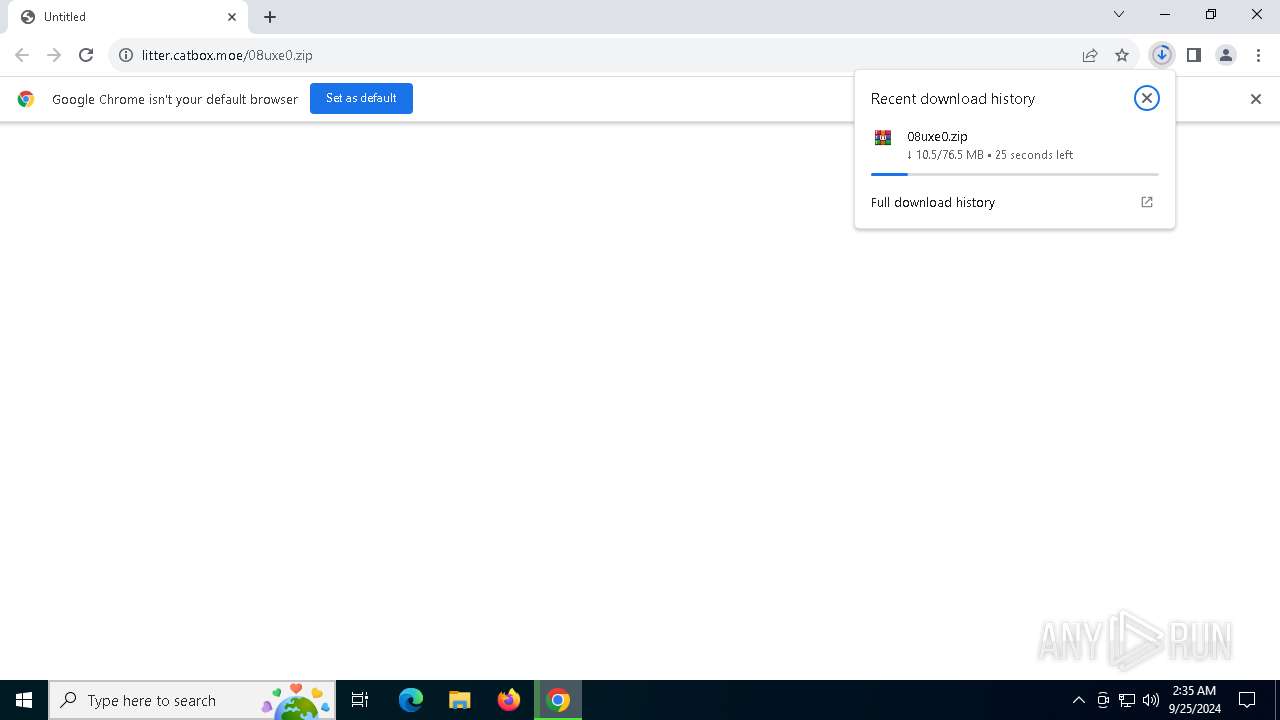
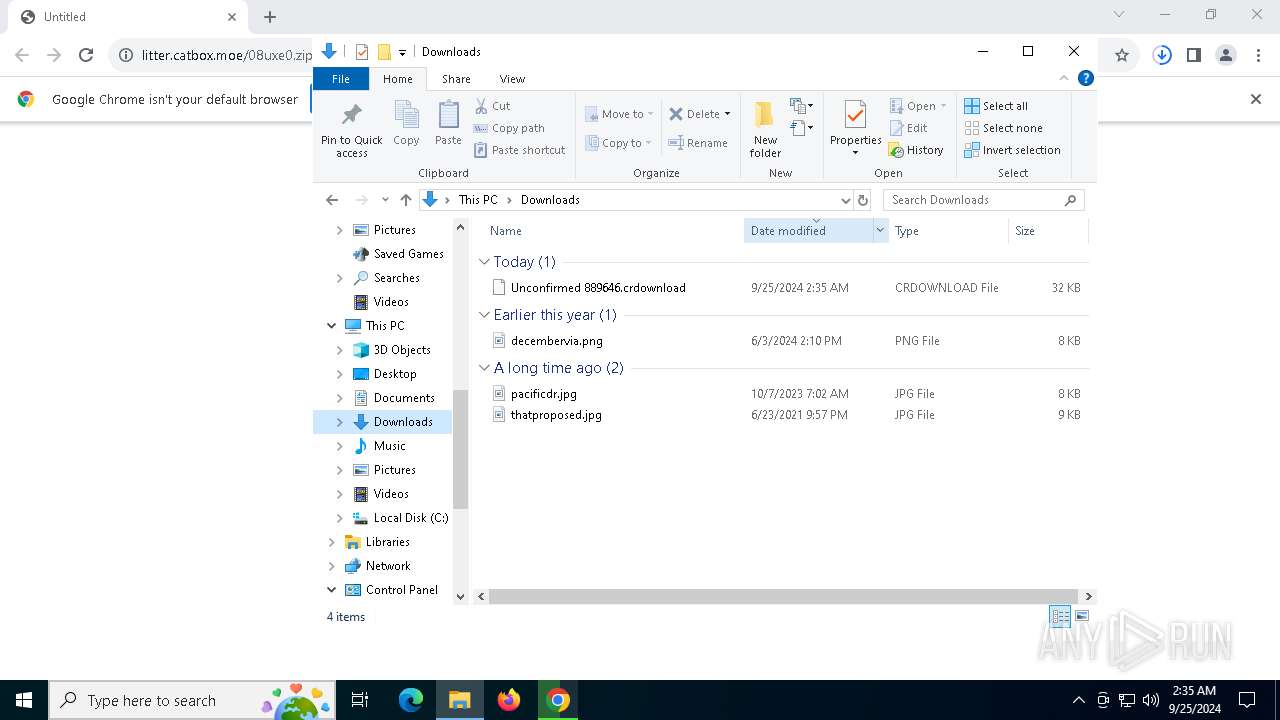
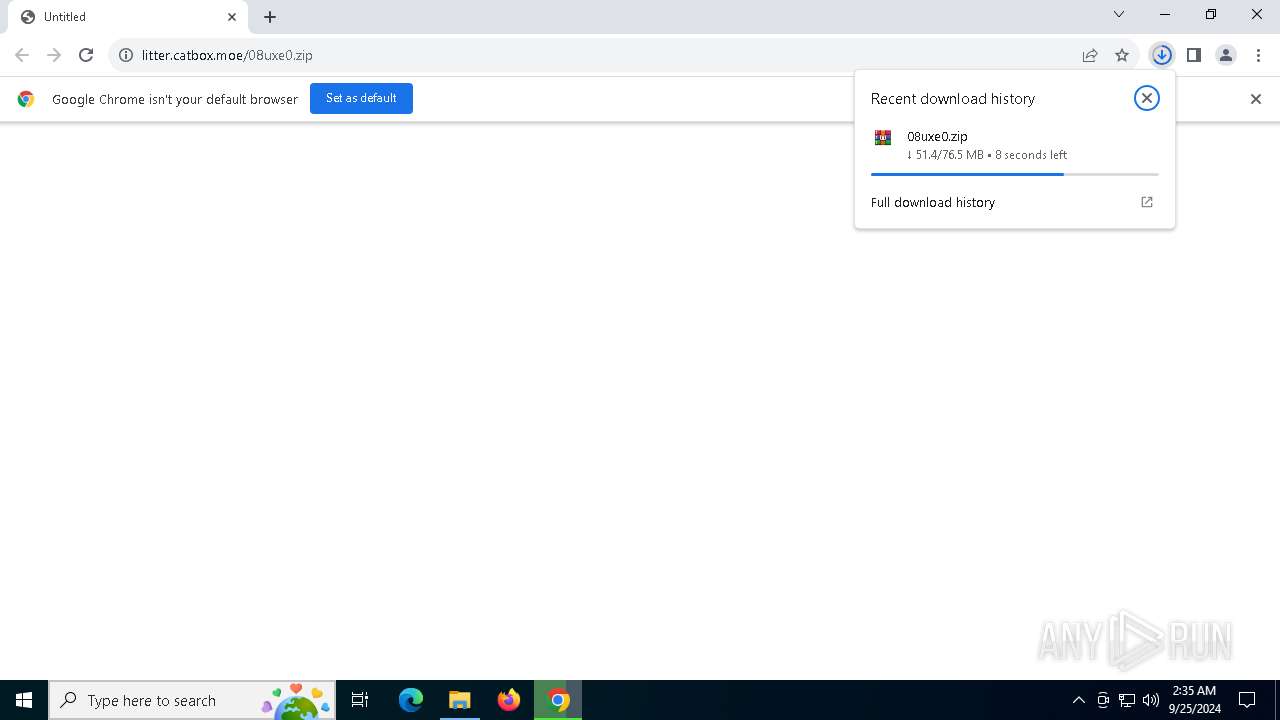
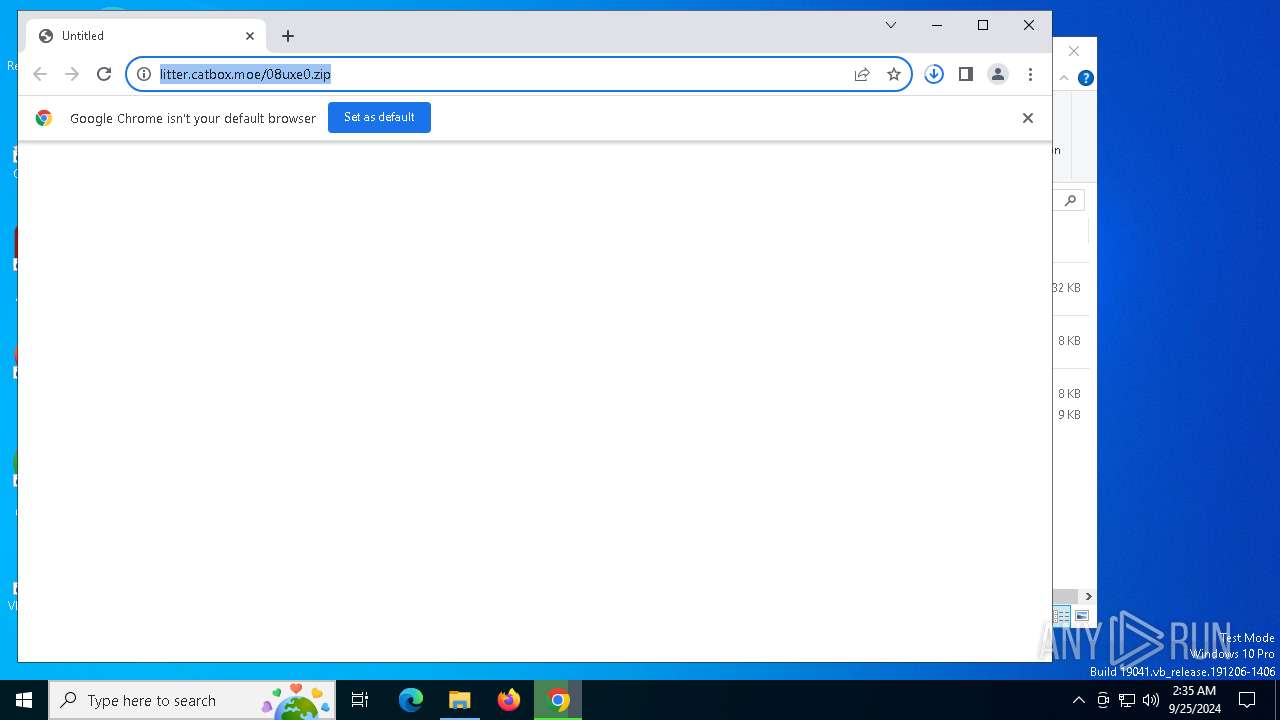
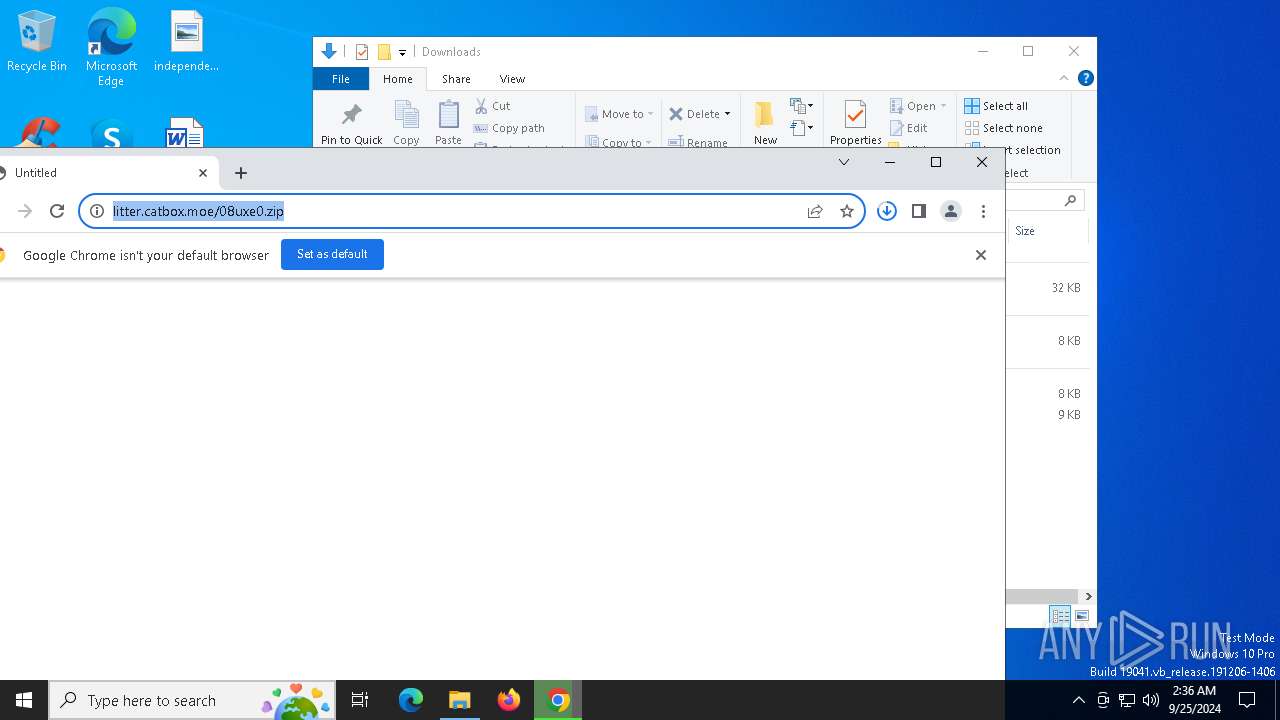
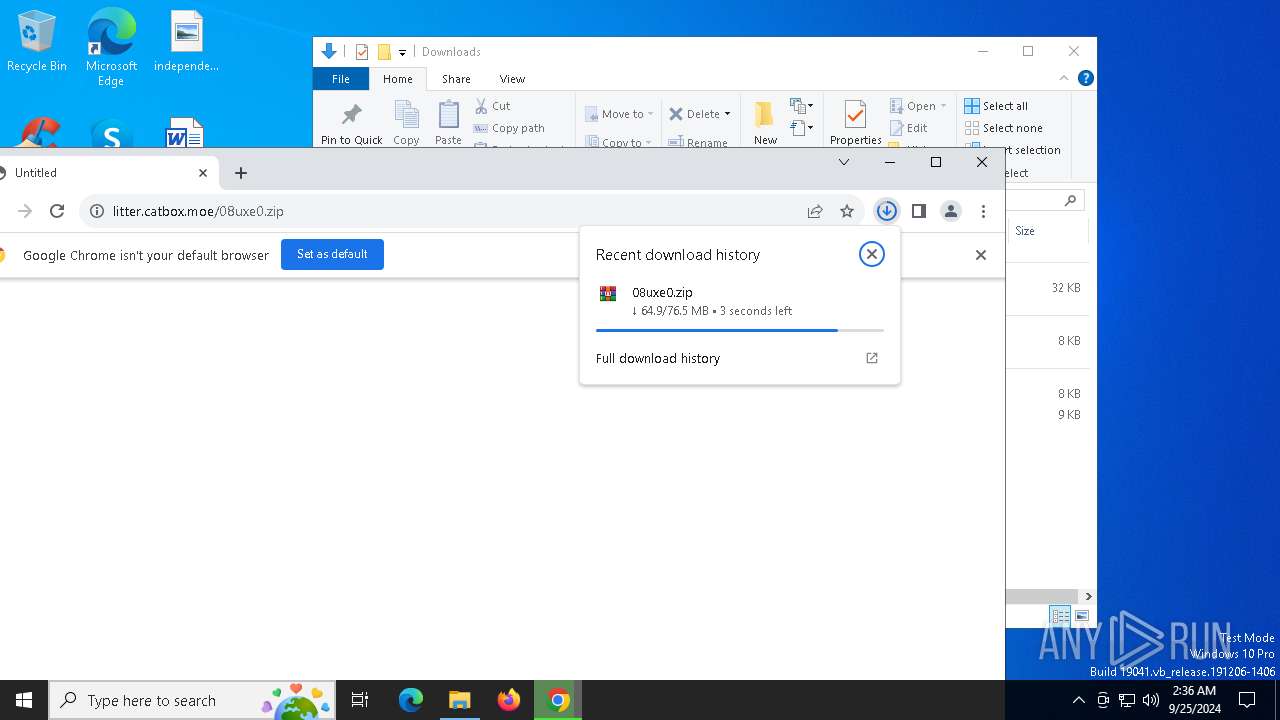
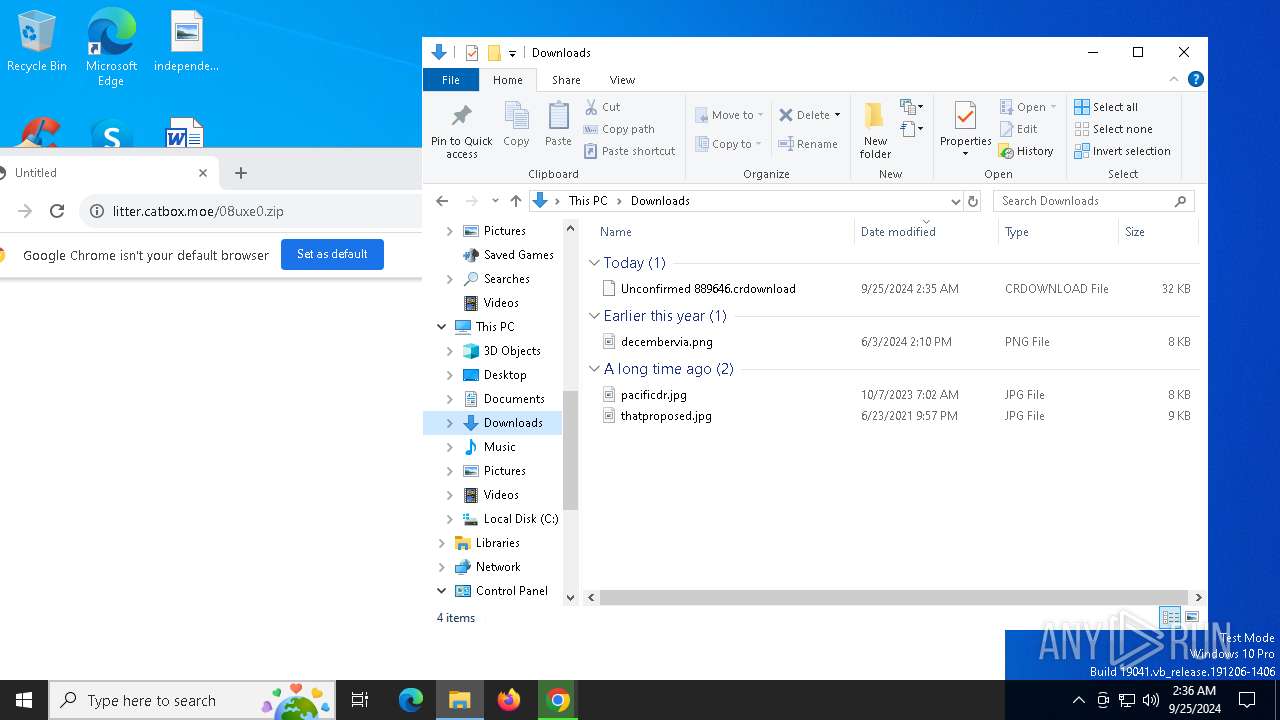
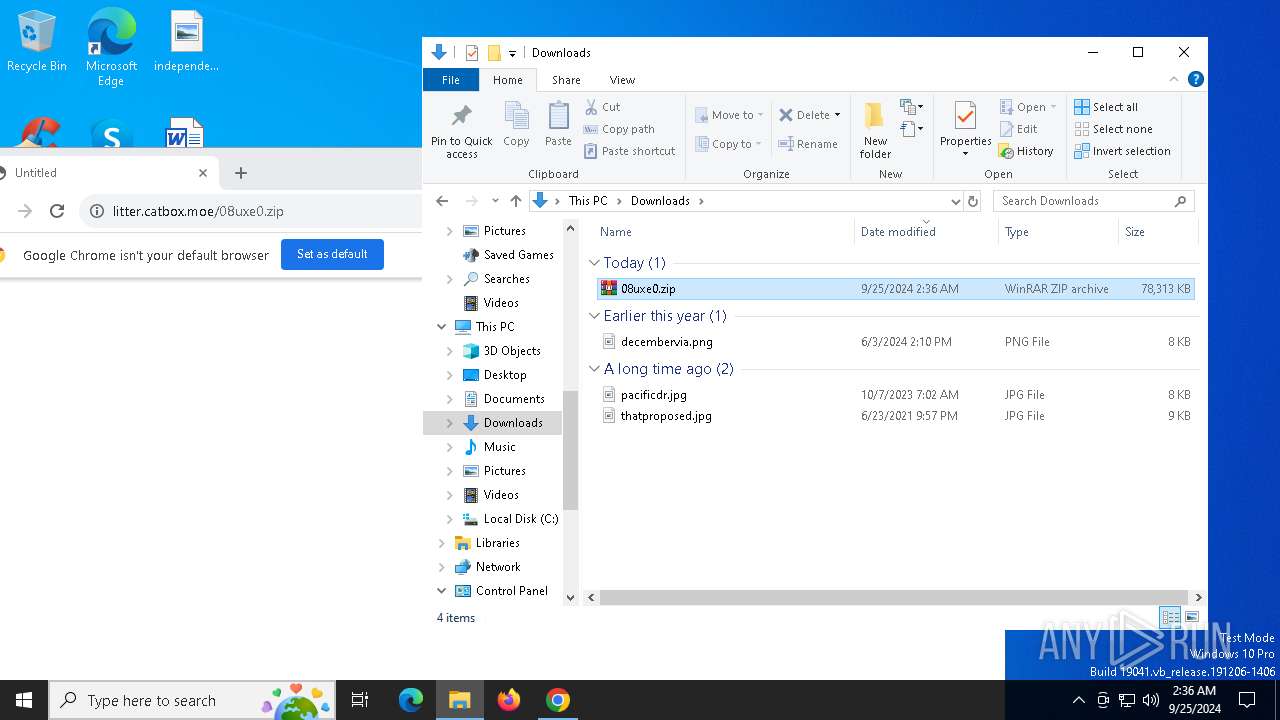
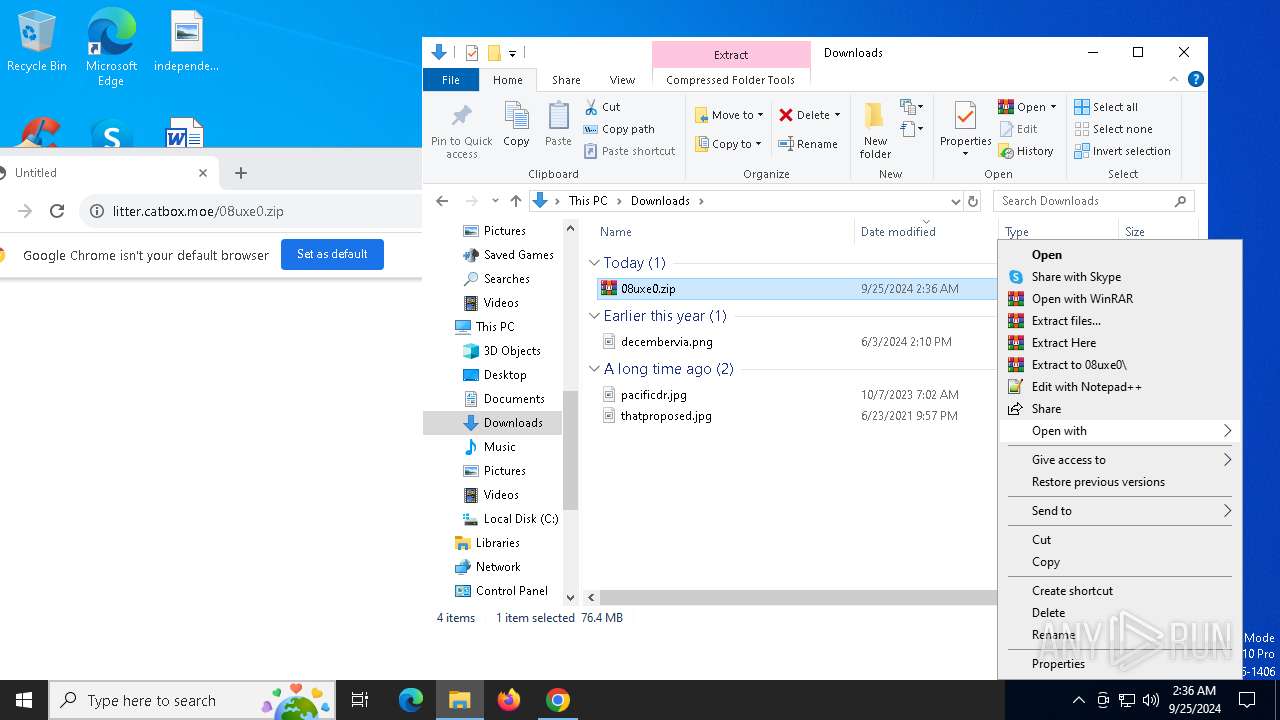
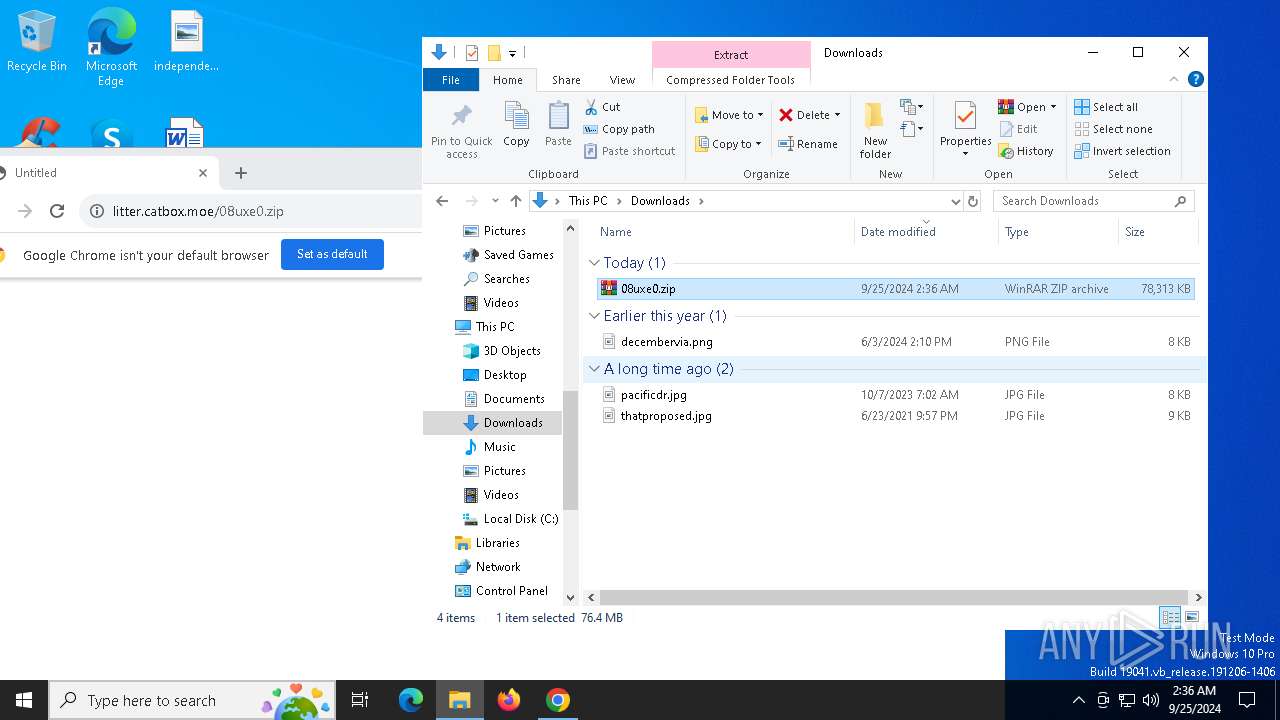
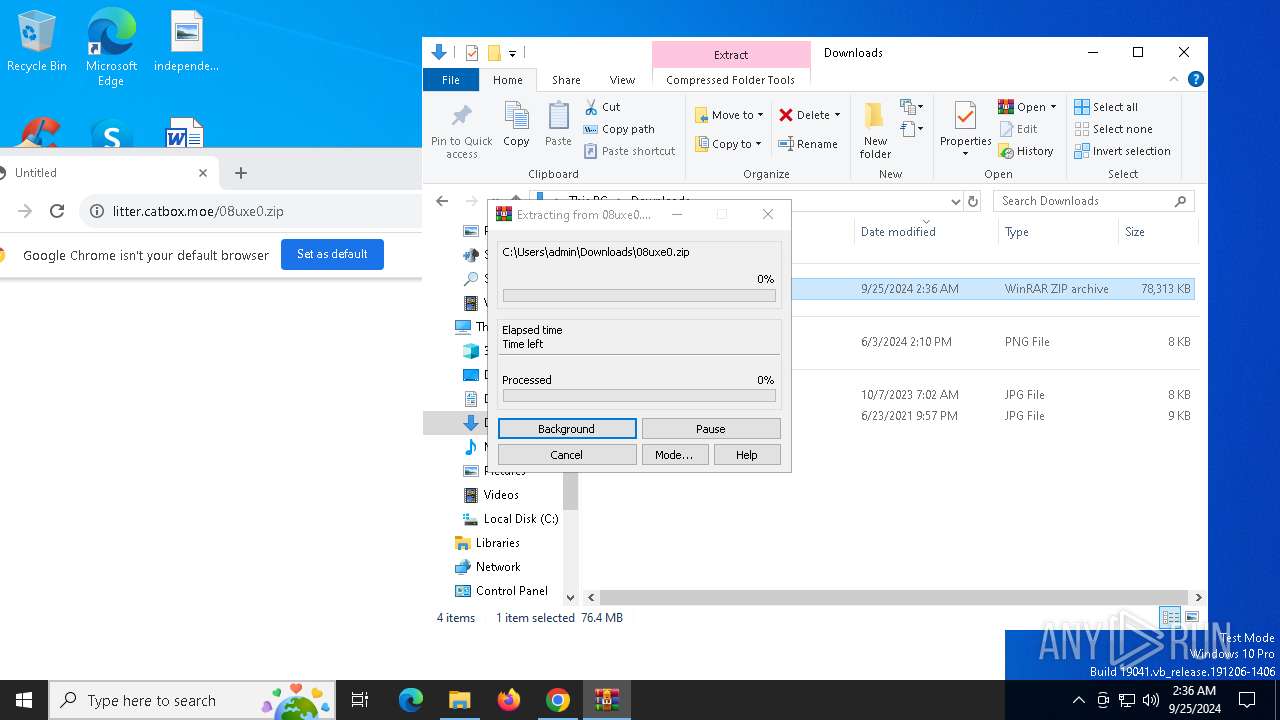
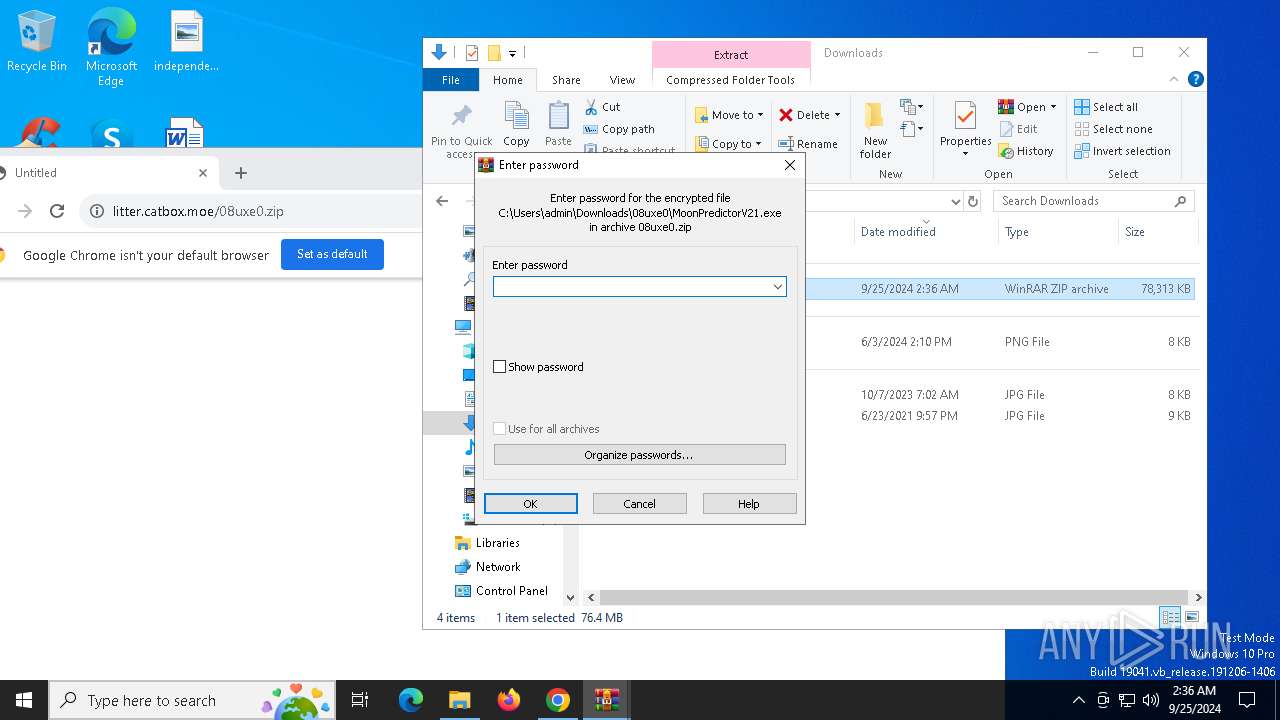
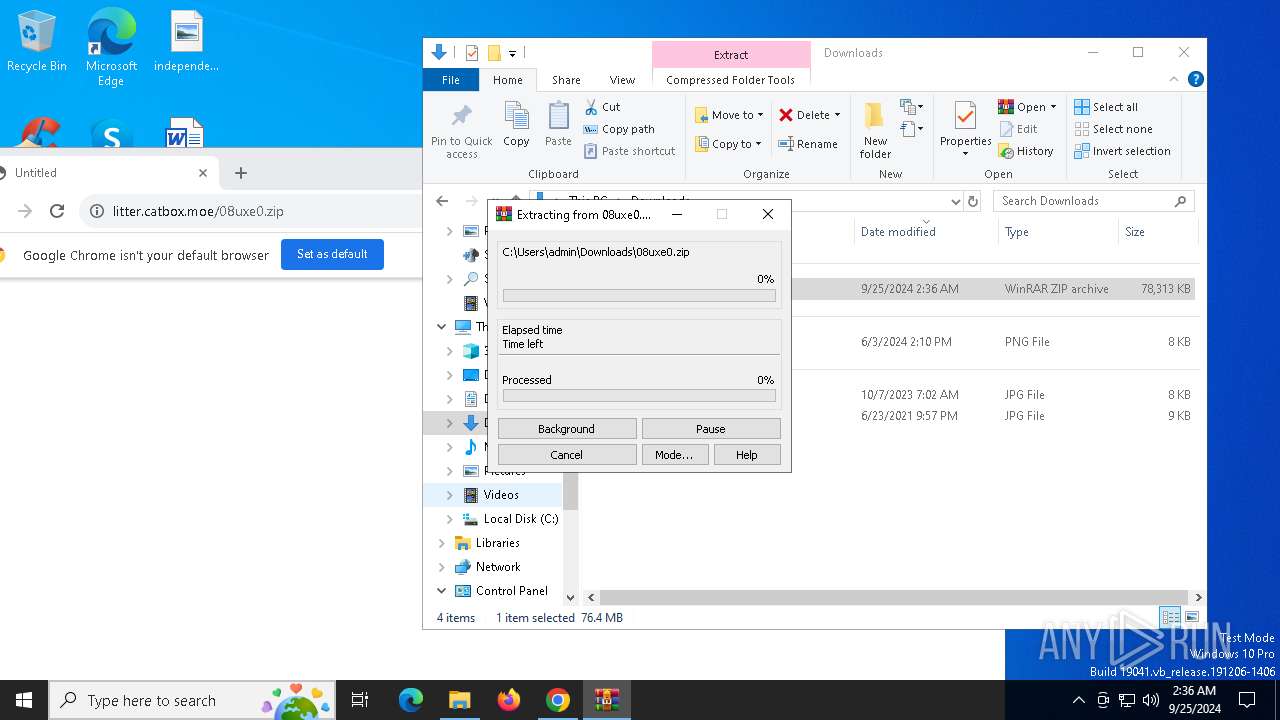
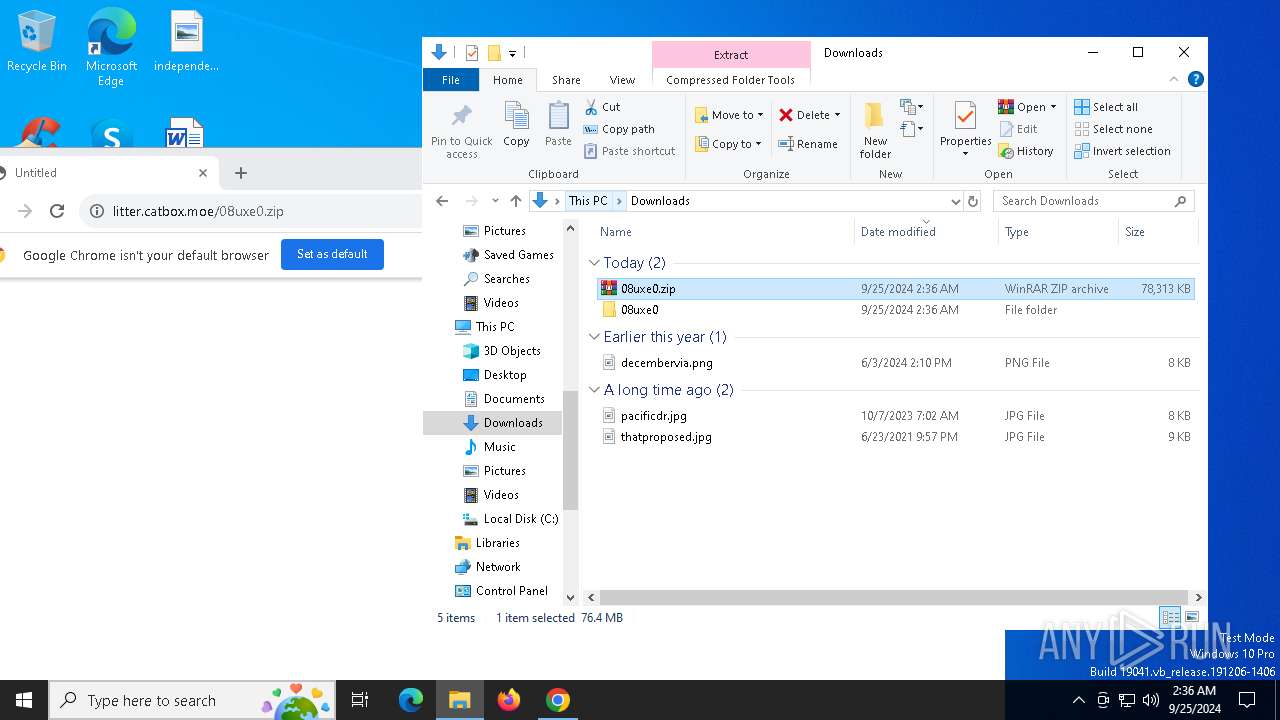
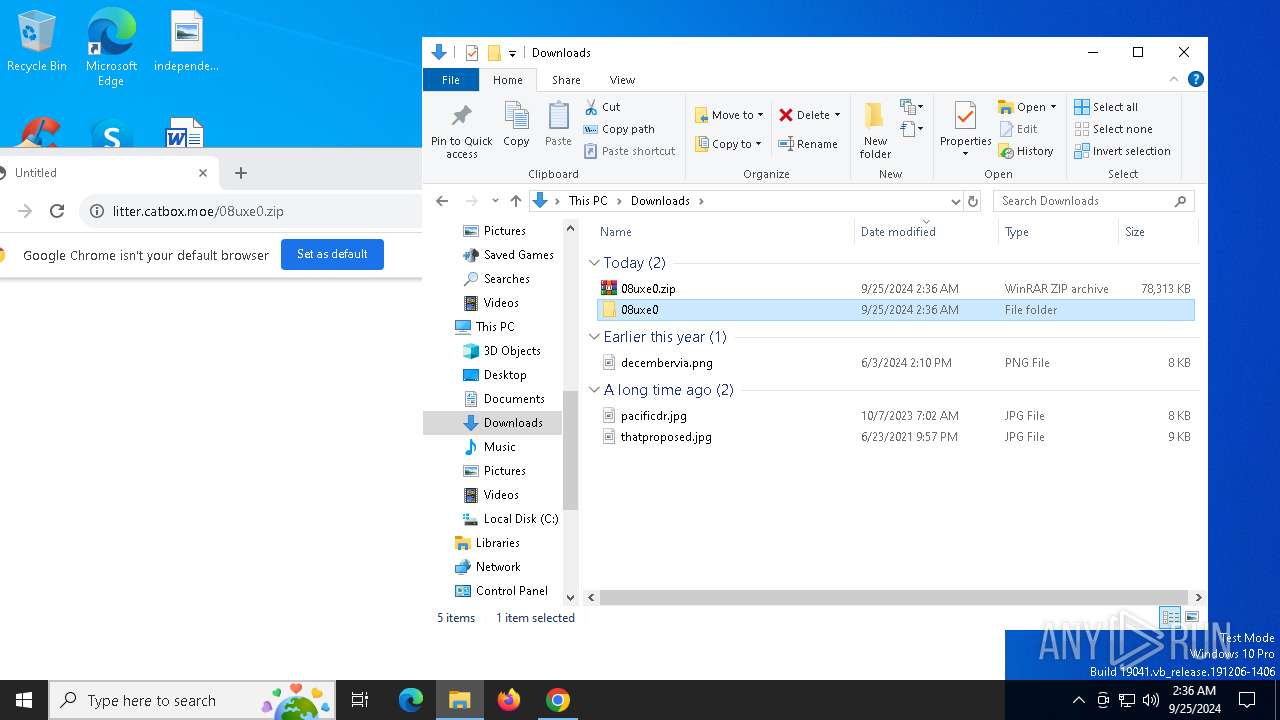
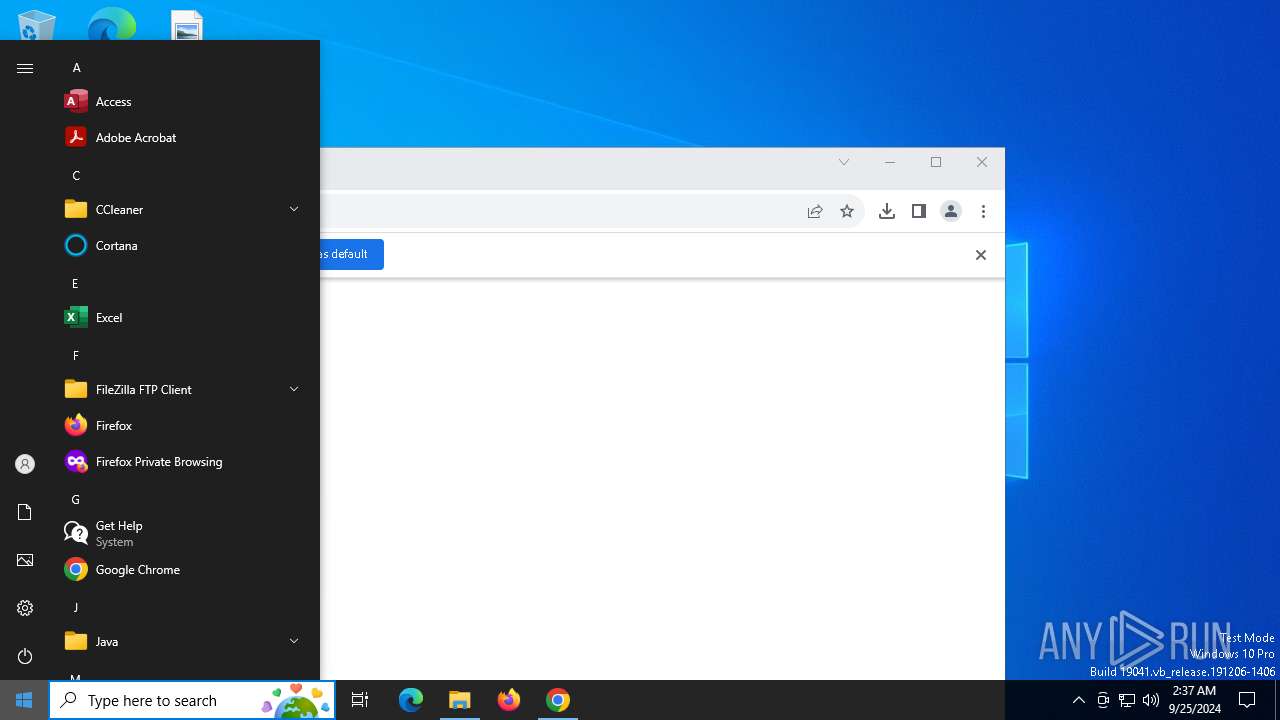
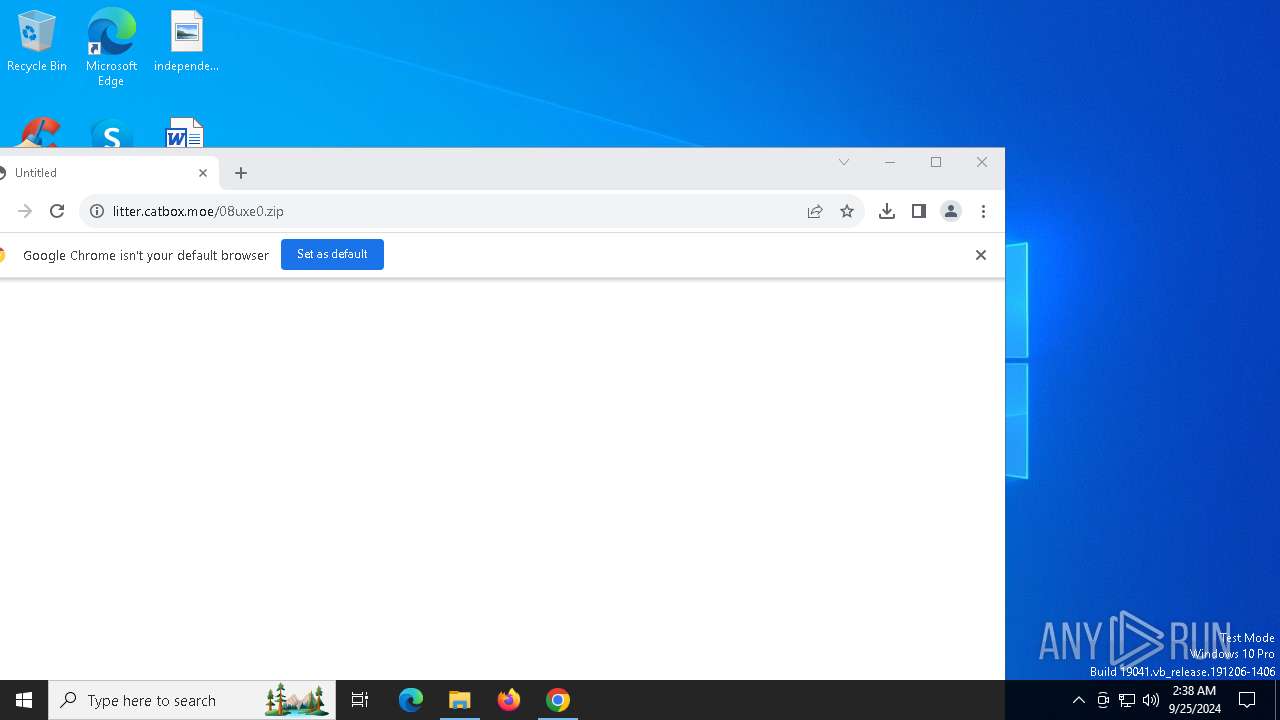
| URL: | https://litter.catbox.moe/08uxe0.zip |
| Full analysis: | https://app.any.run/tasks/917920e7-a3e2-4fa5-bddd-b2eca259e938 |
| Verdict: | Malicious activity |
| Analysis date: | September 25, 2024, 02:35:31 |
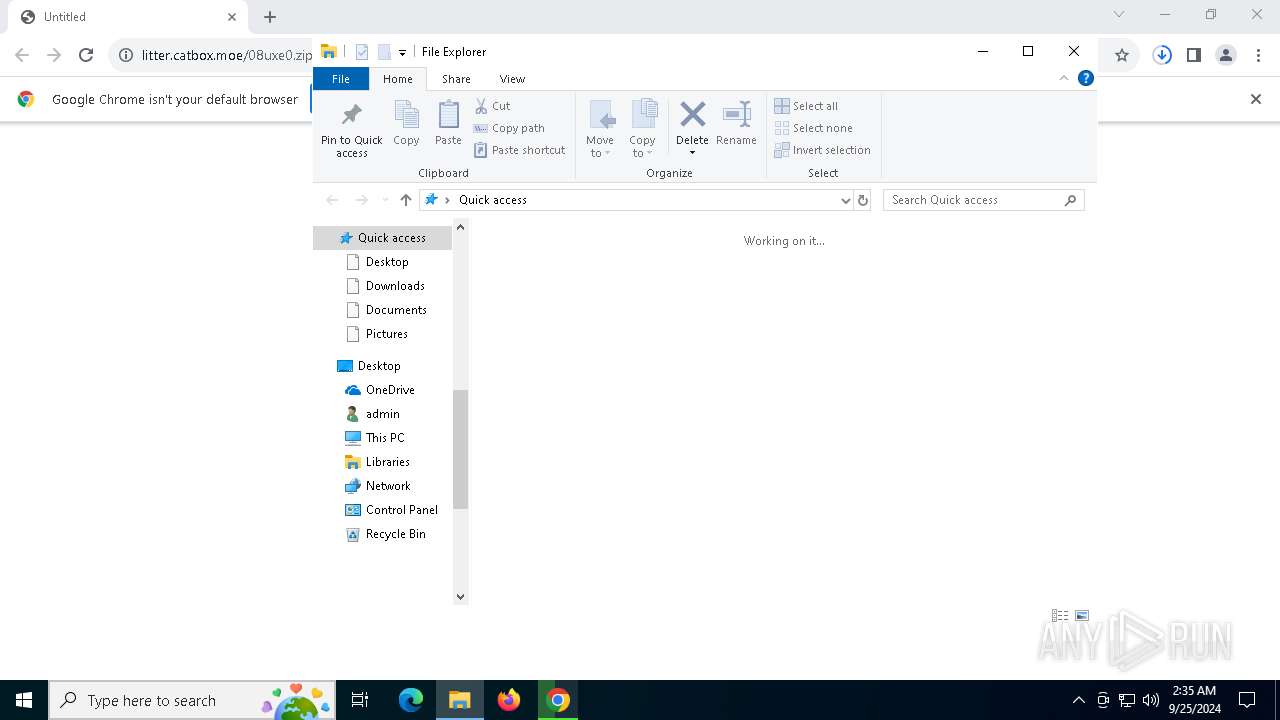
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 562B2448026BED7ACCDF4CCB66DA43BD |
| SHA1: | 666E37771C00A43C8BB8A8D11CED0689FE09079A |
| SHA256: | 4C766639792FB18463E156CF341AB5B749BAB087663346A3D2CC38200CCCCD5E |
| SSDEEP: | 3:N8MRgLdqJ3Nd7fMVn:2MiLWQV |
MALICIOUS
Bypass User Account Control (ComputerDefaults)
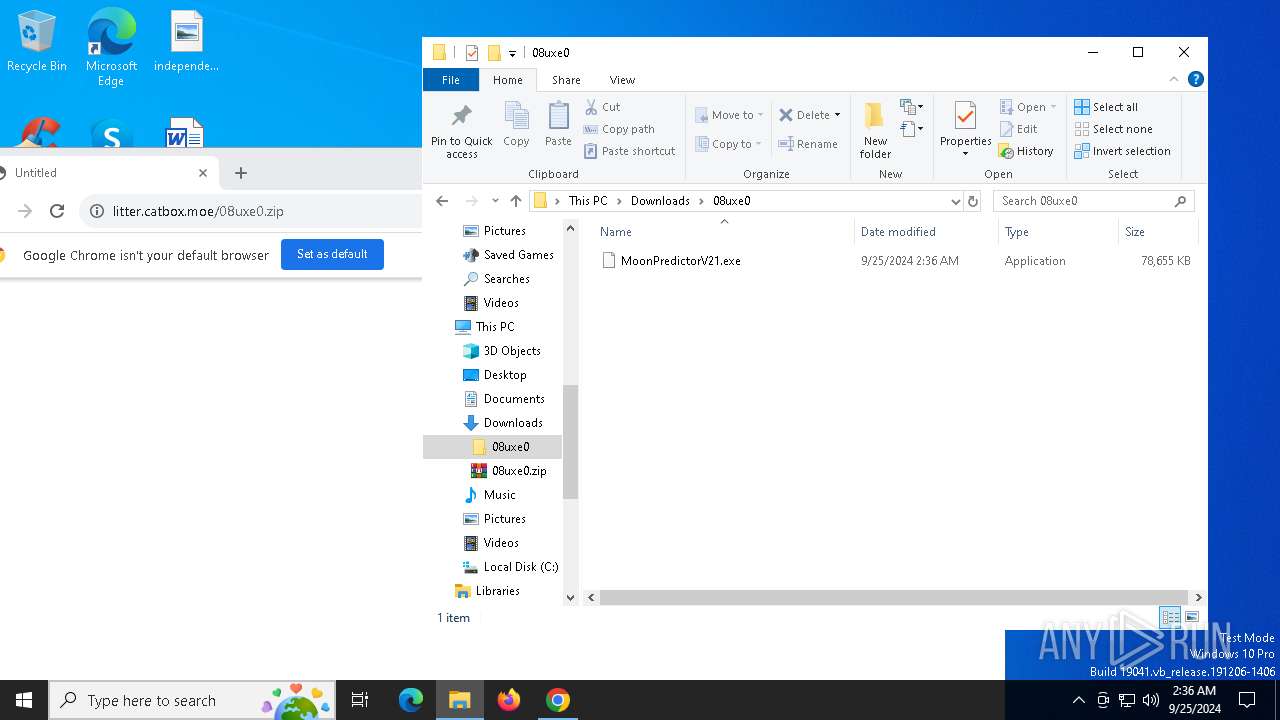
- ComputerDefaults.exe (PID: 6176)
Adds path to the Windows Defender exclusion list
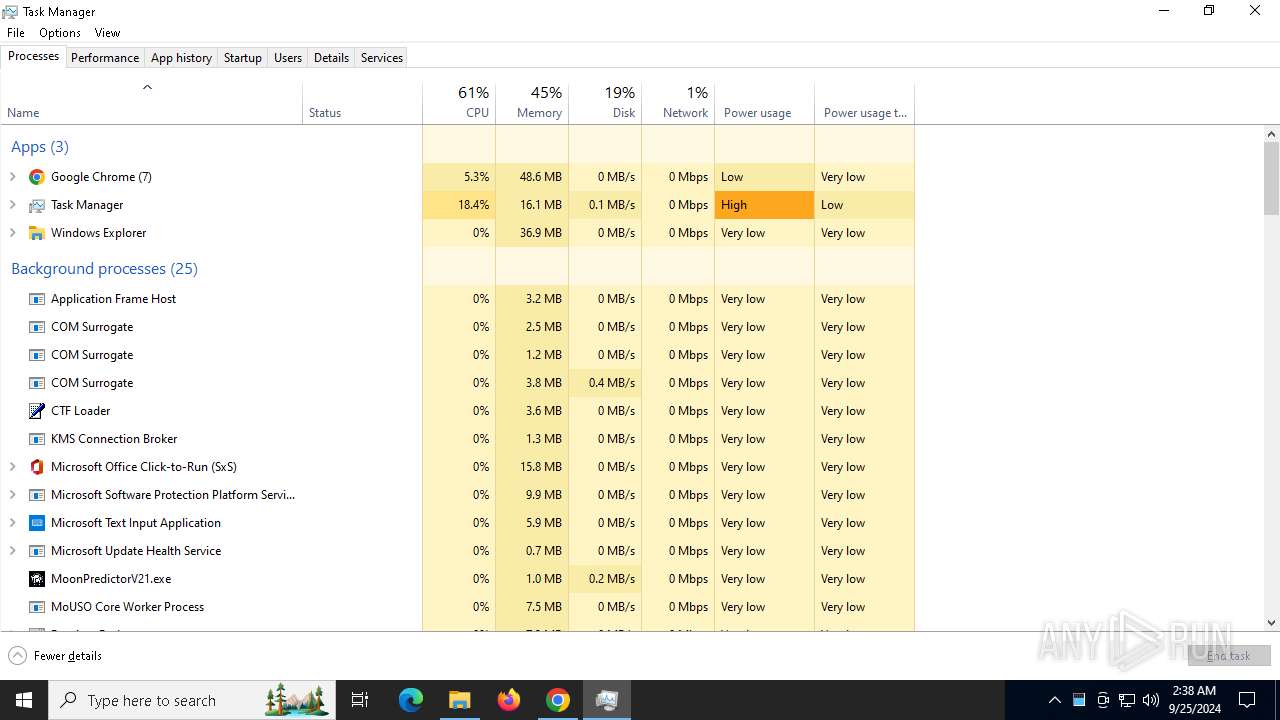
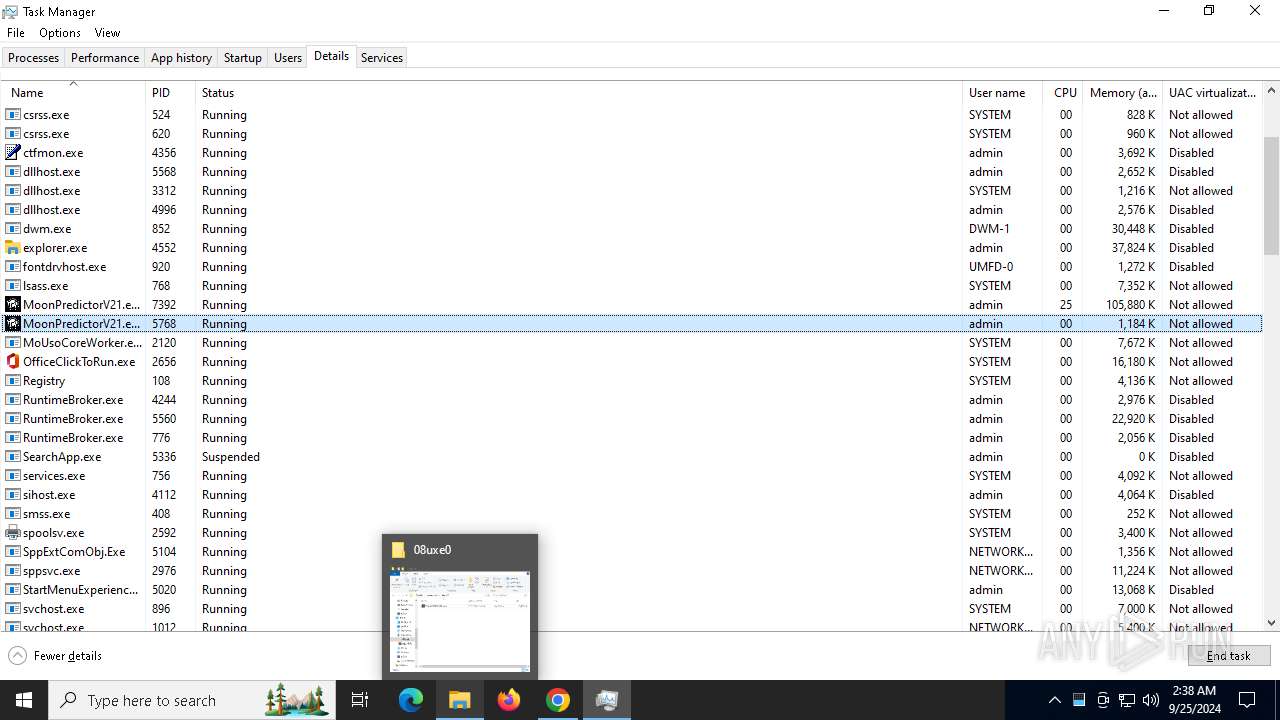
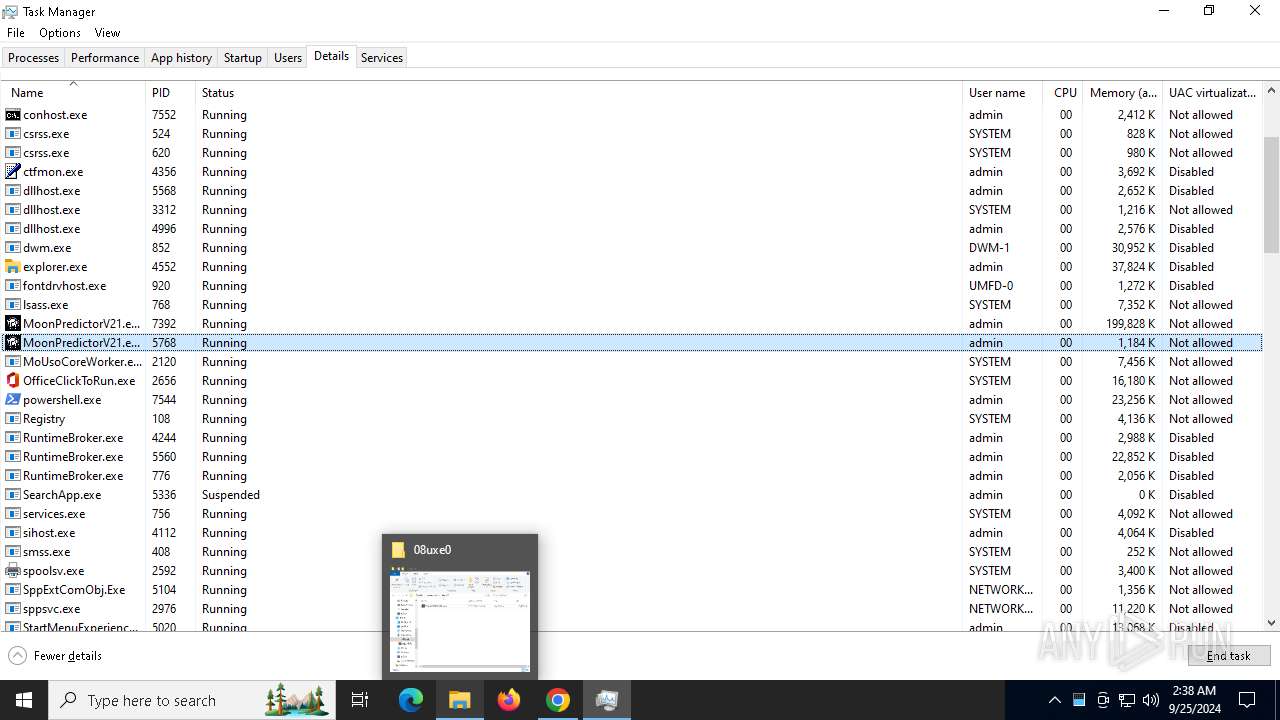
- MoonPredictorV21.exe (PID: 7392)
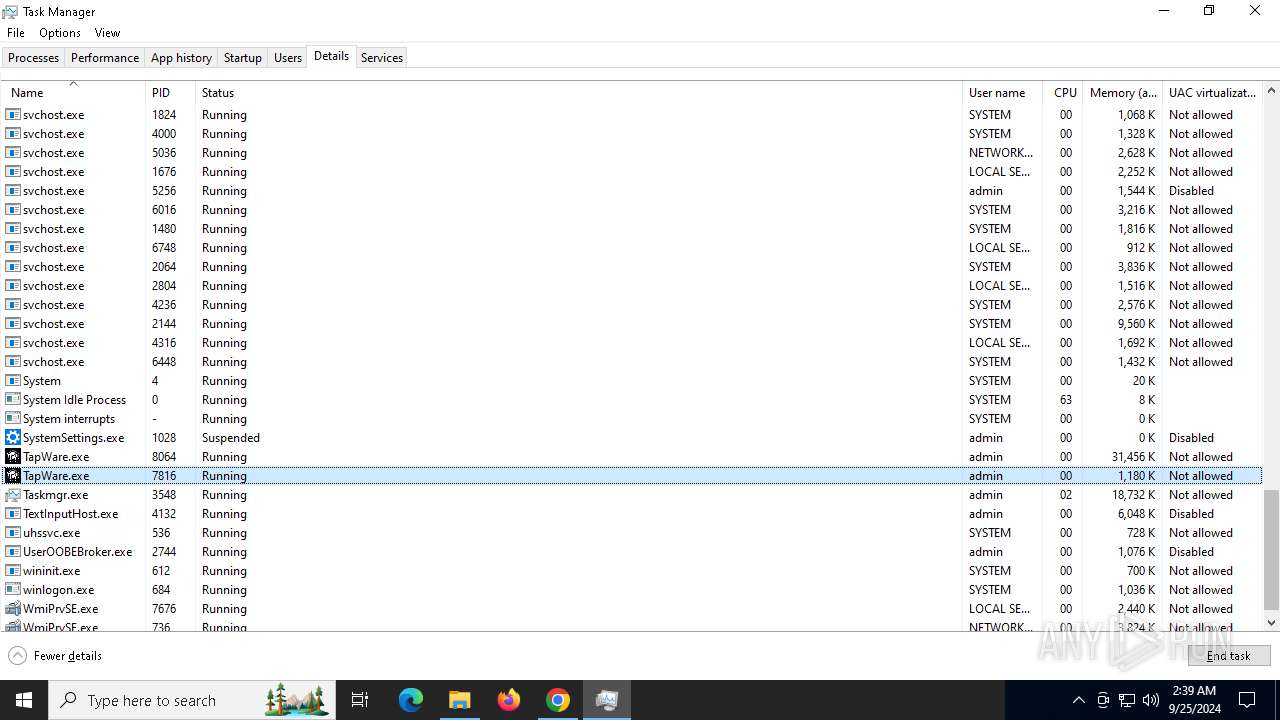
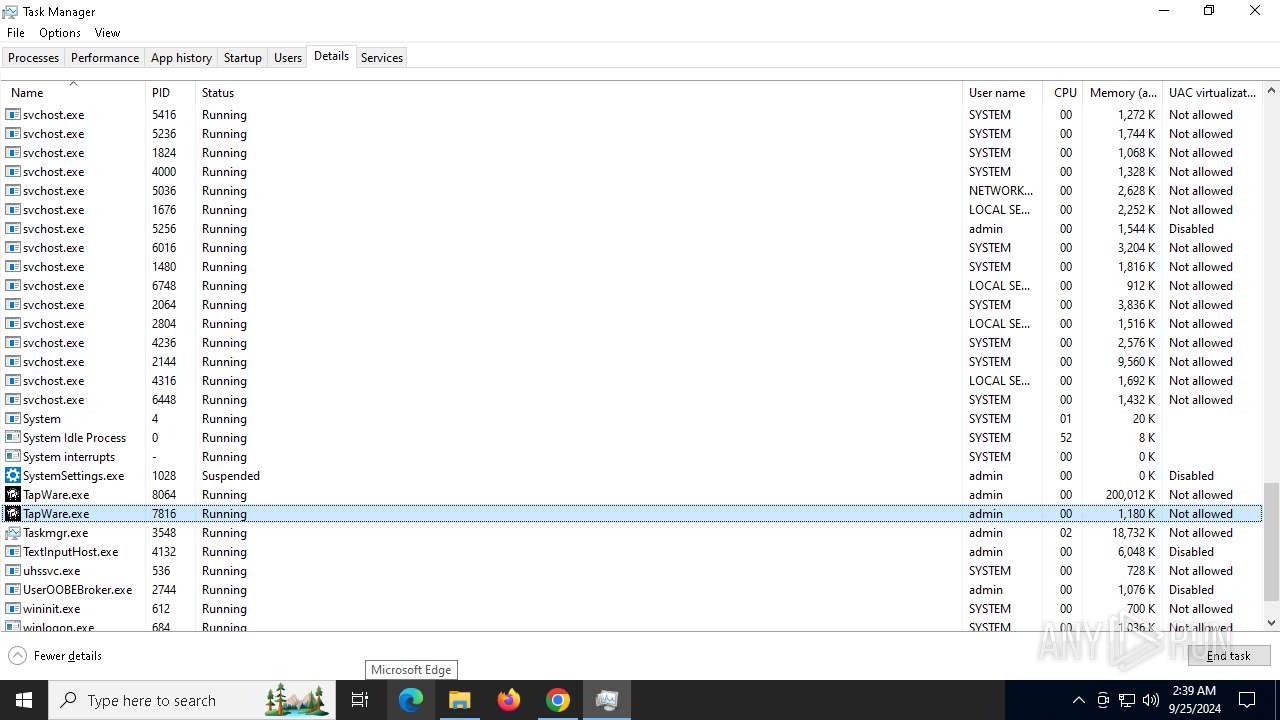
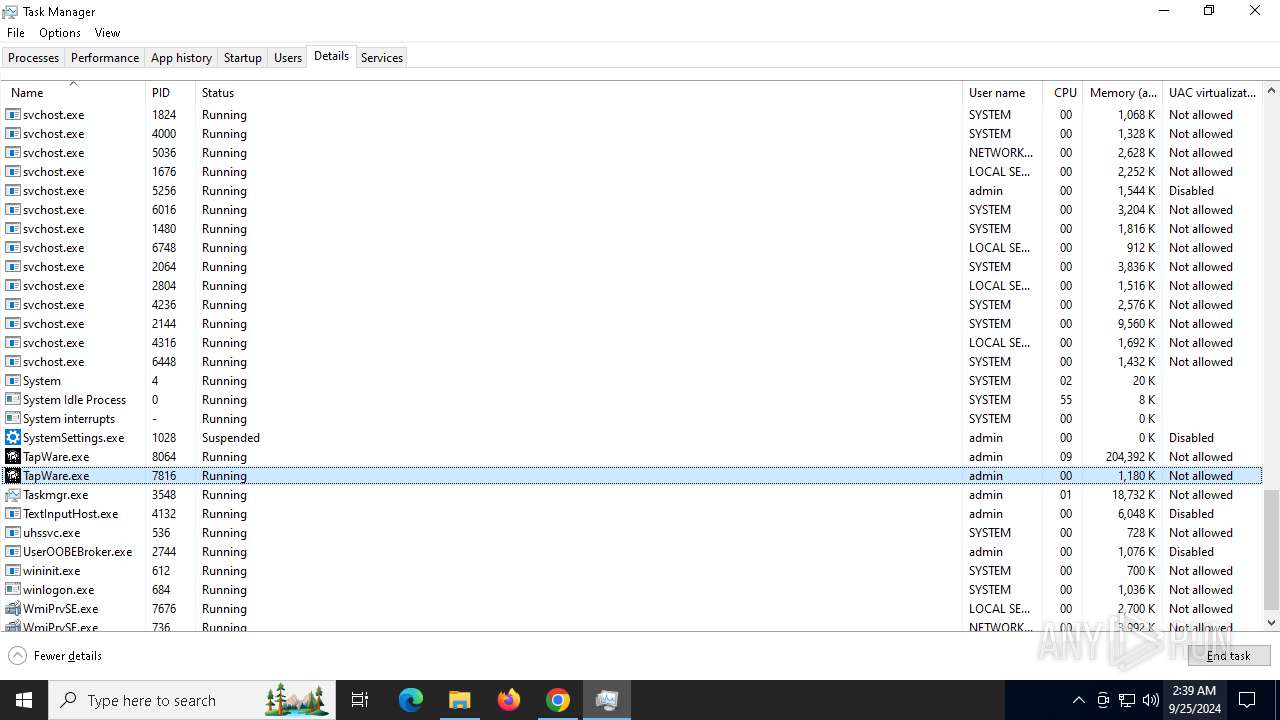
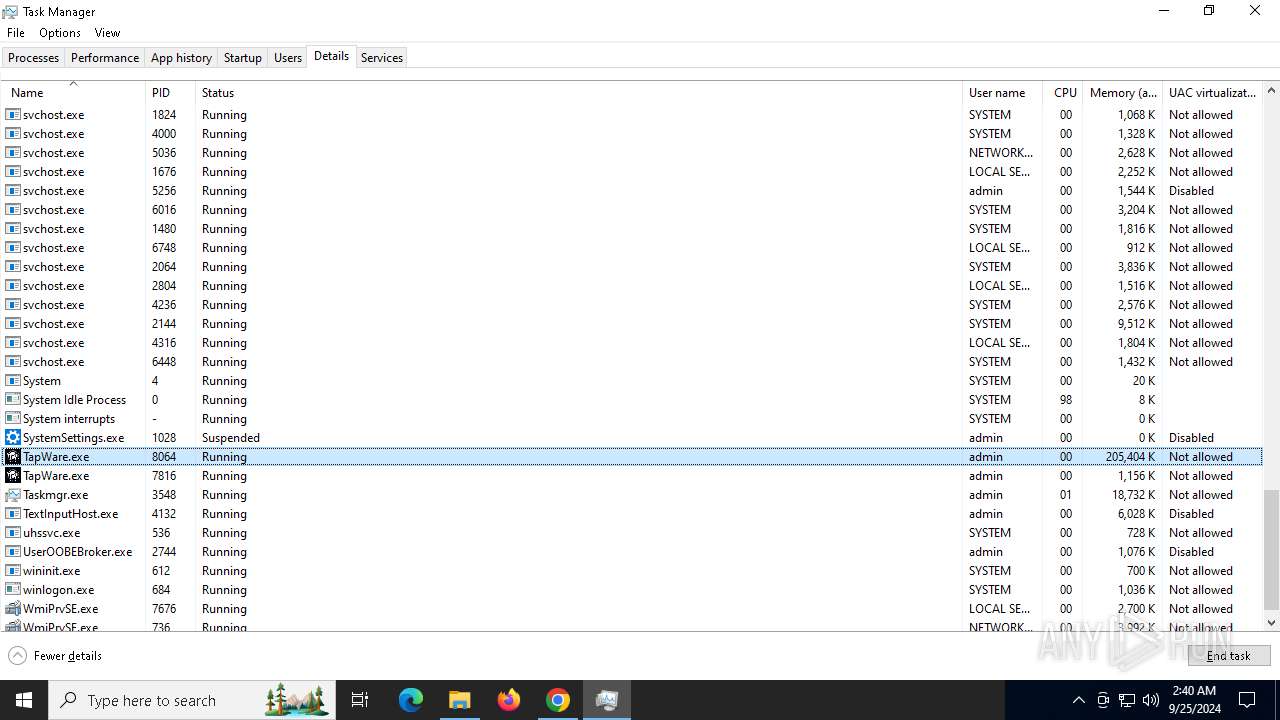
- TapWare.exe (PID: 8064)
SUSPICIOUS
The process drops C-runtime libraries
- MoonPredictorV21.exe (PID: 4784)
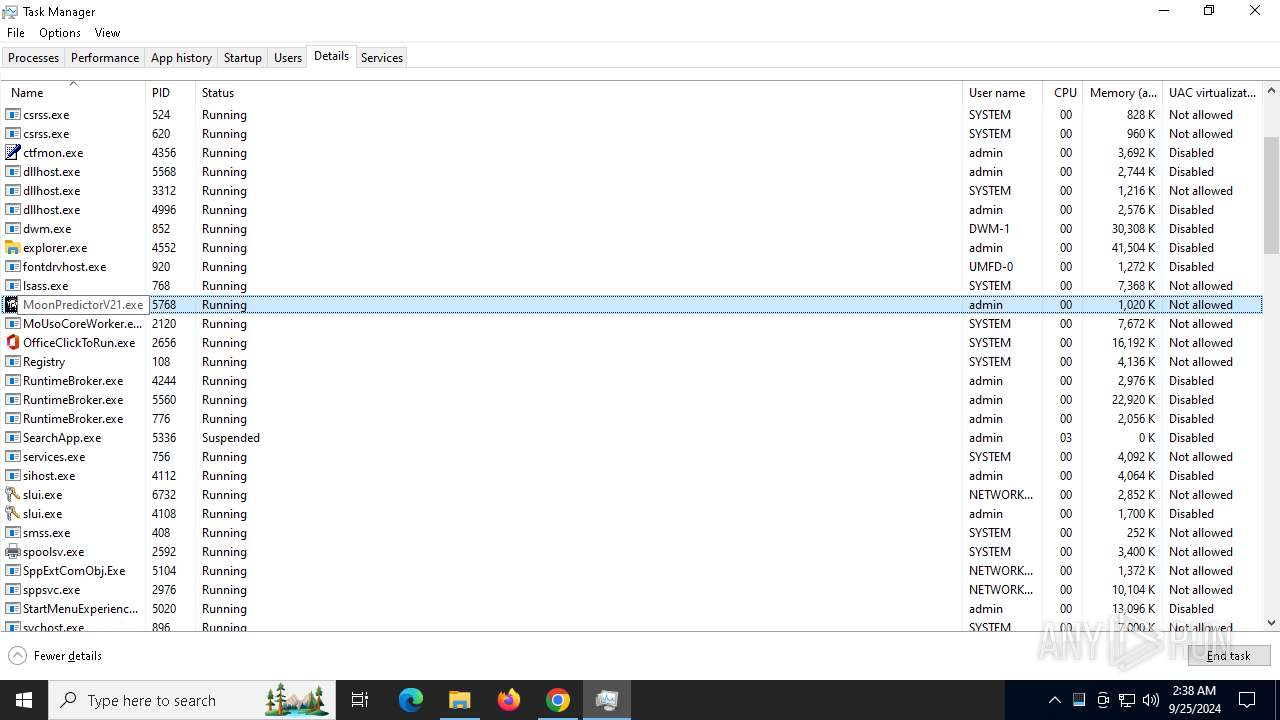
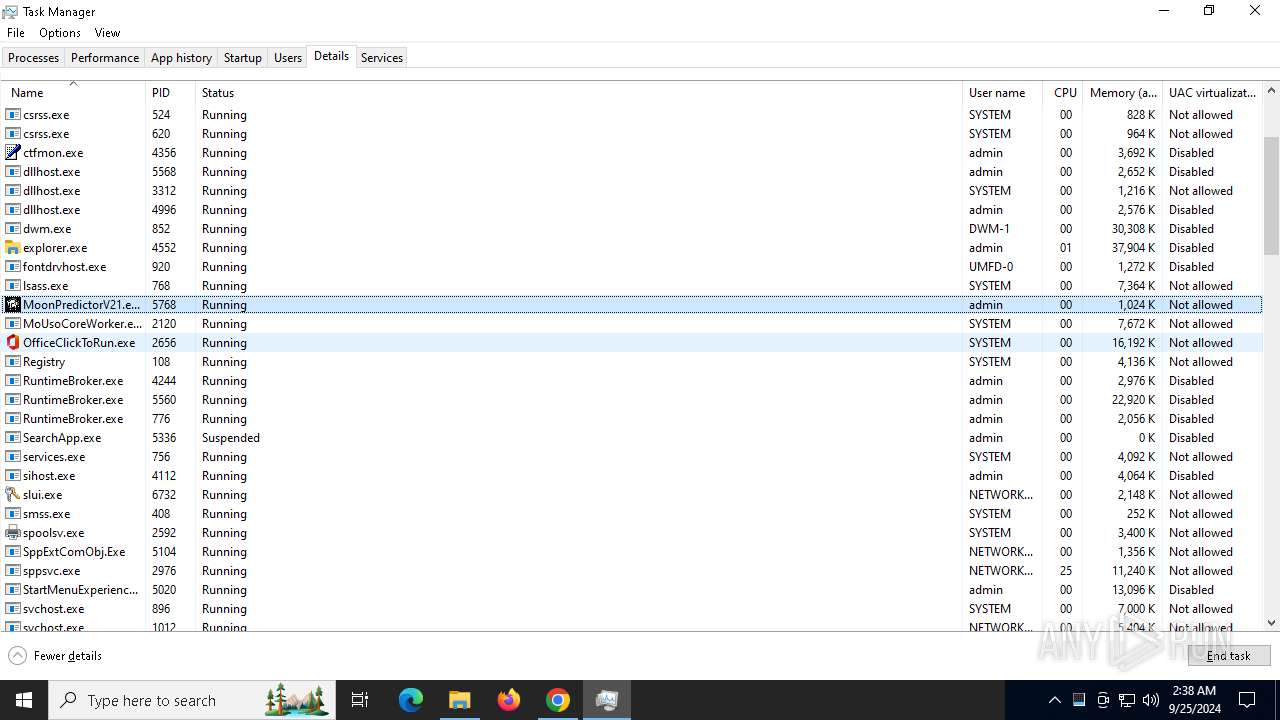
- MoonPredictorV21.exe (PID: 5768)
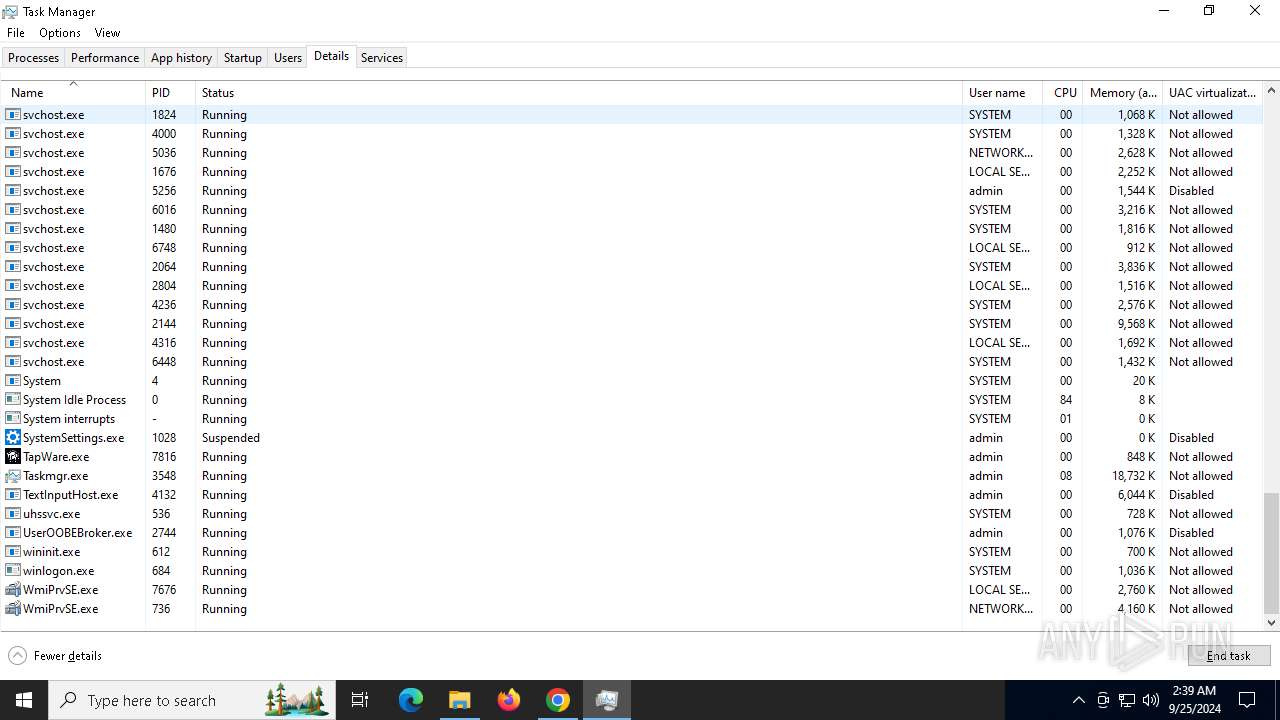
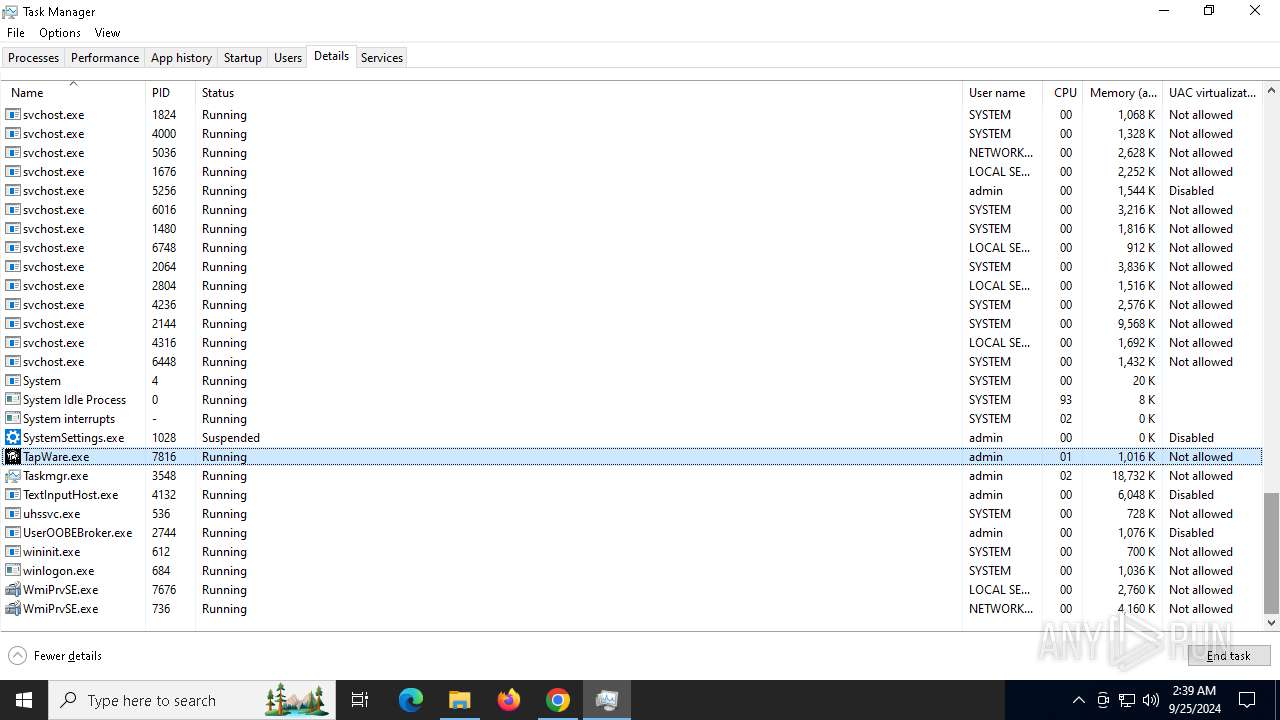
- TapWare.exe (PID: 7816)
Process drops python dynamic module
- MoonPredictorV21.exe (PID: 4784)
- MoonPredictorV21.exe (PID: 5768)
- TapWare.exe (PID: 7816)
Executable content was dropped or overwritten
- MoonPredictorV21.exe (PID: 4784)
- MoonPredictorV21.exe (PID: 5768)
- TapWare.exe (PID: 7816)
Process drops legitimate windows executable
- MoonPredictorV21.exe (PID: 4784)
- MoonPredictorV21.exe (PID: 5768)
- TapWare.exe (PID: 7816)
Starts CMD.EXE for commands execution
- MoonPredictorV21.exe (PID: 904)
- MoonPredictorV21.exe (PID: 7392)
Application launched itself
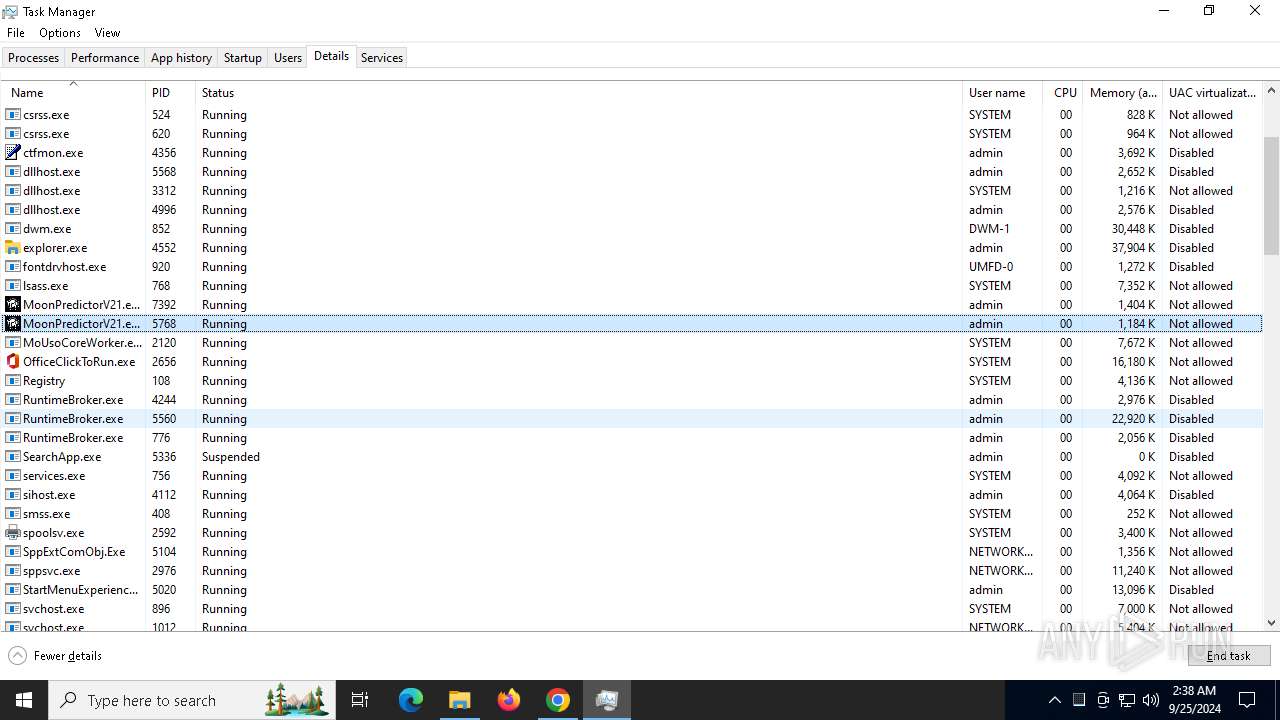
- MoonPredictorV21.exe (PID: 4784)
- MoonPredictorV21.exe (PID: 5768)
- TapWare.exe (PID: 7816)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1804)
- cmd.exe (PID: 1360)
- cmd.exe (PID: 740)
Uses WEVTUTIL.EXE to query events from a log or log file
- cmd.exe (PID: 2520)
- cmd.exe (PID: 304)
Found strings related to reading or modifying Windows Defender settings
- MoonPredictorV21.exe (PID: 904)
Script adds exclusion path to Windows Defender
- MoonPredictorV21.exe (PID: 7392)
- TapWare.exe (PID: 8064)
Starts POWERSHELL.EXE for commands execution
- MoonPredictorV21.exe (PID: 7392)
- TapWare.exe (PID: 8064)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 7736)
Executing commands from a ".bat" file
- MoonPredictorV21.exe (PID: 7392)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7736)
The executable file from the user directory is run by the CMD process
- TapWare.exe (PID: 7816)
There is functionality for taking screenshot (YARA)
- TapWare.exe (PID: 8064)
Found regular expressions for crypto-addresses (YARA)
- TapWare.exe (PID: 8064)
INFO
The process uses the downloaded file
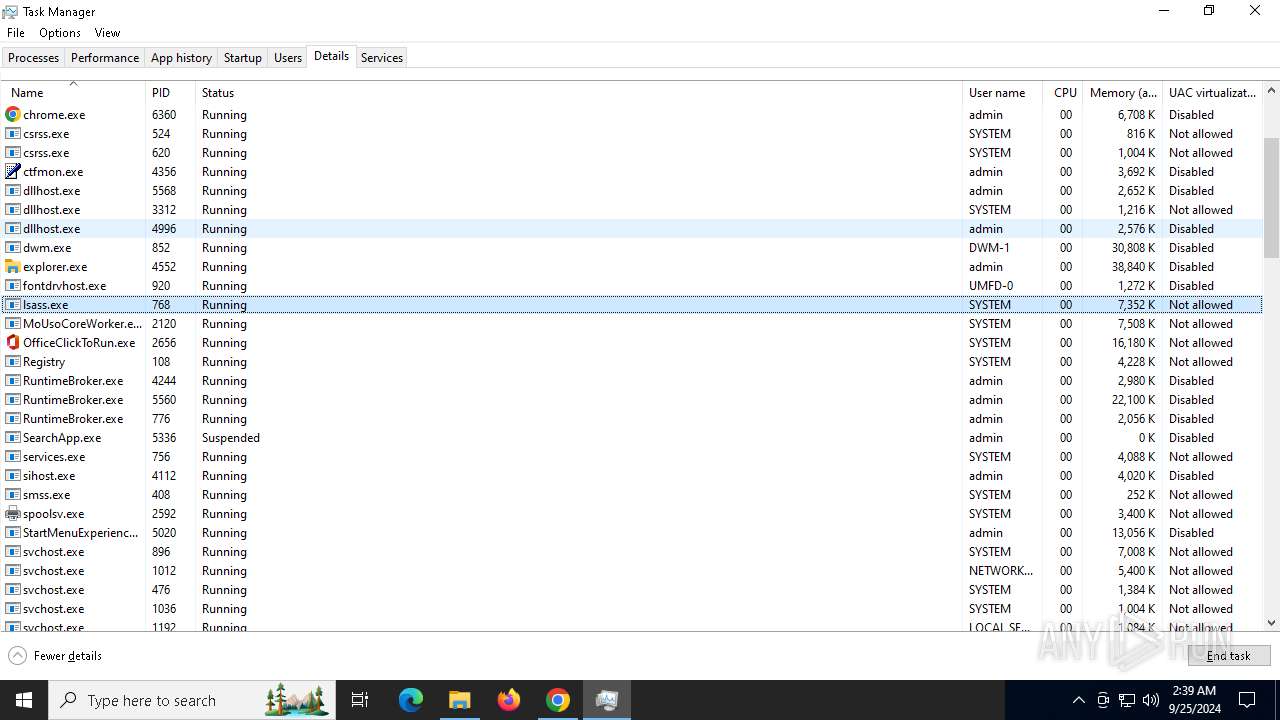
- chrome.exe (PID: 2268)
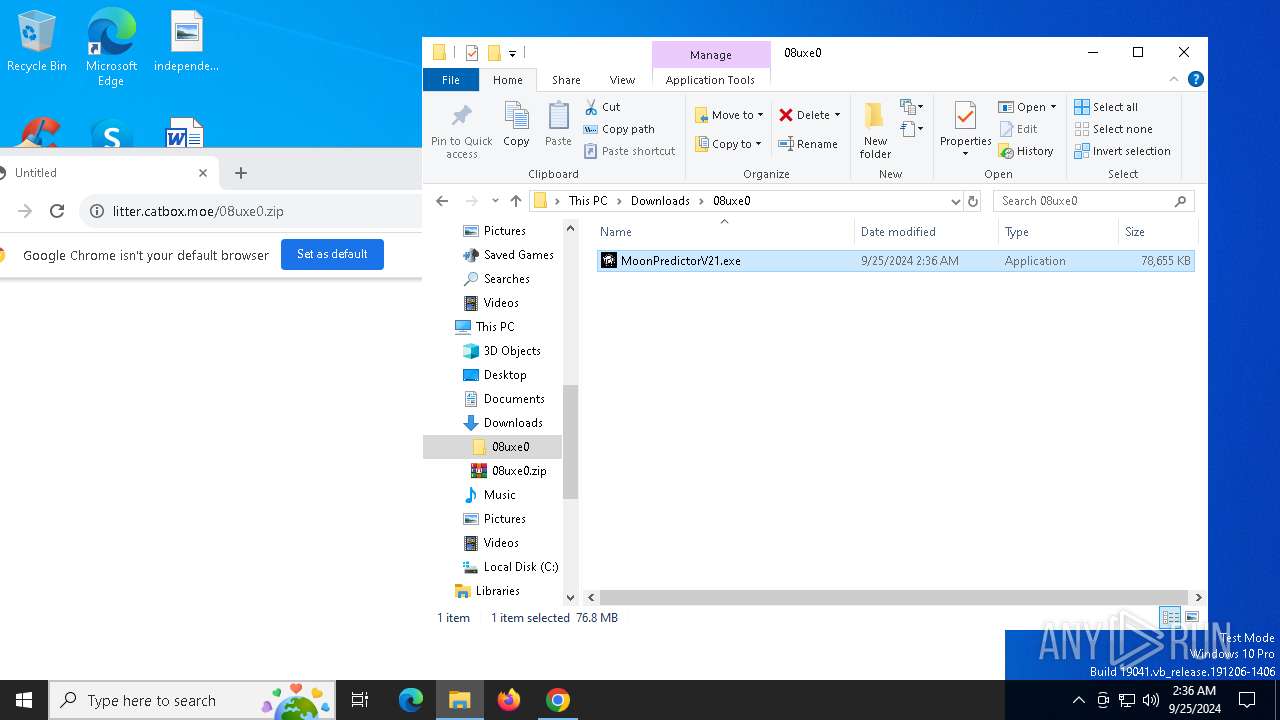
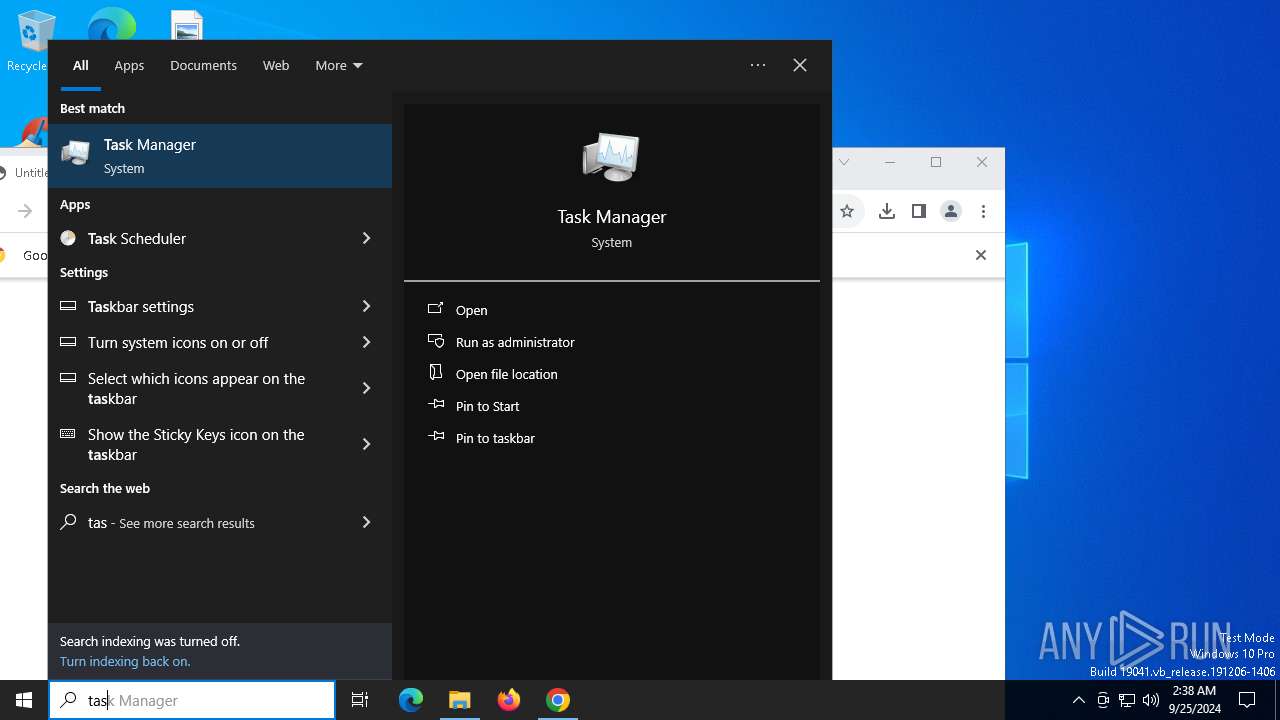
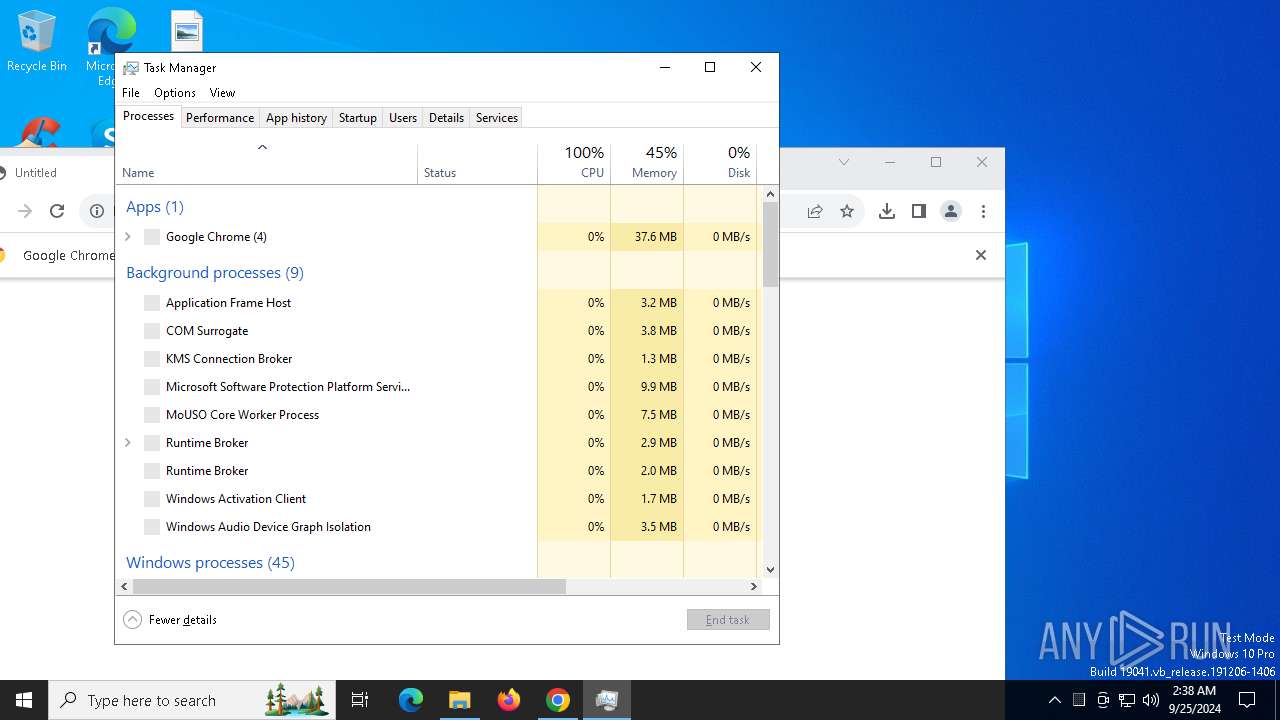
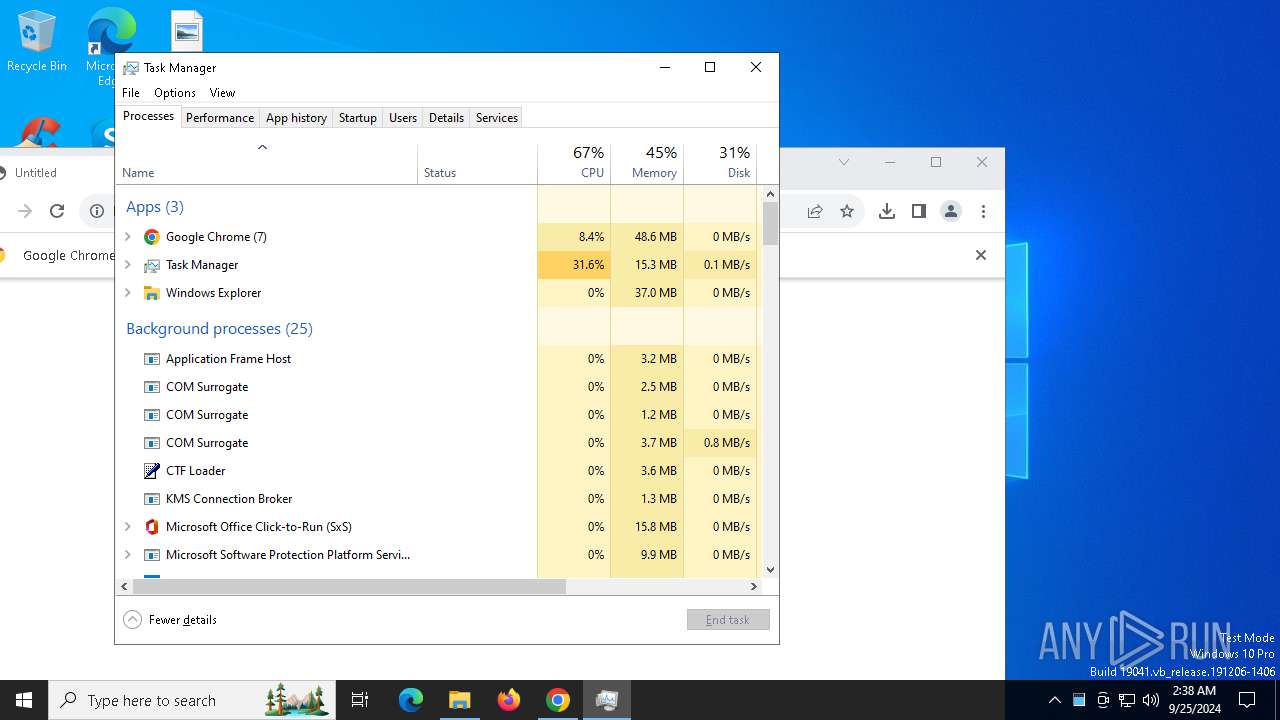
Manual execution by a user
- WinRAR.exe (PID: 6664)
- MoonPredictorV21.exe (PID: 4784)
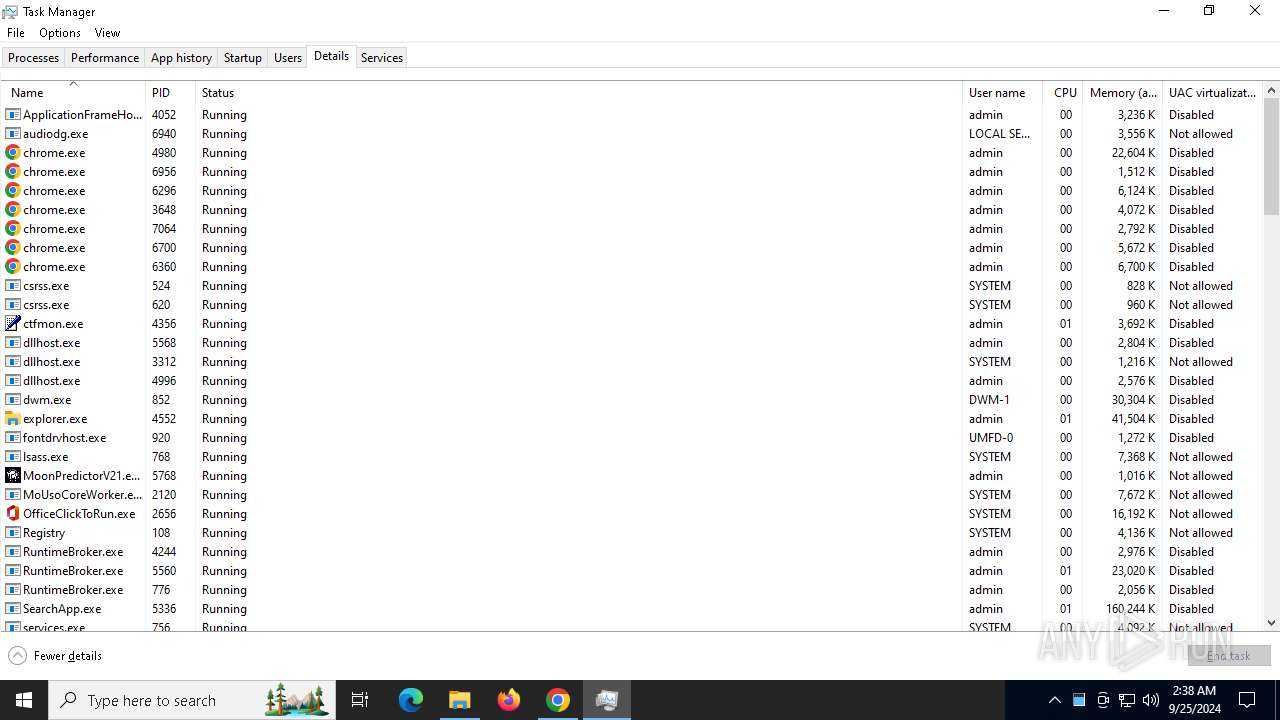
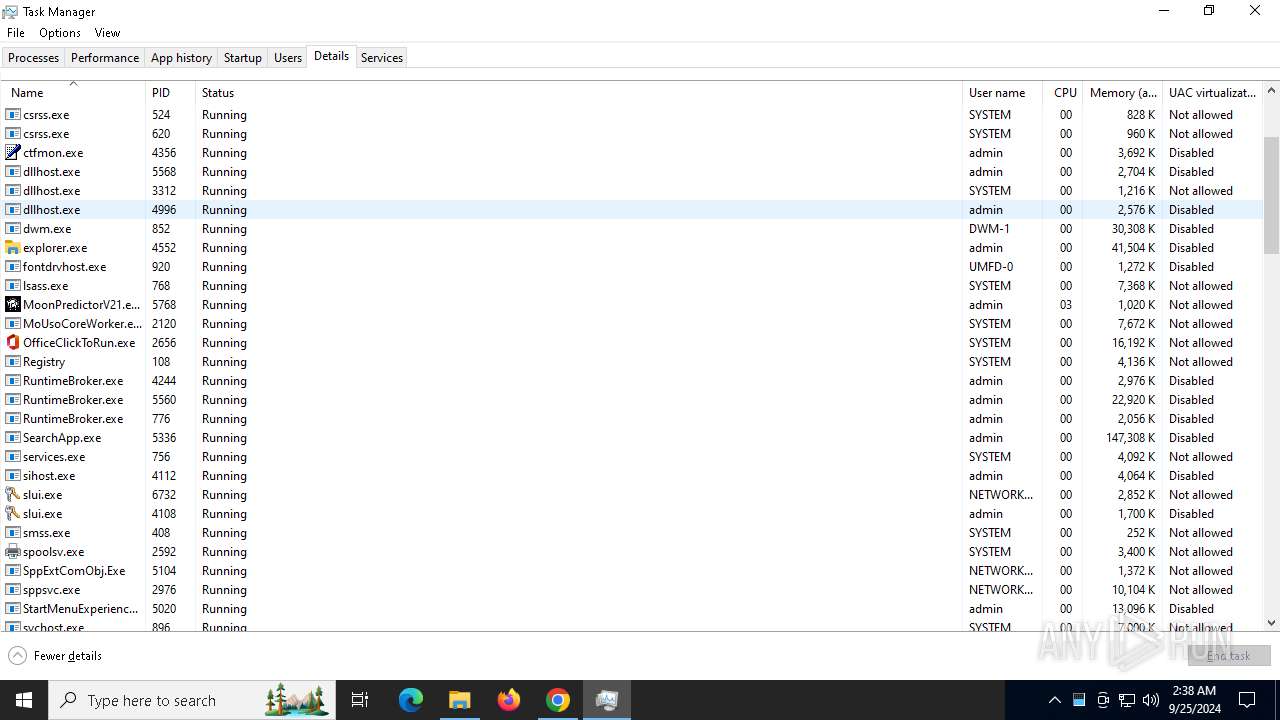
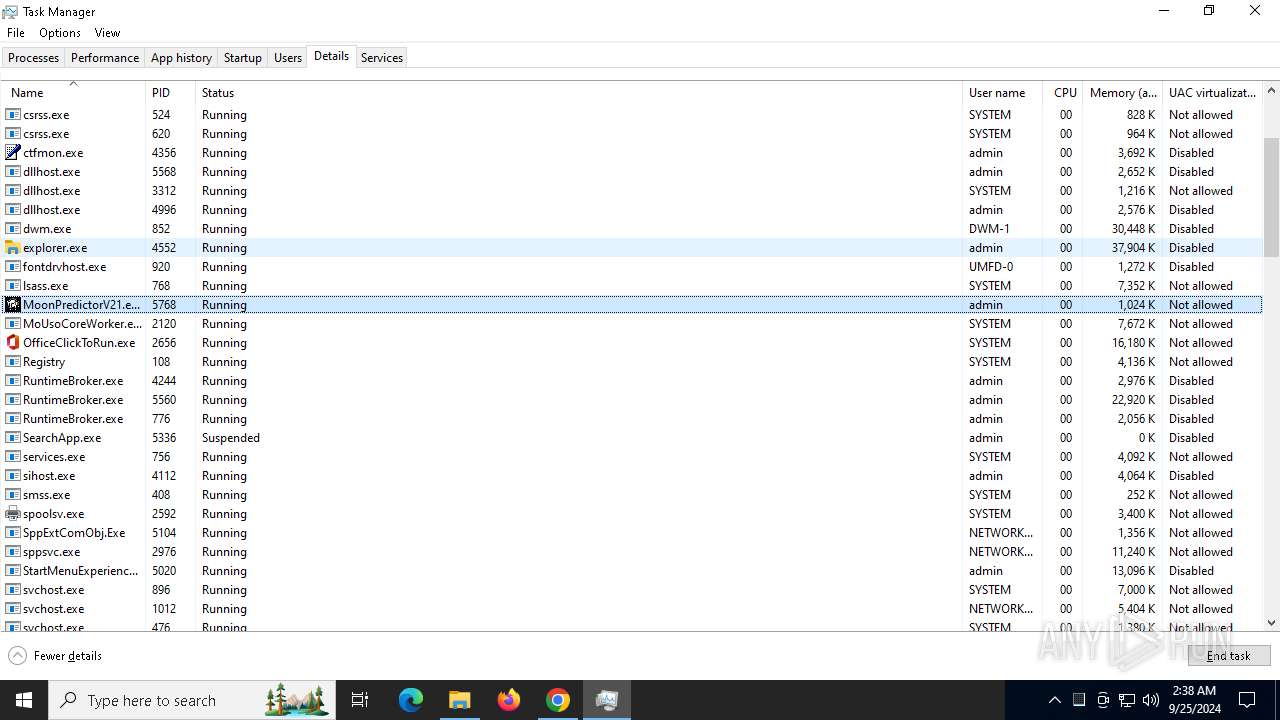
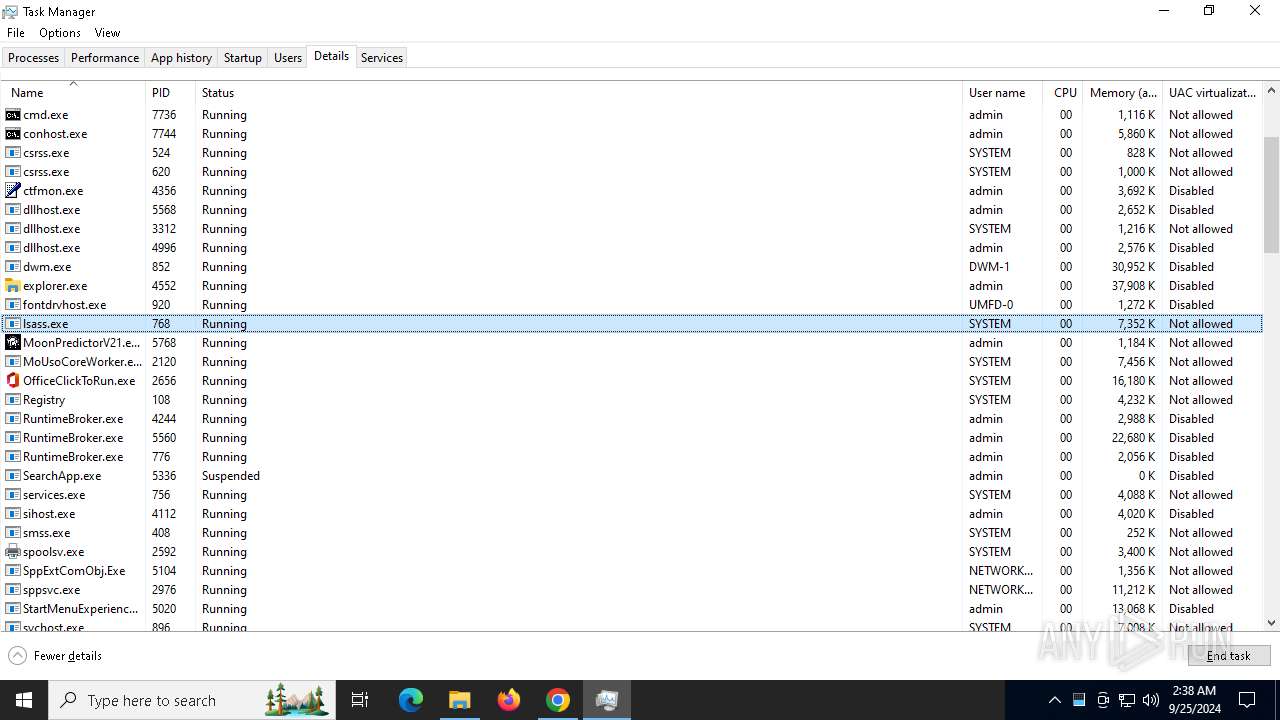
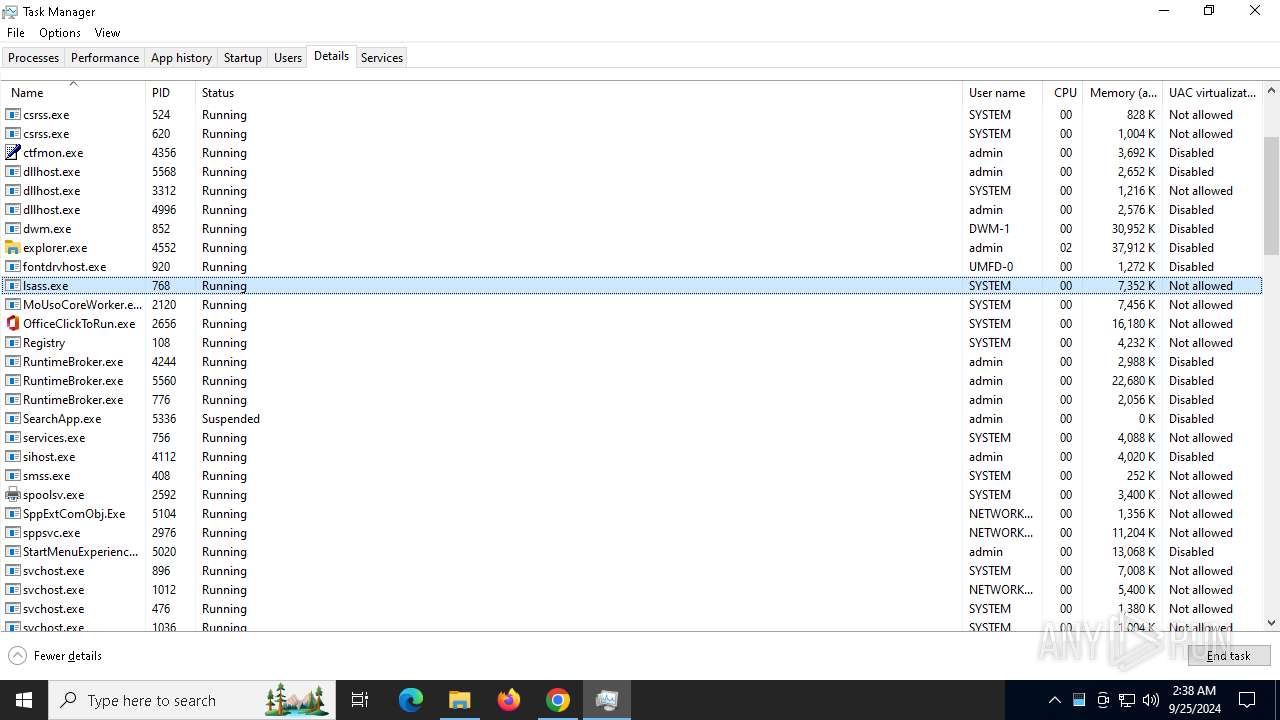
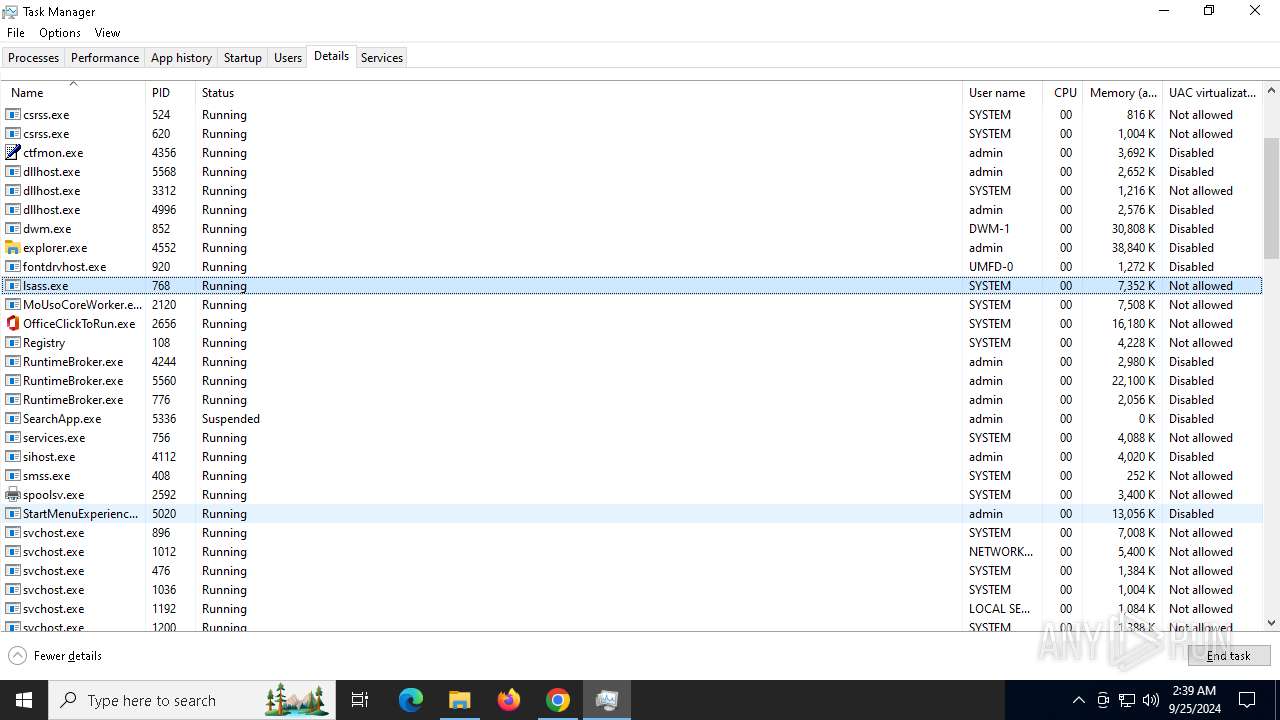
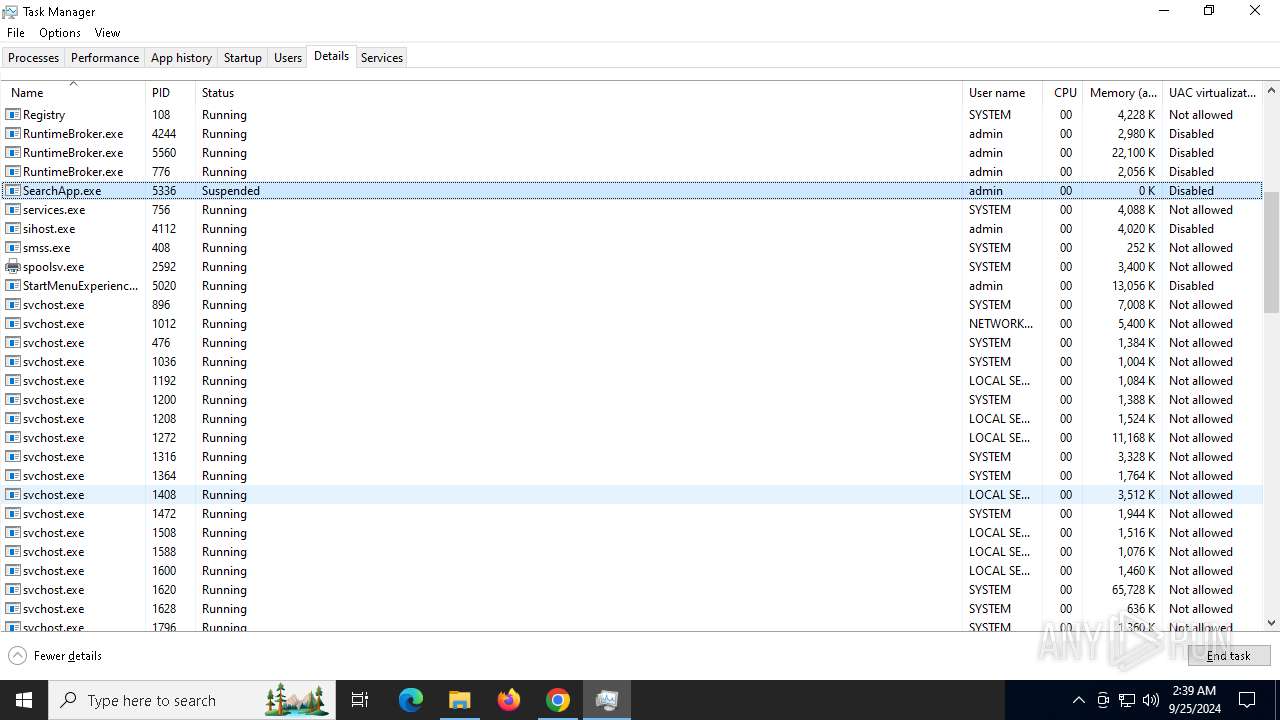
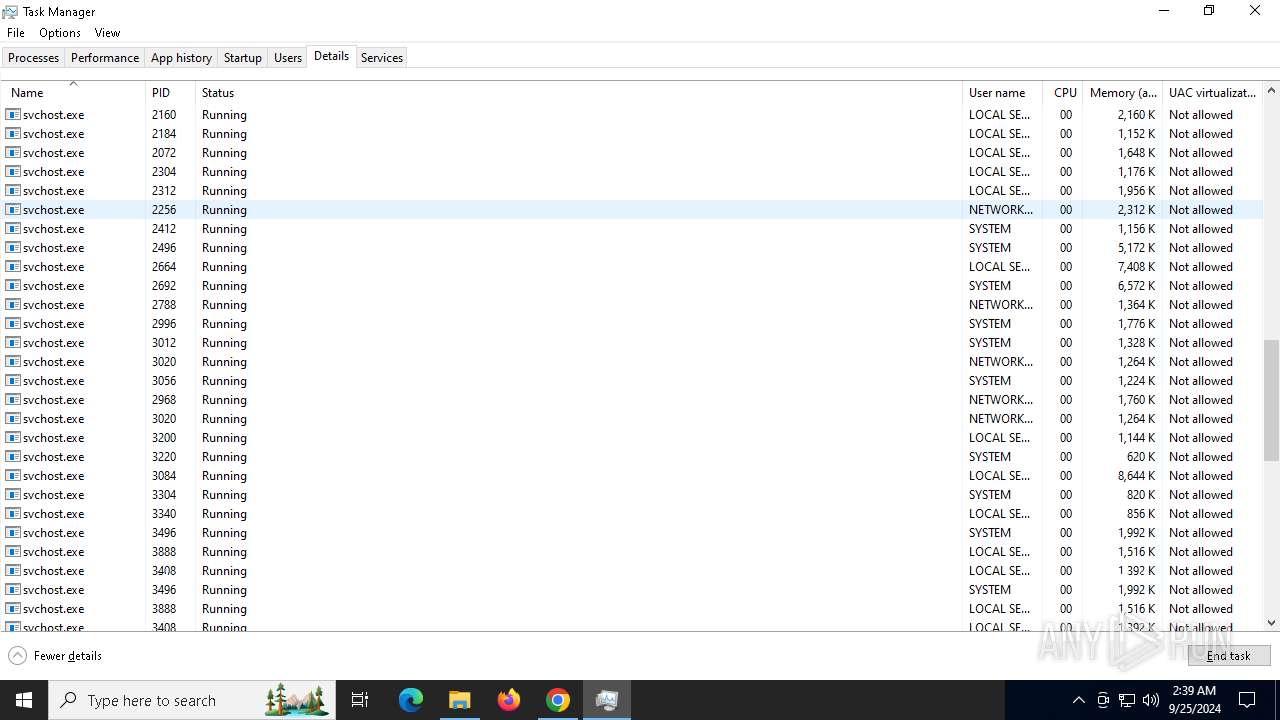
- Taskmgr.exe (PID: 3548)
- Taskmgr.exe (PID: 3896)
Attempting to use file storage service
- chrome.exe (PID: 3648)
PyInstaller has been detected (YARA)
- MoonPredictorV21.exe (PID: 4784)
- MoonPredictorV21.exe (PID: 5768)
- TapWare.exe (PID: 7816)
- TapWare.exe (PID: 8064)
Application launched itself
- chrome.exe (PID: 4980)
Executable content was dropped or overwritten
- chrome.exe (PID: 7320)
- chrome.exe (PID: 7420)
UPX packer has been detected
- MoonPredictorV21.exe (PID: 7392)
- TapWare.exe (PID: 8064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
204
Monitored processes
65
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | C:\WINDOWS\system32\cmd.exe /c "wevtutil qe "Microsoft-Windows-Windows Defender/Operational" /f:text" | C:\Windows\System32\cmd.exe | — | MoonPredictorV21.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 740 | C:\WINDOWS\system32\cmd.exe /c "reg delete hkcu\Software\Classes\ms-settings /f" | C:\Windows\System32\cmd.exe | — | MoonPredictorV21.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5504 --field-trial-handle=1856,i,6320842796854385076,12667593716220716037,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 892 | reg add hkcu\Software\Classes\ms-settings\shell\open\command /v "DelegateExecute" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5220 --field-trial-handle=1856,i,6320842796854385076,12667593716220716037,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 904 | "C:\Users\admin\Downloads\08uxe0\MoonPredictorV21.exe" | C:\Users\admin\Downloads\08uxe0\MoonPredictorV21.exe | — | MoonPredictorV21.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5164 --field-trial-handle=1856,i,6320842796854385076,12667593716220716037,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5396 --field-trial-handle=1856,i,6320842796854385076,12667593716220716037,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1360 | C:\WINDOWS\system32\cmd.exe /c "reg add hkcu\Software\Classes\ms-settings\shell\open\command /v "DelegateExecute" /f" | C:\Windows\System32\cmd.exe | — | MoonPredictorV21.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | C:\WINDOWS\system32\cmd.exe /c "reg add hkcu\Software\Classes\ms-settings\shell\open\command /d "C:\Users\admin\Downloads\08uxe0\MoonPredictorV21.exe" /f" | C:\Windows\System32\cmd.exe | — | MoonPredictorV21.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 538
Read events
23 485
Write events
40
Delete events
13
Modification events
| (PID) Process: | (4980) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4980) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4980) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4980) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4980) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2268) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000D95DC2ABF30EDB01 | |||
| (PID) Process: | (6664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (6664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6664) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
939
Suspicious files
406
Text files
3 185
Unknown types
65
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1fc721.TMP | — | |
MD5:— | SHA256:— | |||
| 4980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1fc721.TMP | — | |
MD5:— | SHA256:— | |||
| 4980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
| 4980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
69
DNS requests
49
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6248 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6164 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6196 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6196 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6164 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2064 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2144 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad36445m2ehnvje342fvryxajoma_3041/jflookgnkcckhobaglndicnbbgbonegd_3041_all_disrgfhbspkatdkpfhliap5vqe.crx3 | unknown | — | — | whitelisted |
2144 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad36445m2ehnvje342fvryxajoma_3041/jflookgnkcckhobaglndicnbbgbonegd_3041_all_disrgfhbspkatdkpfhliap5vqe.crx3 | unknown | — | — | whitelisted |
2144 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad36445m2ehnvje342fvryxajoma_3041/jflookgnkcckhobaglndicnbbgbonegd_3041_all_disrgfhbspkatdkpfhliap5vqe.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6392 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6248 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4980 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3648 | chrome.exe | 108.181.20.36:443 | litter.catbox.moe | TELUS Communications | CA | malicious |
3648 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6196 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
3648 | chrome.exe | 142.250.184.196:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
litter.catbox.moe |
| malicious |
accounts.google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3648 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Temporary File Sharing Service Domain (litter .catbox .moe in TLS SNI) |
3648 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Downloading from a file sharing service is observed |
— | — | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
— | — | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1 ETPRO signatures available at the full report