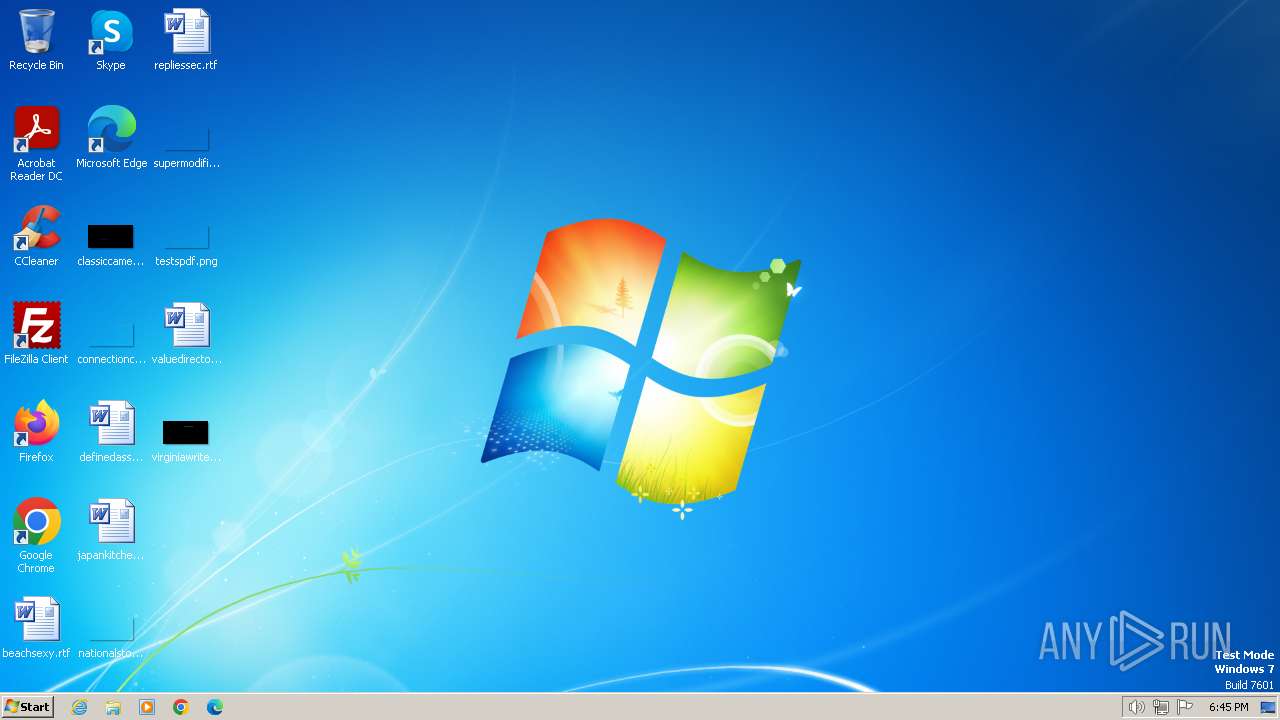
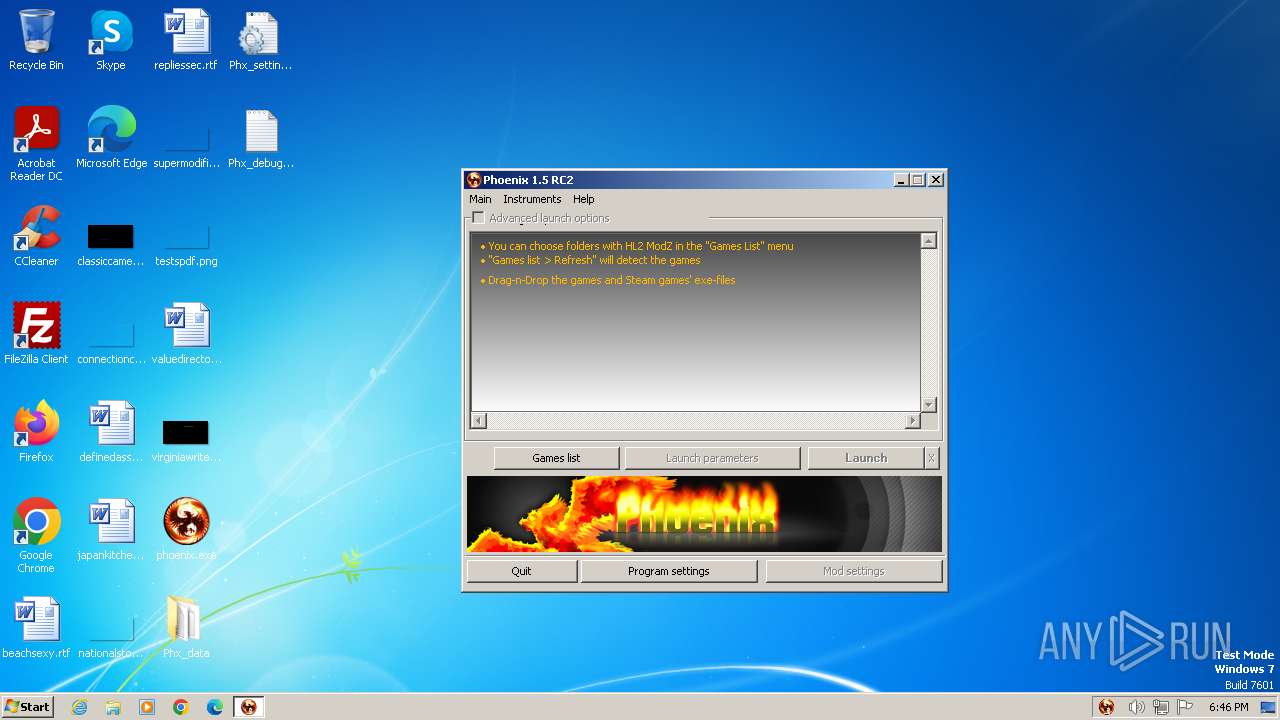
| File name: | phoenix.exe |
| Full analysis: | https://app.any.run/tasks/717af841-41ed-4ee2-82ce-f12d51e36bdb |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2024, 18:45:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
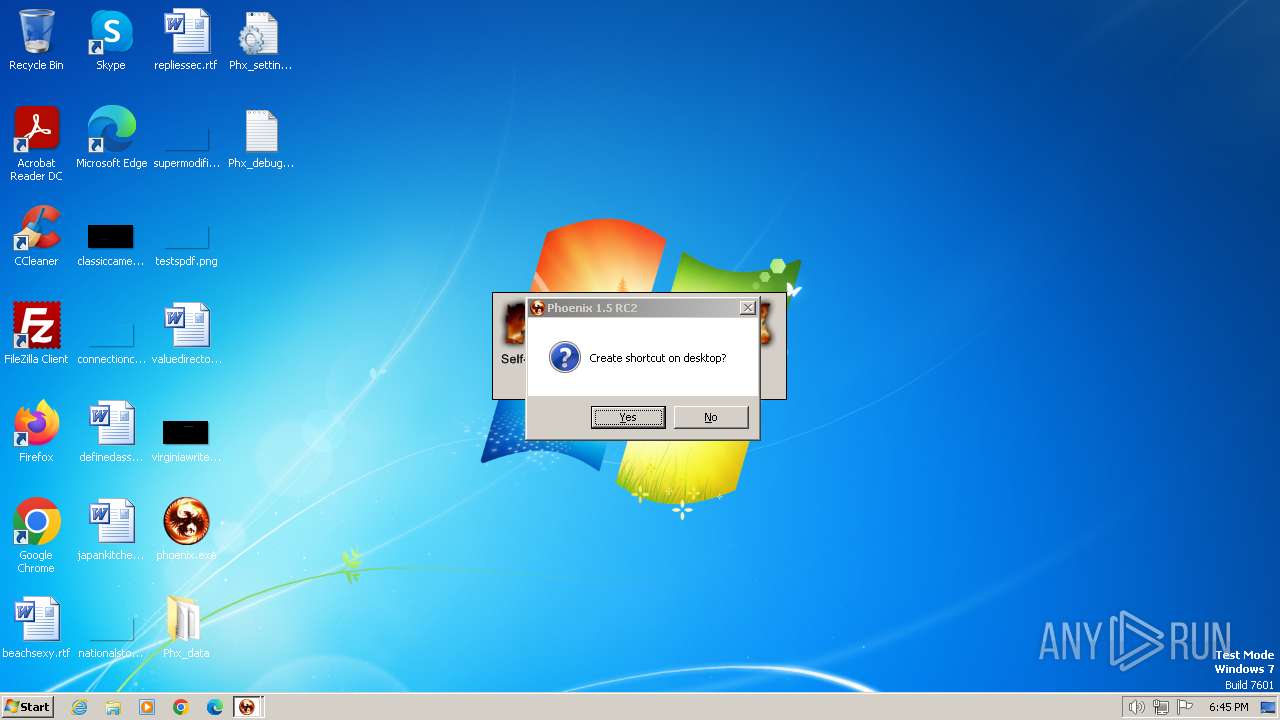
| MIME: | application/x-dosexec |
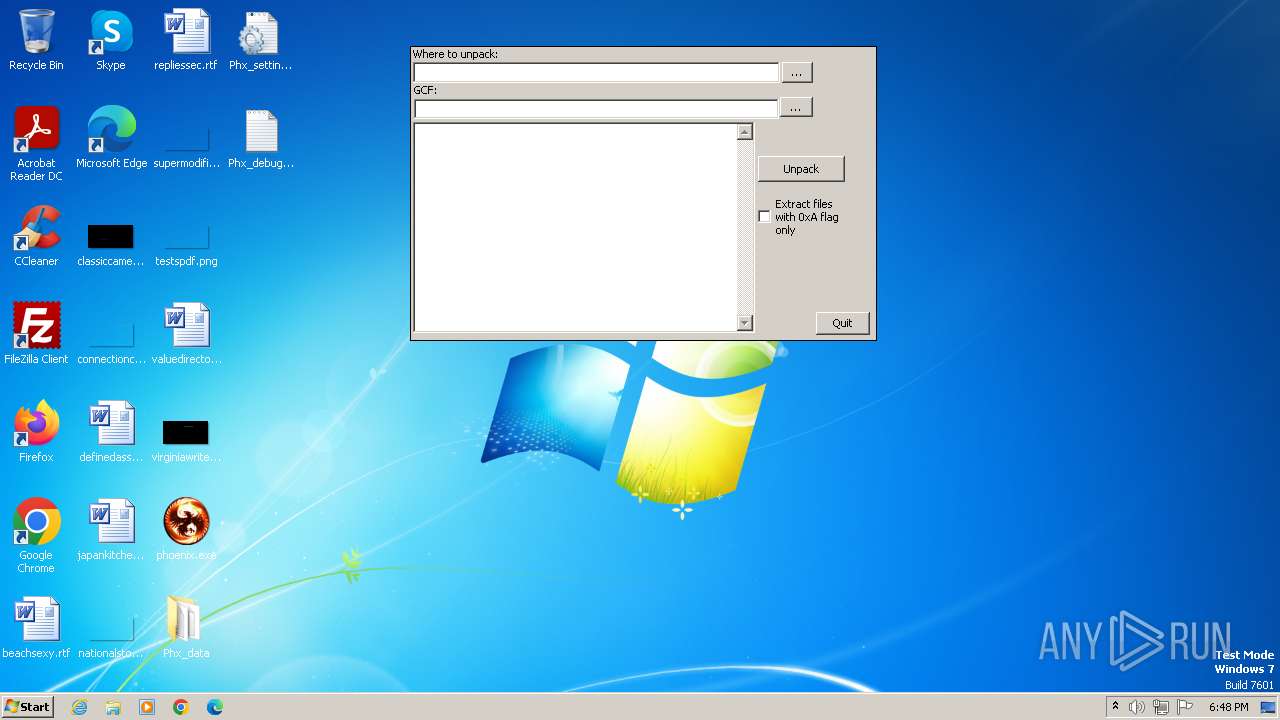
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E660B7B70675FC4E7F0CD45243A3E0F3 |
| SHA1: | 593518C90A993C060C383BC5C3B06D456FBDEEEF |
| SHA256: | 4C9CB394B4F27559966D1B8D063FB4C9A51C9F90C0721F3385D16FDFEC85576C |
| SSDEEP: | 393216:gSbYAJVbaKjWknpJVuYH7R4SclTnOIWHGsD9n6l9A2xmnX:gMxJV5jW8Vum9vq5WmiAu2onX |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process creates files with name similar to system file names
- phoenix.exe (PID: 2204)
- UpdCentre.exe (PID: 2624)
- GCFeX.exe (PID: 2816)
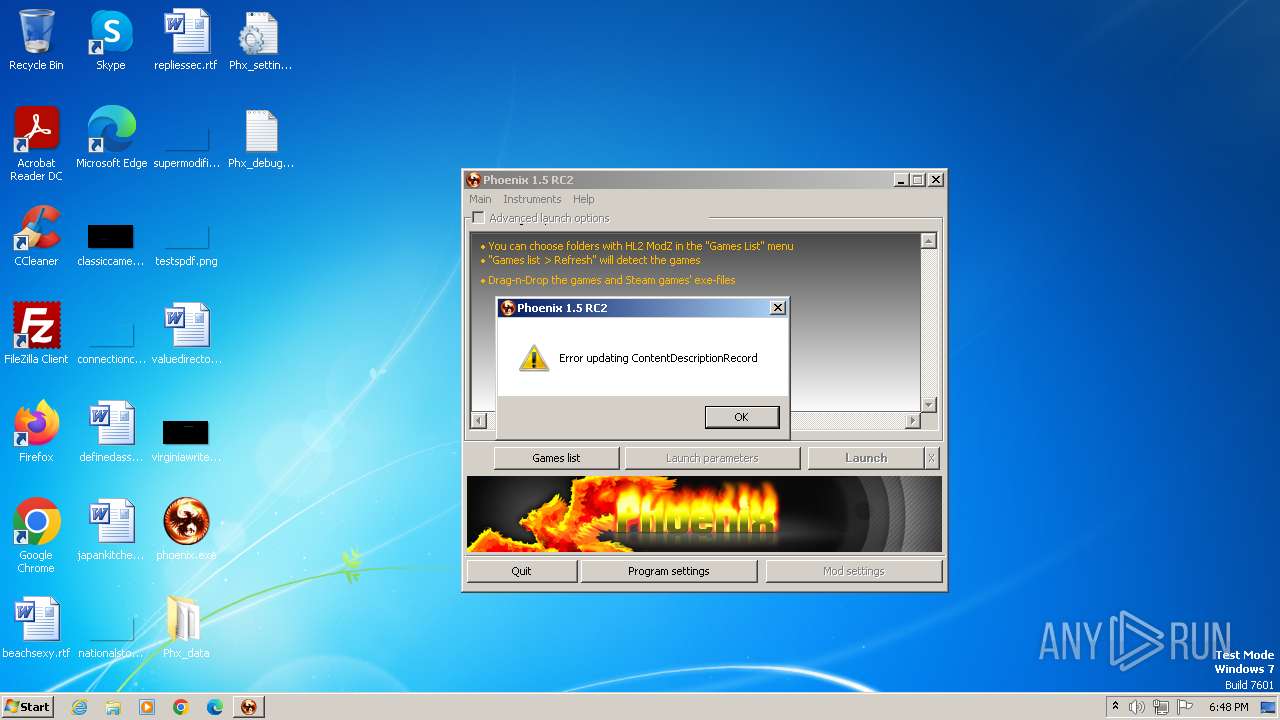
Reads the Internet Settings
- UpdCentre.exe (PID: 2624)
- phoenix.exe (PID: 2204)
INFO
Checks supported languages
- phoenix.exe (PID: 2204)
- UpdCentre.exe (PID: 2624)
- GCFeX.exe (PID: 2816)
Reads the computer name
- phoenix.exe (PID: 2204)
- UpdCentre.exe (PID: 2624)
- GCFeX.exe (PID: 2816)
Malware-specific behavior (creating "System.dll" in Temp)
- phoenix.exe (PID: 2204)
- UpdCentre.exe (PID: 2624)
- GCFeX.exe (PID: 2816)
Drops the executable file immediately after the start
- UpdCentre.exe (PID: 2624)
- phoenix.exe (PID: 2204)
- GCFeX.exe (PID: 2816)
Reads the machine GUID from the registry
- phoenix.exe (PID: 2204)
- UpdCentre.exe (PID: 2624)
Create files in a temporary directory
- phoenix.exe (PID: 2204)
- UpdCentre.exe (PID: 2624)
- GCFeX.exe (PID: 2816)
Checks proxy server information
- UpdCentre.exe (PID: 2624)
- phoenix.exe (PID: 2204)
Connects to unusual port
- phoenix.exe (PID: 2204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:41+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23040 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30cb |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.4.30 |
| ProductVersionNumber: | 1.0.4.30 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
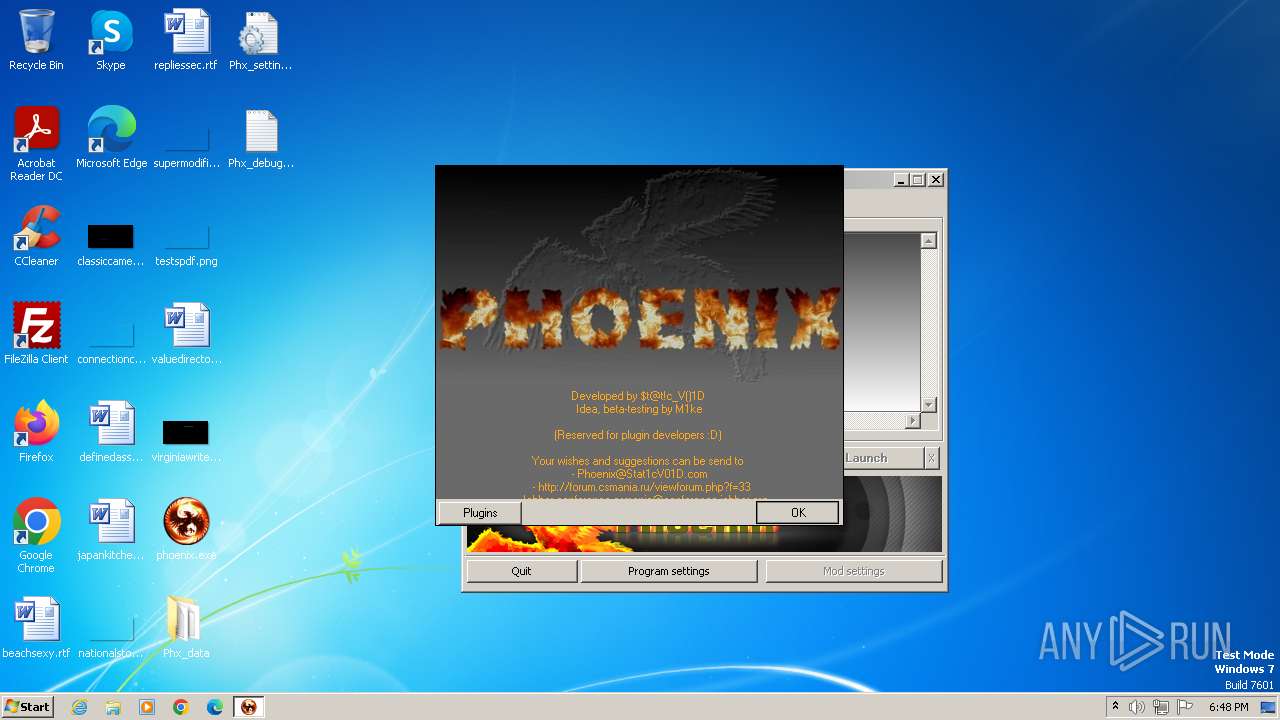
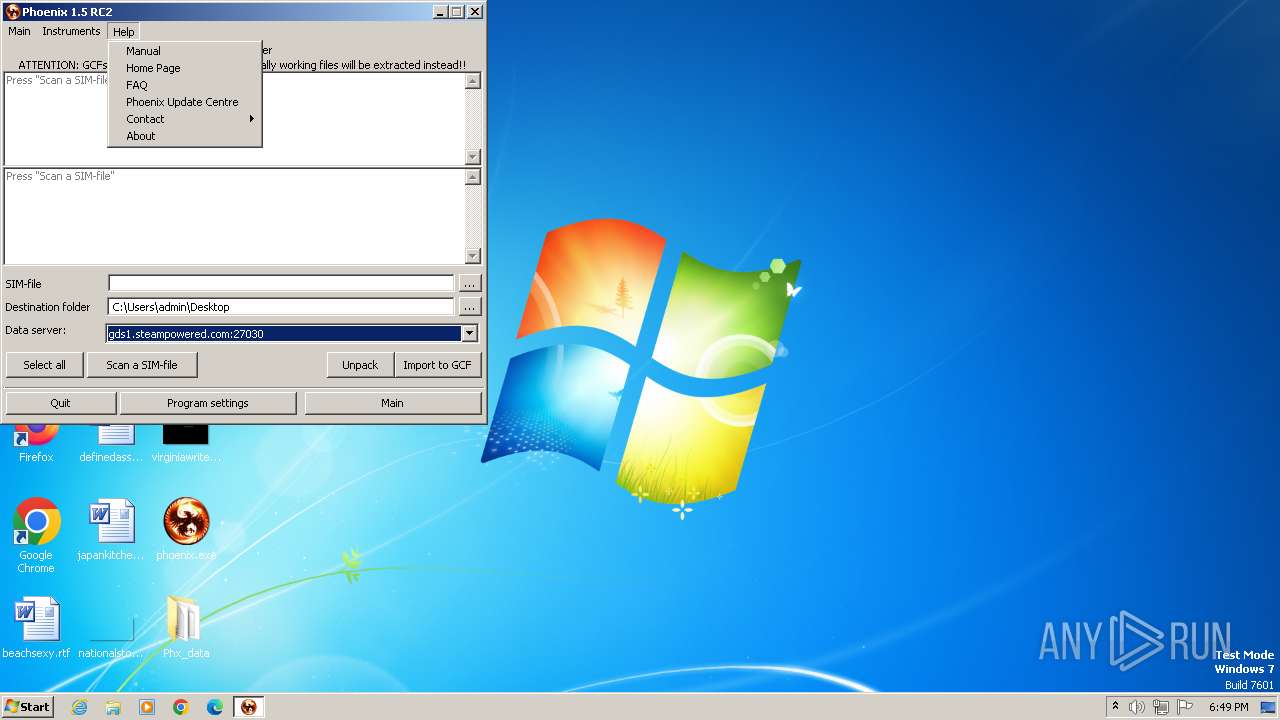
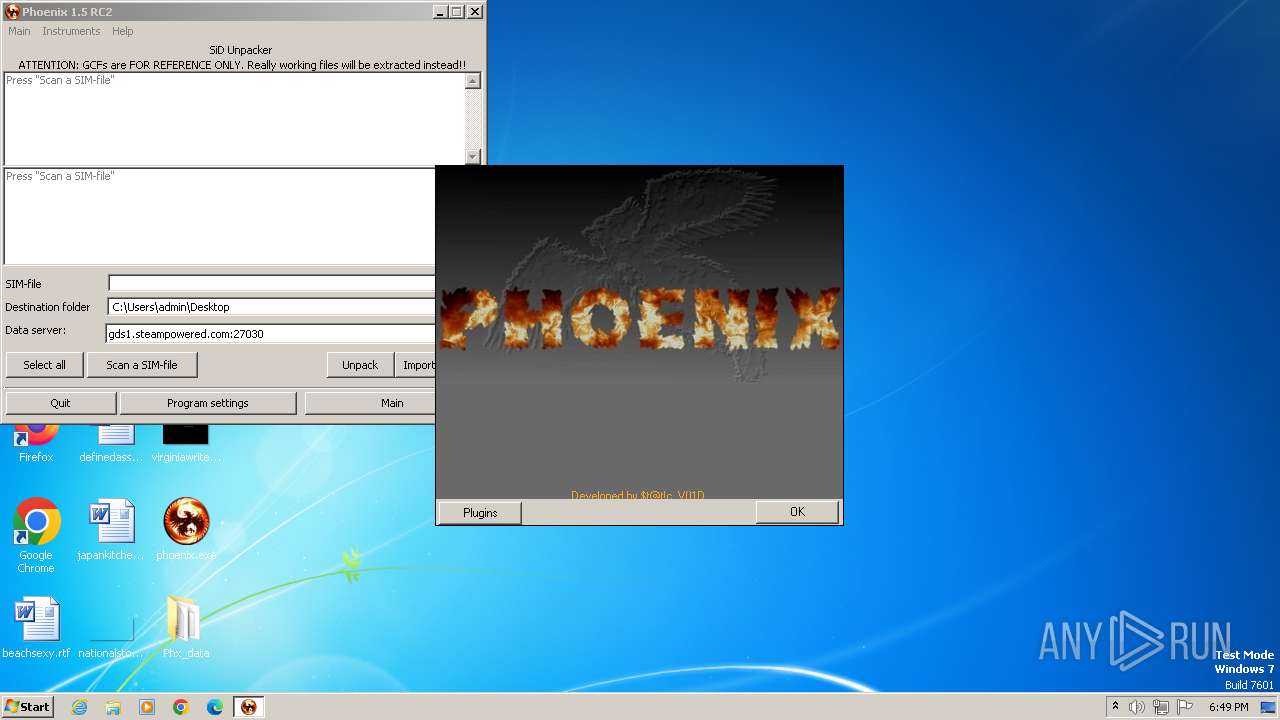
| Comments: | NSIS script by $t@t!c_V()!D. Compiled on 12.02.2012 17:46:34. |
| CompanyName: | $t@t!c_V()!D |
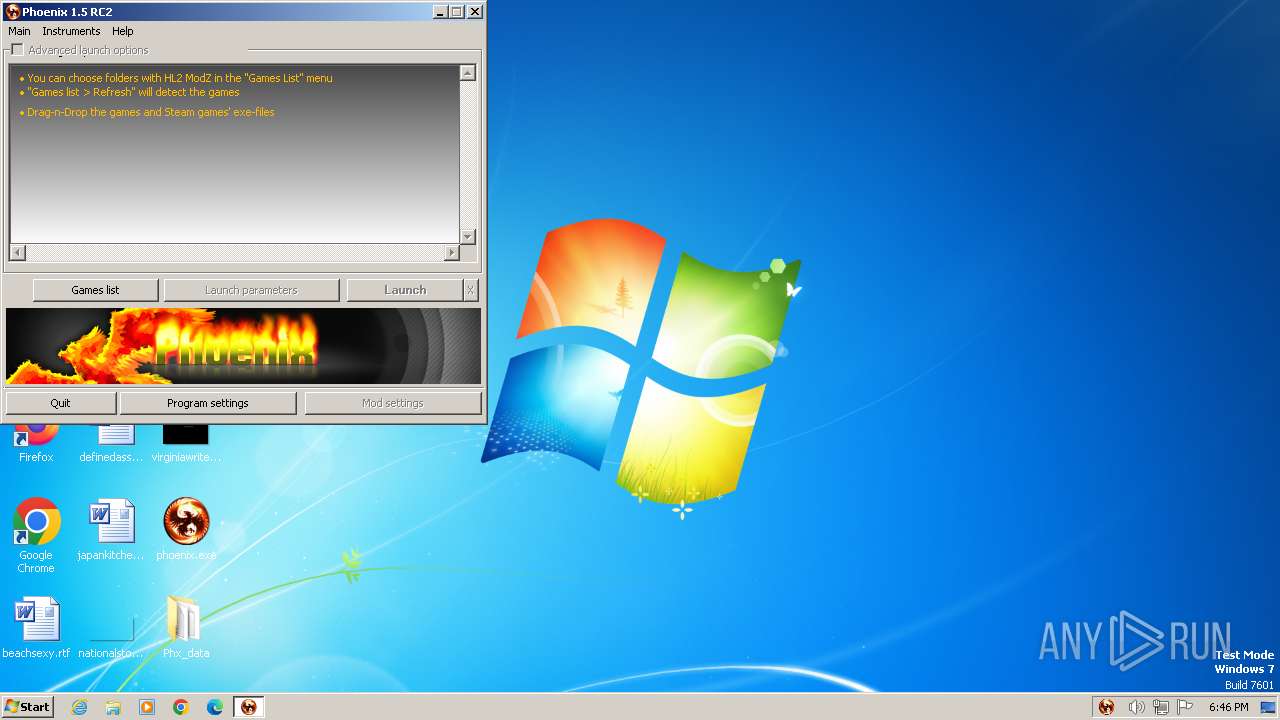
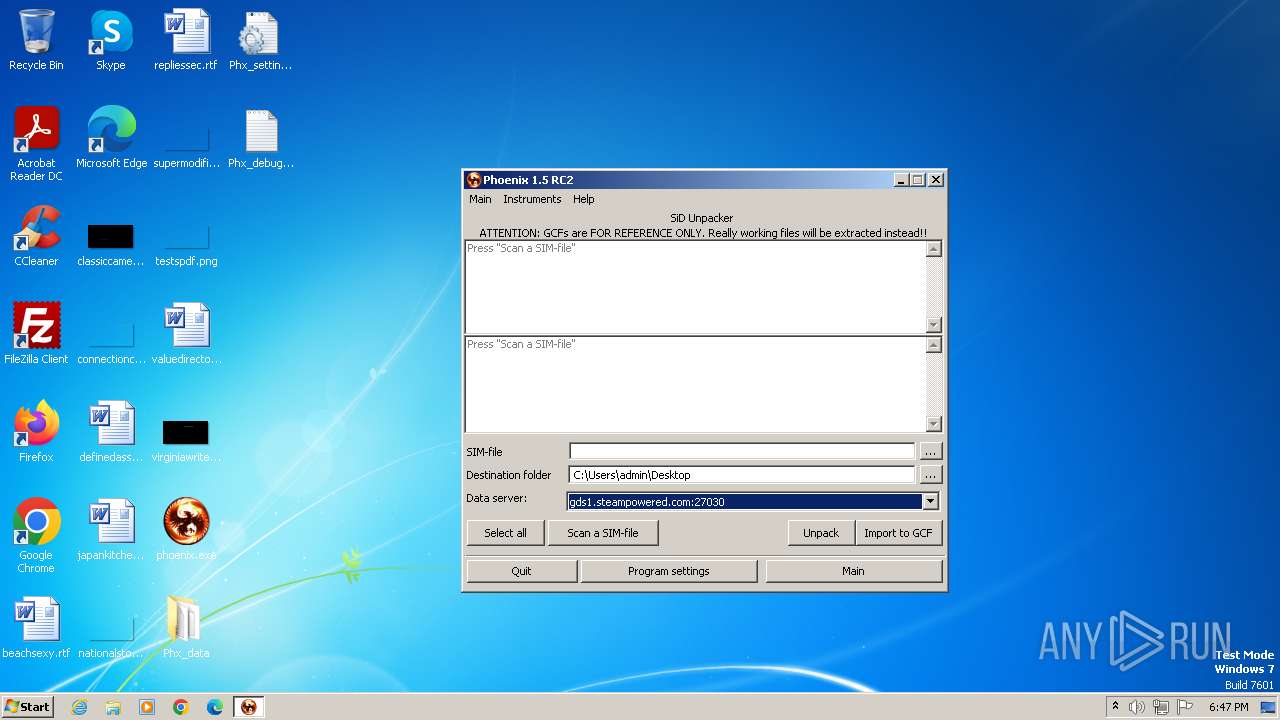
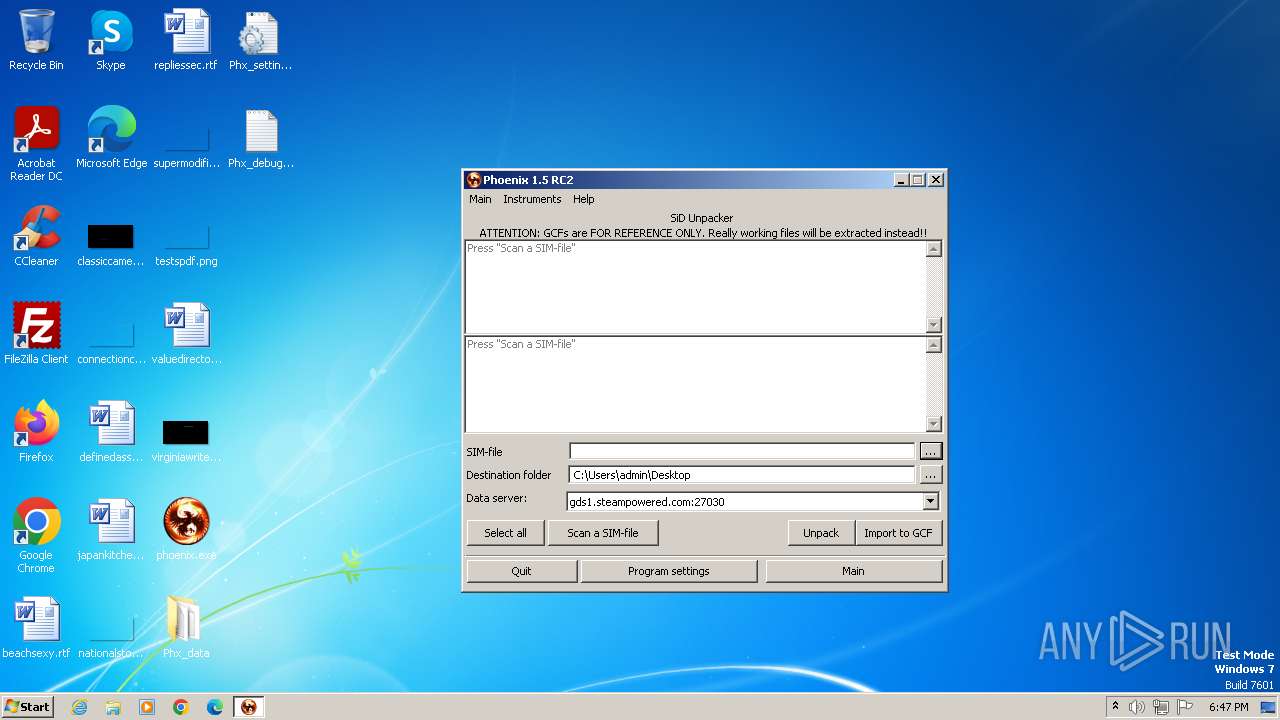
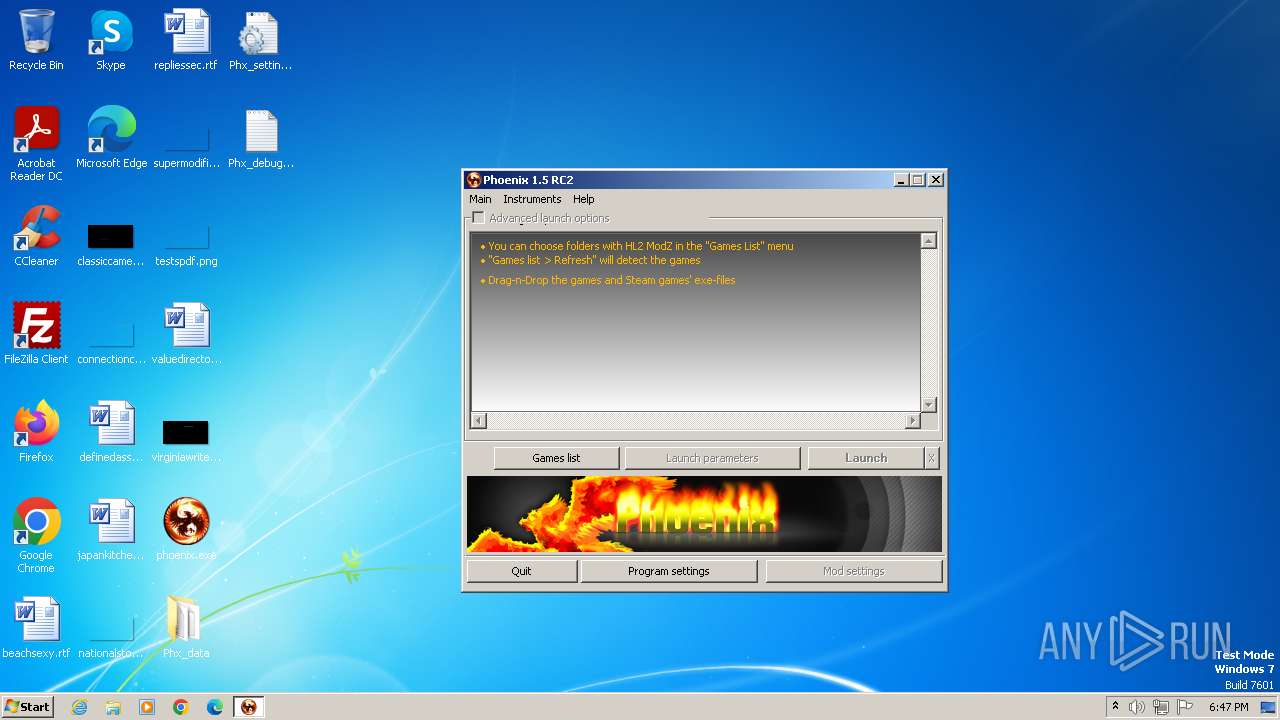
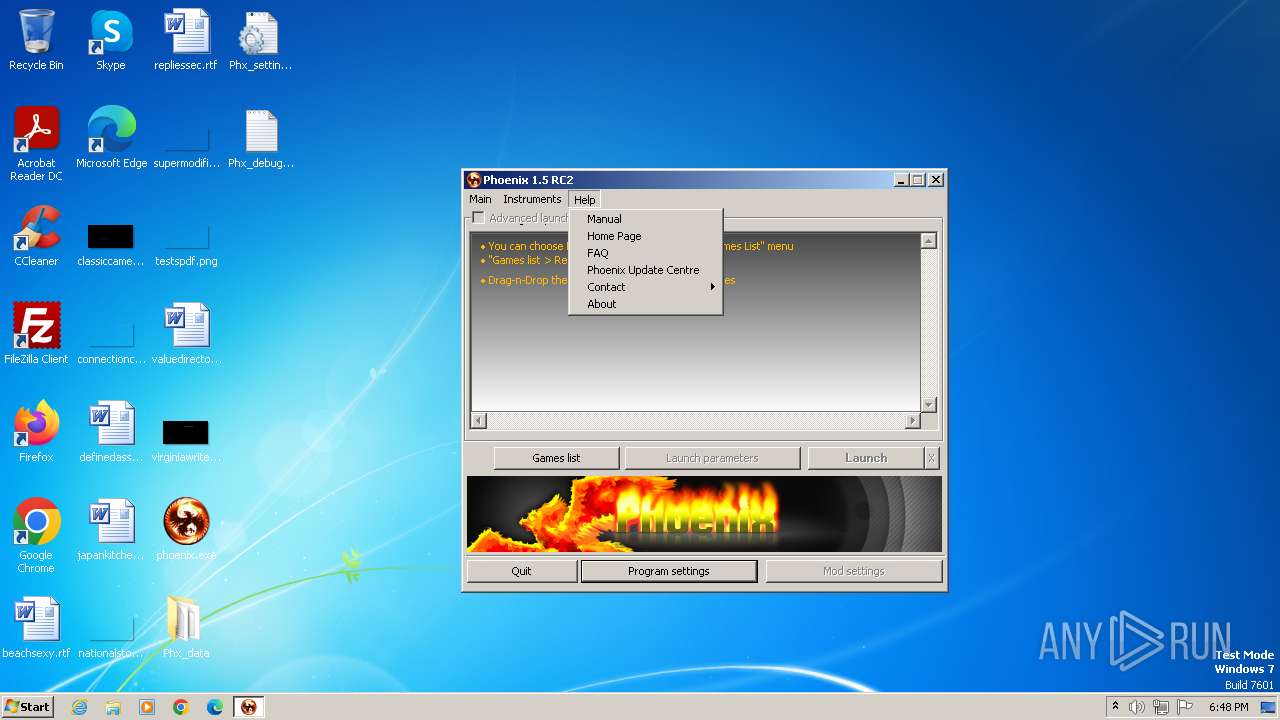
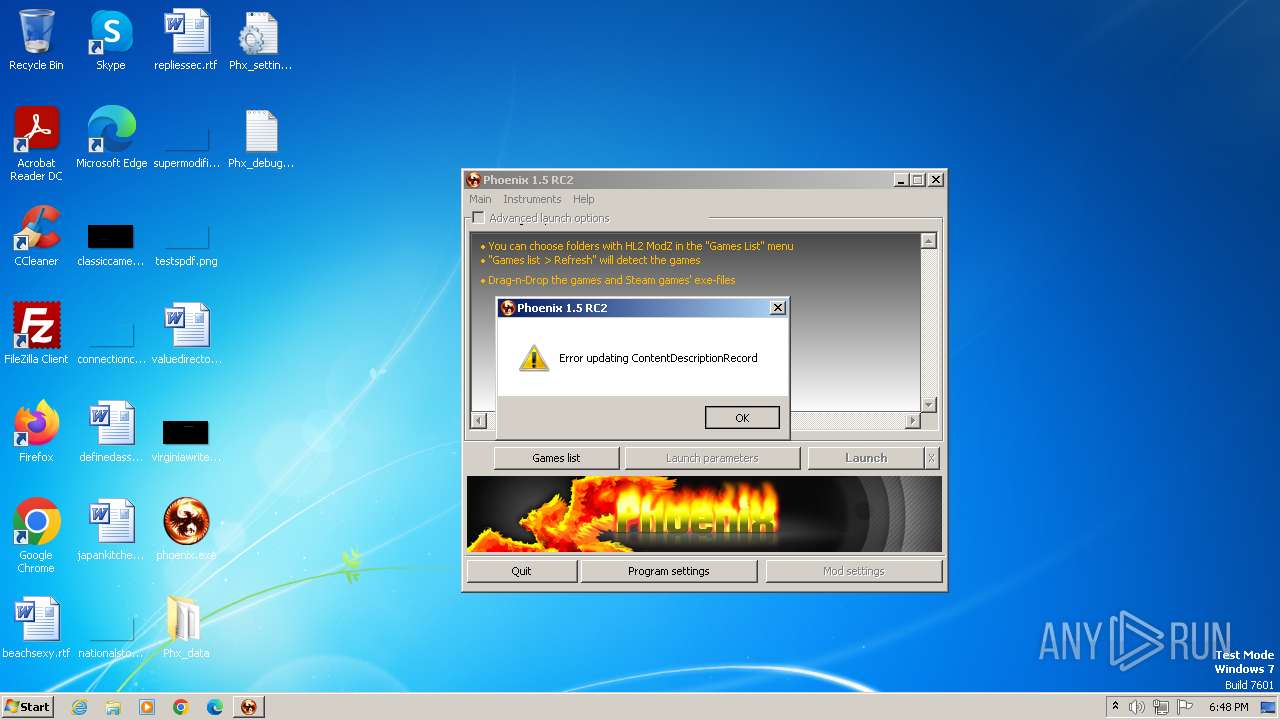
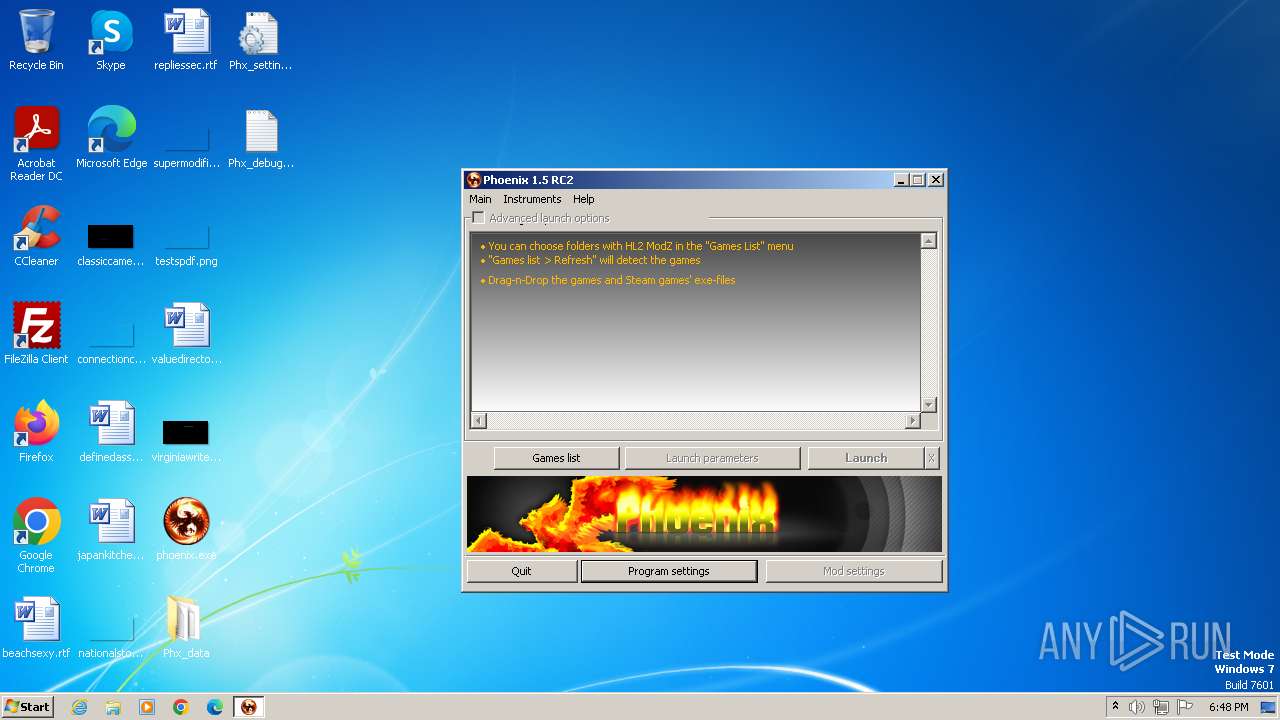
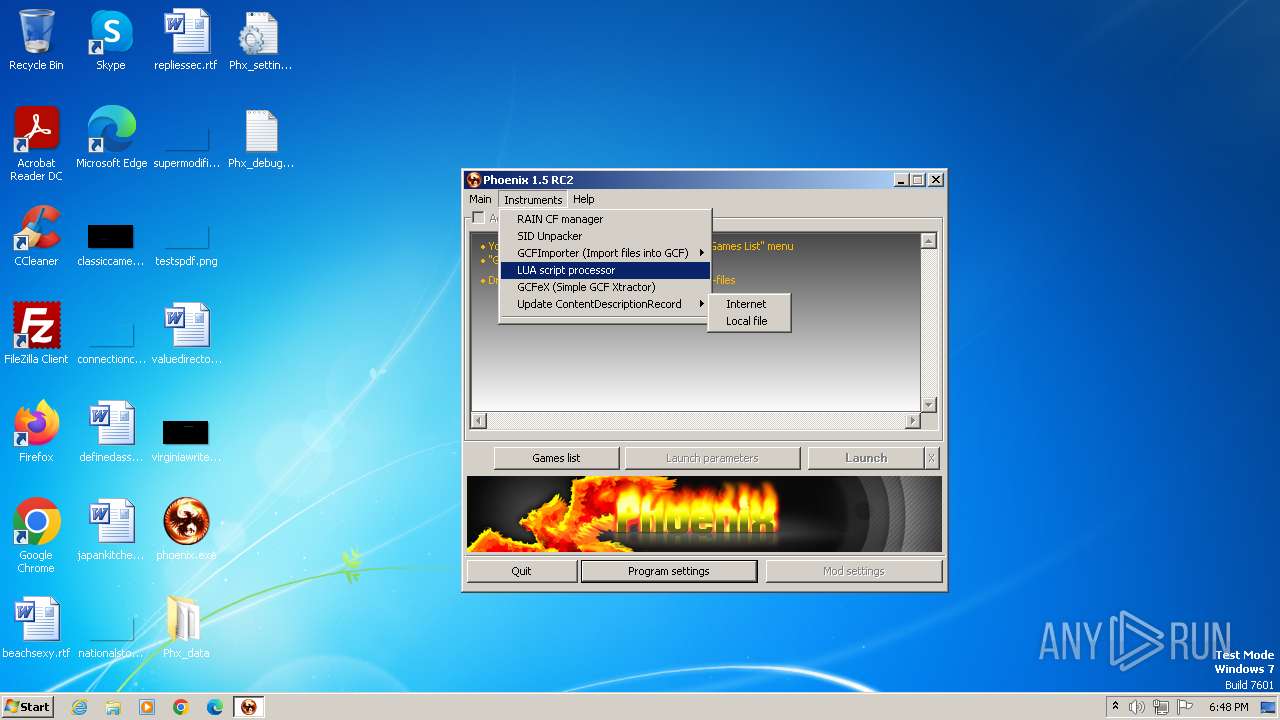
| FileDescription: | Phoenix |
| FileVersion: | 1.5 RC2 |
| InternalName: | ModZ Launcher 3 |
| LegalCopyright: | © 2007-2011 $t@t!c_V()!D |
| LegalTrademarks: | Phoenix is a property of $t@t!c_V()!D |
| OriginalFileName: | Phoenix.exe |
| ProductName: | Phoenix |
Total processes
51
Monitored processes
3
Malicious processes
0
Suspicious processes
2
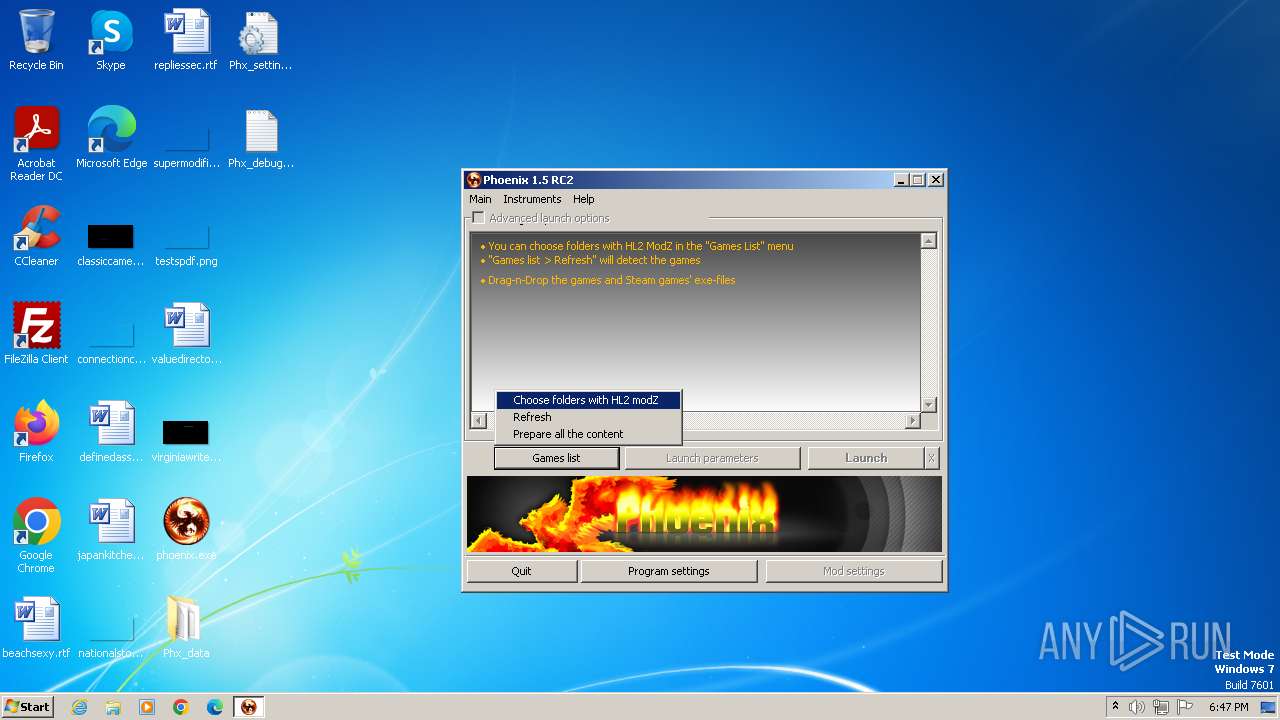
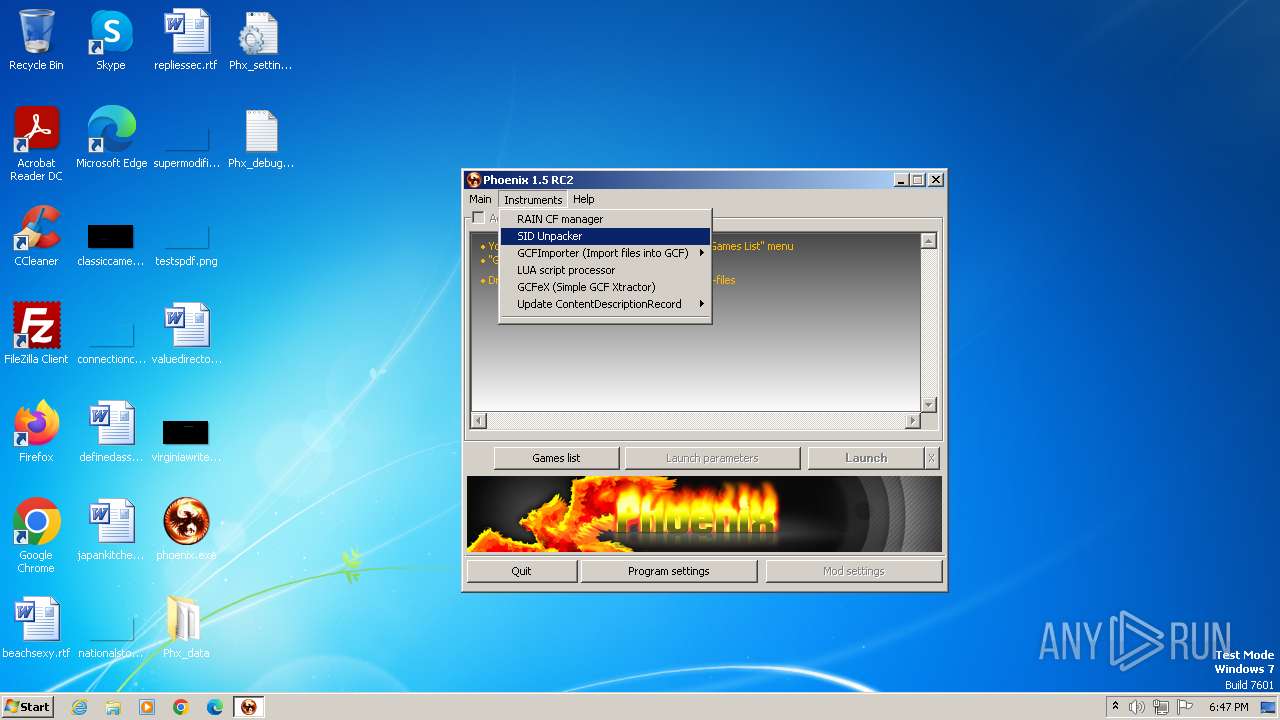
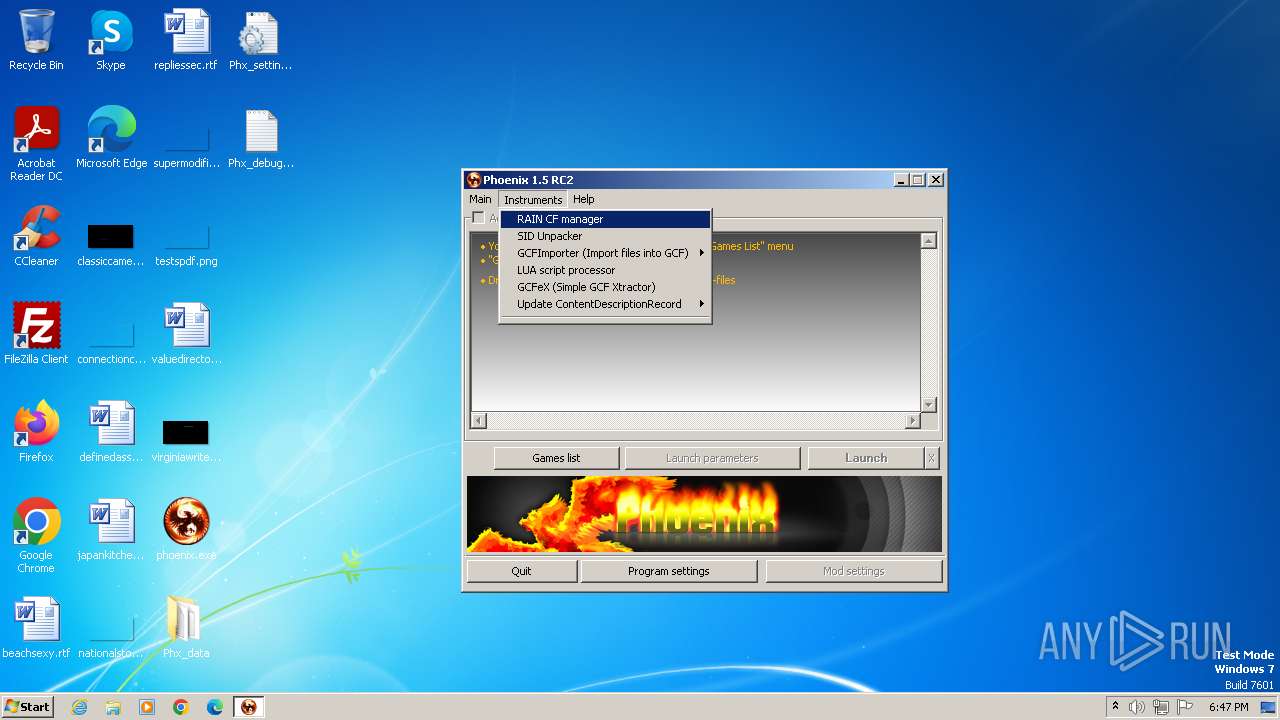
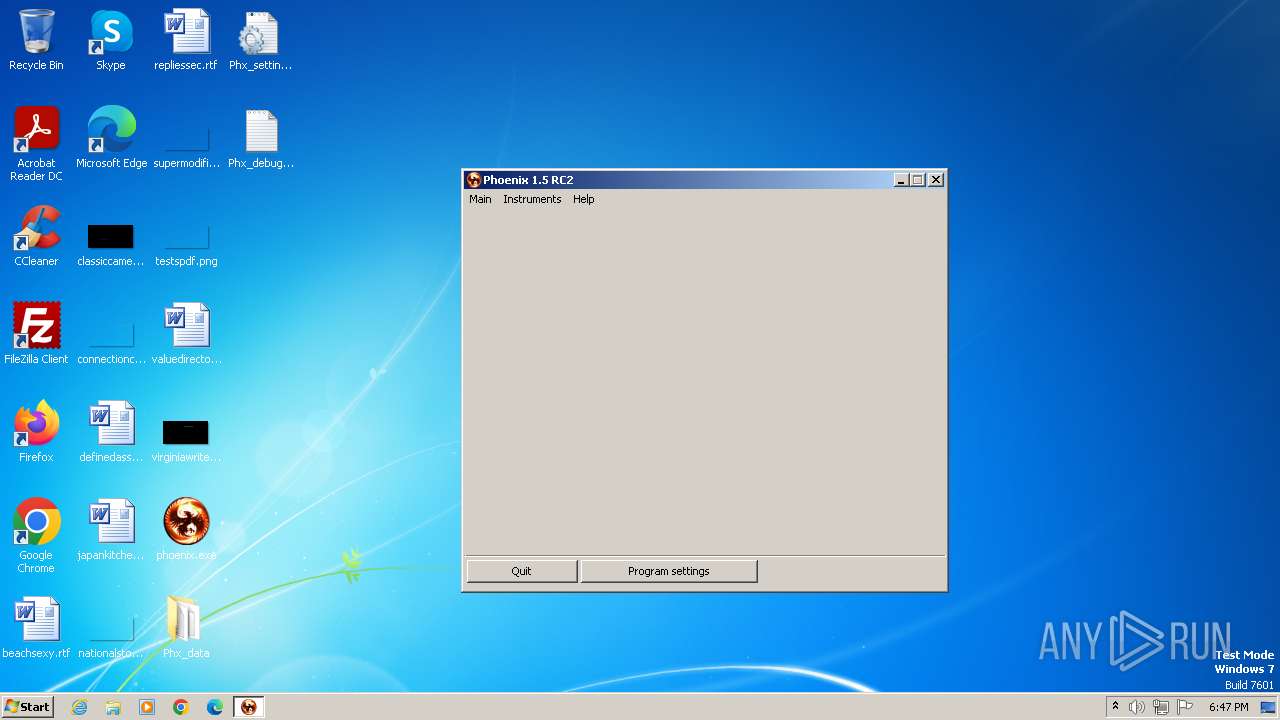
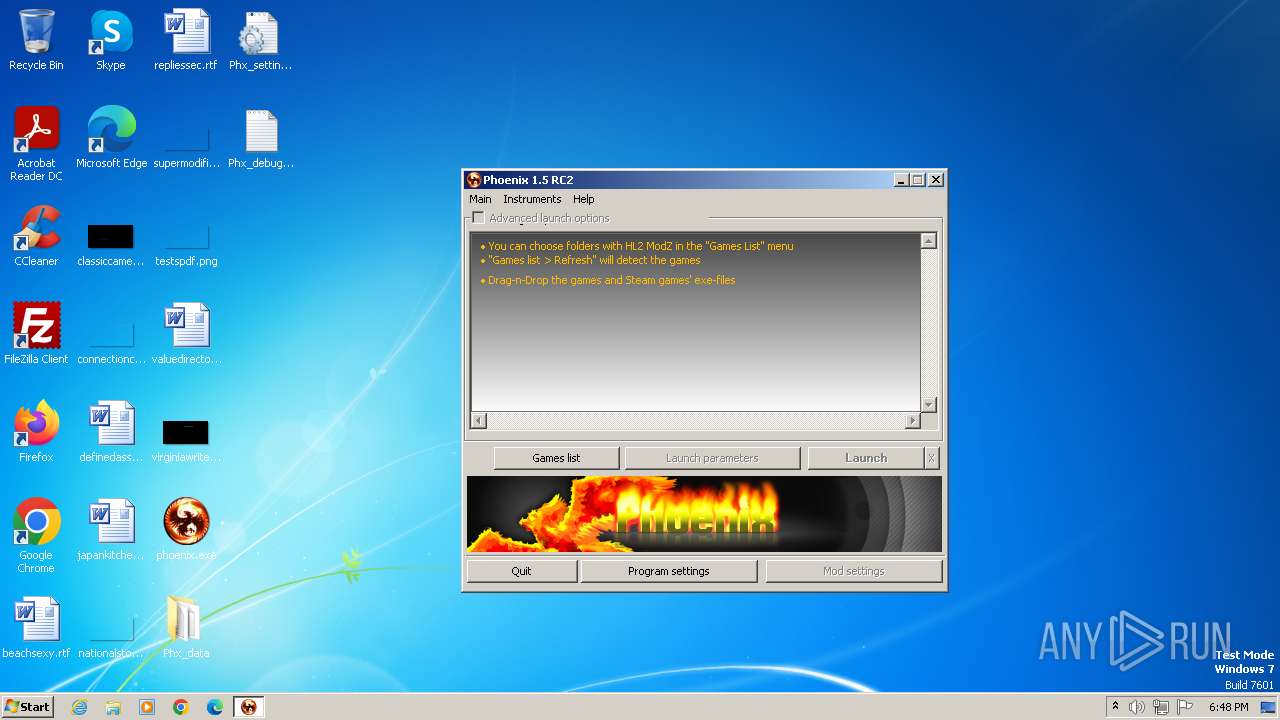
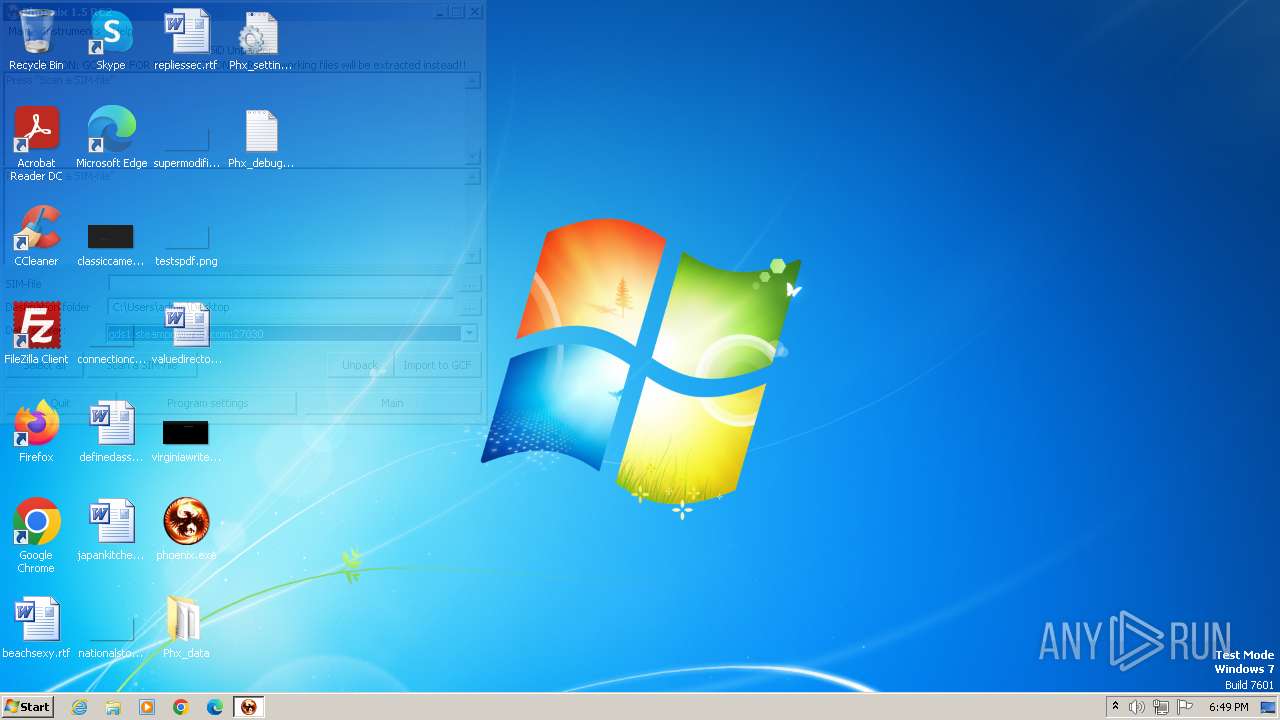
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2204 | "C:\Users\admin\Desktop\phoenix.exe" | C:\Users\admin\Desktop\phoenix.exe | explorer.exe | ||||||||||||
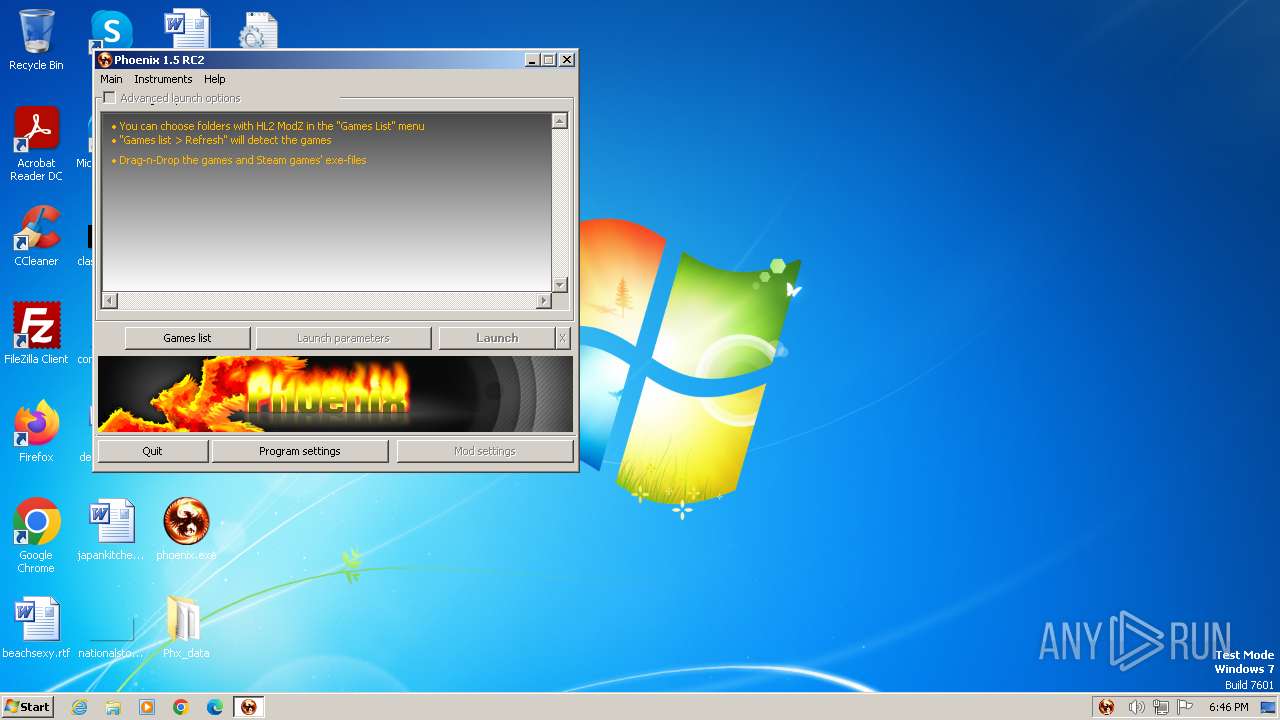
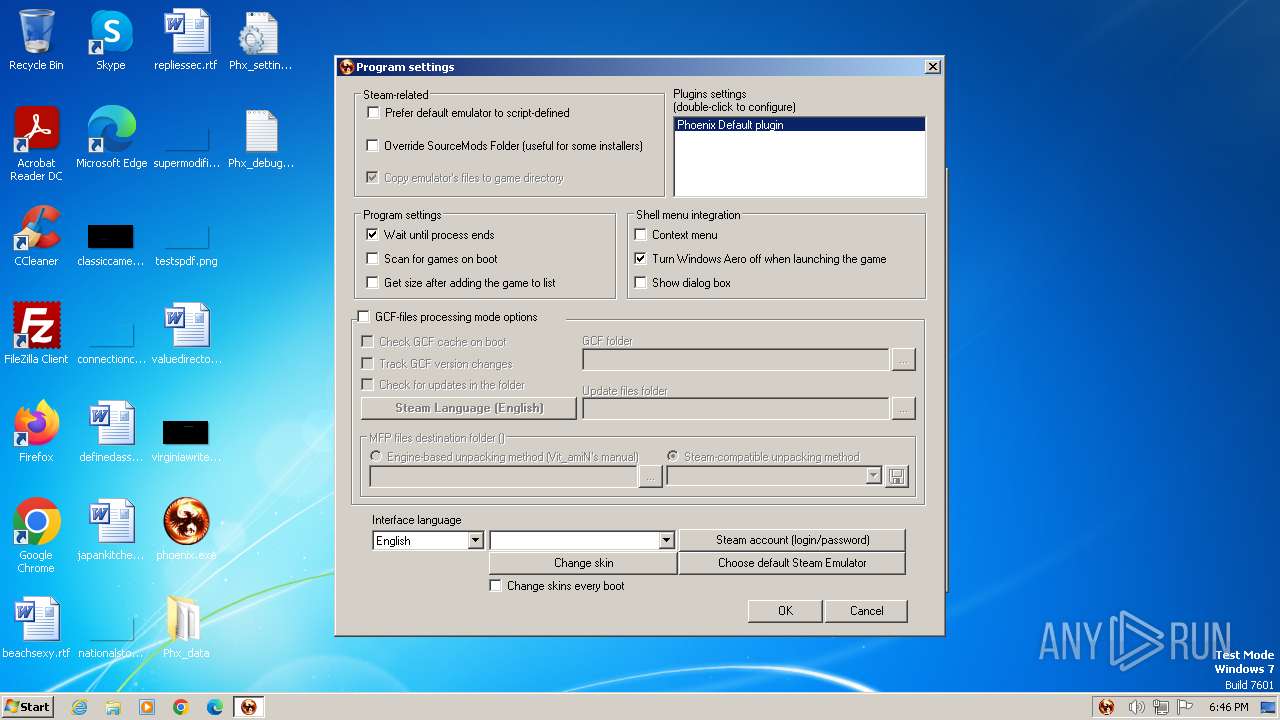
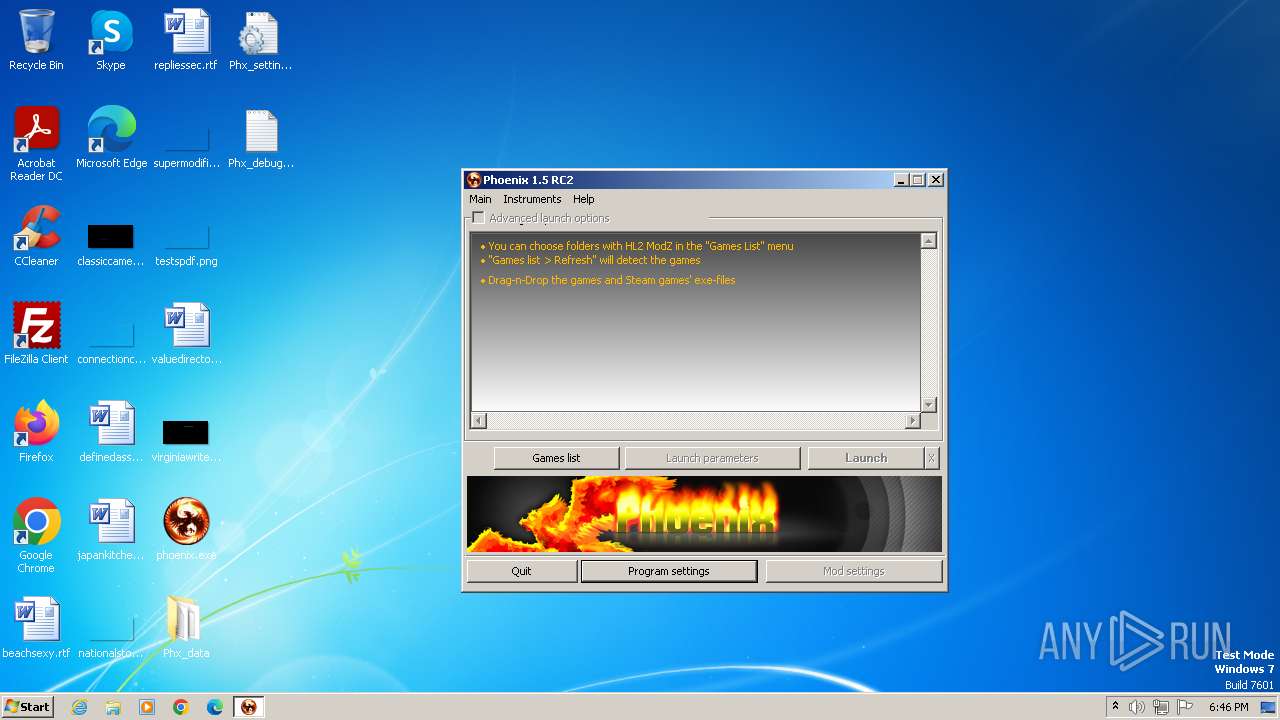
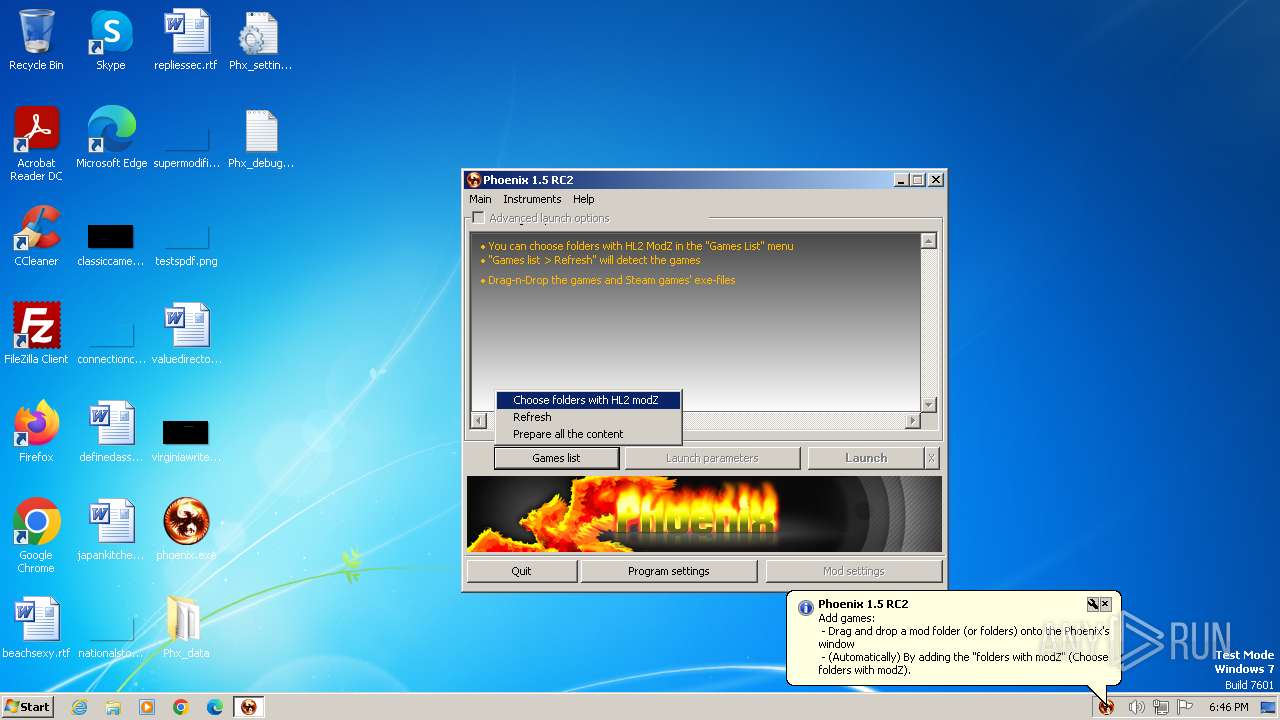
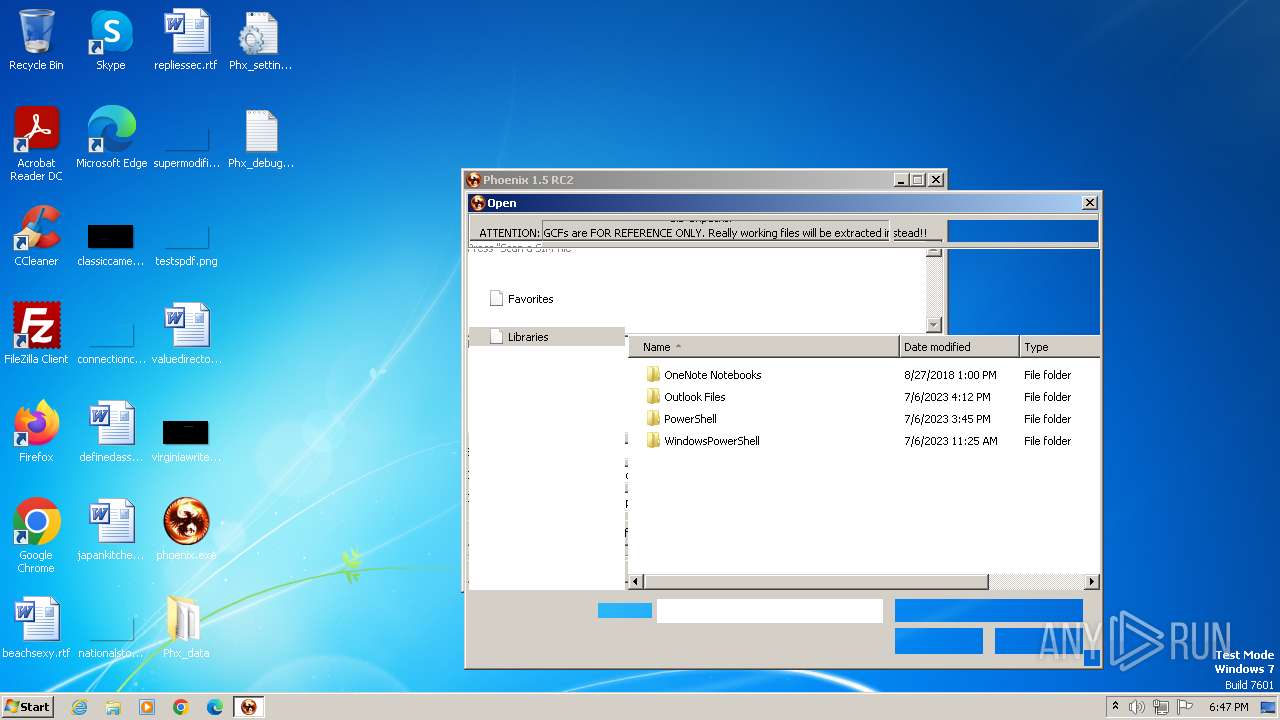
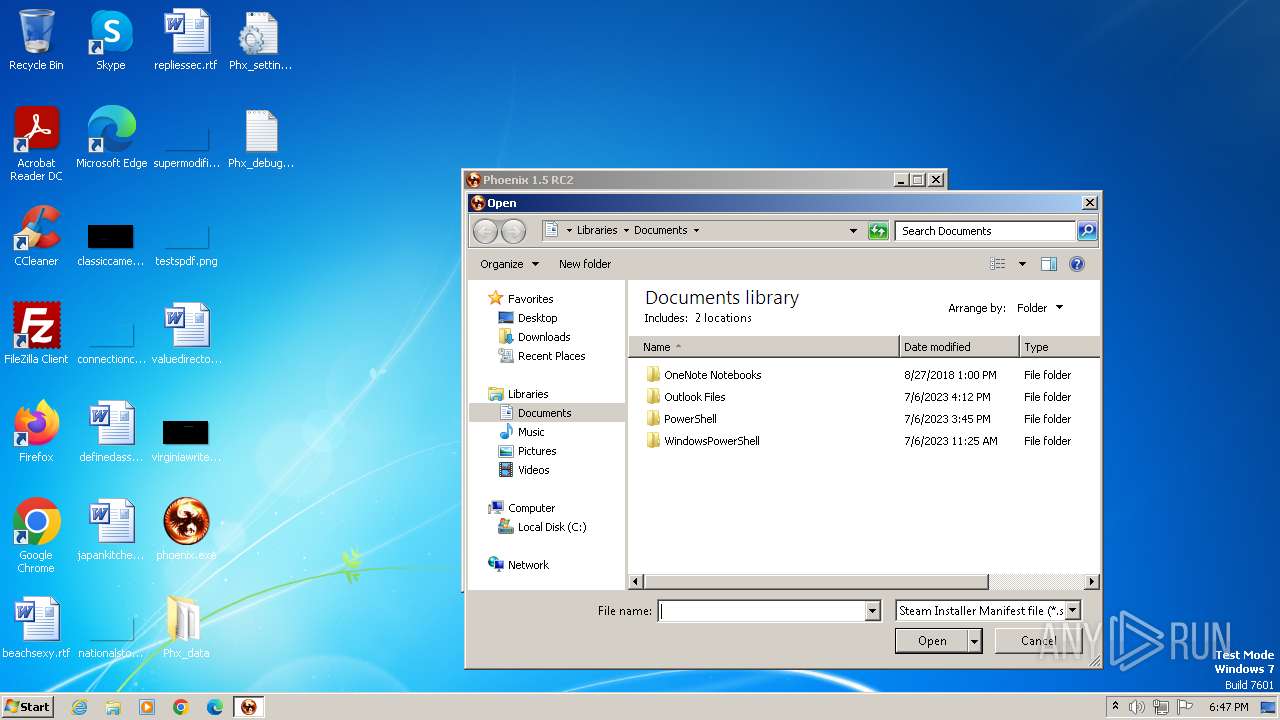
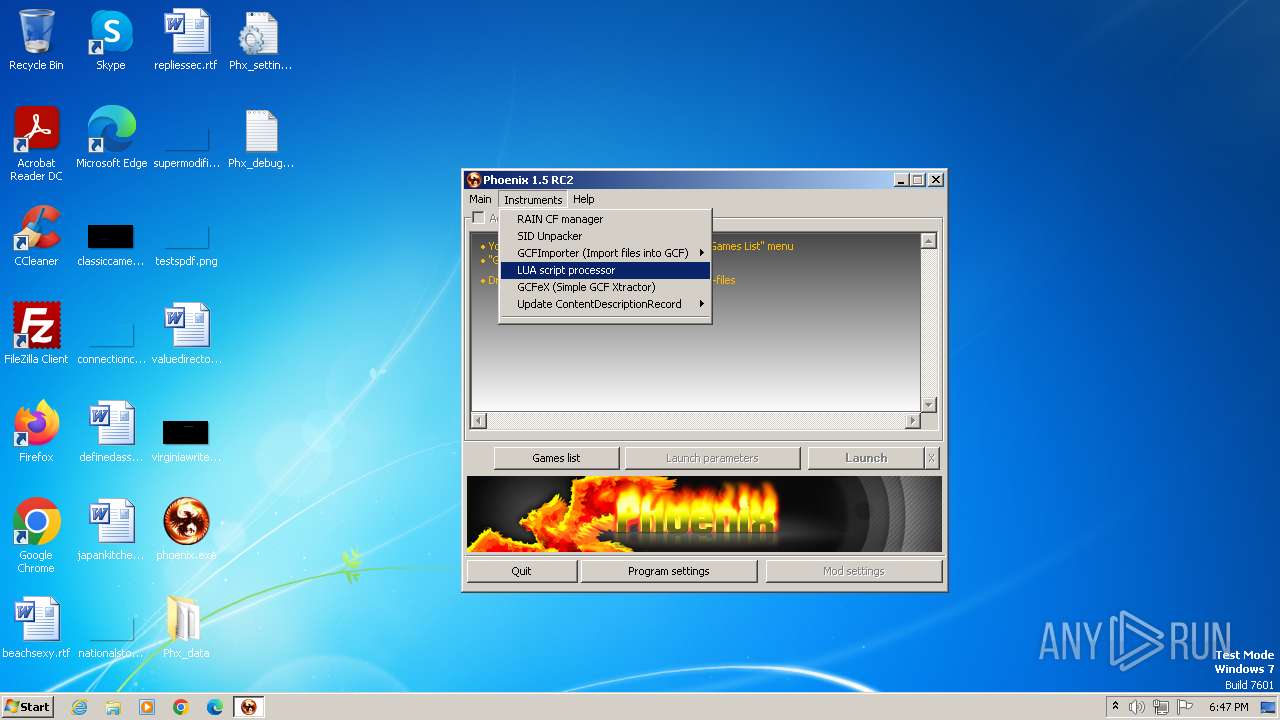
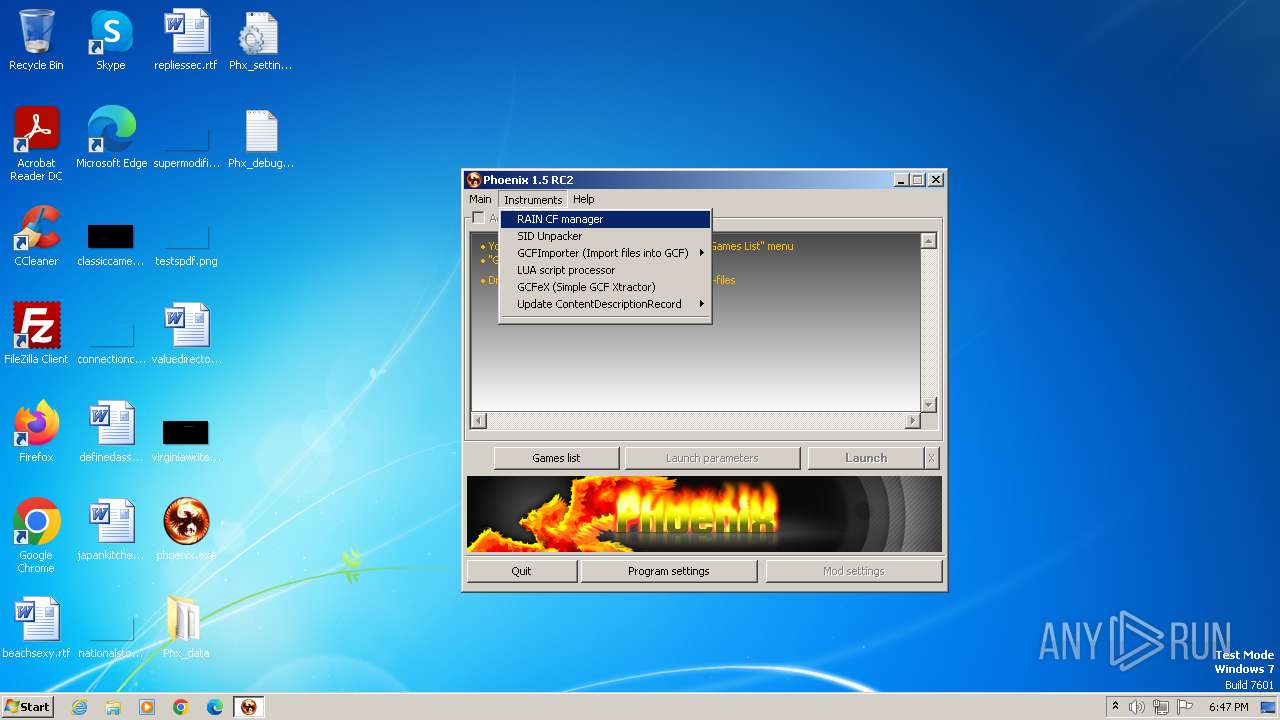
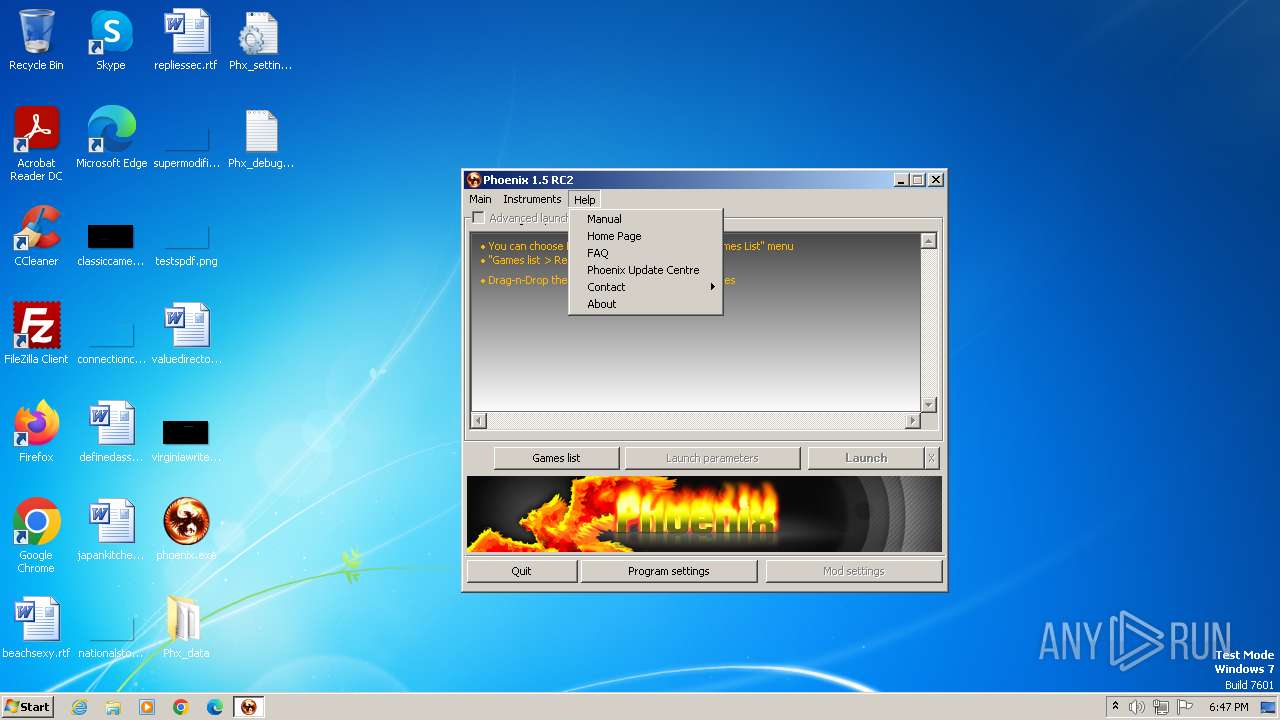
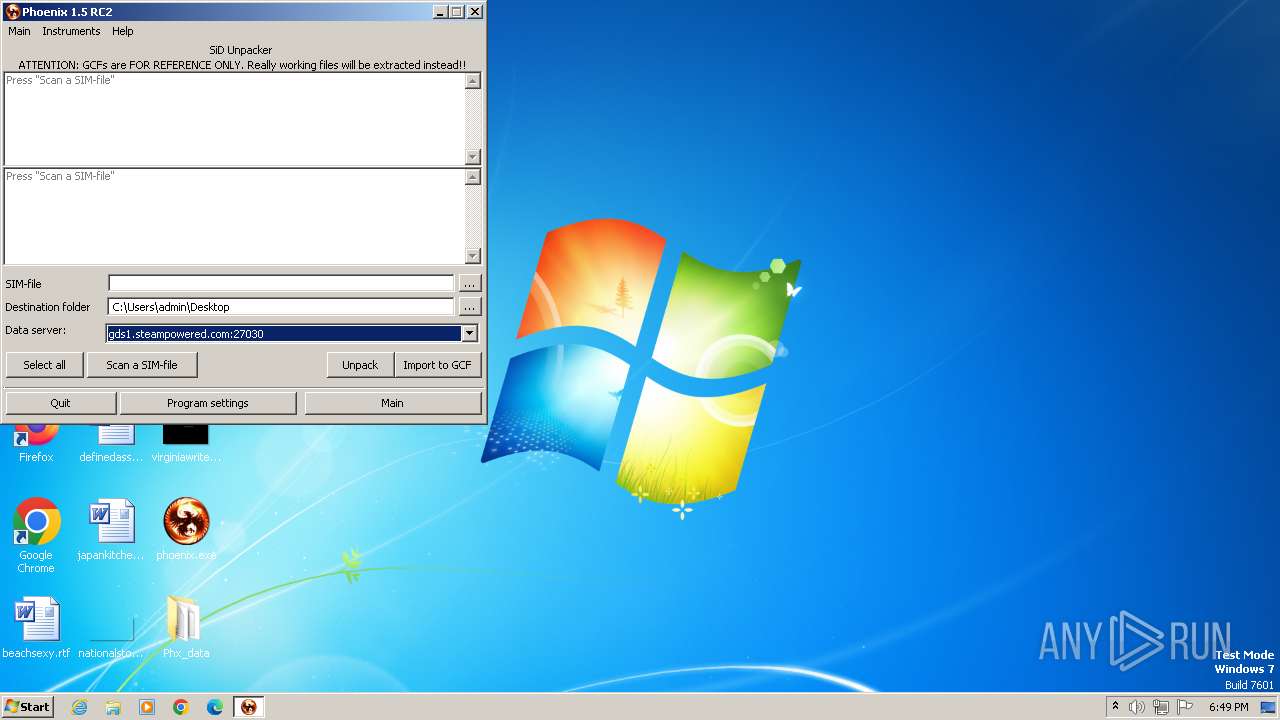
User: admin Company: $t@t!c_V()!D Integrity Level: MEDIUM Description: Phoenix Exit code: 1 Version: 1.5 RC2 Modules
| |||||||||||||||
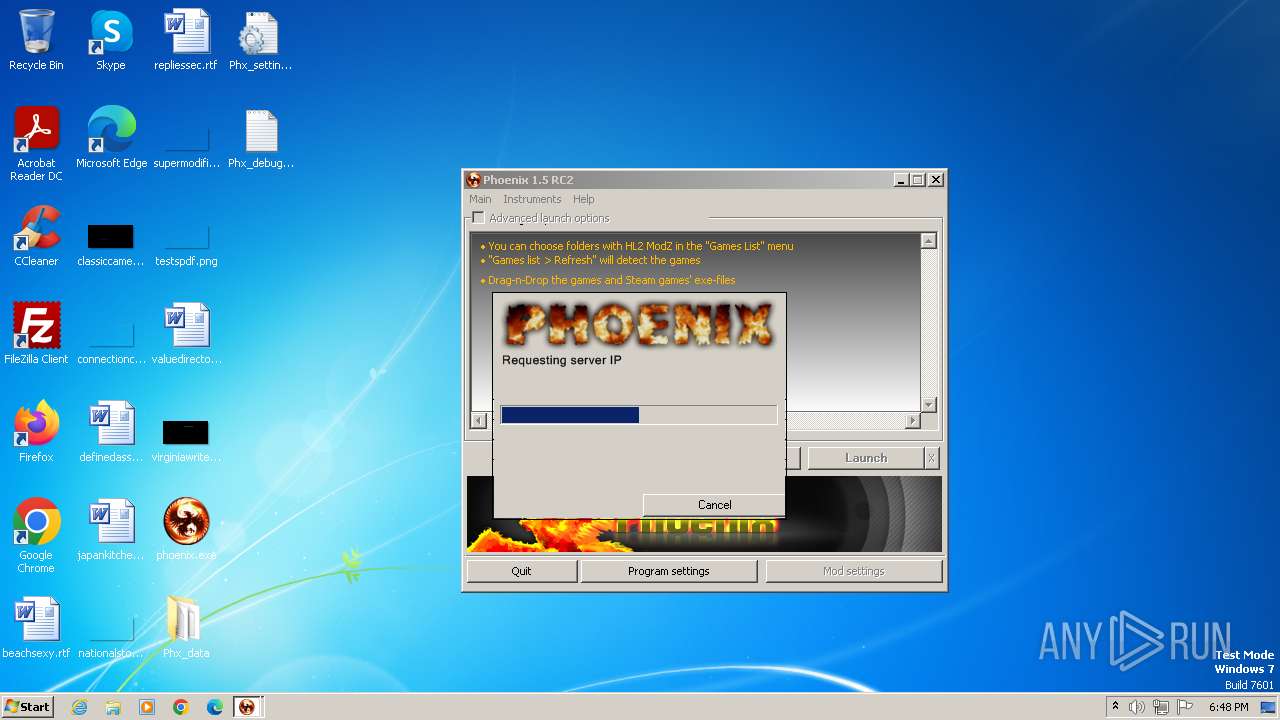
| 2624 | "C:\Users\admin\Desktop\Phx_data\Res\UpdCentre.exe" /currentver=10430 /PhxWND=262572 | C:\Users\admin\Desktop\Phx_data\Res\UpdCentre.exe | phoenix.exe | ||||||||||||
User: admin Company: $t@t!c_V()1D Integrity Level: MEDIUM Description: Phoenix Update Centre Exit code: 0 Version: 1.2 Modules
| |||||||||||||||
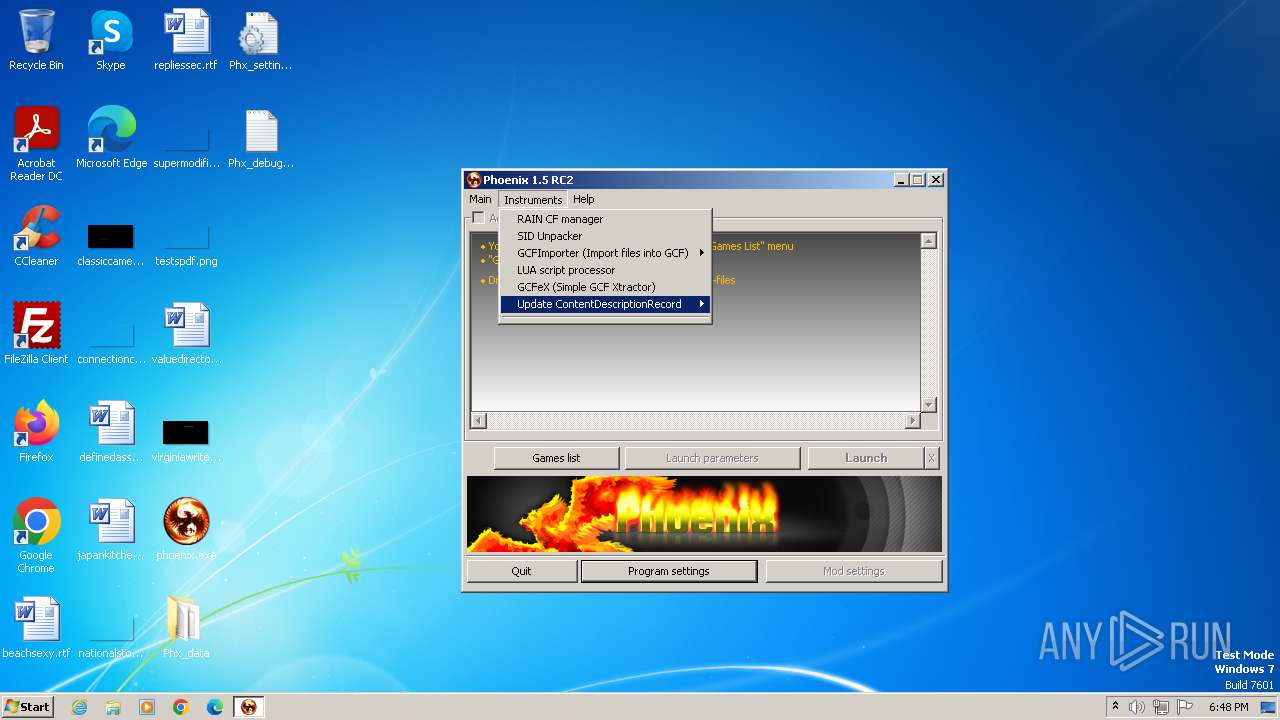
| 2816 | C:\Users\admin\Desktop\Phx_data\Res\GCFeX.exe | C:\Users\admin\Desktop\Phx_data\Res\GCFeX.exe | — | phoenix.exe | |||||||||||
User: admin Company: $t@t!c_V()1D Integrity Level: MEDIUM Description: Game Cache File extractor for Phoenix Exit code: 0 Version: 1.0 Modules
| |||||||||||||||
Total events
2 095
Read events
2 056
Write events
38
Delete events
1
Modification events
| (PID) Process: | (2204) phoenix.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2204) phoenix.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 06000000000000000B0000000100000002000000070000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2204) phoenix.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000006000000000000000B00000001000000070000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2204) phoenix.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2204) phoenix.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2204) phoenix.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2204) phoenix.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2204) phoenix.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 4 |
Value: 700068006F0065006E00690078002E006500780065000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000D0010000BE000000500400009E020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (2204) phoenix.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000030000000000000001000000FFFFFFFF | |||
| (PID) Process: | (2204) phoenix.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
Executable files
53
Suspicious files
32
Text files
85
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | phoenix.exe | C:\Users\admin\Desktop\Phx_debug_log.txt | — | |
MD5:— | SHA256:— | |||
| 2204 | phoenix.exe | C:\Users\admin\Desktop\Phx_data\Res\SharedDLLs\RainCWrapper.dll | executable | |
MD5:1E7606256B18F76D04C528C454F7F868 | SHA256:7DD76FA45A716E8AC2DCABB7AC72D3E33C83E6560B2B191E87AC38D6728B7E6D | |||
| 2204 | phoenix.exe | C:\Users\admin\Desktop\Phx_data\Res\SharedDLLs\SimDecrypt.dll | executable | |
MD5:BB937CB8E64491477B7AFF90E8C3F115 | SHA256:F08CD9C973BD3867977B6C54A900F26B3A796FA87CF1103E993DCA7C95B08460 | |||
| 2204 | phoenix.exe | C:\Users\admin\Desktop\Phx_data\Res\SharedDLLs\VDFParse.dll | executable | |
MD5:55A30732B7664376270D2A95E5AF73AA | SHA256:440CE87EBF573FCEB28C23B3ED8197FEDD308251EE205B24496A40145C707C62 | |||
| 2204 | phoenix.exe | C:\Users\admin\Desktop\Phx_data\Res\SharedDLLs\rain.dll | executable | |
MD5:FD099518479B7B7BA3A37563D18631DA | SHA256:24F3A2917A6469190D2FDB4489C5FB30916461B40C3400961513FAB17D06C4A5 | |||
| 2204 | phoenix.exe | C:\Users\admin\Desktop\Phx_data\Res\SharedDLLs\lua.dll | executable | |
MD5:9EF8FE20BBFA664A5D6F5730EBC09192 | SHA256:6035318816C7F0C7C89BE2D164C842859CB5651C613E62F76221D1EB7AB4E0D3 | |||
| 2204 | phoenix.exe | C:\Users\admin\Desktop\Phx_data\Res\SharedDLLs\m3uhZnAd.dat | executable | |
MD5:00D9CECBBD06138DEBBC8F98DA01E1A1 | SHA256:BBBBE4E428DE60FE59CC3501B8BF600BBBC132711FA7FE69457FB7BC5E7139FB | |||
| 2204 | phoenix.exe | C:\Users\admin\Desktop\Phx_data\Res\SharedDLLs\Main.dll | executable | |
MD5:9168E68DF76A1F05E73F4BCCAE96BC38 | SHA256:0F3250DE4E46223AC483CD905EF26438C573680CF780D3D0811846D487F9A465 | |||
| 2204 | phoenix.exe | C:\Users\admin\Desktop\Phx_settings.ini | text | |
MD5:76F5AE14516A7970EE0819B963130E38 | SHA256:2DD76C5C1339F7B3C35090531AB100AD20D15F9CC4887C61F7B600720959F587 | |||
| 2204 | phoenix.exe | C:\Users\admin\Desktop\Phx_data\Res\bkg_work.exe | executable | |
MD5:D7C6AC95992038A2A5E51394570D454B | SHA256:9198E9939ACEE566636AD653C97815FB01D00DC7B0E19A117745687E4BE4C581 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
3
Threats
2
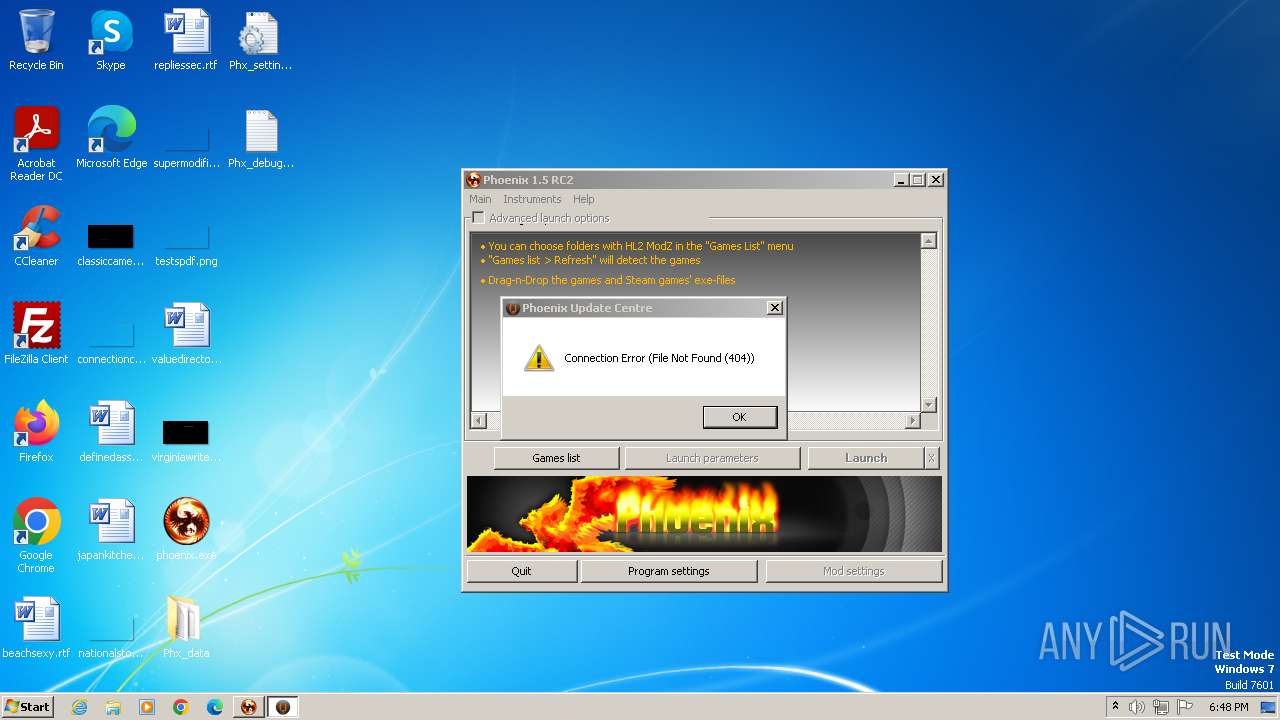
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2624 | UpdCentre.exe | GET | 404 | 49.13.77.253:80 | http://stat1cv01d.ucoz.ru/latest.dat | unknown | xml | 341 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
— | — | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2624 | UpdCentre.exe | 49.13.77.253:80 | stat1cv01d.ucoz.ru | Hetzner Online GmbH | DE | unknown |
2204 | phoenix.exe | 49.13.77.253:27030 | stat1cv01d.ucoz.ru | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stat1cv01d.ucoz.ru |
| unknown |
gds1.steampowered.com |
| unknown |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2624 | UpdCentre.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Generic Phishing domain observed in HTTP Host (DadSec / Storm-1575) |
1 ETPRO signatures available at the full report