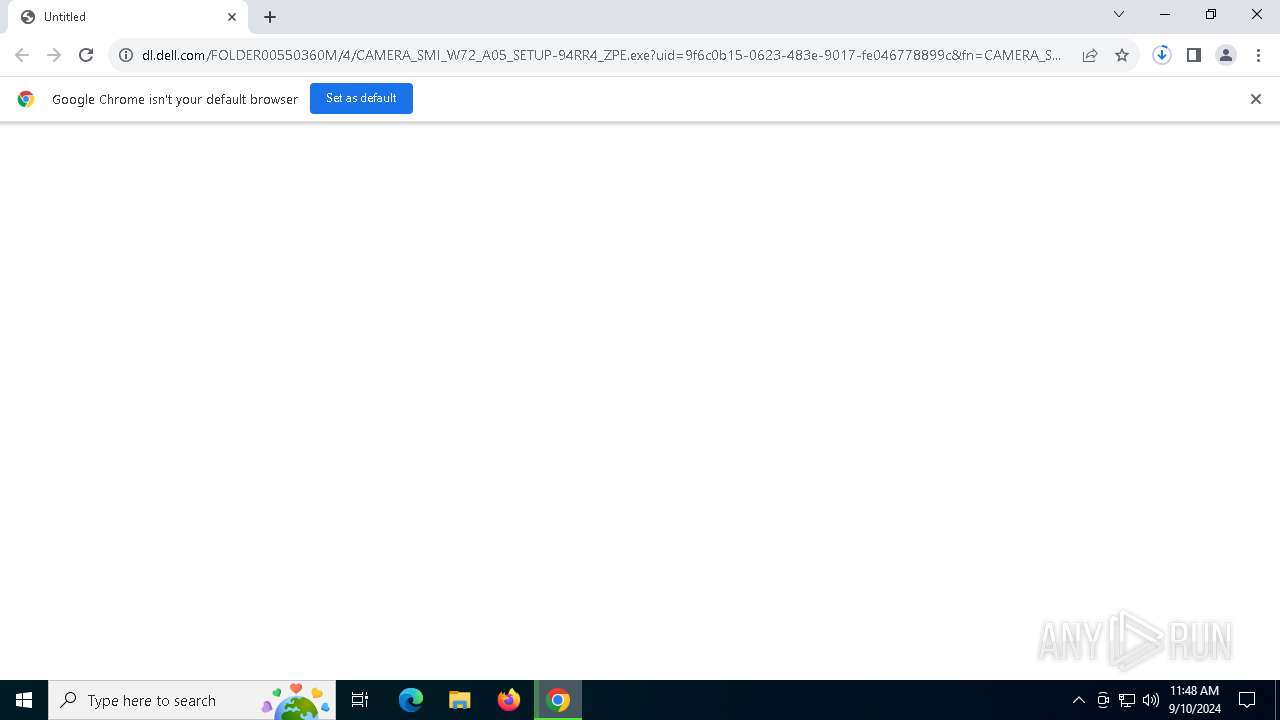
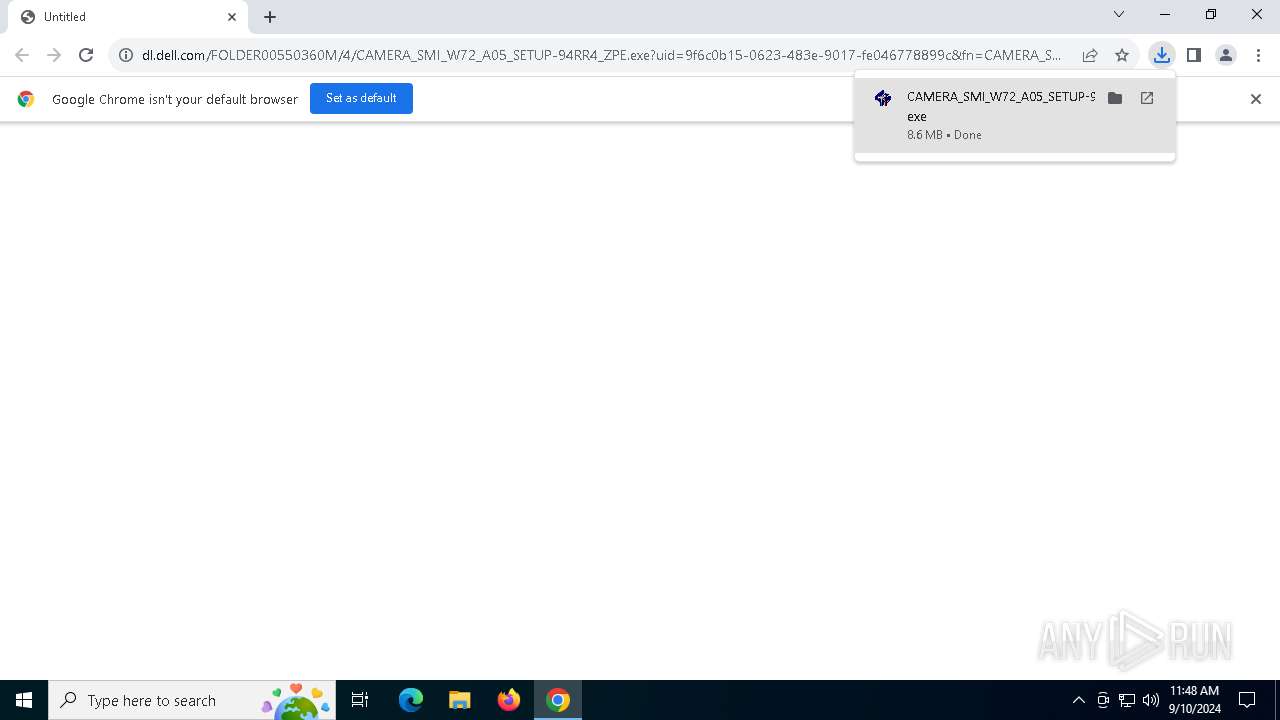
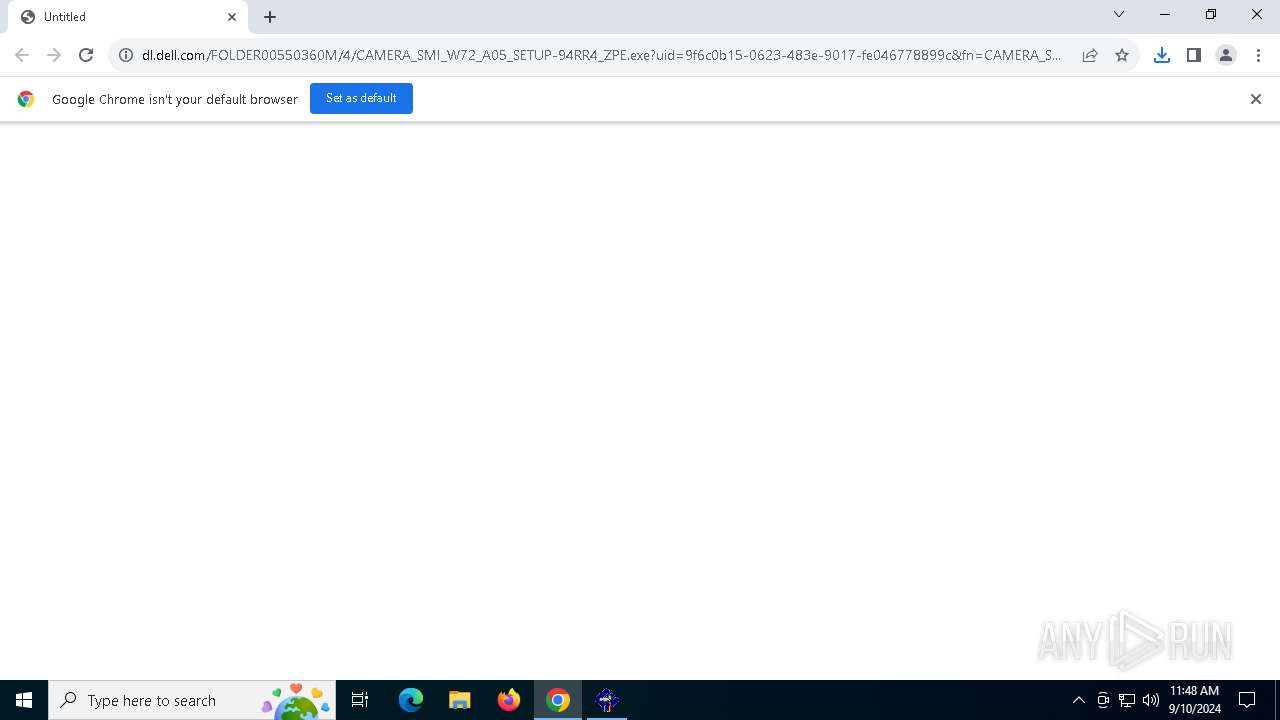
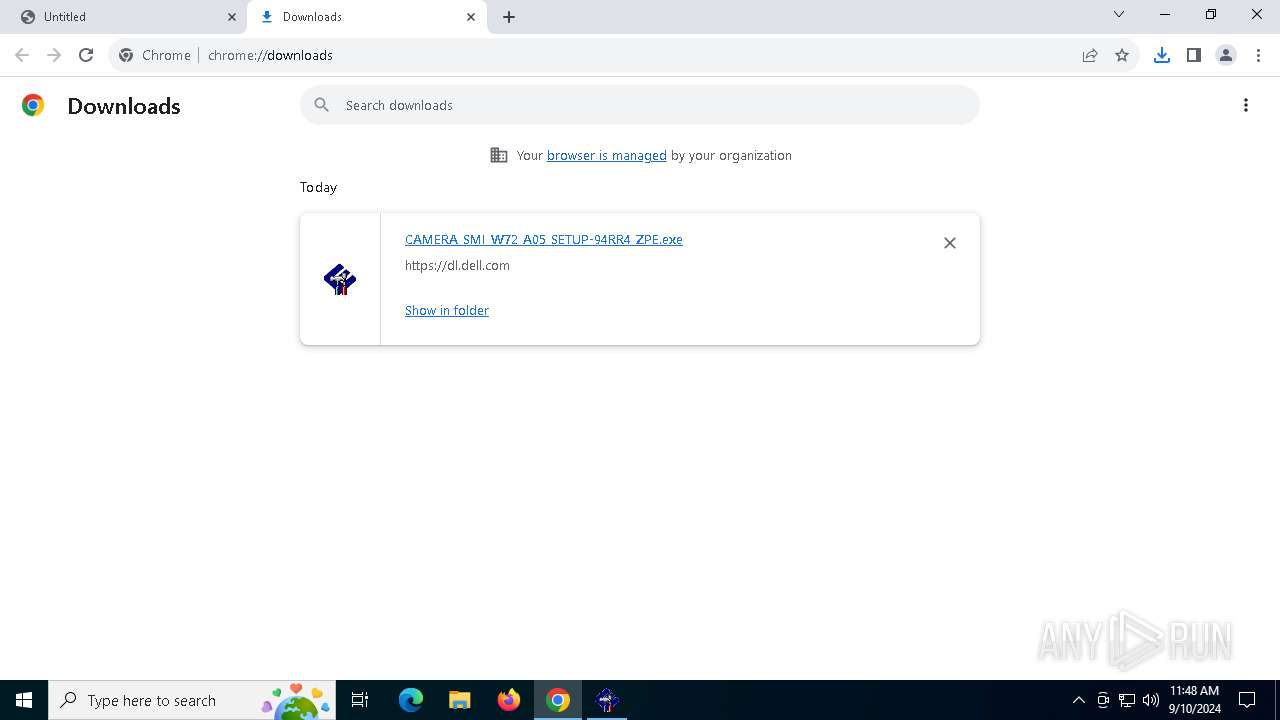
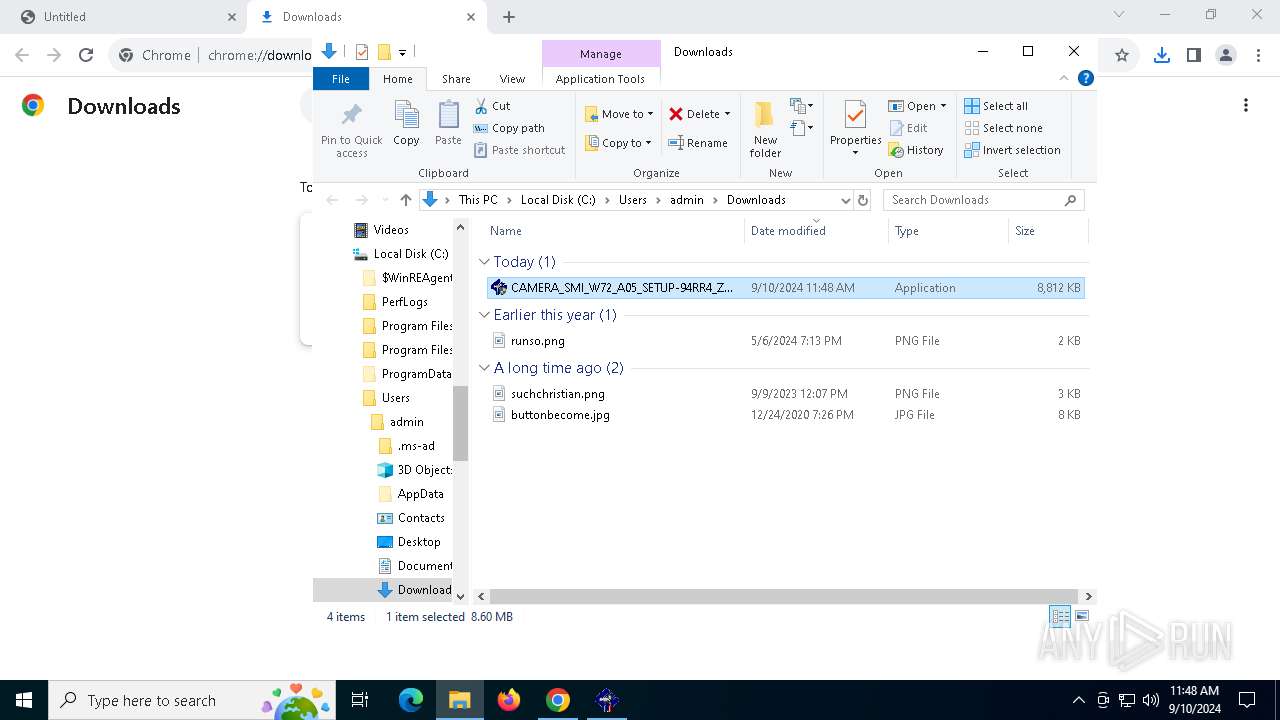
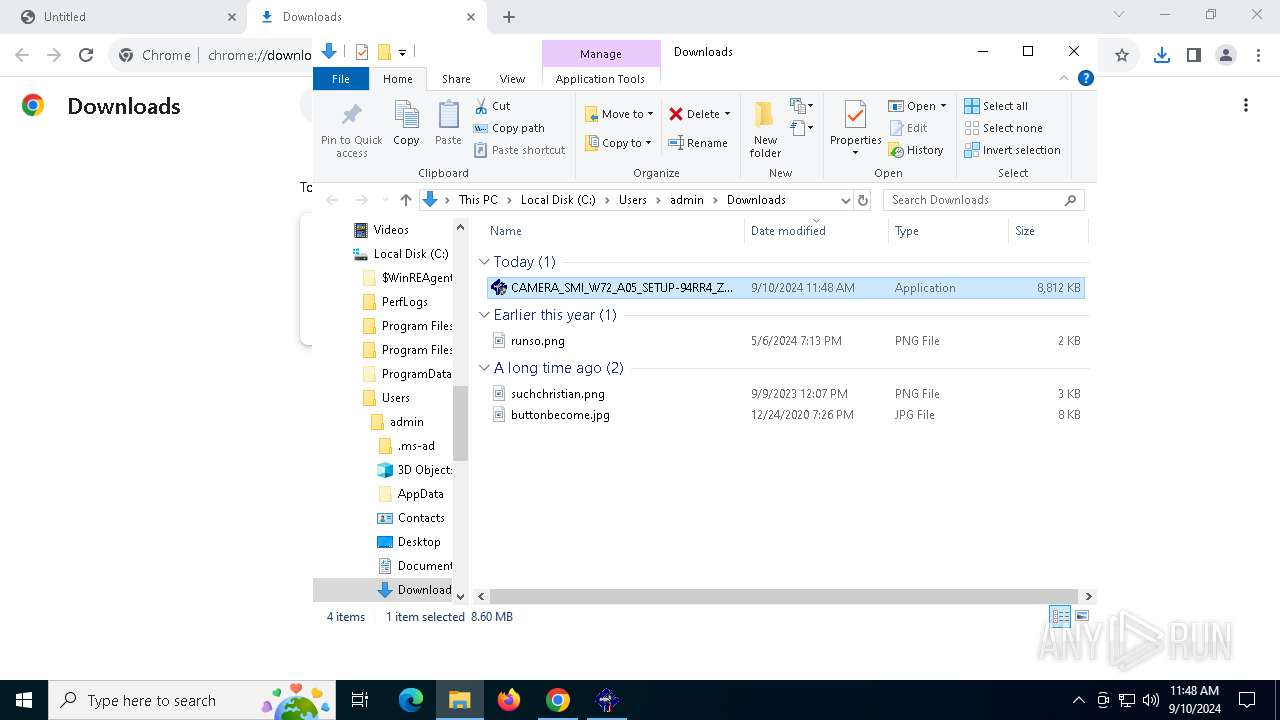
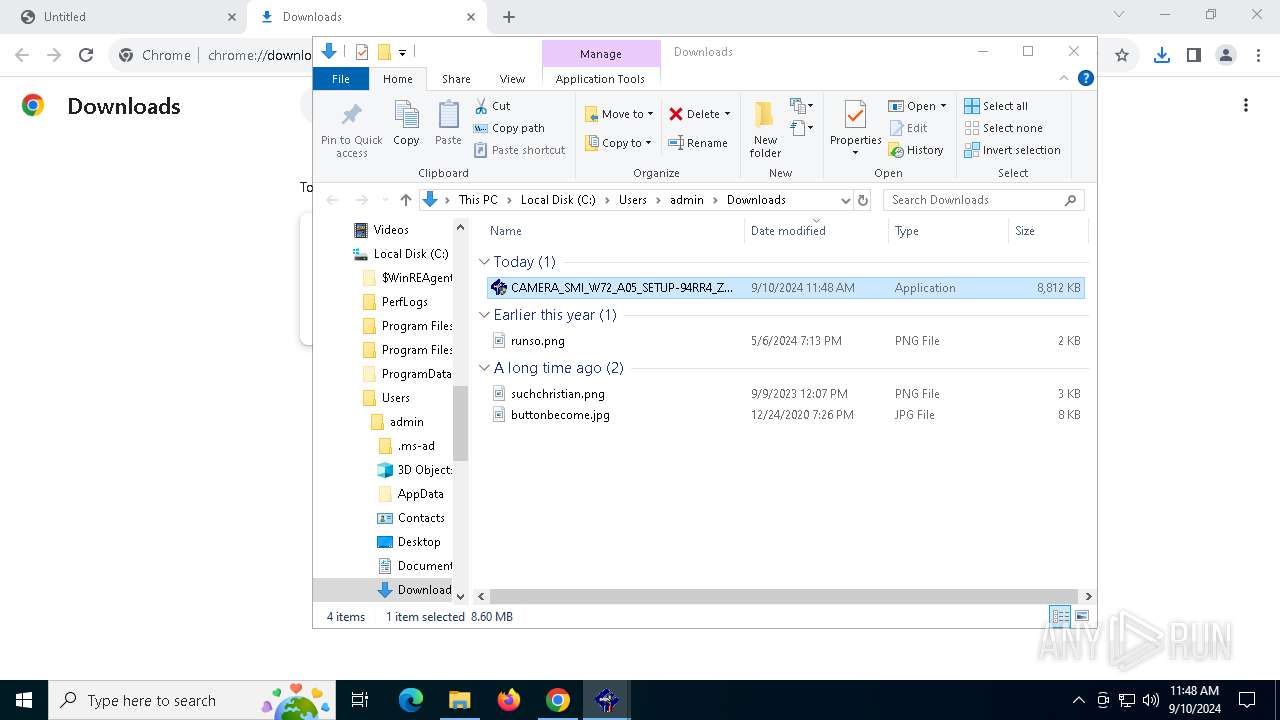
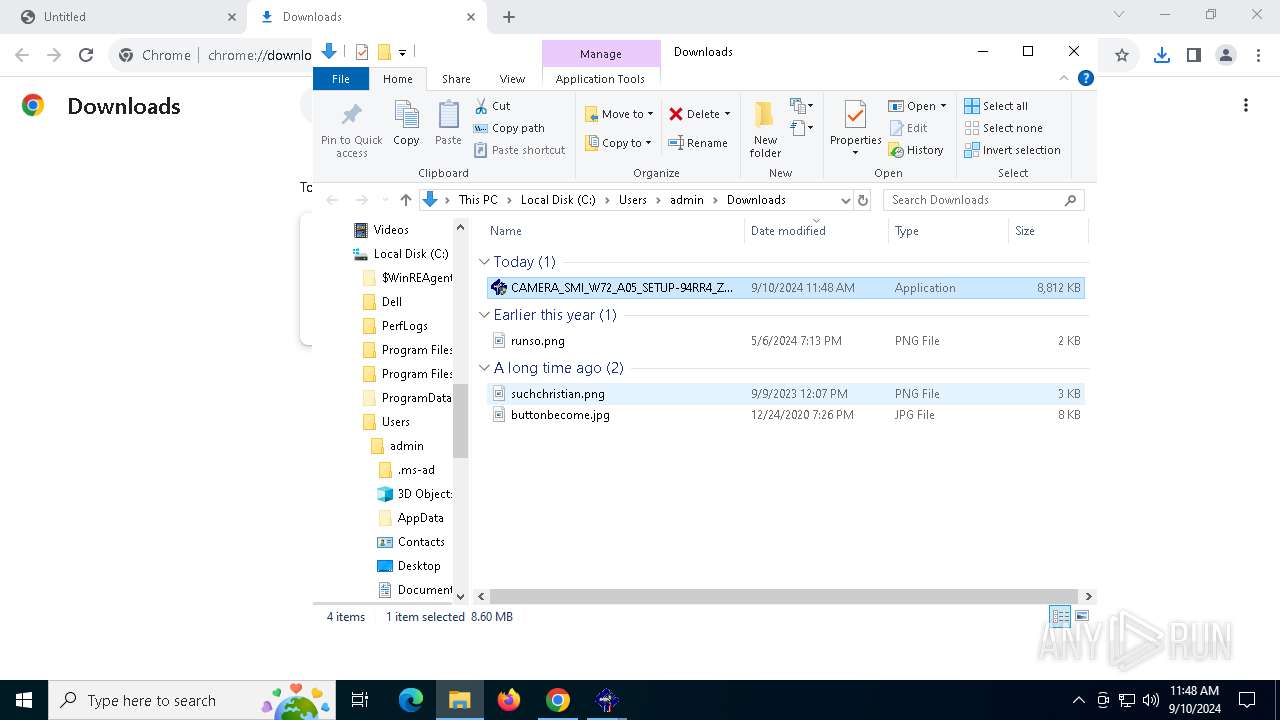
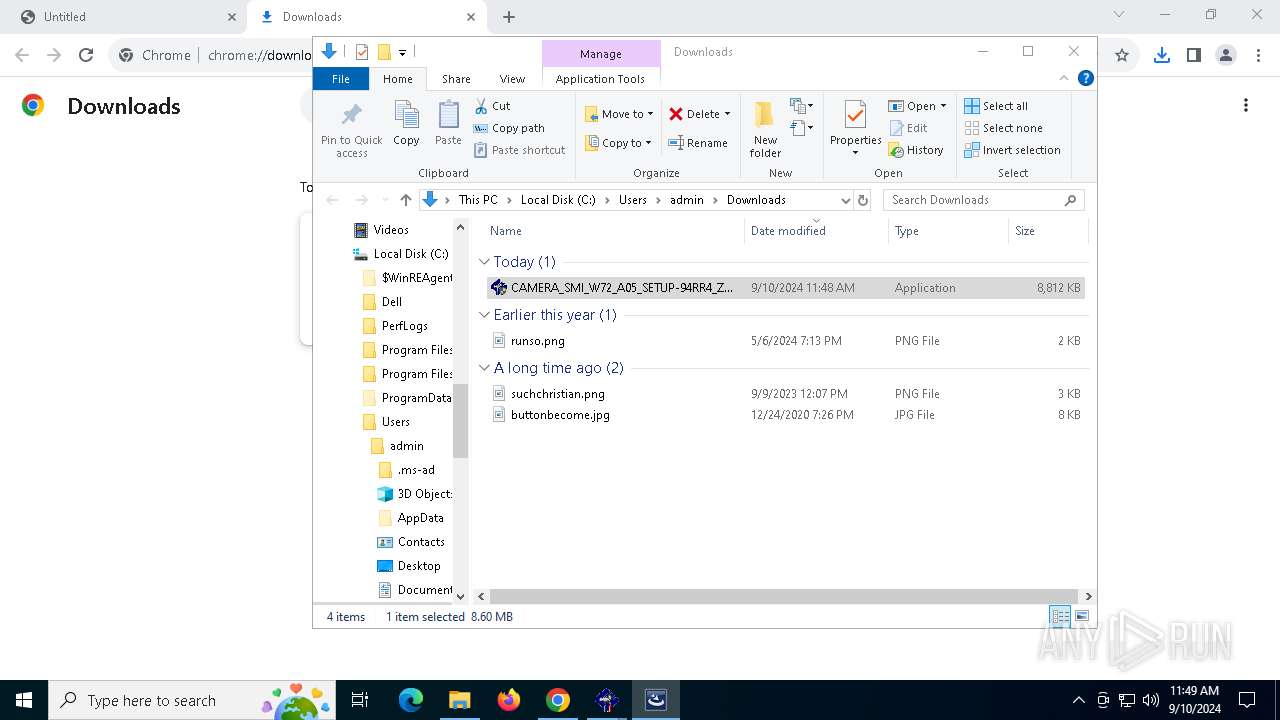
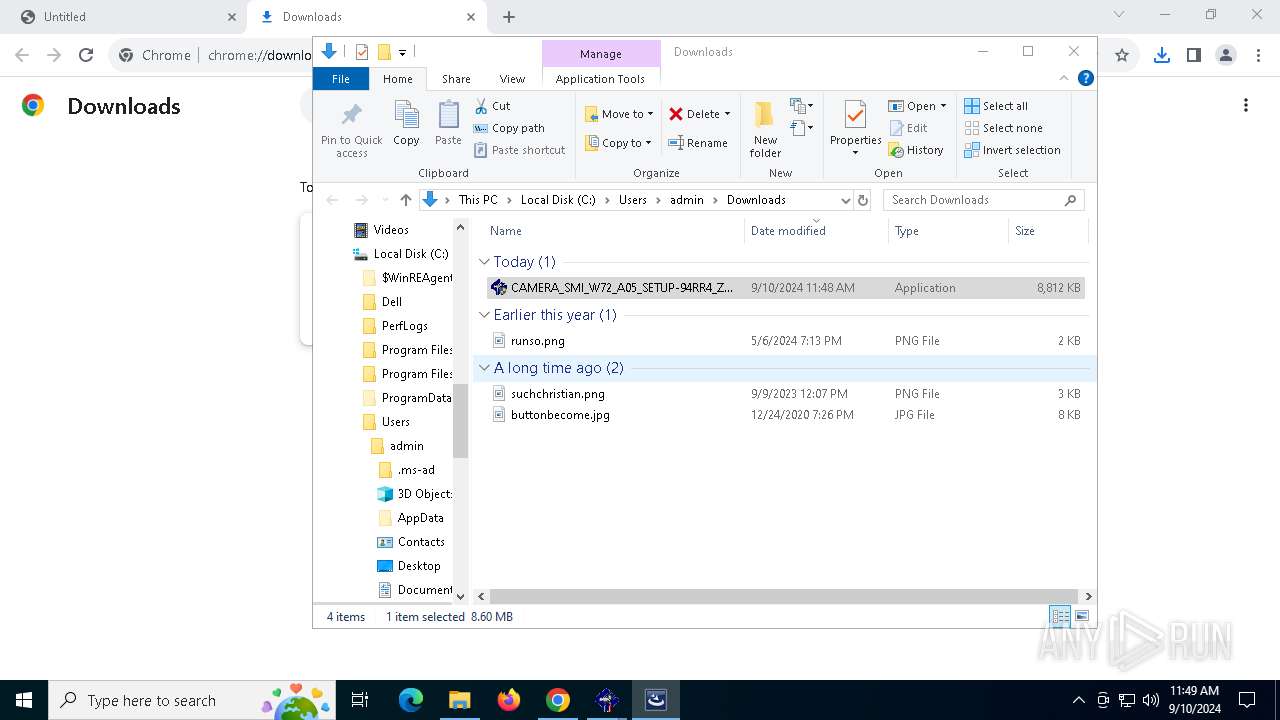
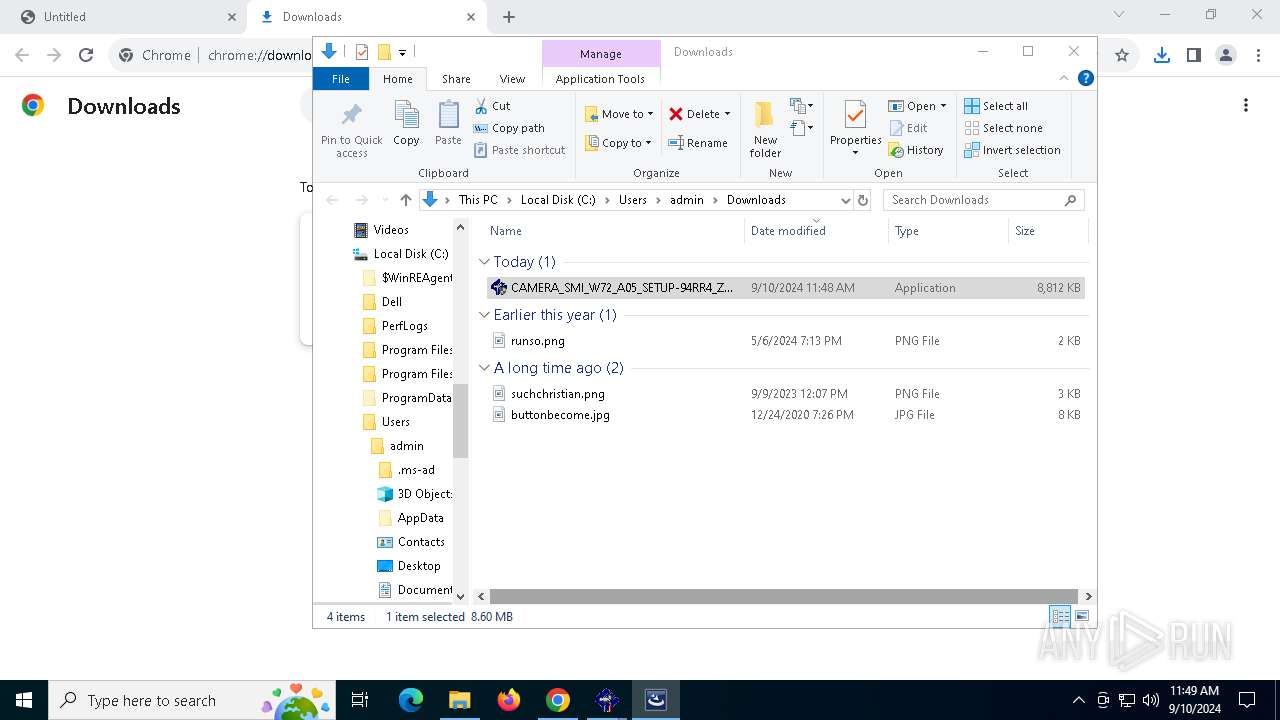
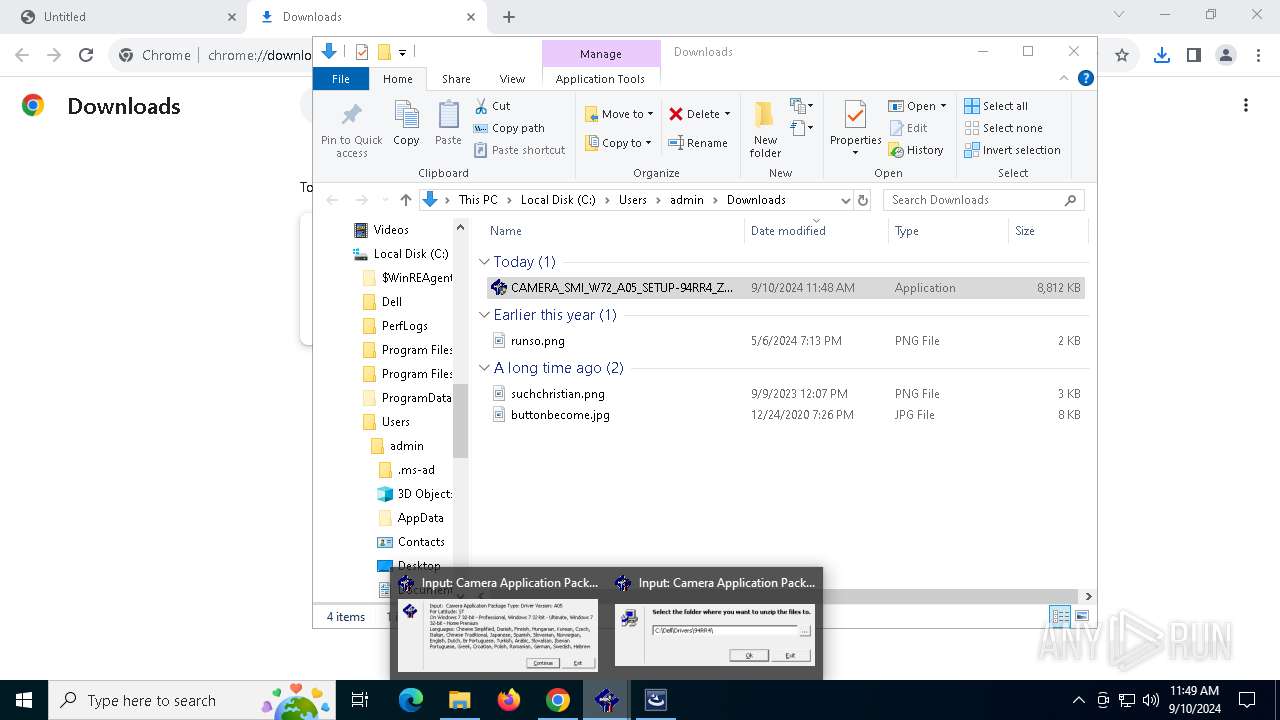
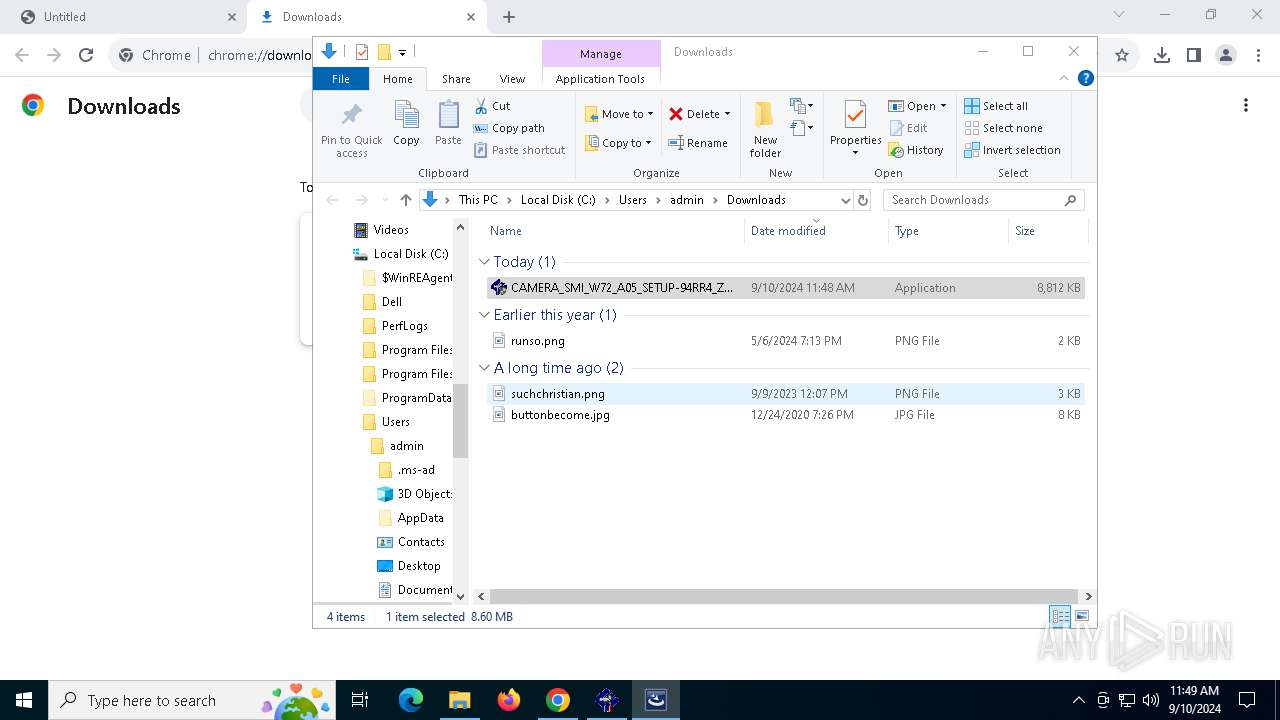
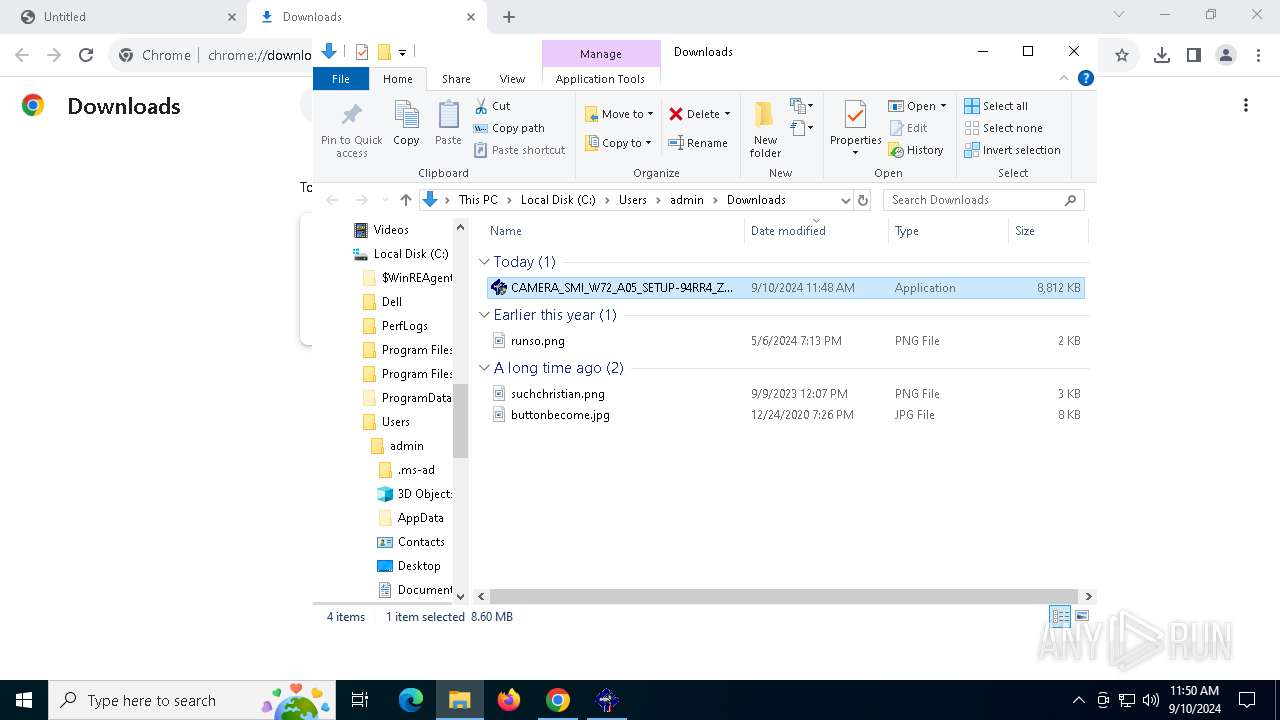
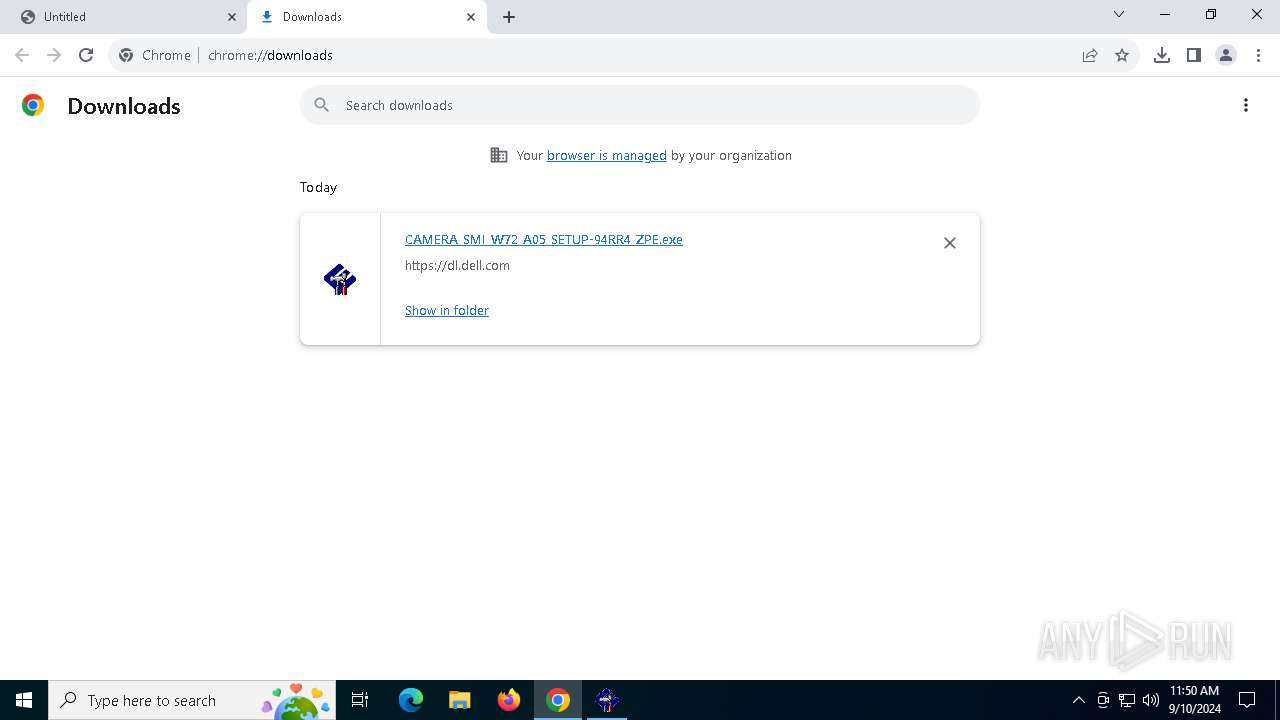
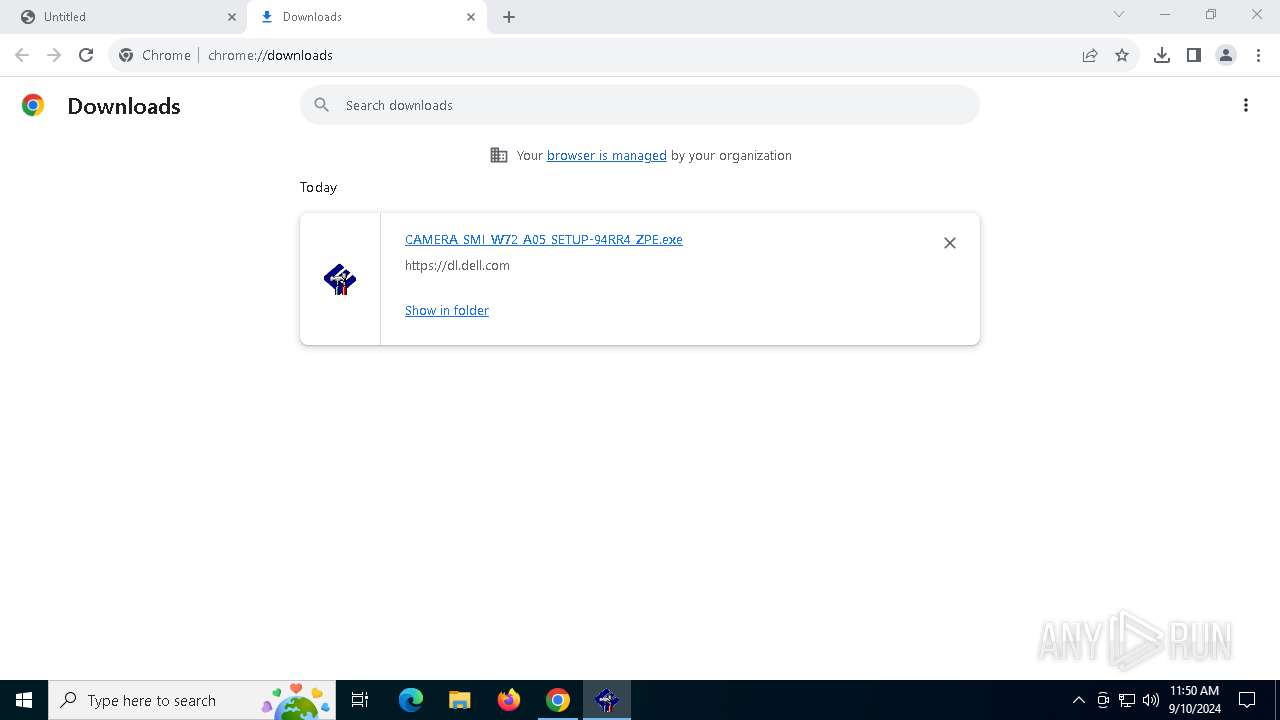
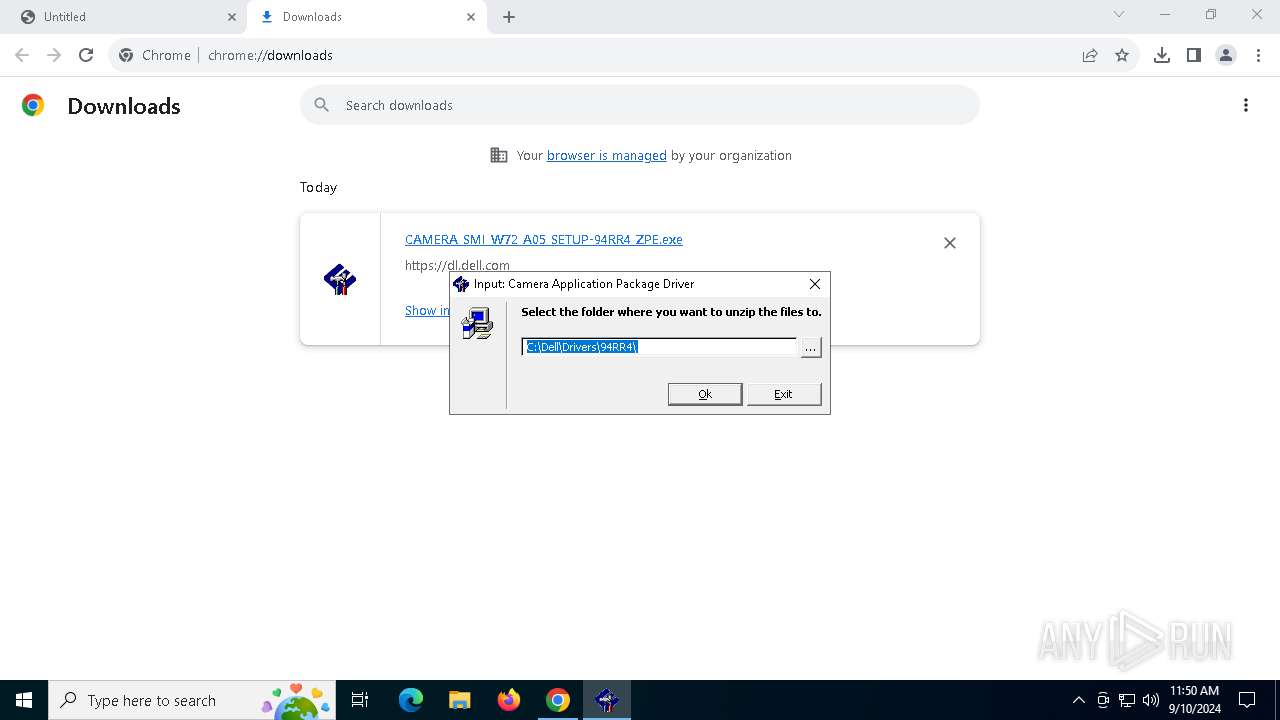
| URL: | https://dl.dell.com/FOLDER00550360M/4/CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe?uid=9f6c0b15-0623-483e-9017-fe046778899c&fn=CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe |
| Full analysis: | https://app.any.run/tasks/d6276763-11bb-47d7-879f-1491ceec260a |
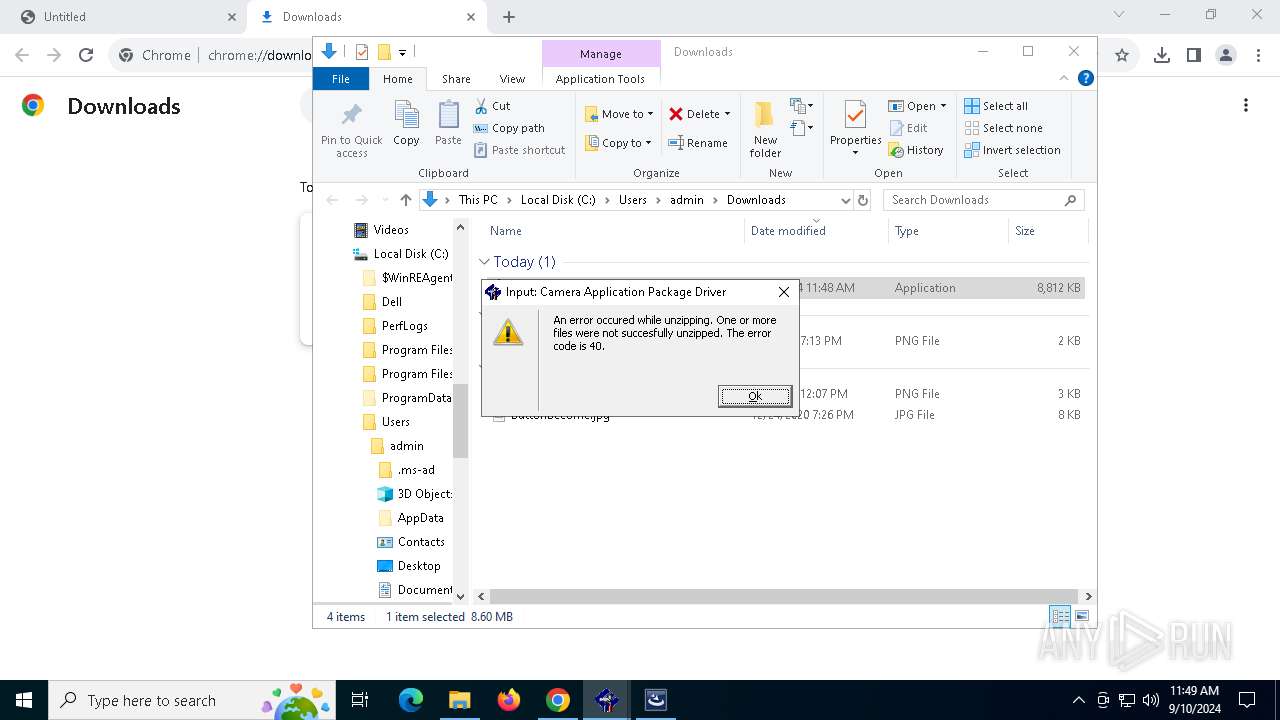
| Verdict: | Malicious activity |
| Analysis date: | September 10, 2024, 11:48:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 8AC17152AE1FC2C53C99160FC5194F6F |
| SHA1: | BA9F4A023D2B76C5A54064ECA65589F5B510B99B |
| SHA256: | 4C40B0B803AC42BAD854AF2FA931228A1D4CC18B05BCD69E3FF44BEBCEEC6763 |
| SSDEEP: | 3:N8RKJ8KInKFVWTCRTogKjIVQSuRxUwNcFOHJ4Wa+a49gKjIVQSuRxUwNn:2o8KmKFVpB9KxFxUwNrxvgKxFxUwNn |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- IS.exe (PID: 6396)
SUSPICIOUS
Reads security settings of Internet Explorer
- setup.exe (PID: 4732)
- SMIServiceWrapper.exe (PID: 2820)
- SMIServiceWrapper.exe (PID: 3272)
- CheckVcamReg.exe (PID: 7336)
- SMIServiceWrapper.exe (PID: 7388)
- ExecuteBatch-Win.exe (PID: 7572)
- SMIServiceWrapper.exe (PID: 7660)
- SMIServiceWrapper.exe (PID: 7920)
- ExecuteBatch-Win.exe (PID: 8100)
- SMIServiceWrapper.exe (PID: 8180)
- SMIServiceWrapper.exe (PID: 7492)
- ExecuteBatch-Win.exe (PID: 7736)
- SMIServiceWrapper.exe (PID: 2868)
- SMIServiceWrapper.exe (PID: 7940)
- SMIServiceWrapper.exe (PID: 8104)
- ExecuteBatch-Win.exe (PID: 7316)
- SMIServiceWrapper.exe (PID: 7600)
- ExecuteBatch-Win.exe (PID: 2576)
- SMIServiceWrapper.exe (PID: 7788)
- SMIServiceWrapper.exe (PID: 8056)
- SMIServiceWrapper.exe (PID: 8068)
- SMIServiceWrapper.exe (PID: 7624)
- ExecuteBatch-Win.exe (PID: 7436)
- ExecuteBatch-Win.exe (PID: 7688)
- SMIServiceWrapper.exe (PID: 7644)
- ExecuteBatch-Win.exe (PID: 6260)
- SMIServiceWrapper.exe (PID: 7228)
- SMIServiceWrapper.exe (PID: 7480)
- ExecuteBatch-Win.exe (PID: 812)
- SMIServiceWrapper.exe (PID: 7808)
- SMIServiceWrapper.exe (PID: 7492)
- SMIServiceWrapper.exe (PID: 8176)
- ExecuteBatch-Win.exe (PID: 8000)
- SMIServiceWrapper.exe (PID: 8128)
- SMIRegistryTool.exe (PID: 7228)
- SMIServiceWrapper.exe (PID: 7796)
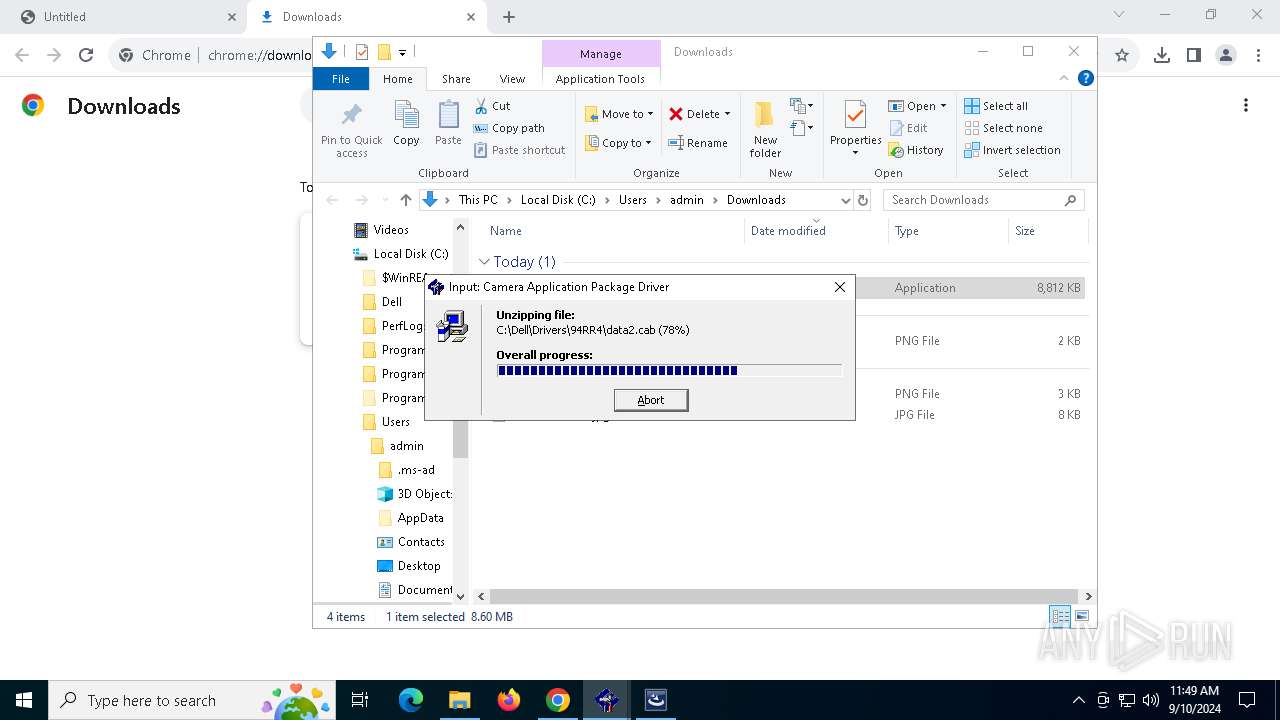
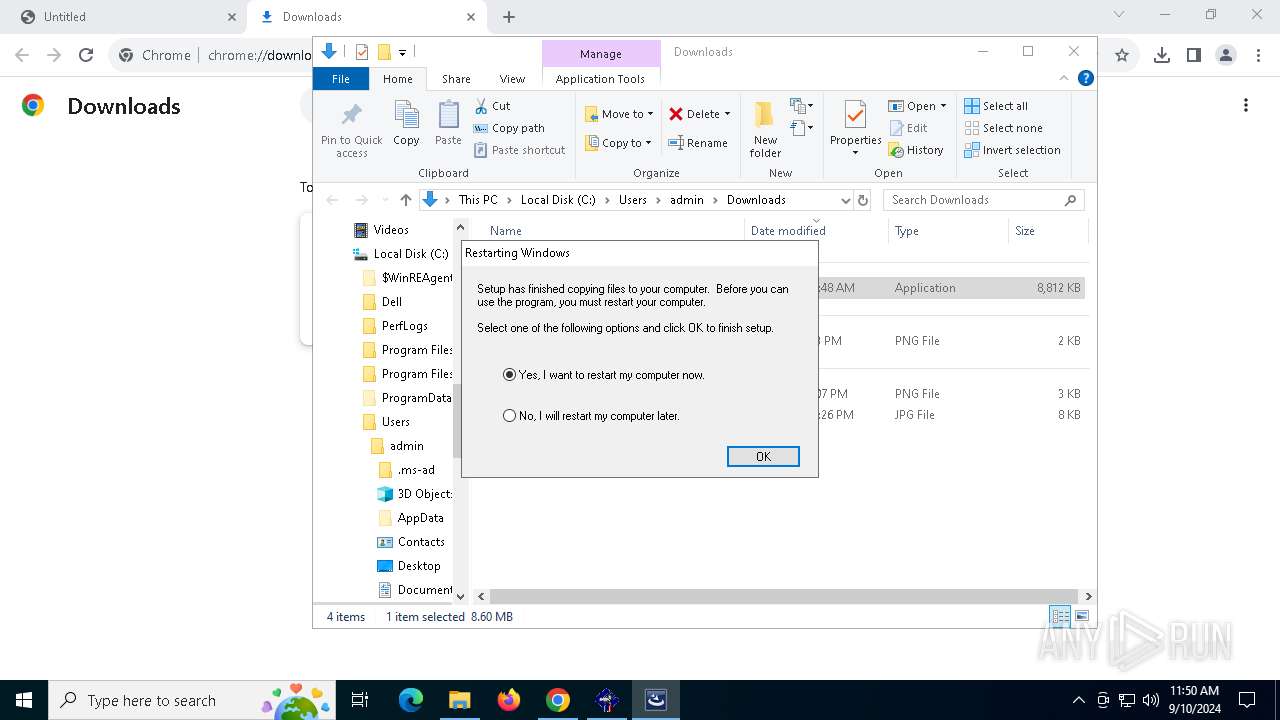
Executable content was dropped or overwritten
- CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe (PID: 1440)
- IS.exe (PID: 6396)
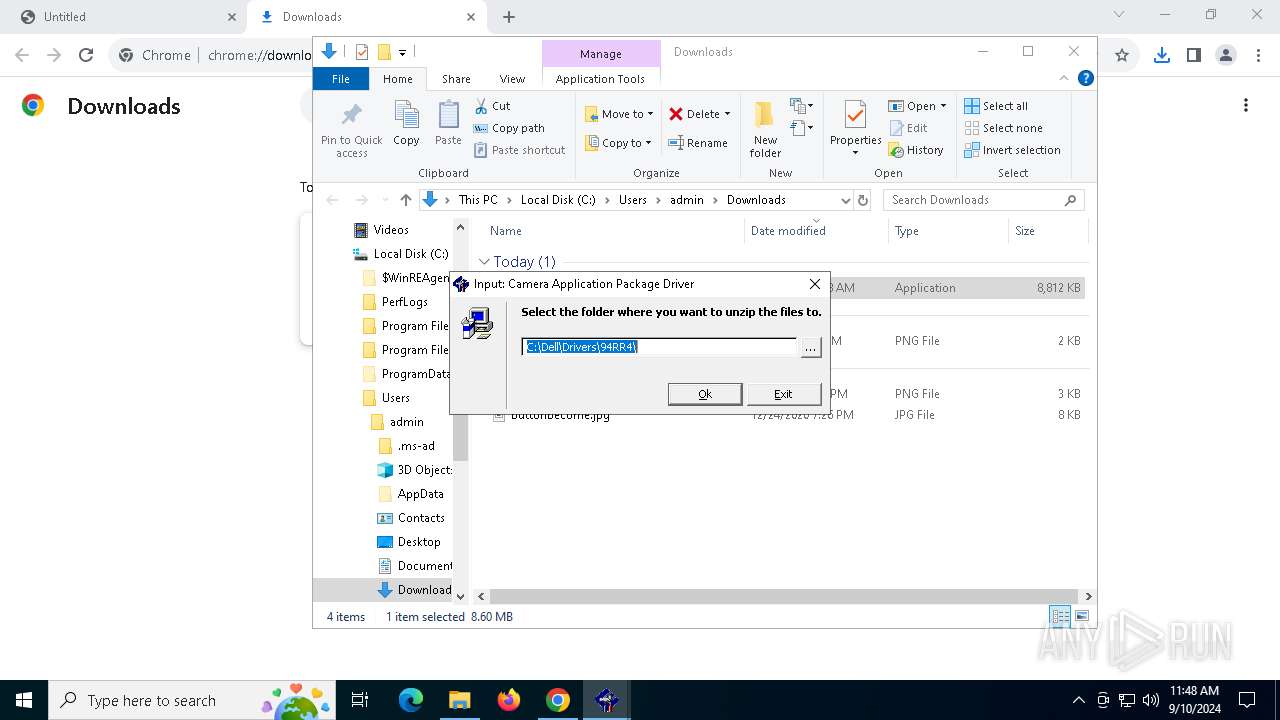
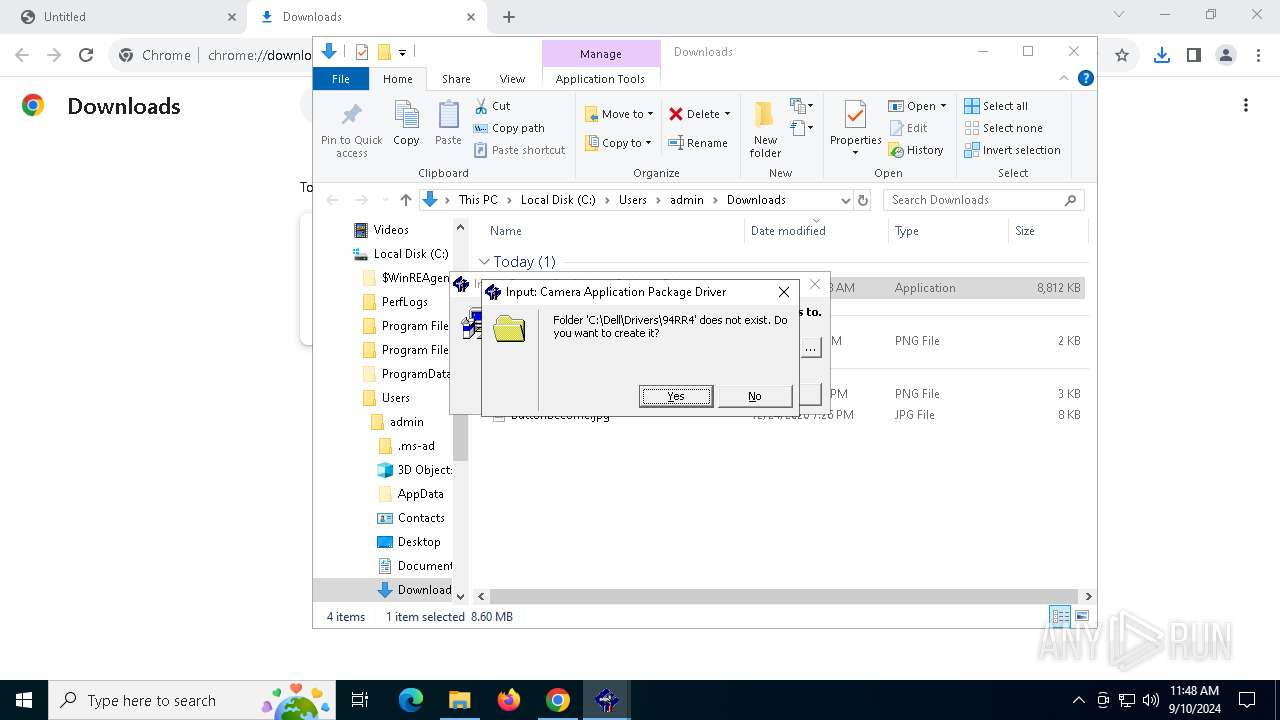
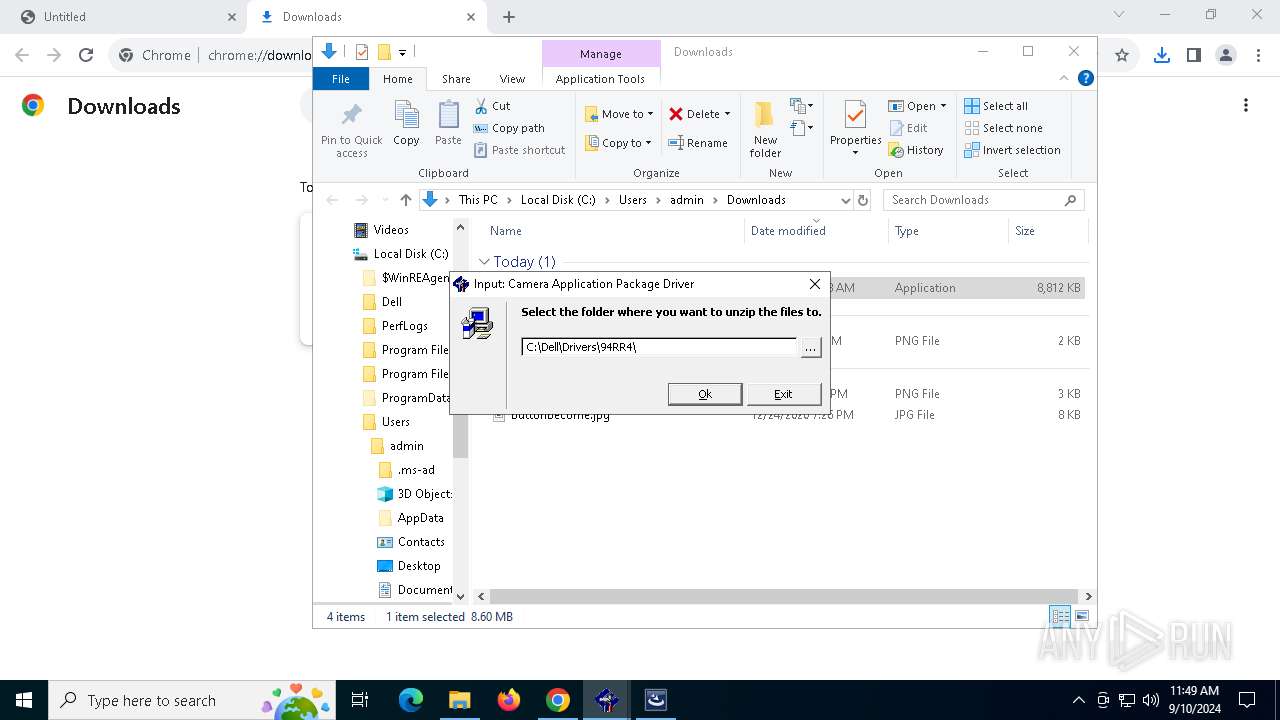
Creates file in the systems drive root
- CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe (PID: 1440)
Executes as Windows Service
- XYNTService.exe (PID: 5520)
- VSSVC.exe (PID: 6844)
- XYNTService.exe (PID: 7536)
- XYNTService.exe (PID: 8068)
- XYNTService.exe (PID: 2508)
- XYNTService.exe (PID: 8136)
- XYNTService.exe (PID: 7872)
- XYNTService.exe (PID: 8092)
- XYNTService.exe (PID: 7572)
- XYNTService.exe (PID: 5052)
- XYNTService.exe (PID: 6516)
- XYNTService.exe (PID: 7576)
- XYNTService.exe (PID: 7484)
Starts CMD.EXE for commands execution
- ExecuteBatch-Win.exe (PID: 1184)
- ExecuteBatch-Win.exe (PID: 7572)
- ExecuteBatch-Win.exe (PID: 8100)
- ExecuteBatch-Win.exe (PID: 7736)
- ExecuteBatch-Win.exe (PID: 7316)
- ExecuteBatch-Win.exe (PID: 2576)
- ExecuteBatch-Win.exe (PID: 7436)
- ExecuteBatch-Win.exe (PID: 7688)
- ExecuteBatch-Win.exe (PID: 6260)
- ExecuteBatch-Win.exe (PID: 812)
- ExecuteBatch-Win.exe (PID: 8000)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 5772)
- cmd.exe (PID: 7592)
- regedit.exe (PID: 7732)
- regedit.exe (PID: 7808)
- cmd.exe (PID: 8124)
- regedit.exe (PID: 7264)
- regedit.exe (PID: 7440)
- cmd.exe (PID: 7824)
- regedit.exe (PID: 5540)
- regedit.exe (PID: 6240)
- regedit.exe (PID: 6920)
- cmd.exe (PID: 7476)
- regedit.exe (PID: 7224)
- regedit.exe (PID: 2508)
- regedit.exe (PID: 3268)
- cmd.exe (PID: 7020)
- regedit.exe (PID: 7412)
- regedit.exe (PID: 3876)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7876)
- regedit.exe (PID: 1764)
- cmd.exe (PID: 7356)
- regedit.exe (PID: 7936)
- regedit.exe (PID: 7244)
- cmd.exe (PID: 1084)
- regedit.exe (PID: 7624)
- regedit.exe (PID: 7048)
- cmd.exe (PID: 8096)
- regedit.exe (PID: 8140)
- regedit.exe (PID: 8072)
- regedit.exe (PID: 400)
- regedit.exe (PID: 7928)
- regedit.exe (PID: 6240)
The process deletes folder without confirmation
- ExecuteBatch-Win.exe (PID: 1184)
- ExecuteBatch-Win.exe (PID: 7572)
- ExecuteBatch-Win.exe (PID: 8100)
- ExecuteBatch-Win.exe (PID: 7736)
- ExecuteBatch-Win.exe (PID: 7316)
- ExecuteBatch-Win.exe (PID: 2576)
- ExecuteBatch-Win.exe (PID: 7436)
- ExecuteBatch-Win.exe (PID: 7688)
- ExecuteBatch-Win.exe (PID: 6260)
- ExecuteBatch-Win.exe (PID: 812)
- ExecuteBatch-Win.exe (PID: 8000)
Searches for installed software
- dllhost.exe (PID: 5980)
- IS.exe (PID: 6396)
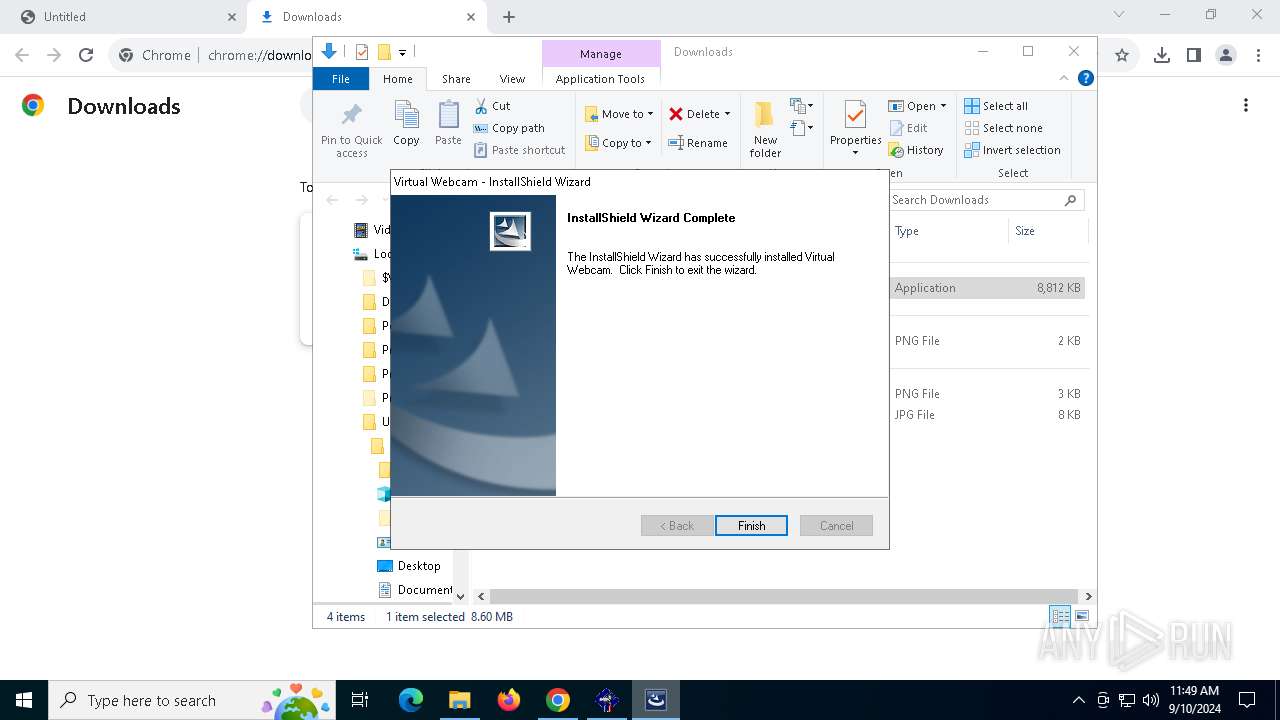
Process drops legitimate windows executable
- IS.exe (PID: 6396)
The process drops C-runtime libraries
- IS.exe (PID: 6396)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 7256)
- regsvr32.exe (PID: 7280)
- regsvr32.exe (PID: 7232)
Creates a software uninstall entry
- IS.exe (PID: 6396)
Uses REG/REGEDIT.EXE to modify registry
- SMIRegistryTool.exe (PID: 7228)
INFO
The process uses the downloaded file
- chrome.exe (PID: 1568)
- chrome.exe (PID: 5088)
- setup.exe (PID: 4732)
- SMIServiceWrapper.exe (PID: 2820)
- SMIServiceWrapper.exe (PID: 3272)
- CheckVcamReg.exe (PID: 7336)
- SMIServiceWrapper.exe (PID: 7388)
- ExecuteBatch-Win.exe (PID: 7572)
- SMIServiceWrapper.exe (PID: 7660)
- SMIServiceWrapper.exe (PID: 7920)
- ExecuteBatch-Win.exe (PID: 8100)
- SMIServiceWrapper.exe (PID: 8180)
- SMIServiceWrapper.exe (PID: 7492)
- SMIServiceWrapper.exe (PID: 2868)
- SMIServiceWrapper.exe (PID: 7940)
- ExecuteBatch-Win.exe (PID: 7736)
- ExecuteBatch-Win.exe (PID: 7316)
- SMIServiceWrapper.exe (PID: 8104)
- SMIServiceWrapper.exe (PID: 7600)
- ExecuteBatch-Win.exe (PID: 2576)
- SMIServiceWrapper.exe (PID: 7788)
- SMIServiceWrapper.exe (PID: 8056)
- ExecuteBatch-Win.exe (PID: 7436)
- SMIServiceWrapper.exe (PID: 8068)
- SMIServiceWrapper.exe (PID: 7624)
- ExecuteBatch-Win.exe (PID: 7688)
- SMIServiceWrapper.exe (PID: 7796)
- SMIServiceWrapper.exe (PID: 7644)
- ExecuteBatch-Win.exe (PID: 6260)
- SMIServiceWrapper.exe (PID: 7228)
- SMIServiceWrapper.exe (PID: 7480)
- ExecuteBatch-Win.exe (PID: 812)
- SMIServiceWrapper.exe (PID: 7492)
- SMIServiceWrapper.exe (PID: 7808)
- ExecuteBatch-Win.exe (PID: 8000)
- SMIServiceWrapper.exe (PID: 8128)
- SMIServiceWrapper.exe (PID: 8176)
- SMIRegistryTool.exe (PID: 7228)
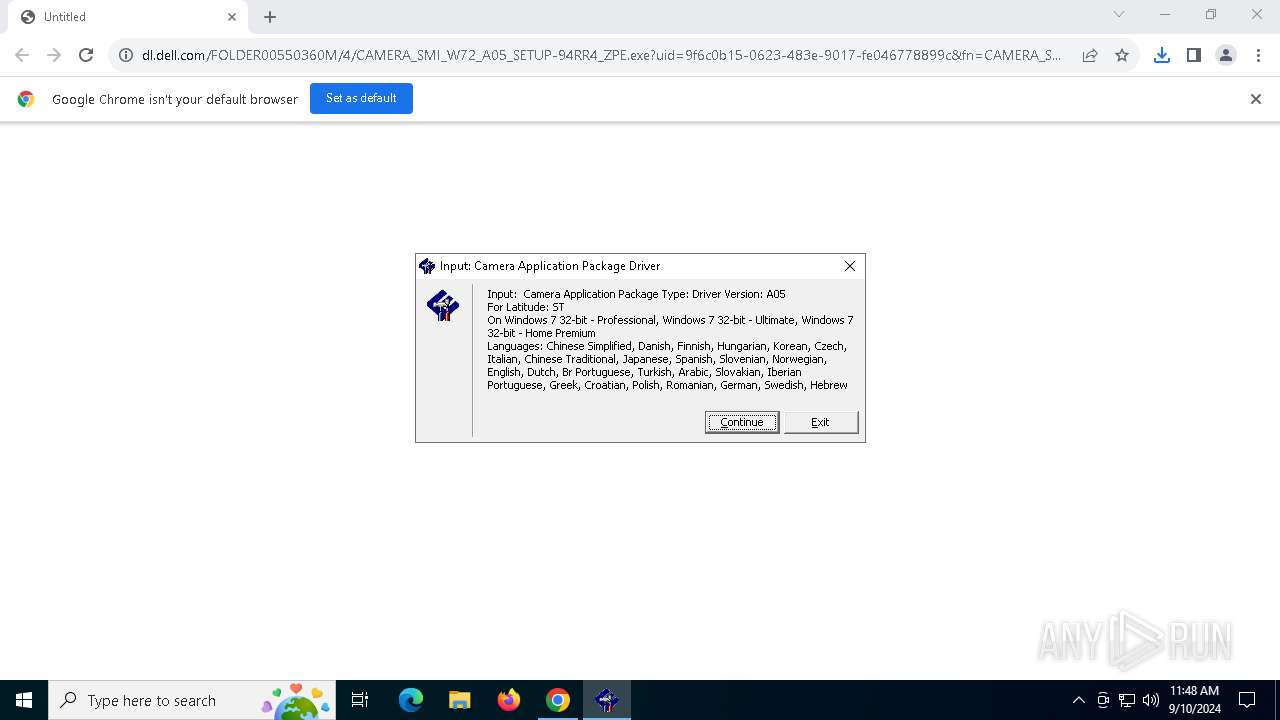
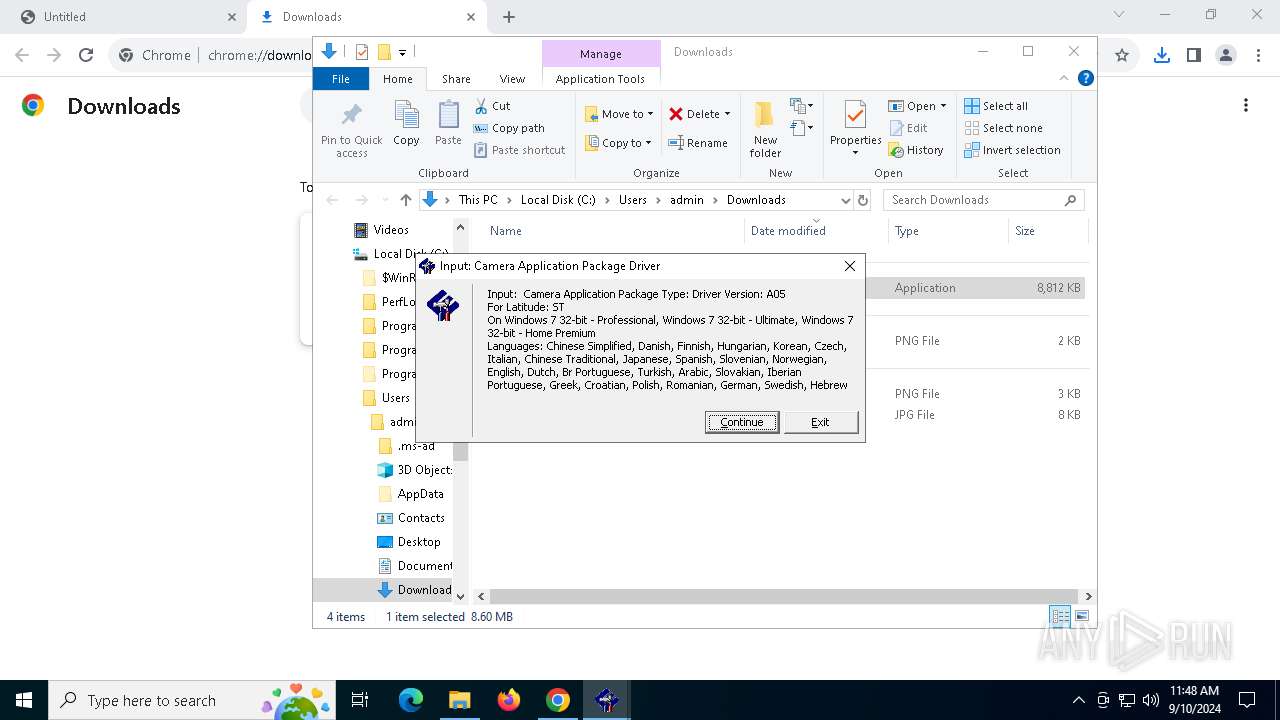
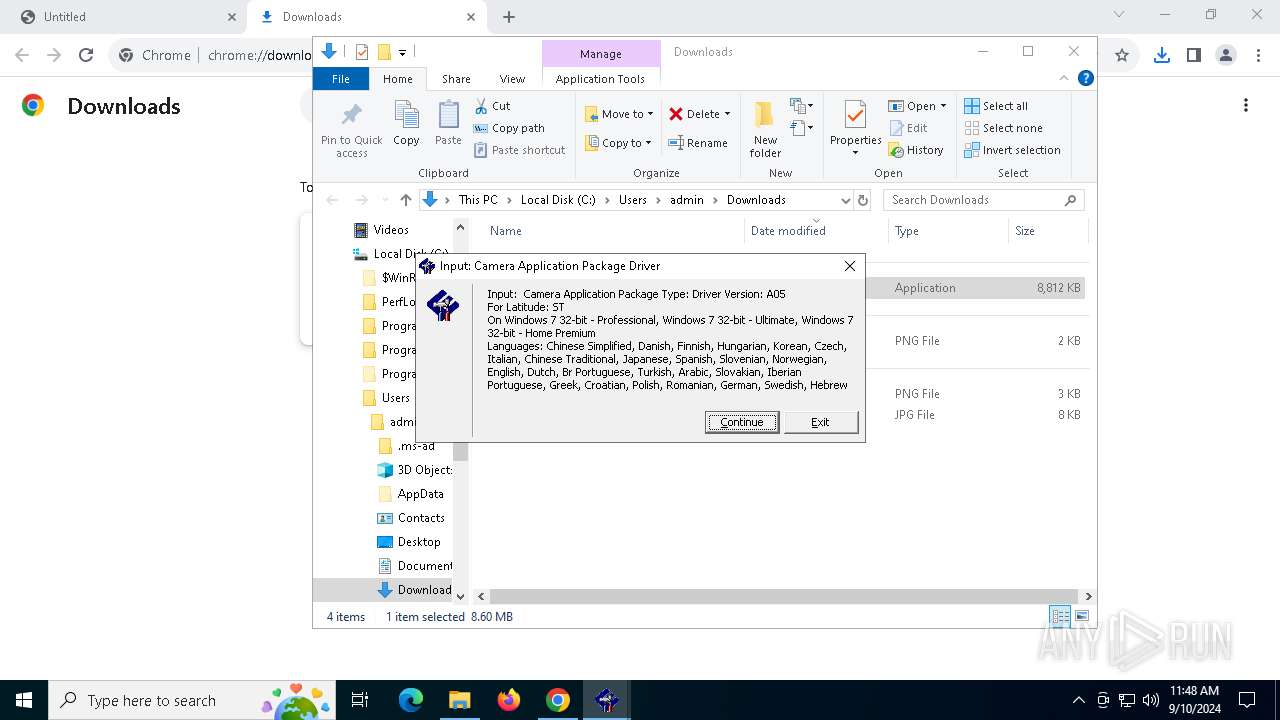
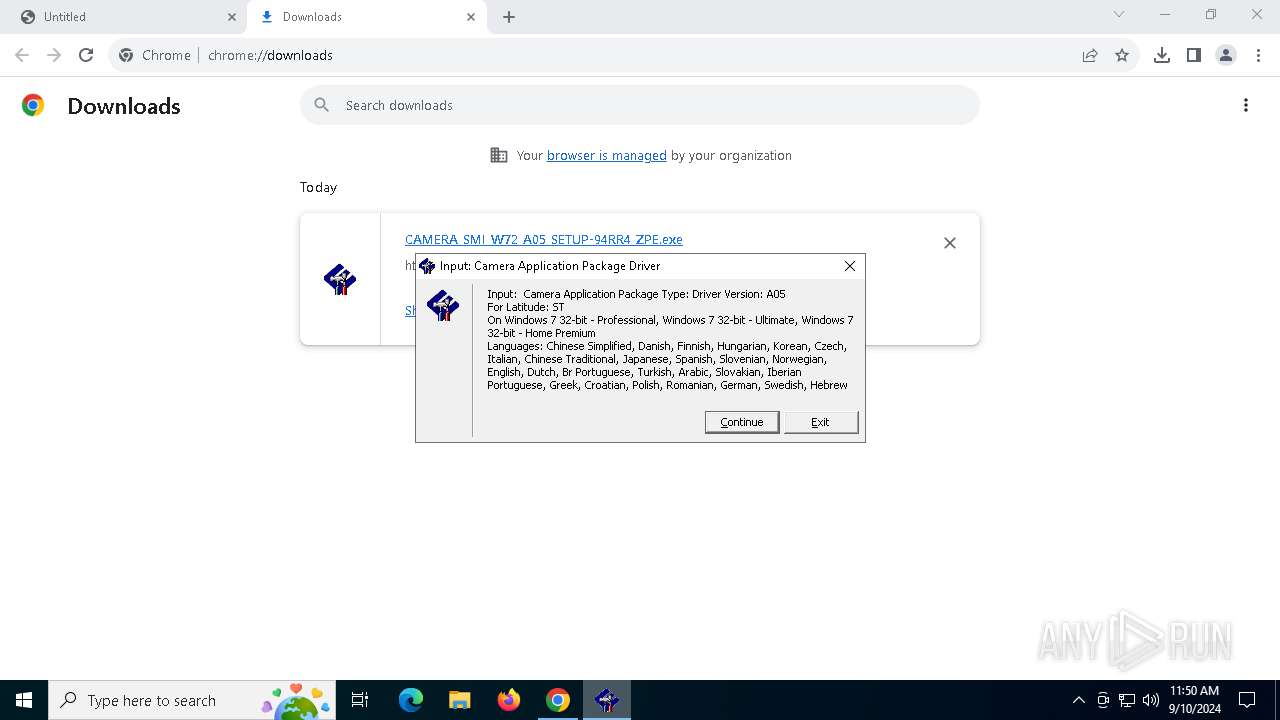
Checks supported languages
- CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe (PID: 3972)
- CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe (PID: 1440)
- CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe (PID: 4060)
- setup.exe (PID: 4732)
- ISBEW64.exe (PID: 1828)
- SMIServiceWrapper.exe (PID: 2820)
- XYNTService.exe (PID: 3352)
- XYNTService.exe (PID: 5376)
- XYNTService.exe (PID: 5520)
- IS.exe (PID: 6396)
- ExecuteBatch-Win.exe (PID: 1184)
- SMIServiceWrapper.exe (PID: 3272)
- XYNTService.exe (PID: 6464)
- ExecuteBatch-Win.exe (PID: 1124)
- XYNTService.exe (PID: 6628)
- ExecuteBatch-Win.exe (PID: 736)
- ExecuteBatch-Win.exe (PID: 7304)
- CheckVcamReg.exe (PID: 7336)
- SMIServiceWrapper.exe (PID: 7388)
- MPTool.exe (PID: 7176)
- XYNTService.exe (PID: 7488)
- XYNTService.exe (PID: 7536)
- ExecuteBatch-Win.exe (PID: 7572)
- SMIServiceWrapper.exe (PID: 7660)
- XYNTService.exe (PID: 7428)
- XYNTService.exe (PID: 7852)
- XYNTService.exe (PID: 7752)
- SMIServiceWrapper.exe (PID: 7920)
- XYNTService.exe (PID: 7960)
- XYNTService.exe (PID: 8020)
- XYNTService.exe (PID: 8068)
- ExecuteBatch-Win.exe (PID: 8100)
- SMIServiceWrapper.exe (PID: 8180)
- XYNTService.exe (PID: 7300)
- SMIServiceWrapper.exe (PID: 7492)
- XYNTService.exe (PID: 2508)
- XYNTService.exe (PID: 7604)
- XYNTService.exe (PID: 7596)
- ExecuteBatch-Win.exe (PID: 7736)
- XYNTService.exe (PID: 6120)
- XYNTService.exe (PID: 7884)
- XYNTService.exe (PID: 6628)
- SMIServiceWrapper.exe (PID: 7940)
- SMIServiceWrapper.exe (PID: 2868)
- XYNTService.exe (PID: 8140)
- ExecuteBatch-Win.exe (PID: 7316)
- XYNTService.exe (PID: 8136)
- SMIServiceWrapper.exe (PID: 8104)
- XYNTService.exe (PID: 7992)
- SMIServiceWrapper.exe (PID: 7600)
- XYNTService.exe (PID: 4040)
- XYNTService.exe (PID: 7488)
- XYNTService.exe (PID: 7576)
- XYNTService.exe (PID: 7616)
- XYNTService.exe (PID: 7872)
- SMIServiceWrapper.exe (PID: 7788)
- XYNTService.exe (PID: 7696)
- ExecuteBatch-Win.exe (PID: 2576)
- SMIServiceWrapper.exe (PID: 8056)
- XYNTService.exe (PID: 8148)
- XYNTService.exe (PID: 7988)
- XYNTService.exe (PID: 8092)
- ExecuteBatch-Win.exe (PID: 7436)
- XYNTService.exe (PID: 6628)
- XYNTService.exe (PID: 7288)
- XYNTService.exe (PID: 8052)
- SMIServiceWrapper.exe (PID: 7624)
- SMIServiceWrapper.exe (PID: 8068)
- XYNTService.exe (PID: 8104)
- XYNTService.exe (PID: 7572)
- ExecuteBatch-Win.exe (PID: 7688)
- SMIServiceWrapper.exe (PID: 7644)
- XYNTService.exe (PID: 7636)
- XYNTService.exe (PID: 4192)
- XYNTService.exe (PID: 7712)
- SMIServiceWrapper.exe (PID: 7796)
- XYNTService.exe (PID: 7908)
- ExecuteBatch-Win.exe (PID: 6260)
- SMIServiceWrapper.exe (PID: 7228)
- XYNTService.exe (PID: 5052)
- XYNTService.exe (PID: 6100)
- XYNTService.exe (PID: 7312)
- XYNTService.exe (PID: 6020)
- SMIServiceWrapper.exe (PID: 7480)
- XYNTService.exe (PID: 376)
- ExecuteBatch-Win.exe (PID: 812)
- SMIServiceWrapper.exe (PID: 7808)
- XYNTService.exe (PID: 1132)
- XYNTService.exe (PID: 6516)
- SMIServiceWrapper.exe (PID: 7492)
- XYNTService.exe (PID: 2724)
- XYNTService.exe (PID: 7740)
- XYNTService.exe (PID: 7720)
- XYNTService.exe (PID: 7576)
- ExecuteBatch-Win.exe (PID: 8000)
- SMIServiceWrapper.exe (PID: 8176)
- XYNTService.exe (PID: 7792)
- XYNTService.exe (PID: 7220)
- XYNTService.exe (PID: 6368)
- SMIServiceWrapper.exe (PID: 8128)
- XYNTService.exe (PID: 7960)
- XYNTService.exe (PID: 7484)
- SMIRegistryTool.exe (PID: 7228)
- XYNTService.exe (PID: 7500)
Reads the computer name
- CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe (PID: 3972)
- CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe (PID: 1440)
- CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe (PID: 4060)
- setup.exe (PID: 4732)
- SMIServiceWrapper.exe (PID: 2820)
- XYNTService.exe (PID: 3352)
- XYNTService.exe (PID: 5376)
- XYNTService.exe (PID: 5520)
- IS.exe (PID: 6396)
- ISBEW64.exe (PID: 1828)
- SMIServiceWrapper.exe (PID: 3272)
- XYNTService.exe (PID: 6628)
- XYNTService.exe (PID: 6464)
- ExecuteBatch-Win.exe (PID: 736)
- ExecuteBatch-Win.exe (PID: 1124)
- MPTool.exe (PID: 7176)
- ExecuteBatch-Win.exe (PID: 7304)
- CheckVcamReg.exe (PID: 7336)
- SMIServiceWrapper.exe (PID: 7388)
- XYNTService.exe (PID: 7428)
- XYNTService.exe (PID: 7488)
- XYNTService.exe (PID: 7536)
- ExecuteBatch-Win.exe (PID: 7572)
- SMIServiceWrapper.exe (PID: 7660)
- XYNTService.exe (PID: 7960)
- XYNTService.exe (PID: 8020)
- XYNTService.exe (PID: 7752)
- XYNTService.exe (PID: 7852)
- SMIServiceWrapper.exe (PID: 7920)
- ExecuteBatch-Win.exe (PID: 8100)
- SMIServiceWrapper.exe (PID: 8180)
- XYNTService.exe (PID: 7300)
- XYNTService.exe (PID: 8068)
- SMIServiceWrapper.exe (PID: 7492)
- XYNTService.exe (PID: 7596)
- XYNTService.exe (PID: 2508)
- XYNTService.exe (PID: 6120)
- XYNTService.exe (PID: 7604)
- ExecuteBatch-Win.exe (PID: 7736)
- XYNTService.exe (PID: 6628)
- SMIServiceWrapper.exe (PID: 2868)
- XYNTService.exe (PID: 7884)
- SMIServiceWrapper.exe (PID: 7940)
- XYNTService.exe (PID: 8140)
- XYNTService.exe (PID: 8136)
- ExecuteBatch-Win.exe (PID: 7316)
- SMIServiceWrapper.exe (PID: 8104)
- XYNTService.exe (PID: 7992)
- XYNTService.exe (PID: 4040)
- XYNTService.exe (PID: 7488)
- SMIServiceWrapper.exe (PID: 7600)
- XYNTService.exe (PID: 7616)
- XYNTService.exe (PID: 7576)
- ExecuteBatch-Win.exe (PID: 2576)
- SMIServiceWrapper.exe (PID: 7788)
- XYNTService.exe (PID: 7696)
- XYNTService.exe (PID: 7872)
- SMIServiceWrapper.exe (PID: 8056)
- XYNTService.exe (PID: 8148)
- XYNTService.exe (PID: 7988)
- XYNTService.exe (PID: 8092)
- XYNTService.exe (PID: 6628)
- SMIServiceWrapper.exe (PID: 8068)
- XYNTService.exe (PID: 7288)
- XYNTService.exe (PID: 8052)
- ExecuteBatch-Win.exe (PID: 7436)
- SMIServiceWrapper.exe (PID: 7624)
- XYNTService.exe (PID: 7572)
- XYNTService.exe (PID: 7636)
- XYNTService.exe (PID: 8104)
- ExecuteBatch-Win.exe (PID: 7688)
- SMIServiceWrapper.exe (PID: 7644)
- XYNTService.exe (PID: 4192)
- XYNTService.exe (PID: 7712)
- SMIServiceWrapper.exe (PID: 7796)
- XYNTService.exe (PID: 6100)
- XYNTService.exe (PID: 7908)
- XYNTService.exe (PID: 5052)
- ExecuteBatch-Win.exe (PID: 6260)
- SMIServiceWrapper.exe (PID: 7228)
- XYNTService.exe (PID: 7312)
- SMIServiceWrapper.exe (PID: 7480)
- XYNTService.exe (PID: 376)
- XYNTService.exe (PID: 6020)
- XYNTService.exe (PID: 1132)
- XYNTService.exe (PID: 6516)
- ExecuteBatch-Win.exe (PID: 812)
- SMIServiceWrapper.exe (PID: 7808)
- XYNTService.exe (PID: 2724)
- XYNTService.exe (PID: 7740)
- SMIServiceWrapper.exe (PID: 7492)
- XYNTService.exe (PID: 7576)
- ExecuteBatch-Win.exe (PID: 8000)
- SMIServiceWrapper.exe (PID: 8176)
- XYNTService.exe (PID: 7720)
- XYNTService.exe (PID: 7792)
- XYNTService.exe (PID: 7220)
- XYNTService.exe (PID: 6368)
- SMIServiceWrapper.exe (PID: 8128)
- XYNTService.exe (PID: 7960)
- XYNTService.exe (PID: 7484)
- SMIRegistryTool.exe (PID: 7228)
- XYNTService.exe (PID: 7500)
Executable content was dropped or overwritten
- chrome.exe (PID: 1568)
- chrome.exe (PID: 7528)
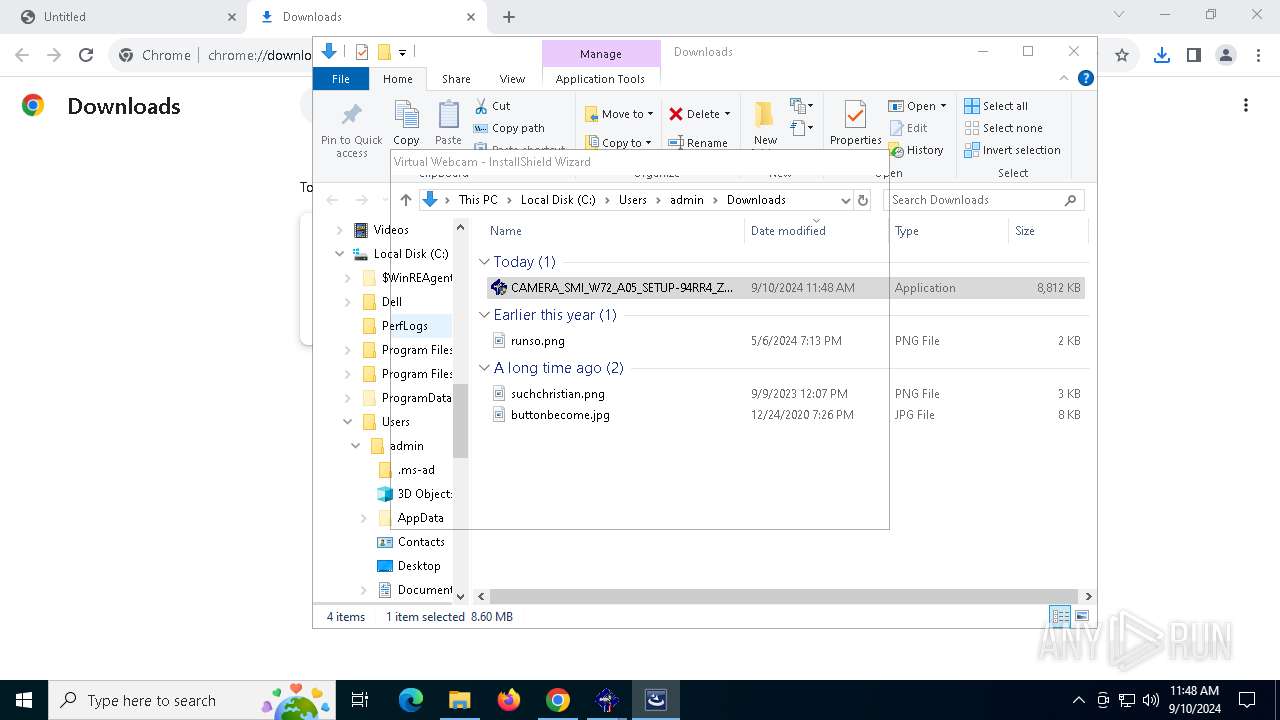
Manual execution by a user
- CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe (PID: 2684)
- CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe (PID: 1440)
- CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe (PID: 6912)
- CAMERA_SMI_W72_A05_SETUP-94RR4_ZPE.exe (PID: 4060)
Sends debugging messages
- setup.exe (PID: 4732)
- MPTool.exe (PID: 7176)
- CheckVcamReg.exe (PID: 7336)
Application launched itself
- chrome.exe (PID: 1568)
Process checks computer location settings
- SMIServiceWrapper.exe (PID: 2820)
- setup.exe (PID: 4732)
- SMIServiceWrapper.exe (PID: 3272)
- CheckVcamReg.exe (PID: 7336)
- SMIServiceWrapper.exe (PID: 7388)
- SMIServiceWrapper.exe (PID: 7660)
- SMIServiceWrapper.exe (PID: 7920)
- SMIServiceWrapper.exe (PID: 8180)
- SMIServiceWrapper.exe (PID: 7492)
- SMIServiceWrapper.exe (PID: 2868)
- SMIServiceWrapper.exe (PID: 7940)
- SMIServiceWrapper.exe (PID: 8104)
- SMIServiceWrapper.exe (PID: 7600)
- SMIServiceWrapper.exe (PID: 7788)
- SMIServiceWrapper.exe (PID: 8056)
- SMIServiceWrapper.exe (PID: 8068)
- SMIServiceWrapper.exe (PID: 7624)
- SMIServiceWrapper.exe (PID: 7644)
- SMIServiceWrapper.exe (PID: 7480)
- SMIServiceWrapper.exe (PID: 7228)
- SMIServiceWrapper.exe (PID: 7492)
- SMIServiceWrapper.exe (PID: 7808)
- SMIServiceWrapper.exe (PID: 8176)
- SMIServiceWrapper.exe (PID: 8128)
- SMIServiceWrapper.exe (PID: 7796)
Create files in a temporary directory
- IS.exe (PID: 6396)
- XYNTService.exe (PID: 3352)
- MPTool.exe (PID: 7176)
Creates files in the program directory
- IS.exe (PID: 6396)
Reads the software policy settings
- slui.exe (PID: 2024)
- slui.exe (PID: 3880)
Checks proxy server information
- slui.exe (PID: 3880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
374
Monitored processes
232
Malicious processes
4
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Program Files (x86)\SMI\Virtual Webcam\DriverPackage\XYNTService.exe" -i | C:\Program Files (x86)\SMI\Virtual Webcam\DriverPackage\XYNTService.exe | — | SMIServiceWrapper.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | XYNTService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 400 | "C:\Windows\System32\regedit.exe" /s "C:\Users\Public\Documents\SMI\Virtual WebCam\DriverPackage\{ADCF9E5F-B7CB-43ED-8003-21FA8E98D1E5}.reg" | C:\Windows\SysWOW64\regedit.exe | — | SMIRegistryTool.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | C:\Users\admin\AppData\Local\Temp\{5AB04AEC-9F22-4B3A-8655-BA5A4684859C}\{FE7AD27A-62B1-44F6-B69C-25D1ECA94F5D}\ExecuteBatch-Win.exe -delete_reg | C:\Users\admin\AppData\Local\Temp\{5AB04AEC-9F22-4B3A-8655-BA5A4684859C}\{FE7AD27A-62B1-44F6-B69C-25D1ECA94F5D}\ExecuteBatch-Win.exe | — | IS.exe | |||||||||||
User: admin Company: SiliconMotion Inc. Integrity Level: HIGH Description: ExecuteBatch-Win.exe Exit code: 2 Version: 1, 0, 0, 17 Modules
| |||||||||||||||
| 812 | "C:\Program Files (x86)\SMI\Virtual Webcam\DriverPackage\ExecuteBatch-Win.exe" | C:\Program Files (x86)\SMI\Virtual Webcam\DriverPackage\ExecuteBatch-Win.exe | — | XYNTService.exe | |||||||||||
User: SYSTEM Company: SiliconMotion Inc. Integrity Level: SYSTEM Description: ExecuteBatch-Win.exe Exit code: 2 Version: 1, 1, 0, 18 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5344 --field-trial-handle=1844,i,12473452919216211881,227656907225234020,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1084 | C:\WINDOWS\system32\cmd.exe /c rmdir /s /q "C:\Users\Public\Documents\SMI" | C:\Windows\SysWOW64\cmd.exe | — | ExecuteBatch-Win.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1124 | C:\Users\admin\AppData\Local\Temp\{5AB04AEC-9F22-4B3A-8655-BA5A4684859C}\{FE7AD27A-62B1-44F6-B69C-25D1ECA94F5D}\ExecuteBatch-Win.exe -check_ax_loaded vcam.ax vcam2.ax | C:\Users\admin\AppData\Local\Temp\{5AB04AEC-9F22-4B3A-8655-BA5A4684859C}\{FE7AD27A-62B1-44F6-B69C-25D1ECA94F5D}\ExecuteBatch-Win.exe | — | IS.exe | |||||||||||
User: admin Company: SiliconMotion Inc. Integrity Level: HIGH Description: ExecuteBatch-Win.exe Exit code: 2 Version: 1, 0, 0, 17 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\SMI\Virtual Webcam\DriverPackage\XYNTService.exe" -r ExecuteBatch-Win | C:\Program Files (x86)\SMI\Virtual Webcam\DriverPackage\XYNTService.exe | — | SMIServiceWrapper.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1184 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | XYNTService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
26 589
Read events
26 308
Write events
254
Delete events
27
Modification events
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1568) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5088) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000418A89577703DB01 | |||
| (PID) Process: | (6396) IS.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000AD5DCD6E7703DB01FC180000D4180000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5980) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000AD5DCD6E7703DB015C170000100A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5980) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000026F2086F7703DB015C170000100A0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5980) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000026F2086F7703DB015C170000100A0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
83
Suspicious files
165
Text files
112
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF12aaaf.TMP | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF12aaaf.TMP | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
| 1568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | text | |
MD5:4B26172585D38A3DD6697E274D0608AC | SHA256:85899A7AF1BD1939EA8264009EC427930FC5C092C8C3193984D6391526319268 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
51
DNS requests
36
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2640 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
2640 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
2640 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
2640 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
2640 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p2zbkxfgkqyr6ljey2oe3bnzoy_2023.11.29.1201/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.11.29.1201_all_acqy67ncydhwie54b6ghdtndubgq.crx3 | unknown | — | — | whitelisted |
2640 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p2zbkxfgkqyr6ljey2oe3bnzoy_2023.11.29.1201/ggkkehgbnfjpeggfpleeakpidbkibbmn_2023.11.29.1201_all_acqy67ncydhwie54b6ghdtndubgq.crx3 | unknown | — | — | whitelisted |
2640 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
2640 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
2640 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nznkibw2gzgvywaue5zmags5nu_1067/efniojlnjndmcbiieegkicadnoecjjef_1067_all_accpz24wozzb5sqf573rya5dh2jq.crx3 | unknown | — | — | whitelisted |
2640 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6012 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6380 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1568 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5712 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5712 | chrome.exe | 2.16.164.99:443 | dl.dell.com | Akamai International B.V. | NL | whitelisted |
1568 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
6012 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6012 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
dl.dell.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
setup.exe | i=0 setup.exe"
|
setup.exe | Exe=c:\dell\drivers\94rr4\IS.exe
|
setup.exe | Open reg key fail in WOW64 platform (2)
|
setup.exe | ROUND <1> ID =6396
|
MPTool.exe | m_vecVID[0]=090c m_vecPID[0]=037c
|
MPTool.exe | m_vecVID[1]=090c m_vecPID[1]=037d
|
MPTool.exe | strParam=-s
|
MPTool.exe | ScanUSBProc--end
|
CheckVcamReg.exe | CheckVcamRegIsExist
|
CheckVcamReg.exe | CheckSourceFilterRegistry Fail , No Find usbdev_video.reg !!!
|