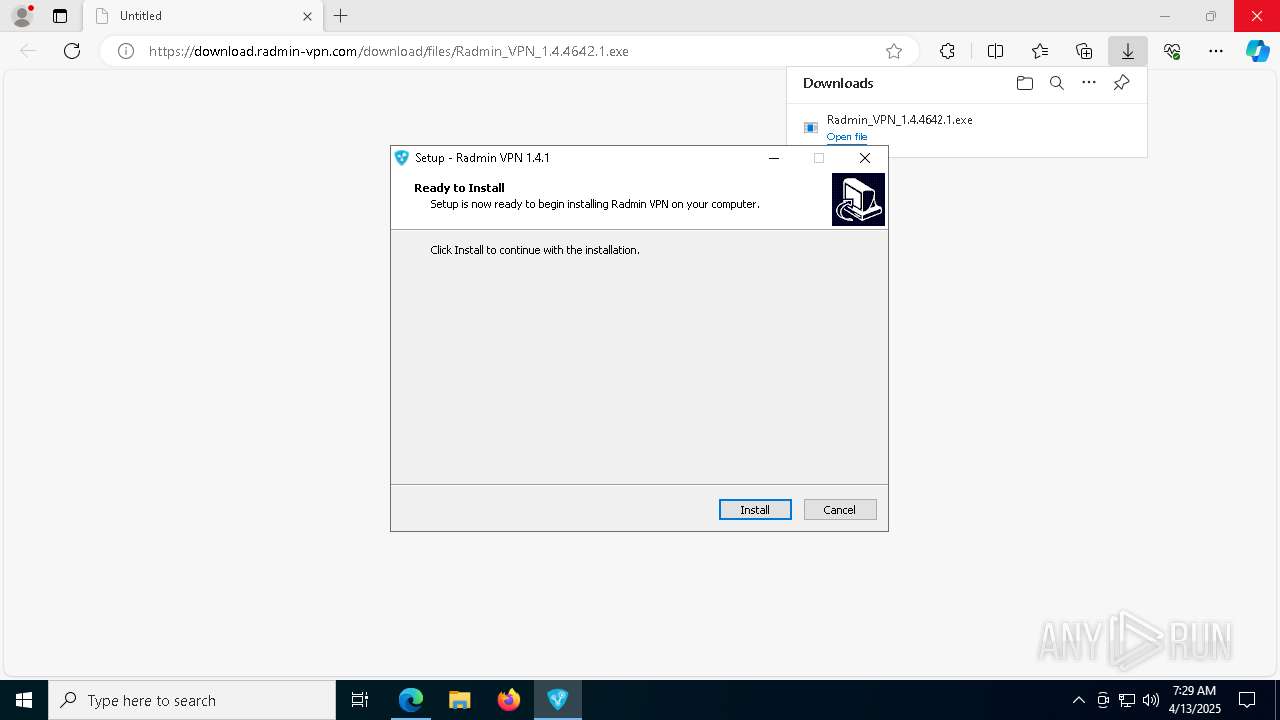
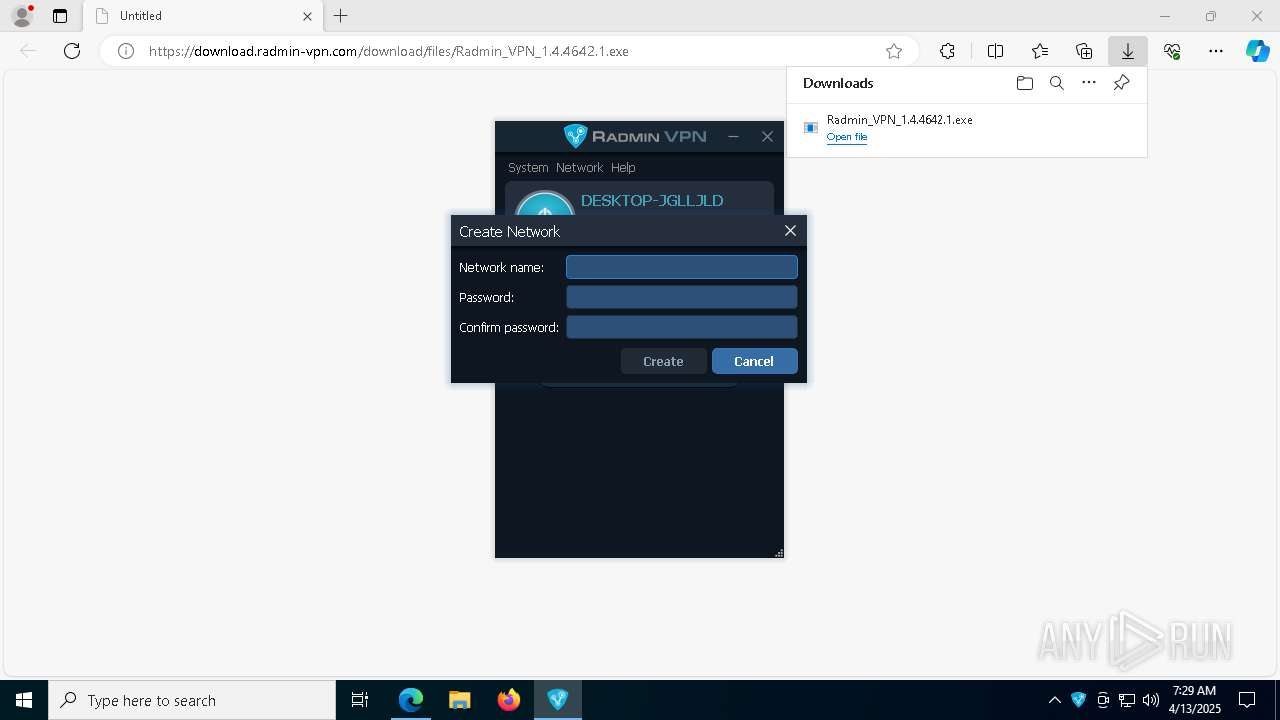
| URL: | https://download.radmin-vpn.com/download/files/Radmin_VPN_1.4.4642.1.exe |
| Full analysis: | https://app.any.run/tasks/e25716f8-8ca1-4203-be84-c7d0d2fafa94 |
| Verdict: | Malicious activity |
| Analysis date: | April 13, 2025, 07:28:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 5FB8D88B298CA79716BEEF9469666354 |
| SHA1: | A34D7B8D361EABE9A589489C0B24C0755C3F5B3B |
| SHA256: | 4CA0DB8C5DBAE83A85A378CCD88281A60B3683AA90ECCE21242A41D2D1271144 |
| SSDEEP: | 3:N8SElUIZSaKLf4IK6zLG:2SKJZiUN6zLG |
MALICIOUS
Changes the autorun value in the registry
- msiexec.exe (PID: 6728)
SUSPICIOUS
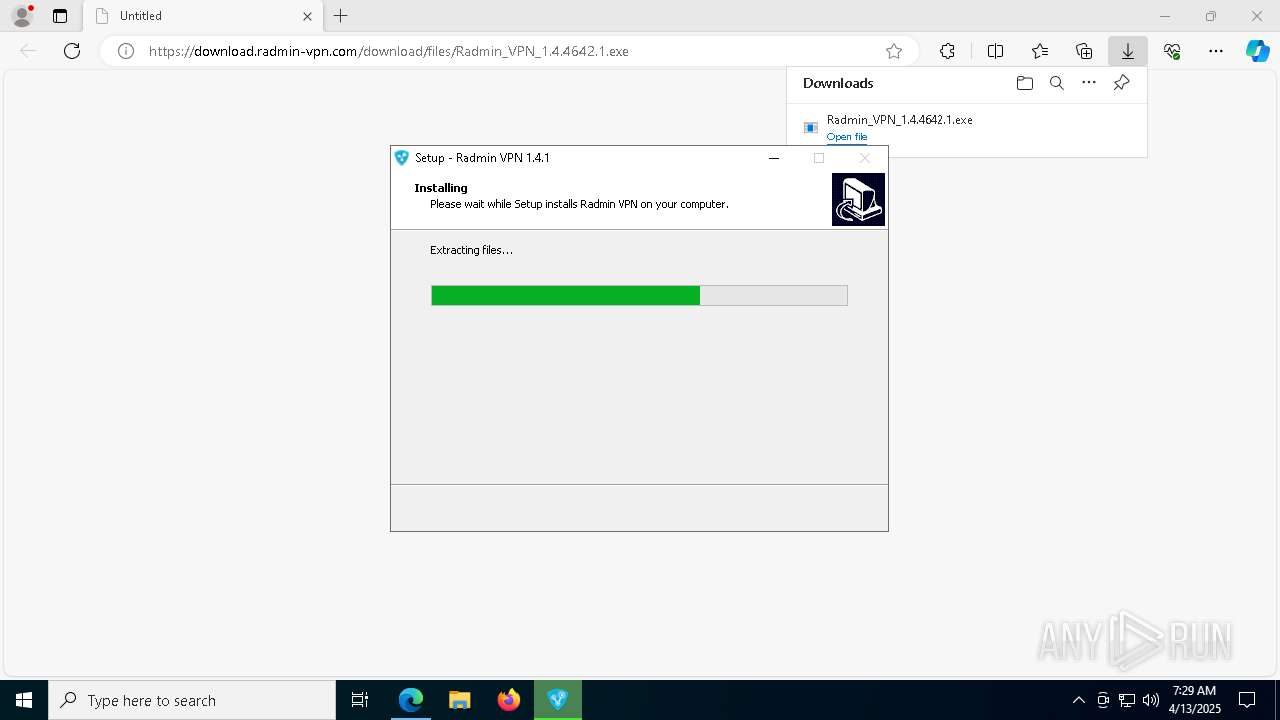
Executable content was dropped or overwritten
- Radmin_VPN_1.4.4642.1.exe (PID: 8248)
- Radmin_VPN_1.4.4642.1.exe (PID: 6392)
- Radmin_VPN_1.4.4642.1.tmp (PID: 1272)
- drvinst.exe (PID: 8620)
- drvinst.exe (PID: 8732)
Reads security settings of Internet Explorer
- Radmin_VPN_1.4.4642.1.tmp (PID: 660)
Process drops legitimate windows executable
- Radmin_VPN_1.4.4642.1.tmp (PID: 1272)
- msiexec.exe (PID: 6728)
Adds/modifies Windows certificates
- msiexec.exe (PID: 6728)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6728)
- Radmin_VPN_1.4.4642.1.tmp (PID: 1272)
Drops a system driver (possible attempt to evade defenses)
- drvinst.exe (PID: 8620)
- msiexec.exe (PID: 6728)
- drvinst.exe (PID: 8732)
Creates files in the driver directory
- drvinst.exe (PID: 8620)
- drvinst.exe (PID: 8732)
- MSI1144.tmp (PID: 5968)
The process creates files with name similar to system file names
- msiexec.exe (PID: 6728)
The process drops C-runtime libraries
- msiexec.exe (PID: 6728)
Uses NETSH.EXE to add a firewall rule or allowed programs
- msiexec.exe (PID: 9032)
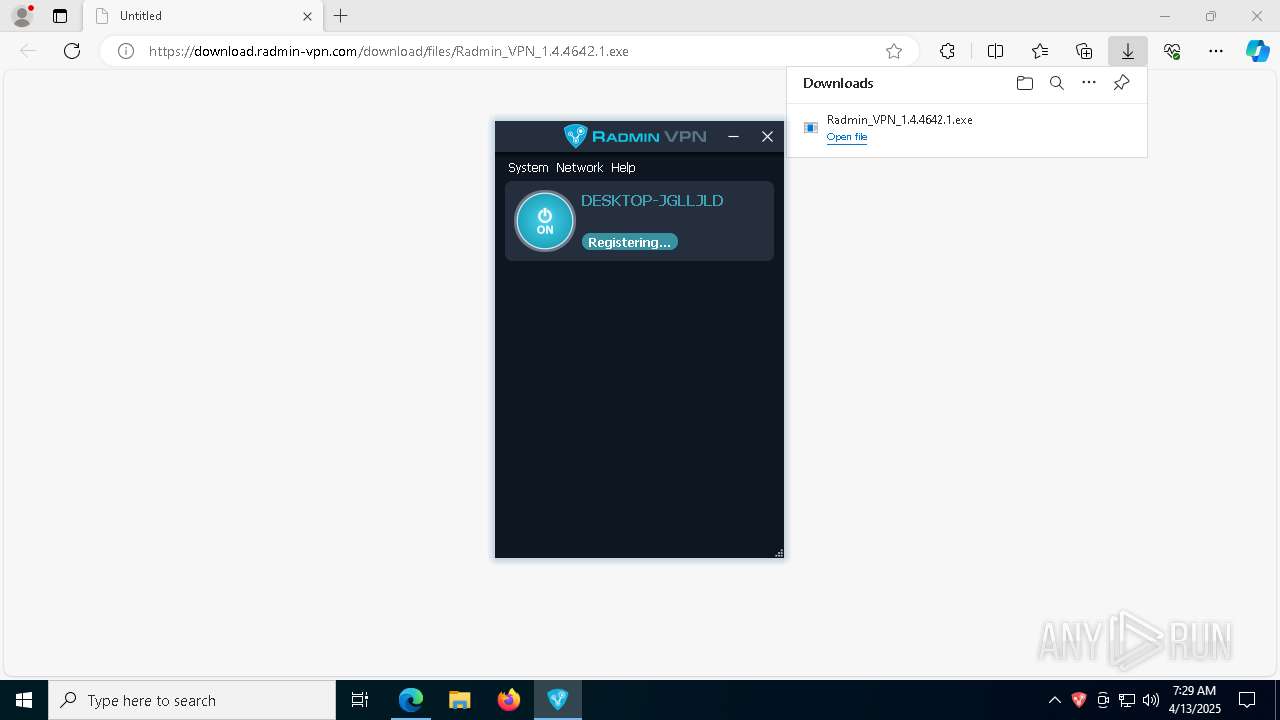
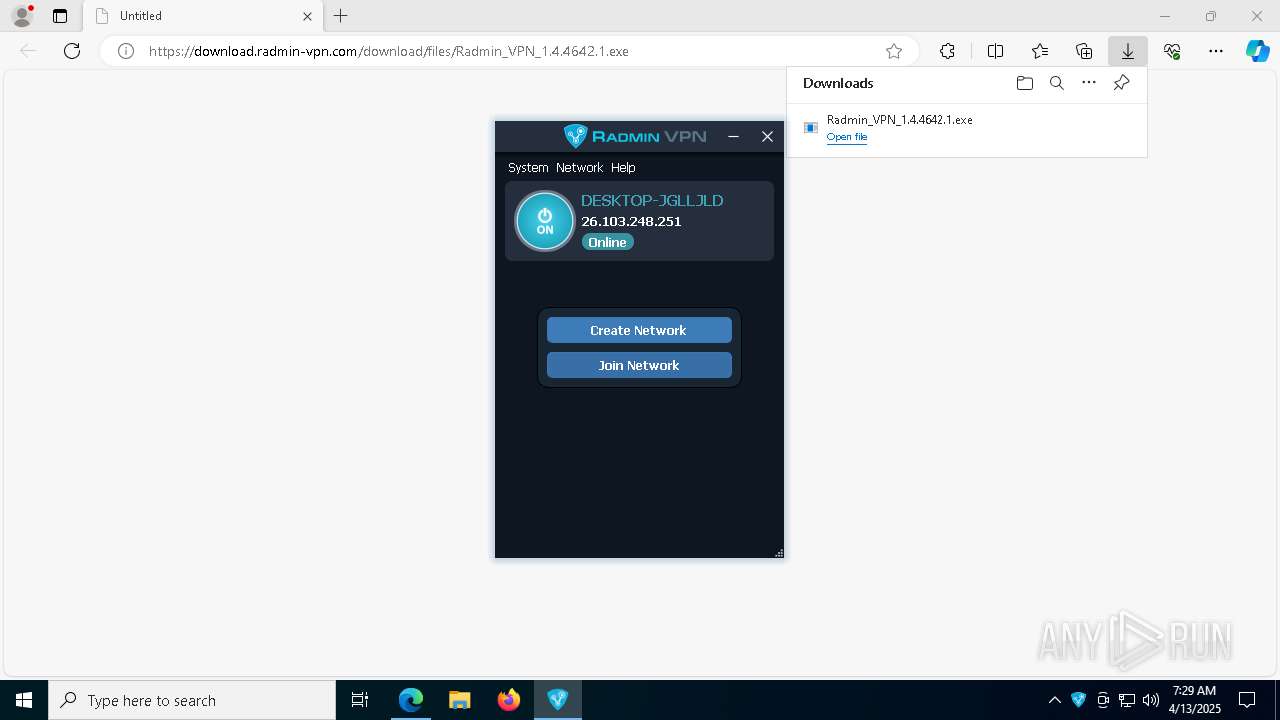
Executes as Windows Service
- RvControlSvc.exe (PID: 2552)
Creates or modifies Windows services
- drvinst.exe (PID: 8732)
Connects to unusual port
- RvControlSvc.exe (PID: 2552)
Starts CMD.EXE for commands execution
- RvControlSvc.exe (PID: 2552)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 8924)
- cmd.exe (PID: 6736)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 1040)
- cmd.exe (PID: 6760)
INFO
Reads Environment values
- identity_helper.exe (PID: 8576)
Checks supported languages
- identity_helper.exe (PID: 8576)
- Radmin_VPN_1.4.4642.1.exe (PID: 8248)
- Radmin_VPN_1.4.4642.1.tmp (PID: 660)
- Radmin_VPN_1.4.4642.1.tmp (PID: 1272)
- Radmin_VPN_1.4.4642.1.exe (PID: 6392)
- msiexec.exe (PID: 1168)
- msiexec.exe (PID: 6728)
- MSI1144.tmp (PID: 5968)
- drvinst.exe (PID: 8620)
- drvinst.exe (PID: 8732)
- RvControlSvc.exe (PID: 2552)
- msiexec.exe (PID: 9032)
- RvRvpnGui.exe (PID: 1812)
Autorun file from Downloads
- msedge.exe (PID: 8908)
- msedge.exe (PID: 7372)
Application launched itself
- msedge.exe (PID: 7372)
Executable content was dropped or overwritten
- msedge.exe (PID: 7676)
- msedge.exe (PID: 7372)
- msiexec.exe (PID: 6728)
Reads the computer name
- identity_helper.exe (PID: 8576)
- Radmin_VPN_1.4.4642.1.tmp (PID: 660)
- Radmin_VPN_1.4.4642.1.tmp (PID: 1272)
- msiexec.exe (PID: 6728)
- msiexec.exe (PID: 1168)
- MSI1144.tmp (PID: 5968)
- drvinst.exe (PID: 8620)
- msiexec.exe (PID: 9032)
- RvControlSvc.exe (PID: 2552)
- RvRvpnGui.exe (PID: 1812)
- drvinst.exe (PID: 8732)
Create files in a temporary directory
- Radmin_VPN_1.4.4642.1.exe (PID: 8248)
- Radmin_VPN_1.4.4642.1.exe (PID: 6392)
- Radmin_VPN_1.4.4642.1.tmp (PID: 1272)
Process checks computer location settings
- Radmin_VPN_1.4.4642.1.tmp (PID: 660)
The sample compiled with english language support
- Radmin_VPN_1.4.4642.1.tmp (PID: 1272)
- msiexec.exe (PID: 6728)
- drvinst.exe (PID: 8620)
- drvinst.exe (PID: 8732)
Reads the software policy settings
- msiexec.exe (PID: 6728)
- MSI1144.tmp (PID: 5968)
- drvinst.exe (PID: 8620)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6728)
- MSI1144.tmp (PID: 5968)
- drvinst.exe (PID: 8620)
- RvControlSvc.exe (PID: 2552)
- RvRvpnGui.exe (PID: 1812)
The sample compiled with russian language support
- msiexec.exe (PID: 6728)
Starts application with an unusual extension
- msiexec.exe (PID: 6728)
Creates files in the program directory
- RvControlSvc.exe (PID: 2552)
Creates a software uninstall entry
- msiexec.exe (PID: 6728)
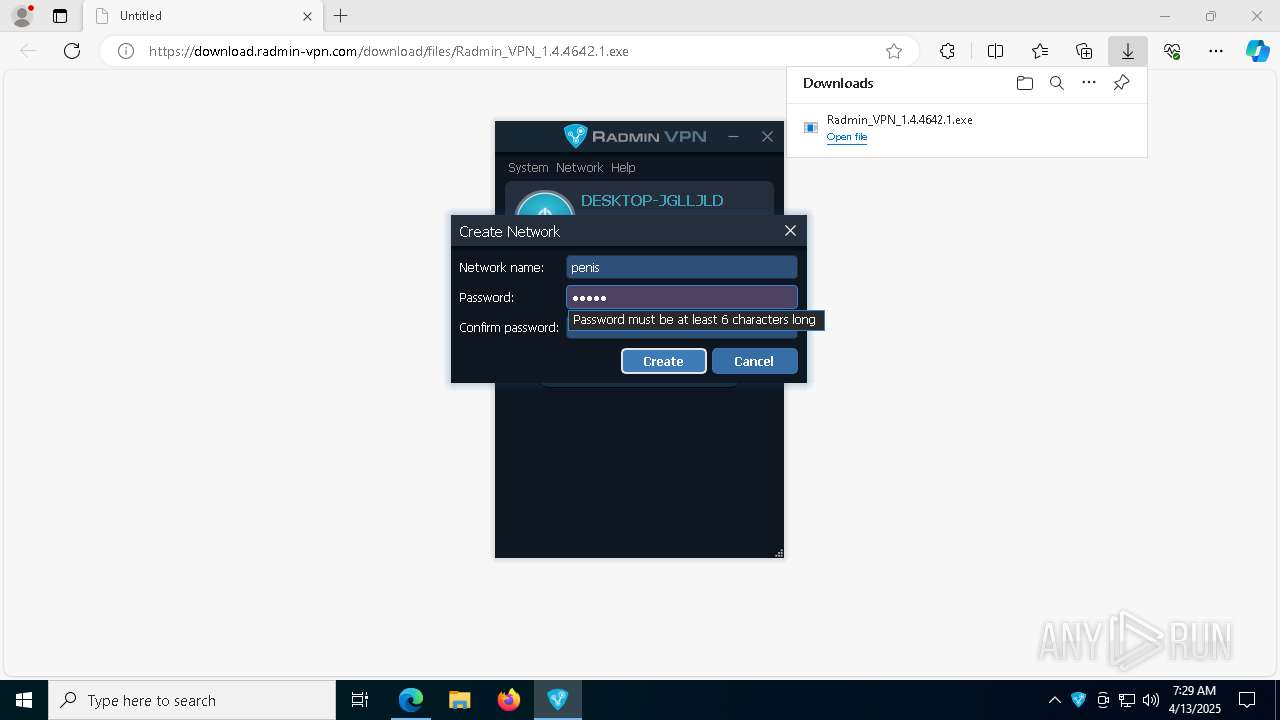
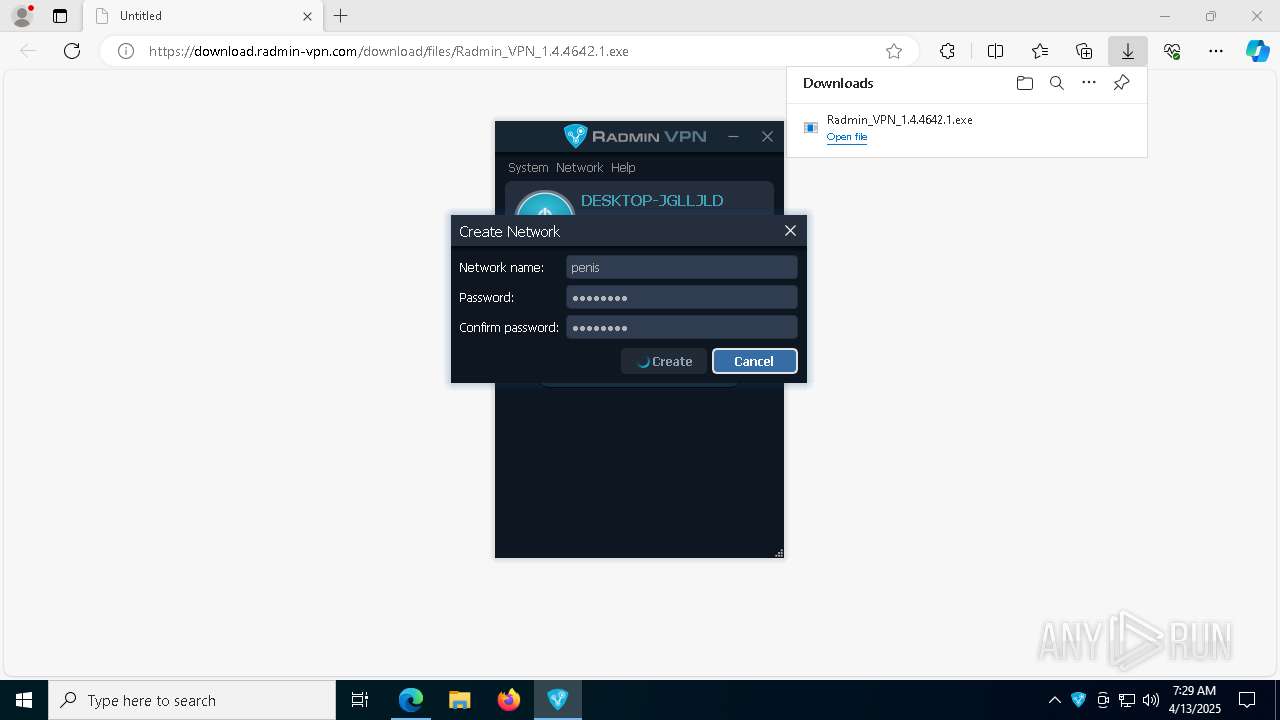
Manual execution by a user
- RvRvpnGui.exe (PID: 1812)
Disables trace logs
- netsh.exe (PID: 8408)
- netsh.exe (PID: 8912)
- netsh.exe (PID: 8392)
- netsh.exe (PID: 1328)
- netsh.exe (PID: 8964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
202
Monitored processes
65
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | netsh advfirewall firewall add rule name="Radmin VPN icmpv4" action=allow enable=yes dir=in profile=any remoteip=26.0.0.0/8 protocol=icmpv4 | C:\Windows\SysWOW64\netsh.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Users\admin\AppData\Local\Temp\is-0EPOF.tmp\Radmin_VPN_1.4.4642.1.tmp" /SL5="$50310,21145108,189952,C:\Users\admin\Downloads\Radmin_VPN_1.4.4642.1.exe" | C:\Users\admin\AppData\Local\Temp\is-0EPOF.tmp\Radmin_VPN_1.4.4642.1.tmp | — | Radmin_VPN_1.4.4642.1.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1040 | C:\WINDOWS\system32\cmd.exe C:\WINDOWS\system32\cmd.exe /c C:\WINDOWS\system32\netsh.exe interface ip add address name="Radmin VPN" addr=26.103.248.251 mask=255.0.0.0 gateway=26.0.0.1 gwmetric=9256 | C:\Windows\SysWOW64\cmd.exe | — | RvControlSvc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | C:\Windows\syswow64\MsiExec.exe -Embedding BDD4BAED16C96DC920A87DB40BF0EF73 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | "C:\Users\admin\AppData\Local\Temp\is-DF3D0.tmp\Radmin_VPN_1.4.4642.1.tmp" /SL5="$1802DC,21145108,189952,C:\Users\admin\Downloads\Radmin_VPN_1.4.4642.1.exe" /SPAWNWND=$90296 /NOTIFYWND=$50310 | C:\Users\admin\AppData\Local\Temp\is-DF3D0.tmp\Radmin_VPN_1.4.4642.1.tmp | Radmin_VPN_1.4.4642.1.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1328 | C:\WINDOWS\system32\netsh.exe interface ip add route prefix=0.0.0.0/0 interface="Radmin VPN" nexthop=26.0.0.1 publish=Yes metric=9256 | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1548 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | "C:\Program Files (x86)\Radmin VPN\RvRvpnGui.exe" /show | C:\Program Files (x86)\Radmin VPN\RvRvpnGui.exe | — | explorer.exe | |||||||||||
User: admin Company: Famatech Corp. Integrity Level: MEDIUM Description: Radmin VPN Version: 1.4.4642.1 Modules
| |||||||||||||||
| 2420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 364
Read events
24 830
Write events
339
Delete events
195
Modification events
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9D797E2B3A912F00 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 034C872B3A912F00 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {ACD6C560-01A2-4374-8D9D-DF133B7B8F3A} | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 555EAC2B3A912F00 | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (7372) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
129
Suspicious files
261
Text files
44
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b73c.TMP | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b75b.TMP | — | |
MD5:— | SHA256:— | |||
| 7372 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
65
DNS requests
45
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.36:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7372 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEANmchMIZYHj%2F%2B8%2Bj8Y68sw%3D | unknown | — | — | whitelisted |
7372 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
9116 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
9116 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.36:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7372 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7676 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7676 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7676 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
download.radmin-vpn.com |
| unknown |
business.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |