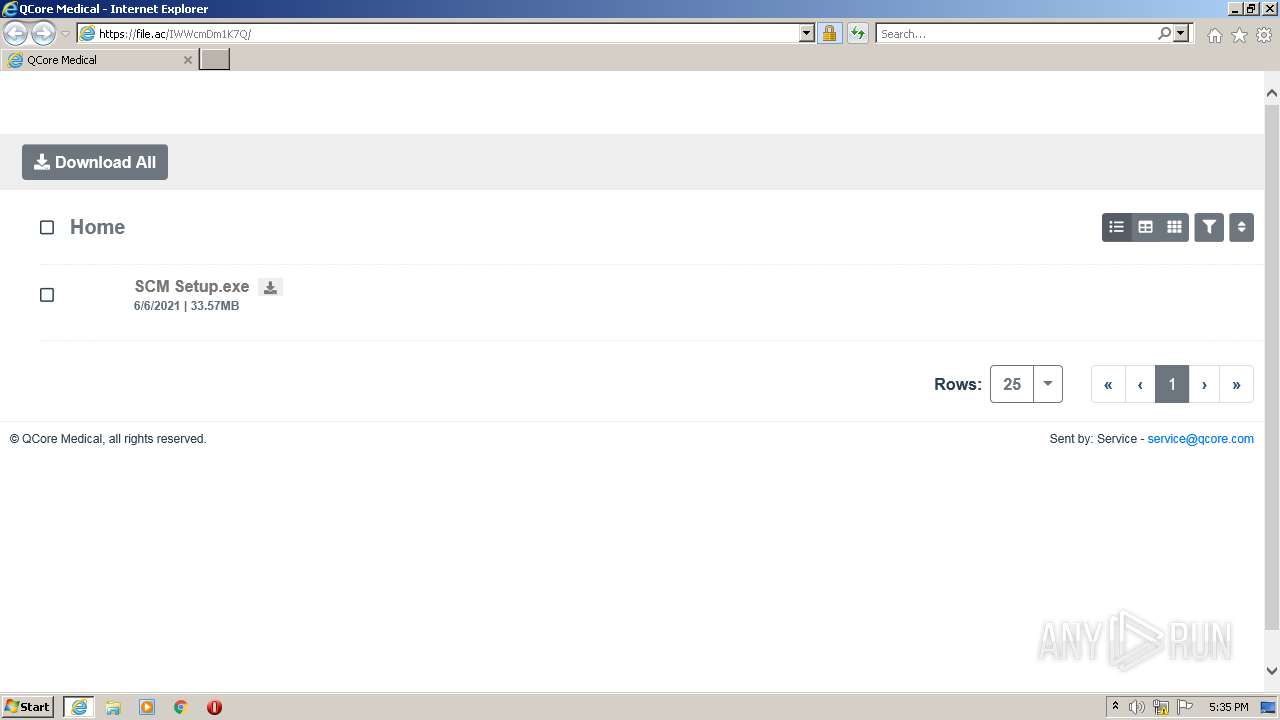
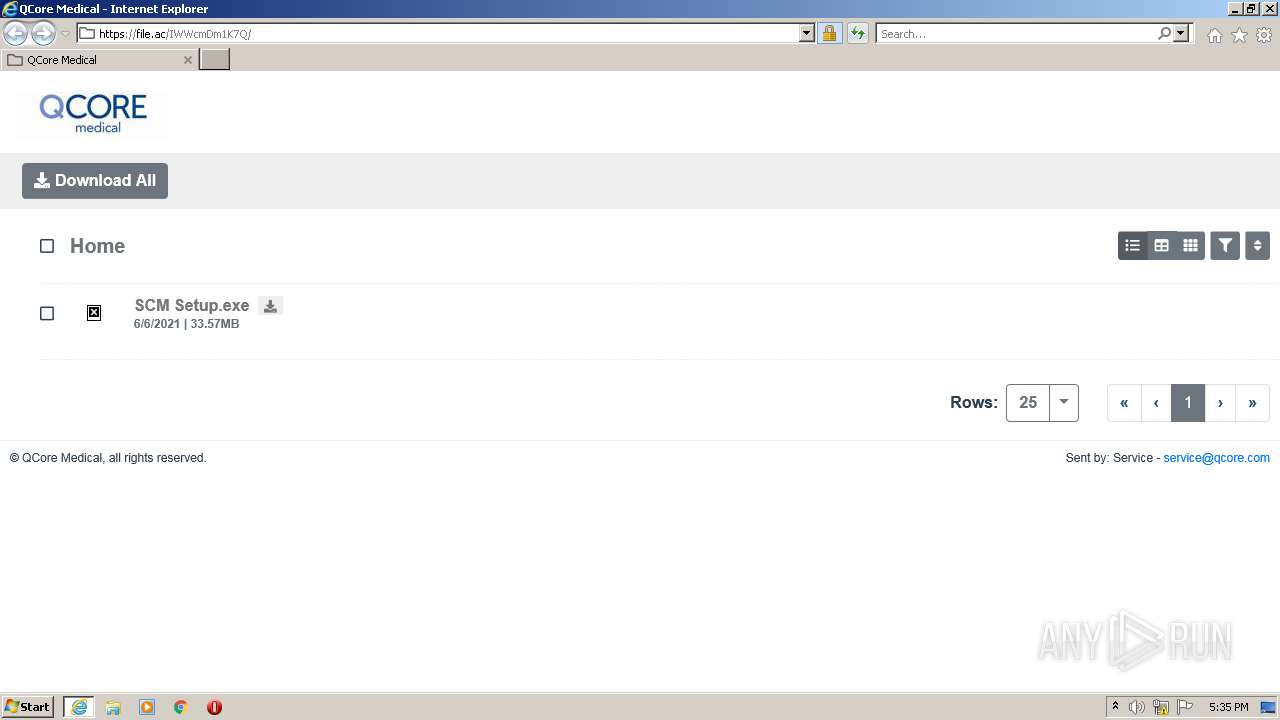
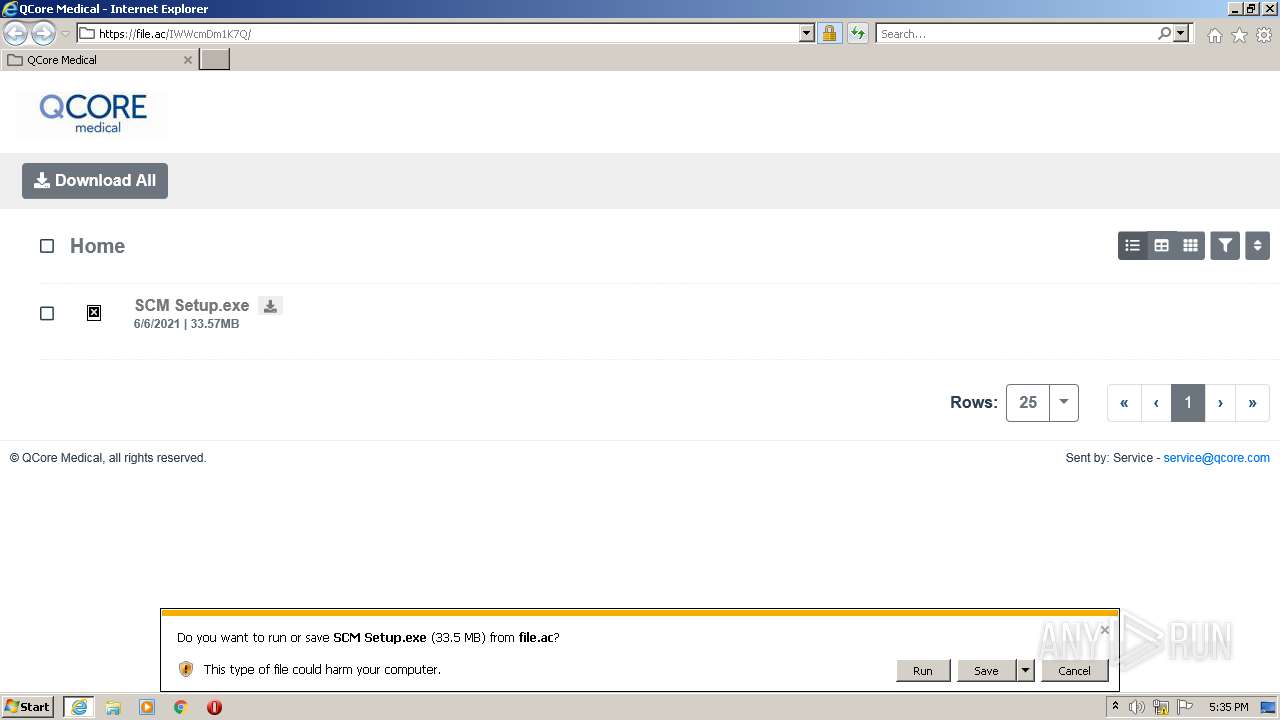
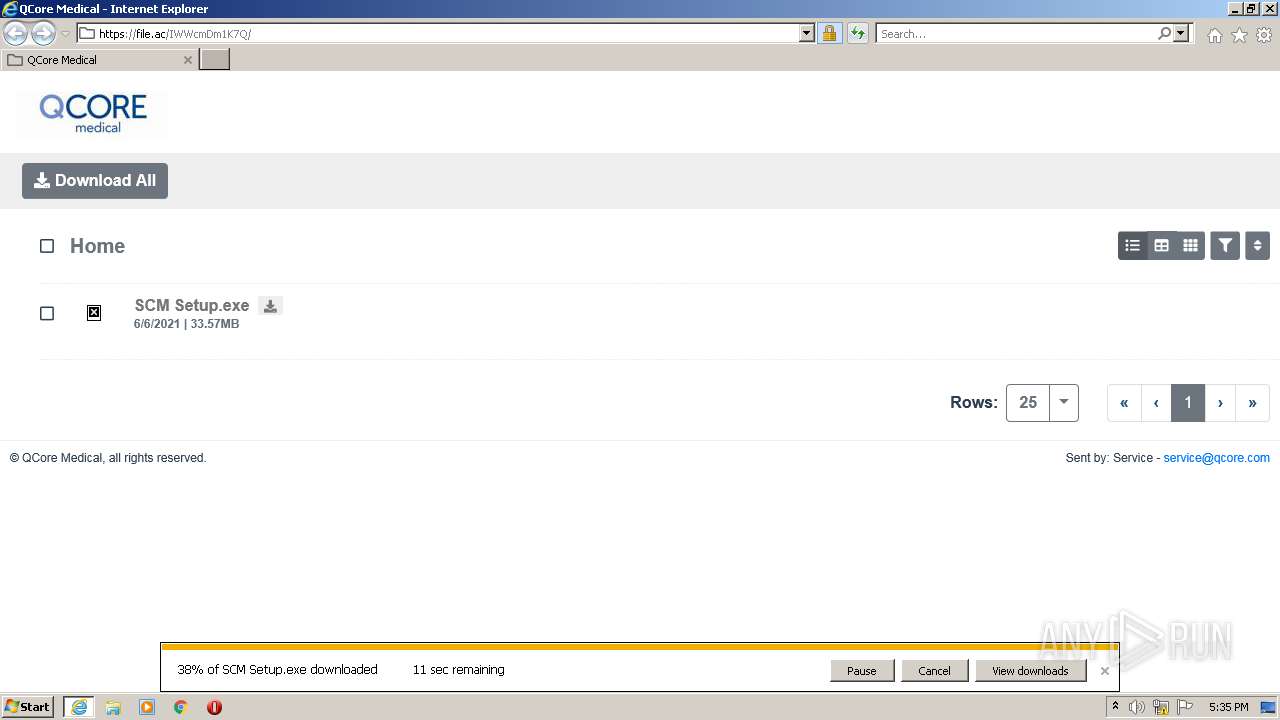
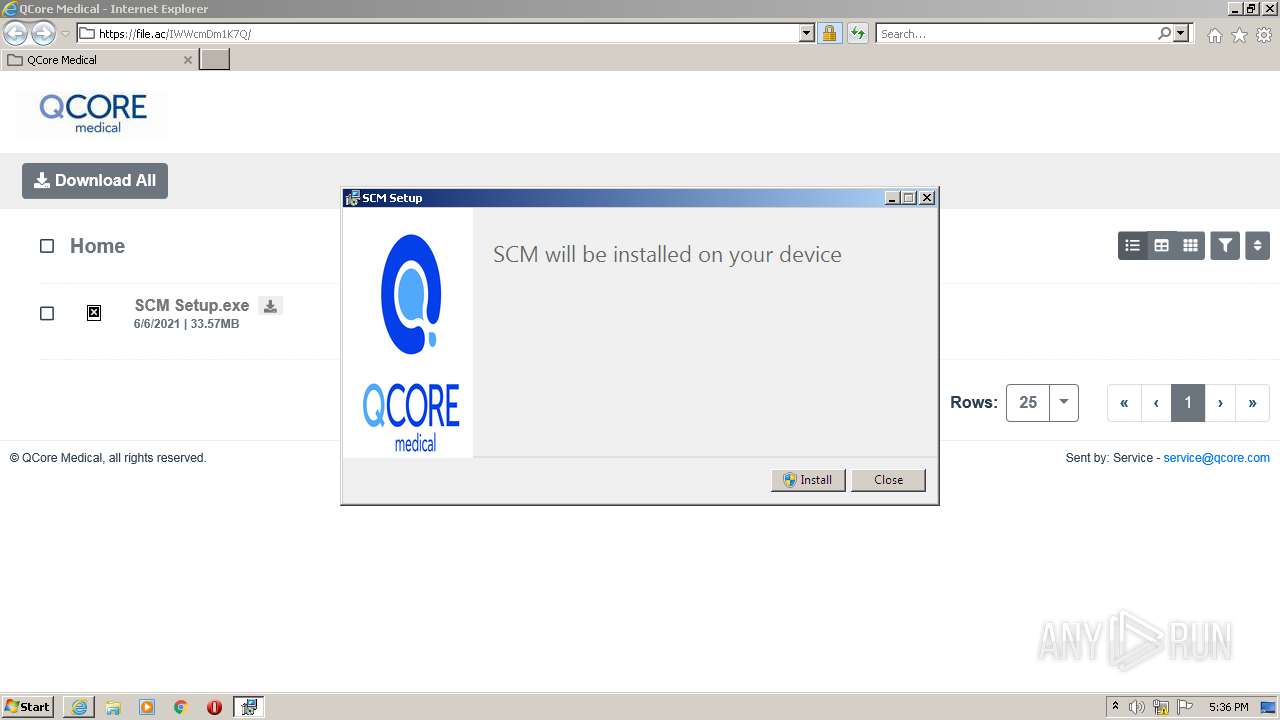
| URL: | https://file.ac/IWWcmDm1K7Q/ |
| Full analysis: | https://app.any.run/tasks/71986506-b36a-4c58-a5e6-005374a584a3 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 16:35:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 73000D43C51E457679B03F28504DD449 |
| SHA1: | 5EB49222F7E742863F917F98B6B192FD609AB45B |
| SHA256: | 4C3EC5CCC04559867652C8D42D427831B1F96183D0EB112AA10DCF7B2E40B32C |
| SSDEEP: | 3:N8Qan:2Qa |
MALICIOUS
Drops executable file immediately after starts
- iexplore.exe (PID: 3904)
- SCM Setup.exe (PID: 2268)
- SCM Setup.exe (PID: 1952)
Application was dropped or rewritten from another process
- SCM Setup.exe (PID: 2268)
- SCM Setup.exe (PID: 1952)
Loads dropped or rewritten executable
- SCM Setup.exe (PID: 1952)
SUSPICIOUS
Drops a file with a compile date too recent
- iexplore.exe (PID: 3904)
- SCM Setup.exe (PID: 2268)
- SCM Setup.exe (PID: 1952)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3904)
- SCM Setup.exe (PID: 2268)
- SCM Setup.exe (PID: 1952)
Checks supported languages
- SCM Setup.exe (PID: 2268)
- SCM Setup.exe (PID: 1952)
Searches for installed software
- SCM Setup.exe (PID: 1952)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3904)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3476)
Reads the computer name
- iexplore.exe (PID: 3904)
- iexplore.exe (PID: 3476)
Checks supported languages
- iexplore.exe (PID: 3904)
- iexplore.exe (PID: 3476)
Application launched itself
- iexplore.exe (PID: 3476)
Reads settings of System Certificates
- iexplore.exe (PID: 3904)
- iexplore.exe (PID: 3476)
Checks Windows Trust Settings
- iexplore.exe (PID: 3904)
- iexplore.exe (PID: 3476)
Changes settings of System certificates
- iexplore.exe (PID: 3476)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3476)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3476)
Reads internet explorer settings
- iexplore.exe (PID: 3904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
4
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1952 | "C:\Users\admin\AppData\Local\Temp\{D6B61DD5-3B95-4A80-BA51-BEEF136B1EF1}\.cr\SCM Setup.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\SCM Setup.exe" -burn.filehandle.attached=152 -burn.filehandle.self=160 | C:\Users\admin\AppData\Local\Temp\{D6B61DD5-3B95-4A80-BA51-BEEF136B1EF1}\.cr\SCM Setup.exe | SCM Setup.exe | ||||||||||||
User: admin Company: QCore Medical LTD. Integrity Level: MEDIUM Description: SCM Exit code: 0 Version: 2.2.0.65333 Modules
| |||||||||||||||
| 2268 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\SCM Setup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\SCM Setup.exe | iexplore.exe | ||||||||||||
User: admin Company: QCore Medical LTD. Integrity Level: MEDIUM Description: SCM Exit code: 0 Version: 2.2.0.65333 Modules
| |||||||||||||||
| 3476 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://file.ac/IWWcmDm1K7Q/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3904 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3476 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 326
Read events
16 171
Write events
145
Delete events
10
Modification events
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30977641 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30977641 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
4
Suspicious files
18
Text files
34
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3904 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6T384ZKC.txt | text | |
MD5:— | SHA256:— | |||
| 3904 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 3904 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 3904 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:— | SHA256:— | |||
| 3904 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C25BD1FF31269A066A75E13D91B56FC2 | der | |
MD5:— | SHA256:— | |||
| 3904 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
| 3904 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C25BD1FF31269A066A75E13D91B56FC2 | binary | |
MD5:— | SHA256:— | |||
| 3904 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3904 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\app.b9c9999f[1].js | text | |
MD5:— | SHA256:— | |||
| 3904 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\linkhome.578b0213[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
49
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3904 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQDu3NahAqedLAD%2BoUZIsvv3 | US | der | 472 b | whitelisted |
3904 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 2.18 Kb | whitelisted |
3476 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
3476 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
3904 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 1.42 Kb | whitelisted |
3904 | iexplore.exe | GET | 200 | 2.16.186.18:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgSbet8dS2F%2By7ehEOdVvZDRsA%3D%3D | unknown | der | 503 b | shared |
3904 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCwCT6kdIoTJo6Fg32CbzD3 | US | der | 472 b | whitelisted |
3476 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCwCT6kdIoTJo6Fg32CbzD3 | US | der | 472 b | whitelisted |
3476 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3904 | iexplore.exe | GET | 200 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?11ef6661bc1891a3 | US | compressed | 60.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3904 | iexplore.exe | 209.43.40.107:443 | file.ac | IQuest Internet | US | unknown |
3904 | iexplore.exe | 67.27.233.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3904 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | — | US | suspicious |
3904 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
3476 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3476 | iexplore.exe | 209.43.40.107:443 | file.ac | IQuest Internet | US | unknown |
3476 | iexplore.exe | 209.43.40.108:443 | www.static-assets.com | IQuest Internet | US | unknown |
3904 | iexplore.exe | 209.43.40.50:443 | sentry.lumanox.io | IQuest Internet | US | unknown |
3476 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3904 | iexplore.exe | 209.43.40.108:443 | www.static-assets.com | IQuest Internet | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
file.ac |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
sentry.lumanox.io |
| whitelisted |
www.static-assets.com |
| unknown |