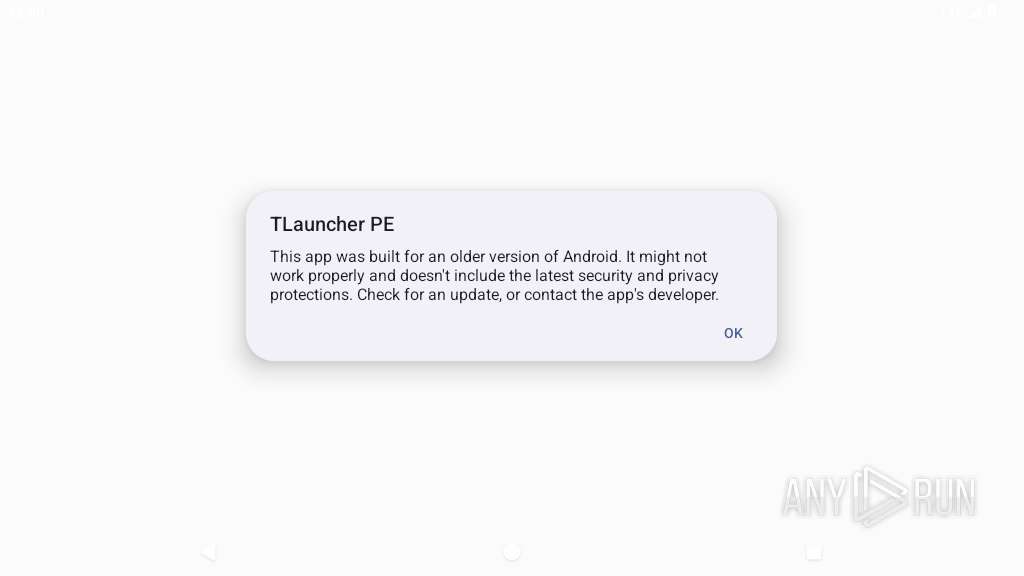
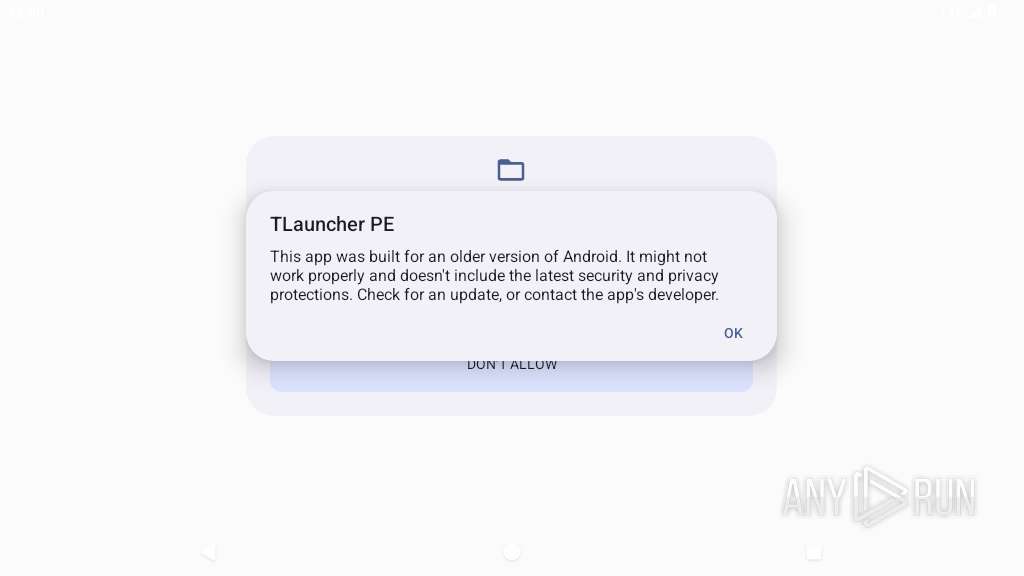
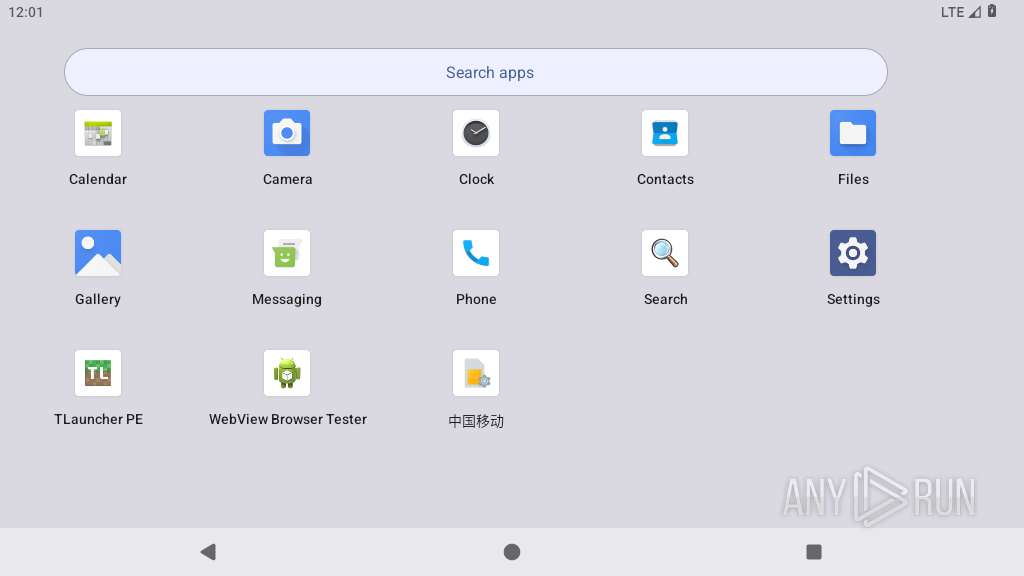
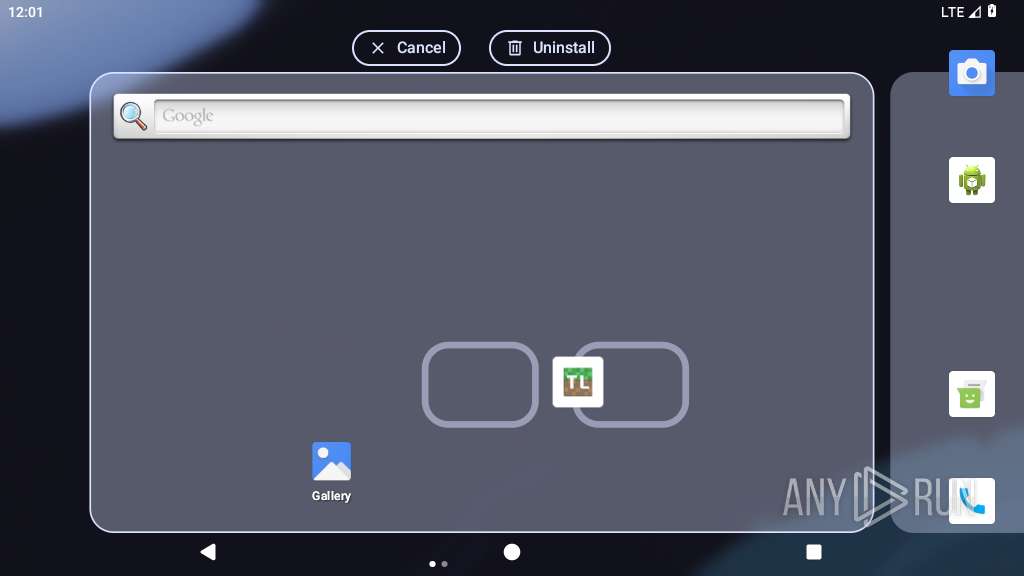
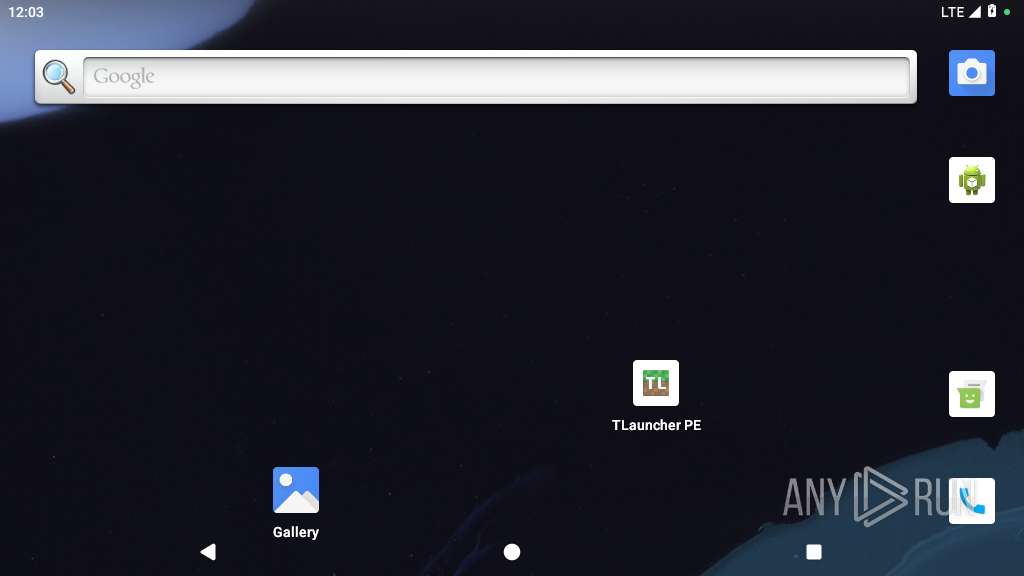
| File name: | TLauncher-PE-0.4.8.apk |
| Full analysis: | https://app.any.run/tasks/fd174f76-87ad-49a0-bd38-84aa57a62127 |
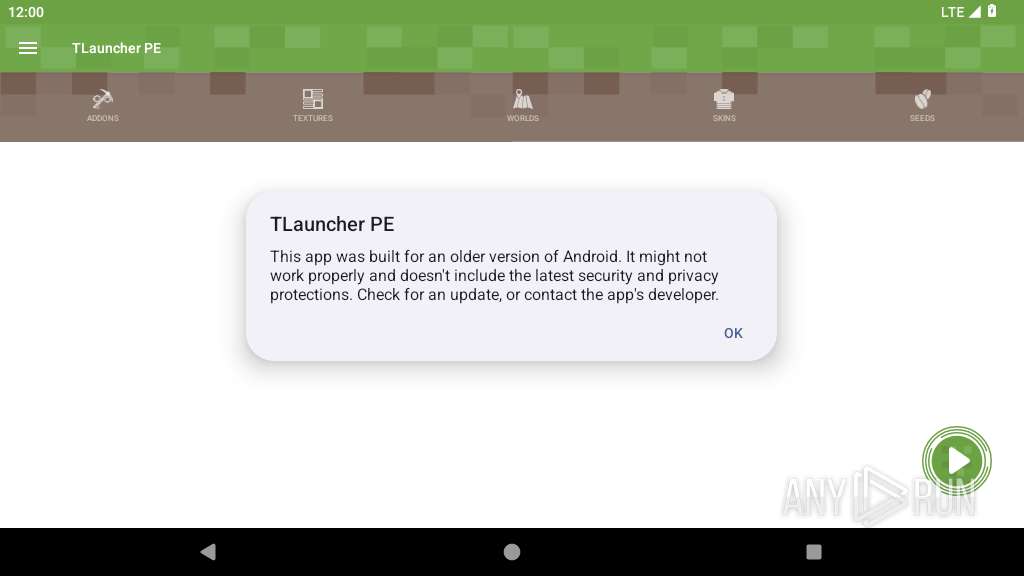
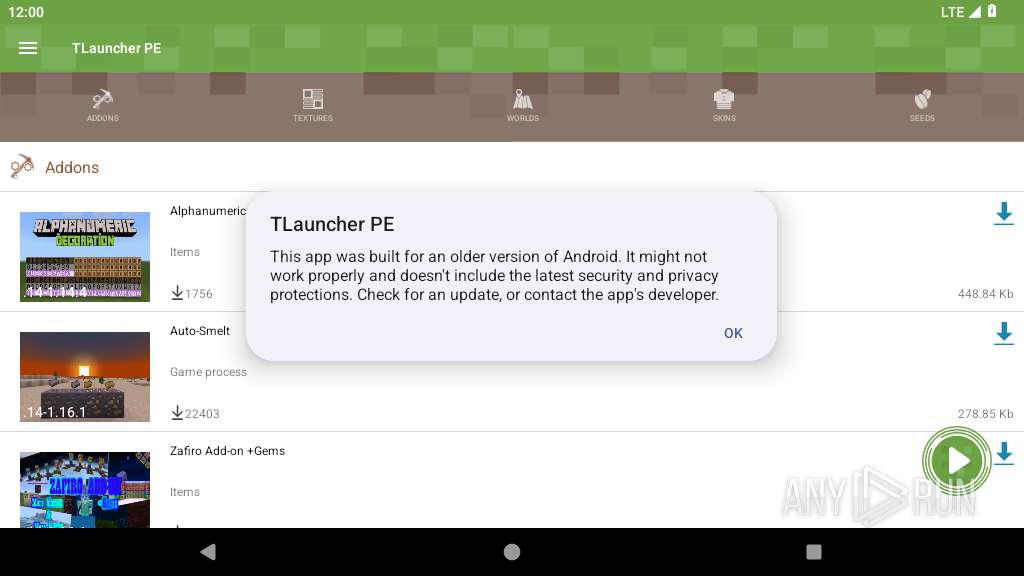
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2025, 12:00:21 |
| OS: | Android 14 |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with AndroidManifest.xml |
| MD5: | 0D458F83492D3F6A77C3551D578E55CC |
| SHA1: | 65FA19F25DEB1EF8E9922CB6DD3262F7F7A5C711 |
| SHA256: | 4C5801733CE29255E48A72CD1764324E6D6E1D3D8100C4FCE95849F6FD97E1C3 |
| SSDEEP: | 393216:pOvePB8Ay2vO4qrg9ud/QED2DZ0oZCo+0fX:RPZvqMId4EyDvxX |
MALICIOUS
No malicious indicators.SUSPICIOUS
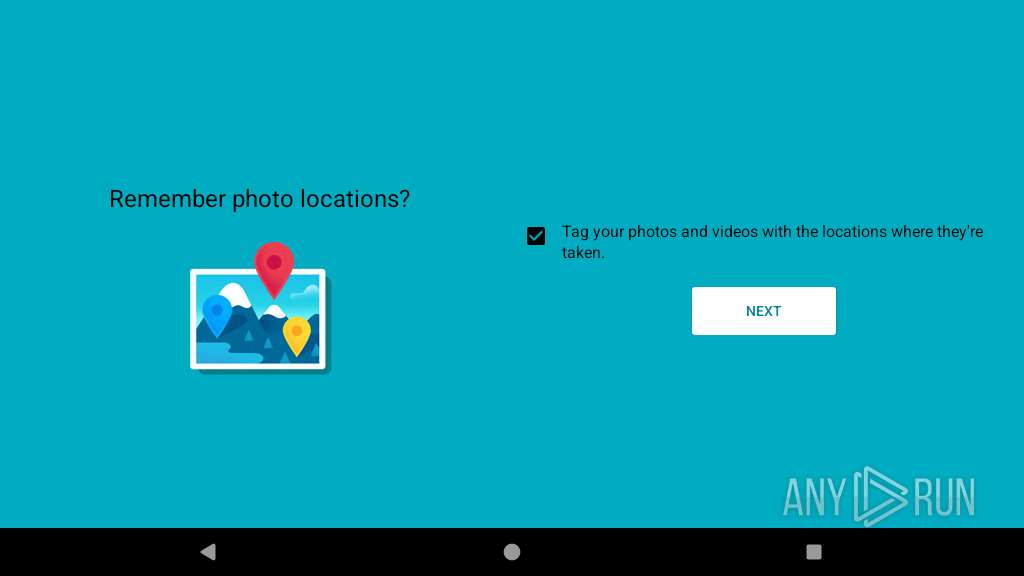
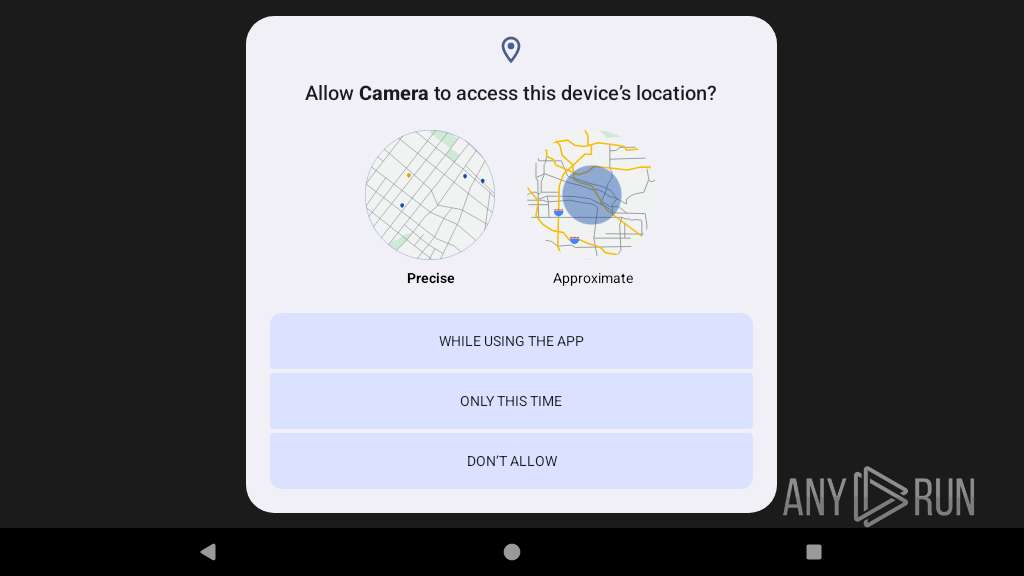
Acquires a wake lock to keep the device awake
- app_process64 (PID: 2205)
Creates a WakeLock to manage power state
- app_process64 (PID: 2205)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2205)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2205)
Accesses external device storage files
- app_process64 (PID: 2205)
Accesses system-level resources
- app_process64 (PID: 2205)
Retrieves a list of running application processes
- app_process64 (PID: 2205)
Accesses memory information
- app_process64 (PID: 2205)
Starts a service
- app_process64 (PID: 2205)
Establishing a connection
- app_process64 (PID: 2205)
Checks if ADB is enabled
- app_process64 (PID: 2205)
Uses encryption API functions
- app_process64 (PID: 2205)
Executes dynamic code using class loader
- app_process64 (PID: 2205)
Retrieves installed applications on device
- app_process64 (PID: 2205)
INFO
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2205)
Loads a native library into the application
- app_process64 (PID: 2205)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2205)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 2205)
Dynamically loads a class in Java
- app_process64 (PID: 2205)
Detects device power status
- app_process64 (PID: 2205)
Retrieves the value of a system setting
- app_process64 (PID: 2205)
Returns elapsed time since boot
- app_process64 (PID: 2205)
Gets file name without full path
- app_process64 (PID: 2205)
Retrieves CPU core information
- app_process64 (PID: 2205)
Dynamically registers broadcast event listeners
- app_process64 (PID: 2205)
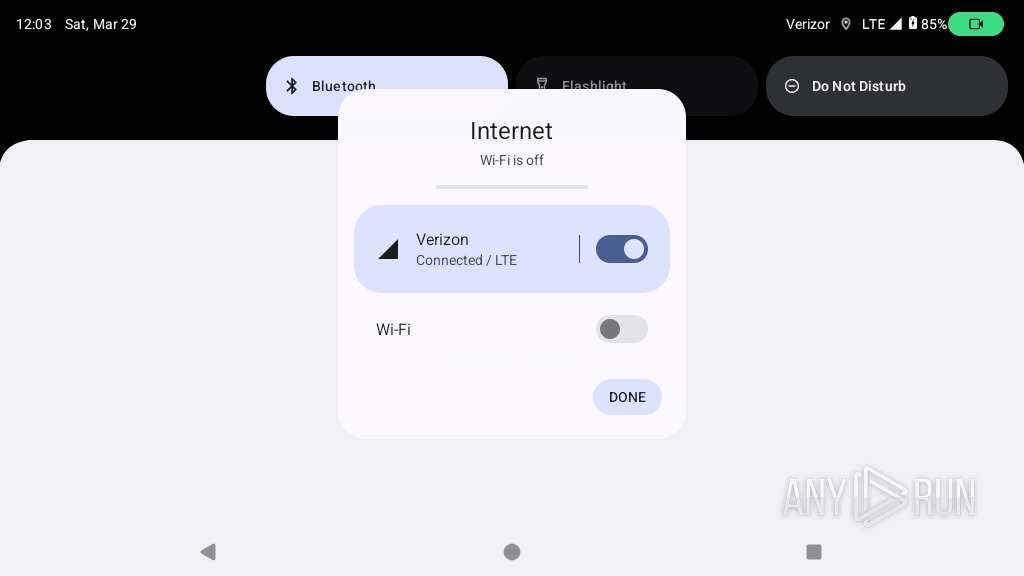
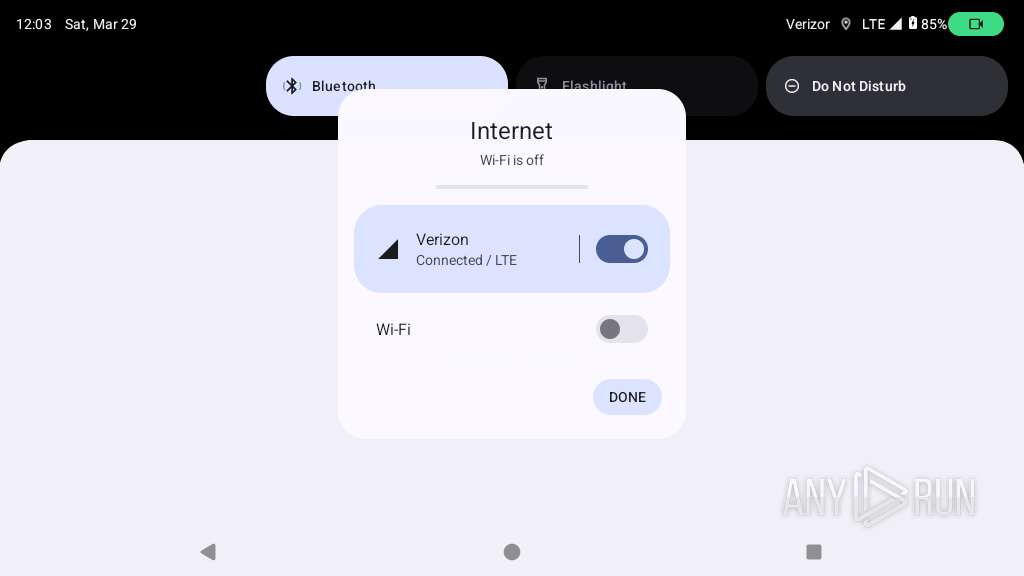
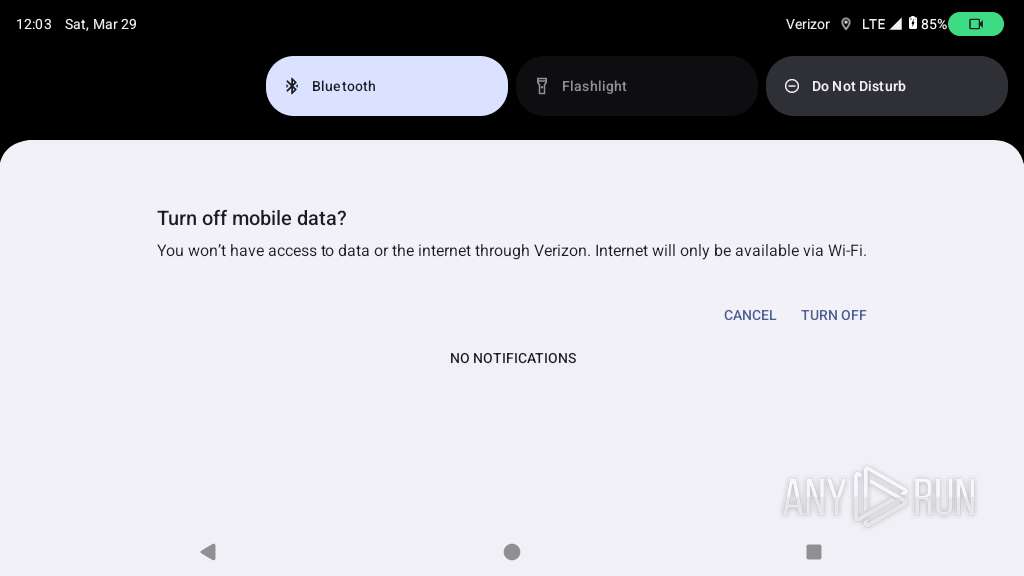
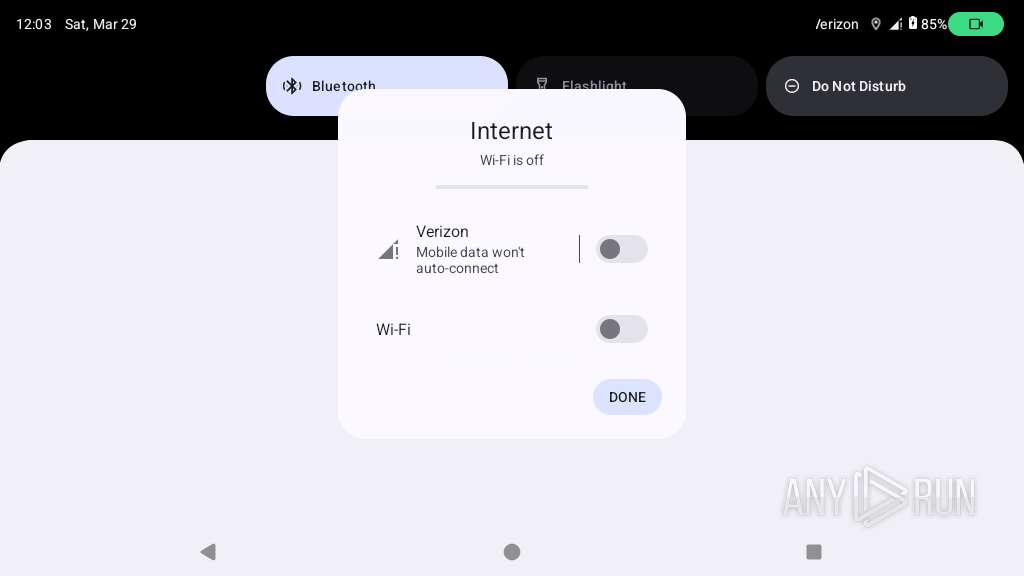
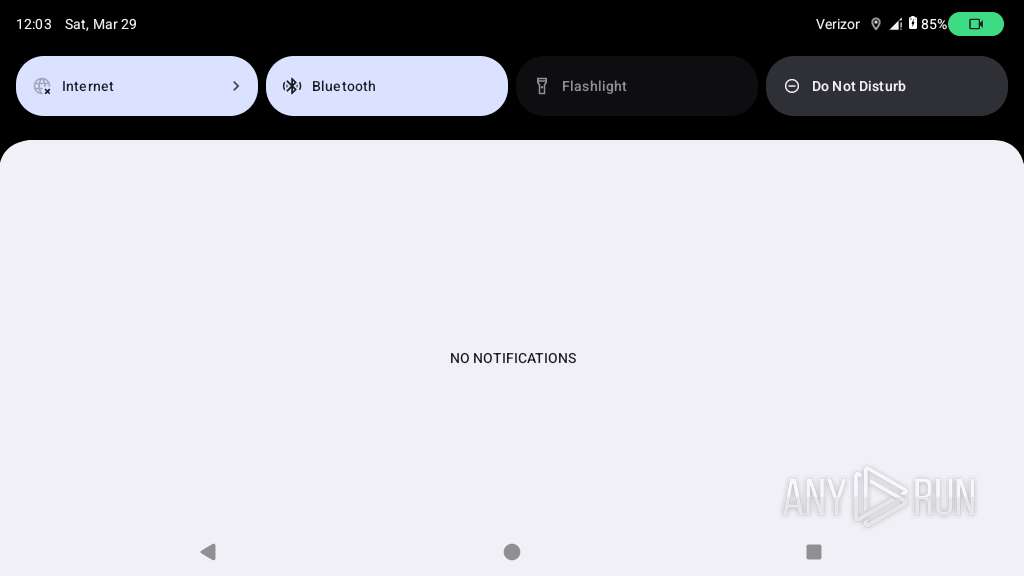
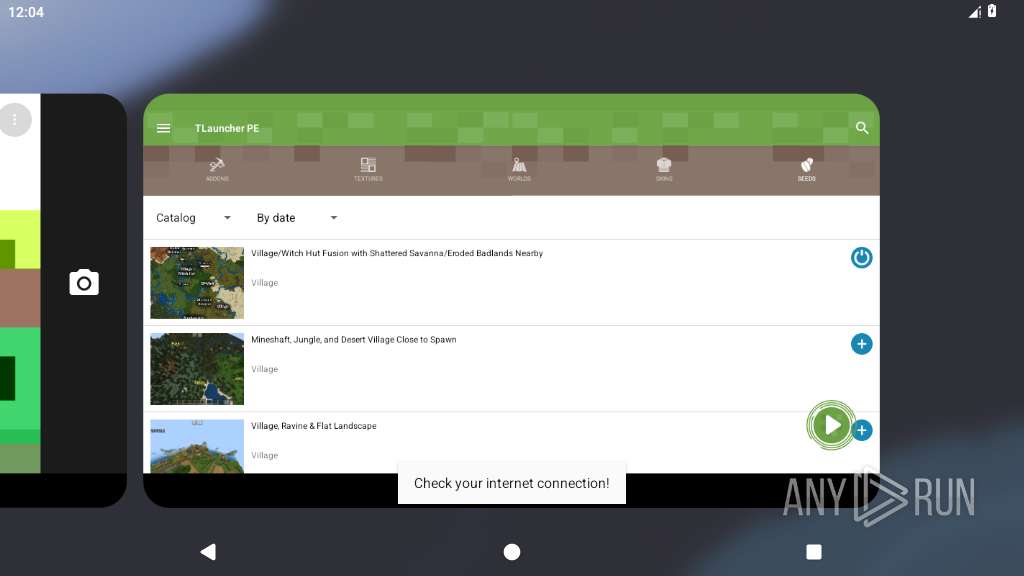
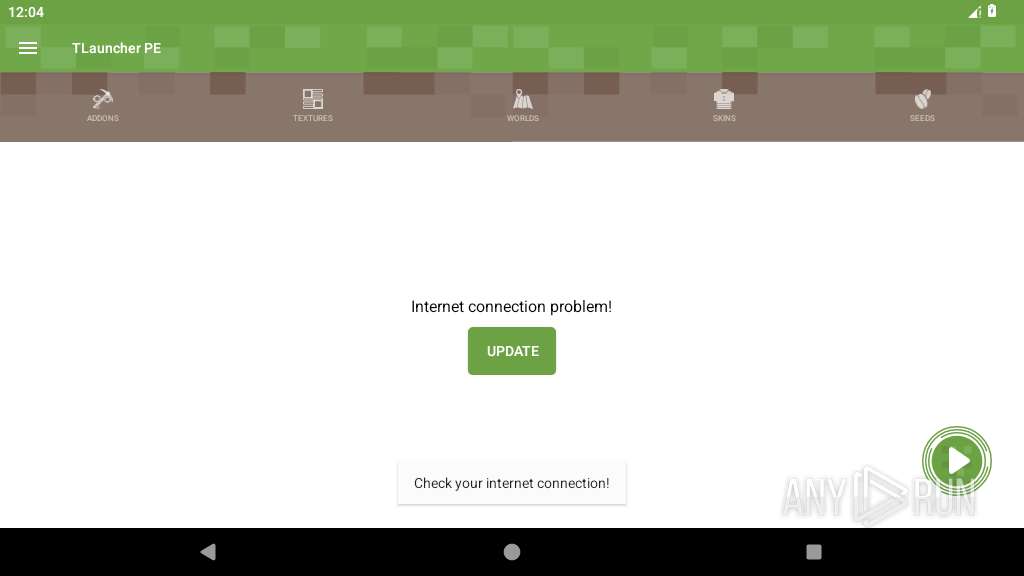
Verifies whether the device is connected to the internet
- app_process64 (PID: 2205)
Stores data using SQLite database
- app_process64 (PID: 2205)
Retrieves the value of a secure system setting
- app_process64 (PID: 2205)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (51.9) |
|---|---|---|
| .spe | | | SPSS Extension (29.7) |
| .jar | | | Java Archive (14.3) |
| .zip | | | ZIP compressed archive (3.9) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:07:09 12:57:38 |
| ZipCRC: | 0xa6489108 |
| ZipCompressedSize: | 2586 |
| ZipUncompressedSize: | 8848 |
| ZipFileName: | AndroidManifest.xml |
Total processes
136
Monitored processes
12
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 342 | /system/bin/netd | /system/bin/netd | init | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2205 | org.tlauncher.tlauncherpe | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2269 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2271 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 9 | ||||
| 2320 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2509 | org.chromium.webview_shell | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2535 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2798 | com.android.server.telecom:ui | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2817 | com.android.dialer | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2912 | com.android.calllogbackup | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
80
Text files
102
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2205 | app_process64 | /data/user/0/org.tlauncher.tlauncherpe/shared_prefs/com.google.android.gms.measurement.prefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2205 | app_process64 | /data/user/0/org.tlauncher.tlauncherpe/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2205 | app_process64 | /data/user/0/org.tlauncher.tlauncherpe/shared_prefs/com.google.android.gms.appid.xml | xml | |
MD5:— | SHA256:— | |||
| 2205 | app_process64 | /data/user/0/org.tlauncher.tlauncherpe/app_webview/Default/Local Storage/leveldb/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 2205 | app_process64 | /data/user/0/org.tlauncher.tlauncherpe/app_webview/Default/Local Storage/leveldb/000001.dbtmp | text | |
MD5:— | SHA256:— | |||
| 2205 | app_process64 | /data/user/0/org.tlauncher.tlauncherpe/app_webview/Default/Local Storage/leveldb/CURRENT | text | |
MD5:— | SHA256:— | |||
| 2205 | app_process64 | /data/user/0/org.tlauncher.tlauncherpe/cache/WebView/Default/HTTP Cache/Code Cache/js/index | binary | |
MD5:— | SHA256:— | |||
| 2205 | app_process64 | /data/user/0/org.tlauncher.tlauncherpe/cache/WebView/Default/HTTP Cache/Code Cache/webui_js/index | binary | |
MD5:— | SHA256:— | |||
| 2205 | app_process64 | /data/user/0/org.tlauncher.tlauncherpe/cache/WebView/Default/HTTP Cache/Code Cache/wasm/index | binary | |
MD5:— | SHA256:— | |||
| 2205 | app_process64 | /data/user/0/org.tlauncher.tlauncherpe/cache/WebView/Default/HTTP Cache/Code Cache/webui_js/index-dir/temp-index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
41
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
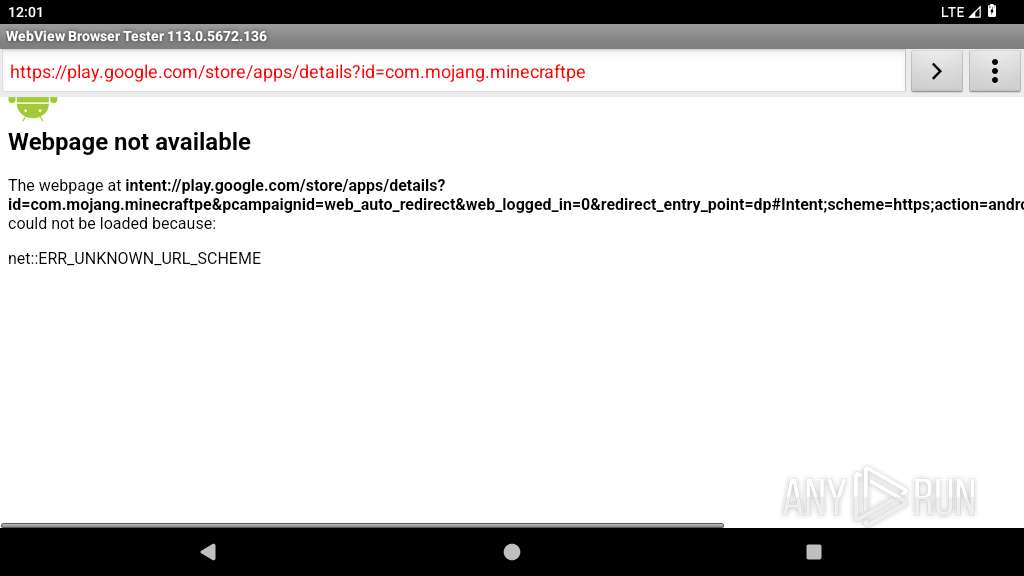
— | — | GET | 204 | 142.250.185.227:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
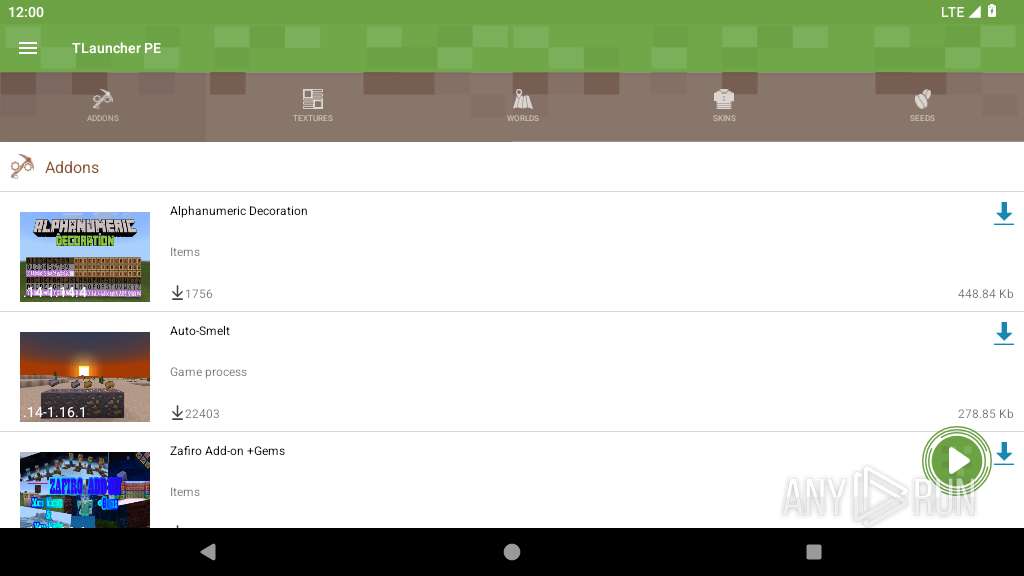
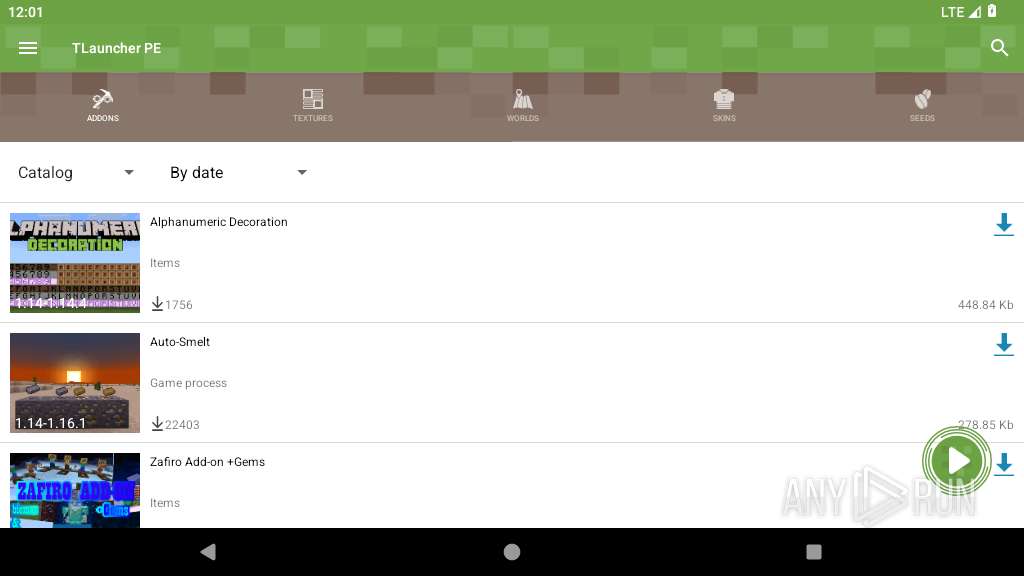
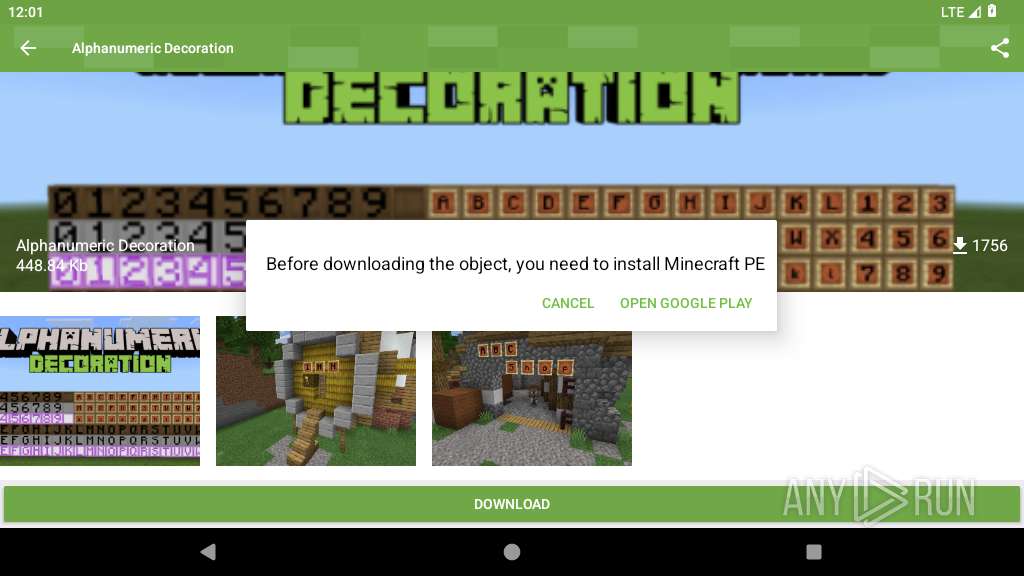
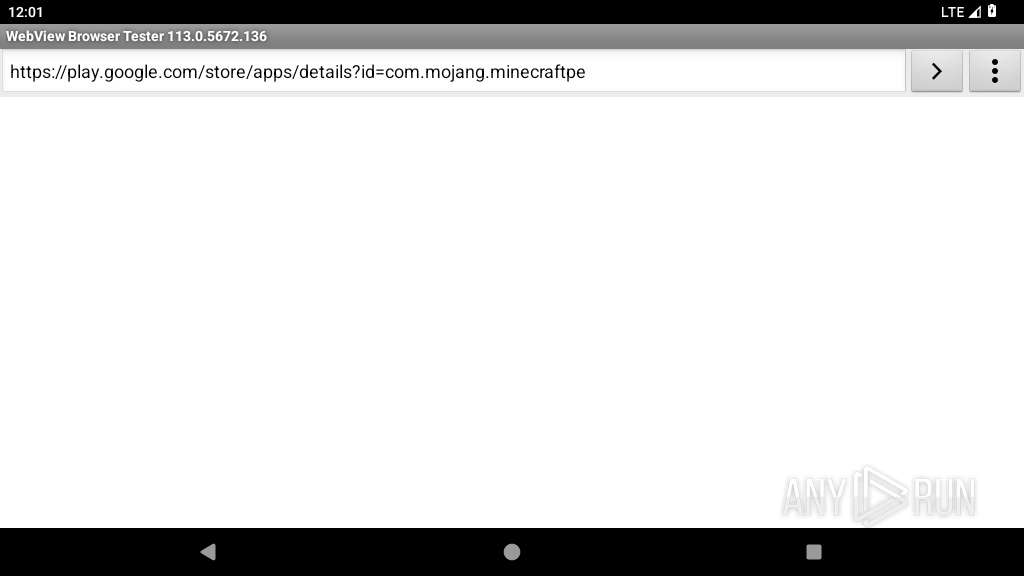
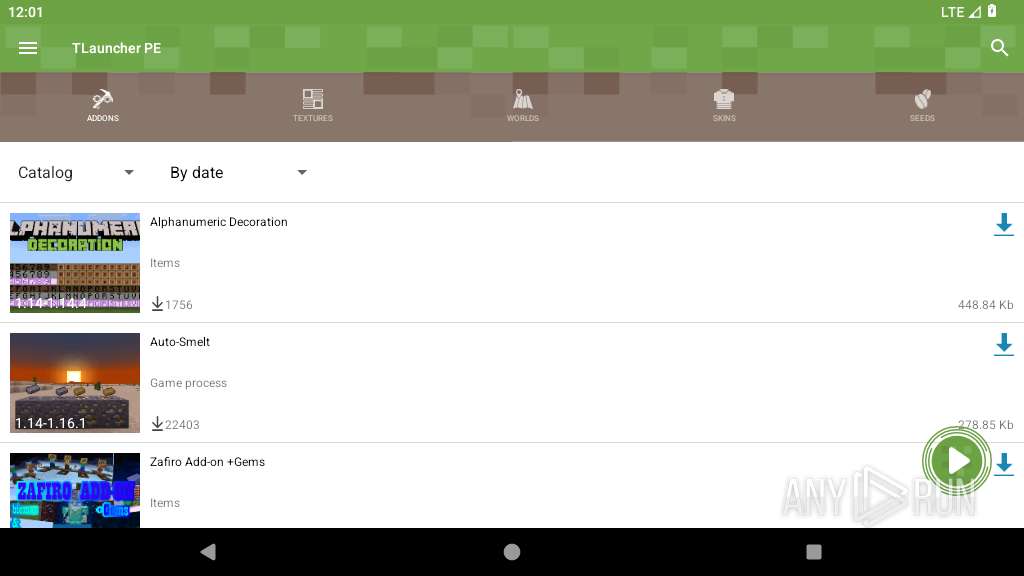
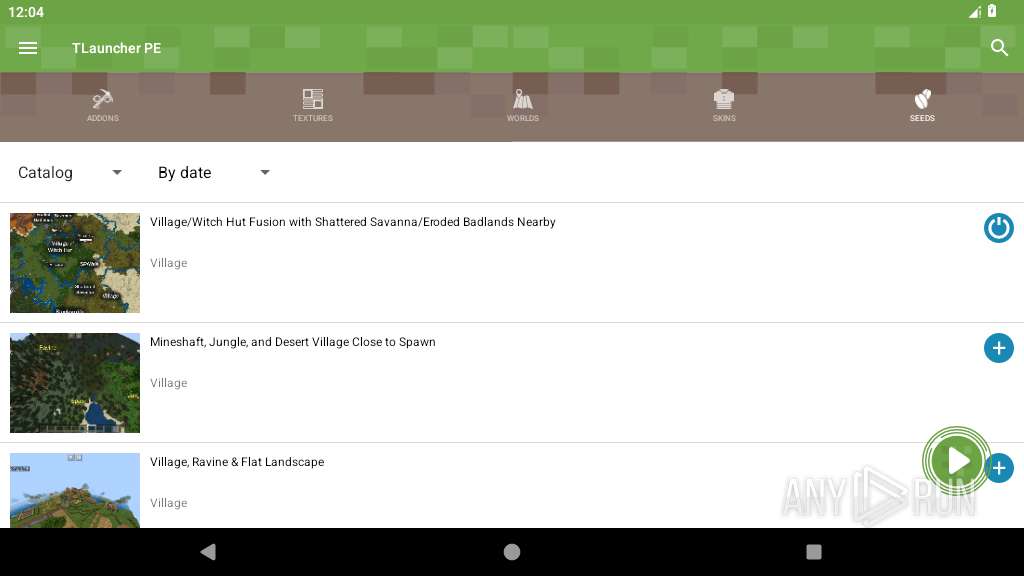
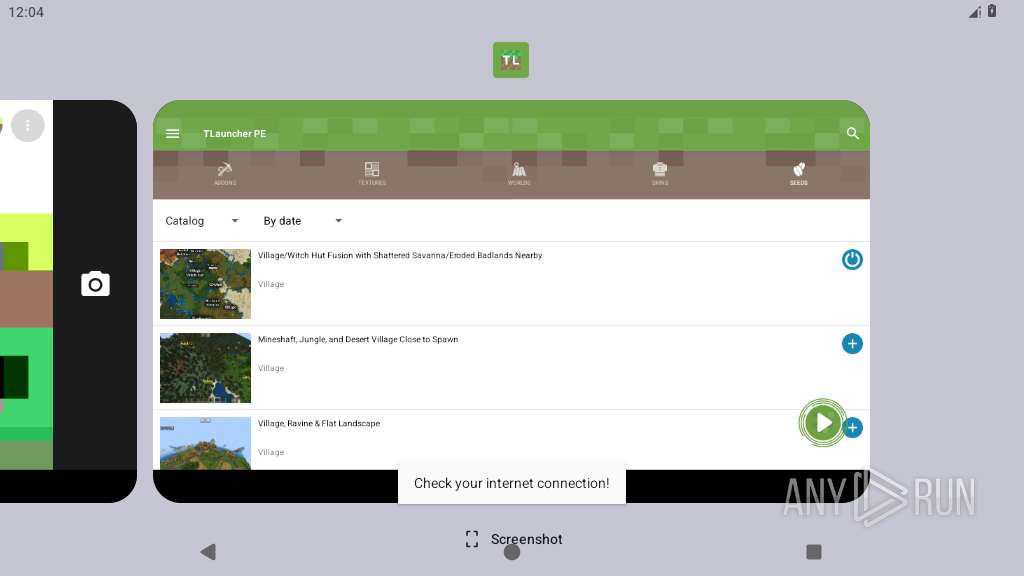
2205 | app_process64 | GET | 200 | 104.20.36.13:80 | http://repo-pe.tlauncher.org/api/objects?type=&page=&lang=&search=&type=4&page=1&lang=2&search=&sort=date:desc&category=0&version= | unknown | — | — | unknown |
2205 | app_process64 | GET | 200 | 104.20.36.13:80 | http://repo-pe.tlauncher.org/api/objects?type=&page=&lang=&search=&type=3&page=1&lang=2&search=&sort=date:desc&category=0&version= | unknown | — | — | unknown |
2205 | app_process64 | GET | 200 | 104.20.36.13:80 | http://repo-pe.tlauncher.org/api/objects?type=&page=&lang=&search=&type=1&page=1&lang=2&search=&sort=date:desc&category=0 | unknown | — | — | unknown |
2205 | app_process64 | GET | 200 | 104.20.36.13:80 | http://repo-pe.tlauncher.org/api/objects?type=&page=&lang=&search=&type=2&page=1&lang=2&search=&sort=date:desc&category=0 | unknown | — | — | unknown |
2205 | app_process64 | GET | 200 | 104.20.36.13:80 | http://repo-pe.tlauncher.org/api/objects?type=&page=&lang=&search=&type=5&page=1&lang=2&search=&sort=date:desc&category=0 | unknown | — | — | unknown |
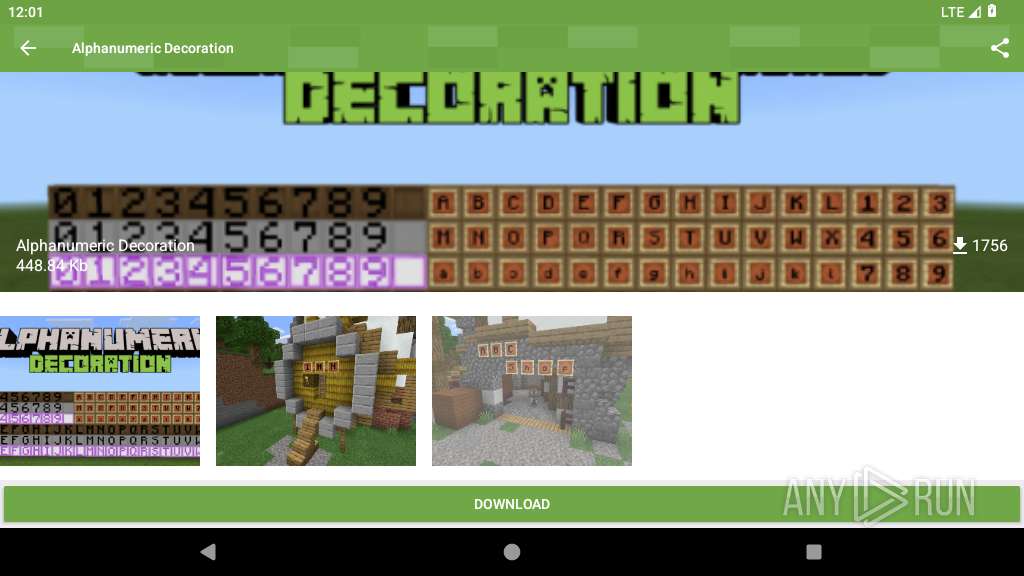
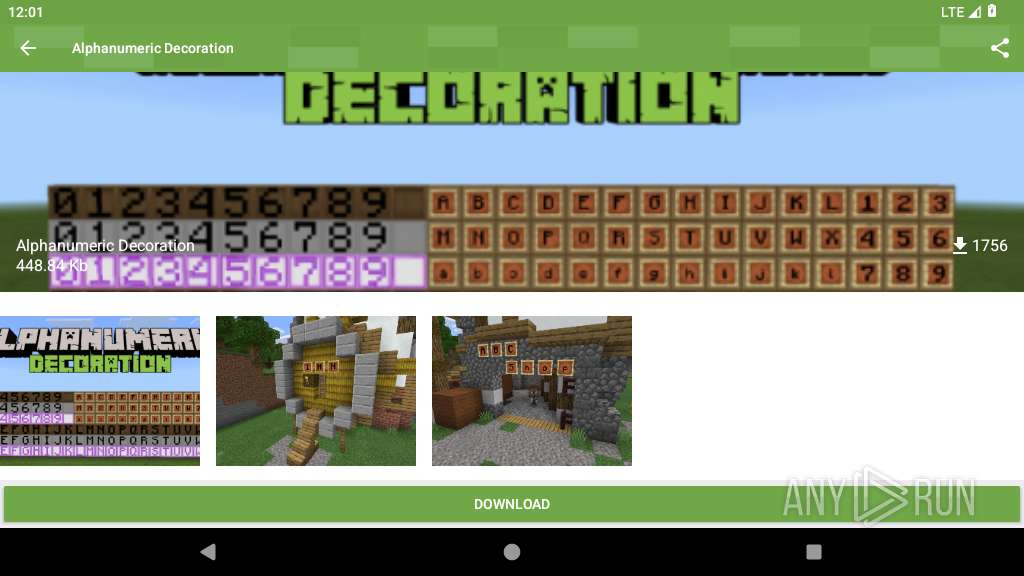
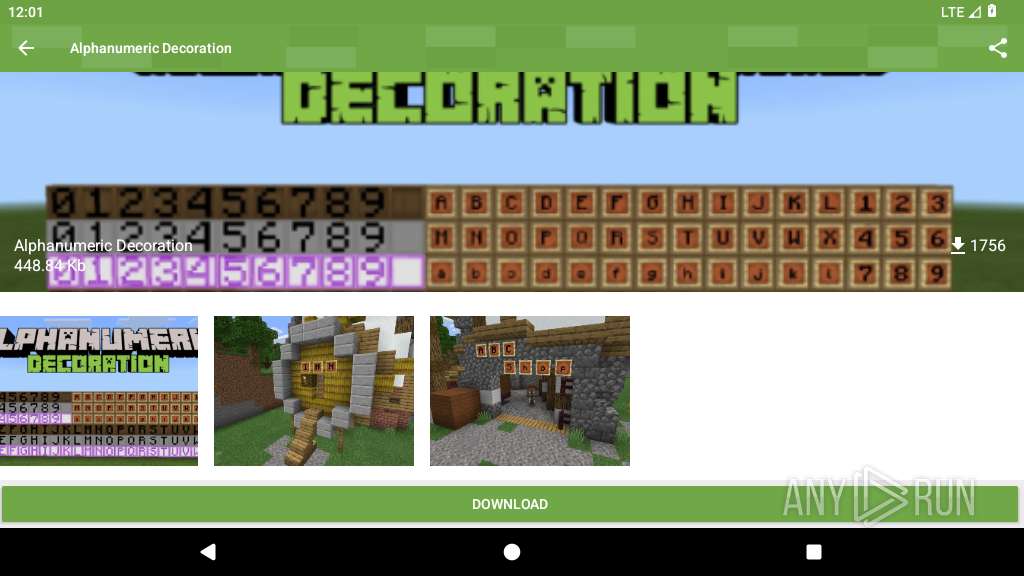
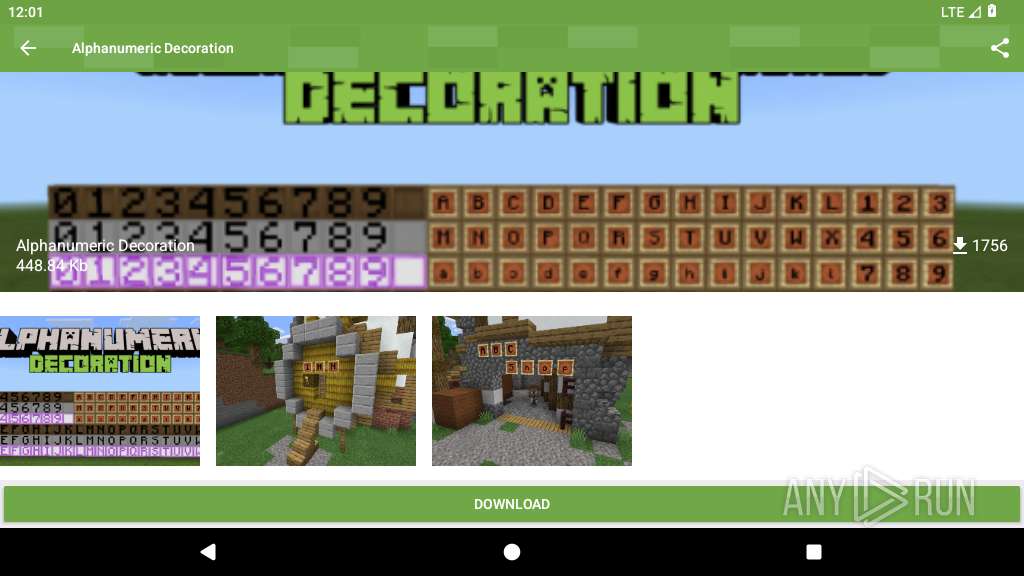
2205 | app_process64 | GET | 200 | 104.20.36.13:80 | http://repo-pe.tlauncher.org/files/objects/17353/imgs/3/alphanumeric-decoration_1-520x245.png | unknown | — | — | unknown |
2205 | app_process64 | GET | 200 | 104.20.36.13:80 | http://repo-pe.tlauncher.org/api/objects?type=&page=&lang=&search=&type=3&page=1&lang=2&search=&sort=date:desc&category=0&version= | unknown | — | — | unknown |
2205 | app_process64 | GET | 200 | 104.20.36.13:80 | http://repo-pe.tlauncher.org/api/objects?type=&page=&lang=&search=&type=4&page=1&lang=2&search=&sort=date:desc&category=0&version= | unknown | — | — | unknown |
2205 | app_process64 | GET | 200 | 104.20.36.13:80 | http://repo-pe.tlauncher.org/api/objects?type=&page=&lang=&search=&type=4&page=1&lang=2&search=&sort=date:desc&category=0&version= | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
447 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 216.239.35.4:123 | time.android.com | — | — | whitelisted |
342 | netd | 8.8.8.8:443 | — | — | — | malicious |
— | — | 8.8.8.8:853 | — | GOOGLE | US | malicious |
— | — | 142.250.185.227:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.250.184.228:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 74.125.71.81:443 | — | GOOGLE | US | unknown |
2320 | app_process32 | 142.250.185.195:443 | — | GOOGLE | US | whitelisted |
2320 | app_process32 | 172.217.16.142:443 | — | GOOGLE | US | whitelisted |
2205 | app_process64 | 104.20.36.13:80 | — | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
google.com |
| whitelisted |
l0W3Zk-dnsotls-ds.metric.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |