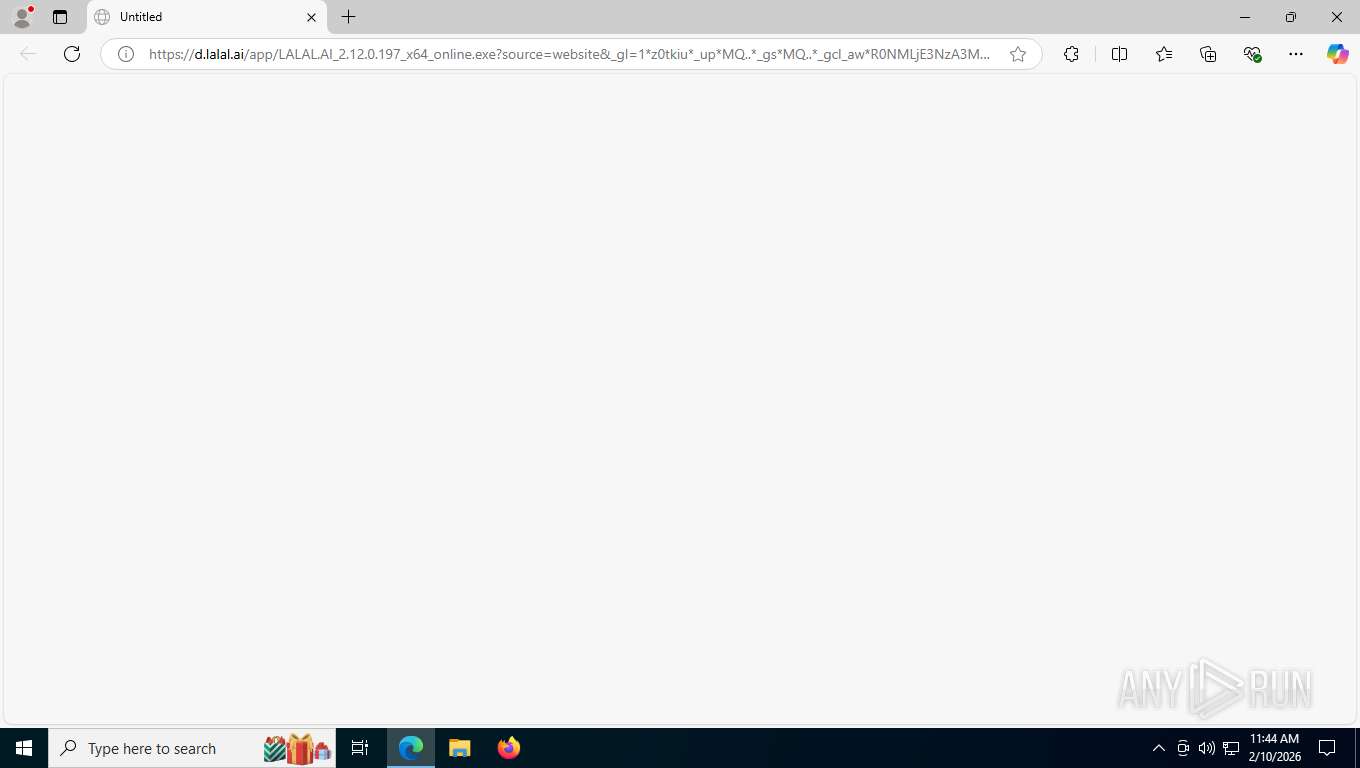
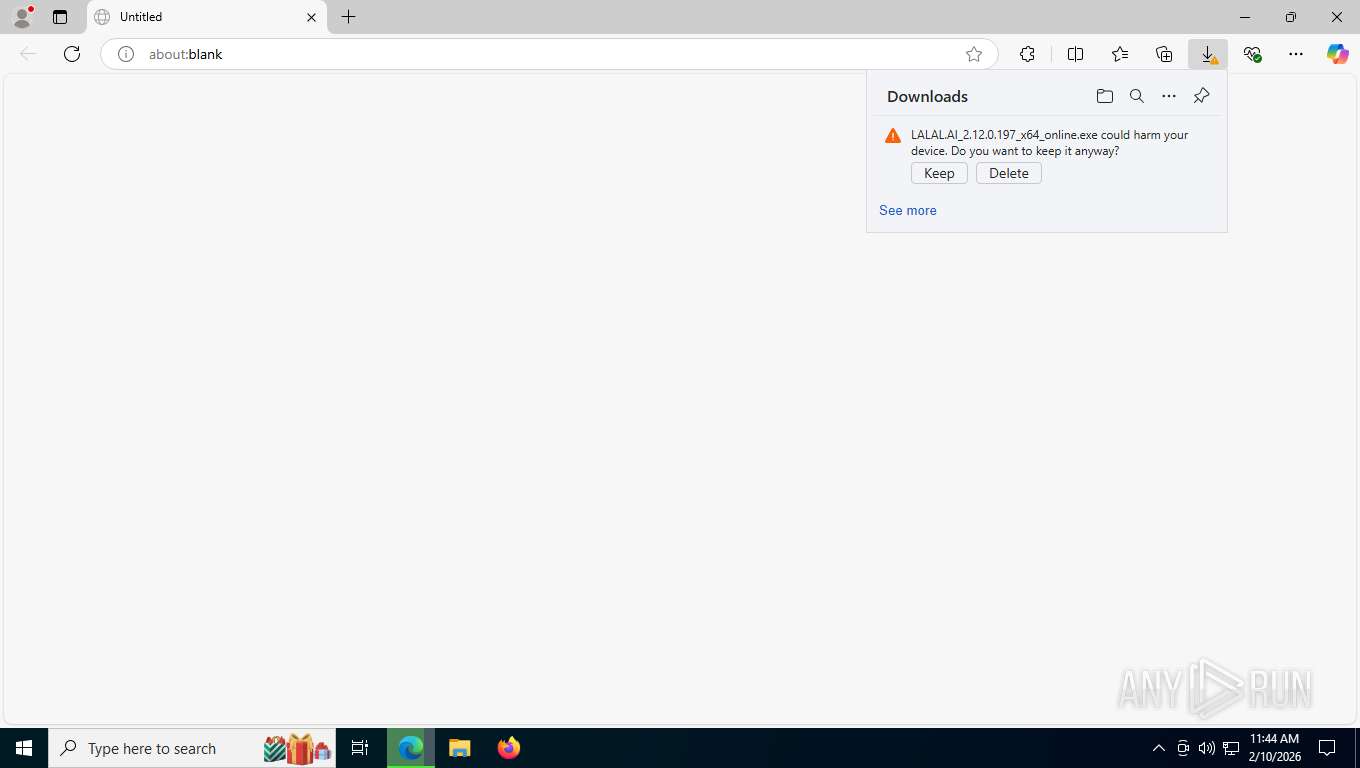
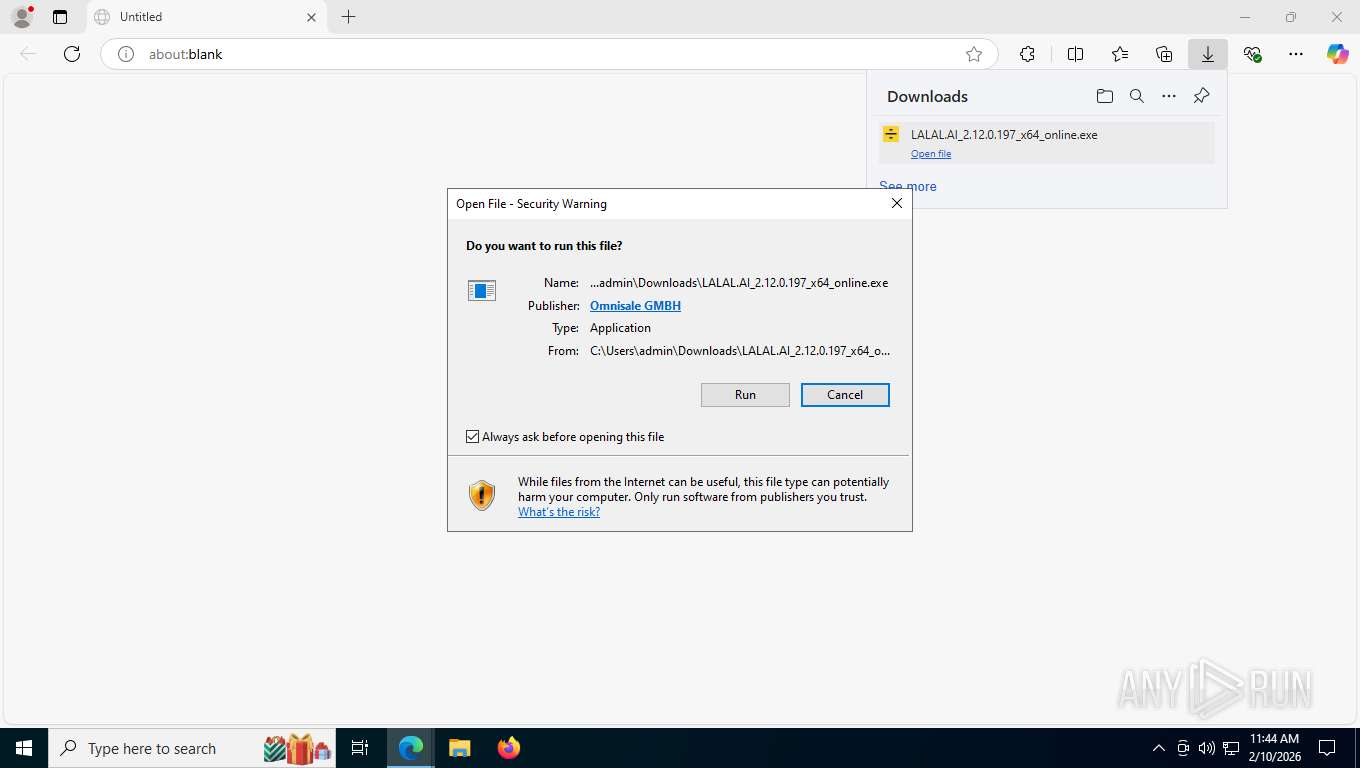
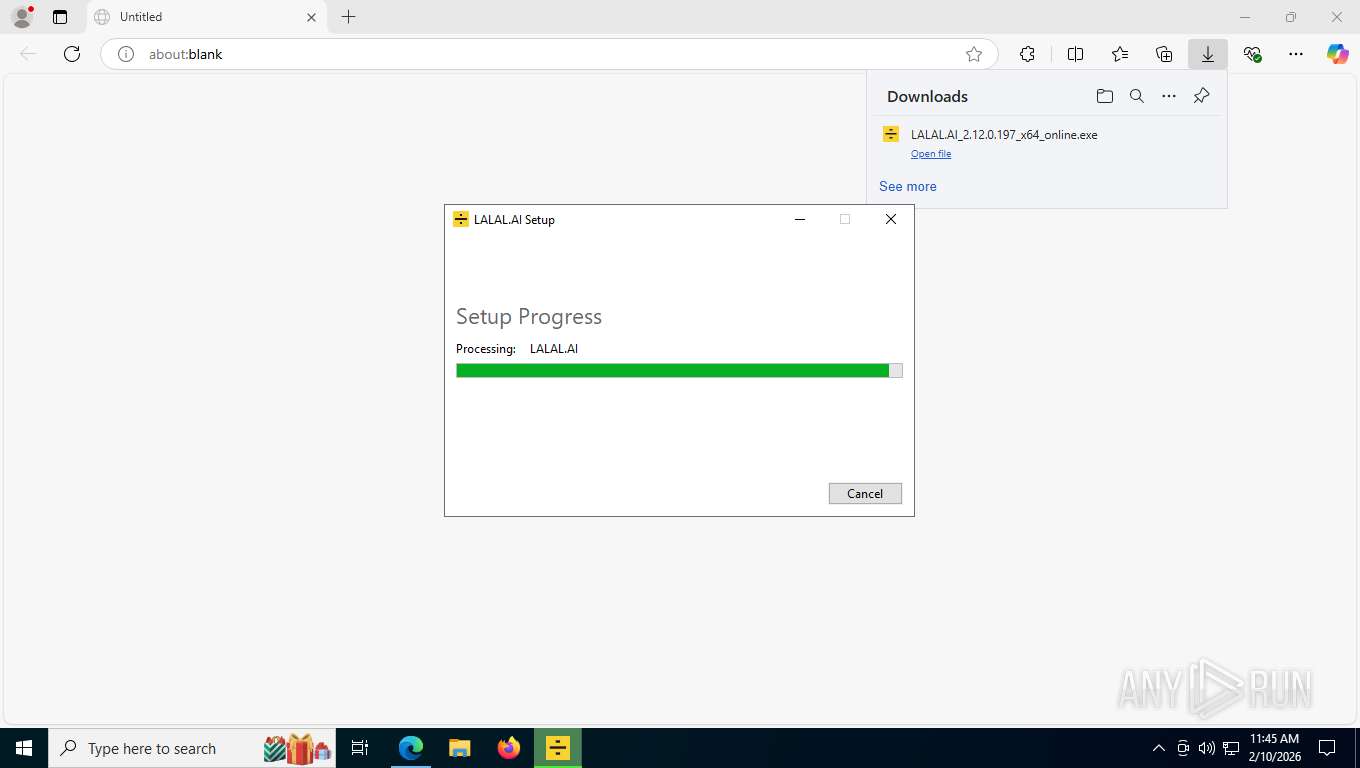
| URL: | https://d.lalal.ai/app/LALAL.AI_2.12.0.197_x64_online.exe?source=website&_gl=1*z0tkiu*_up*MQ..*_gs*MQ..*_gcl_aw*R0NMLjE3NzA3MzQ5ODIuQ2owS0NRaUF5NnZNQmhEQ0FSSXNBSzhyT2dsNEdocVVVYk90U2R6NFRKeF9CMjNWZXdqclBmamM4OHMzX2luZzVyRnlzemtVX1NxMEVJTWFBdHRURUFMd193Y0I.*_gcl_au*MTQ3NDk1ODEyMS4xNzcwNzIzNDM5*_ga*NDQ4OTgwOTc0LjE3NzA3MjM0Mzk.*_ga_GLLN9N0XMJ*czE3NzA3MzQ5NzckbzMkZzEkdDE3NzA3MzQ5ODEkajU2JGwwJGgzMDk5ODU4OTA.&gclid=Cj0KCQiAy6vMBhDCARIsAK8rOgl4GhqUUbOtSdz4TJx_B23VewjrPfjc88s3_ing5rFyszkU_Sq0EIMaAttTEALw_wcB&gbraid=0AAAAACTgyH2U6R9q8tdEpt0sr7HQ7JTKU |
| Full analysis: | https://app.any.run/tasks/1e37a7c7-7a65-4644-96a6-802b0febba88 |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2026, 16:44:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5390C3B600542844231D0B61EEE0E31C |
| SHA1: | FFB70C22DBB33E537624DE72D59062261A0A3314 |
| SHA256: | 4C5D5E43CA75FF236106F2D4DE8165941137744D1577FDAF789C588C04166AA7 |
| SSDEEP: | 12:2y5kWcoXxRx/pjfkIUuYoLfW5iKDeZCwQZGZ:2k5Rktoy5DDesXS |
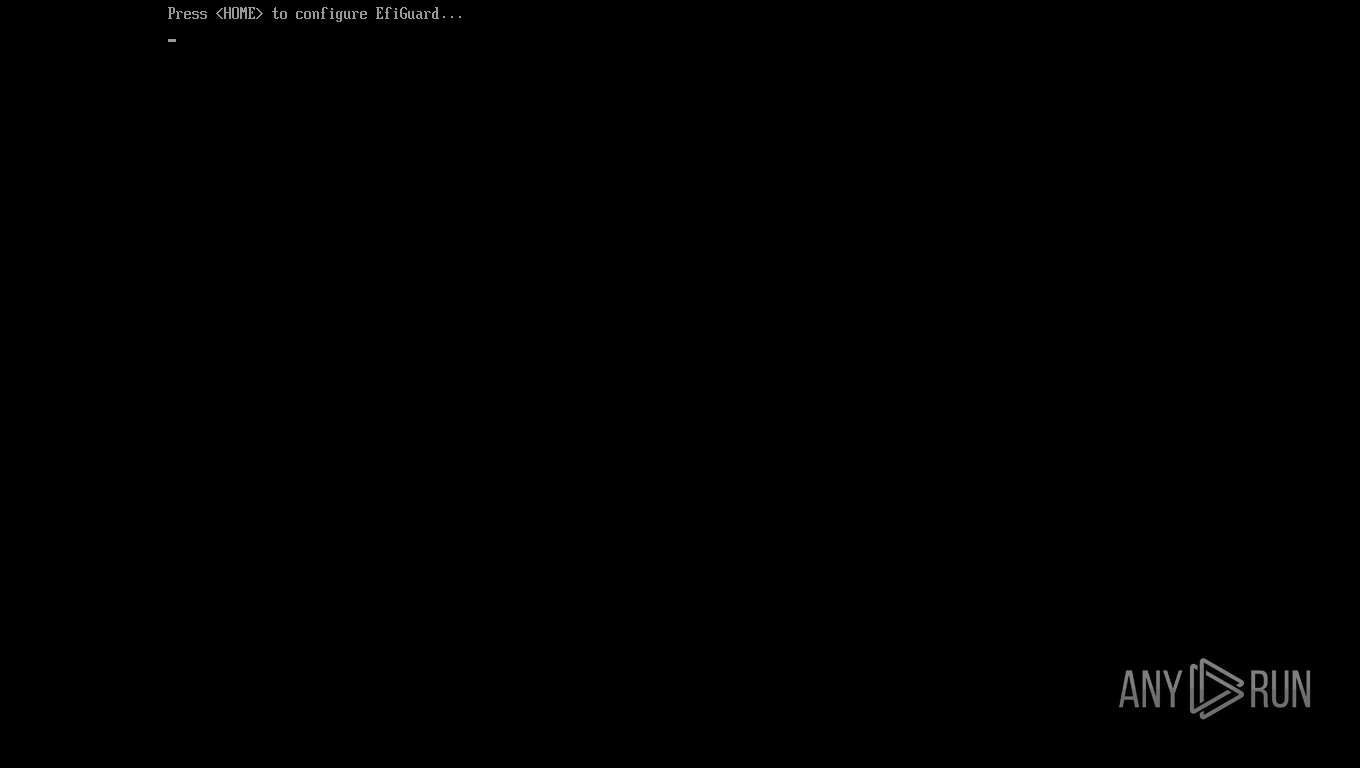
MALICIOUS
Changes the autorun value in the registry
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 5868)
- VC_redist.x64.exe (PID: 4364)
Changes settings of System certificates
- msiexec.exe (PID: 8104)
SUSPICIOUS
Executable content was dropped or overwritten
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 6800)
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 8060)
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 5868)
- vc_redist.x64.14.50.35719.0.exe (PID: 1036)
- VC_redist.x64.exe (PID: 4364)
- vc_redist.x64.14.50.35719.0.exe (PID: 8396)
- VC_redist.x64.exe (PID: 4852)
- VC_redist.x64.exe (PID: 5216)
Searches for installed software
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 8060)
- dllhost.exe (PID: 7416)
- vc_redist.x64.14.50.35719.0.exe (PID: 8396)
- VC_redist.x64.exe (PID: 4364)
- VC_redist.x64.exe (PID: 4852)
- VC_redist.x64.exe (PID: 5216)
Starts itself from another location
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 8060)
- vc_redist.x64.14.50.35719.0.exe (PID: 8396)
Executes as Windows Service
- VSSVC.exe (PID: 8628)
Process drops legitimate windows executable
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 8060)
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 5868)
- vc_redist.x64.14.50.35719.0.exe (PID: 1036)
- vc_redist.x64.14.50.35719.0.exe (PID: 8396)
- VC_redist.x64.exe (PID: 4364)
- msiexec.exe (PID: 8104)
- VC_redist.x64.exe (PID: 5216)
Starts a Microsoft application from unusual location
- VC_redist.x64.exe (PID: 4364)
- vc_redist.x64.14.50.35719.0.exe (PID: 8396)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8104)
- lalalai.exe (PID: 6704)
Application launched itself
- VC_redist.x64.exe (PID: 3212)
- VC_redist.x64.exe (PID: 4852)
The process drops C-runtime libraries
- msiexec.exe (PID: 8104)
Adds/modifies Windows certificates
- msiexec.exe (PID: 8104)
Process drops SQLite DLL files
- msiexec.exe (PID: 8104)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4284)
Reads the date of Windows installation
- lalalai.exe (PID: 6704)
Get information on the list of running processes
- lalalai.exe (PID: 6704)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 9152)
- msiexec.exe (PID: 8104)
Application launched itself
- msedge.exe (PID: 9152)
- msedge.exe (PID: 6484)
Drops script file
- msedge.exe (PID: 6148)
- msiexec.exe (PID: 8104)
Reads Environment values
- identity_helper.exe (PID: 8332)
- lalalai.exe (PID: 6704)
Reads the computer name
- identity_helper.exe (PID: 8332)
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 8060)
- vc_redist.x64.14.50.35719.0.exe (PID: 1036)
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 5868)
- vc_redist.x64.14.50.35719.0.exe (PID: 8396)
- VC_redist.x64.exe (PID: 4364)
- msiexec.exe (PID: 8104)
- VC_redist.x64.exe (PID: 4852)
- VC_redist.x64.exe (PID: 5216)
- msiexec.exe (PID: 1320)
- msiexec.exe (PID: 5508)
- PLUGScheduler.exe (PID: 4284)
- lalalai.exe (PID: 6704)
- identity_helper.exe (PID: 8012)
Checks supported languages
- identity_helper.exe (PID: 8332)
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 6800)
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 8060)
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 5868)
- vc_redist.x64.14.50.35719.0.exe (PID: 1036)
- VC_redist.x64.exe (PID: 4364)
- vc_redist.x64.14.50.35719.0.exe (PID: 8396)
- msiexec.exe (PID: 8104)
- VC_redist.x64.exe (PID: 3212)
- VC_redist.x64.exe (PID: 4852)
- VC_redist.x64.exe (PID: 5216)
- msiexec.exe (PID: 1320)
- msiexec.exe (PID: 5508)
- PLUGScheduler.exe (PID: 4284)
- lalalai.exe (PID: 6704)
- identity_helper.exe (PID: 8012)
Create files in a temporary directory
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 6800)
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 8060)
- vc_redist.x64.14.50.35719.0.exe (PID: 8396)
- VC_redist.x64.exe (PID: 4364)
- VC_redist.x64.exe (PID: 4852)
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 5868)
- lalalai.exe (PID: 6704)
The sample compiled with english language support
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 6800)
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 8060)
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 5868)
- vc_redist.x64.14.50.35719.0.exe (PID: 1036)
- vc_redist.x64.14.50.35719.0.exe (PID: 8396)
- VC_redist.x64.exe (PID: 4364)
- msiexec.exe (PID: 8104)
- VC_redist.x64.exe (PID: 4852)
- VC_redist.x64.exe (PID: 5216)
Reads security settings of Internet Explorer
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 8060)
- vc_redist.x64.14.50.35719.0.exe (PID: 8396)
- VC_redist.x64.exe (PID: 4852)
- lalalai.exe (PID: 6704)
Process checks computer location settings
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 8060)
- vc_redist.x64.14.50.35719.0.exe (PID: 8396)
- VC_redist.x64.exe (PID: 4852)
Manages system restore points
- SrTasks.exe (PID: 2288)
Creates files in the program directory
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 5868)
- VC_redist.x64.exe (PID: 4364)
- PLUGScheduler.exe (PID: 4284)
Launching a file from a Registry key
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 5868)
- VC_redist.x64.exe (PID: 4364)
Creates a software uninstall entry
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 5868)
- VC_redist.x64.exe (PID: 4364)
- msiexec.exe (PID: 8104)
Reads the machine GUID from the registry
- LALAL.AI_2.12.0.197_x64_online.exe (PID: 5868)
- msiexec.exe (PID: 8104)
- VC_redist.x64.exe (PID: 4364)
Creates files or folders in the user directory
- msiexec.exe (PID: 8104)
- lalalai.exe (PID: 6704)
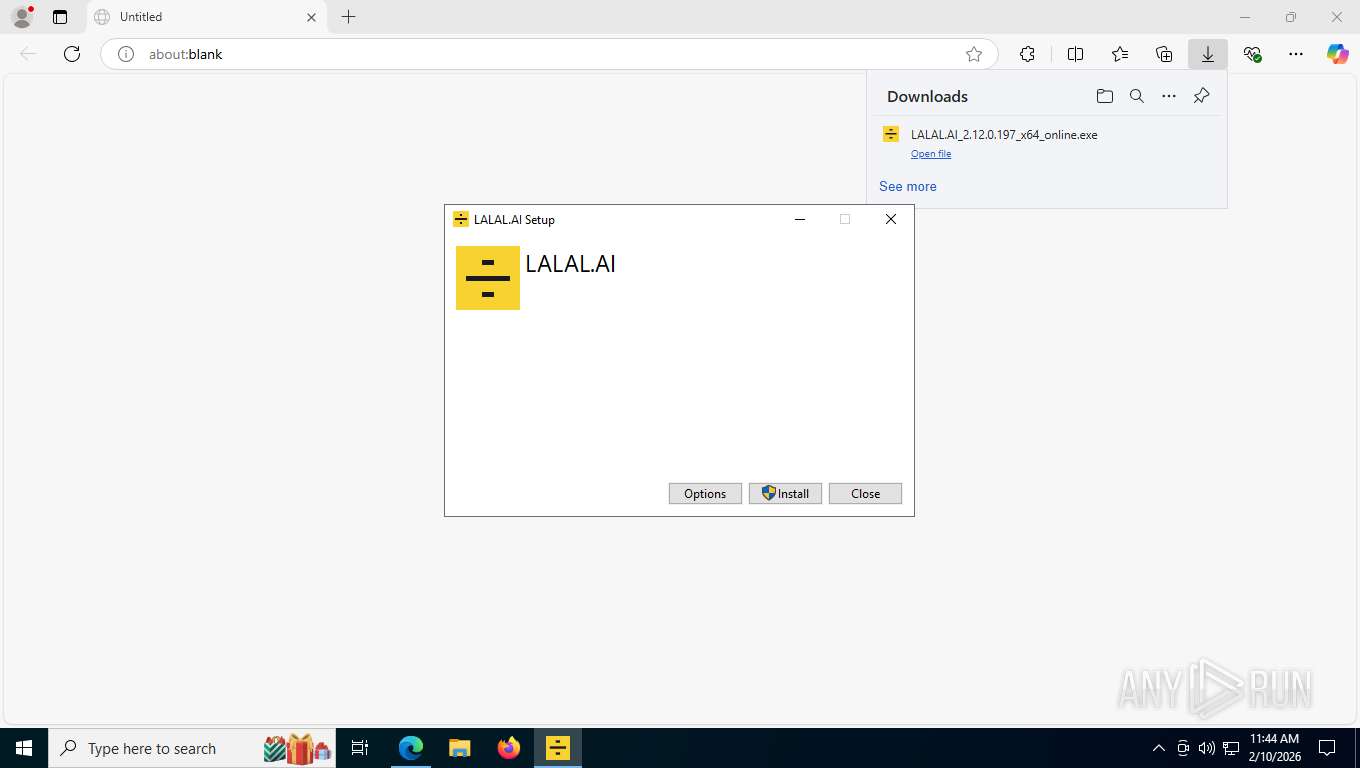
Manual execution by a user
- lalalai.exe (PID: 6704)
Reads Windows Product ID
- lalalai.exe (PID: 6704)
Reads product name
- lalalai.exe (PID: 6704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
380
Monitored processes
73
Malicious processes
2
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4300,i,4703136879472544984,7091684656888850354,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=4312 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6568,i,16688621968440656425,15713644552319931430,262144 --variations-seed-version --mojo-platform-channel-handle=5864 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1036 | "C:\ProgramData\Package Cache\7EE9442CEAEEF605EA66849F042B8410433C988D\vc_redist.x64.14.50.35719.0.exe" /install /quiet /norestart | C:\ProgramData\Package Cache\7EE9442CEAEEF605EA66849F042B8410433C988D\vc_redist.x64.14.50.35719.0.exe | LALAL.AI_2.12.0.197_x64_online.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ v14 Redistributable (x64) - 14.50.35719 Exit code: 3010 Version: 14.50.35719.0 Modules
| |||||||||||||||
| 1188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5208,i,4703136879472544984,7091684656888850354,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5392 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1320 | C:\Windows\syswow64\MsiExec.exe -Embedding 454B22EAB8480C5A0DBB75BEAC48C4ED | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1428 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7160,i,4703136879472544984,7091684656888850354,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7016 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7944,i,4703136879472544984,7091684656888850354,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7088 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1948 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5400,i,4703136879472544984,7091684656888850354,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5844 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=6216,i,16688621968440656425,15713644552319931430,262144 --variations-seed-version --mojo-platform-channel-handle=6900 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2036 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5792,i,4703136879472544984,7091684656888850354,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6456 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
17 635
Read events
16 219
Write events
1 024
Delete events
392
Modification events
| (PID) Process: | (7416) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000825FF292AC9ADC01F81C000004180000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7416) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 15 | |||
| (PID) Process: | (7416) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000000E231693AC9ADC01F81C000008090000E80300000100000000000000000000001A640CAE4B4FCB4797AA9799A05E828B00000000000000000000000000000000 | |||
| (PID) Process: | (5868) LALAL.AI_2.12.0.197_x64_online.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000005E019392AC9ADC01EC16000078200000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7416) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000009F709592AC9ADC01F81C000004180000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7416) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000BD38EB92AC9ADC01F81C000004180000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7416) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000BD38EB92AC9ADC01F81C000004180000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7416) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000007A9AED92AC9ADC01F81C000004180000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7416) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000075F1193AC9ADC01F81C000004180000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8628) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000003C702493AC9ADC01B421000040200000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
98
Suspicious files
320
Text files
695
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 9152 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e52c1.TMP | — | |
MD5:— | SHA256:— | |||
| 9152 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e52c1.TMP | — | |
MD5:— | SHA256:— | |||
| 9152 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 9152 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 9152 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e52c1.TMP | — | |
MD5:— | SHA256:— | |||
| 9152 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e52d1.TMP | — | |
MD5:— | SHA256:— | |||
| 9152 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 9152 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 9152 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e5300.TMP | — | |
MD5:— | SHA256:— | |||
| 9152 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
634
TCP/UDP connections
218
DNS requests
207
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
9048 | msedge.exe | GET | 304 | 150.171.28.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
8448 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8448 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
9152 | msedge.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTh4QXD3xfHaxna9yfH20h%2Ft5LfbQQUZZ9RzoVofy%2BKRYiq3acxux4NAF4CEzMABp2kc9wX5PaYbWUAAAAGnaQ%3D | unknown | — | — | whitelisted |
8104 | msiexec.exe | GET | 200 | 184.24.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
9048 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:SyUNpCsQrDouZzthJnAXKAn_pOh-O7p4Lq8jXPyiKOw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
9048 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 446 b | whitelisted |
9048 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/extensionwebstorebase/v1/crx?os=win&arch=x64&os_arch=x86_64&nacl_arch=x86-64&prod=edgecrx&prodchannel=&prodversion=133.0.3065.92&lang=en-US&acceptformat=crx3,puff&x=id%3Djmjflgjpcpepeafmmgdpfkogkghcpiha%26v%3D1.2.1%26installedby%3Dother%26uc%26ping%3Dr%253D53%2526e%253D1 | unknown | xml | 413 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7004 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8568 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.110.201:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
9048 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
d.lalal.ai |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
9048 | msedge.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
9048 | msedge.exe | Potentially Bad Traffic | ET INFO Executable served from Amazon S3 |
9048 | msedge.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
6900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6768 | MoUsoCoreWorker.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
6900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|