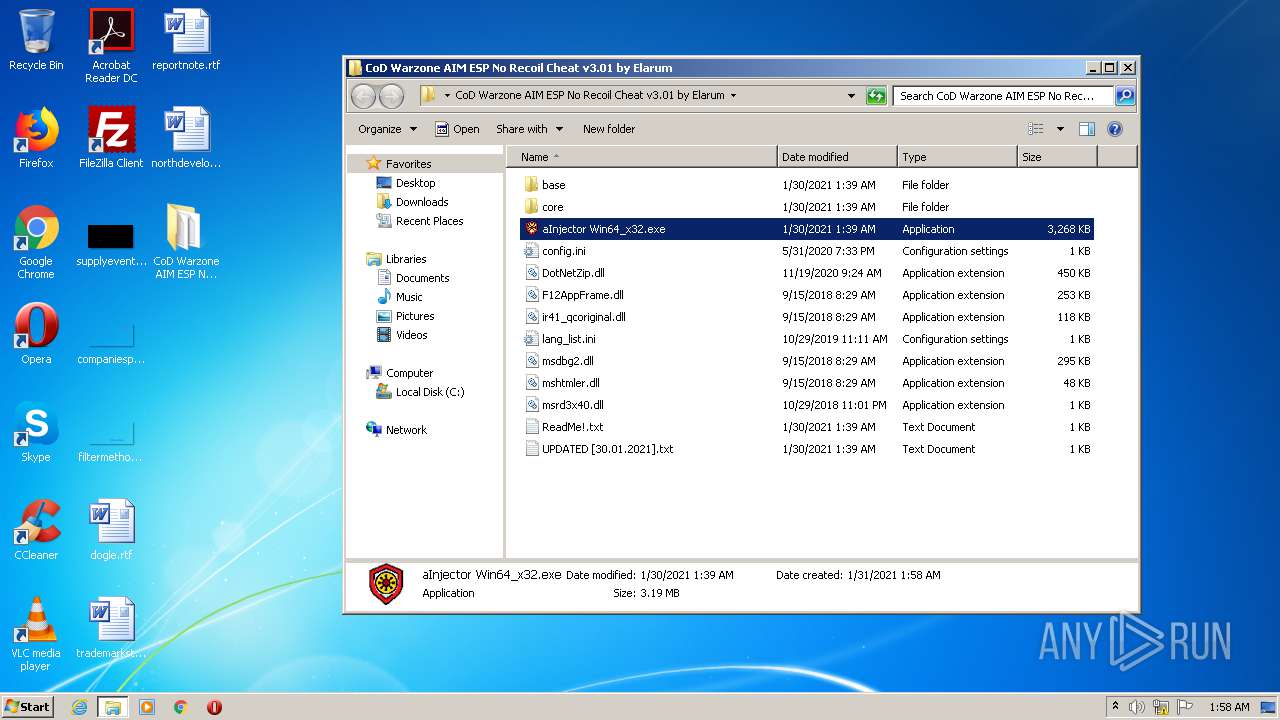
| File name: | CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum.zip |
| Full analysis: | https://app.any.run/tasks/64a4bbca-f16e-4e76-a9cc-918a5840edba |
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2021, 01:58:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4325A13F8D7EEC89D24DDF495AF512B5 |
| SHA1: | 75707F949BA1CFEB8DFF6A74F496DE42F2B69639 |
| SHA256: | 4C496D62F7550AB452E7A35636A505E4B65F455A9D42950B5E6133B88BF4886A |
| SSDEEP: | 98304:RfYpcLWSy78kiNXAuF7ASjUOB8NGjM7eyeVm2misrZJHyl:R2cK/6NXAu+SjUO07ey1f3dJSl |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3548)
Application was dropped or rewritten from another process
- aInjector Win64_x32.exe (PID: 3448)
- aInjector Win64_x32.exe (PID: 1896)
- aInjector Win64_x32.exe (PID: 4004)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 996)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 996)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 996)
Drops a file with too old compile date
- WinRAR.exe (PID: 996)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 996)
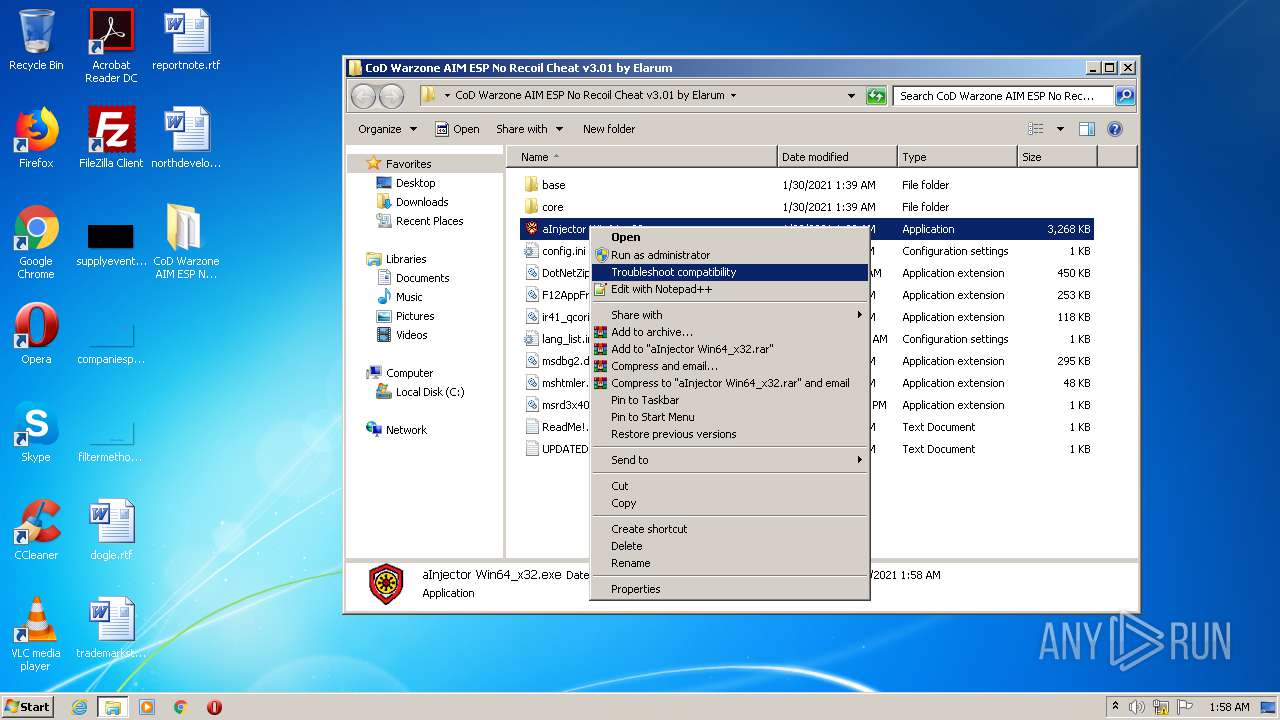
Manual execution by user
- aInjector Win64_x32.exe (PID: 1896)
- aInjector Win64_x32.exe (PID: 3448)
- aInjector Win64_x32.exe (PID: 4004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:01:30 03:39:27 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
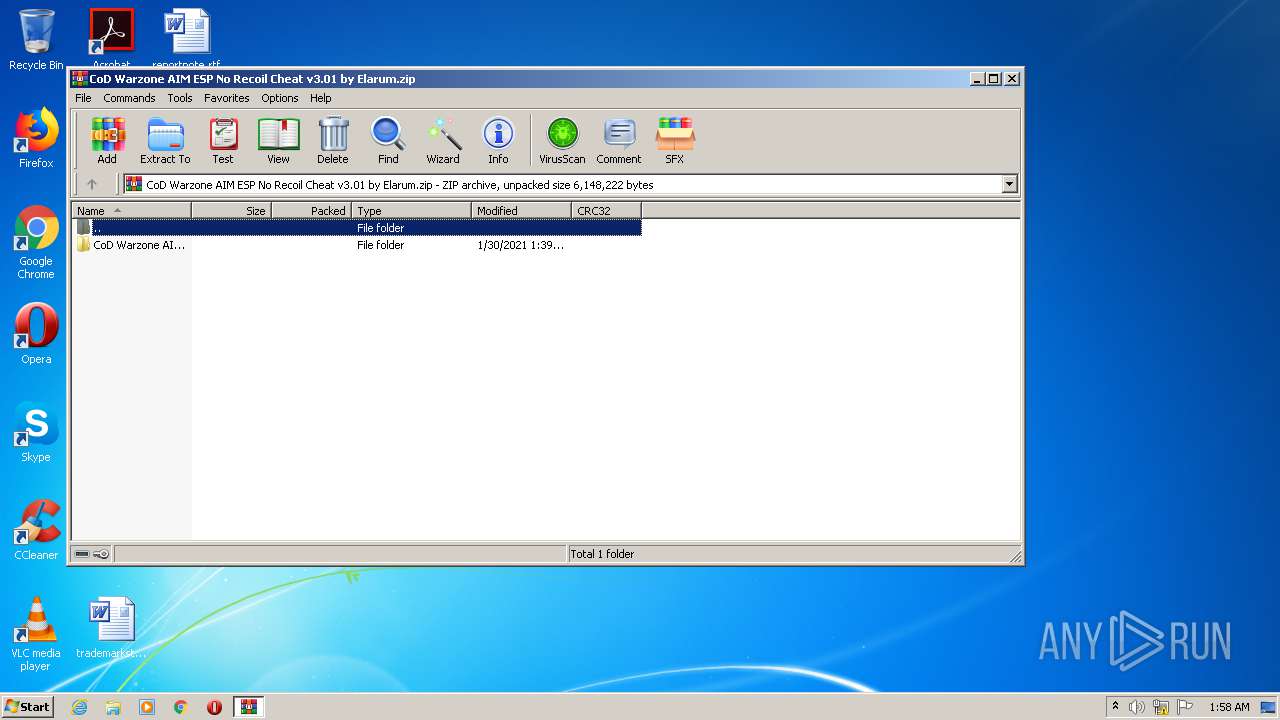
| ZipFileName: | CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum/ |
Total processes
44
Monitored processes
5
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
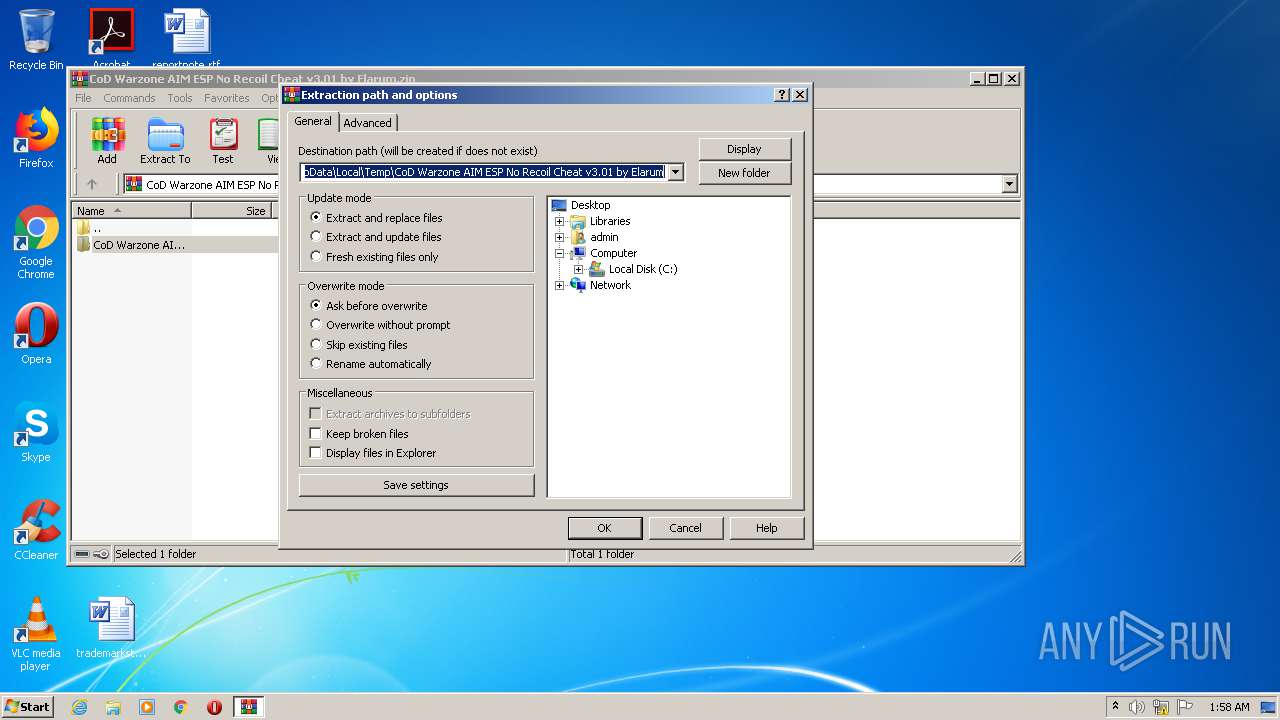
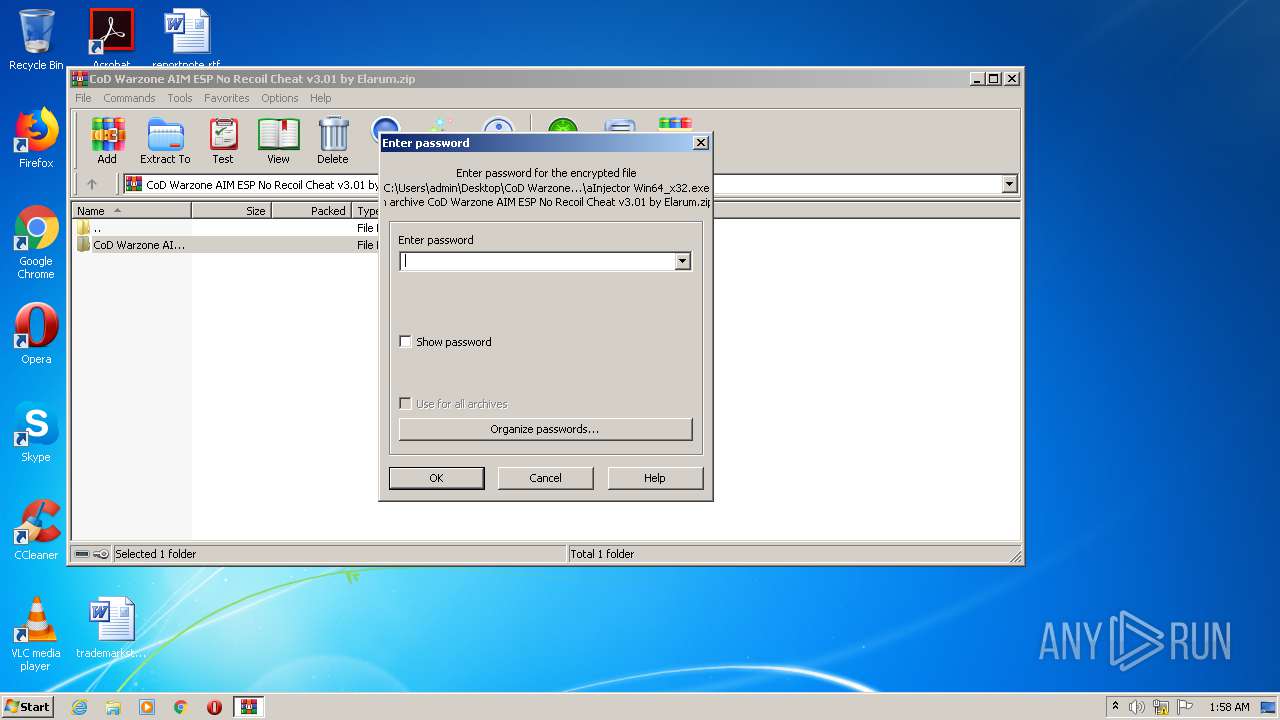
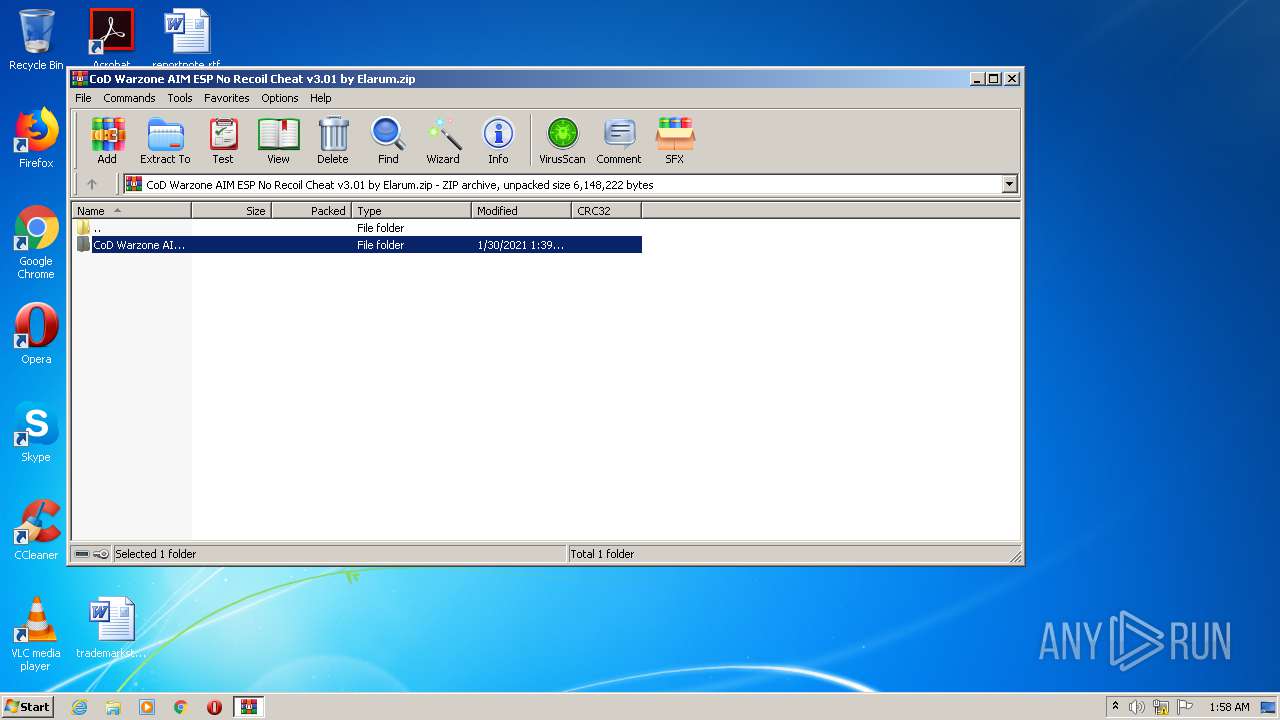
| 996 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
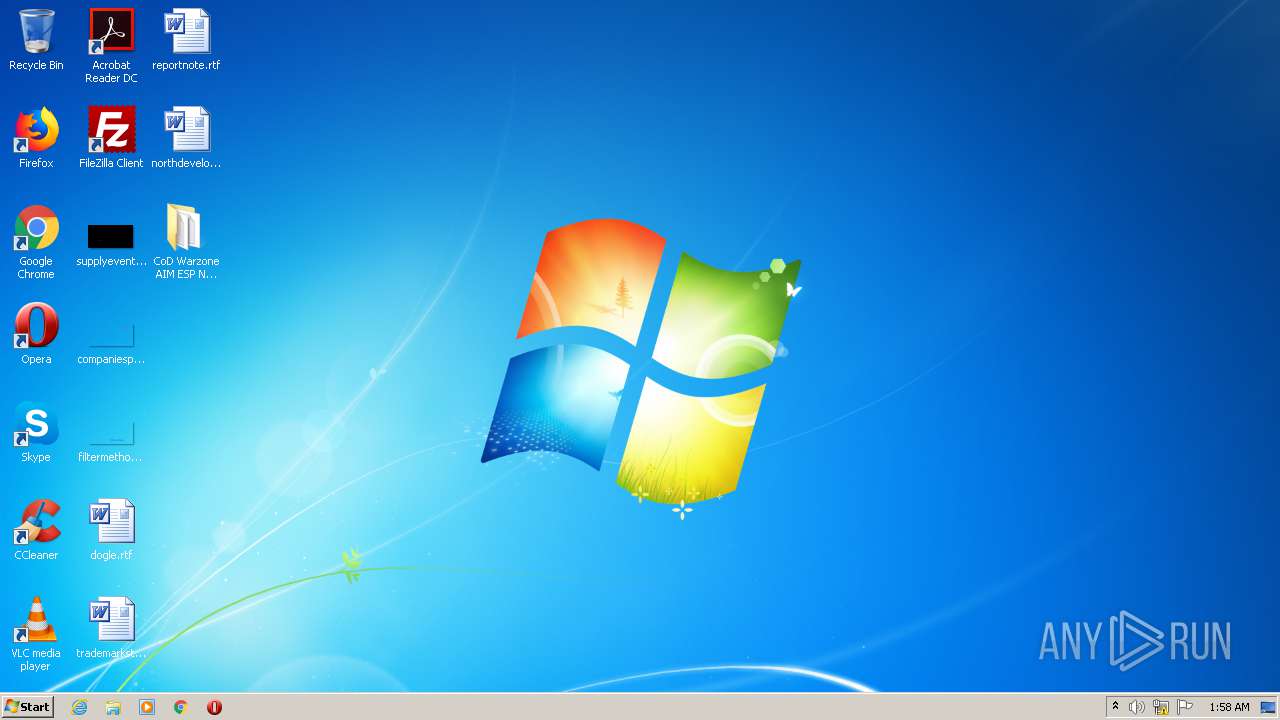
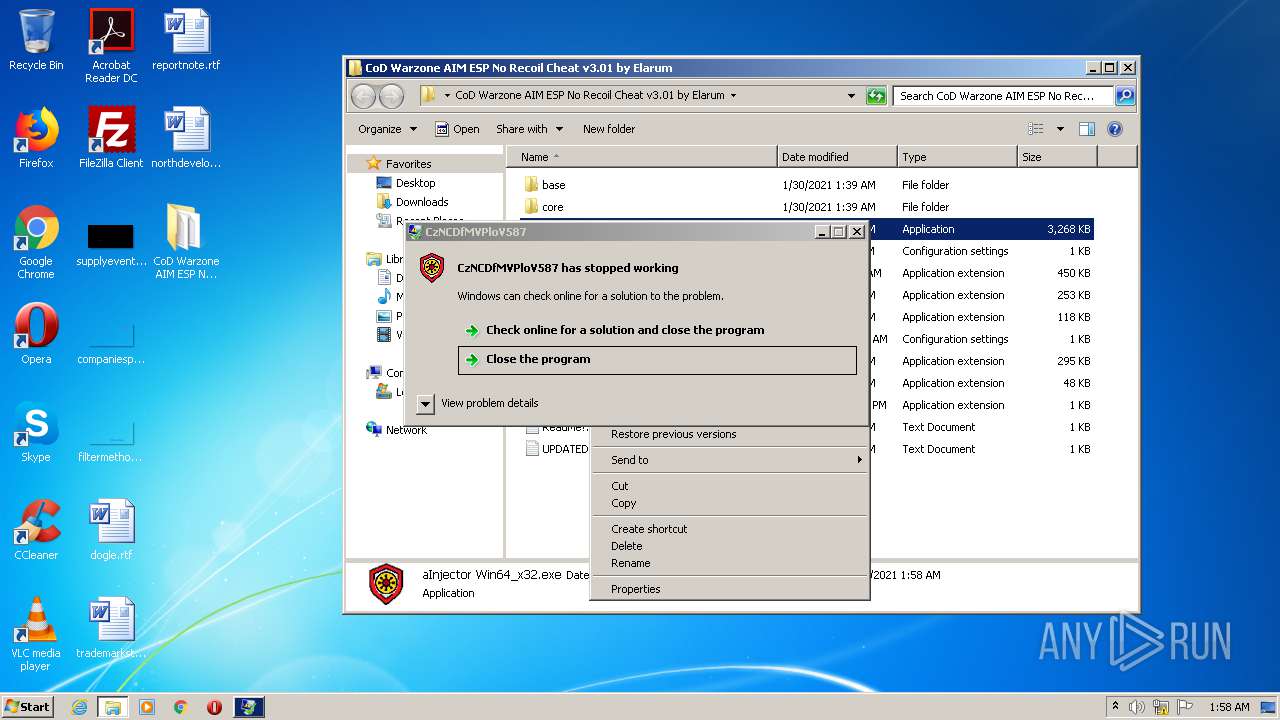
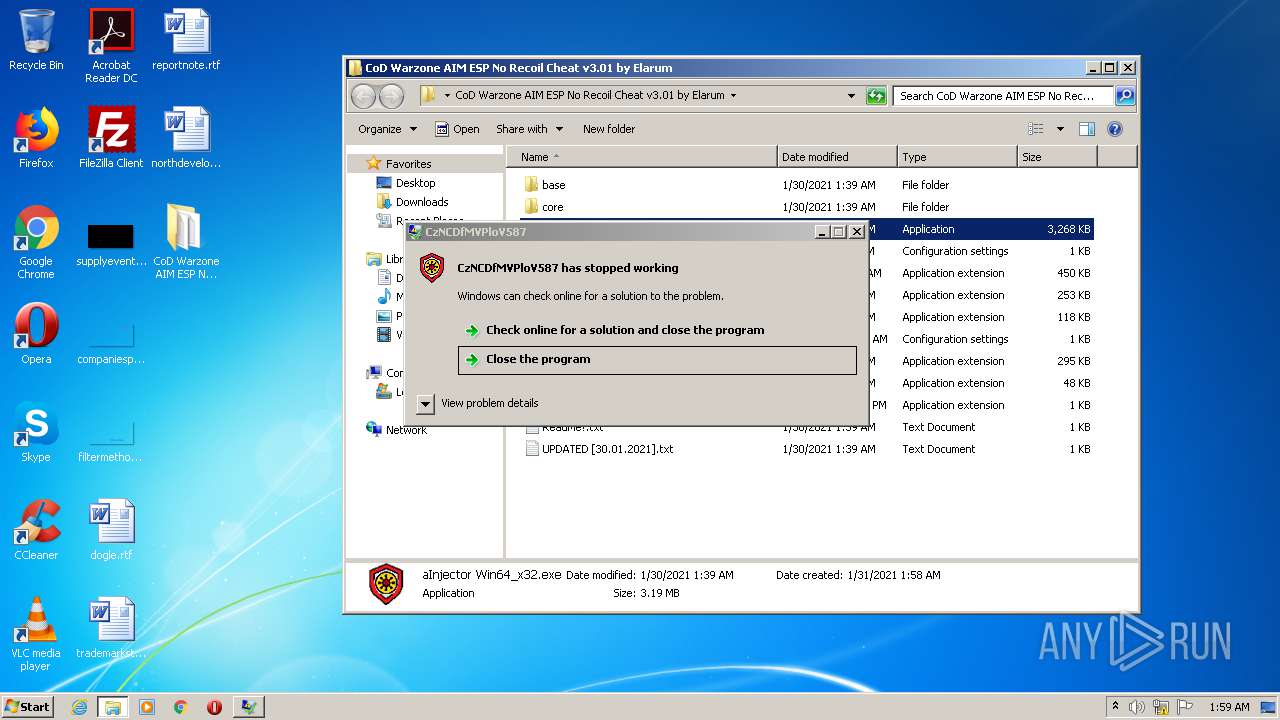
| 1896 | "C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\aInjector Win64_x32.exe" | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\aInjector Win64_x32.exe | explorer.exe | ||||||||||||
User: admin Company: KNwXJCsVyUe iyanOCNSeNqYmhE THqduCEmxP NAQfpB Integrity Level: MEDIUM Description: CzNCDfMVPloV587 Exit code: 2148734499 Version: 19.3.10.23386 Modules
| |||||||||||||||
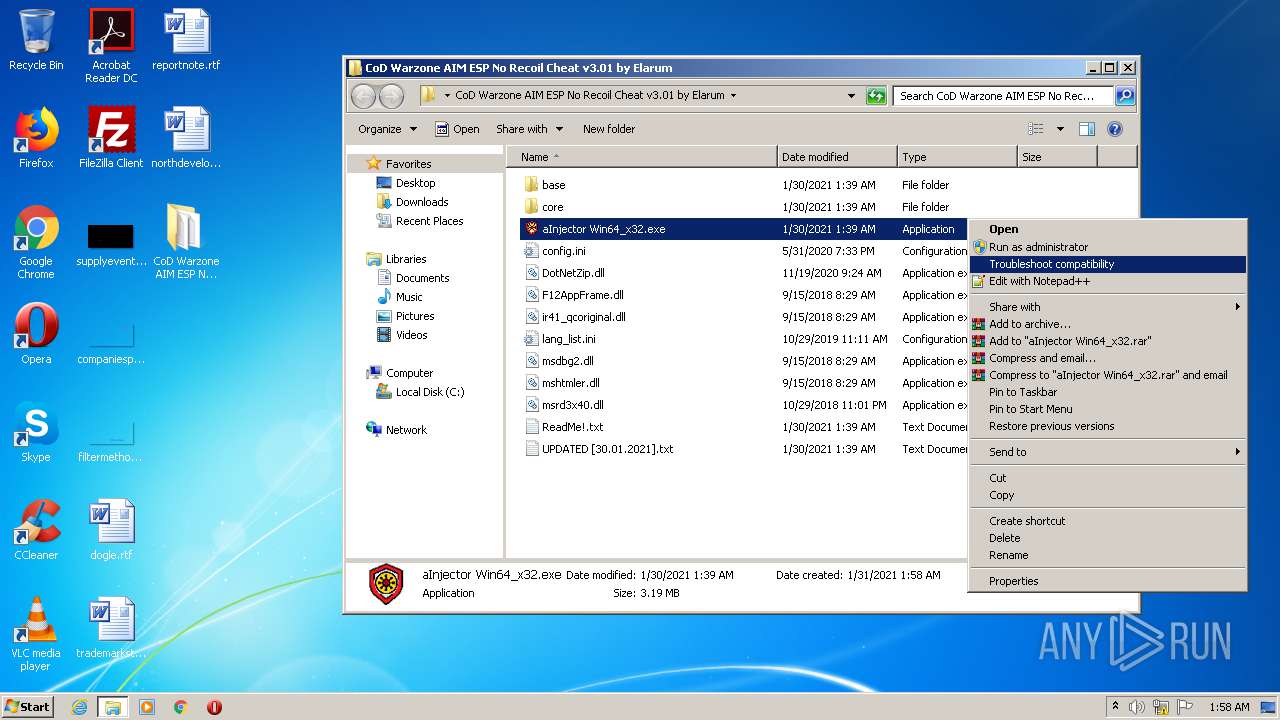
| 3448 | "C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\aInjector Win64_x32.exe" | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\aInjector Win64_x32.exe | explorer.exe | ||||||||||||
User: admin Company: KNwXJCsVyUe iyanOCNSeNqYmhE THqduCEmxP NAQfpB Integrity Level: HIGH Description: CzNCDfMVPloV587 Exit code: 0 Version: 19.3.10.23386 Modules
| |||||||||||||||
| 3548 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4004 | "C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\aInjector Win64_x32.exe" | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\aInjector Win64_x32.exe | — | explorer.exe | |||||||||||
User: admin Company: KNwXJCsVyUe iyanOCNSeNqYmhE THqduCEmxP NAQfpB Integrity Level: MEDIUM Description: CzNCDfMVPloV587 Exit code: 1 Version: 19.3.10.23386 Modules
| |||||||||||||||
Total events
869
Read events
831
Write events
38
Delete events
0
Modification events
| (PID) Process: | (996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (996) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum.zip | |||
| (PID) Process: | (996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
12
Suspicious files
1
Text files
5
Unknown types
0
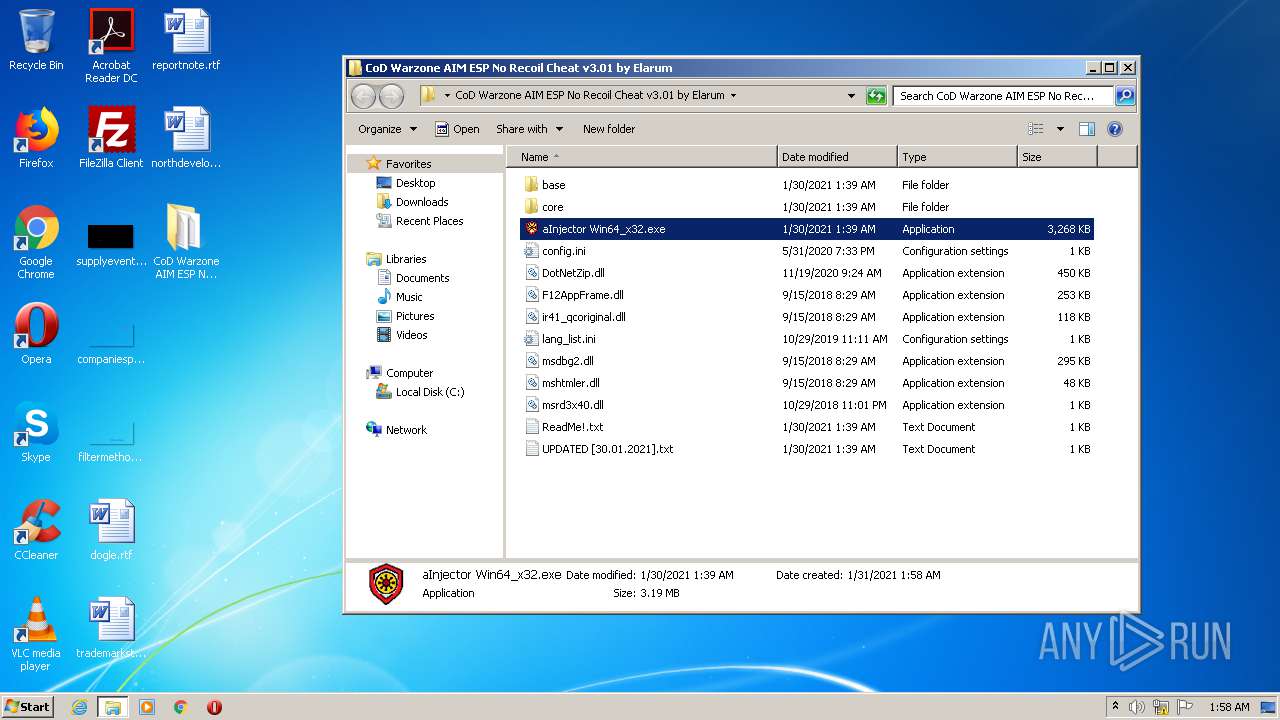
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
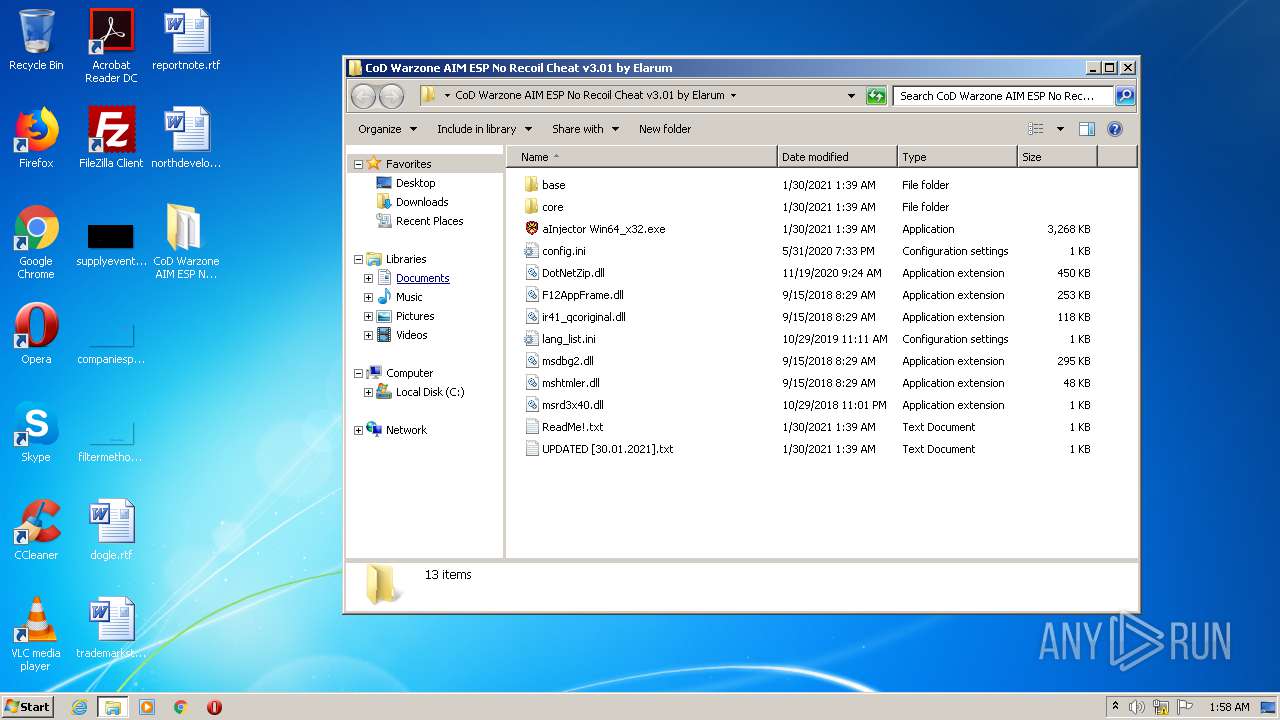
| 996 | WinRAR.exe | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\core\appserverai.dll | executable | |
MD5:— | SHA256:— | |||
| 996 | WinRAR.exe | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\config.ini | text | |
MD5:— | SHA256:— | |||
| 996 | WinRAR.exe | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\base\luainstall.dll | executable | |
MD5:— | SHA256:— | |||
| 996 | WinRAR.exe | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\aInjector Win64_x32.exe | executable | |
MD5:— | SHA256:— | |||
| 996 | WinRAR.exe | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\base\init.js | text | |
MD5:— | SHA256:— | |||
| 996 | WinRAR.exe | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\core\slc.dll | executable | |
MD5:— | SHA256:— | |||
| 996 | WinRAR.exe | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\mshtmler.dll | executable | |
MD5:— | SHA256:— | |||
| 996 | WinRAR.exe | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\lang_list.ini | text | |
MD5:— | SHA256:— | |||
| 996 | WinRAR.exe | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\ReadMe!.txt | text | |
MD5:— | SHA256:— | |||
| 996 | WinRAR.exe | C:\Users\admin\Desktop\CoD Warzone AIM ESP No Recoil Cheat v3.01 by Elarum\msrd3x40.dll | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1896 | aInjector Win64_x32.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
3448 | aInjector Win64_x32.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger LLP | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.telegram.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1896 | aInjector Win64_x32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3448 | aInjector Win64_x32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
Process | Message |
|---|---|
aInjector Win64_x32.exe | CLR: Managed code called FailFast without specifying a reason.
|
aInjector Win64_x32.exe | CLR: Managed code called FailFast without specifying a reason.
|