| File name: | lockyRansomware.bin |
| Full analysis: | https://app.any.run/tasks/38b57b69-6815-4ffe-8522-896ec4a32a09 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 17:15:38 |
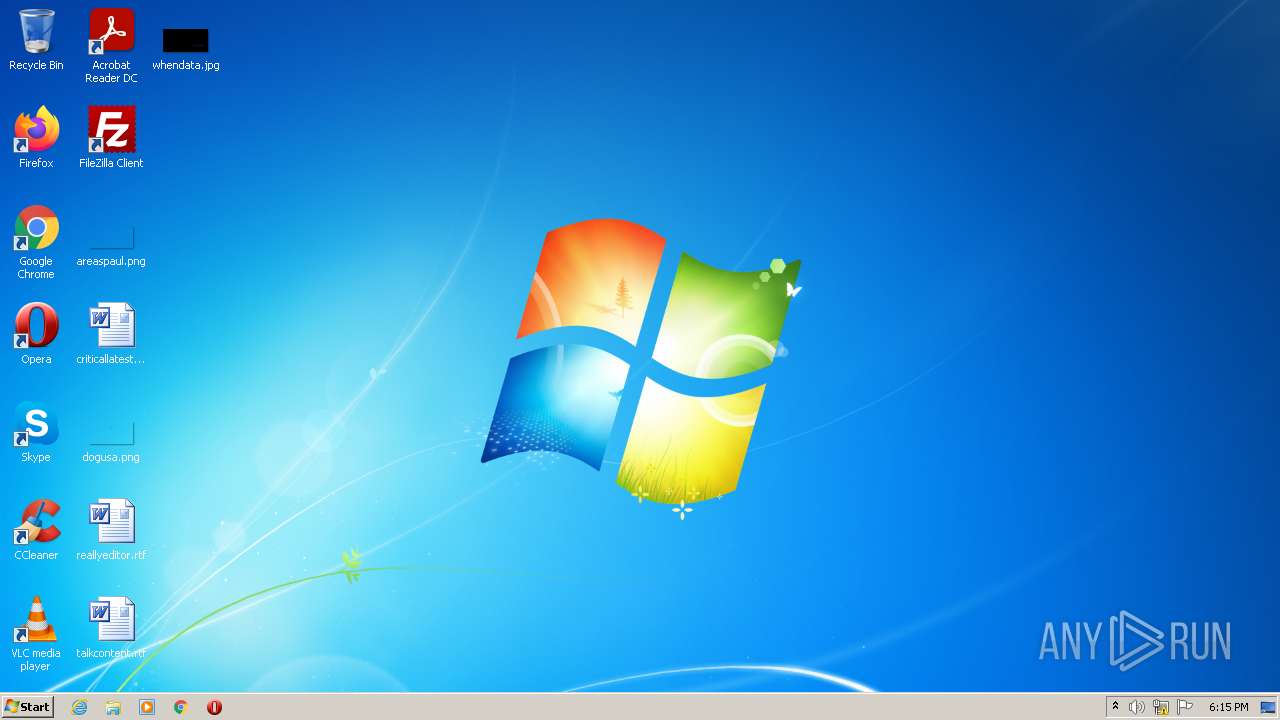
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 67E0107CB365D9360C707C260D3ACFA9 |
| SHA1: | D58A690203881B682446D431177EA86F87CEEF27 |
| SHA256: | 4C054127056FB400ACBAB7825AA2754942121E6C49B0F82AE20E65422ABDEE4F |
| SSDEEP: | 12288:LN2Rwpfr+foKIQG5IYBoOltIG5epfJ3p4zON:J2RwRQkHzIG5e5s6N |
MALICIOUS
Loads the Task Scheduler COM API
- lockyRansomware.bin.exe (PID: 2800)
Drops executable file immediately after starts
- lockyRansomware.bin.exe (PID: 2800)
SUSPICIOUS
Checks supported languages
- lockyRansomware.bin.exe (PID: 2800)
- cmd.exe (PID: 2516)
Reads the computer name
- lockyRansomware.bin.exe (PID: 2800)
Drops a file with a compile date too recent
- lockyRansomware.bin.exe (PID: 2800)
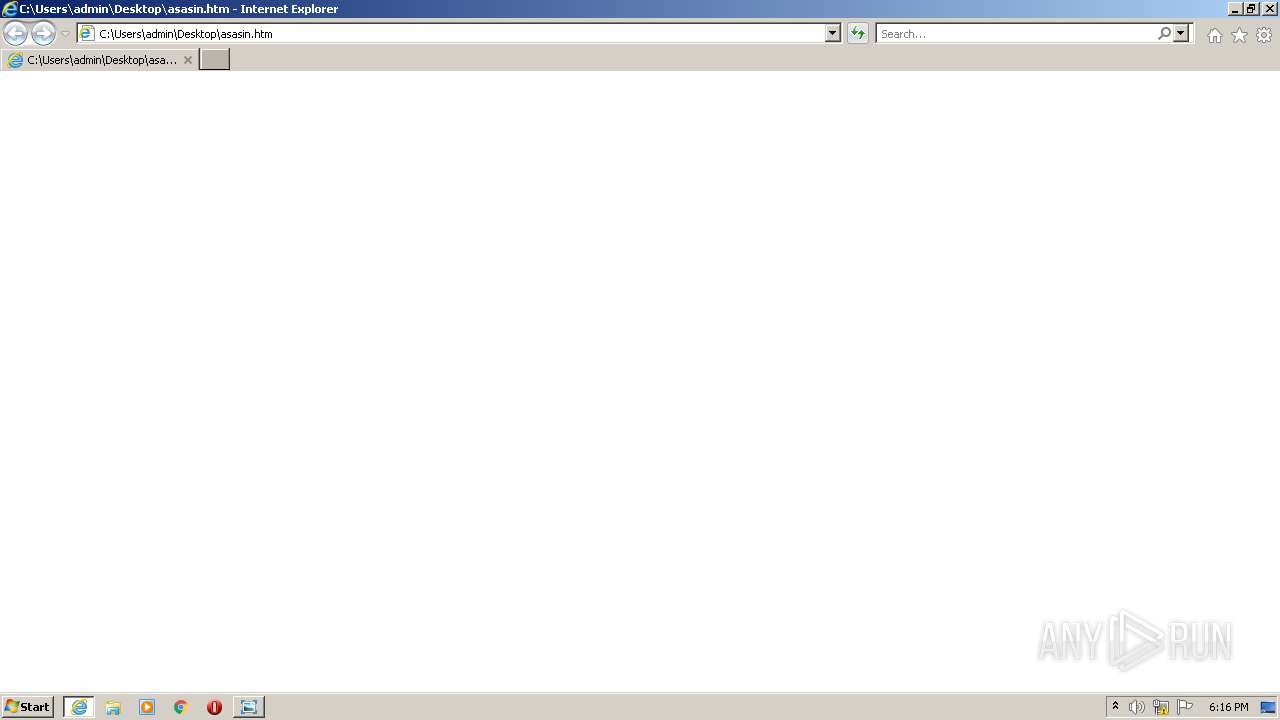
Starts Internet Explorer
- lockyRansomware.bin.exe (PID: 2800)
Creates files in the program directory
- lockyRansomware.bin.exe (PID: 2800)
Executed via COM
- DllHost.exe (PID: 4060)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2716)
Starts CMD.EXE for commands execution
- lockyRansomware.bin.exe (PID: 2800)
INFO
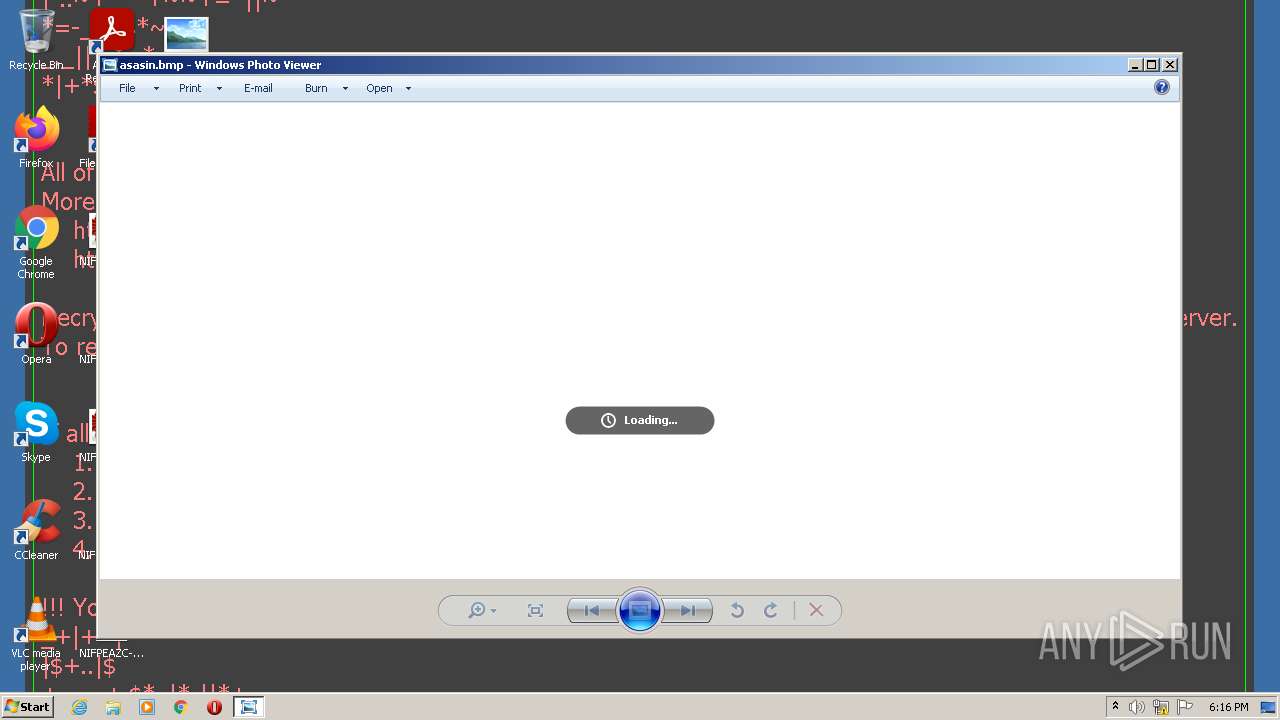
Dropped object may contain Bitcoin addresses
- lockyRansomware.bin.exe (PID: 2800)
Checks supported languages
- DllHost.exe (PID: 4060)
- iexplore.exe (PID: 696)
- iexplore.exe (PID: 2716)
Reads the computer name
- iexplore.exe (PID: 696)
- iexplore.exe (PID: 2716)
- DllHost.exe (PID: 4060)
Application launched itself
- iexplore.exe (PID: 696)
Changes internet zones settings
- iexplore.exe (PID: 696)
Reads internet explorer settings
- iexplore.exe (PID: 2716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (64.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (13.5) |
| .exe | | | Win32 Executable (generic) (9.3) |
| .exe | | | Win16/32 Executable Delphi generic (4.2) |
| .exe | | | Generic Win/DOS Executable (4.1) |
EXIF
EXE
| VarFileInfo: | - |
|---|---|
| Tag040904B0: | - |
| TechSupport: | http://www.3ware.com |
| ProductVersion: | SRV 1.03.00.001 |
| ProductName: | 3ware Storage Controller |
| LegalCopyright: | Copyright © 2000 by 3ware, Inc. |
| InternalName: | 3wareSrv |
| FileVersion: | SRV 1.03.00.001 |
| FileDescription: | 3ware Driver Service |
| CompanyName: | 3ware, Inc. |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | 7 |
| ObjectFileType: | Driver |
| FileOS: | Windows NT |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.3.0.1 |
| FileVersionNumber: | 1.3.0.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x3222 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 593408 |
| CodeSize: | 77824 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2016:03:30 02:00:03+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Mar-2016 00:00:03 |
| Detected languages: |
|
| CompanyName: | 3ware, Inc. |
| FileDescription: | 3ware Driver Service |
| FileVersion: | SRV 1.03.00.001 |
| InternalName: | 3wareSrv |
| LegalCopyright: | Copyright © 2000 by 3ware, Inc. |
| ProductName: | 3ware Storage Controller |
| ProductVersion: | SRV 1.03.00.001 |
| TechSupport: | http://www.3ware.com |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 30-Mar-2016 00:00:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00013000 | 0x00012200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.33432 |
.data | 0x00014000 | 0x000234AC | 0x00023600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.5826 |
.rdata | 0x00038000 | 0x000272A0 | 0x00027400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.60232 |
.pdata | 0x00060000 | 0x00042040 | 0x0003DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.41053 |
.idata | 0x000A3000 | 0x0000337C | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.44436 |
.rsrc | 0x000A7000 | 0x00000D4C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.11947 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.41978 | 1412 | UNKNOWN | English - United States | RT_VERSION |
2 | 2.57313 | 296 | UNKNOWN | English - United States | RT_ICON |
IDI_3WARE | 2.37086 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
WINMM.dll |
WINSPOOL.DRV |
ole32.dll |
Total processes
41
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 696 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\Desktop\asasin.htm | C:\Program Files\Internet Explorer\iexplore.exe | — | lockyRansomware.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2516 | cmd.exe /C del /Q /F "C:\Users\admin\AppData\Local\Temp\lockyRansomware.bin.exe" | C:\Windows\system32\cmd.exe | — | lockyRansomware.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2716 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:696 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2800 | "C:\Users\admin\AppData\Local\Temp\lockyRansomware.bin.exe" | C:\Users\admin\AppData\Local\Temp\lockyRansomware.bin.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4060 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 728
Read events
1 661
Write events
67
Delete events
0
Modification events
| (PID) Process: | (2800) lockyRansomware.bin.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | WallpaperStyle |
Value: 0 | |||
| (PID) Process: | (2800) lockyRansomware.bin.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | TileWallpaper |
Value: 0 | |||
| (PID) Process: | (2800) lockyRansomware.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FFE2A43C-56B9-4BF5-9A79-CC6D4285608A} {00000122-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000002A78BA5D6D6CD801 | |||
| (PID) Process: | (2800) lockyRansomware.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: lockyRansomware.bin.exe | |||
| (PID) Process: | (696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960749 | |||
| (PID) Process: | (696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960749 | |||
| (PID) Process: | (696) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
367
Text files
380
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2800 | lockyRansomware.bin.exe | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | binary | |
MD5:— | SHA256:— | |||
| 2800 | lockyRansomware.bin.exe | C:\Users\admin\Documents\OneNote Notebooks\Personal\Open Notebook.onetoc2 | binary | |
MD5:— | SHA256:— | |||
| 2800 | lockyRansomware.bin.exe | C:\Users\admin\Desktop\reallyeditor.rtf | binary | |
MD5:— | SHA256:— | |||
| 2800 | lockyRansomware.bin.exe | C:\Users\admin\Desktop\criticallatest.rtf | binary | |
MD5:— | SHA256:— | |||
| 2800 | lockyRansomware.bin.exe | C:\Users\admin\Desktop\NIFPEAZC-M556-R7CW-07D24AEF-0B173E5CEF78.asasin | text | |
MD5:— | SHA256:— | |||
| 2800 | lockyRansomware.bin.exe | C:\Users\admin\Documents\Outlook Files\Outlook.pst | binary | |
MD5:— | SHA256:— | |||
| 2800 | lockyRansomware.bin.exe | C:\Users\admin\Documents\Outlook Files\Outlook Data File - test.pst | binary | |
MD5:— | SHA256:— | |||
| 2800 | lockyRansomware.bin.exe | C:\Users\admin\Documents\Outlook Files\NIFPEAZC-M556-R7CW-AF825A3D-4AE246CA82A1.asasin | pst | |
MD5:D1E8D2BA20B3D12C4D0B1F42172F20EF | SHA256:91FC6A482926AE6F2AC3D7B71D7F565A3A27A78AABF9BC16EC56A3AC303FC366 | |||
| 2800 | lockyRansomware.bin.exe | C:\Users\admin\Documents\NIFPEAZC-M556-R7CW-8FCDF638-2253E1B2EF58.asasin | text | |
MD5:— | SHA256:— | |||
| 2800 | lockyRansomware.bin.exe | C:\Users\admin\Documents\Outlook Files\NIFPEAZC-M556-R7CW-5F06E30E-D47AEDBDA908.asasin | pst | |
MD5:CFFB4CF3E00E22A0099697E786243831 | SHA256:47DE5084EA2AF8959C10FC1C4734B0B4F68F2BD49E2612075E2733A5EA00FD12 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report