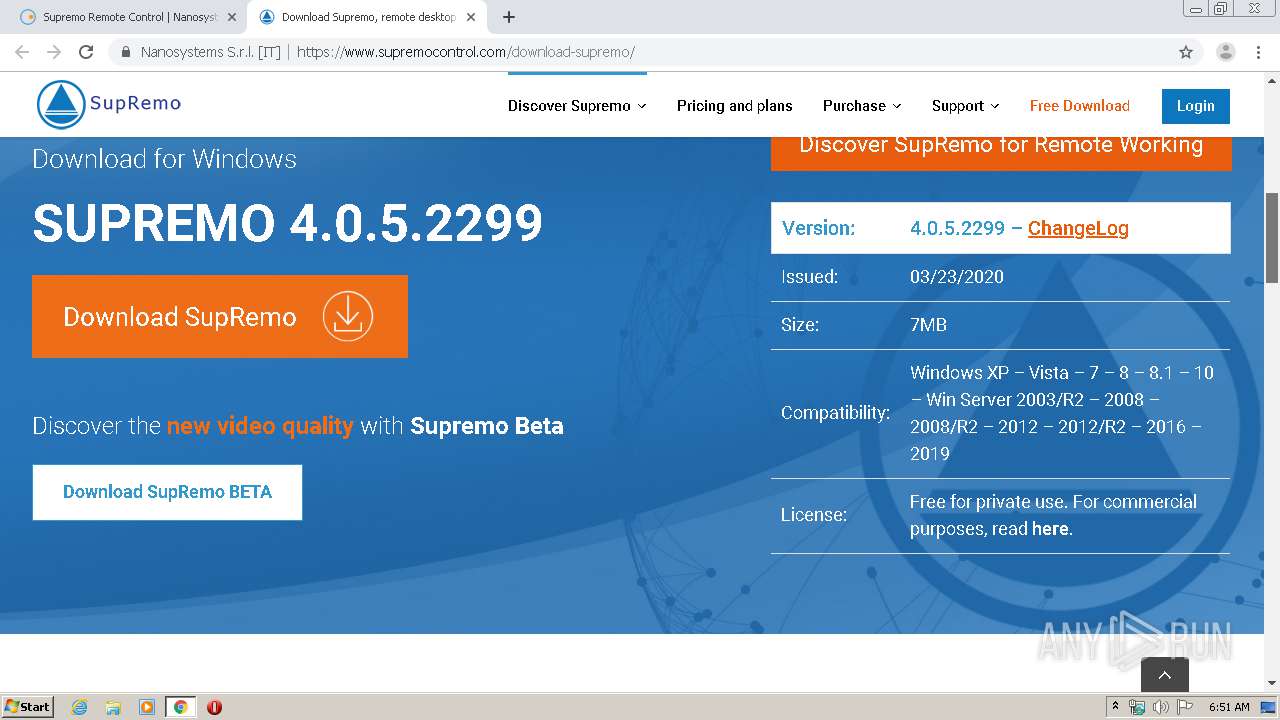
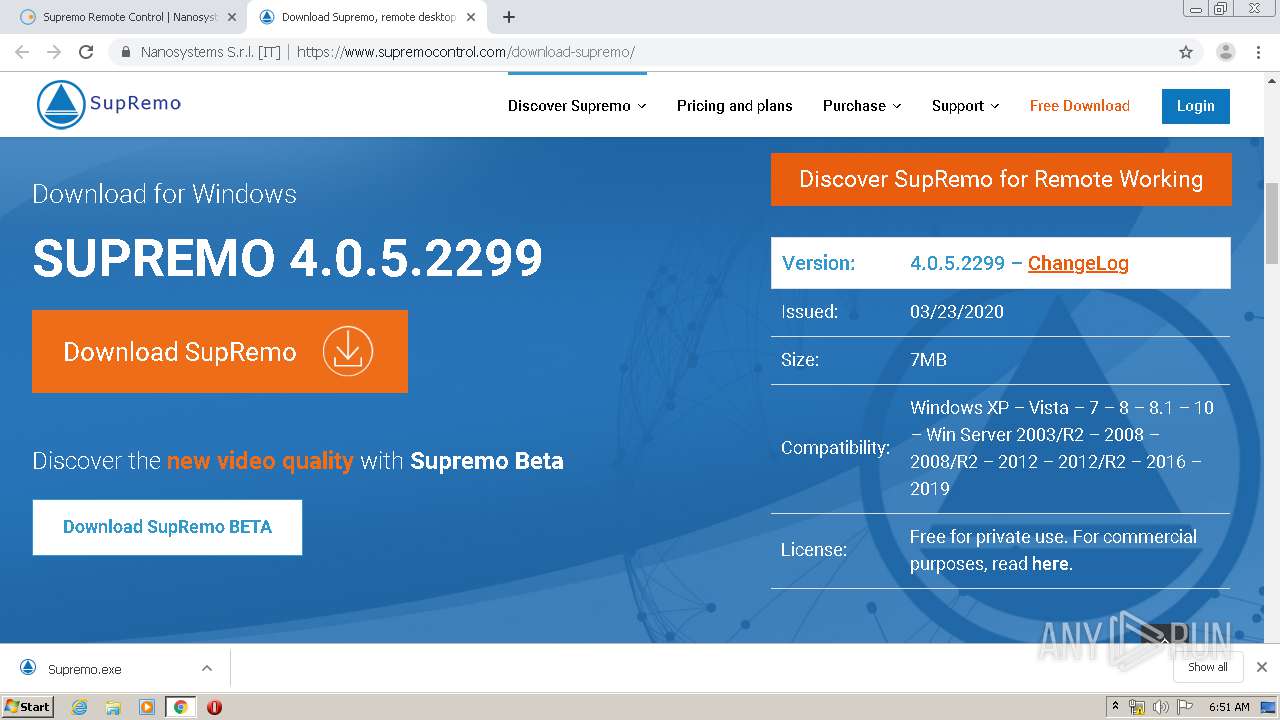
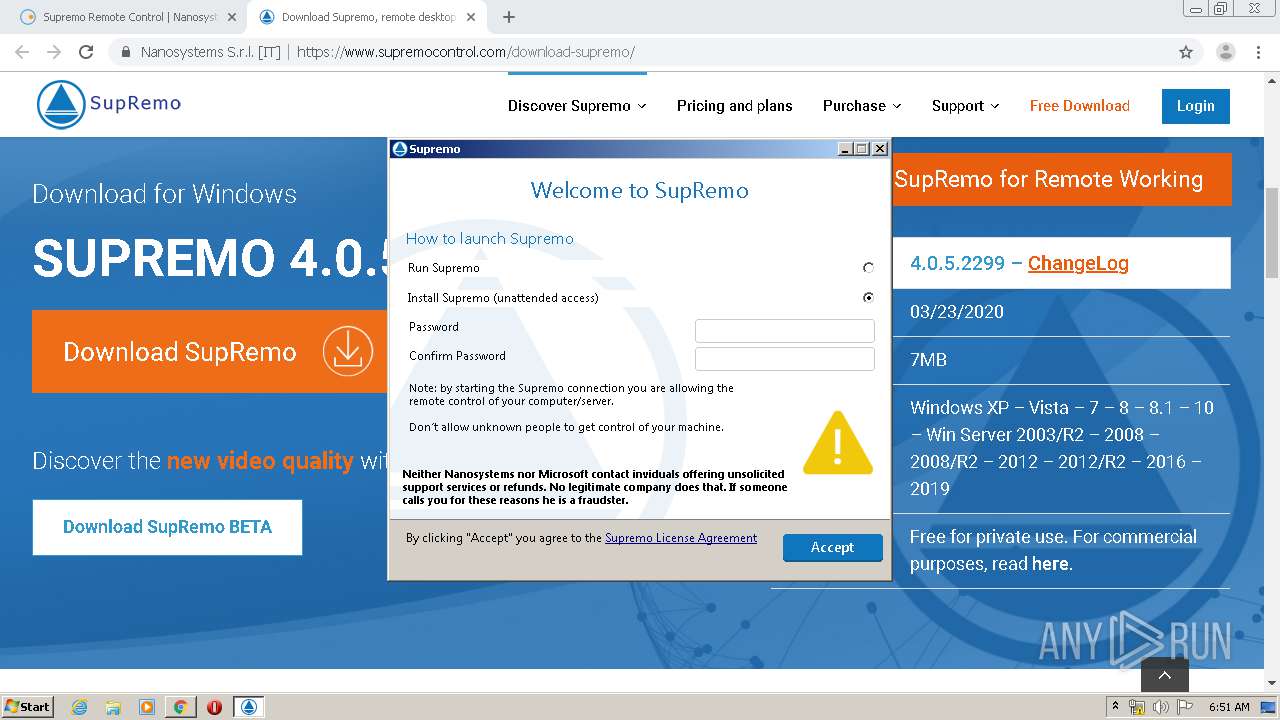
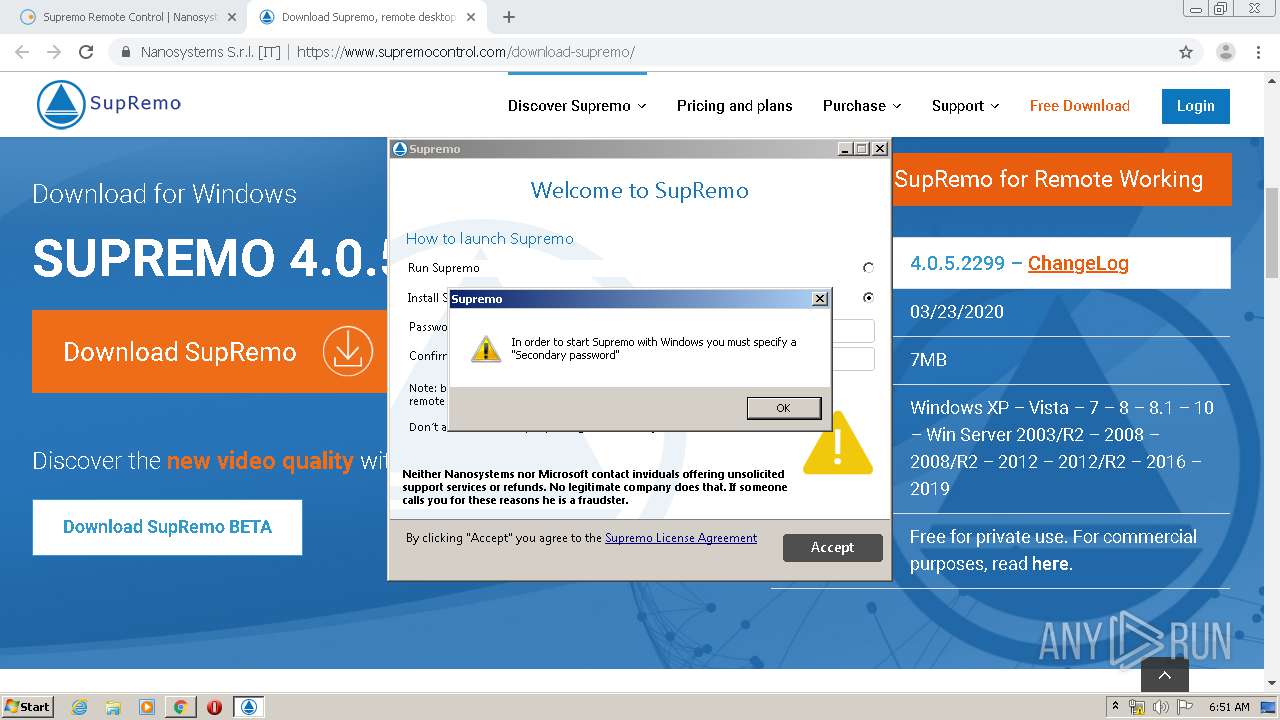
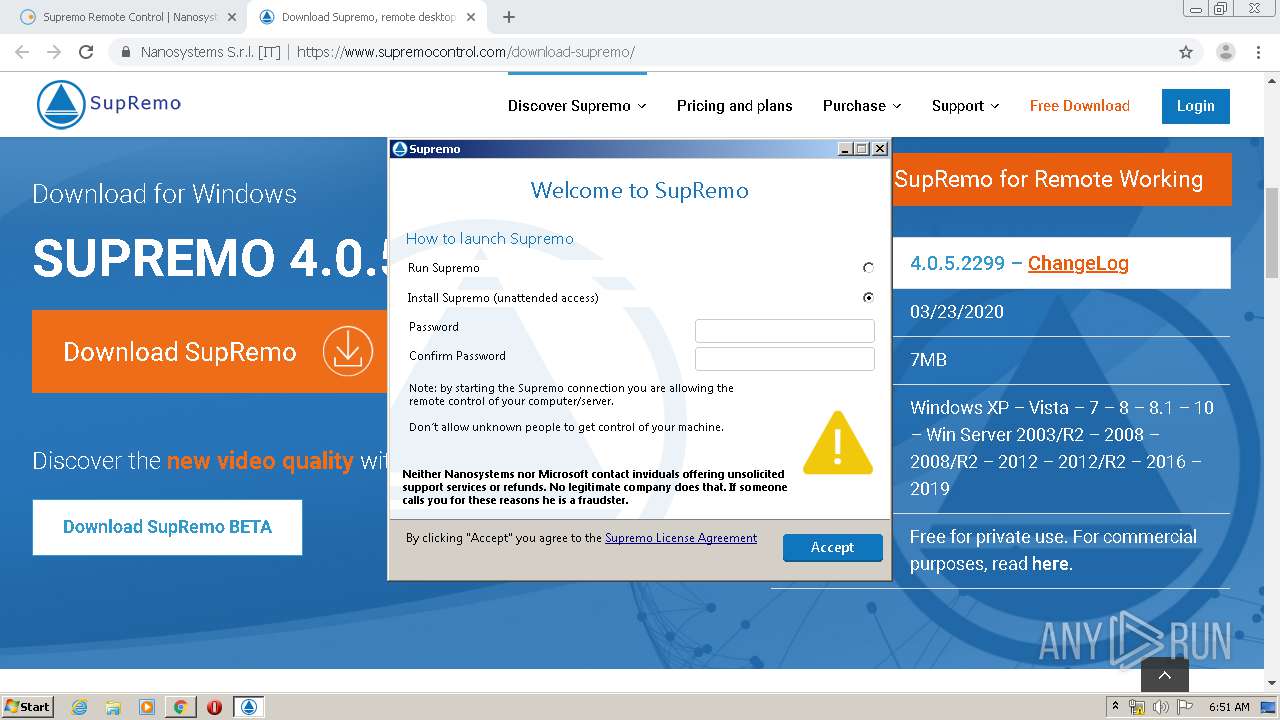
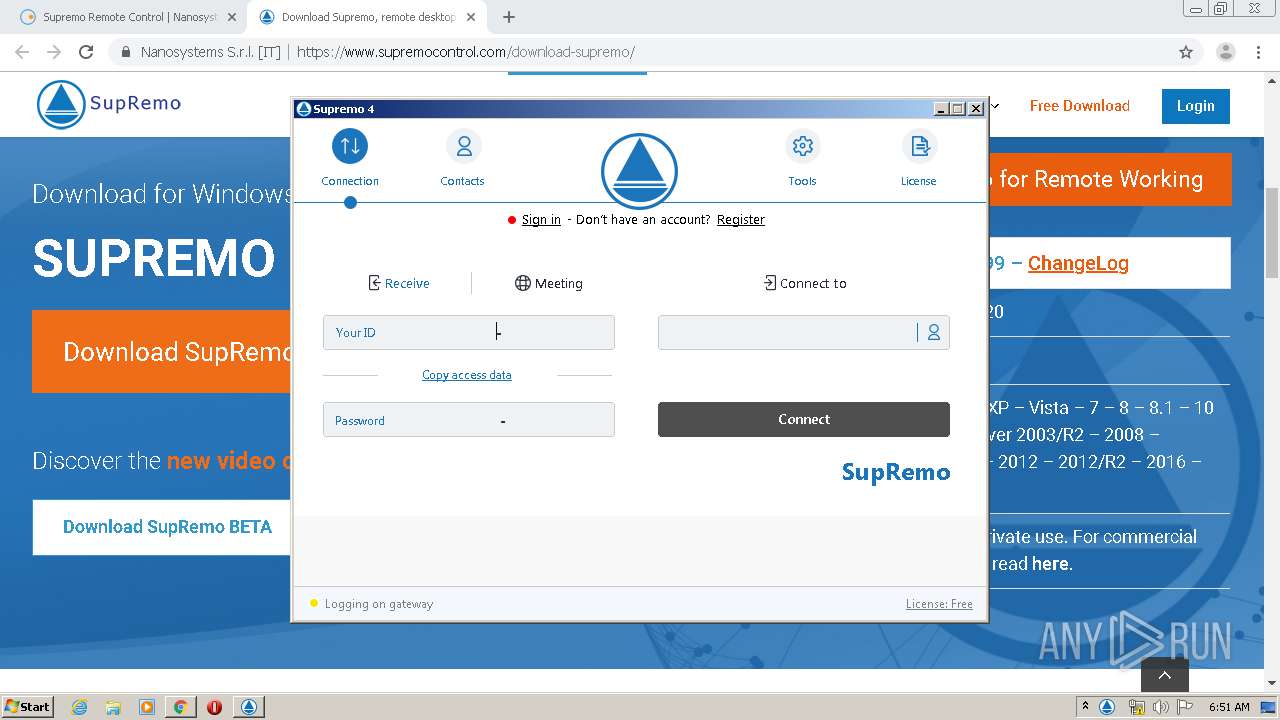
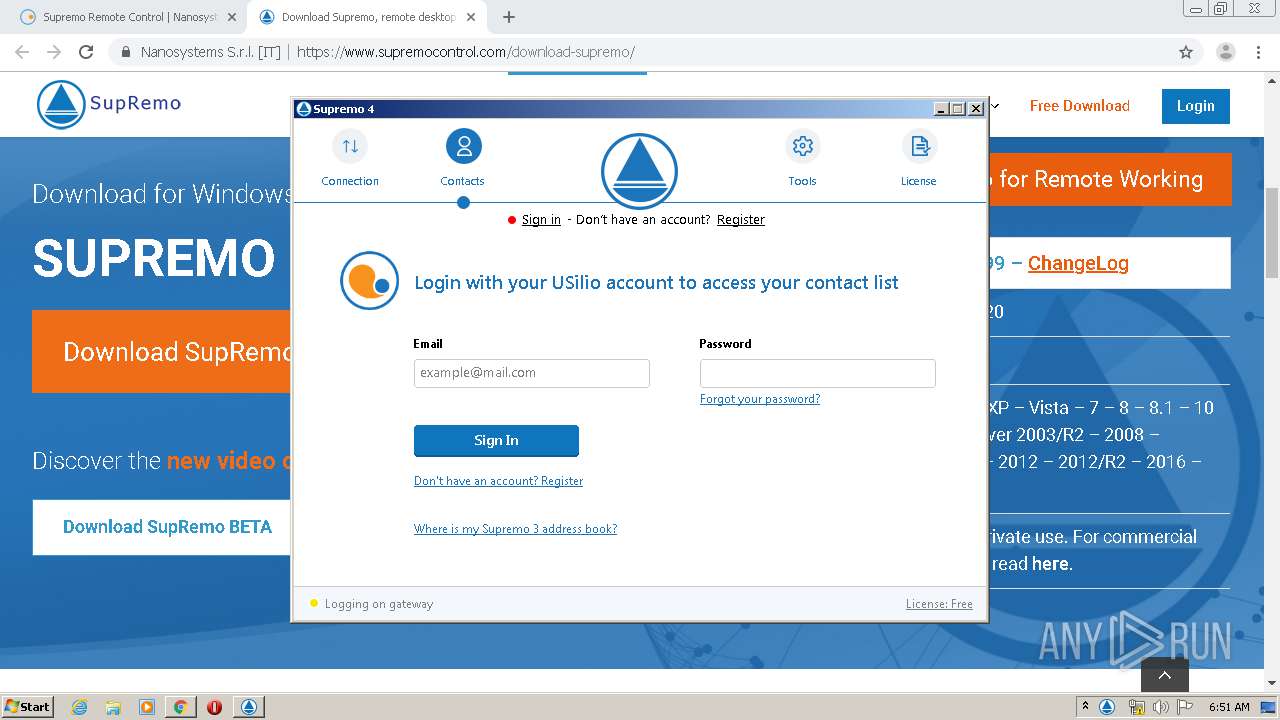
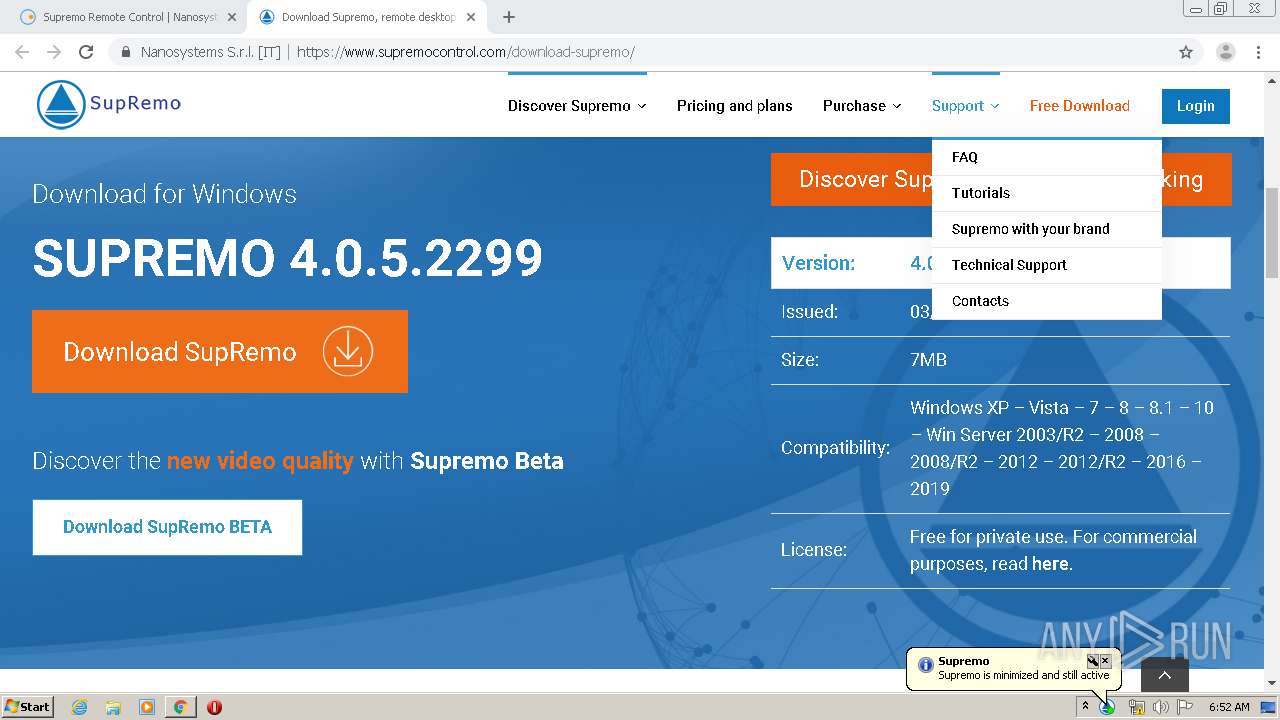
| URL: | https://www.nanosystems.it/supremo-remote-desktop/ |
| Full analysis: | https://app.any.run/tasks/63a82ed0-9799-4cbb-9329-e85f988448a6 |
| Verdict: | Malicious activity |
| Analysis date: | May 08, 2020, 05:50:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5FE46593EC0467E63B77184EC68A9E7F |
| SHA1: | 47F40699FB3515D7FCEA69B0C7EEA29568F04A7D |
| SHA256: | 4C51D893549B6FF73DFB063A0A832E66D21221164C68E5FF1191EB634EA4B2F0 |
| SSDEEP: | 3:N8DSLw+bHkgVQ4XAIKAIBzfKn:2OLwUFQ4Qh3fK |
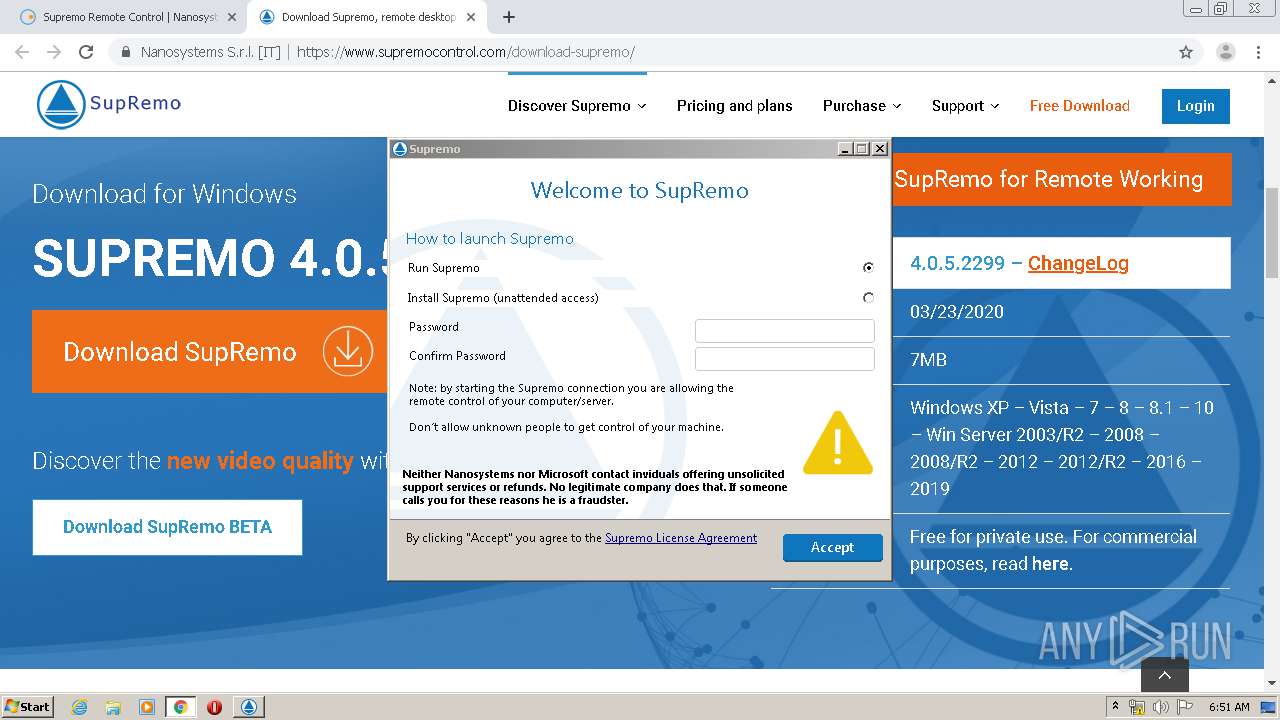
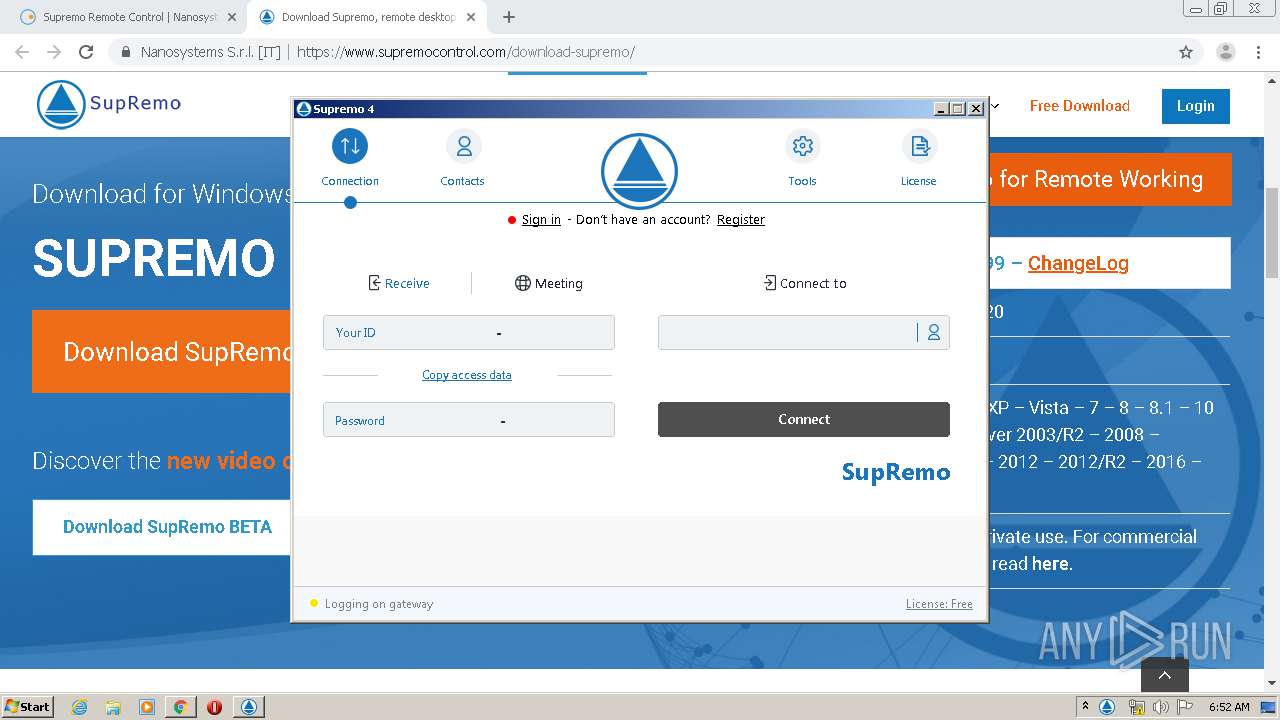
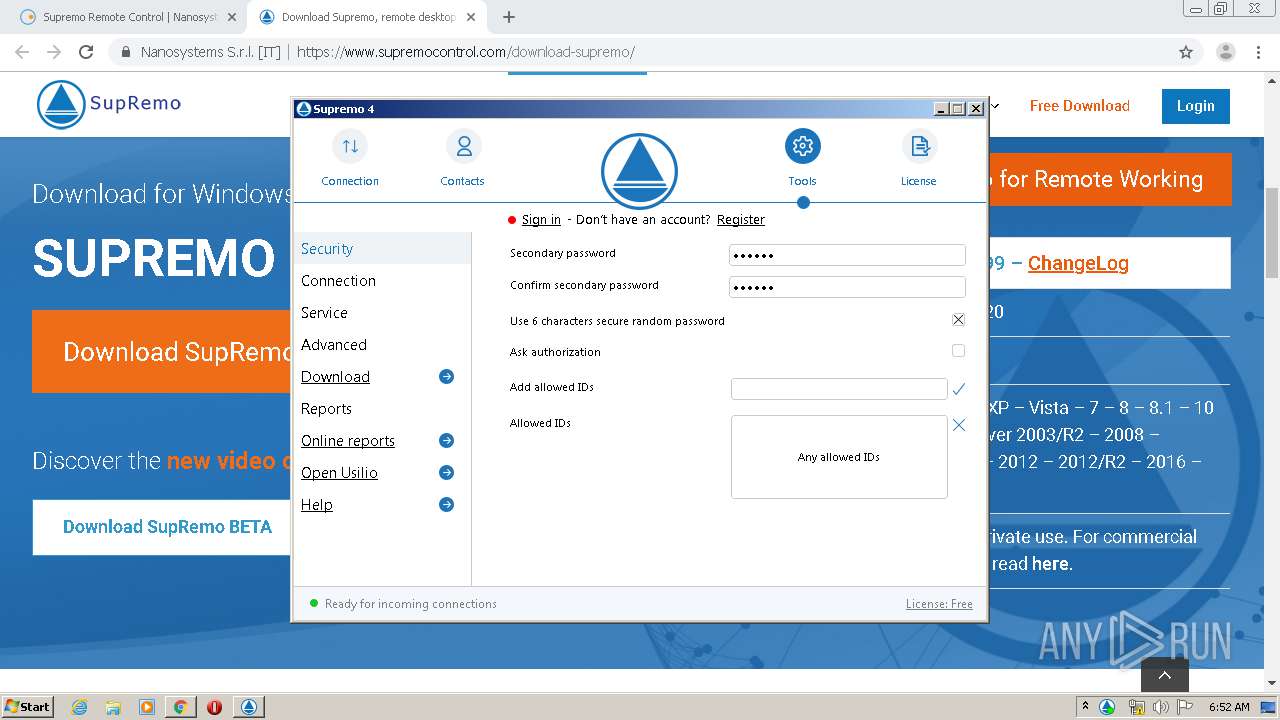
MALICIOUS
Application was dropped or rewritten from another process
- Supremo.exe (PID: 2392)
- SupremoSystem.exe (PID: 3344)
- SupremoHelper.exe (PID: 2964)
- Supremo.exe (PID: 2240)
- SupremoService.exe (PID: 1948)
- SupremoService.exe (PID: 3428)
- Supremo.exe (PID: 3460)
- SupremoSystem.exe (PID: 2348)
Starts NET.EXE for service management
- Supremo.exe (PID: 2240)
Changes settings of System certificates
- Supremo.exe (PID: 3460)
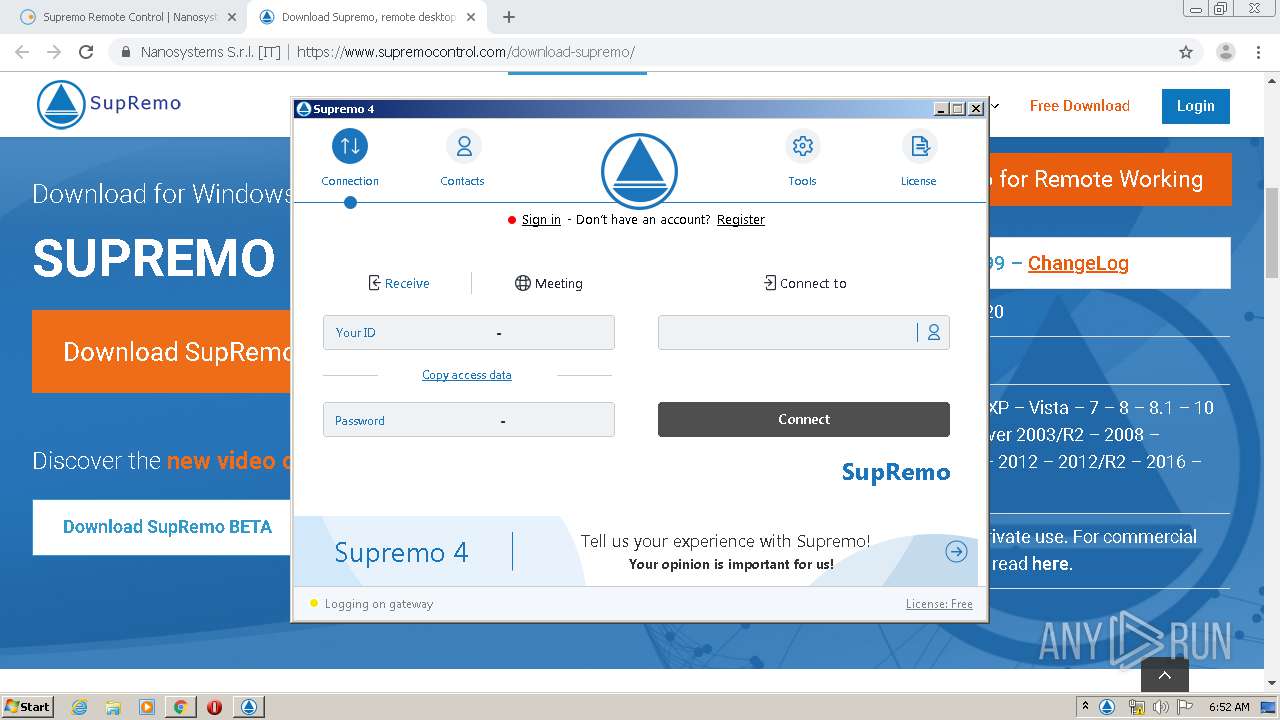
SUSPICIOUS
Creates files in the Windows directory
- Supremo.exe (PID: 3460)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1640)
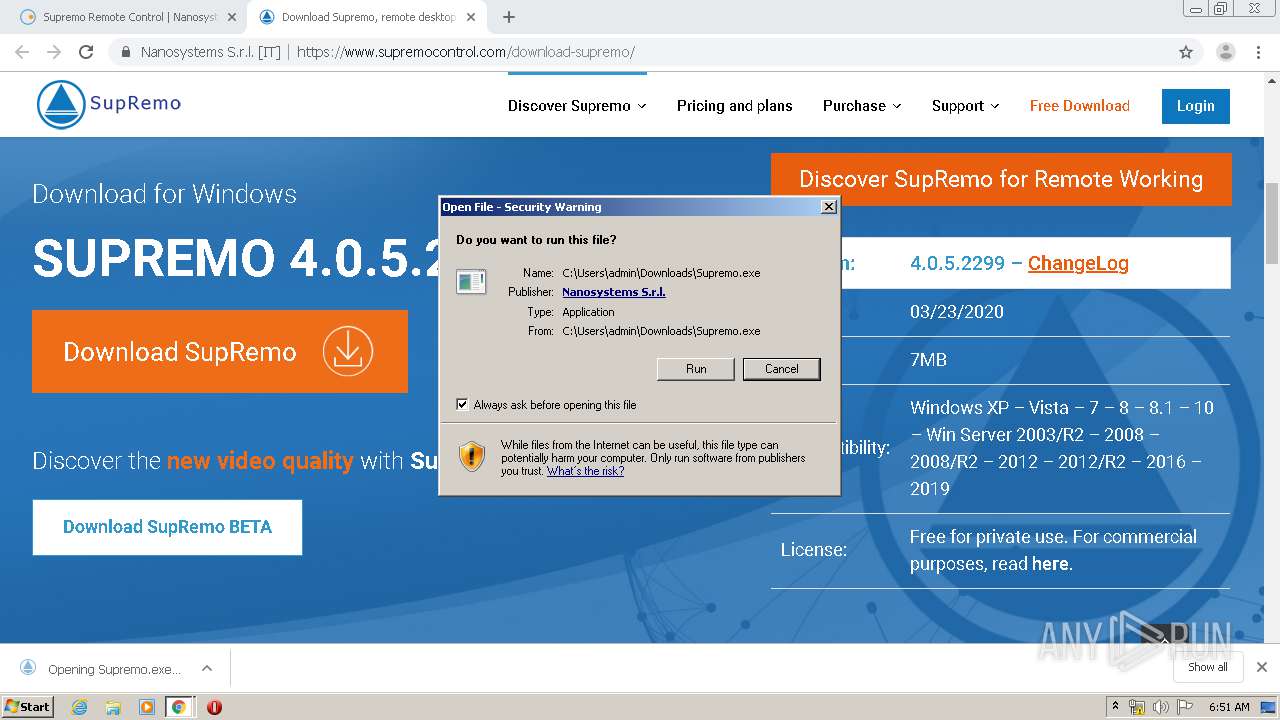
Executable content was dropped or overwritten
- chrome.exe (PID: 3220)
- Supremo.exe (PID: 2392)
- chrome.exe (PID: 1640)
- Supremo.exe (PID: 3460)
- Supremo.exe (PID: 2240)
Creates files in the program directory
- Supremo.exe (PID: 2392)
- Supremo.exe (PID: 2240)
- SupremoService.exe (PID: 3428)
- Supremo.exe (PID: 3460)
Application launched itself
- Supremo.exe (PID: 3460)
Executed as Windows Service
- SupremoService.exe (PID: 3428)
- SupremoSystem.exe (PID: 3344)
Removes files from Windows directory
- Supremo.exe (PID: 2240)
- Supremo.exe (PID: 3460)
Reads Windows Product ID
- Supremo.exe (PID: 3460)
Checks for external IP
- Supremo.exe (PID: 3460)
Adds / modifies Windows certificates
- Supremo.exe (PID: 3460)
Modifies the open verb of a shell class
- Supremo.exe (PID: 3460)
INFO
Reads the hosts file
- chrome.exe (PID: 1640)
- chrome.exe (PID: 3220)
Reads Internet Cache Settings
- chrome.exe (PID: 1640)
Reads settings of System Certificates
- chrome.exe (PID: 1640)
- chrome.exe (PID: 3220)
- Supremo.exe (PID: 3460)
Application launched itself
- chrome.exe (PID: 1640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
82
Monitored processes
37
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,14904994007432484404,17854045932524788532,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5905400601889168148 --mojo-platform-channel-handle=3944 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 528 | "C:\Windows\System32\net.exe" start SupremoService | C:\Windows\System32\net.exe | — | Supremo.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,14904994007432484404,17854045932524788532,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12262248436141591281 --mojo-platform-channel-handle=4324 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,14904994007432484404,17854045932524788532,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10288920280355602492 --mojo-platform-channel-handle=2680 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,14904994007432484404,17854045932524788532,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7177169691397248265 --mojo-platform-channel-handle=4656 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://www.nanosystems.it/supremo-remote-desktop/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,14904994007432484404,17854045932524788532,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3644429946918442109 --mojo-platform-channel-handle=4868 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,14904994007432484404,17854045932524788532,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18148227666662616341 --mojo-platform-channel-handle=4268 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Supremo\SupremoService.exe" /INSTALL /SILENT | C:\Program Files\Supremo\SupremoService.exe | — | Supremo.exe | |||||||||||
User: SYSTEM Company: Nanosystems S.r.l. Integrity Level: SYSTEM Description: Supremo Service Exit code: 0 Version: 4.0.5.2299 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,14904994007432484404,17854045932524788532,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6746156003815818994 --mojo-platform-channel-handle=4368 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 865
Read events
2 322
Write events
2 538
Delete events
5
Modification events
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1640-13233390615335125 |
Value: 259 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1640) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
8
Suspicious files
241
Text files
221
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EB4F317-668.pma | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\93bc5ad0-3cc6-48d9-be6c-f30043ed1bdd.tmp | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa8731b.TMP | text | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1640 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa874d1.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
50
DNS requests
31
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3220 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
3220 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
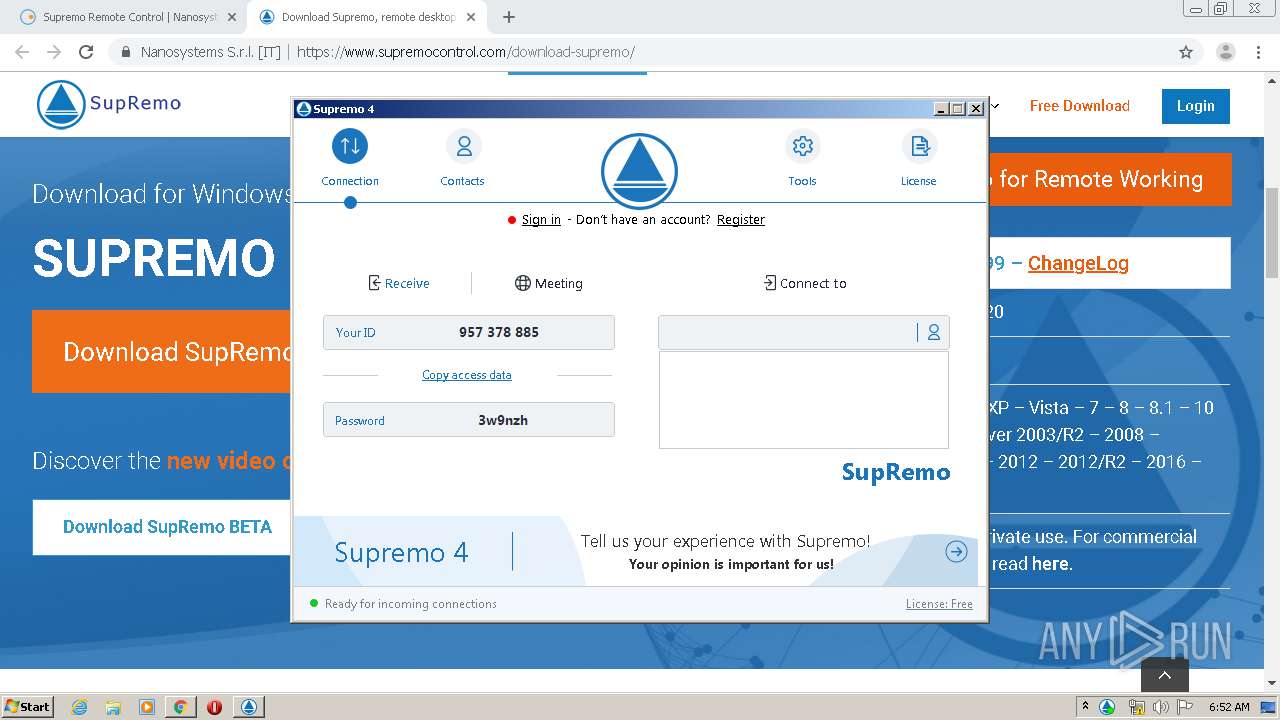
3460 | Supremo.exe | POST | 200 | 51.91.247.241:443 | http://supremogw98.nanosystems.it:443/$rdgate?ACTION=HELLO&ID=NEW | GB | binary | 27 b | suspicious |
3460 | Supremo.exe | POST | 200 | 51.91.247.241:443 | http://supremogw98.nanosystems.it:443/$rdgate?ID=E5EBE616F0C14AD8AD69960333820B5A | GB | binary | 15 b | suspicious |
3460 | Supremo.exe | POST | — | 51.91.82.26:80 | http://supremogw32.nanosystems.it/gatewaylist.php | GB | — | — | suspicious |
3220 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
3220 | chrome.exe | GET | 200 | 74.125.4.203:80 | http://r5---sn-aigzrner.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.192.69.144&mm=28&mn=sn-aigzrner&ms=nvh&mt=1588916962&mv=m&mvi=4&pl=25&shardbypass=yes | US | crx | 816 Kb | whitelisted |
3460 | Supremo.exe | POST | — | 51.91.247.241:443 | http://supremogw98.nanosystems.it:443/$rdgate?ID=E5EBE616F0C14AD8AD69960333820B5A | GB | — | — | suspicious |
3220 | chrome.exe | GET | 200 | 173.194.137.72:80 | http://r3---sn-aigzrn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.192.69.144&mm=28&mn=sn-aigzrn76&ms=nvh&mt=1588916962&mv=m&mvi=2&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3220 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEChOOcFLOG2InHKZ5YzQWlc%3D | US | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3220 | chrome.exe | 51.38.116.154:443 | www.nanosystems.it | — | GB | unknown |
3220 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
3220 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3220 | chrome.exe | 216.58.210.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3220 | chrome.exe | 173.194.76.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3220 | chrome.exe | 172.217.22.35:443 | www.google.co.uk | Google Inc. | US | whitelisted |
3220 | chrome.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3220 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3220 | chrome.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
3220 | chrome.exe | 216.58.206.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.nanosystems.it |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
www.google.com |
| malicious |
s.w.org |
| whitelisted |
ecommerce.nanosystems.it |
| unknown |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3460 | Supremo.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
3460 | Supremo.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
3460 | Supremo.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3460 | Supremo.exe | Misc activity | REMOTE [PTsecurity] Remote Desktop Service Activity |
3460 | Supremo.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3460 | Supremo.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3460 | Supremo.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2 ETPRO signatures available at the full report