| download: | index.html |
| Full analysis: | https://app.any.run/tasks/2d5c0fd3-927b-4d45-b74e-4b49858f8dd7 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 14:44:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 5ED1FEC52510DD2DB2EBC5F00C4A78FD |
| SHA1: | 27F2B3885E6D681C60532832137D8FD91248BEE5 |
| SHA256: | 4C3652E8A974A013B7450690D46A0B3FF0A77903DF294B6982FF15ECBC40145F |
| SSDEEP: | 1536:c+xbVX0NBlEFpfB1IFIIUIeah1yfgjU2fJkHEBUztBJsGHVNwv2:/W1dU2osHv2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 2912)
Reads settings of System Certificates
- iexplore.exe (PID: 3272)
- chrome.exe (PID: 2192)
Application launched itself
- iexplore.exe (PID: 2912)
- chrome.exe (PID: 2932)
Reads internet explorer settings
- iexplore.exe (PID: 3272)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3272)
Creates files in the user directory
- iexplore.exe (PID: 3272)
Changes settings of System certificates
- iexplore.exe (PID: 3272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| ContentType: | text/html; charset=utf-8 |
|---|---|
| HTTPEquivXUACompatible: | IE=edge,chrome=1 |
| CacheControl: | no-cache |
| viewport: | width=device-width, initial-scale=1.0, user-scalable=no, minimum-scale=1.0, maximum-scale=1.0 |
| HandheldFriendly: | |
| formatDetection: | address=no |
| csrfToken: | 97bc592b27a9ada2d9a4bb418ed0ebed |
| csrfParam: | csrf_token |
| Title: | РБК — новости, акции, курсы валют, доллар, евро |
| Description: | «РосБизнесКонсалтинг» — ведущая российская компания, работающая в сферах масс-медиа и информационных технологий. |
| Copyright: | «РосБизнесКонсалтинг» |
| twitterSite: | @ru_rbc |
| twitterCreator: | @ru_rbc |
| twitterTitle: | РБК – новости в реальном времени |
| twitterDescription: | Главные новости политики, экономики и бизнеса, комментарии аналитиков, финансовые данные с российских и мировых биржевых систем на сайте rbc.ru. |
| twitterImage: | РБК – новости в реальном времени |
| Keywords: | новости, доллар, политика, курс, акции, облигации, нефть, рубль, евро, финансы, экономика, банк, кредит, вексель, информация, фондовый, инвестиционный, рынок, недвижимость, валюта, эмитент, комментарии, аналитика, продаж/продажа, цена, компания, товары, исследование, прогноз, индекс, рейтинг, биржа, семинар, фондовый, ПИФ, доходность, IPO, паевой |
| ReplyTo: | webmaster@rbc.ru |
| twitterCard: | summary |
| msapplicationTileColor: | #ffffff |
| msapplicationTileImage: | //s.rbk.ru/v10_rbcnews_static/common/common-10.1.40/images/mstile-144x144.png |
| msapplicationSquare70x70logo: | //s.rbk.ru/v10_rbcnews_static/common/common-10.1.40/images/mstile-70x70.png |
| msapplicationSquare150x150logo: | //s.rbk.ru/v10_rbcnews_static/common/common-10.1.40/images/mstile-150x150.png |
| msapplicationSquare310x310logo: | //s.rbk.ru/v10_rbcnews_static/common/common-10.1.40/images/mstile-310x310.png |
| msapplicationWide310x150logo: | //s.rbk.ru/v10_rbcnews_static/common/common-10.1.40/images/mstile-310x150.png |
| themeColor: | #ffffff |
| appleItunesApp: | app-id=1172278022 |
Total processes
43
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=900,7005666894914942618,11307468040314065842,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7328176636596825948 --mojo-platform-channel-handle=1528 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2936 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
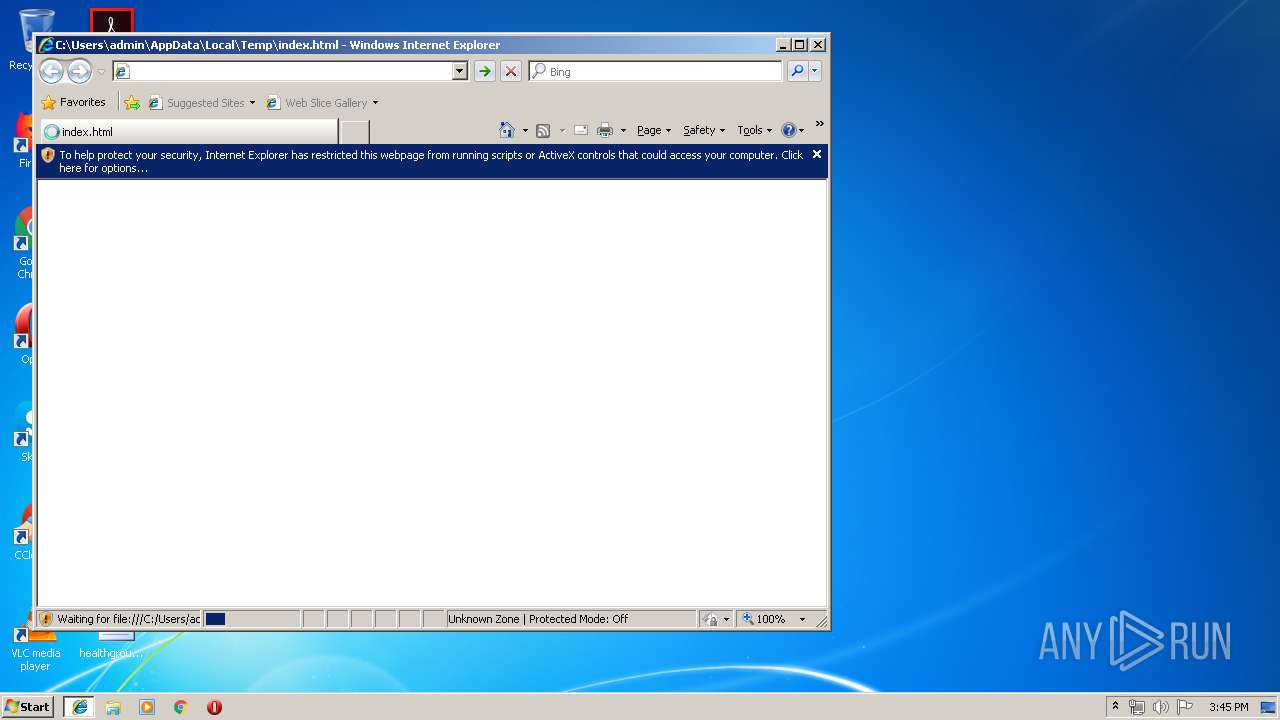
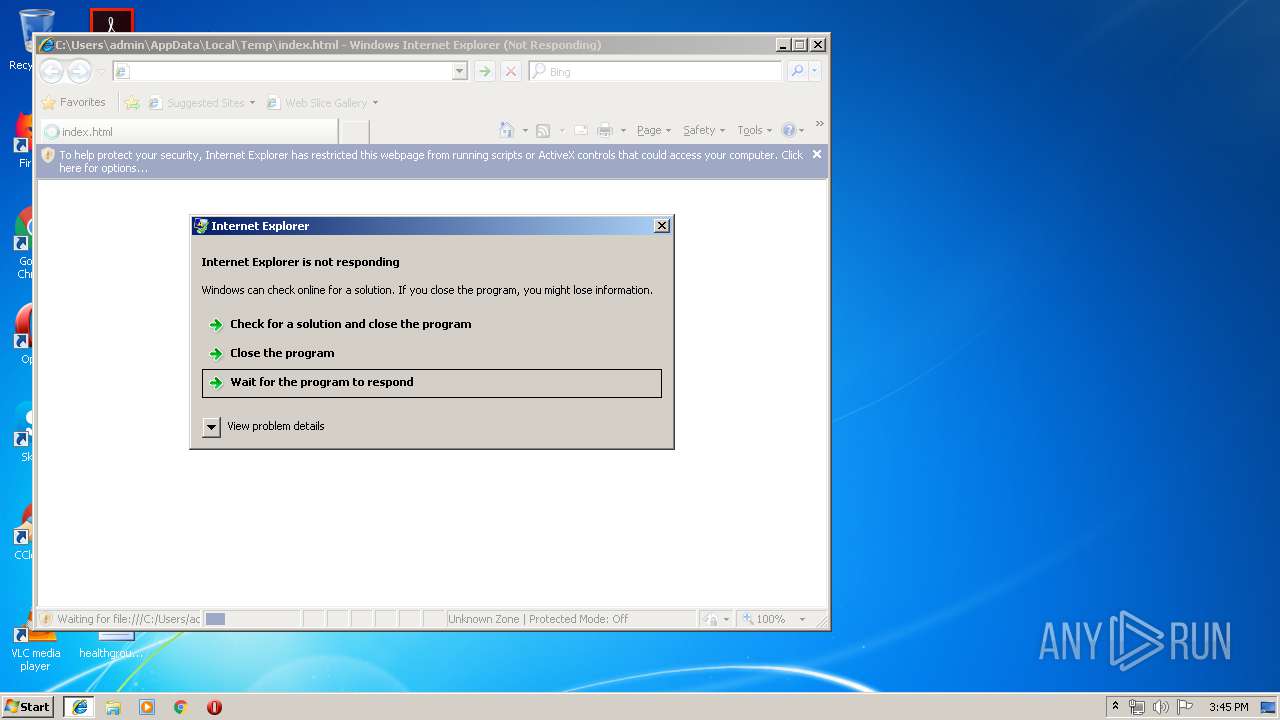
| 2912 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 3489660927 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,7005666894914942618,11307468040314065842,131072 --enable-features=PasswordImport --service-pipe-token=13908847208029060724 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13908847208029060724 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2300 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,7005666894914942618,11307468040314065842,131072 --enable-features=PasswordImport --service-pipe-token=17621300962004449366 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17621300962004449366 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3272 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2912 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebb0f18,0x6ebb0f28,0x6ebb0f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,7005666894914942618,11307468040314065842,131072 --enable-features=PasswordImport --service-pipe-token=3751427983474825506 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3751427983474825506 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=900,7005666894914942618,11307468040314065842,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10524514650556220642 --mojo-platform-channel-handle=956 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
767
Read events
652
Write events
108
Delete events
7
Modification events
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006E000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E307040001000F000E002D001000C602 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {147EC2F3-5F8D-11E9-B3B3-5254004A04AF} |
Value: 0 | |||
Executable files
0
Suspicious files
20
Text files
25
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2912 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3272 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@mail[2].txt | — | |
MD5:— | SHA256:— | |||
| 2912 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF98A30CA50DF2D369.TMP | — | |
MD5:— | SHA256:— | |||
| 2912 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF27175F6328486E9F.TMP | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
25
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2912 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2912 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3272 | iexplore.exe | 142.93.168.226:443 | cdn.onthe.io | — | CA | unknown |
4 | System | 185.72.229.2:445 | s.rbk.ru | Rosbusinessconsulting Cjsc | RU | unknown |
— | — | 185.72.229.2:137 | s.rbk.ru | Rosbusinessconsulting Cjsc | RU | unknown |
4 | System | 194.226.130.229:445 | www.tns-counter.ru | JSC ADFACT | RU | unknown |
4 | System | 194.226.130.226:445 | www.tns-counter.ru | JSC ADFACT | RU | unknown |
4 | System | 194.226.130.227:445 | www.tns-counter.ru | JSC ADFACT | RU | unknown |
4 | System | 194.226.130.228:445 | www.tns-counter.ru | JSC ADFACT | RU | suspicious |
4 | System | 194.226.130.228:139 | www.tns-counter.ru | JSC ADFACT | RU | suspicious |
4 | System | 87.250.251.119:445 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s.rbk.ru |
| whitelisted |
www.bing.com |
| whitelisted |
cdn.onthe.io |
| whitelisted |
top-fwz1.mail.ru |
| whitelisted |
www.tns-counter.ru |
| whitelisted |
mc.yandex.ru |
| whitelisted |
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |