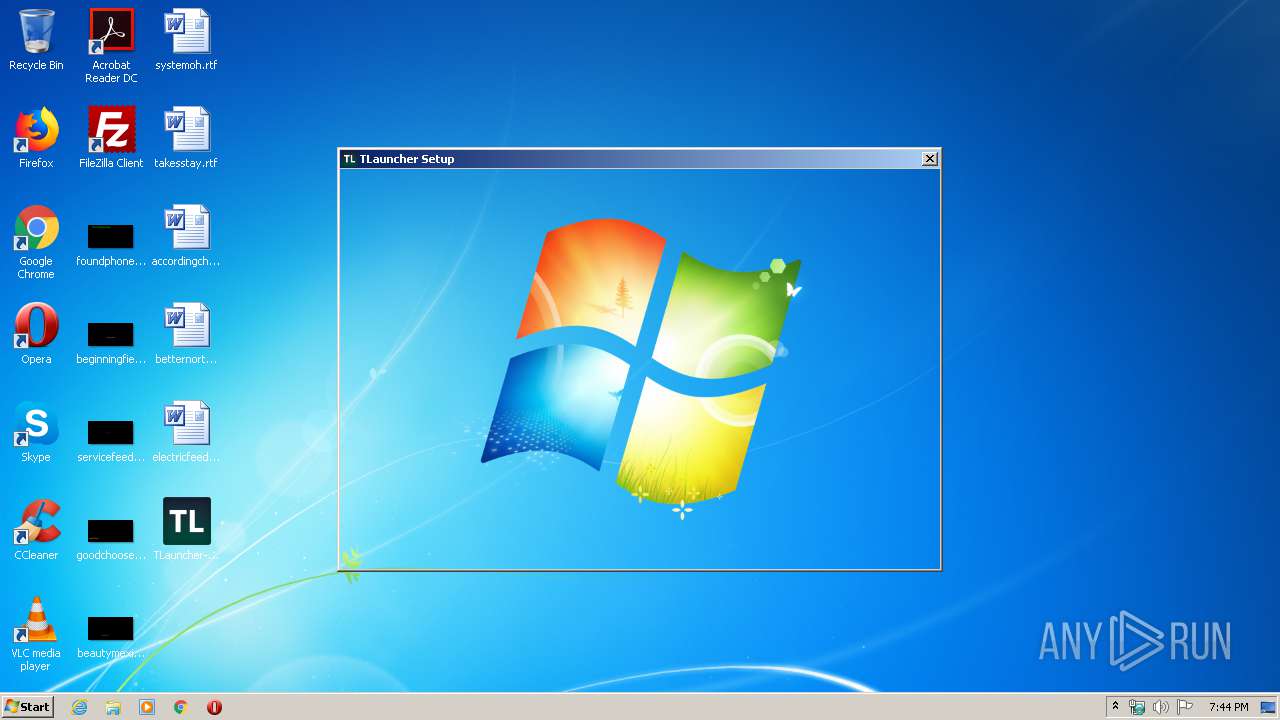
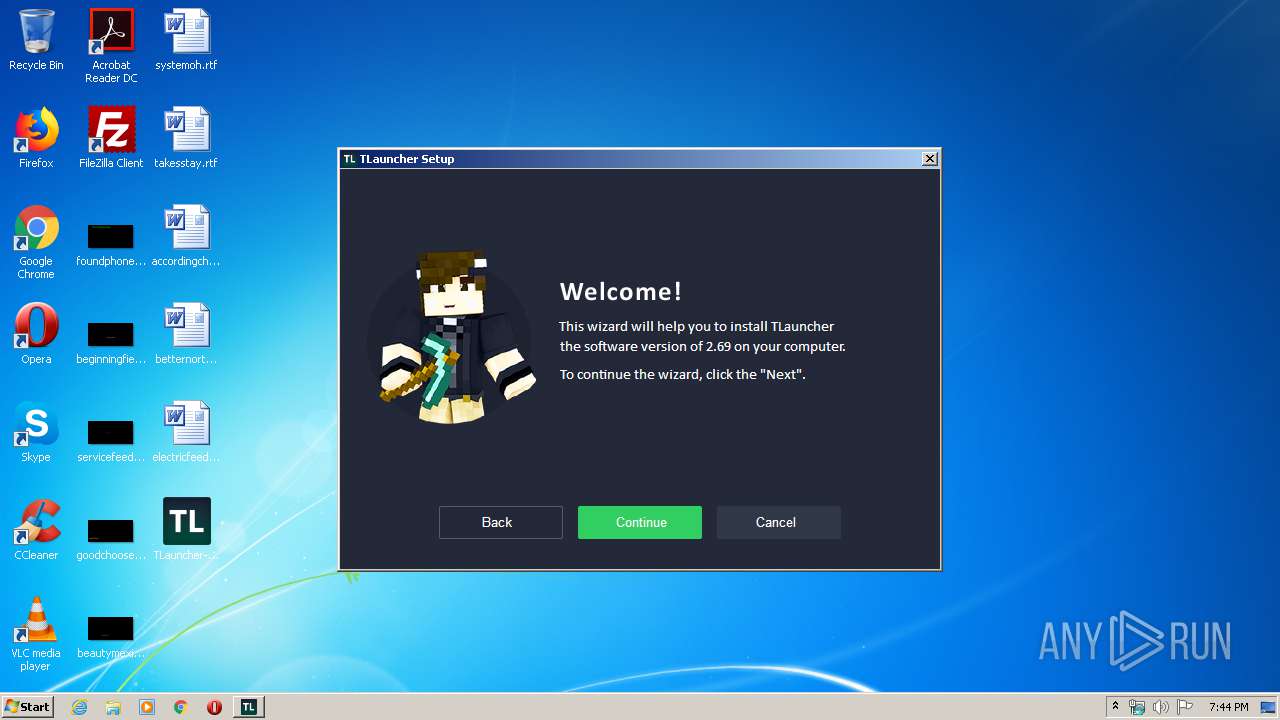
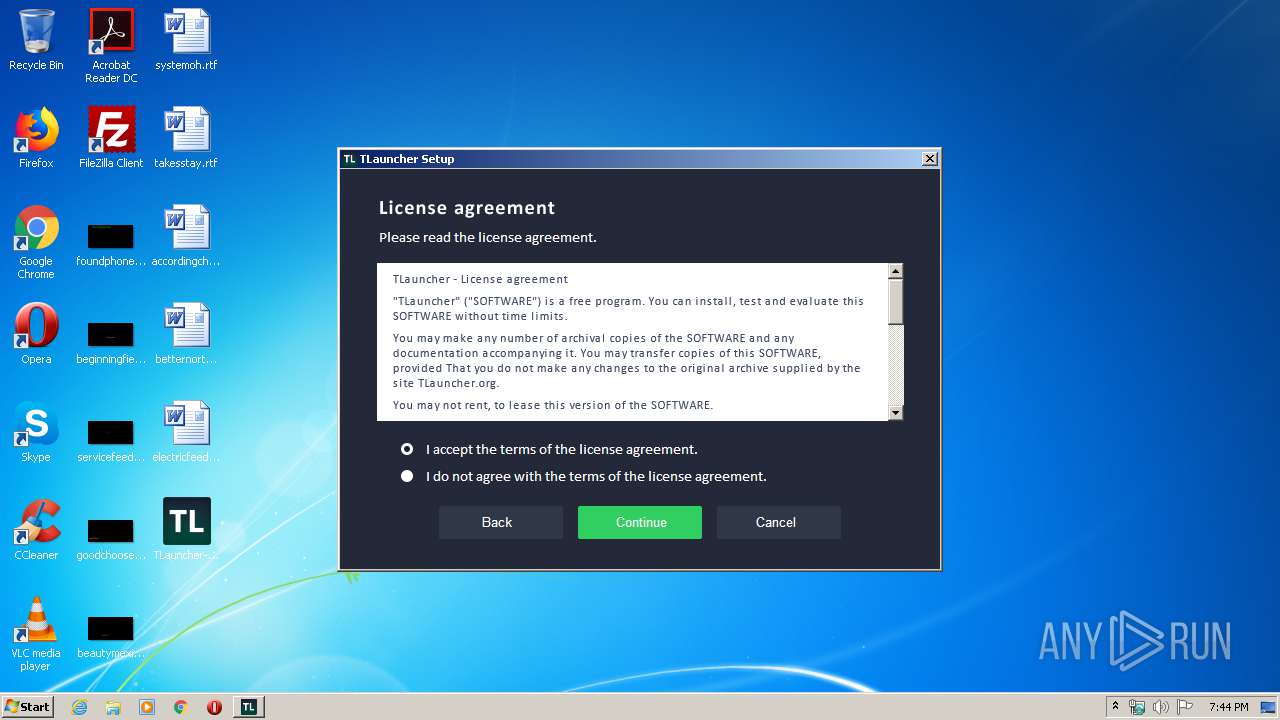
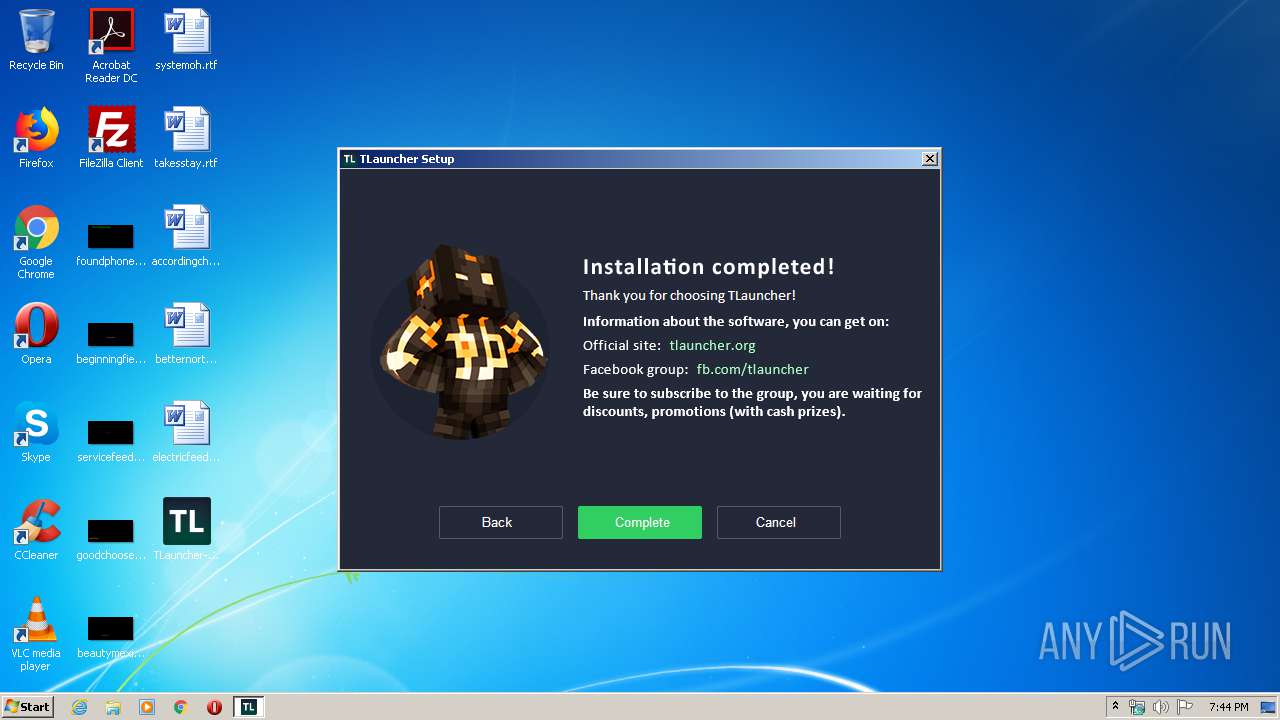
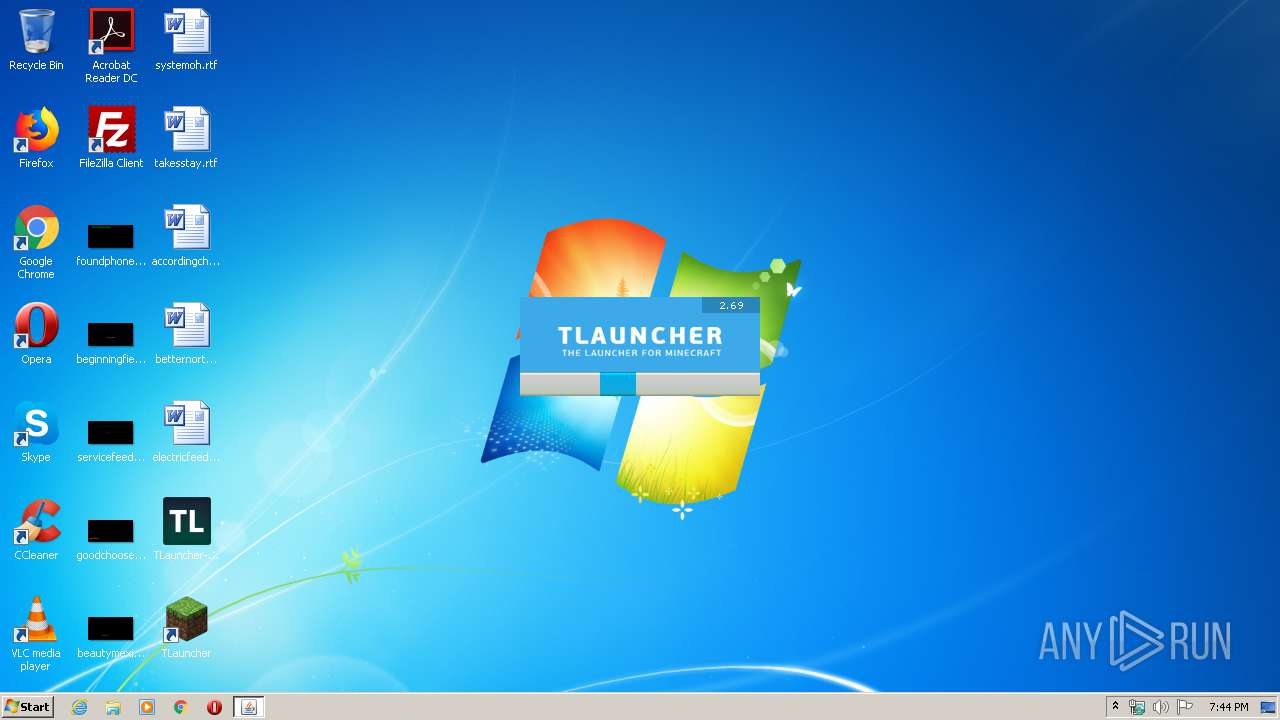
| File name: | TLauncher-2.69-Installer-0.5.2.exe |
| Full analysis: | https://app.any.run/tasks/226a79b1-6d7f-4a2b-ab1f-0618841fcae4 |
| Verdict: | Malicious activity |
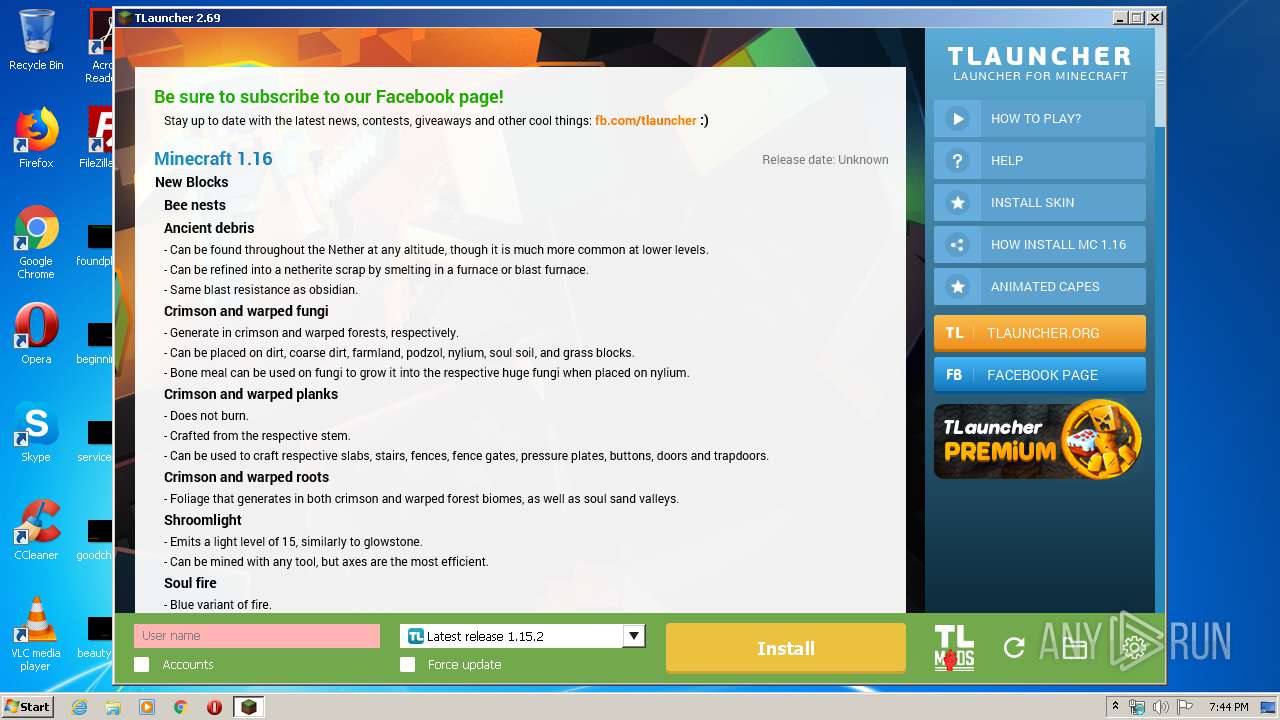
| Analysis date: | March 18, 2020, 19:43:37 |
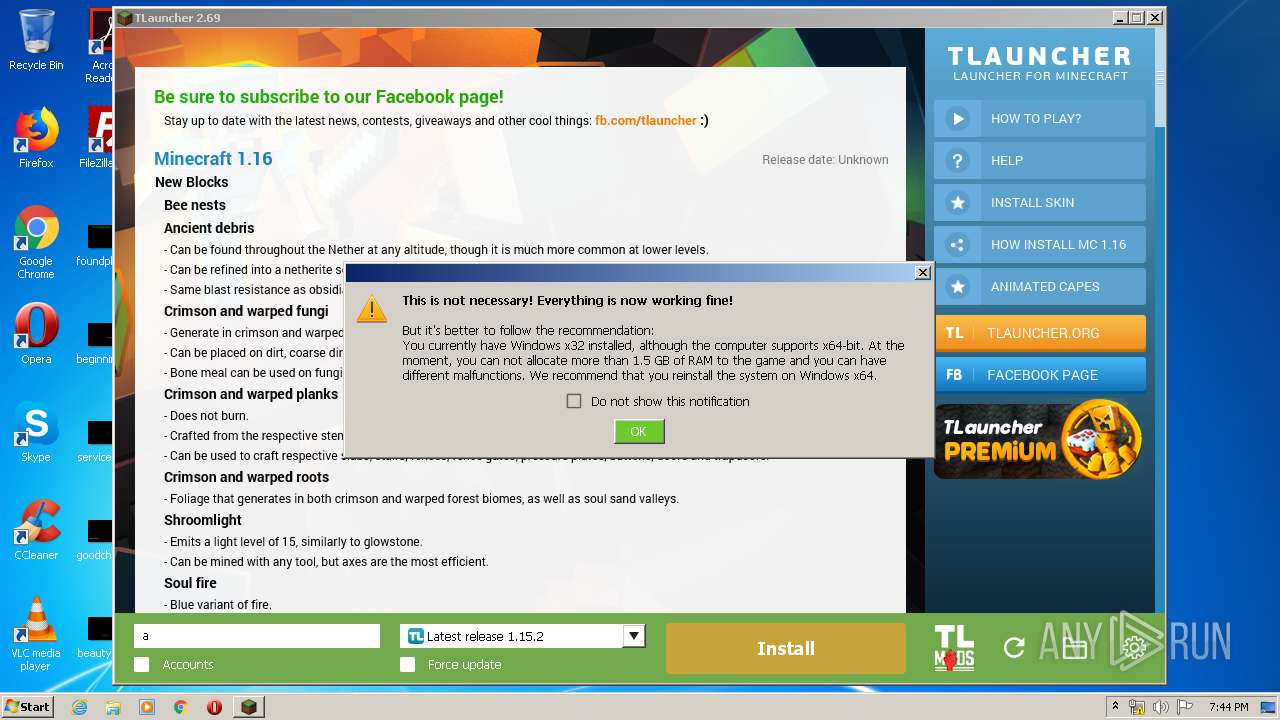
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5D9AAF4088910768120E081FBBFFCE80 |
| SHA1: | FA8643E5BBF4CDEBDDD0BD1AF6568540C630FE46 |
| SHA256: | 4C1993FF60A9013A1E7226BF737F84BEEFEB6B69677D6BC1F544959640479E79 |
| SSDEEP: | 393216:MXgumBb5fsD441ffz4e4oQL1CbfvIzAtdB7l7RPupq:Mwu05+1Hz4e4tCEzuB7l7RR |
MALICIOUS
Application was dropped or rewritten from another process
- irsetup.exe (PID: 1760)
- TLauncher.exe (PID: 4044)
Loads dropped or rewritten executable
- irsetup.exe (PID: 1760)
SUSPICIOUS
Executable content was dropped or overwritten
- TLauncher-2.69-Installer-0.5.2.exe (PID: 2456)
- irsetup.exe (PID: 1760)
Reads Internet Cache Settings
- irsetup.exe (PID: 1760)
Executes JAVA applets
- TLauncher.exe (PID: 4044)
- javaw.exe (PID: 3840)
Creates files in the user directory
- irsetup.exe (PID: 1760)
- javaw.exe (PID: 3840)
- javaw.exe (PID: 3048)
- dxdiag.exe (PID: 1352)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 3840)
- javaw.exe (PID: 3048)
Reads internet explorer settings
- irsetup.exe (PID: 1760)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2076)
- cmd.exe (PID: 548)
- cmd.exe (PID: 4064)
- cmd.exe (PID: 404)
Starts application with an unusual extension
- cmd.exe (PID: 2076)
- cmd.exe (PID: 548)
- cmd.exe (PID: 4064)
- cmd.exe (PID: 404)
- cmd.exe (PID: 3432)
- cmd.exe (PID: 2720)
Application launched itself
- javaw.exe (PID: 3840)
Connects to unusual port
- javaw.exe (PID: 3048)
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 3432)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.8) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (36.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (9) |
| .exe | | | Win32 Executable (generic) (6.1) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:03 20:13:08+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 23552 |
| InitializedDataSize: | 142336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2ce1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.5.2.0 |
| ProductVersionNumber: | 2.69.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | TLauncher Setup |
| CompanyName: | TLauncher Inc. |
| FileDescription: | TLauncher Setup |
| FileVersion: | 0.5.2.0 |
| InternalName: | TLauncher |
| LegalCopyright: | TLauncher Copyright © 2019 |
| LegalTrademarks: | TLauncher |
| OriginalFileName: | suf_launch.exe |
| ProductName: | TLauncher |
| ProductVersion: | 2.69.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jan-2019 19:13:08 |
| Detected languages: |
|
| Comments: | TLauncher Setup |
| CompanyName: | TLauncher Inc. |
| FileDescription: | TLauncher Setup |
| FileVersion: | 0.5.2.0 |
| InternalName: | TLauncher |
| LegalCopyright: | TLauncher Copyright © 2019 |
| LegalTrademarks: | TLauncher |
| OriginalFilename: | suf_launch.exe |
| ProductName: | TLauncher |
| ProductVersion: | 2.69.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Jan-2019 19:13:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A18 | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40733 |
.rdata | 0x00007000 | 0x00002F54 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05968 |
.data | 0x0000A000 | 0x00001968 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.59807 |
.rsrc | 0x0000C000 | 0x0001DDCC | 0x0001DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.50308 |
.reloc | 0x0002A000 | 0x000010D0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.81847 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.37674 | 1413 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.87454 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.04321 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.10433 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.15069 | 6760 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.24063 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.45174 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.39733 | 1720 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.52276 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.9892 | 132 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
68
Monitored processes
23
Malicious processes
5
Suspicious processes
0
Behavior graph
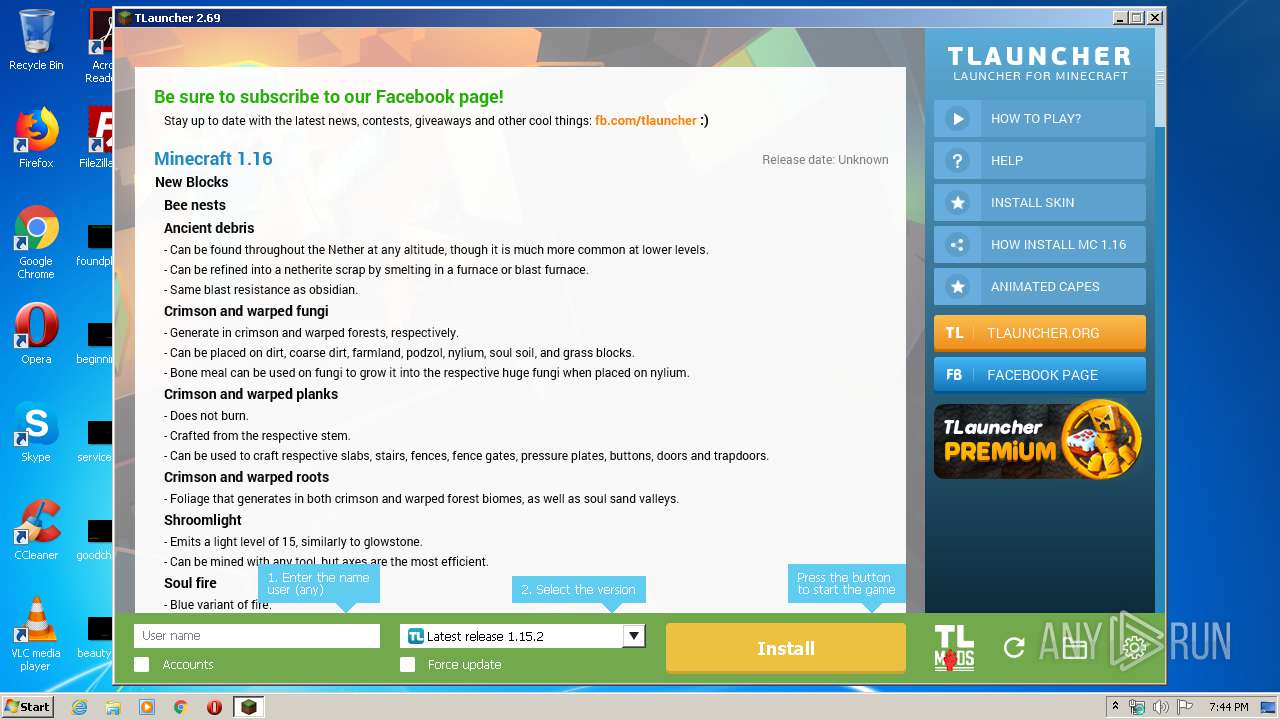
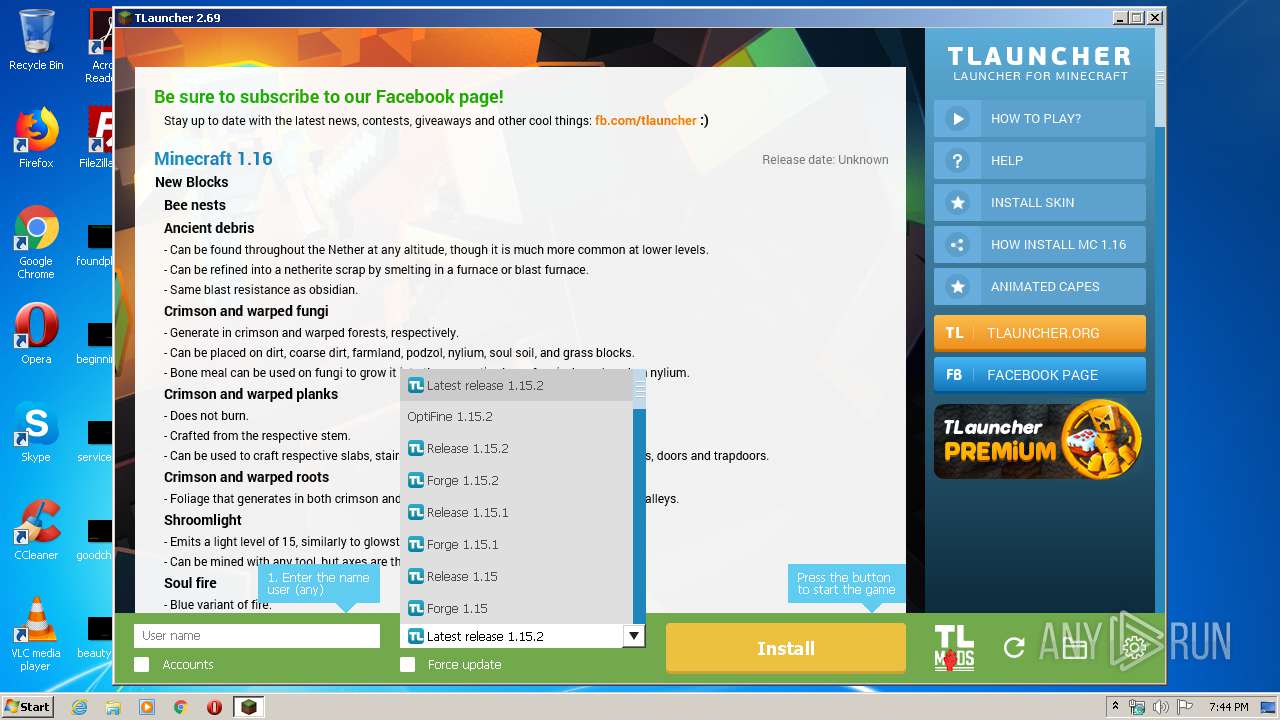
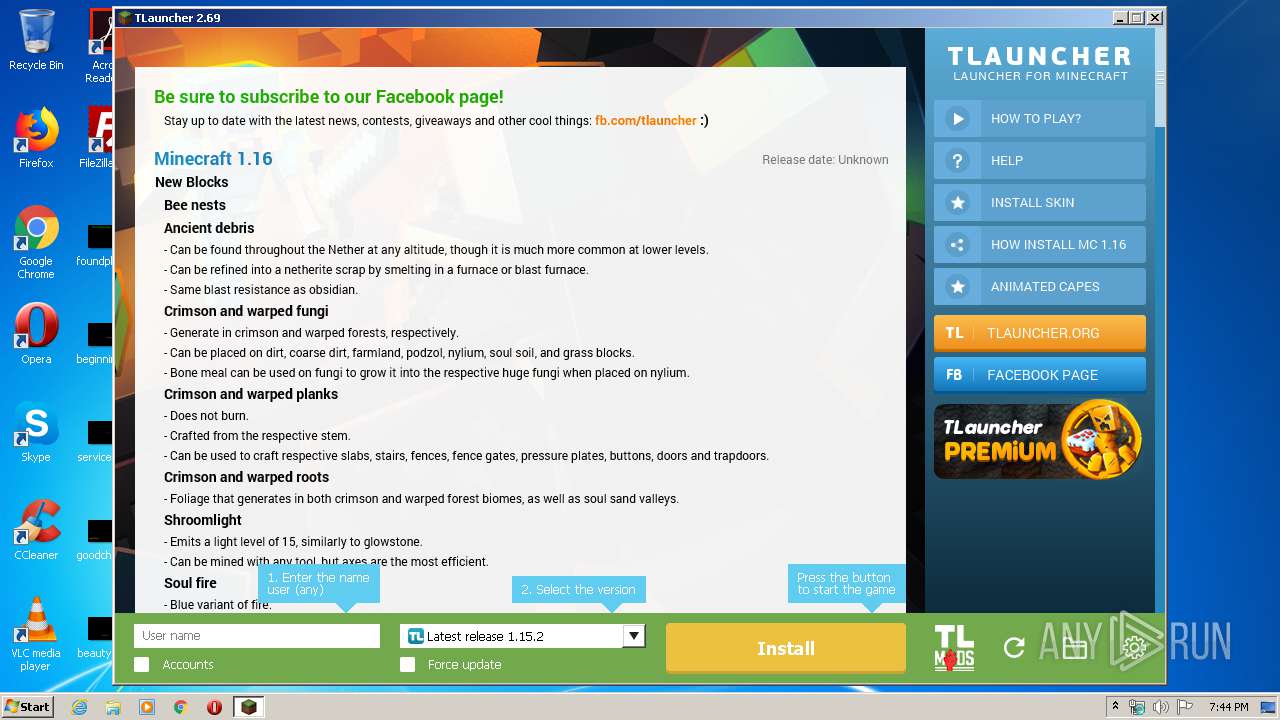
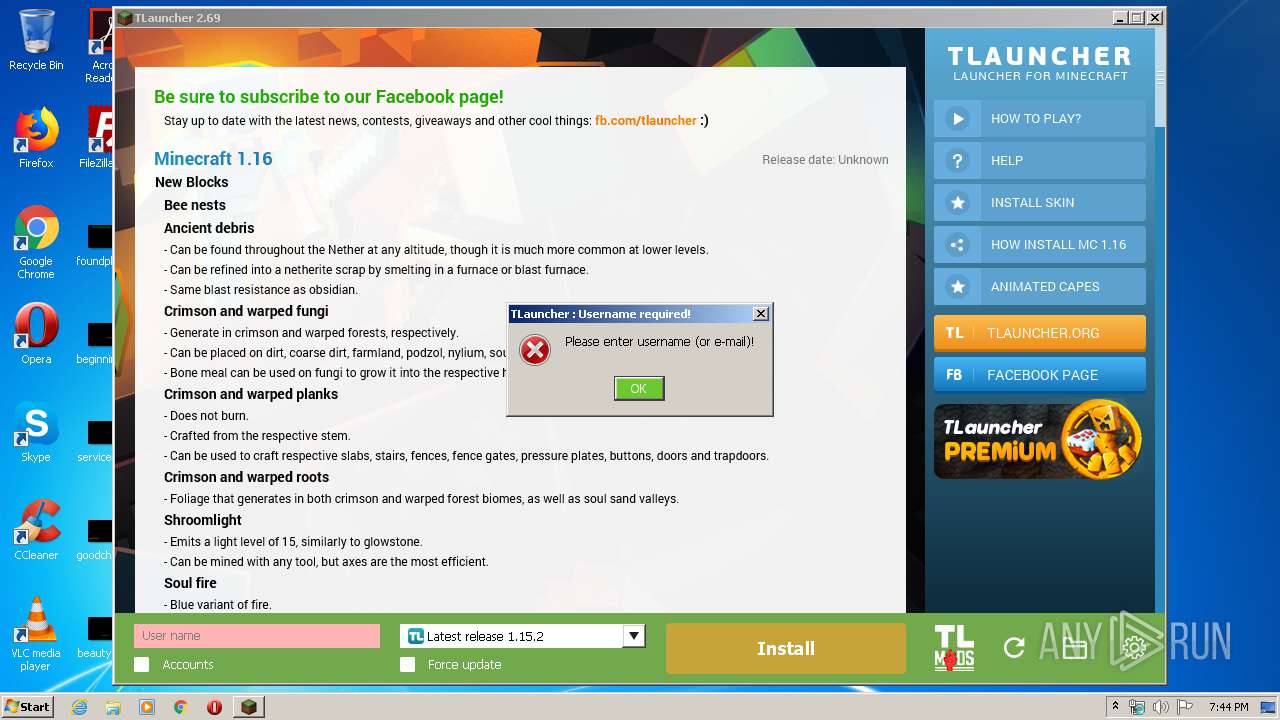
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | cmd.exe /C chcp 437 & wmic CPU get NAME | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 548 | cmd.exe /C chcp 437 & wmic os get osarchitecture | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1352 | dxdiag /whql:off /t C:\Users\admin\AppData\Roaming\.minecraft\logs\tlauncher\dxdiag.txt | C:\Windows\system32\dxdiag.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft DirectX Diagnostic Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1760 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe" __IRAOFF:1905626 "__IRAFN:C:\Users\admin\Desktop\TLauncher-2.69-Installer-0.5.2.exe" "__IRCT:1" "__IRTSS:14984508" "__IRSID:S-1-5-21-1302019708-1500728564-335382590-1000" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | TLauncher-2.69-Installer-0.5.2.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: MEDIUM Description: Setup Application Exit code: 0 Version: 9.5.3.0 Modules
| |||||||||||||||
| 2004 | systeminfo | C:\Windows\system32\systeminfo.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Displays system information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2076 | cmd.exe /C chcp 437 & wmic os get osarchitecture | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2456 | "C:\Users\admin\Desktop\TLauncher-2.69-Installer-0.5.2.exe" | C:\Users\admin\Desktop\TLauncher-2.69-Installer-0.5.2.exe | explorer.exe | ||||||||||||
User: admin Company: TLauncher Inc. Integrity Level: MEDIUM Description: TLauncher Setup Exit code: 0 Version: 0.5.2.0 Modules
| |||||||||||||||
| 2540 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2720 | cmd.exe /C chcp 437 & dxdiag /whql:off /t C:\Users\admin\AppData\Roaming\.minecraft\logs\tlauncher\dxdiag.txt | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 650
Read events
1 471
Write events
163
Delete events
16
Modification events
| (PID) Process: | (2456) TLauncher-2.69-Installer-0.5.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2456) TLauncher-2.69-Installer-0.5.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1760) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1760) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1760) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1760) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1760) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3840) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (3048) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3048) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
10
Suspicious files
21
Text files
67
Unknown types
120
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1760 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.dat | — | |
MD5:— | SHA256:— | |||
| 1760 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG1.PNG | image | |
MD5:— | SHA256:— | |||
| 1760 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG5.PNG | image | |
MD5:— | SHA256:— | |||
| 2456 | TLauncher-2.69-Installer-0.5.2.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | executable | |
MD5:— | SHA256:— | |||
| 1760 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG7.PNG | image | |
MD5:— | SHA256:— | |||
| 1760 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG9.PNG | image | |
MD5:— | SHA256:— | |||
| 1760 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG8.PNG | image | |
MD5:— | SHA256:— | |||
| 1760 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG10.PNG | image | |
MD5:— | SHA256:— | |||
| 1760 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG3.PNG | image | |
MD5:— | SHA256:— | |||
| 1760 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG12.PNG | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
118
TCP/UDP connections
19
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
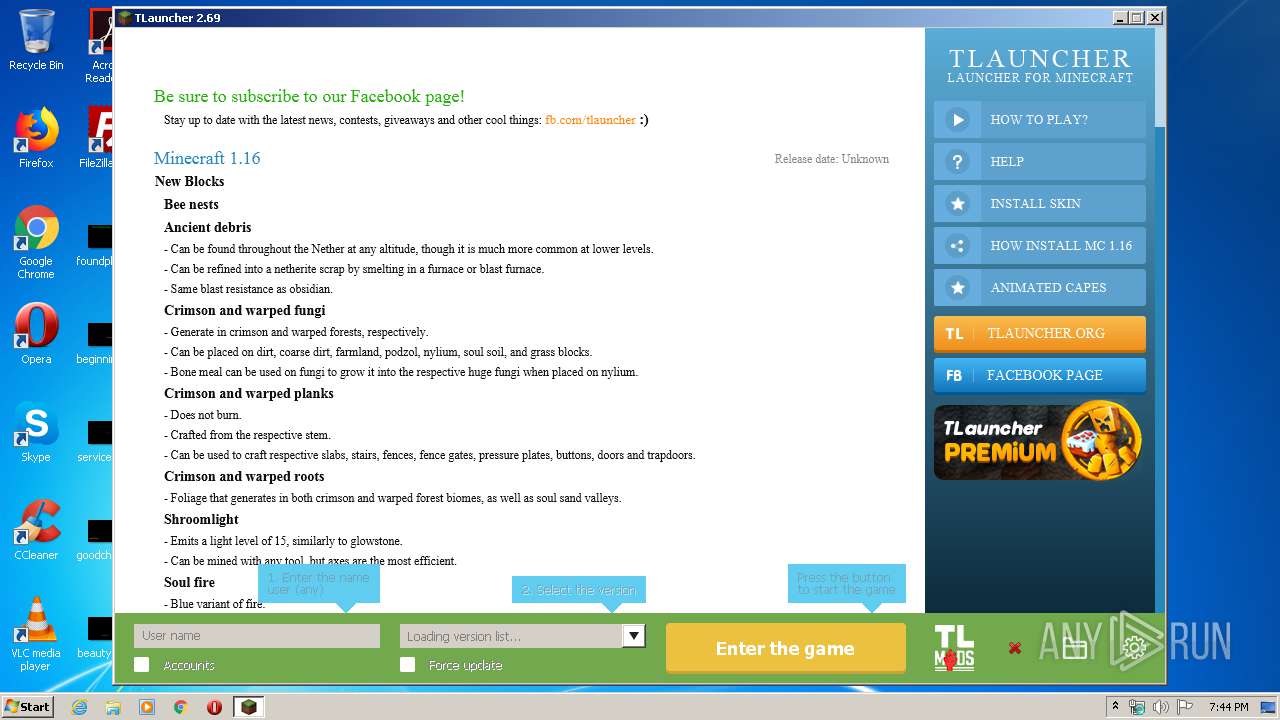
3048 | javaw.exe | GET | 200 | 104.22.33.161:80 | http://page.tlauncher.org/update/downloads/configs/client/eng.html | US | html | 16.9 Kb | malicious |
3048 | javaw.exe | GET | 200 | 104.22.33.161:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn1.png | US | image | 160 b | malicious |
3048 | javaw.exe | GET | 200 | 104.22.33.161:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn2.png | US | image | 199 b | malicious |
3048 | javaw.exe | GET | 200 | 104.22.33.161:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/fb.png | US | image | 170 b | malicious |
3048 | javaw.exe | GET | 200 | 104.22.33.161:80 | http://img.tlauncher.org/update/downloads/configs/client/images/tl-en-pe-news.png | US | image | 129 Kb | malicious |
3048 | javaw.exe | GET | 200 | 104.22.33.161:80 | http://repo.tlauncher.org/update/lch/update_2.0.json?version=2.69&client=17aa9f62-d8ef-43e2-8985-63c13cba8086 | US | text | 7.69 Kb | whitelisted |
3048 | javaw.exe | GET | 200 | 104.22.33.161:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/tl2.png | US | image | 113 b | malicious |
3048 | javaw.exe | GET | 200 | 104.22.33.161:80 | http://img.tlauncher.org/update/downloads/configs/client/images/ad1.png | US | image | 71.3 Kb | malicious |
3048 | javaw.exe | GET | 200 | 104.22.33.161:80 | http://repo.tlauncher.org/update/downloads/configs/inner_servers.json | US | text | 3.17 Kb | whitelisted |
3048 | javaw.exe | GET | 200 | 104.22.33.161:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn3.png | US | image | 213 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3048 | javaw.exe | 104.22.33.161:80 | page.tlauncher.org | Cloudflare Inc | US | unknown |
3048 | javaw.exe | 99.86.1.139:443 | launchermeta.mojang.com | AT&T Services, Inc. | US | unknown |
3048 | javaw.exe | 143.204.202.80:80 | resources.download.minecraft.net | — | US | suspicious |
3048 | javaw.exe | 5.9.78.146:8092 | stat.tlrepo.com | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
page.tlauncher.org |
| malicious |
repo.tlauncher.org |
| whitelisted |
img.tlauncher.org |
| malicious |
launchermeta.mojang.com |
| whitelisted |
resources.download.minecraft.net |
| shared |
stat.tlrepo.com |
| suspicious |