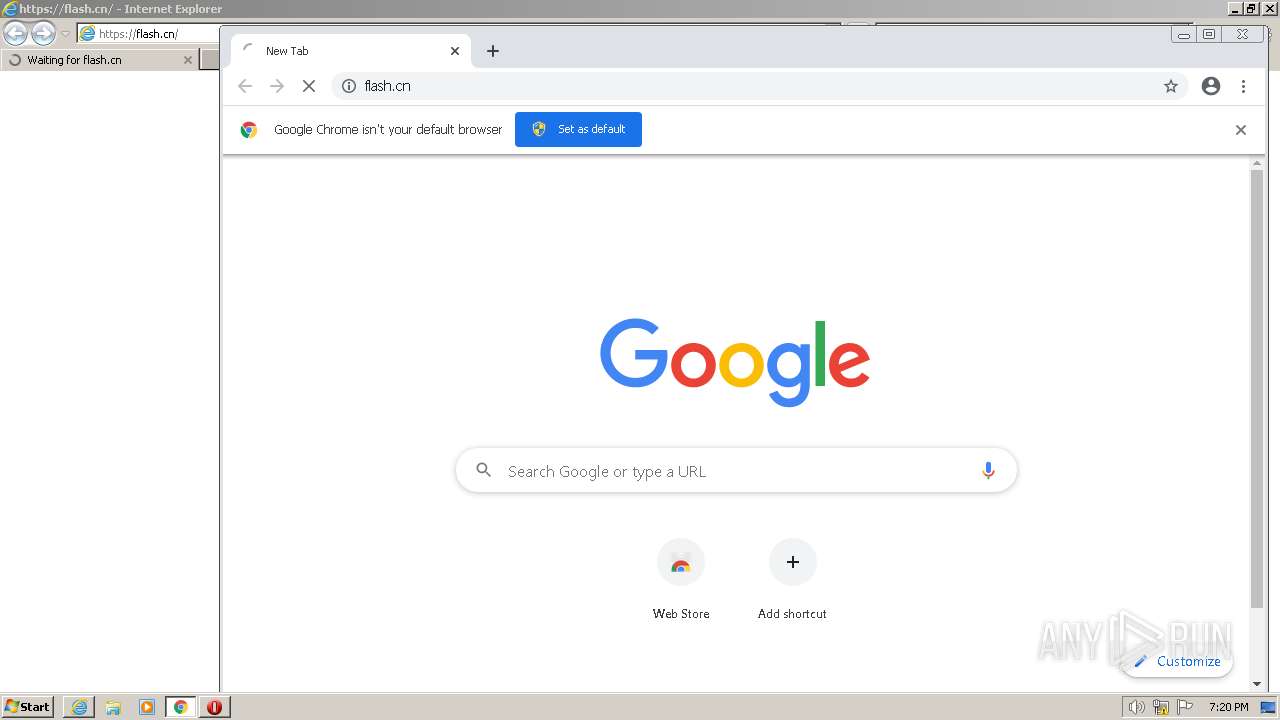
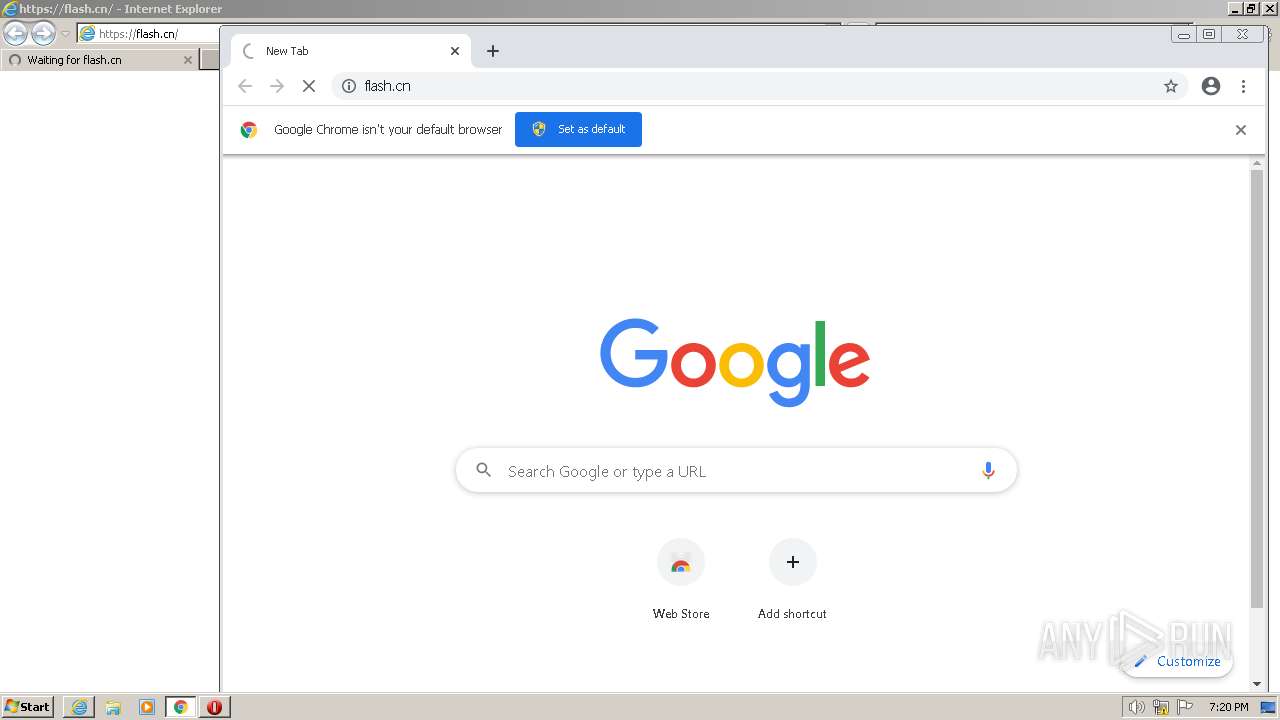
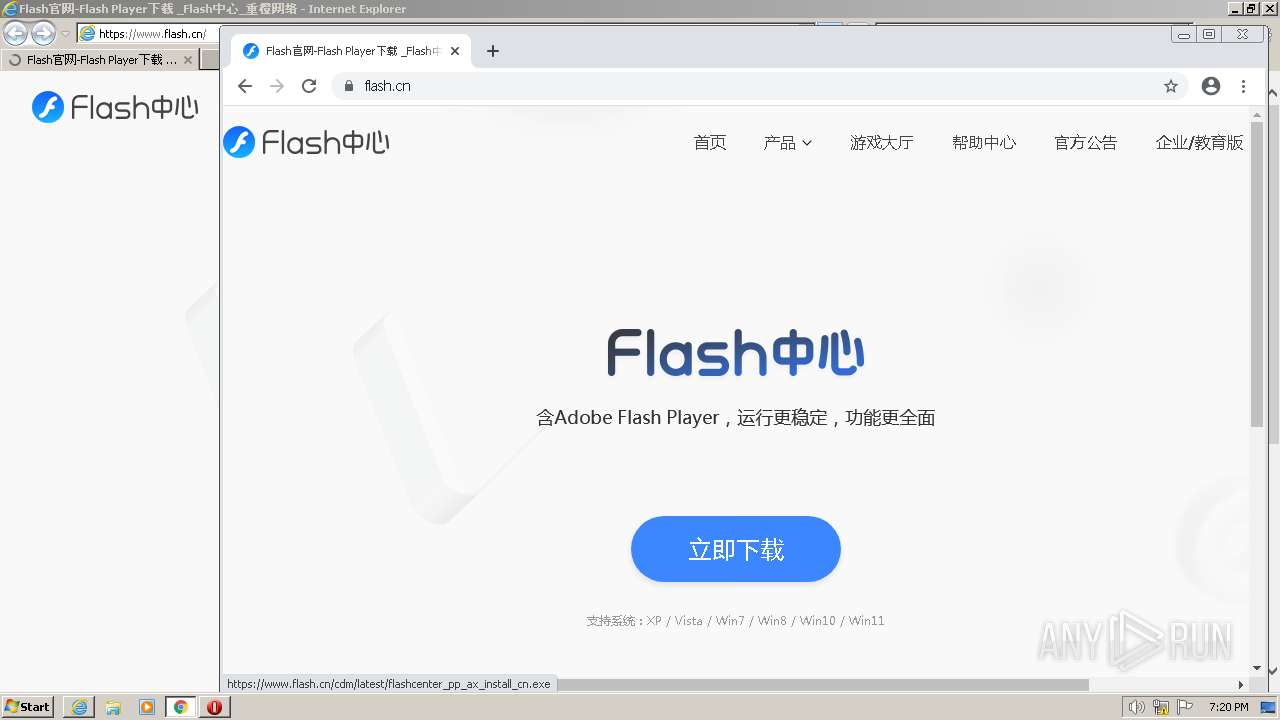
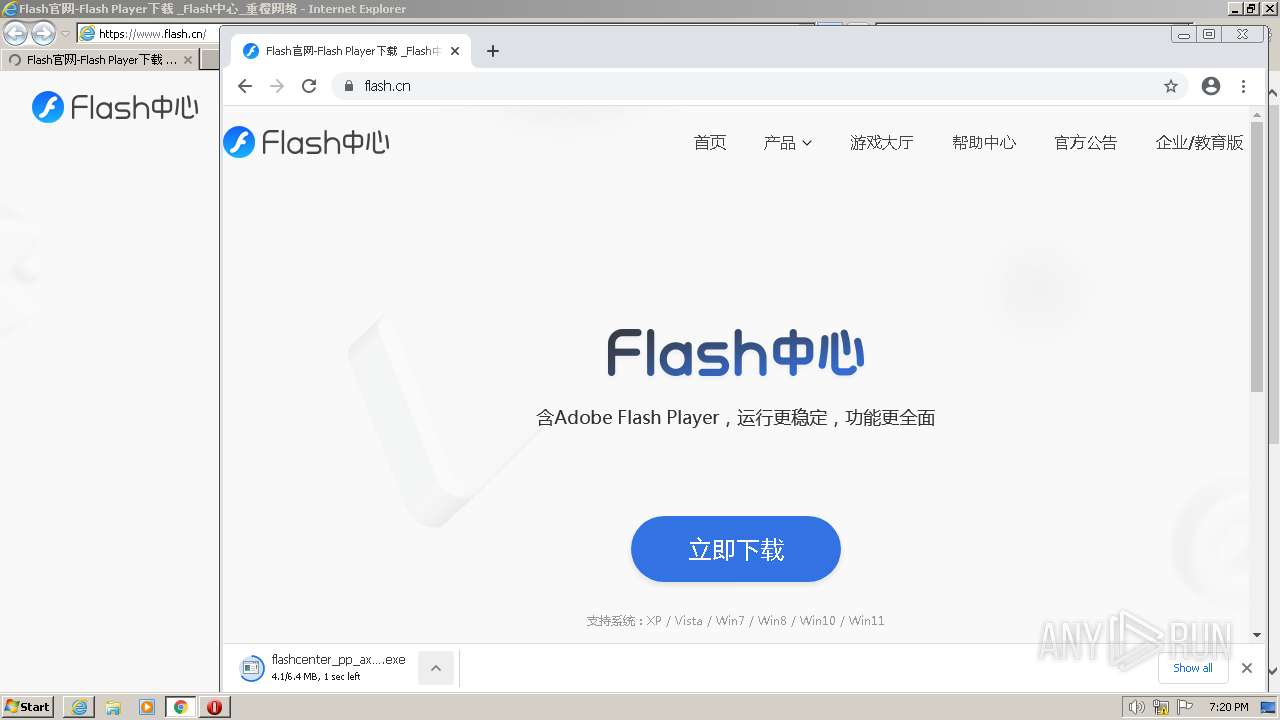
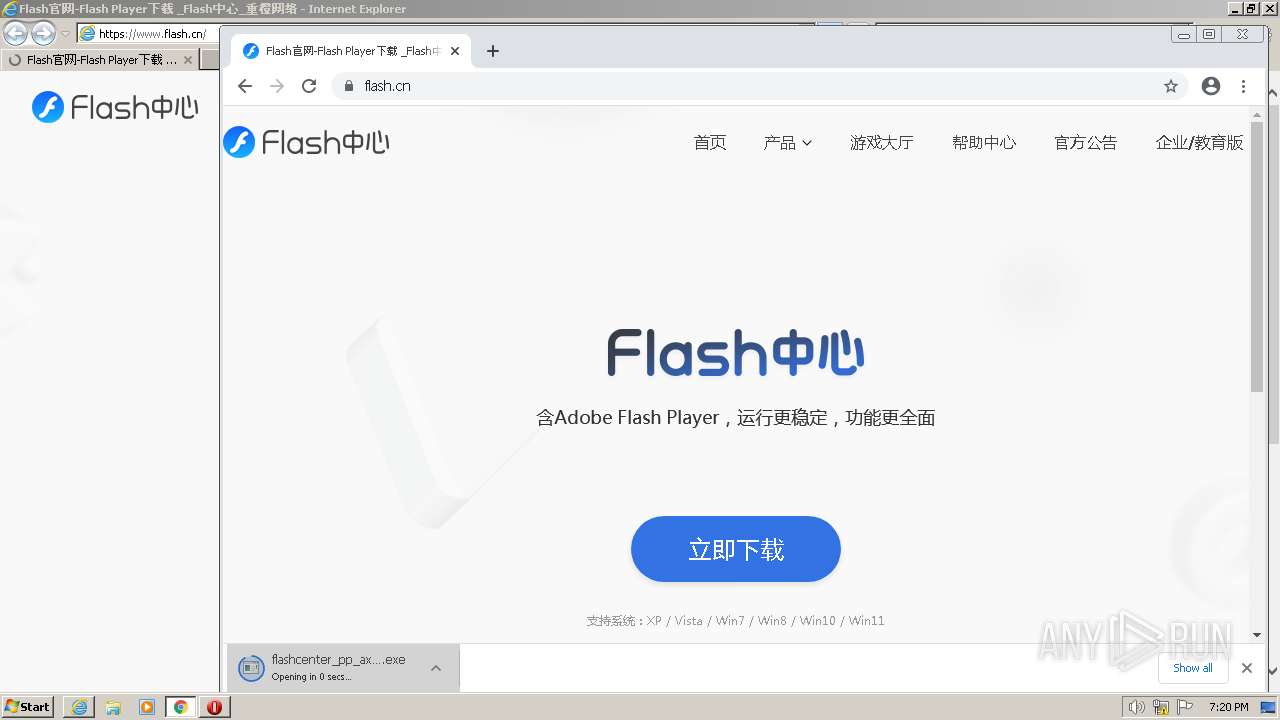
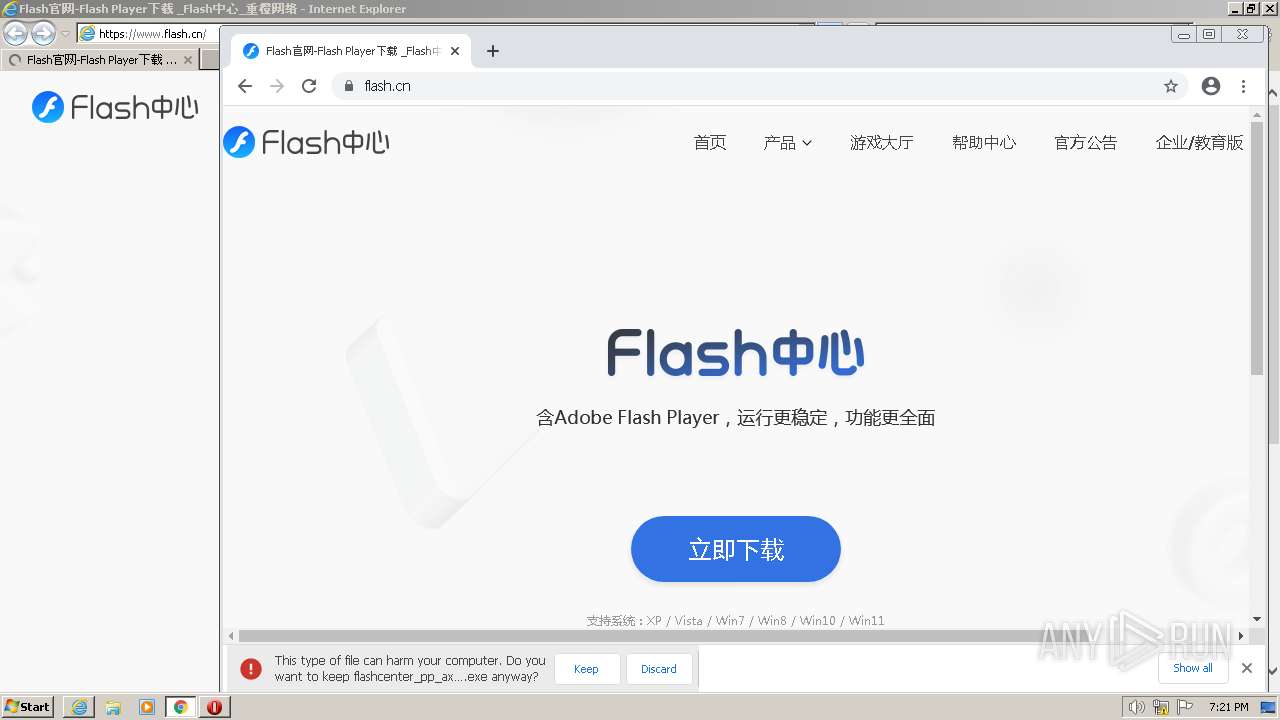
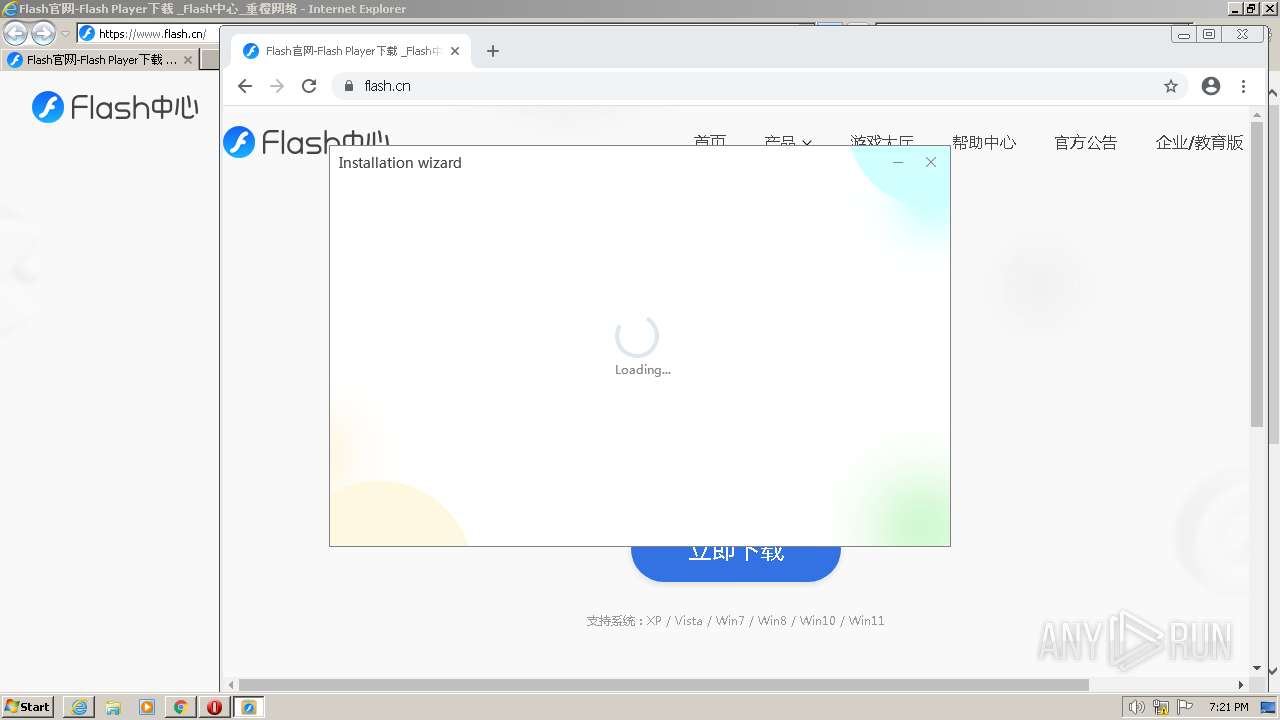
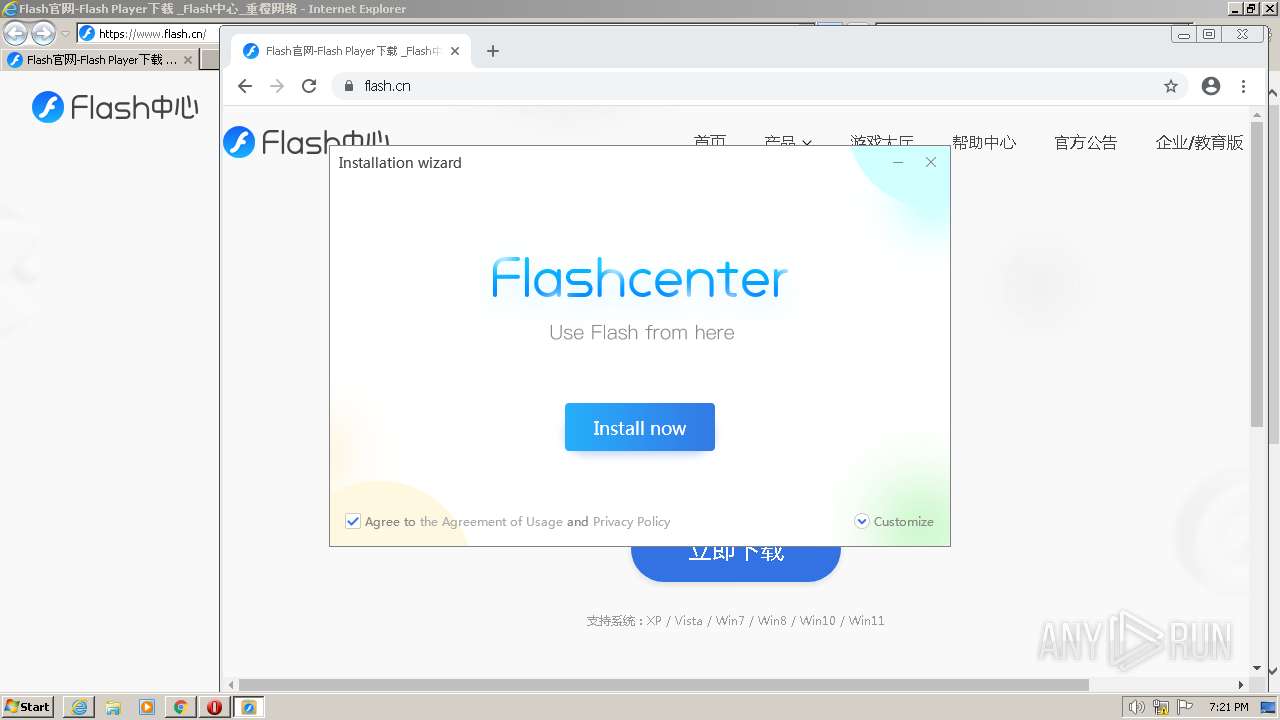
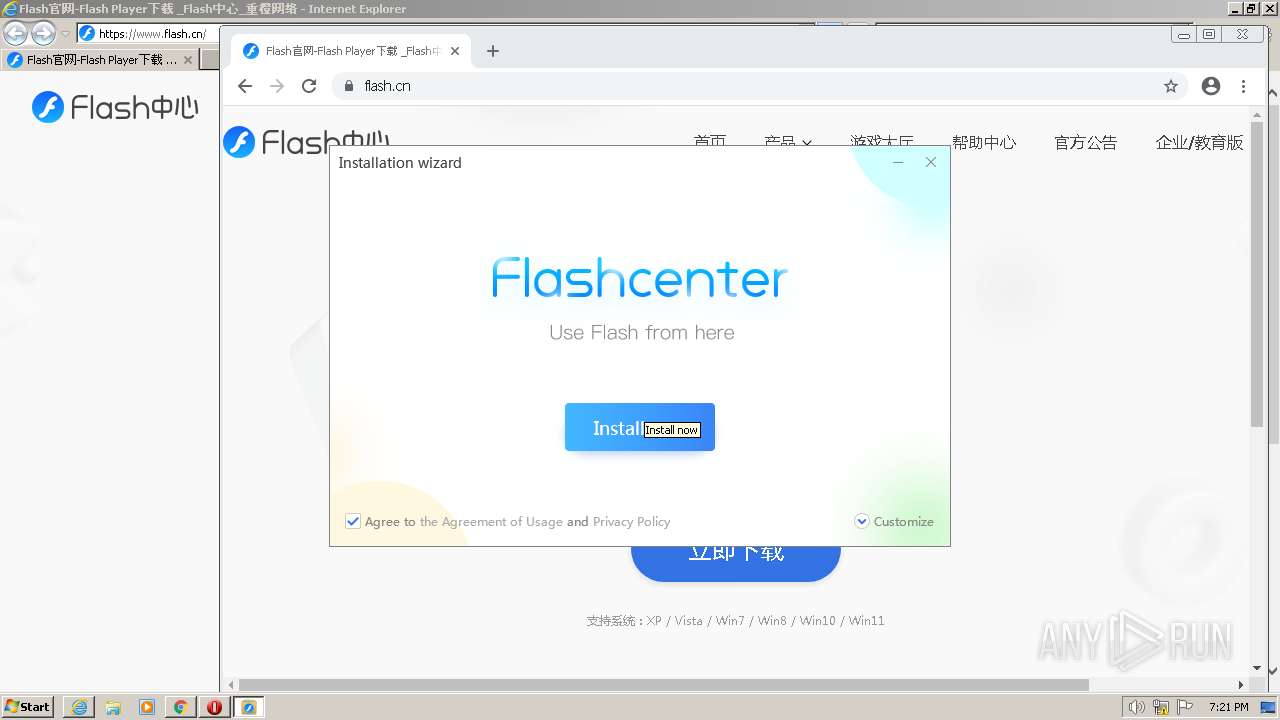
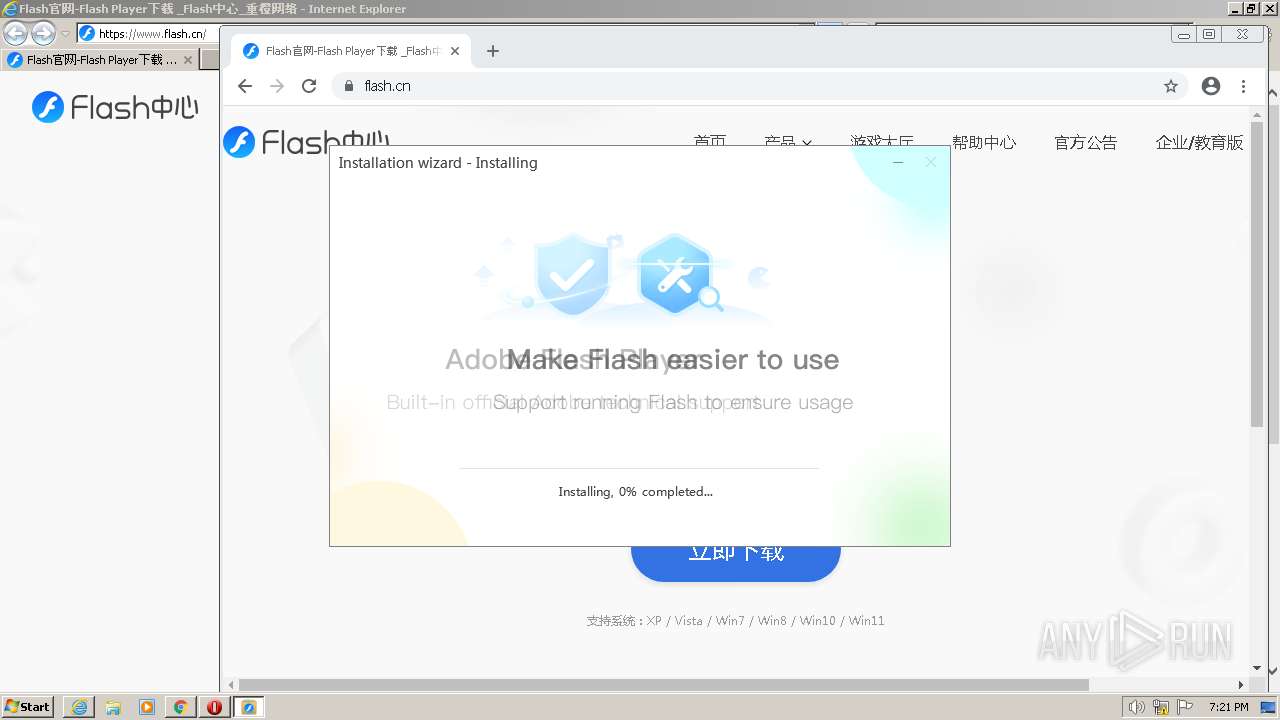
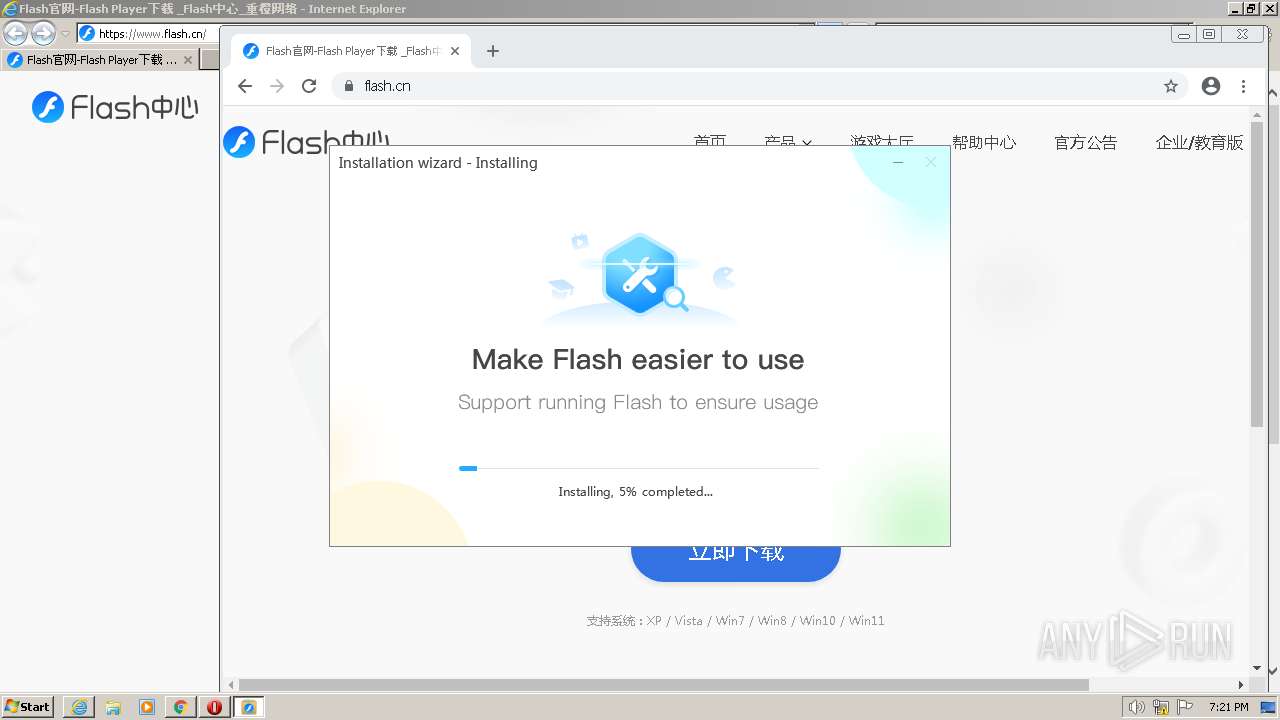
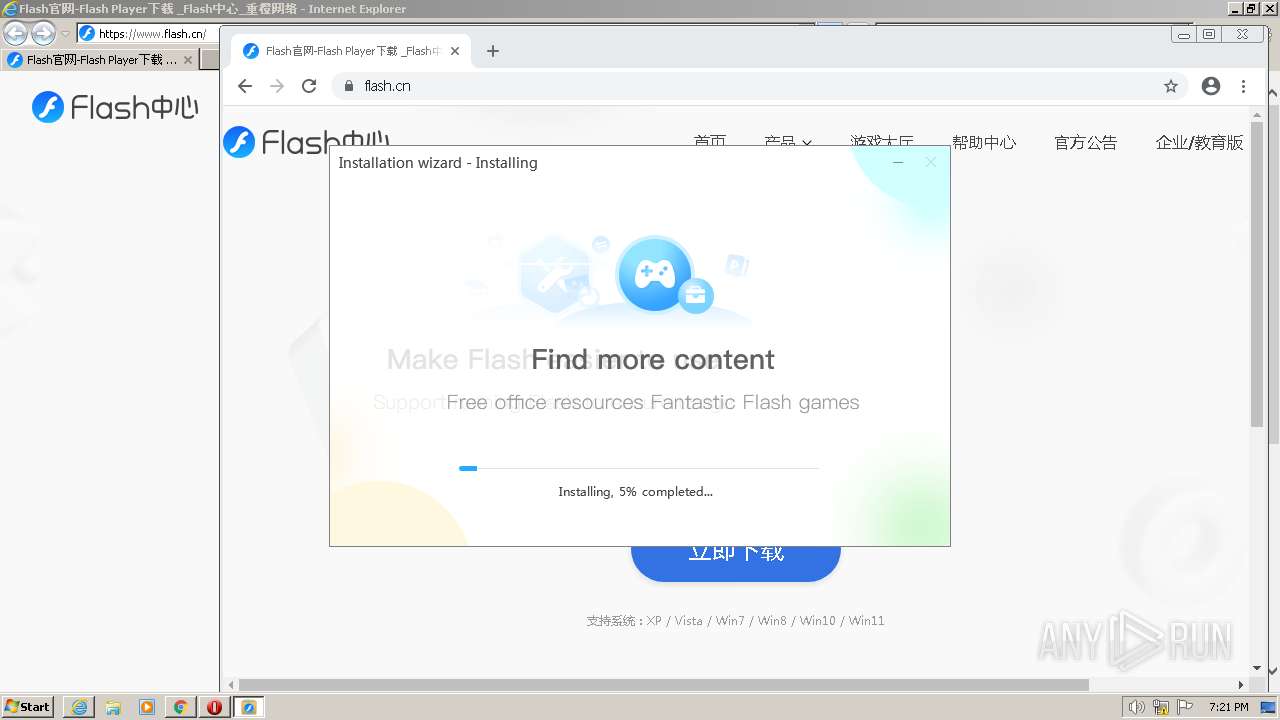
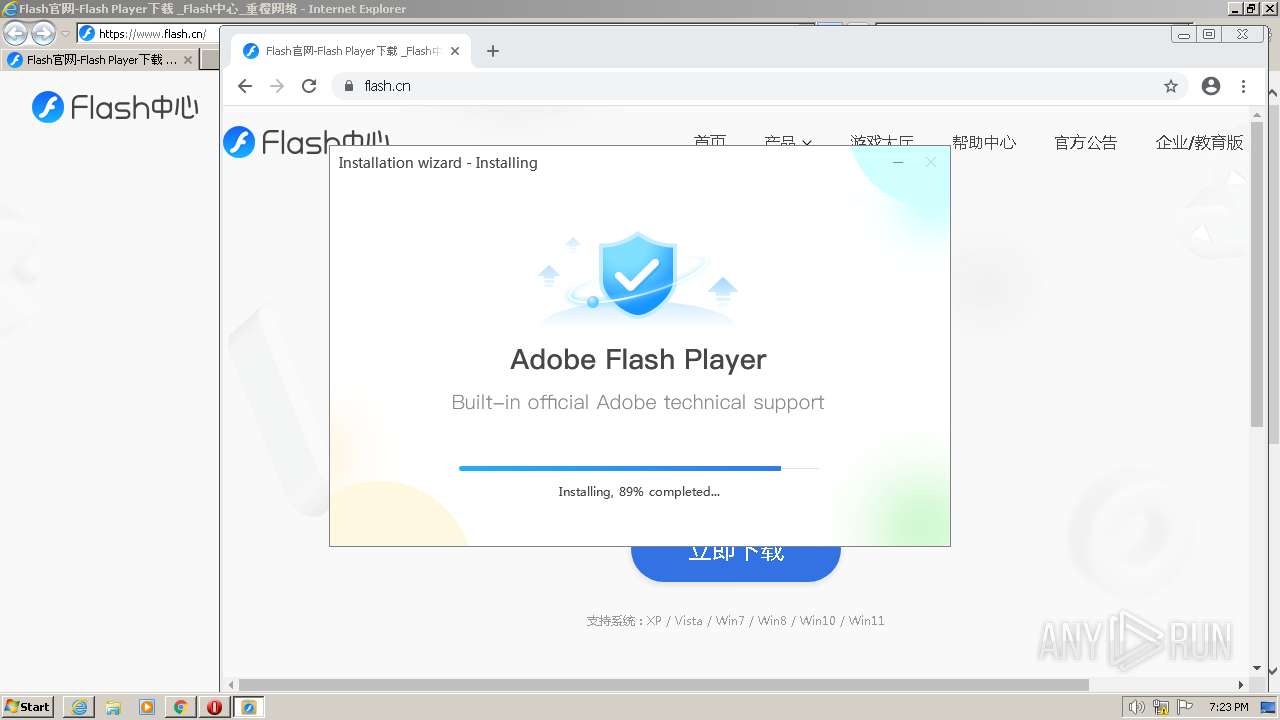
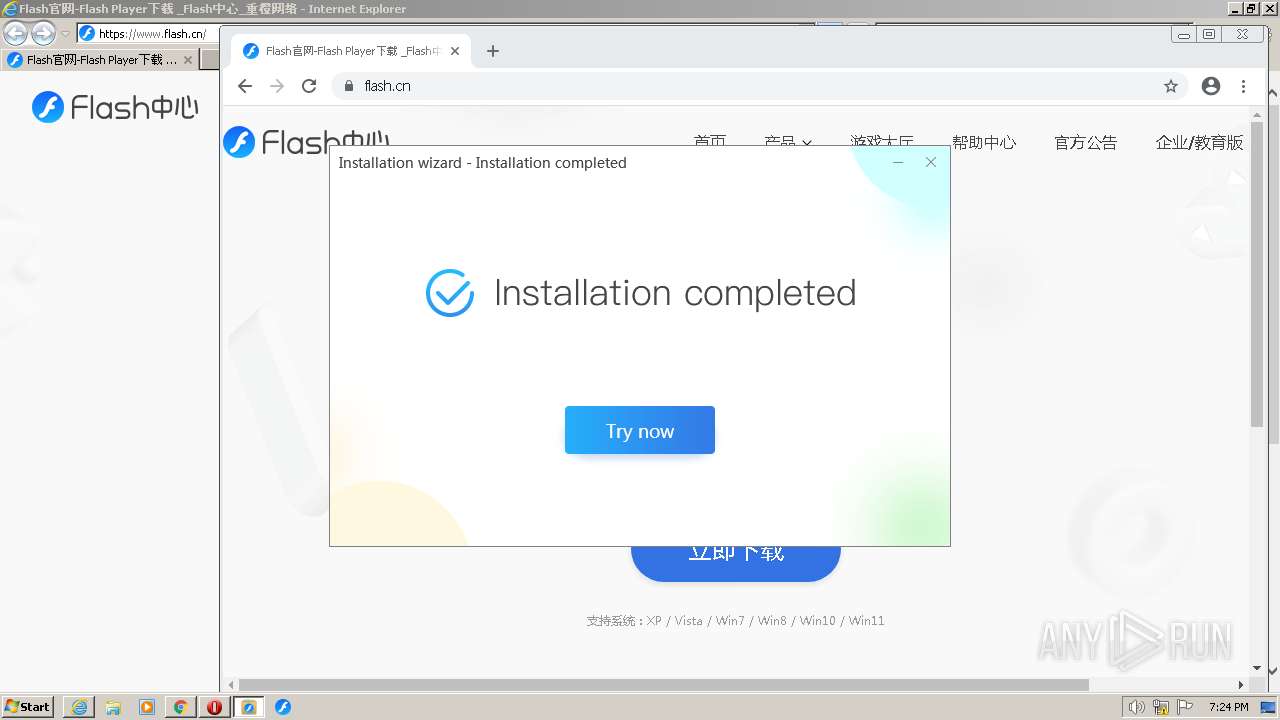
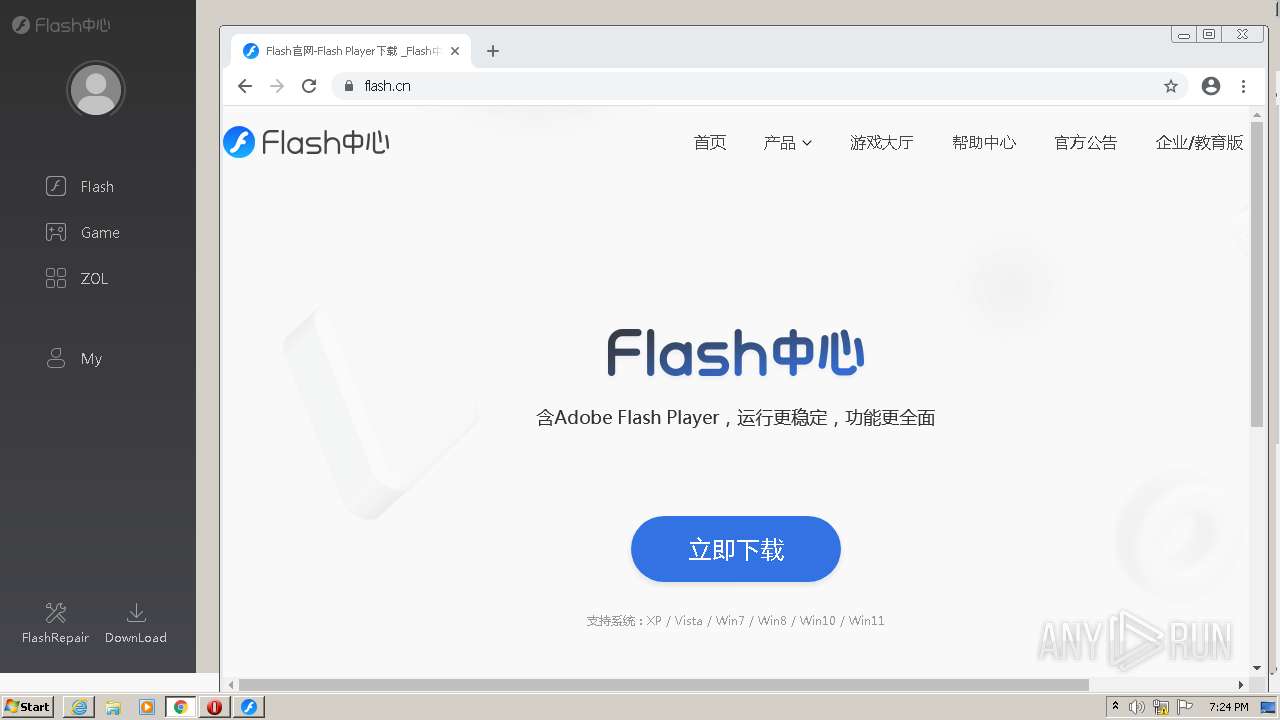
| URL: | https://flash.cn |
| Full analysis: | https://app.any.run/tasks/c170b0ed-5f76-4d3f-a08f-cb8a1a07ac1b |
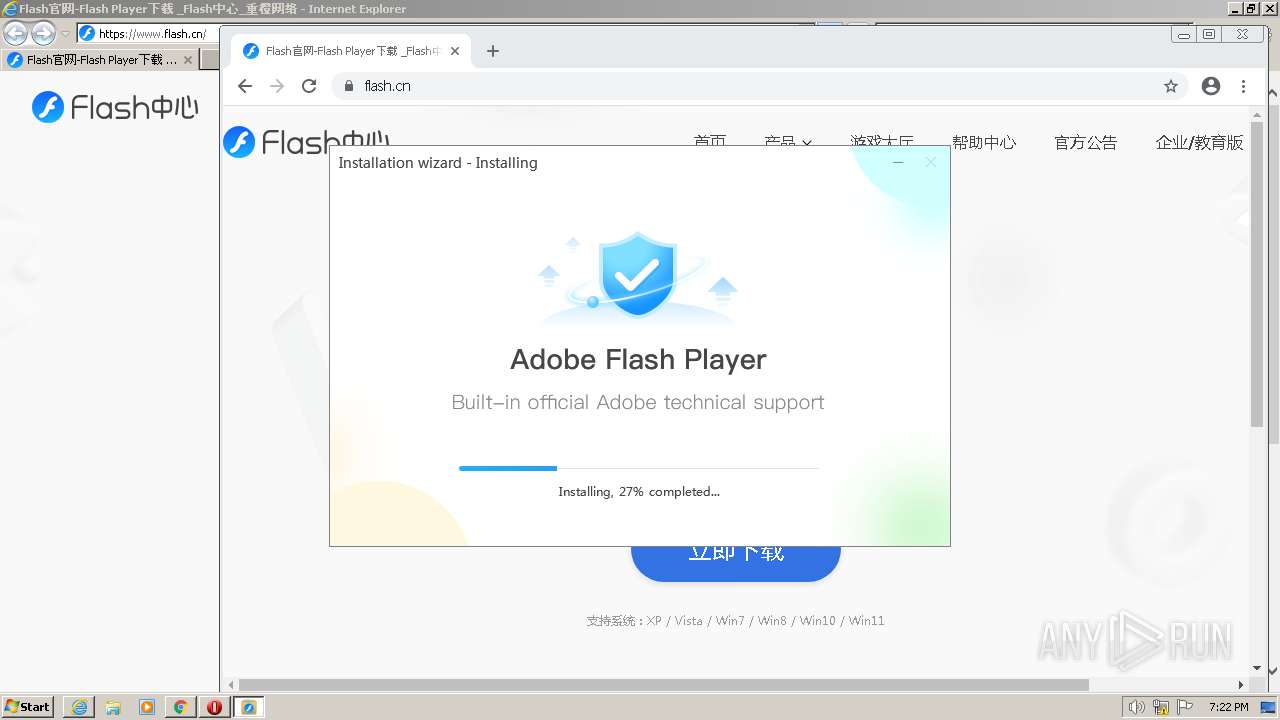
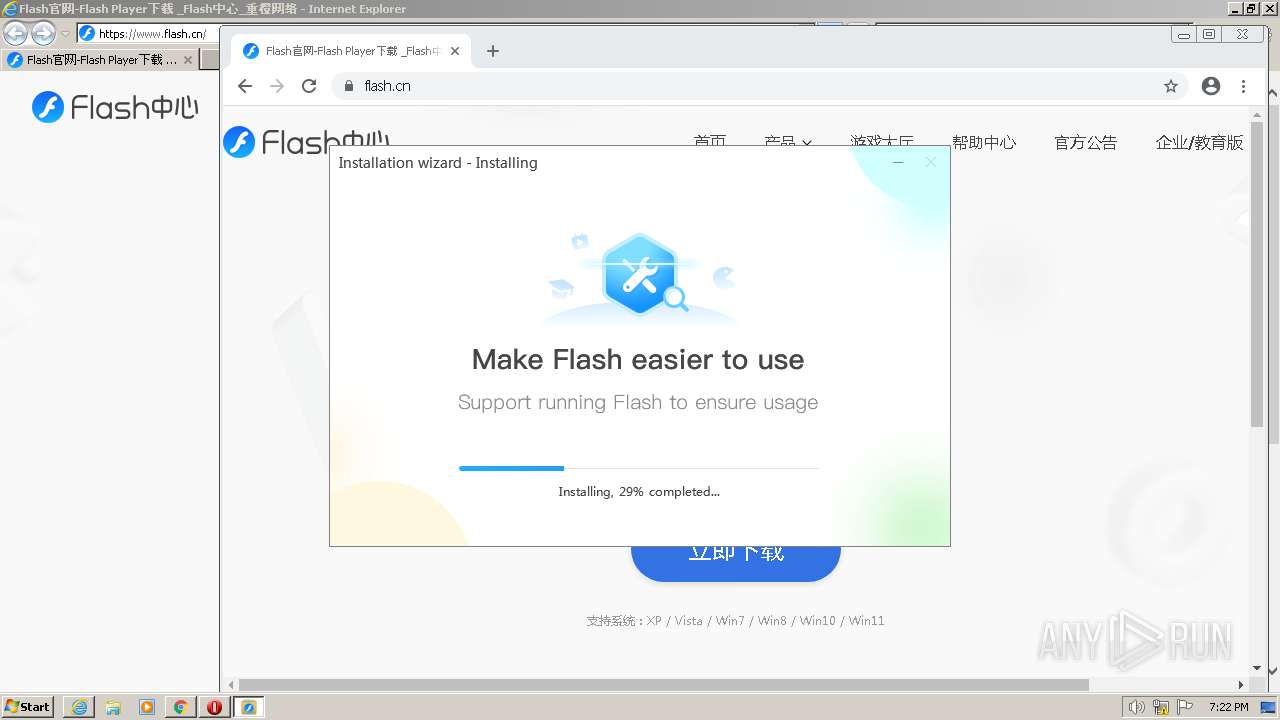
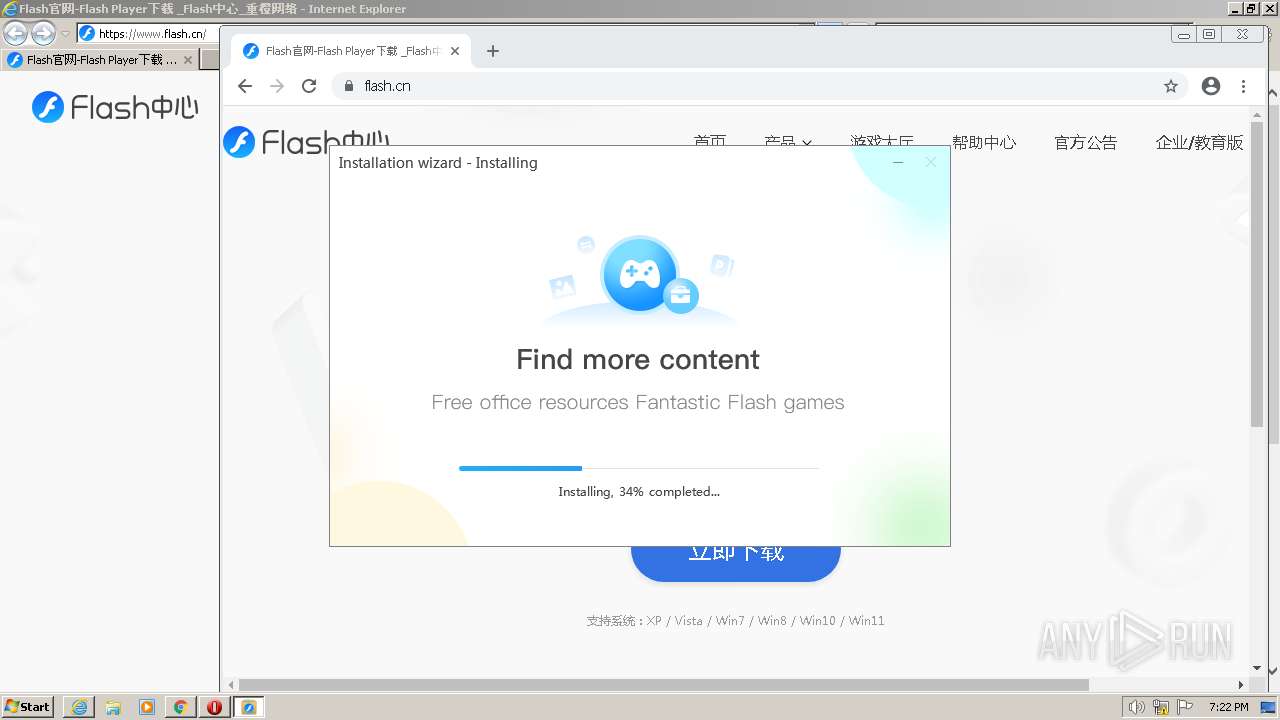
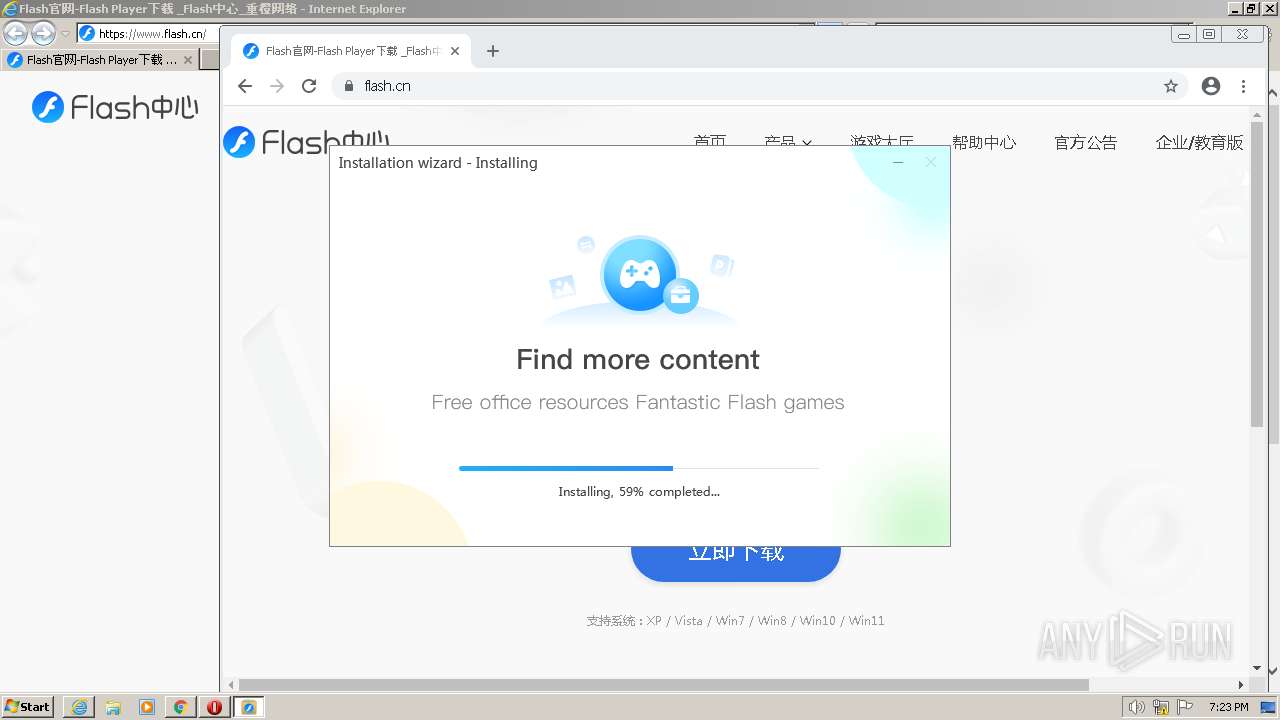
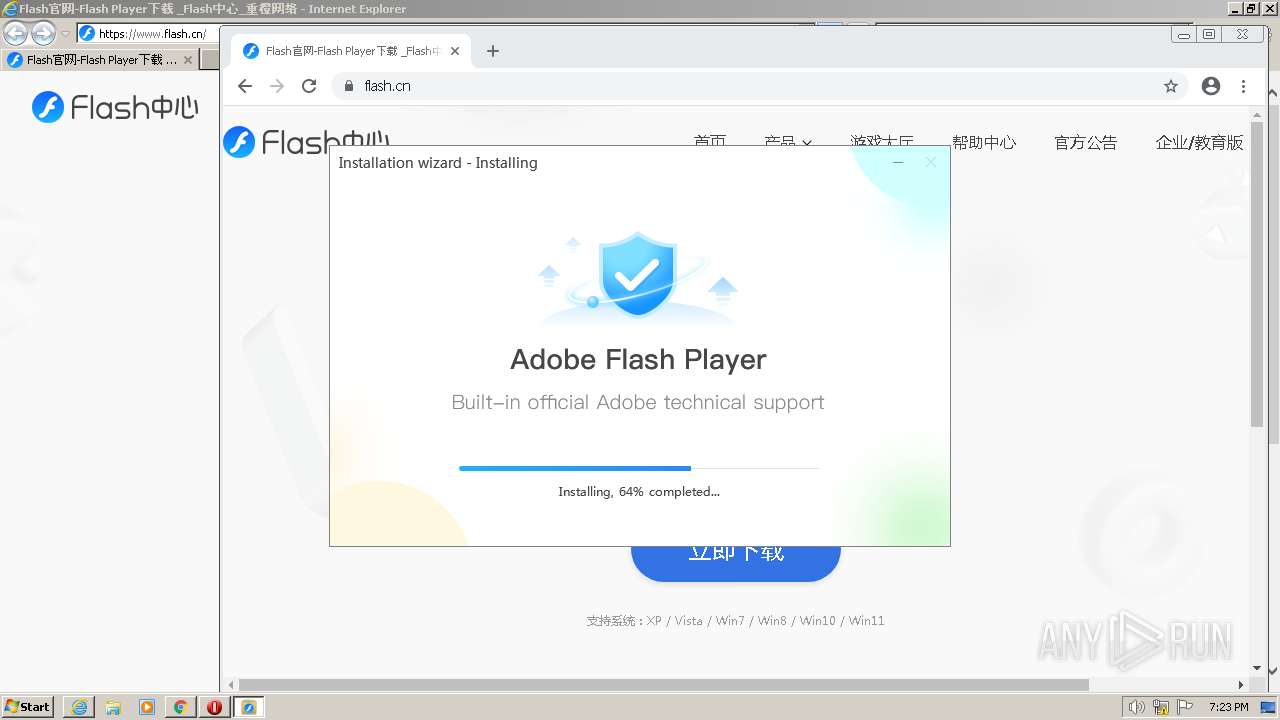
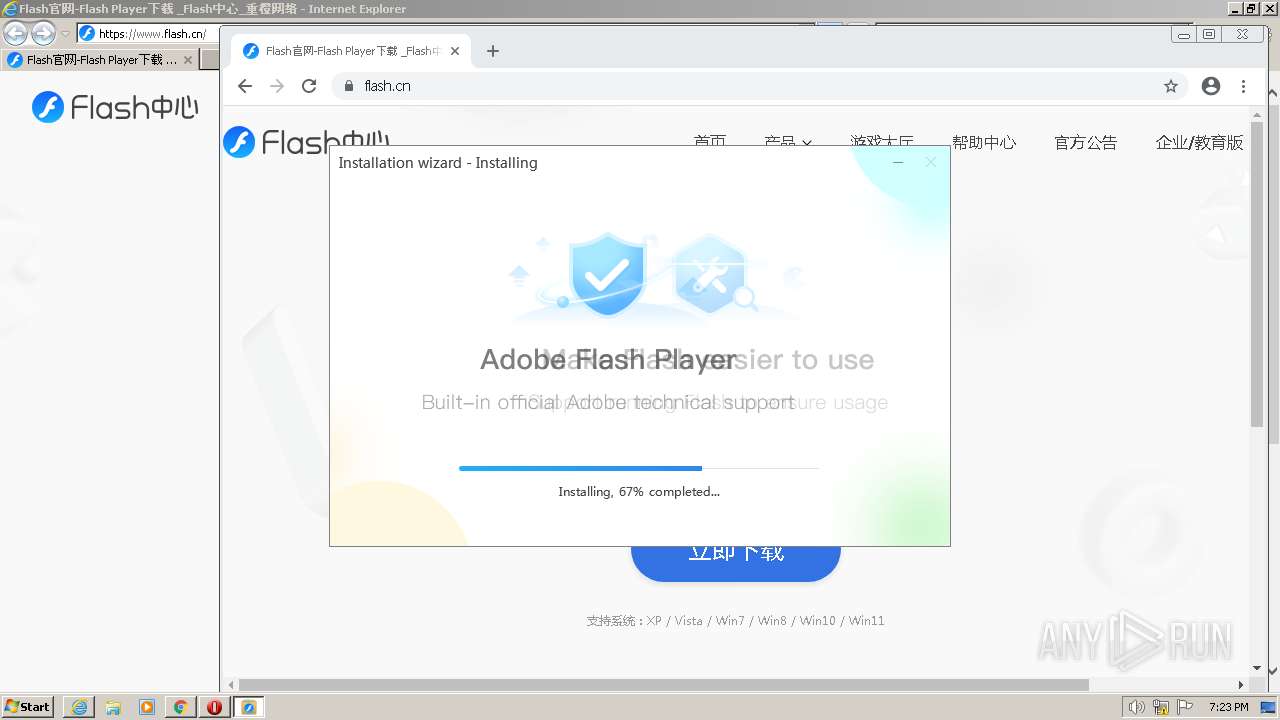
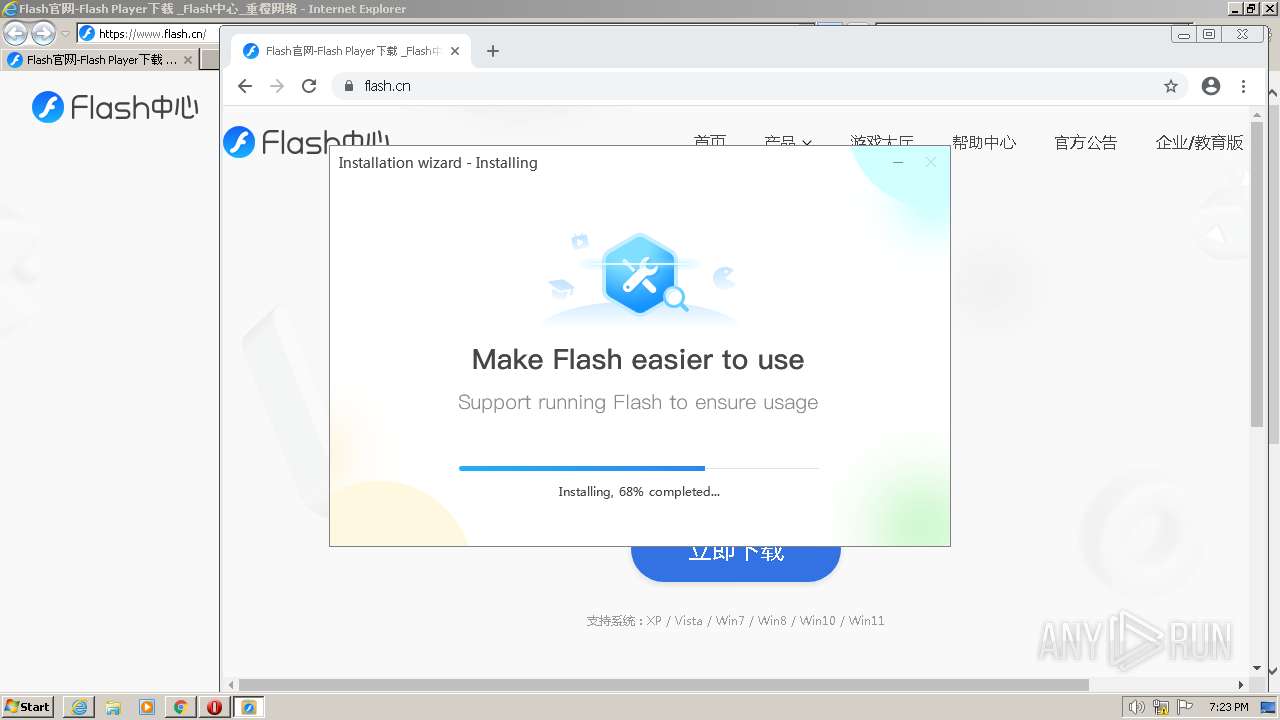
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2023, 18:19:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1F040A7C7D9B1C4760FA3950C1C362B4 |
| SHA1: | 2AB174A12CC217A7BAB519B68FA119B2D331EEAA |
| SHA256: | 4C79A9C3EACDEBBF939B068CBC0F15641528A16FFBEC22956833496E78F97FB1 |
| SSDEEP: | 3:N8AW4Ln:2zG |
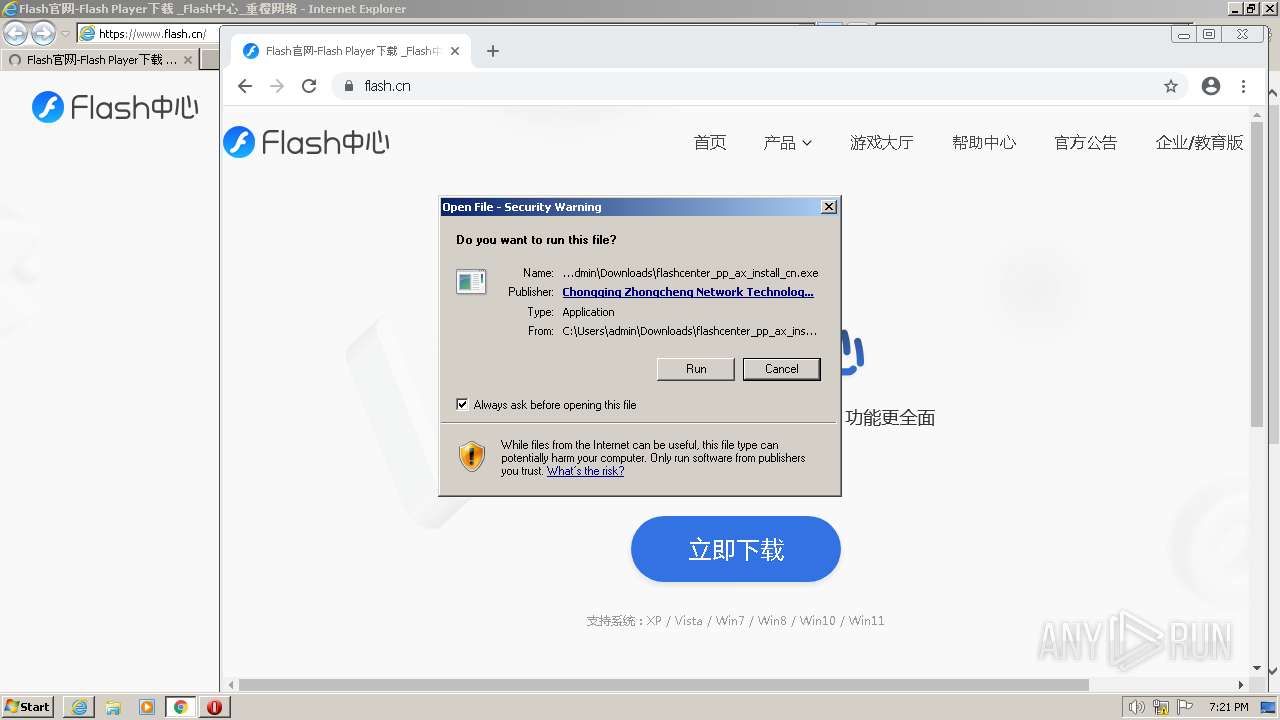
MALICIOUS
Application was dropped or rewritten from another process
- flashcenter_pp_ax_install_cn.exe (PID: 3804)
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
- FlashHelperService.exe (PID: 2028)
- FlashHelperService.exe (PID: 4052)
- FlashCenterSvc.exe (PID: 3716)
- FlashCenterSvc.exe (PID: 2252)
- FCLogin.exe (PID: 2456)
- FlashCenter.exe (PID: 1148)
- FCBrowser.exe (PID: 4000)
- FCBrowser.exe (PID: 2856)
- FCBrowser.exe (PID: 3160)
- FCBrowser.exe (PID: 3196)
- FCBrowser.exe (PID: 308)
- FCBrowser.exe (PID: 3380)
Creates a writable file the system directory
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
- flashcenter_pp_ax_install_cn.exe (PID: 3804)
- FlashHelperService.exe (PID: 4052)
Loads dropped or rewritten executable
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
- FlashCenterSvc.exe (PID: 2252)
- FlashCenterSvc.exe (PID: 3716)
- FlashCenter.exe (PID: 1148)
- FCBrowser.exe (PID: 4000)
- FCLogin.exe (PID: 2456)
- FCBrowser.exe (PID: 3380)
- FCBrowser.exe (PID: 3196)
- FCBrowser.exe (PID: 308)
- FCBrowser.exe (PID: 2856)
- FCBrowser.exe (PID: 3160)
Actions looks like stealing of personal data
- FlashCenterSvc.exe (PID: 3716)
SUSPICIOUS
Reads the Internet Settings
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
- FlashCenter.exe (PID: 1148)
- FCBrowser.exe (PID: 4000)
Application launched itself
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- FCBrowser.exe (PID: 4000)
Reads security settings of Internet Explorer
- flashcenter_pp_ax_install_cn.exe (PID: 3804)
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
Checks Windows Trust Settings
- flashcenter_pp_ax_install_cn.exe (PID: 3804)
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
Adds/modifies Windows certificates
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- flashcenter_pp_ax_install_cn.exe (PID: 3804)
- FCBrowser.exe (PID: 4000)
Reads settings of System Certificates
- flashcenter_pp_ax_install_cn.exe (PID: 3804)
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
- FlashCenter.exe (PID: 1148)
- FCBrowser.exe (PID: 2856)
Executable content was dropped or overwritten
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
- flashcenter_pp_ax_install_cn.exe (PID: 3804)
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
Reads Internet Explorer settings
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
Reads Microsoft Outlook installation path
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
Starts application with an unusual extension
- flashcenter_pp_ax_install_cn.exe (PID: 3804)
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
Process requests binary or script from the Internet
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
Starts CMD.EXE for commands execution
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
Disables SEHOP
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
Executes as Windows Service
- FlashHelperService.exe (PID: 4052)
- FlashCenterSvc.exe (PID: 3716)
Uses TASKKILL.EXE to kill process
- ns6EF3.tmp (PID: 2176)
- ns6FCF.tmp (PID: 1572)
- ns7128.tmp (PID: 2068)
- ns70AA.tmp (PID: 3816)
- ns7204.tmp (PID: 1712)
- ns733F.tmp (PID: 3116)
- ns742B.tmp (PID: 2148)
- ns7507.tmp (PID: 3864)
- ns7272.tmp (PID: 3704)
- ns7585.tmp (PID: 3040)
- ns73AD.tmp (PID: 3092)
- ns75F3.tmp (PID: 1156)
- ns7661.tmp (PID: 1360)
The process creates files with name similar to system file names
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
- FCBrowser.exe (PID: 3196)
Searches for installed software
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
INFO
Application launched itself
- iexplore.exe (PID: 2976)
- chrome.exe (PID: 2736)
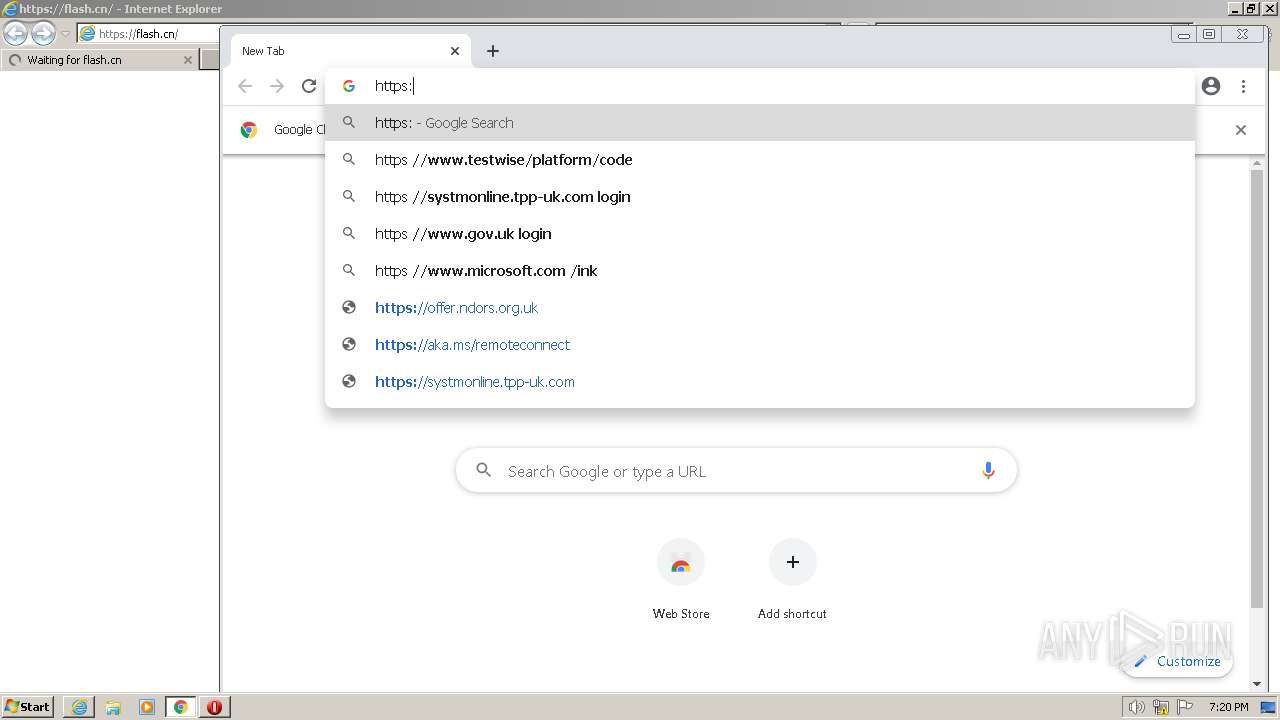
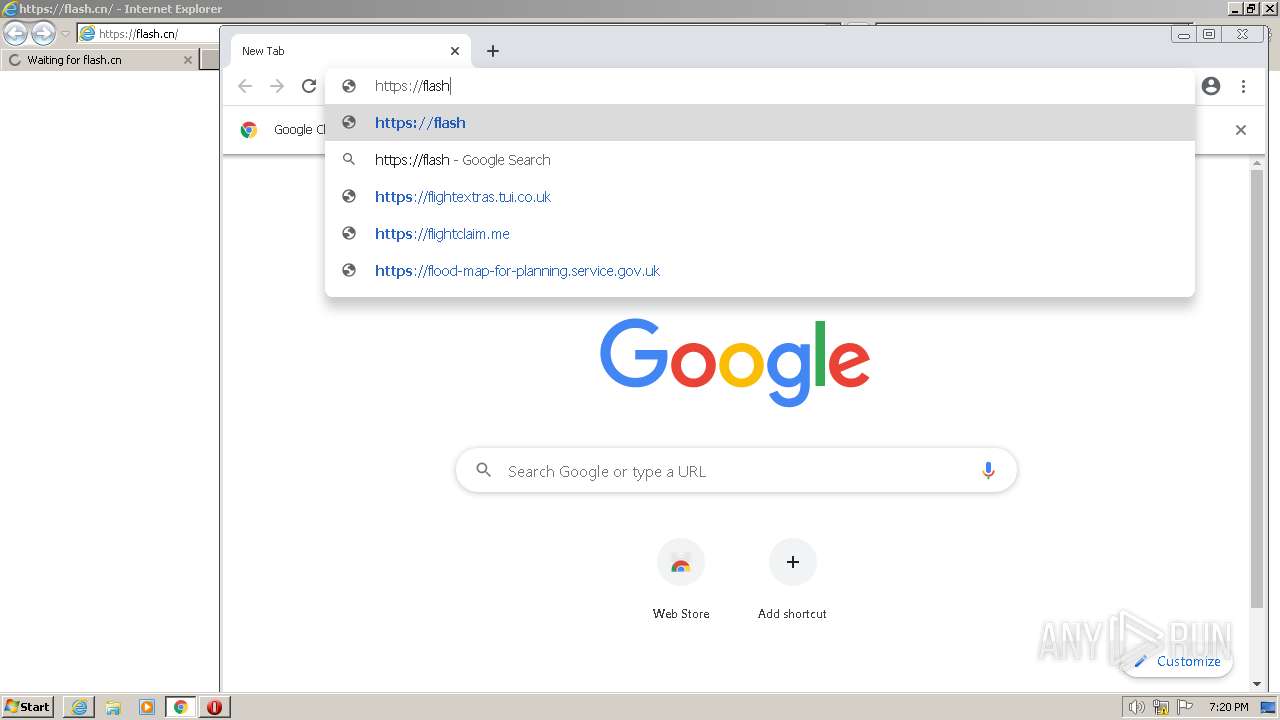
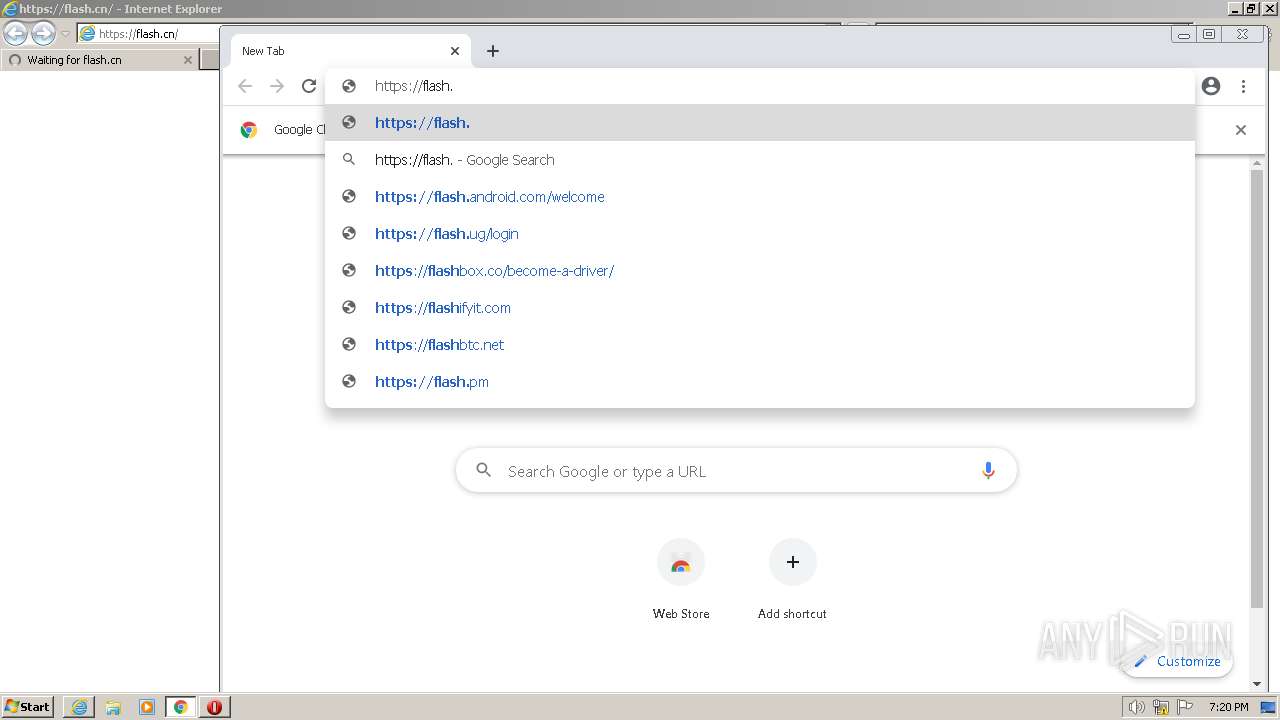
Manual execution by a user
- chrome.exe (PID: 2736)
Executable content was dropped or overwritten
- chrome.exe (PID: 3176)
- chrome.exe (PID: 2736)
The process uses the downloaded file
- chrome.exe (PID: 616)
- chrome.exe (PID: 2736)
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
The process checks LSA protection
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- flashcenter_pp_ax_install_cn.exe (PID: 3804)
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
- taskkill.exe (PID: 3556)
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
- taskkill.exe (PID: 2680)
- taskkill.exe (PID: 1584)
- taskkill.exe (PID: 2912)
- taskkill.exe (PID: 2696)
- taskkill.exe (PID: 2516)
- taskkill.exe (PID: 2792)
- taskkill.exe (PID: 3220)
- taskkill.exe (PID: 2600)
- taskkill.exe (PID: 1476)
- taskkill.exe (PID: 2932)
- taskkill.exe (PID: 2228)
- taskkill.exe (PID: 3780)
- FlashHelperService.exe (PID: 4052)
- FlashCenterSvc.exe (PID: 3716)
- FlashCenter.exe (PID: 1148)
- FCLogin.exe (PID: 2456)
- FCBrowser.exe (PID: 4000)
- FCBrowser.exe (PID: 3160)
- FCBrowser.exe (PID: 2856)
Create files in a temporary directory
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
Reads the computer name
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- flashcenter_pp_ax_install_cn.exe (PID: 3804)
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- FlashPlayerUpdateService.exe (PID: 3424)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
- FlashHelperService.exe (PID: 2028)
- FlashHelperService.exe (PID: 4052)
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
- FlashCenterSvc.exe (PID: 2252)
- FlashCenterSvc.exe (PID: 3716)
- FlashCenter.exe (PID: 1148)
- FCBrowser.exe (PID: 4000)
- FCLogin.exe (PID: 2456)
- FCBrowser.exe (PID: 3160)
- FCBrowser.exe (PID: 3196)
- FCBrowser.exe (PID: 3380)
- FCBrowser.exe (PID: 2856)
- FCBrowser.exe (PID: 308)
Checks supported languages
- flashcenter_pp_ax_install_cn.exe (PID: 3804)
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- FlashPlayerUpdateService.exe (PID: 3424)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
- FlashHelperService.exe (PID: 2028)
- FlashHelperService.exe (PID: 4052)
- ns6EF3.tmp (PID: 2176)
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
- ns70AA.tmp (PID: 3816)
- ns7128.tmp (PID: 2068)
- ns6FCF.tmp (PID: 1572)
- ns7204.tmp (PID: 1712)
- ns7272.tmp (PID: 3704)
- ns742B.tmp (PID: 2148)
- ns733F.tmp (PID: 3116)
- ns73AD.tmp (PID: 3092)
- ns7585.tmp (PID: 3040)
- ns7507.tmp (PID: 3864)
- ns75F3.tmp (PID: 1156)
- ns7661.tmp (PID: 1360)
- FlashCenterSvc.exe (PID: 2252)
- FlashCenterSvc.exe (PID: 3716)
- FlashCenter.exe (PID: 1148)
- FCBrowser.exe (PID: 4000)
- FCLogin.exe (PID: 2456)
- FCBrowser.exe (PID: 3160)
- FCBrowser.exe (PID: 3196)
- FCBrowser.exe (PID: 2856)
- FCBrowser.exe (PID: 3380)
- FCBrowser.exe (PID: 308)
Creates files or folders in the user directory
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
- FlashCenter.exe (PID: 1148)
- FlashCenterSvc.exe (PID: 3716)
- FCLogin.exe (PID: 2456)
- FCBrowser.exe (PID: 4000)
- FCBrowser.exe (PID: 2856)
Reads the machine GUID from the registry
- flashcenter_pp_ax_install_cn.exe (PID: 3804)
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
- FlashHelperService.exe (PID: 4052)
- FlashCenterSvc.exe (PID: 3716)
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
- FlashCenter.exe (PID: 1148)
- FCBrowser.exe (PID: 4000)
- FCLogin.exe (PID: 2456)
- FCBrowser.exe (PID: 2856)
- FCBrowser.exe (PID: 3160)
Checks proxy server information
- flashcenter_pp_ax_install_cn.exe (PID: 3360)
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
- FlashCenter.exe (PID: 1148)
Process checks are UAC notifies on
- 81EE83DD-C986-405F-934C-F0CF41043640 (PID: 1808)
- E4A6A032-1CD2-4F06-BAEB-5DFD671B18D4 (PID: 2472)
Reads Environment values
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
Creates files in the program directory
- 19C84137-C79C-4701-BB04-2F98E894142C (PID: 3512)
Process checks computer location settings
- FCBrowser.exe (PID: 3160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
149
Monitored processes
83
Malicious processes
13
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\FlashCenter\FCBrowser.exe" --type=utility --field-trial-handle=1244,5127478463743438358,4576114472012933838,131072 --enable-features=CastMediaRouteProvider,CookieDeprecationMessages,CrossOriginEmbedderPolicy,CrossOriginOpenerPolicy,DocumentPolicy,FeaturePolicyForClientHints,OriginIsolationHeader,OriginPolicy,UserAgentClientHint --disable-features=OutOfBlinkCors --lang=zh-CN --service-sandbox-type=audio --no-sandbox --enable-experimental-web-platform-features --log-file="C:\Program Files\FlashCenter\debug.log" --log-severity=disable --user-agent="Mozilla/5.0 (Windows NT 7sp1; X86) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/83.0.4103.97 Safari/537.36 FCBrowser/3.0.4.202 Browser/3.0.4.202" --lang=zh-CN --log-file="C:\Program Files\FlashCenter\debug.log" --mojo-platform-channel-handle=2124 /prefetch:8 | C:\Program Files\FlashCenter\FCBrowser.exe | — | FCBrowser.exe | |||||||||||
User: admin Company: Chongqing Zhongcheng Network Technology Co., Ltd Integrity Level: HIGH Description: FCBrowse Exit code: 0 Version: 3.0.4.202 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=988,17066259065432026370,11228819383028660845,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2440 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=988,17066259065432026370,11228819383028660845,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2352 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=988,17066259065432026370,11228819383028660845,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1772 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=988,17066259065432026370,11228819383028660845,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=952 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=988,17066259065432026370,11228819383028660845,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2816 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=988,17066259065432026370,11228819383028660845,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2768 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\FlashCenter\FlashCenter.exe" {\"launchtype\":\"CDMInstall\",\"type\":\"open_weburl\",\"data\":{\"url\":\"https://www.flash.cn/success/rxdm230418153952.html?from=install&_category_id=4&_plan_id=49&_content_id=1140&_material_id=0&tt=1688667601&guid=x\"}} | C:\Program Files\FlashCenter\FlashCenter.exe | flashcenter_pp_ax_install_cn.exe | ||||||||||||
User: admin Company: Chongqing Zhongcheng Network Technology Co., Ltd Integrity Level: HIGH Description: Flash Center Exit code: 0 Version: 3.0.4.202 Modules
| |||||||||||||||
| 1156 | "C:\Users\admin\AppData\Local\Temp\nsz38AF.tmp\ns75F3.tmp" taskkill /F /IM "FlashCenterSa.exe" | C:\Users\admin\AppData\Local\Temp\nsz38AF.tmp\ns75F3.tmp | — | 19C84137-C79C-4701-BB04-2F98E894142C | |||||||||||
User: admin Integrity Level: HIGH Exit code: 128 Modules
| |||||||||||||||
| 1360 | "C:\Users\admin\AppData\Local\Temp\nsz38AF.tmp\ns7661.tmp" taskkill /F /IM "FlashTool.exe" | C:\Users\admin\AppData\Local\Temp\nsz38AF.tmp\ns7661.tmp | — | 19C84137-C79C-4701-BB04-2F98E894142C | |||||||||||
User: admin Integrity Level: HIGH Exit code: 128 Modules
| |||||||||||||||
Total events
52 904
Read events
52 316
Write events
408
Delete events
180
Modification events
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
118
Suspicious files
329
Text files
481
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-64A705CC-AB0.pma | — | |
MD5:— | SHA256:— | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF11e8d6.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 1816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:FB885004616D47B39BA13E3A4D090E43 | SHA256:F1BE5321C6651B9FBC5268ED06609ECA635E3767144B60300A230E8ABDB4462F | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF11e8f6.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2ffb1a38-9359-43b4-9a5b-ca91c9fb90d2.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
195
DNS requests
94
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
852 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/eua6zlfhpj3roq46nymxtbz4zq_2022.10.19.1145/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.10.19.1145_all_ac7cecrzrmfngskhgmtk6zmhfjoa.crx3 | US | — | — | whitelisted |
3604 | iexplore.exe | GET | — | 8.253.207.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2b93a530c105d1fc | US | — | — | whitelisted |
2976 | iexplore.exe | GET | 200 | 8.253.207.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f76cced43a7fe2b9 | US | compressed | 4.70 Kb | whitelisted |
2976 | iexplore.exe | GET | 200 | 8.253.207.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?29e53430279f2afe | US | compressed | 4.70 Kb | whitelisted |
2976 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | binary | 1.47 Kb | whitelisted |
3604 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | US | binary | 1.41 Kb | whitelisted |
2976 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
3604 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | US | der | 1.40 Kb | whitelisted |
3604 | iexplore.exe | GET | 200 | 163.181.56.171:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSmVYFXwi%2FRq9wx3PKhB8lC%2FFYUyAQUkZ9eMRWuEJ%2BtYMH3wcyqSDQvDCYCEA4Vk%2BzdmfUfAQmC1x6TBx0%3D | US | der | 471 b | whitelisted |
1808 | 81EE83DD-C986-405F-934C-F0CF41043640 | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2400 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3604 | iexplore.exe | 116.177.240.70:443 | flash.cn | CHINA UNICOM China169 Backbone | CN | unknown |
3604 | iexplore.exe | 8.248.149.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
2736 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3176 | chrome.exe | 142.250.185.228:443 | www.google.com | GOOGLE | US | whitelisted |
3176 | chrome.exe | 142.250.186.78:443 | clients2.google.com | GOOGLE | US | whitelisted |
3176 | chrome.exe | 142.250.181.237:443 | accounts.google.com | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
flash.cn |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
ocsp.dcocsp.cn |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlFinished(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlError(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlSSLError(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QString::arg: Argument missing: QPushButton{font: 9pt "Microsoft YaHei UI";color:#444444;background-color:#FFFFFF;text-align:left;padding-left:16px;width:128px;height:32px;border: 0px; },
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlFinished(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlError(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | QObject::connect: Cannot connect CUrlEvent::signalUrlSSLError(QString) to (nullptr)::(nullptr)
|
FlashCenter.exe | Could not parse stylesheet of object QPushButton(0x25496b0)
|
FlashCenter.exe | Could not parse stylesheet of object QPushButton(0x2549370)
|
FlashCenter.exe | Could not parse stylesheet of object QPushButton(0x2549350)
|