| File name: | RealPlayer-20.1.0.313.exe |
| Full analysis: | https://app.any.run/tasks/e61302c4-91c4-4c7d-bae9-67072ef50ee0 |
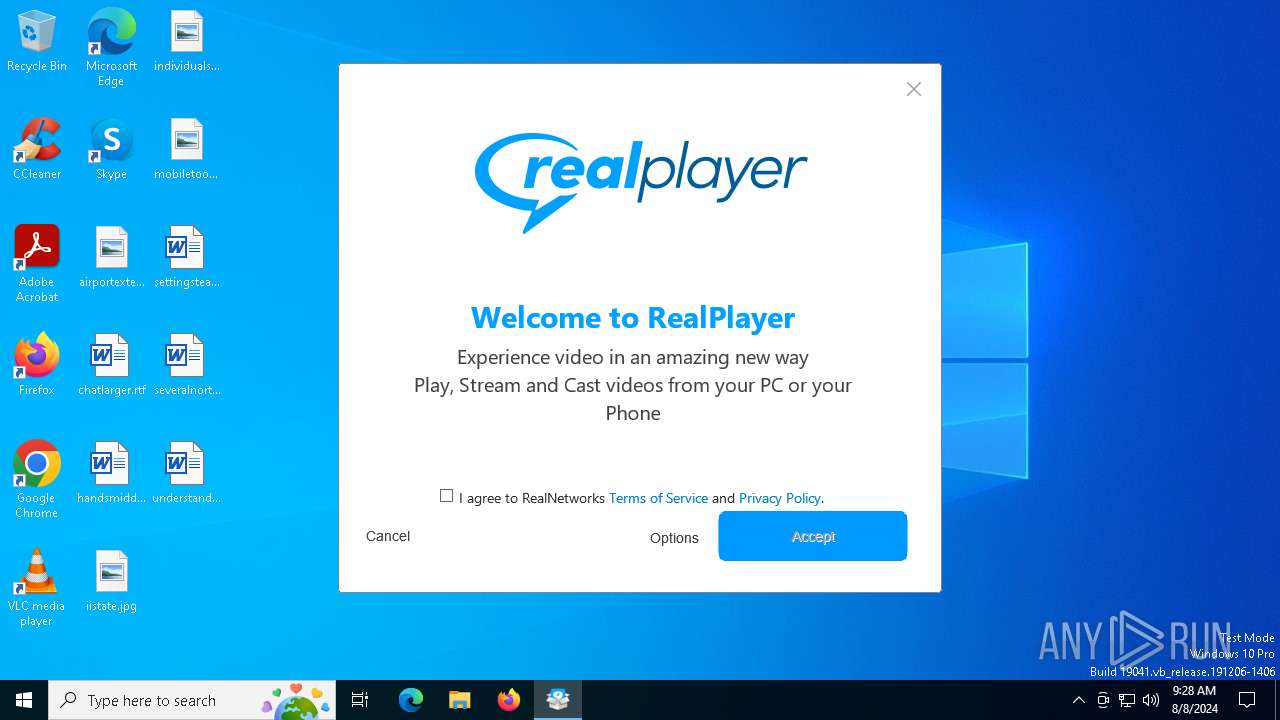
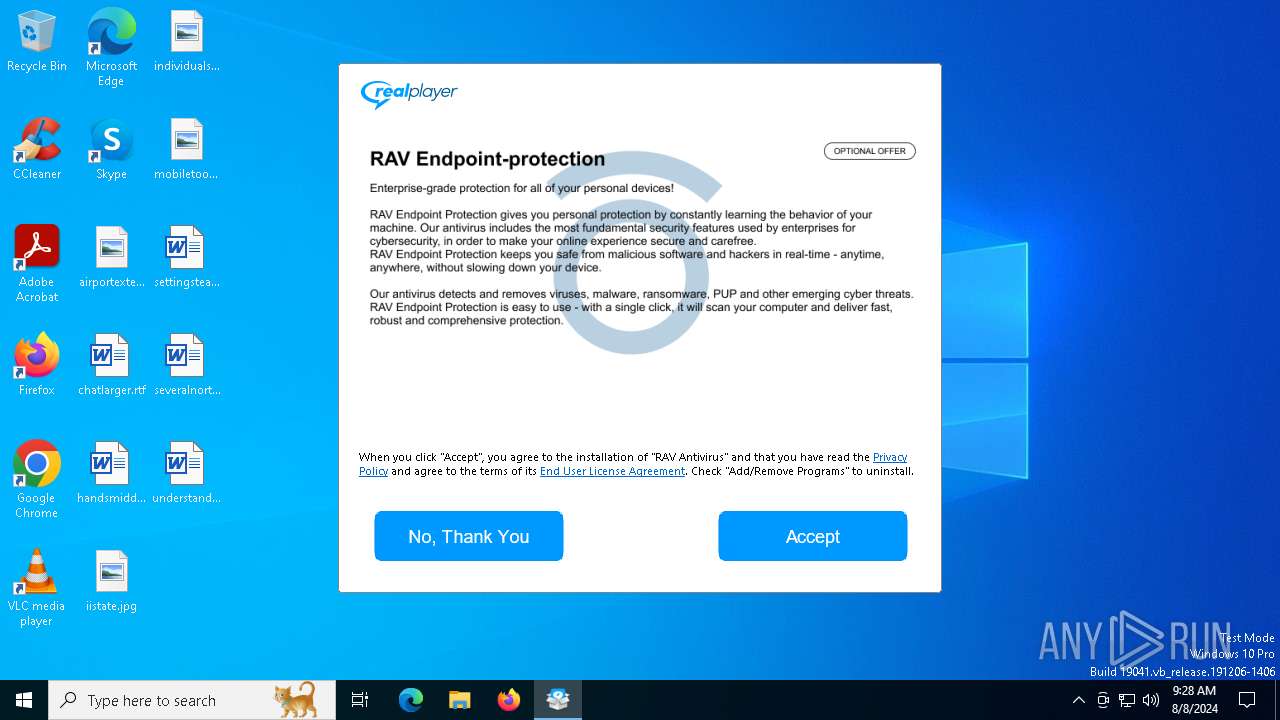
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
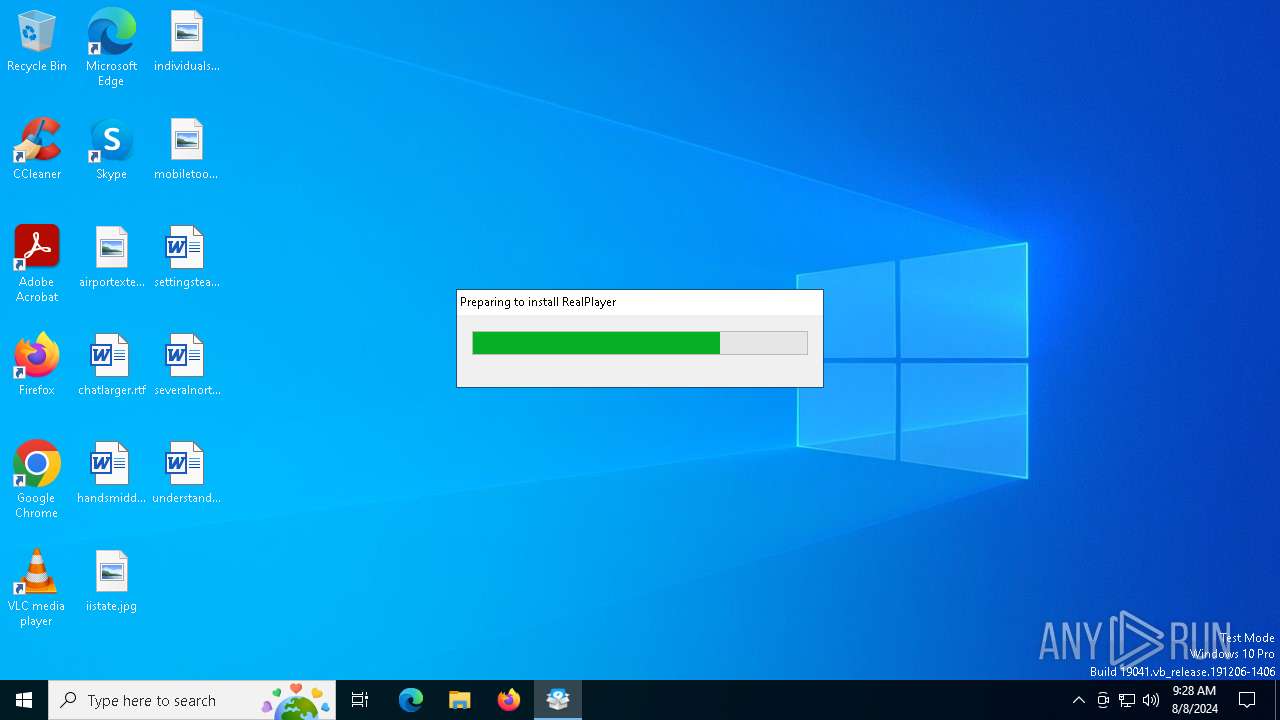
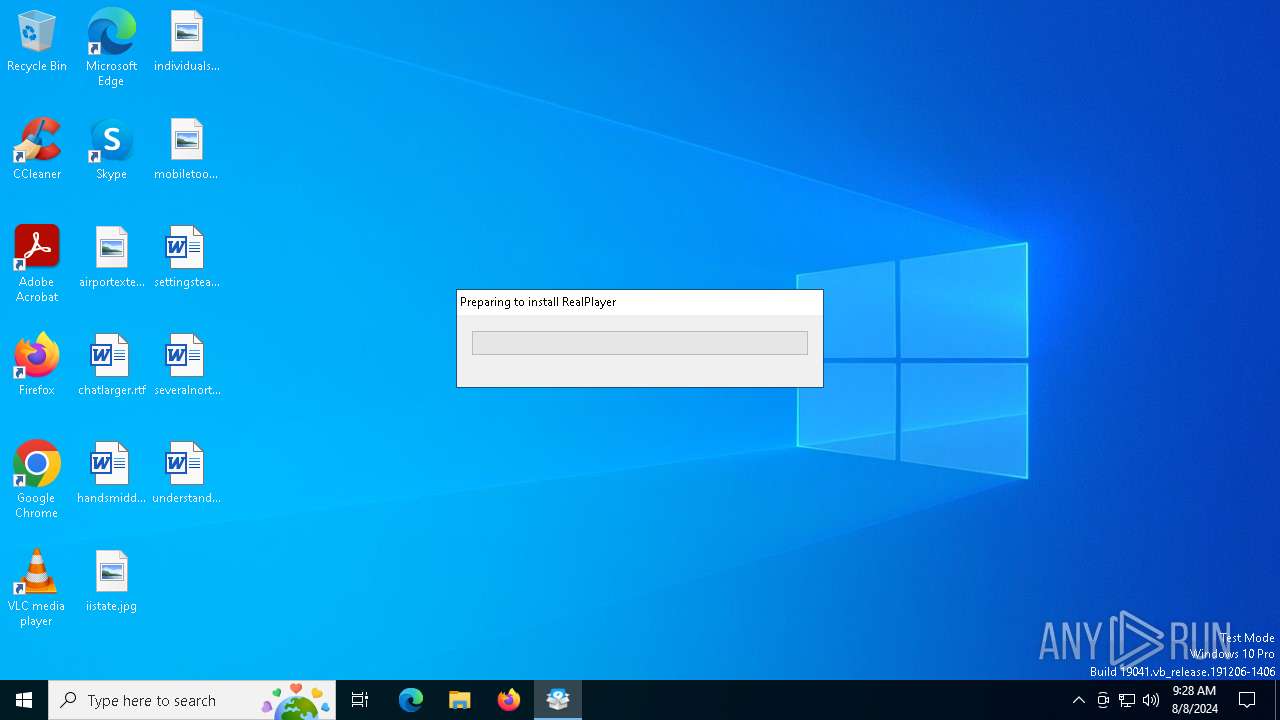
| Analysis date: | August 08, 2024, 09:28:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AC112ED34CFE0D7F99C05AE1F8CB985E |
| SHA1: | 01CCB7E9F4644DE2B2F4BECD72C8EF9A07D7CADF |
| SHA256: | 4C4A62B1232BCD651E7FE90797AD7D596F1891A6B6FEAAE891B17502F68C6E98 |
| SSDEEP: | 49152:PLbSZc0B9MyW1yA3HzfJvyBCUSGgXCqQjr:P/QLB9Mz1hzBSS |
MALICIOUS
Drops the executable file immediately after the start
- RealPlayer-20.1.0.313.exe (PID: 6380)
- rnsetup0.exe (PID: 6484)
- rnupdate0.exe (PID: 6612)
- rnsetup1.exe (PID: 6656)
- TiWorker.exe (PID: 3032)
- msiexec.exe (PID: 420)
- RealPlayer.exe (PID: 6260)
- MicrosoftEdgeWebview2Setup.exe (PID: 6864)
Steals credentials from Web Browsers
- RealPlayer.exe (PID: 6260)
- rnsetup1.exe (PID: 6656)
Changes the autorun value in the registry
- RealPlayer.exe (PID: 6260)
Registers / Runs the DLL via REGSVR32.EXE
- RealPlayer.exe (PID: 6260)
Scans artifacts that could help determine the target
- RealPlayer.exe (PID: 6260)
Actions looks like stealing of personal data
- rnsetup1.exe (PID: 6656)
SUSPICIOUS
Reads the date of Windows installation
- RealPlayer-20.1.0.313.exe (PID: 6380)
- rnupdate0.exe (PID: 6612)
- MicrosoftEdgeUpdate.exe (PID: 6316)
Executable content was dropped or overwritten
- RealPlayer-20.1.0.313.exe (PID: 6380)
- rnsetup0.exe (PID: 6484)
- rnupdate0.exe (PID: 6612)
- RealPlayer.exe (PID: 6260)
- TiWorker.exe (PID: 3032)
- rnsetup1.exe (PID: 6656)
- MicrosoftEdgeWebview2Setup.exe (PID: 6864)
Reads security settings of Internet Explorer
- RealPlayer-20.1.0.313.exe (PID: 6380)
- rnsetup0.exe (PID: 6484)
- rnupdate0.exe (PID: 6612)
- rnsetup1.exe (PID: 6656)
- RealPlayer.exe (PID: 6260)
- rpdsvc.exe (PID: 4084)
- MicrosoftEdgeUpdate.exe (PID: 6316)
- lowproc.exe (PID: 532)
- lowproc.exe (PID: 6412)
- lowproc.exe (PID: 6188)
Checks Windows Trust Settings
- rnsetup0.exe (PID: 6484)
- msiexec.exe (PID: 420)
- rnsetup1.exe (PID: 6656)
- RealPlayer.exe (PID: 6260)
Reads Microsoft Outlook installation path
- rnsetup1.exe (PID: 6656)
Process requests binary or script from the Internet
- rnsetup1.exe (PID: 6656)
Reads Internet Explorer settings
- rnsetup1.exe (PID: 6656)
Potential Corporate Privacy Violation
- rnsetup0.exe (PID: 6484)
The process creates files with name similar to system file names
- RealPlayer.exe (PID: 6260)
Process drops legitimate windows executable
- RealPlayer.exe (PID: 6260)
- msiexec.exe (PID: 420)
- TiWorker.exe (PID: 3032)
- MicrosoftEdgeWebview2Setup.exe (PID: 6864)
- MicrosoftEdgeUpdate.exe (PID: 6316)
The process drops C-runtime libraries
- RealPlayer.exe (PID: 6260)
- msiexec.exe (PID: 420)
- TiWorker.exe (PID: 3032)
Write to the desktop.ini file (may be used to cloak folders)
- RealPlayer.exe (PID: 6260)
Adds/modifies Windows certificates
- msiexec.exe (PID: 420)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 420)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 6452)
- RealPlayer.exe (PID: 6260)
- regsvr32.exe (PID: 5180)
Creates or modifies Windows services
- RealPlayer.exe (PID: 6260)
Executes as Windows Service
- rpdsvc.exe (PID: 4084)
- RealPlayerUpdateSvc.exe (PID: 4644)
Uses TASKKILL.EXE to kill process
- rpdsvc.exe (PID: 4084)
Creates a software uninstall entry
- RealPlayer.exe (PID: 6260)
- MicrosoftEdgeUpdate.exe (PID: 6316)
Changes Internet Explorer settings (feature browser emulation)
- RealPlayer.exe (PID: 6260)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 6864)
- MicrosoftEdgeUpdate.exe (PID: 6316)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 6316)
Searches for installed software
- RealPlayer.exe (PID: 6260)
Uses REG/REGEDIT.EXE to modify registry
- defenc.exe (PID: 1492)
Creates file in the systems drive root
- realplay_mountpoints.exe (PID: 5552)
The process checks if it is being run in the virtual environment
- rpdsvc.exe (PID: 4084)
INFO
Checks supported languages
- RealPlayer-20.1.0.313.exe (PID: 6380)
- rnsetup0.exe (PID: 6484)
- rnupdate0.exe (PID: 6612)
- rnsetup1.exe (PID: 6656)
- rndlp.exe (PID: 6932)
- RealPlayer.exe (PID: 6260)
- msiexec.exe (PID: 420)
- rpdsvc.exe (PID: 4084)
- MicrosoftEdgeWebview2Setup.exe (PID: 6864)
- MicrosoftEdgeUpdate.exe (PID: 6316)
- rplibcvtapp.exe (PID: 1536)
- rndevicedbbuilder.exe (PID: 4016)
- msiexec.exe (PID: 1860)
- msiexec.exe (PID: 6300)
- RealPlayerUpdateSvc.exe (PID: 4644)
- realplay_mountpoints.exe (PID: 5552)
- setreg.exe (PID: 6388)
- defenc.exe (PID: 1492)
- lowproc.exe (PID: 6188)
- lowproc.exe (PID: 6412)
- lowproc.exe (PID: 532)
Checks proxy server information
- rnsetup0.exe (PID: 6484)
- rnsetup1.exe (PID: 6656)
- rndlp.exe (PID: 6932)
- RealPlayer.exe (PID: 6260)
- MicrosoftEdgeUpdate.exe (PID: 6316)
- wermgr.exe (PID: 5484)
- lowproc.exe (PID: 6188)
- lowproc.exe (PID: 6412)
- lowproc.exe (PID: 532)
Reads the computer name
- RealPlayer-20.1.0.313.exe (PID: 6380)
- rnsetup0.exe (PID: 6484)
- rnupdate0.exe (PID: 6612)
- rnsetup1.exe (PID: 6656)
- rndlp.exe (PID: 6932)
- msiexec.exe (PID: 420)
- RealPlayer.exe (PID: 6260)
- rpdsvc.exe (PID: 4084)
- MicrosoftEdgeUpdate.exe (PID: 6316)
- RealPlayerUpdateSvc.exe (PID: 4644)
- msiexec.exe (PID: 6300)
- msiexec.exe (PID: 1860)
- lowproc.exe (PID: 6412)
- lowproc.exe (PID: 6188)
- lowproc.exe (PID: 532)
Creates files or folders in the user directory
- rnsetup0.exe (PID: 6484)
- rnsetup1.exe (PID: 6656)
- msiexec.exe (PID: 420)
- RealPlayer.exe (PID: 6260)
- realplay_mountpoints.exe (PID: 5552)
Create files in a temporary directory
- RealPlayer-20.1.0.313.exe (PID: 6380)
- rnsetup0.exe (PID: 6484)
- rnupdate0.exe (PID: 6612)
- rnsetup1.exe (PID: 6656)
- RealPlayer.exe (PID: 6260)
Reads the machine GUID from the registry
- rnsetup0.exe (PID: 6484)
- rndlp.exe (PID: 6932)
- msiexec.exe (PID: 420)
- RealPlayer.exe (PID: 6260)
- rnsetup1.exe (PID: 6656)
- RealPlayerUpdateSvc.exe (PID: 4644)
Process checks computer location settings
- RealPlayer-20.1.0.313.exe (PID: 6380)
- rnupdate0.exe (PID: 6612)
- MicrosoftEdgeUpdate.exe (PID: 6316)
Reads the software policy settings
- rnsetup0.exe (PID: 6484)
- rnsetup1.exe (PID: 6656)
- rndlp.exe (PID: 6932)
- msiexec.exe (PID: 420)
- RealPlayer.exe (PID: 6260)
- MicrosoftEdgeUpdate.exe (PID: 6316)
- wermgr.exe (PID: 5484)
Creates files in the program directory
- rnsetup0.exe (PID: 6484)
- RealPlayer.exe (PID: 6260)
- rpdsvc.exe (PID: 4084)
- MicrosoftEdgeWebview2Setup.exe (PID: 6864)
- msiexec.exe (PID: 6264)
- msiexec.exe (PID: 4844)
Reads Environment values
- rndlp.exe (PID: 6932)
- MicrosoftEdgeUpdate.exe (PID: 6316)
- rpdsvc.exe (PID: 4084)
Process checks Internet Explorer phishing filters
- rnsetup1.exe (PID: 6656)
Disables trace logs
- rndlp.exe (PID: 6932)
Executable content was dropped or overwritten
- msiexec.exe (PID: 420)
Creates a software uninstall entry
- msiexec.exe (PID: 420)
Reads CPU info
- rpdsvc.exe (PID: 4084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:04:20 17:28:22+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 59904 |
| InitializedDataSize: | 82944 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4504 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.6.0.9 |
| ProductVersionNumber: | 9.6.0.9 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | RealNetworks, Inc. |
| FileDescription: | RealNetworks Installer |
| InternalName: | RealNetworks Installer |
| ProductName: | RealNetworks Installer (32-bit) |
| OriginalFileName: | rnsetup.EXE |
| FileVersion: | 9.6.0.9 |
| ProductVersion: | 9.6.0.9 |
Total processes
178
Monitored processes
42
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 532 | C:\Users\admin\AppData\Local\Temp\lowproc.exe .real.com rntrack | C:\Users\admin\AppData\Local\Temp\lowproc.exe | — | rnsetup1.exe | |||||||||||
User: admin Company: RealNetworks, Inc. Integrity Level: LOW Description: RealNetworks Installer Exit code: 0 Version: 9.9.0.20 Modules
| |||||||||||||||
| 1492 | C:\Users\admin\AppData\Local\Temp\~rnsetup\defenc.exe ra8 | C:\Users\admin\AppData\Local\Temp\~rnsetup\defenc.exe | — | RealPlayer.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1524 | msiexec /x{E3AE96D6-E196-45B4-AF62-2B41998B9E37} /qn | C:\Windows\SysWOW64\msiexec.exe | — | RealPlayer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 1605 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1536 | C:\Users\admin\AppData\Local\Temp\~rnsetup\rplibcvtapp.exe | C:\Users\admin\AppData\Local\Temp\~rnsetup\rplibcvtapp.exe | — | RealPlayer.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1860 | C:\Windows\syswow64\MsiExec.exe -Embedding 057AB0BE3DE7B3C68C7431EFA0EE9AF4 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | CheckNetIsolation.exe loopbackexempt -a -n=e03e4889.realplayercloud_ntp9rbjg1j5m8 | C:\Windows\SysWOW64\CheckNetIsolation.exe | — | RealPlayer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: AppContainer Network Isolation Diagnostic Tool Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2508 | msiexec /i "C:\Users\admin\AppData\Local\Temp\~rnsetup\vc10_runtime.msi" /qn REBOOT=ReallySuppress ARPSYSTEMCOMPONENT=1 MSIFASTINSTALL=1 | C:\Windows\SysWOW64\msiexec.exe | — | RealPlayer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2584 | regedit.exe /s C:\Users\admin\AppData\Local\Temp\~rnsetup\defenc.reg | C:\Windows\SysWOW64\regedit.exe | — | defenc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3032 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
46 596
Read events
43 723
Write events
2 472
Delete events
401
Modification events
| (PID) Process: | (6380) RealPlayer-20.1.0.313.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6380) RealPlayer-20.1.0.313.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6380) RealPlayer-20.1.0.313.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6380) RealPlayer-20.1.0.313.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6484) rnsetup0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6484) rnsetup0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6484) rnsetup0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6484) rnsetup0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6484) rnsetup0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6484) rnsetup0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
1 072
Suspicious files
221
Text files
1 140
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6484 | rnsetup0.exe | C:\ProgramData\Real\RealPlayer\S-1-5-18 | text | |
MD5:59AD59954B3B912C669C189CC34A41A0 | SHA256:D76F36A7D044D3BDD661913279B8A4566DD90BF33E1550DB81DD9E7D1FE39348 | |||
| 6484 | rnsetup0.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_427CDB1C9AAC2BAE6B426DB11F126FA2 | binary | |
MD5:7DD0F5FC74881AFA48EA764279AE7799 | SHA256:01F94A7792E1EC99537E8095D8404A57E337921E03D7F19506BFBCE69EEBA987 | |||
| 6656 | rnsetup1.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\log[1].txt | text | |
MD5:5751D1AAFDB7375CBD1BB221E286CEBA | SHA256:5BC8F416A15291783D353DA675B9283C4E06E547D9FD93F89F1962FCB9CCF431 | |||
| 6484 | rnsetup0.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\geoloc[1].json | text | |
MD5:4DF8151CC172CB00A338DF17A6F27786 | SHA256:289080EF47149AC71A70D3BAE0CAA652A117F4B94568AF16703DA8B5BA8BABB2 | |||
| 6484 | rnsetup0.exe | C:\Users\admin\AppData\Local\Temp\rnupdate0.exe | executable | |
MD5:7F5CF0D405E7994E0FF2E9FE6848EC33 | SHA256:02B2FC60F7AF0ADD3FED50605CD4B6E8CC52C61828AF25B68B1E35BBAED84456 | |||
| 6484 | rnsetup0.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\250291F3FA7935E360EA9925CBAB58AC_FA3BD2DF95502FE1C0337EE85ED4A2DC | binary | |
MD5:F149A75A0BDC028E8AA85DC63422B597 | SHA256:0ABD95EA8C5ACDF38A8858BD841F15AA8A510AE1D0558E9EC8EA46B0799B46F6 | |||
| 6656 | rnsetup1.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\geoloc[1].json | text | |
MD5:24B73F56B033B02C1DFE4EF98DF22DBC | SHA256:44AB0E60F16DDD6F3DFBCA1A15B2D80C19A2217301E0A522231F661EB0E4CFCB | |||
| 6484 | rnsetup0.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\RealPlayer[1].exe | executable | |
MD5:7F5CF0D405E7994E0FF2E9FE6848EC33 | SHA256:02B2FC60F7AF0ADD3FED50605CD4B6E8CC52C61828AF25B68B1E35BBAED84456 | |||
| 6380 | RealPlayer-20.1.0.313.exe | C:\Users\admin\AppData\Local\Temp\rnsetup0.exe | executable | |
MD5:122902EBA56CEBF6BE2295D4D7383872 | SHA256:D3B3E8EF291C070D7FCD99096746B53E08F40262D5ED4920DCBBC829AD91088F | |||
| 6656 | rnsetup1.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\stubinst_config_en[1].xml | xml | |
MD5:0C2C2A91EAEF593592CDFA3C38C0CC4E | SHA256:9F378007F1B9B1FC16BD97C36FA2609D21DD5E820649B6157E0B3AD1AACAD0FE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
69
DNS requests
27
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6484 | rnsetup0.exe | GET | 200 | 152.199.20.39:80 | http://log.realone.com/rpinst/log.txt?action=uhcom&value=stubstarted_standalone&prod=stub&version=9.6.0.9&distcode=T20END01&sessionid=1392898280&loc=none®ion=&userid=6ba087569423431d8a35ace46a60b172&sysid=cb8758267cec4245a2145477c366930b&stampcode=T20END01&payload=RealPlayer&li=en&os=10.0.19045|SP0|en&ie=11.00.19041.1&origcode=&overcode=&xml_id=&pkg_id= | unknown | — | — | whitelisted |
6484 | rnsetup0.exe | GET | 200 | 152.199.20.39:80 | http://log.realone.com/rpinst/log.txt?action=installerstarted&value=normal&procid=Intel(R)Core(TM)i5-6400CPU@2.70GHz&gpuid=MicrosoftBasicDisplayAdapter&dotnetver=2.0.50727|3.0|3.5|4&exename="realplayer-20.1.0.313.exe"&webuserid=&prod=stub&version=9.6.0.9&distcode=T20END01&sessionid=1392898280&loc=none®ion=&userid=6ba087569423431d8a35ace46a60b172&sysid=cb8758267cec4245a2145477c366930b&stampcode=T20END01&payload=RealPlayer&li=en&os=10.0.19045|SP0|en&ie=11.00.19041.1&origcode=&overcode=&xml_id=&pkg_id= | unknown | — | — | whitelisted |
6484 | rnsetup0.exe | GET | 302 | 44.224.153.250:80 | http://switchboard.real.com/geoloc/index.html | unknown | — | — | whitelisted |
6484 | rnsetup0.exe | GET | 200 | 192.229.221.95:80 | http://status.thawte.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRzhKfQYsAHQZZDzb8RtQ5PgsTjQQQUpYz%2BMszrDyzUGcYIuAAkiF3DxbcCEA%2B3DW7YSEAe4KIvzn97thk%3D | unknown | — | — | whitelisted |
6484 | rnsetup0.exe | GET | 302 | 44.224.153.250:80 | http://switchboard.real.com/player/installer.html?cd=stub_update&prod=RealPlayer&ver=20.1&distcode=T20END01&sessionid=1392898280&loc=de®ion=he&stampcode=T20END01&li=en&os=10.0.19045|SP0|en&oem=rp20_en_us | unknown | — | — | whitelisted |
6484 | rnsetup0.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAkO6MXeW%2Fpi0q4v9wl8SFc%3D | unknown | — | — | whitelisted |
6484 | rnsetup0.exe | GET | 200 | 152.199.20.39:80 | http://cache-download.real.com/free/windows/installer/stubinst/xml/rp20/stubinst_config_en.xml?prod=RealPlayer&ver=20.1&distcode=T20END01&sessionid=1392898280&loc=de®ion=he&stampcode=T20END01&li=en&os=10.0.19045|SP0|en&oem=rp20_en_us | unknown | — | — | whitelisted |
6656 | rnsetup1.exe | GET | 200 | 152.199.20.39:80 | http://cache-download.real.com/free/windows/installer/stubinst/xml/rp24/stubinst_config_en.xml?prod=RealPlayer&ver=24.0&distcode=T24ENGAR&sessionid=1423346885&loc=de®ion=he&stampcode=T24ENGAR&li=en&os=10.0.19045|SP0|en&oem=rp24_en_us | unknown | — | — | whitelisted |
6656 | rnsetup1.exe | GET | 200 | 152.199.20.39:80 | http://log.realone.com/rpinst/log.txt?action=preEula&prod=stub&version=9.9.0.11&distcode=T24ENGAR&sessionid=1423346885&seq=4&loc=de®ion=he&userid=6ba087569423431d8a35ace46a60b172&sysid=cb8758267cec4245a2145477c366930b&stampcode=T24ENGAR&payload=RealPlayer&li=en&os=10.0.19045|SP0|en&ie=11.00.19041.1&origcode=&overcode=&xml_id=06272024122744&pkg_id=9.9.0.20&oldcode=t20end01&install_version=24.0.0.311&rcodechr=2&rcodegtb=4&rcodepid=0&rcodense=-999&rcodenss=-999&rcodereactgc=0&rcoderise=0&rcoderp=0&rcodewzip32=-1&rcodewzip64=0&page_wzip32_wzip32country=1&page_wzip64_wzip64country=1 | unknown | — | — | whitelisted |
6656 | rnsetup1.exe | GET | 200 | 152.199.20.39:80 | http://log.realone.com/rpinst/log.txt?action=uhcom&value=stubstarted_standalone&prod=stub&version=9.9.0.11&distcode=T24ENGAR&sessionid=1423346885&seq=1&loc=none®ion=&userid=6ba087569423431d8a35ace46a60b172&sysid=cb8758267cec4245a2145477c366930b&stampcode=T24ENGAR&payload=RealPlayer&li=en&os=10.0.19045|SP0|en&ie=11.00.19041.1&origcode=&overcode=&xml_id=&pkg_id=&oldcode=t20end01 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4576 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6080 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6484 | rnsetup0.exe | 152.199.20.39:80 | log.realone.com | EDGECAST | US | unknown |
6484 | rnsetup0.exe | 44.224.153.250:80 | switchboard.real.com | AMAZON-02 | US | unknown |
6484 | rnsetup0.exe | 34.217.184.5:443 | peoplesearch.real.com | AMAZON-02 | US | unknown |
6484 | rnsetup0.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6656 | rnsetup1.exe | 152.199.20.39:80 | log.realone.com | EDGECAST | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
log.realone.com |
| whitelisted |
switchboard.real.com |
| whitelisted |
peoplesearch.real.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.thawte.com |
| whitelisted |
cache-download.real.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
d367d5hazt3s7q.cloudfront.net |
| whitelisted |
d1tai3ahgv7amc.cloudfront.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6484 | rnsetup0.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6484 | rnsetup0.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
Process | Message |
|---|---|
RealPlayer.exe | xsetapp CreateProcess: ' |
RealPlayer.exe | msiexec /fvomus "C:\Users\admin\AppData\Local\Temp\~rnsetup\vs2015x86_redist.msi" /qn REBOOT=ReallySuppress ARPSYSTEMCOMPONENT=1 MSIFASTINSTALL=1 |
RealPlayer.exe | '
|
RealPlayer.exe | xsetapp CreateProcess: ' |
RealPlayer.exe | msiexec /i "C:\Users\admin\AppData\Local\Temp\~rnsetup\vs2015x86_redist.msi" /qn REBOOT=ReallySuppress ARPSYSTEMCOMPONENT=1 MSIFASTINSTALL=1 |
RealPlayer.exe | '
|
RealPlayer.exe | Creating process: 'C:\Users\admin\AppData\Local\Temp\~rnsetup\MicrosoftEdgeWebview2Setup.exe /silent /install'
|
RealPlayer.exe | process exit code -2147219704 (C:\Users\admin\AppData\Local\Temp\~rnsetup\MicrosoftEdgeWebview2Setup.exe /silent /install)
|
RealPlayer.exe | Creating process: 'C:\Users\admin\AppData\Local\Temp\~rnsetup\rplibcvtapp.exe'
|
RealPlayer.exe | process exit code 0 (C:\Users\admin\AppData\Local\Temp\~rnsetup\rplibcvtapp.exe)
|