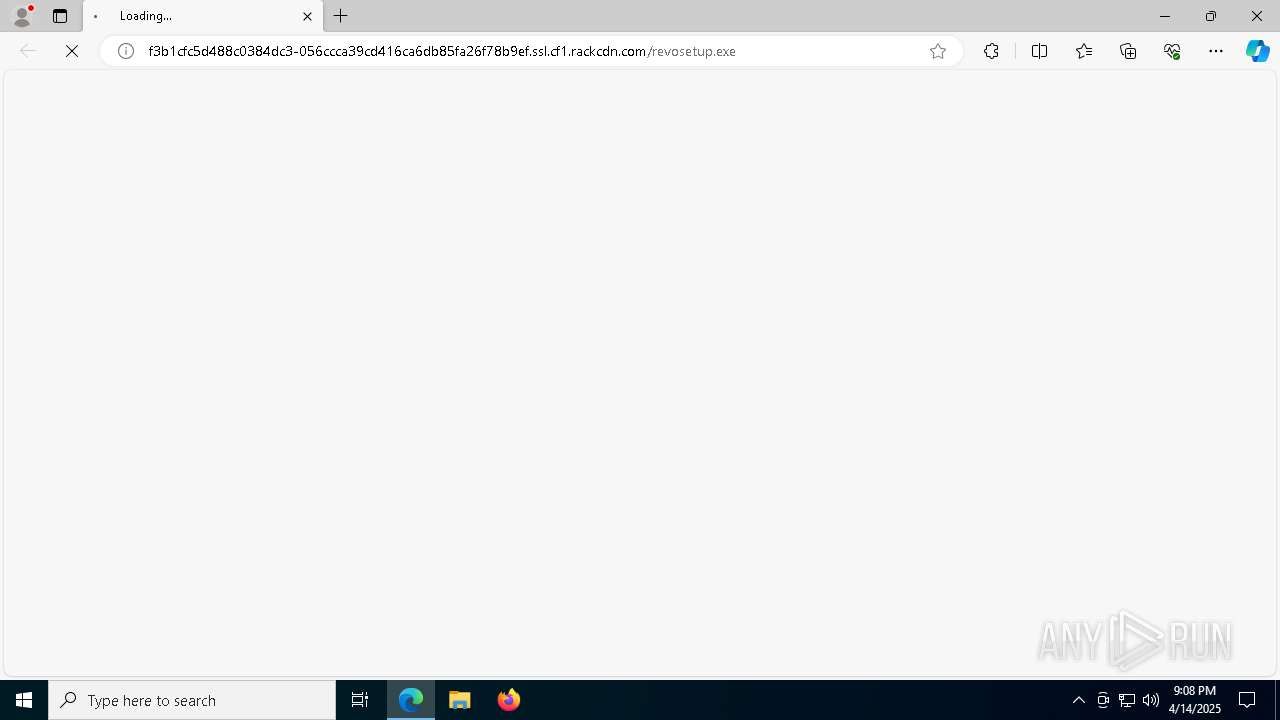
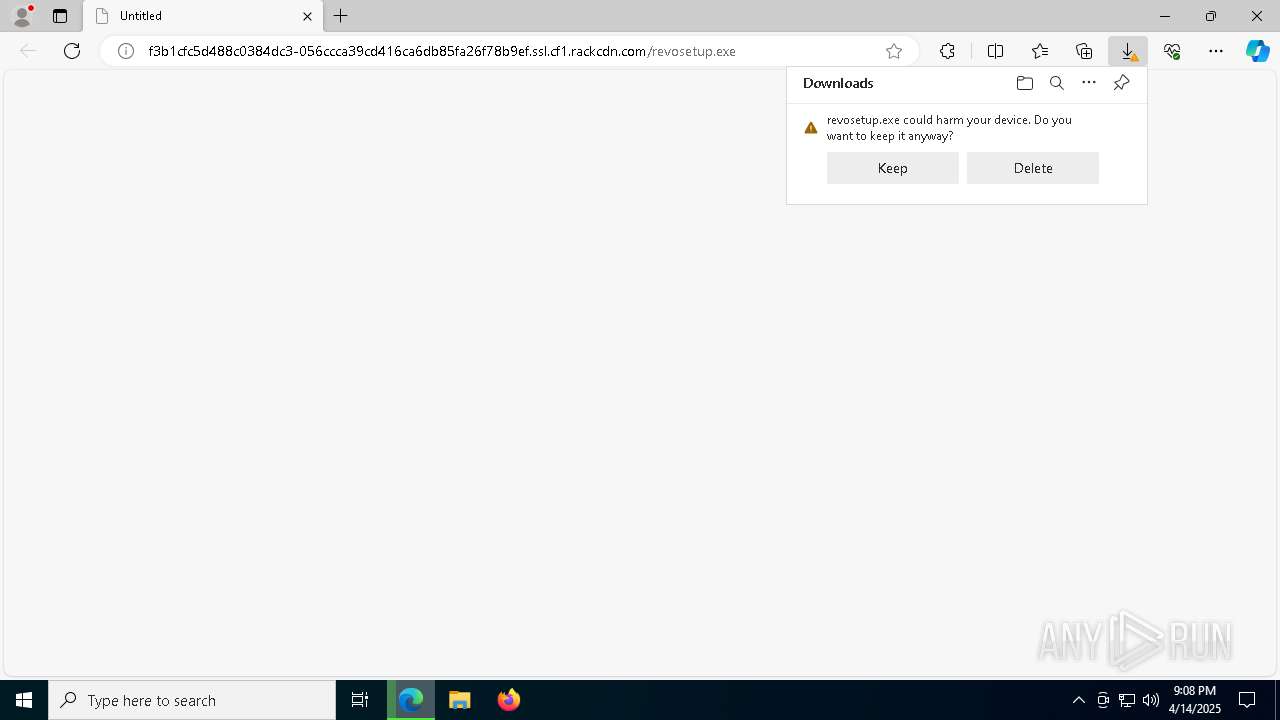
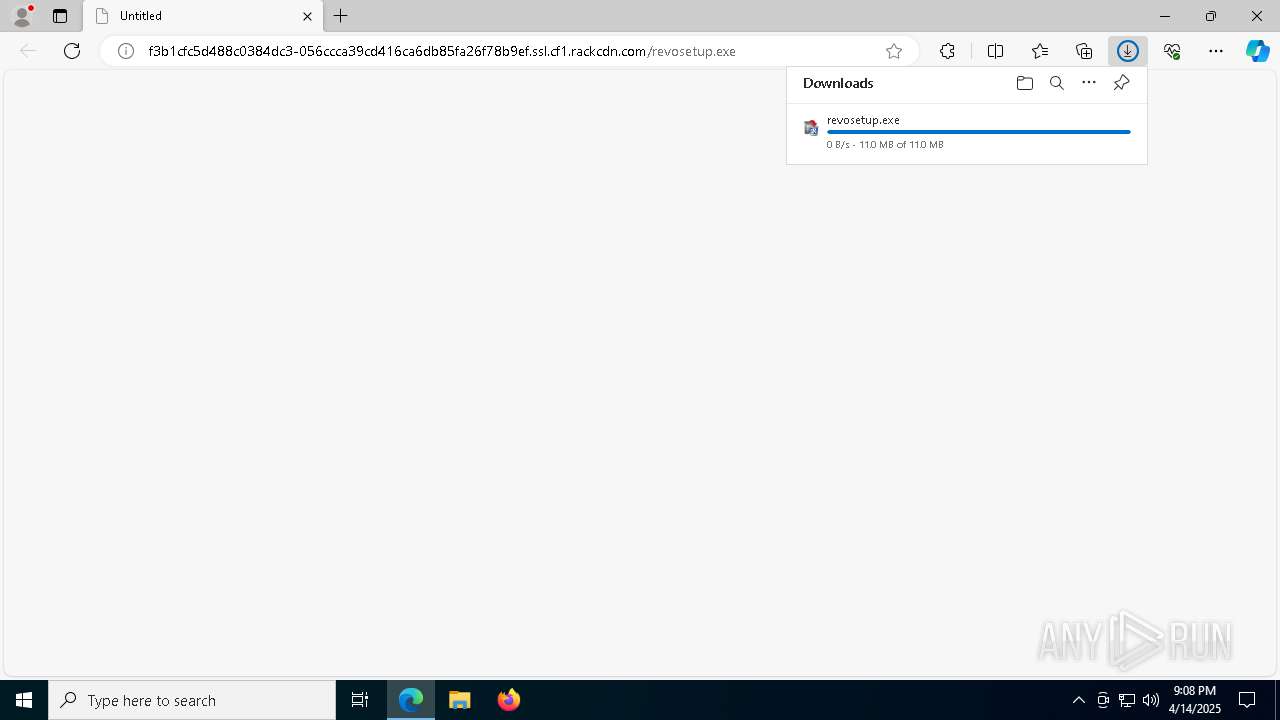
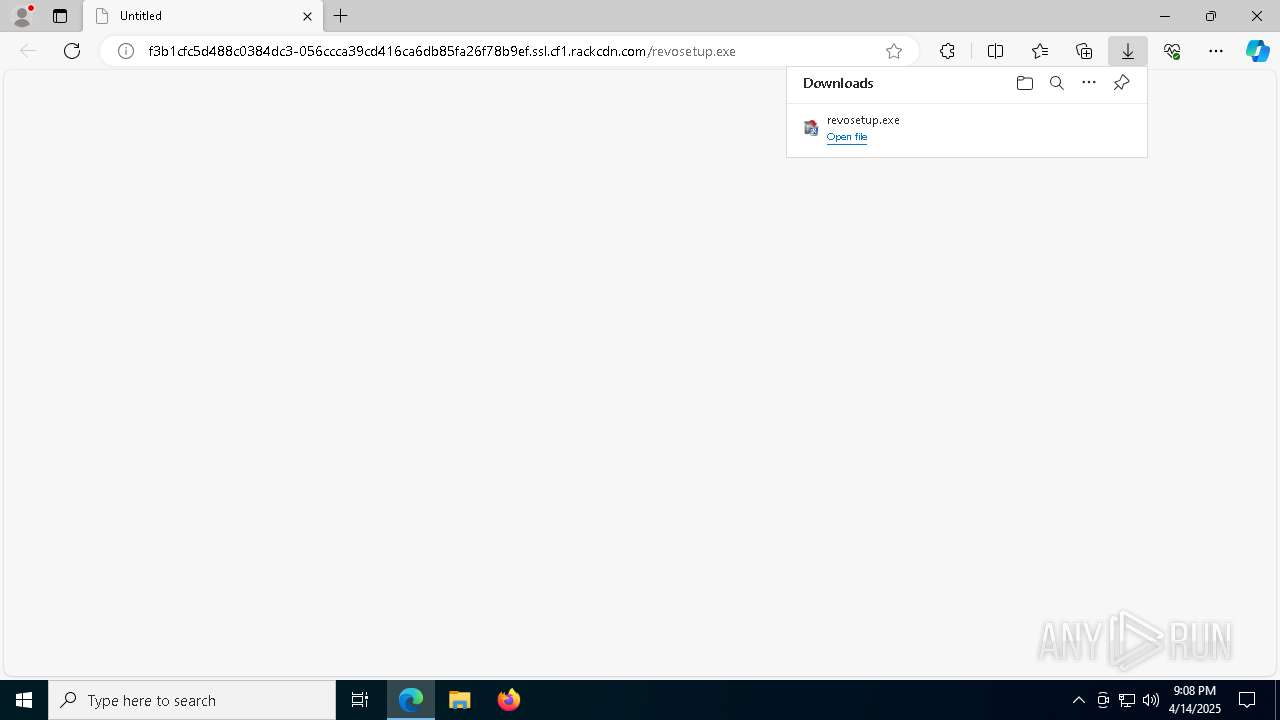
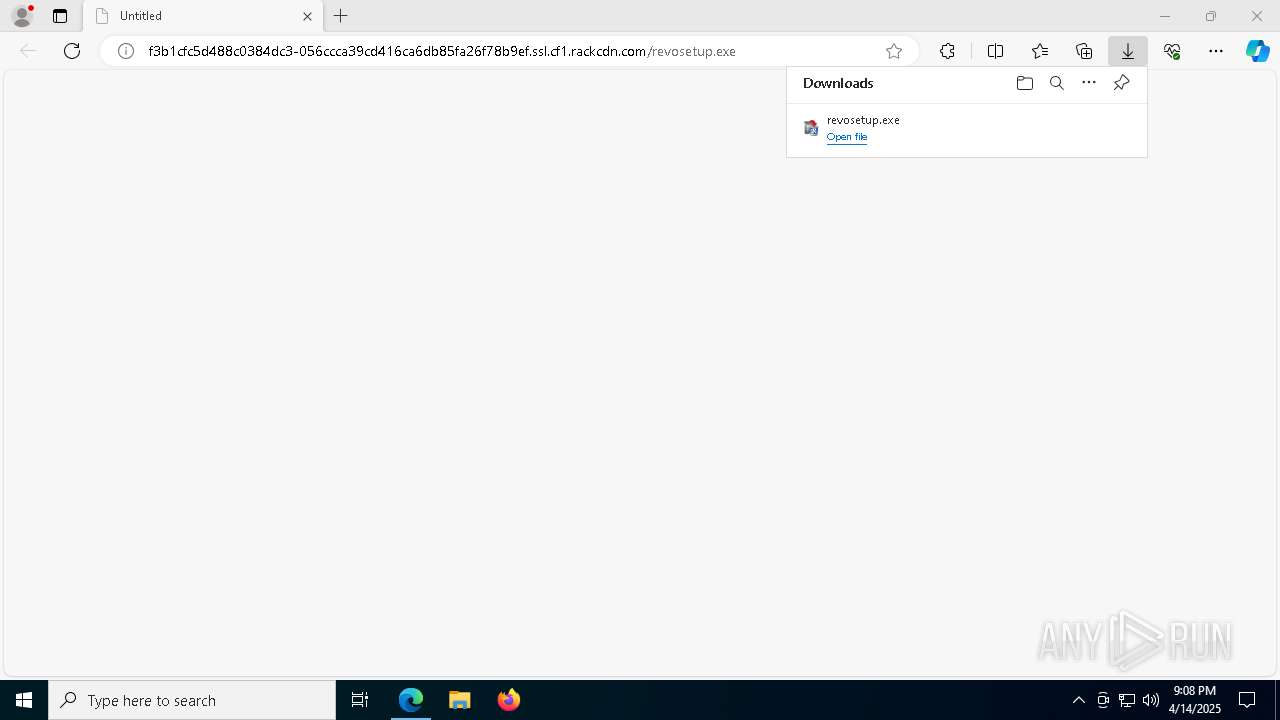
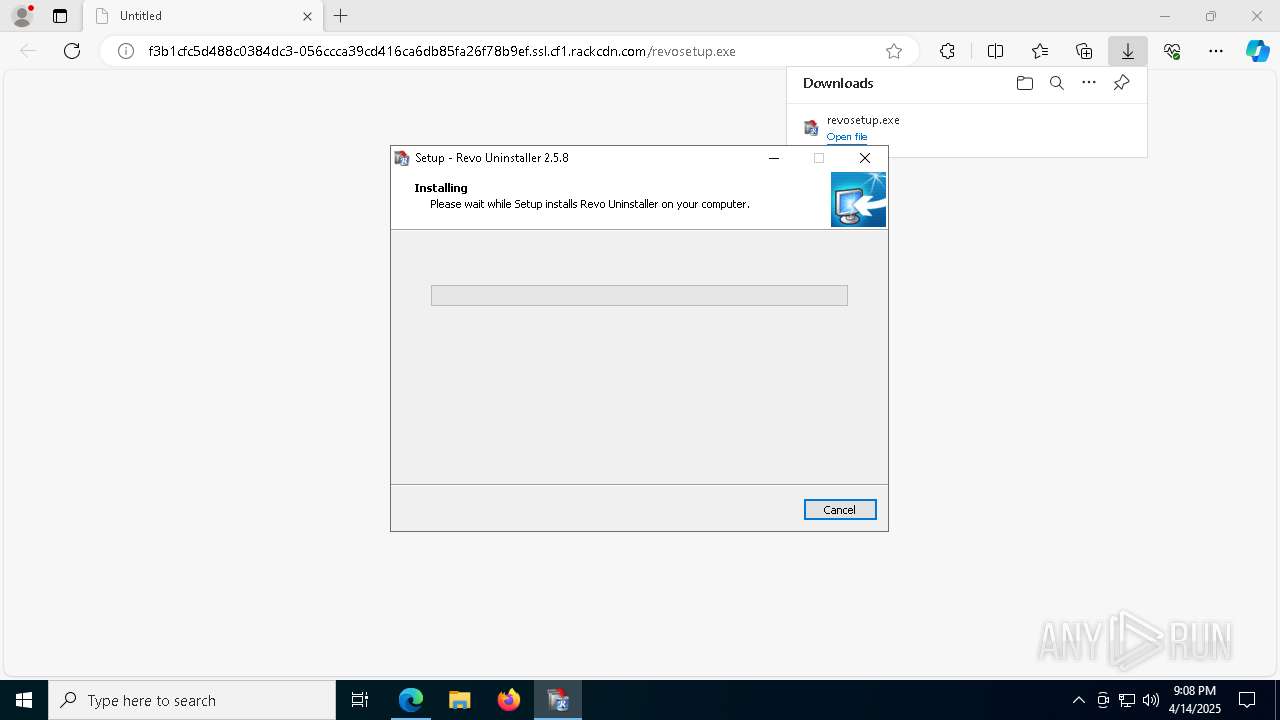
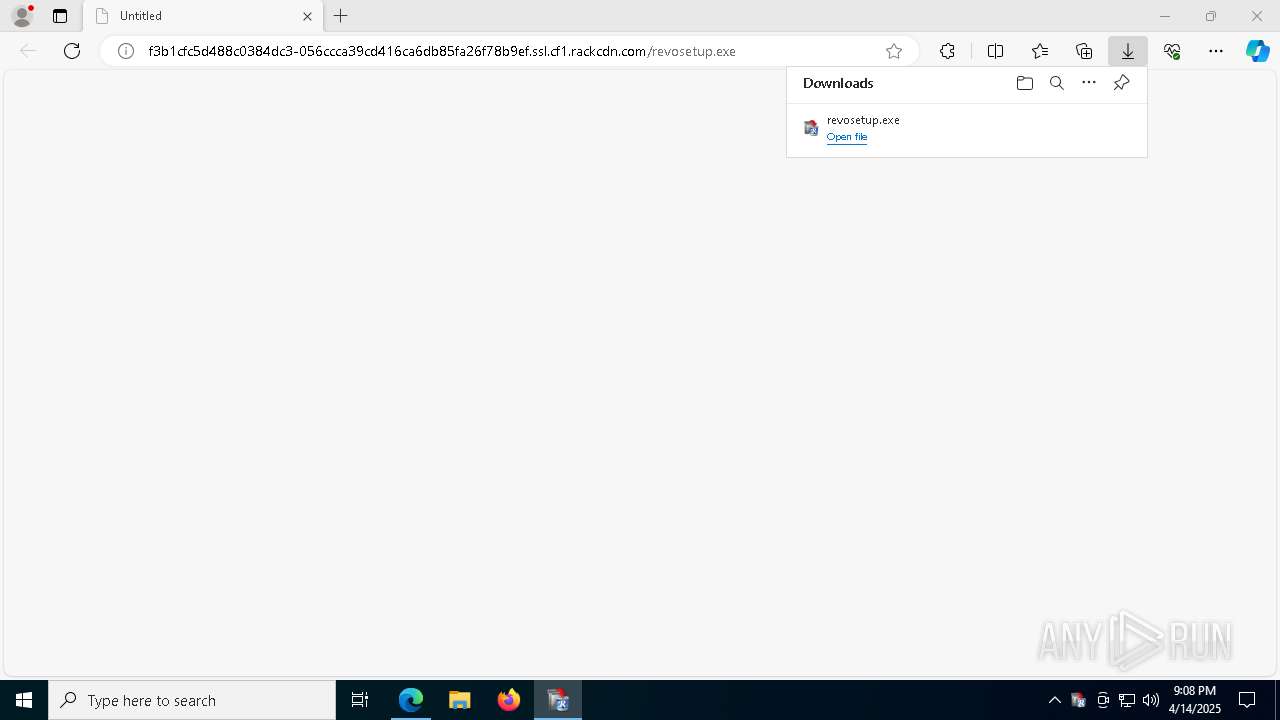
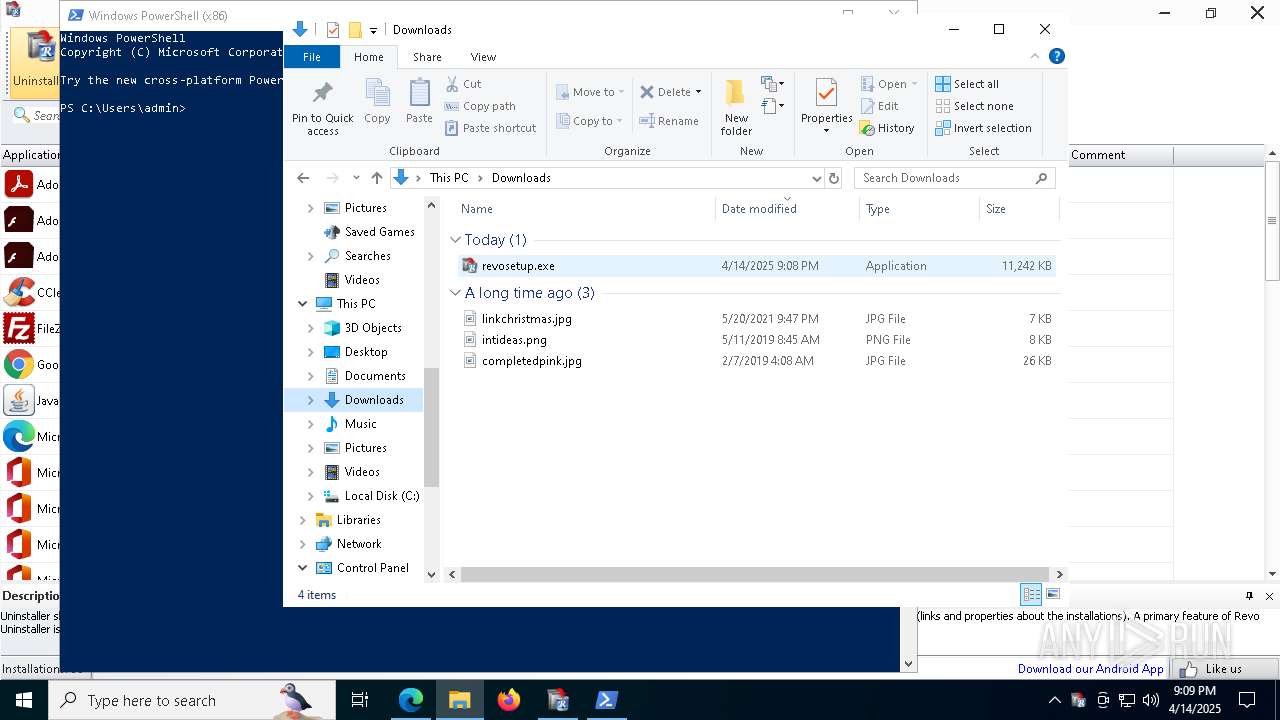
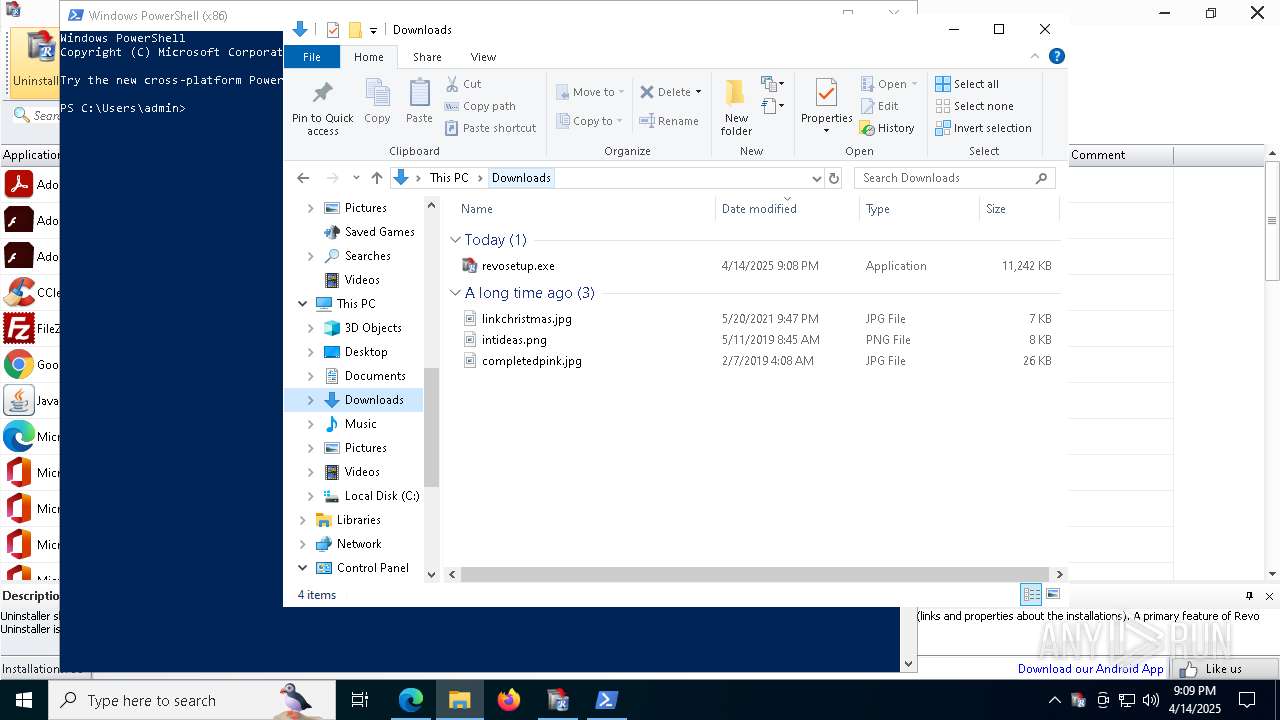
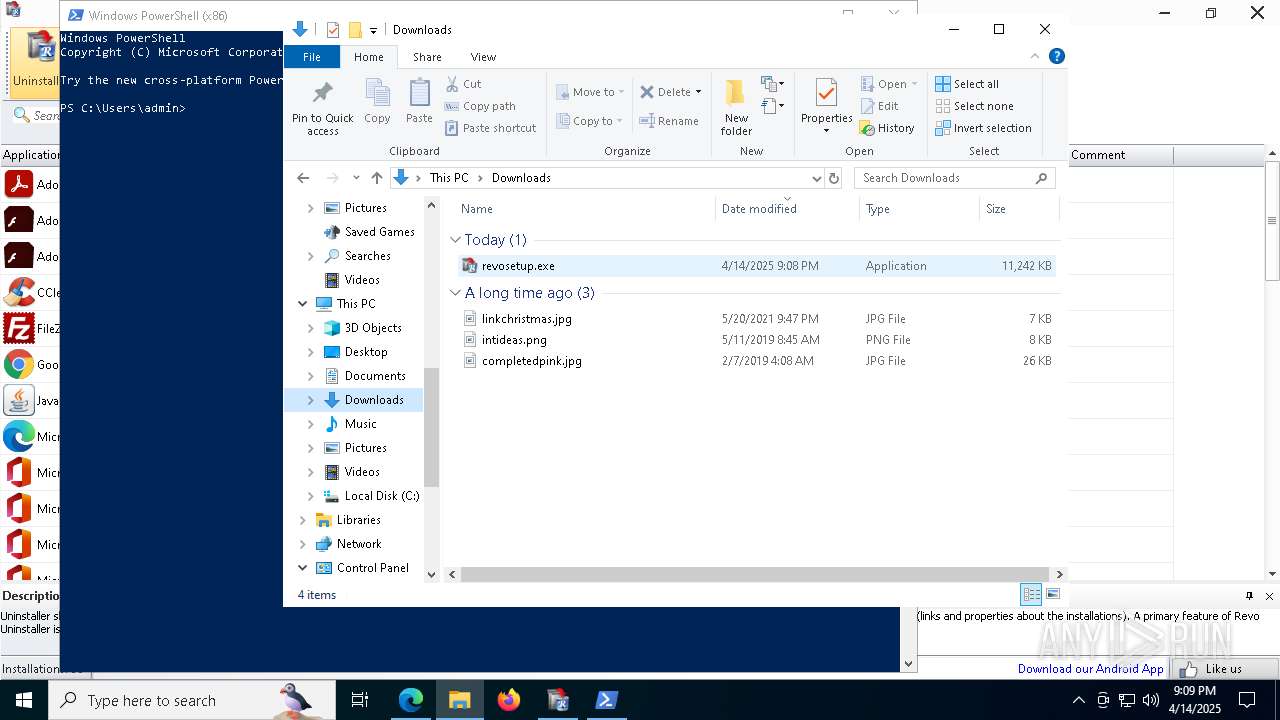
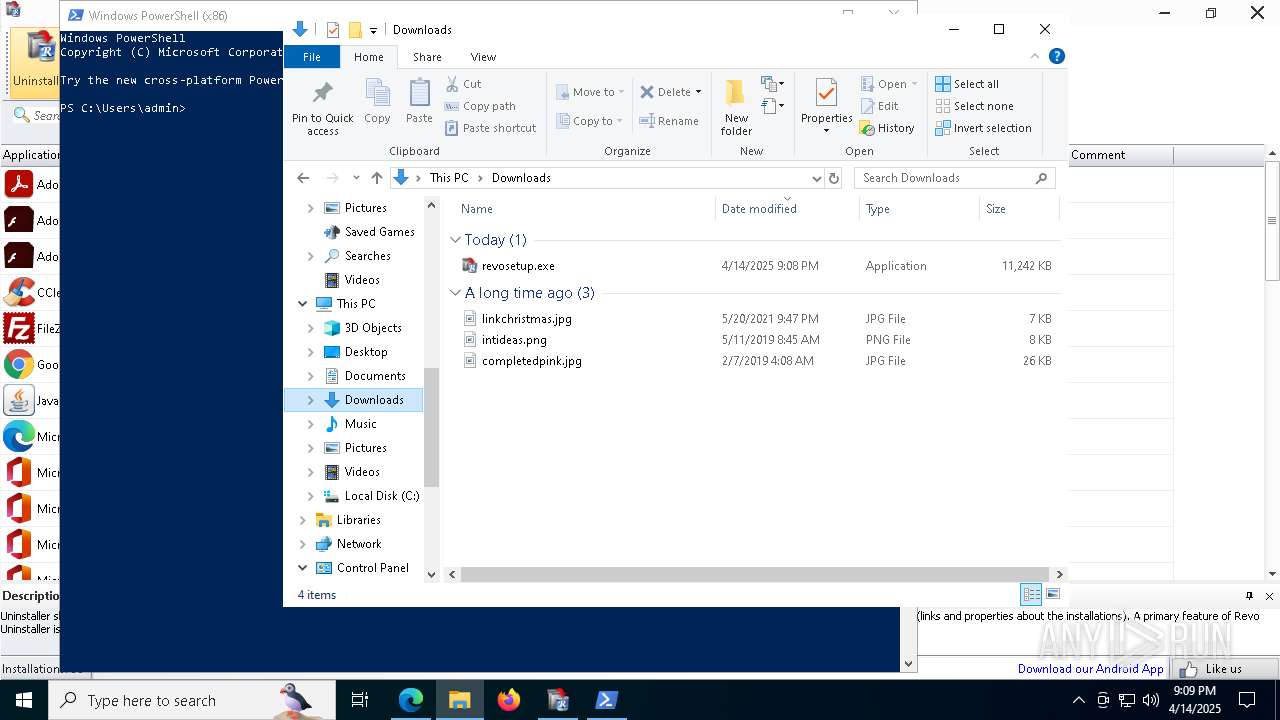
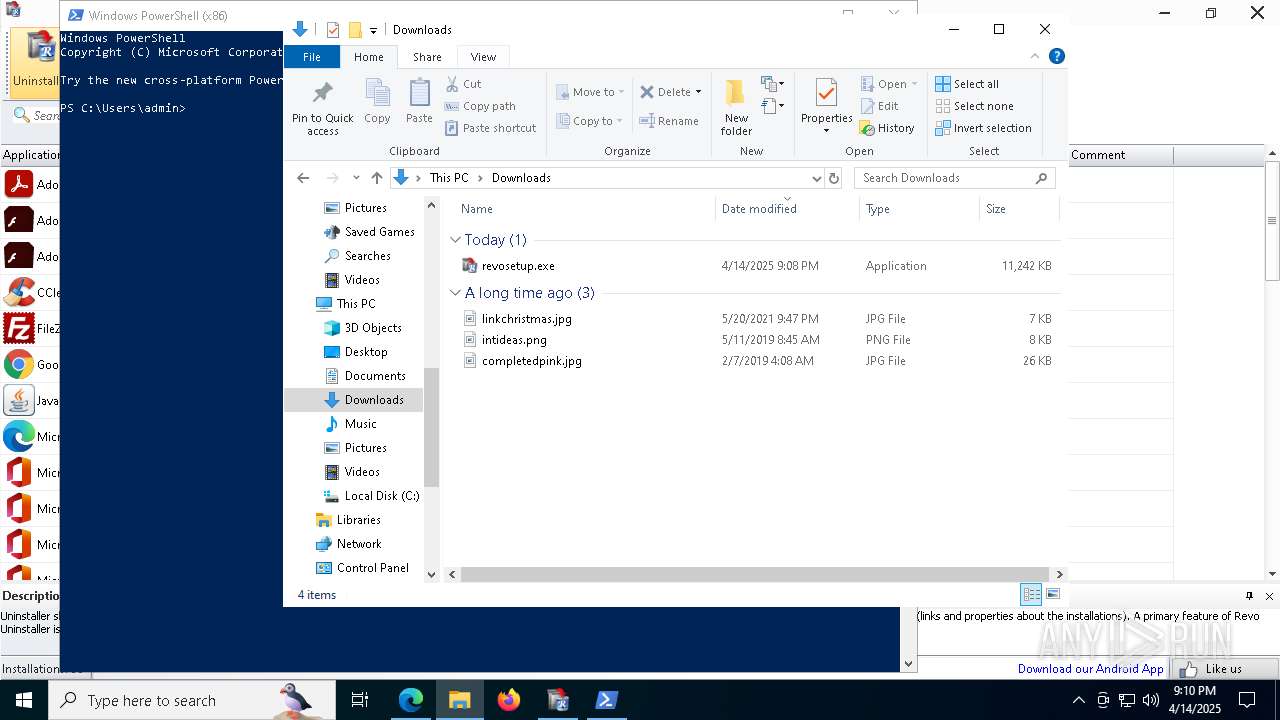
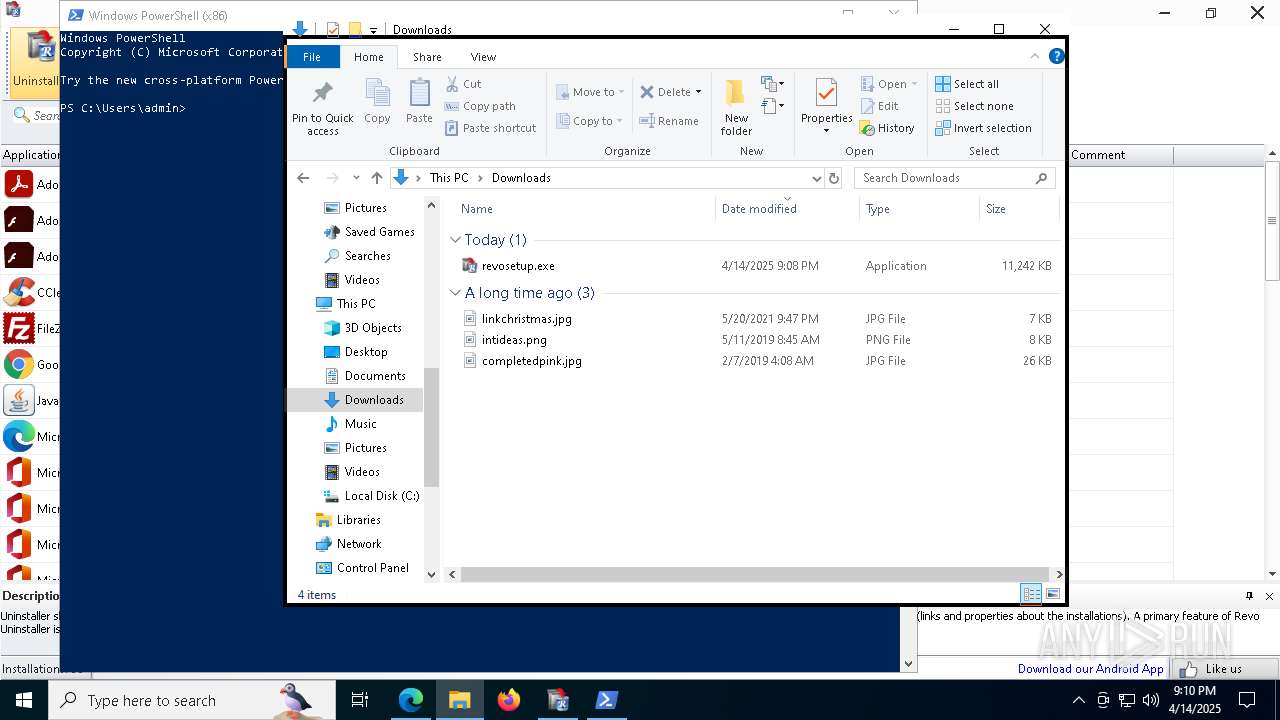
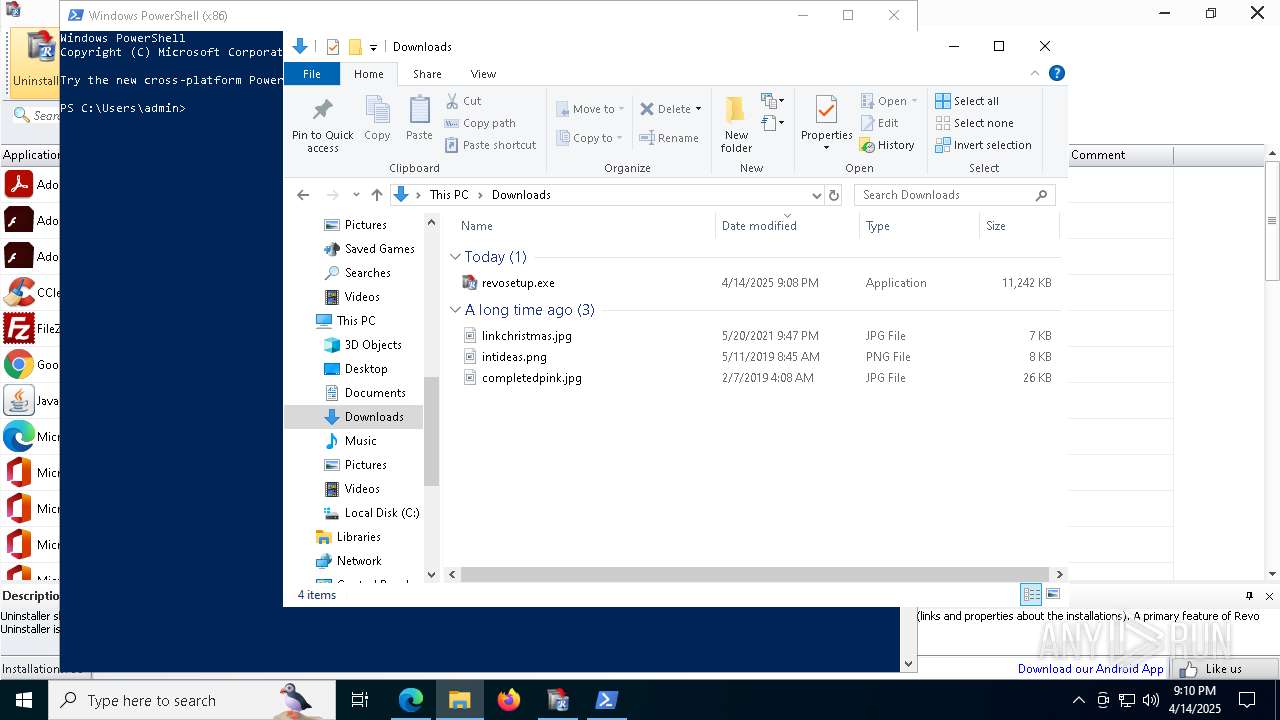
| URL: | f3b1cfc5d488c0384dc3-056ccca39cd416ca6db85fa26f78b9ef.ssl.cf1.rackcdn.com/revosetup.exe |
| Full analysis: | https://app.any.run/tasks/84c5f11d-07d4-4037-91c6-2a5910390942 |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2025, 21:07:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 14B8A9F4054BDD7D602ED9BB428559B7 |
| SHA1: | 2464320905AF9772FE6185F3BB98C7C1352751DA |
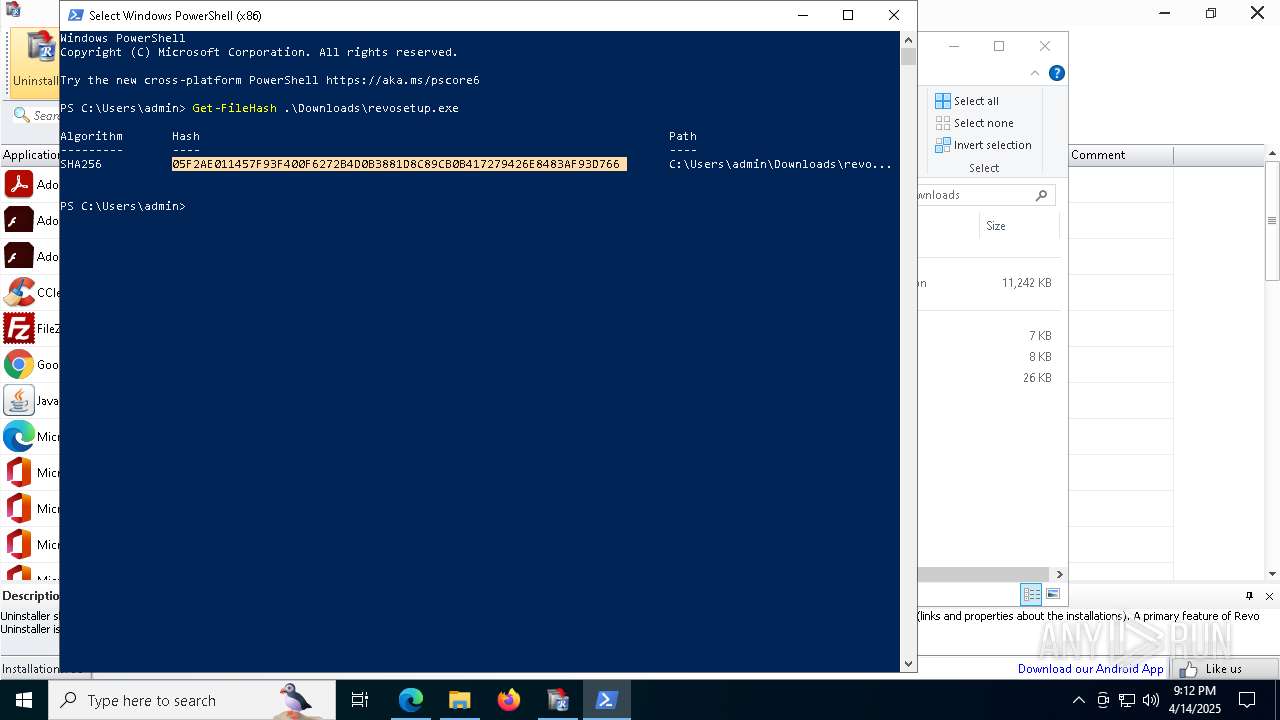
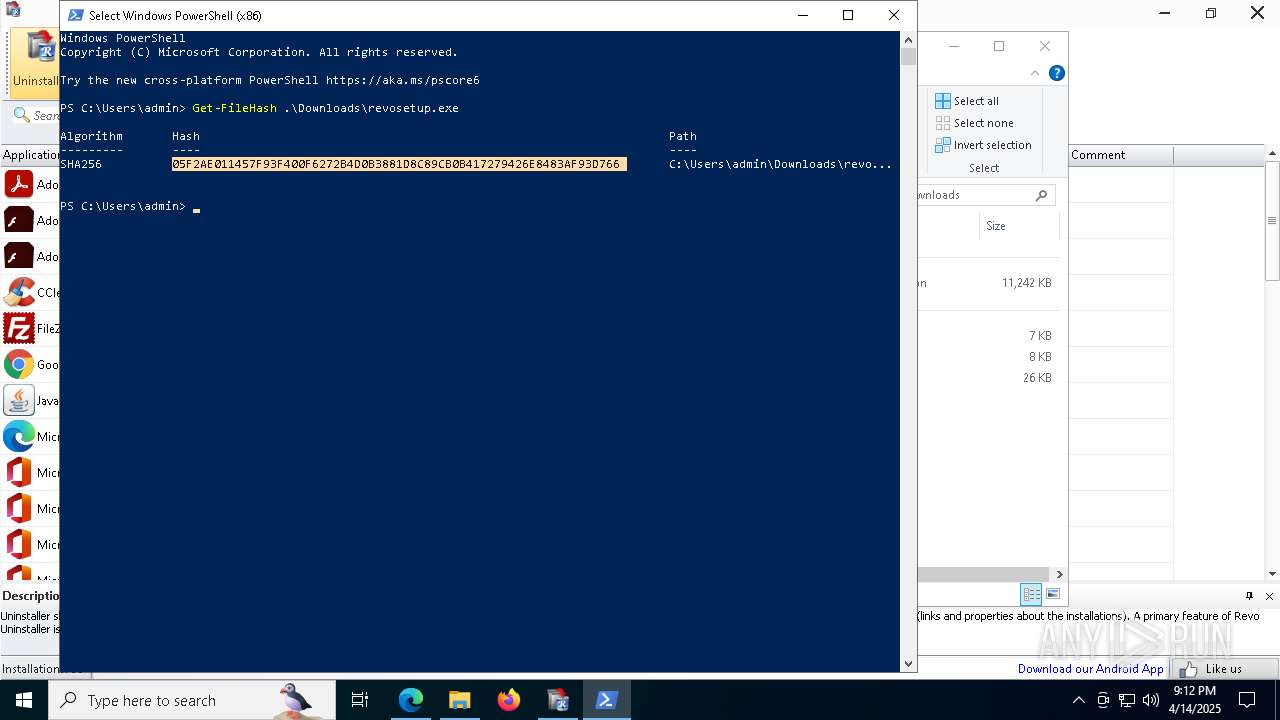
| SHA256: | 4C037C61E4B91CB36B31365143E00DAFF1E7E303B9BA1C5DABD2FC7CF4C57C3C |
| SSDEEP: | 3:6BRddGP6KREbTKq8WO9uKIMk0lA:6dUG2TflA |
MALICIOUS
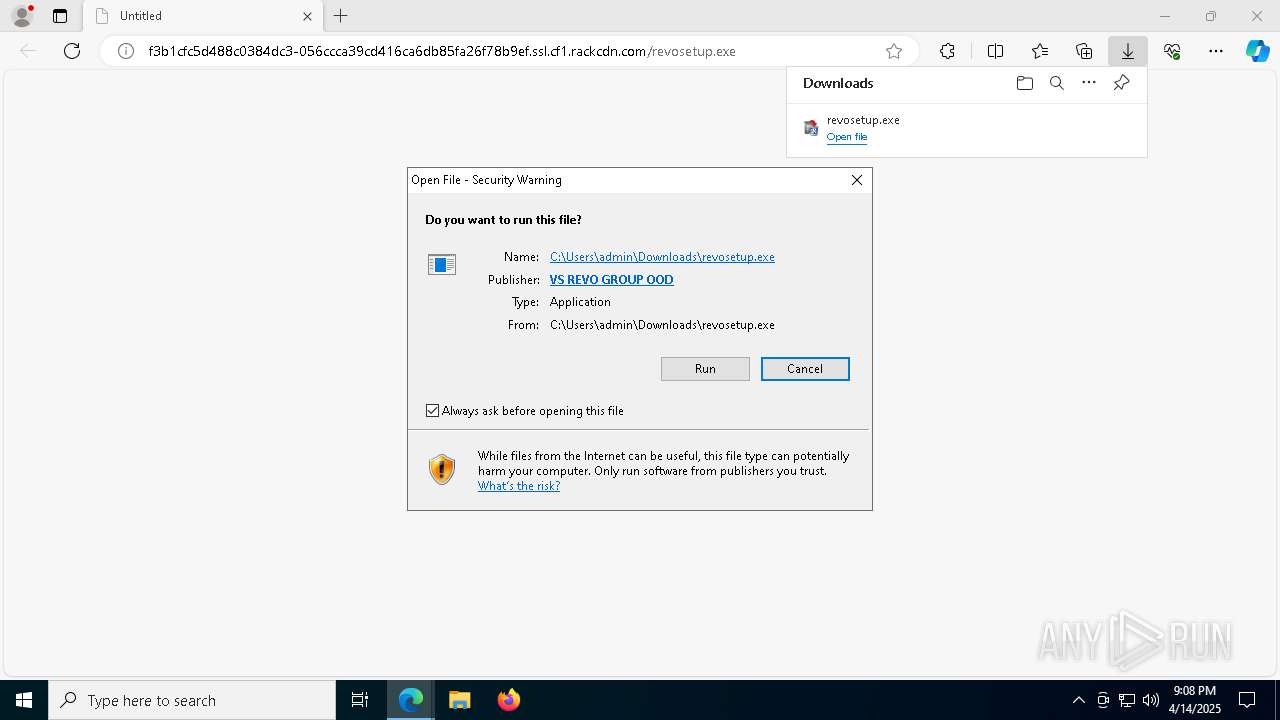
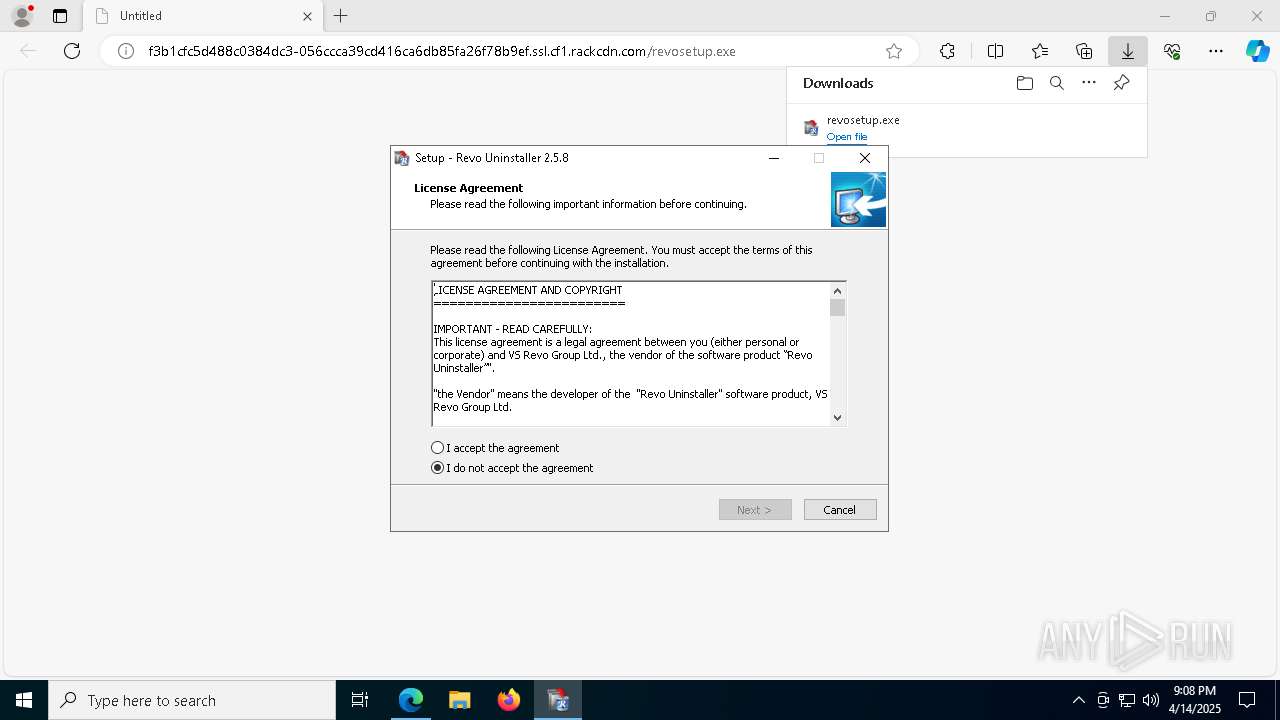
Executing a file with an untrusted certificate
- revosetup.exe (PID: 4024)
- revosetup.exe (PID: 1072)
- RevoUninHelper.exe (PID: 8840)
- RevoUnin.exe (PID: 6392)
- RevoUninHelper.exe (PID: 7900)
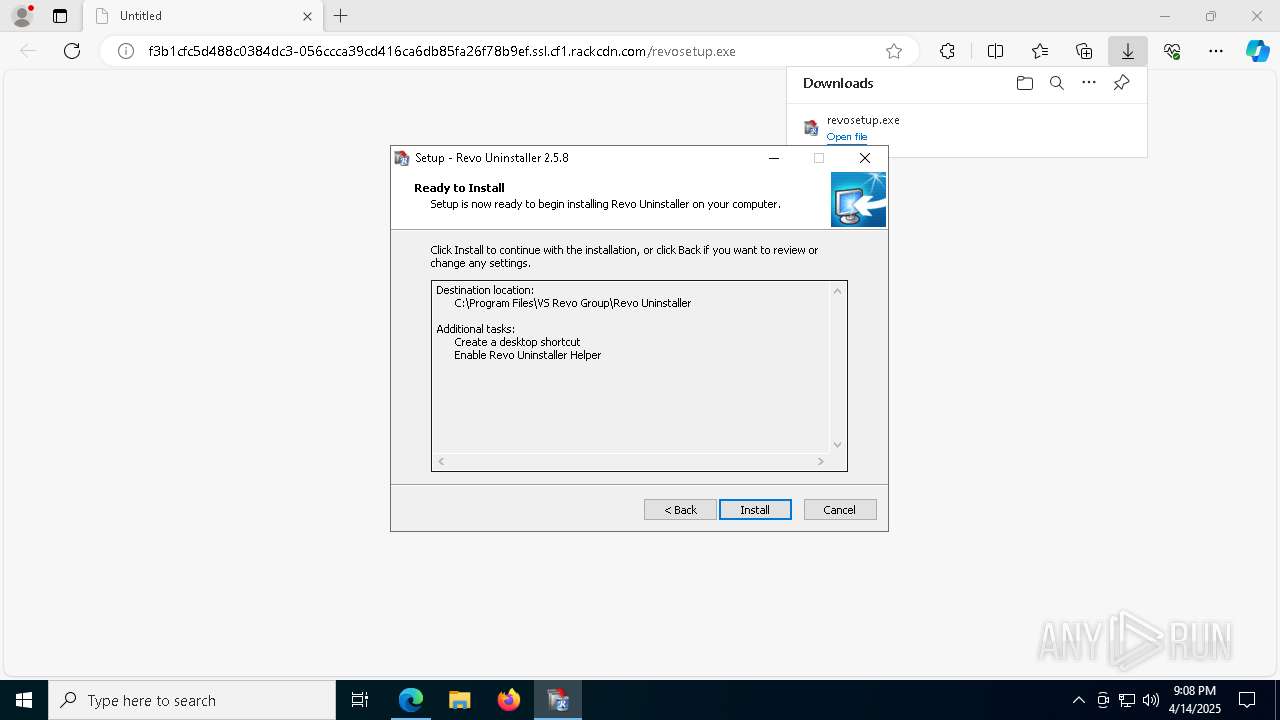
Changes the autorun value in the registry
- rundll32.exe (PID: 2040)
SUSPICIOUS
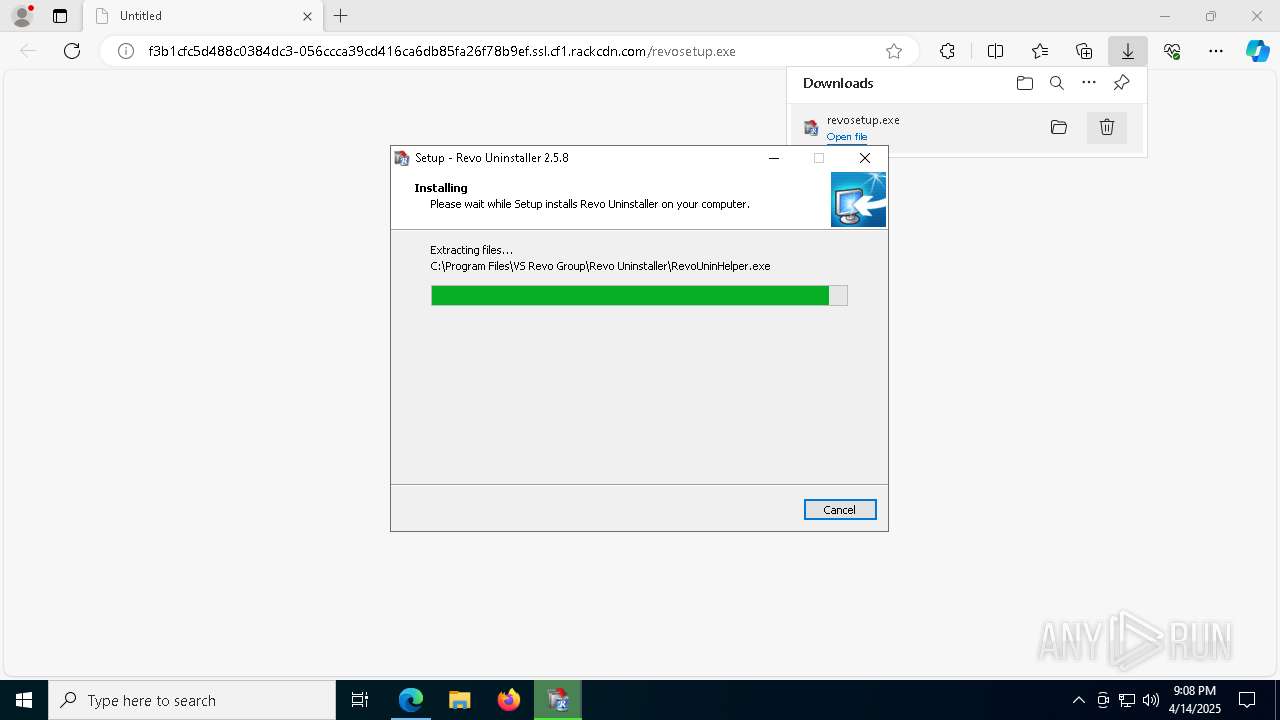
Executable content was dropped or overwritten
- revosetup.exe (PID: 4024)
- revosetup.exe (PID: 1072)
- revosetup.tmp (PID: 1672)
- rundll32.exe (PID: 2040)
Reads security settings of Internet Explorer
- revosetup.tmp (PID: 4620)
- revosetup.tmp (PID: 1672)
- RevoUninHelper.exe (PID: 8840)
- RevoUnin.exe (PID: 6392)
Uses TASKKILL.EXE to kill process
- revosetup.tmp (PID: 1672)
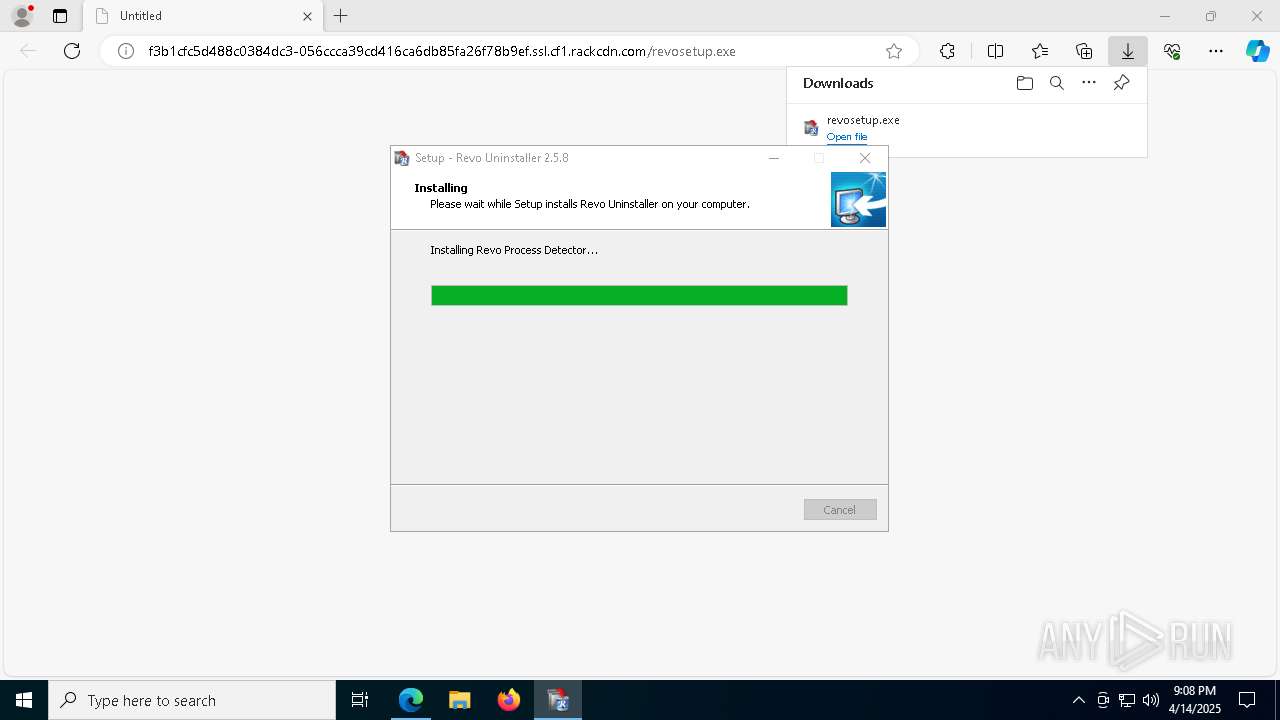
Stops a currently running service
- sc.exe (PID: 632)
Uses RUNDLL32.EXE to load library
- revosetup.tmp (PID: 1672)
Drops a system driver (possible attempt to evade defenses)
- revosetup.tmp (PID: 1672)
- rundll32.exe (PID: 2040)
Reads the Windows owner or organization settings
- revosetup.tmp (PID: 1672)
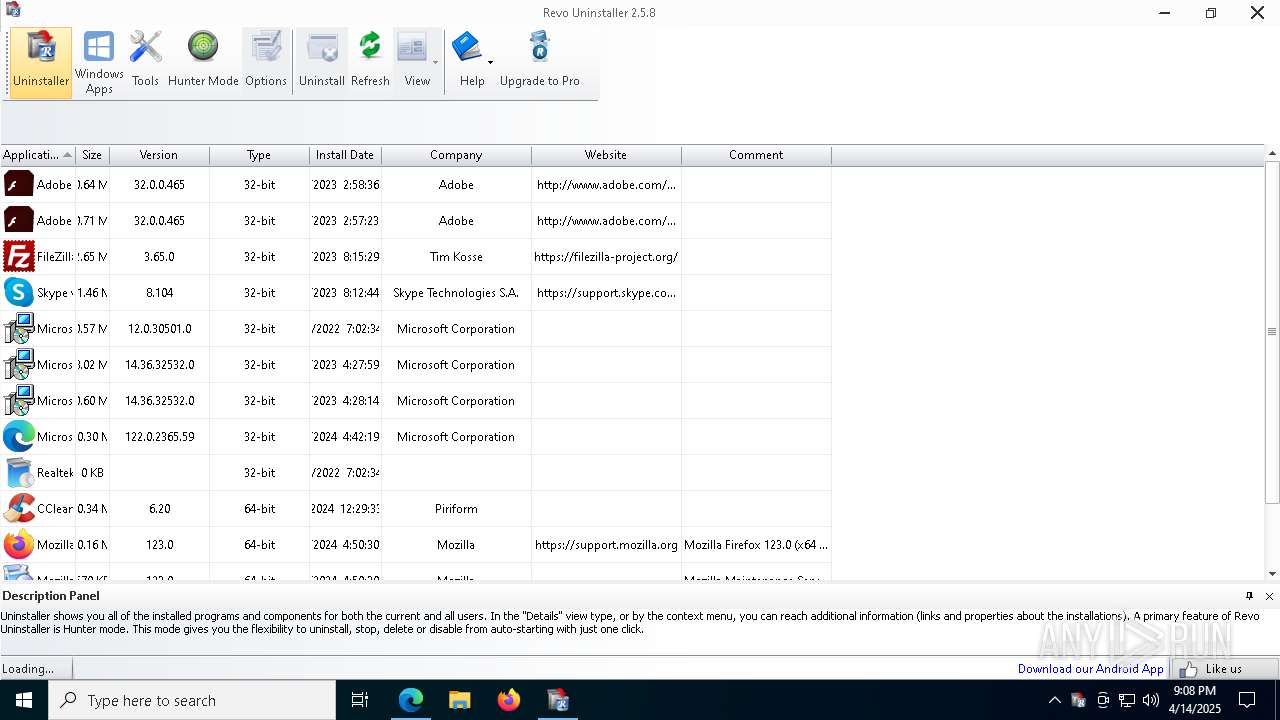
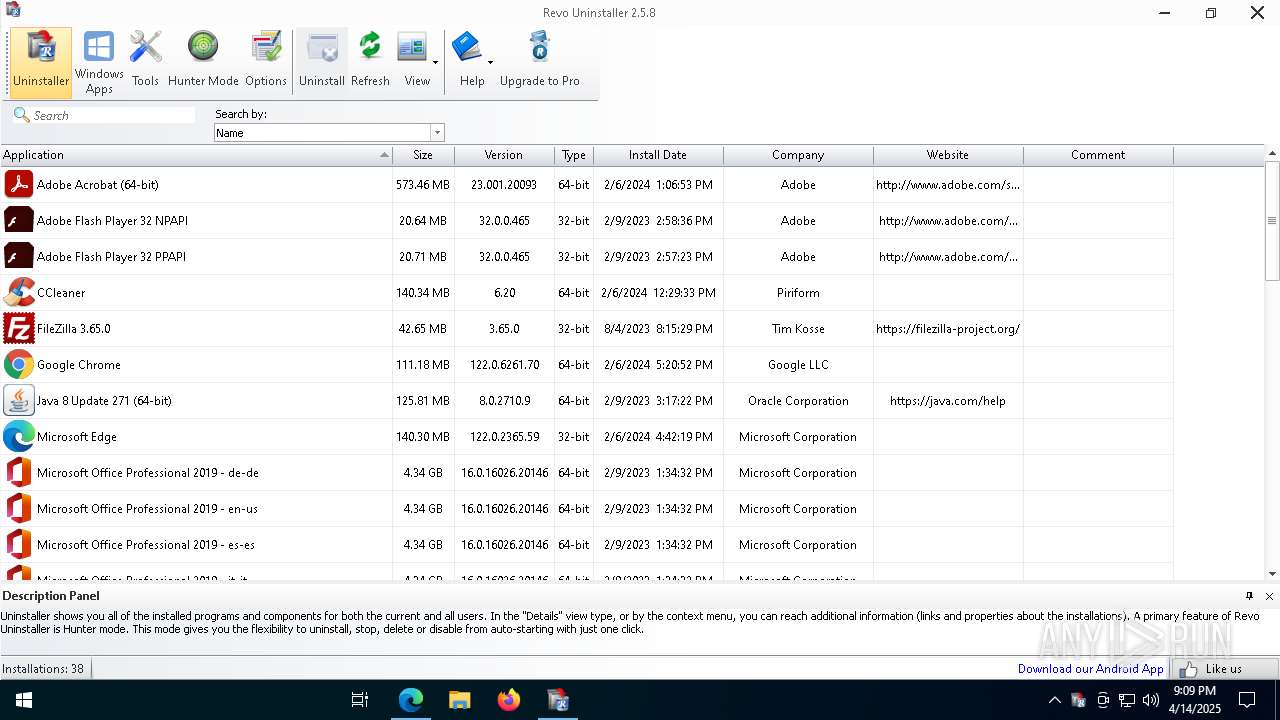
Searches for installed software
- RevoUnin.exe (PID: 6392)
- RevoUninHelper.exe (PID: 8840)
There is functionality for taking screenshot (YARA)
- RevoUninHelper.exe (PID: 8840)
INFO
Application launched itself
- msedge.exe (PID: 900)
Executable content was dropped or overwritten
- msedge.exe (PID: 7392)
- msedge.exe (PID: 900)
- msedge.exe (PID: 4980)
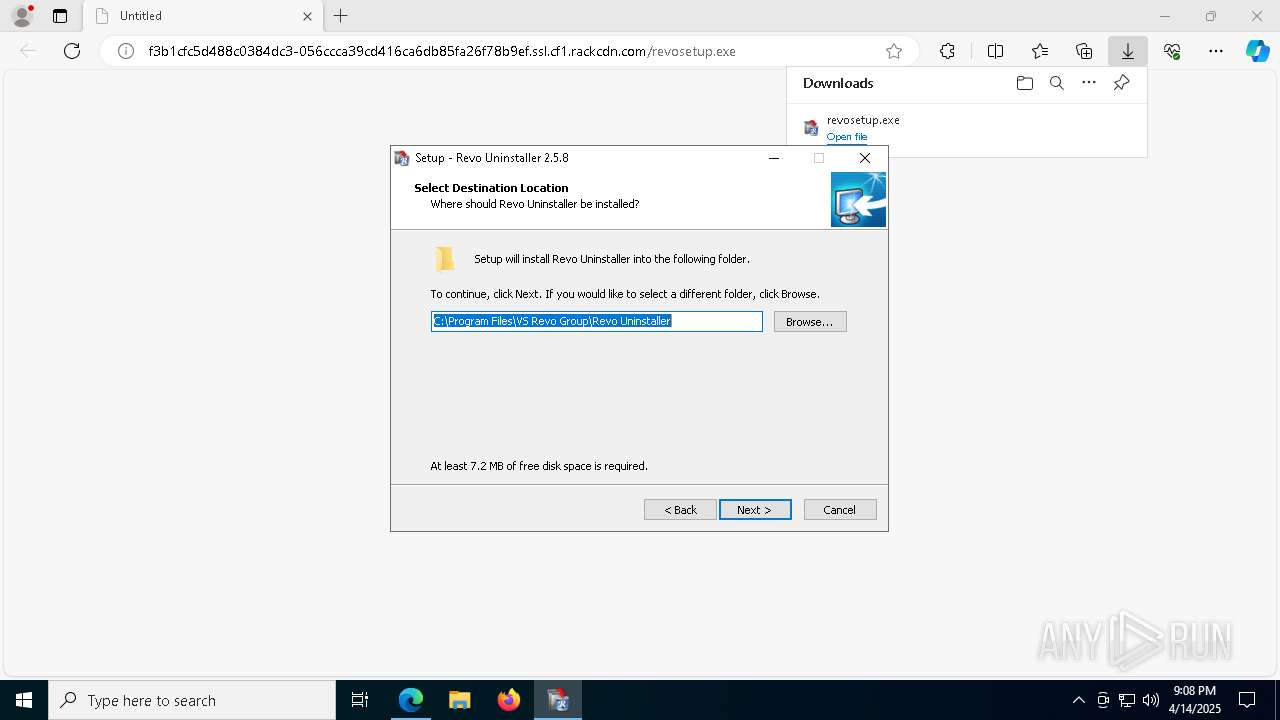
Create files in a temporary directory
- revosetup.exe (PID: 4024)
- revosetup.tmp (PID: 1672)
- revosetup.exe (PID: 1072)
- RevoUninHelper.exe (PID: 8840)
Reads Environment values
- identity_helper.exe (PID: 8664)
Reads the computer name
- identity_helper.exe (PID: 8664)
- revosetup.tmp (PID: 4620)
- revosetup.tmp (PID: 1672)
- RevoUninHelper.exe (PID: 8840)
- RevoUnin.exe (PID: 6392)
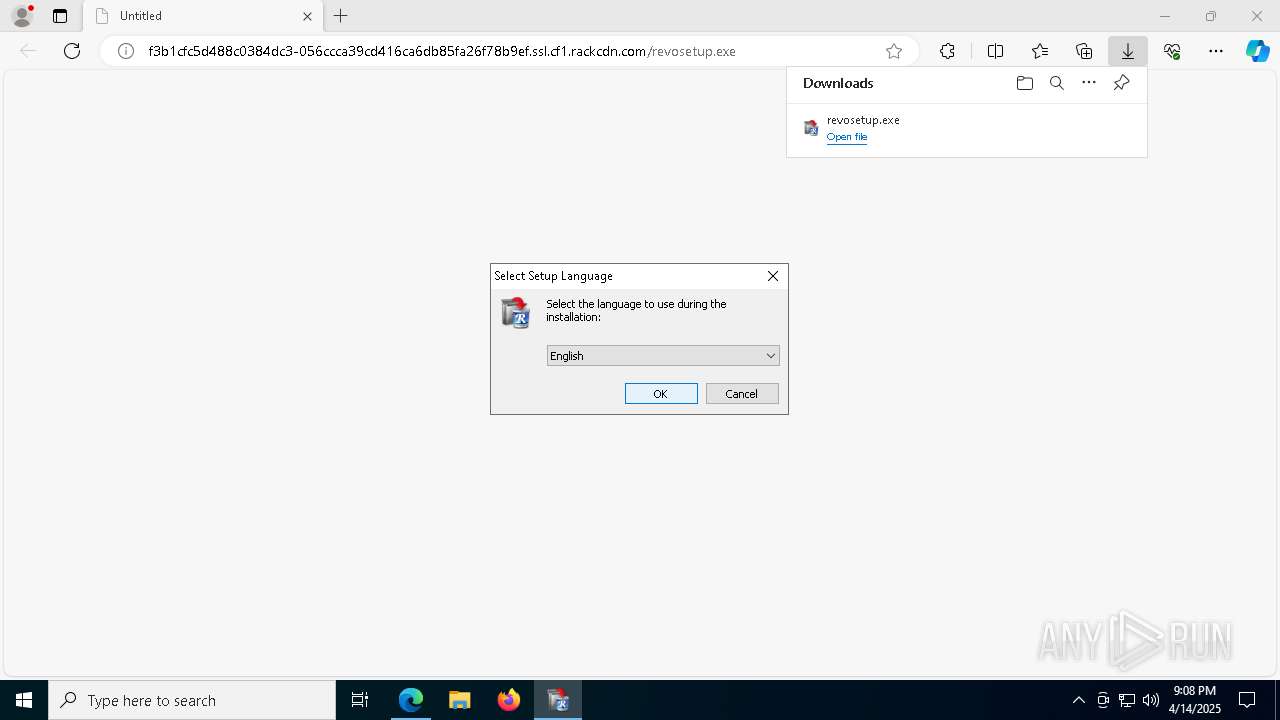
Checks supported languages
- identity_helper.exe (PID: 8664)
- revosetup.tmp (PID: 4620)
- revosetup.exe (PID: 4024)
- revosetup.exe (PID: 1072)
- revosetup.tmp (PID: 1672)
- RevoUninHelper.exe (PID: 8840)
- RevoUnin.exe (PID: 6392)
- RevoUninHelper.exe (PID: 7900)
Process checks computer location settings
- revosetup.tmp (PID: 4620)
- revosetup.tmp (PID: 1672)
Creates files in the program directory
- revosetup.tmp (PID: 1672)
The sample compiled with english language support
- revosetup.tmp (PID: 1672)
- rundll32.exe (PID: 2040)
- msedge.exe (PID: 4980)
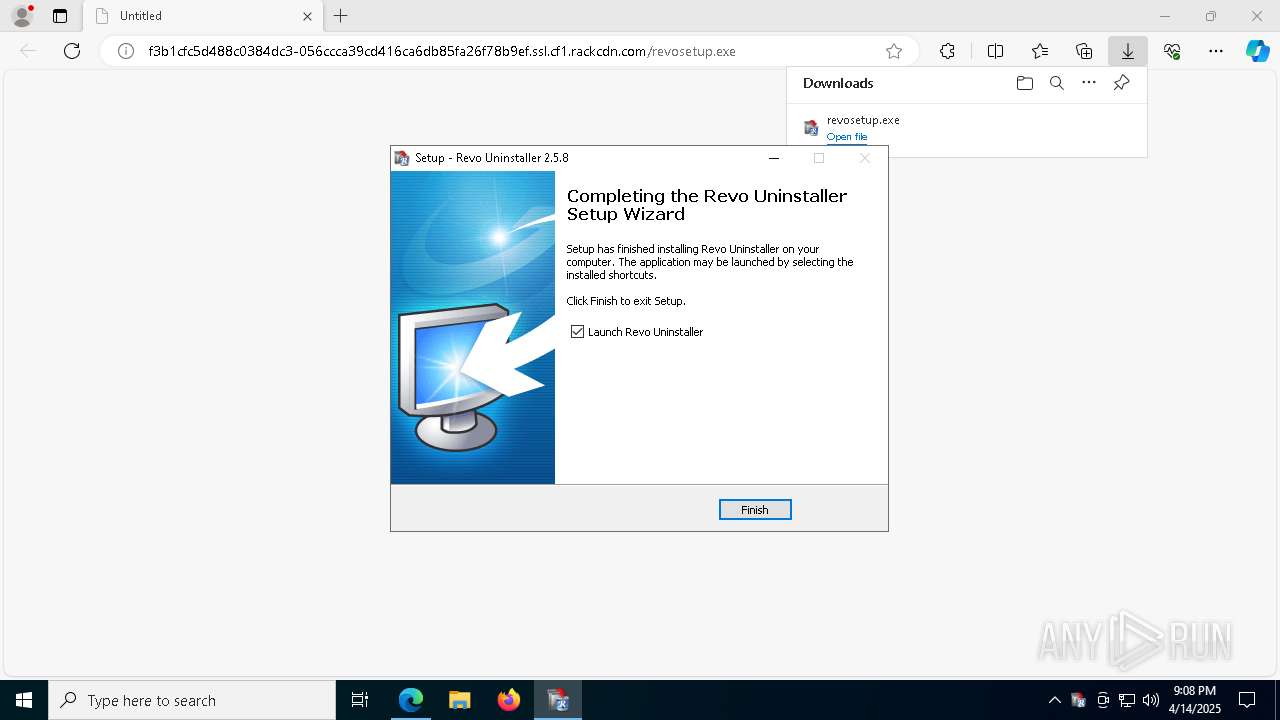
Creates a software uninstall entry
- revosetup.tmp (PID: 1672)
Creates files in the driver directory
- rundll32.exe (PID: 2040)
Detects InnoSetup installer (YARA)
- revosetup.exe (PID: 4024)
- revosetup.tmp (PID: 4620)
- revosetup.exe (PID: 1072)
- revosetup.tmp (PID: 1672)
Compiled with Borland Delphi (YARA)
- revosetup.exe (PID: 4024)
- revosetup.exe (PID: 1072)
- revosetup.tmp (PID: 1672)
- revosetup.tmp (PID: 4620)
Reads the time zone
- runonce.exe (PID: 8812)
Reads security settings of Internet Explorer
- runonce.exe (PID: 8812)
REVOUNINSTALLER mutex has been found
- RevoUninHelper.exe (PID: 8840)
- RevoUninHelper.exe (PID: 7900)
Local mutex for internet shortcut management
- RevoUninHelper.exe (PID: 8840)
- RevoUnin.exe (PID: 6392)
Checks proxy server information
- RevoUninHelper.exe (PID: 8840)
- slui.exe (PID: 5344)
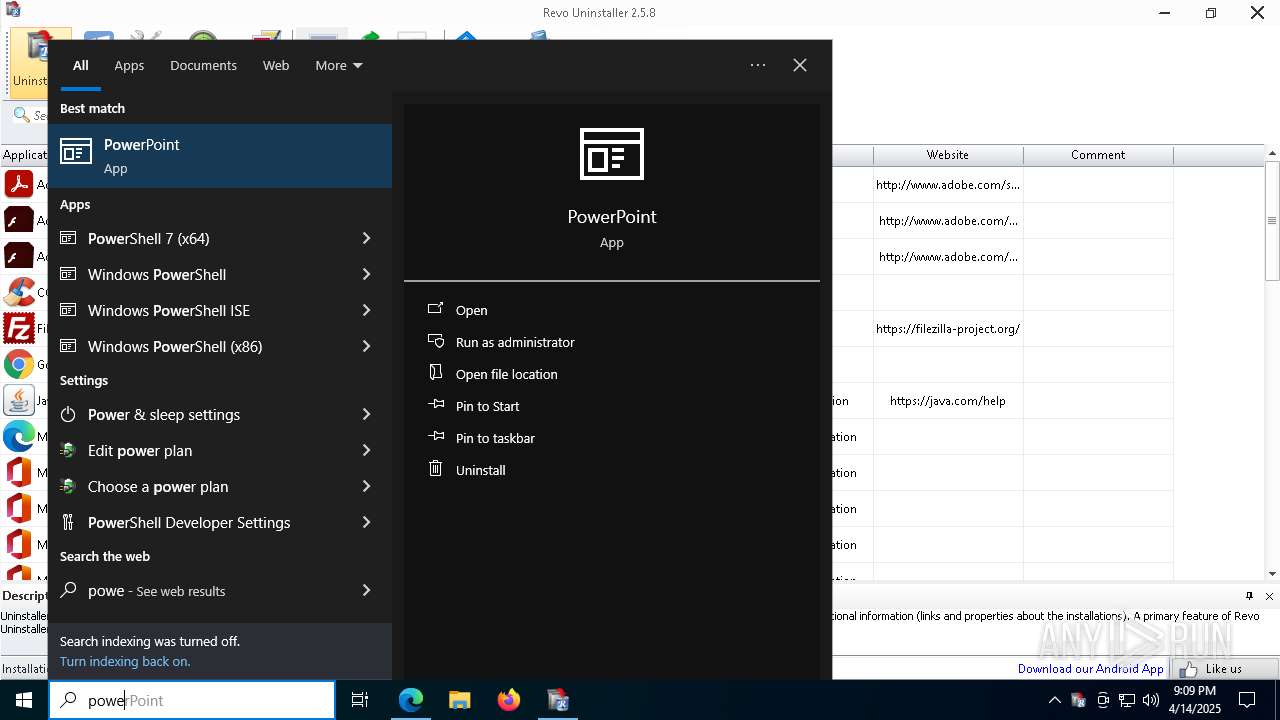
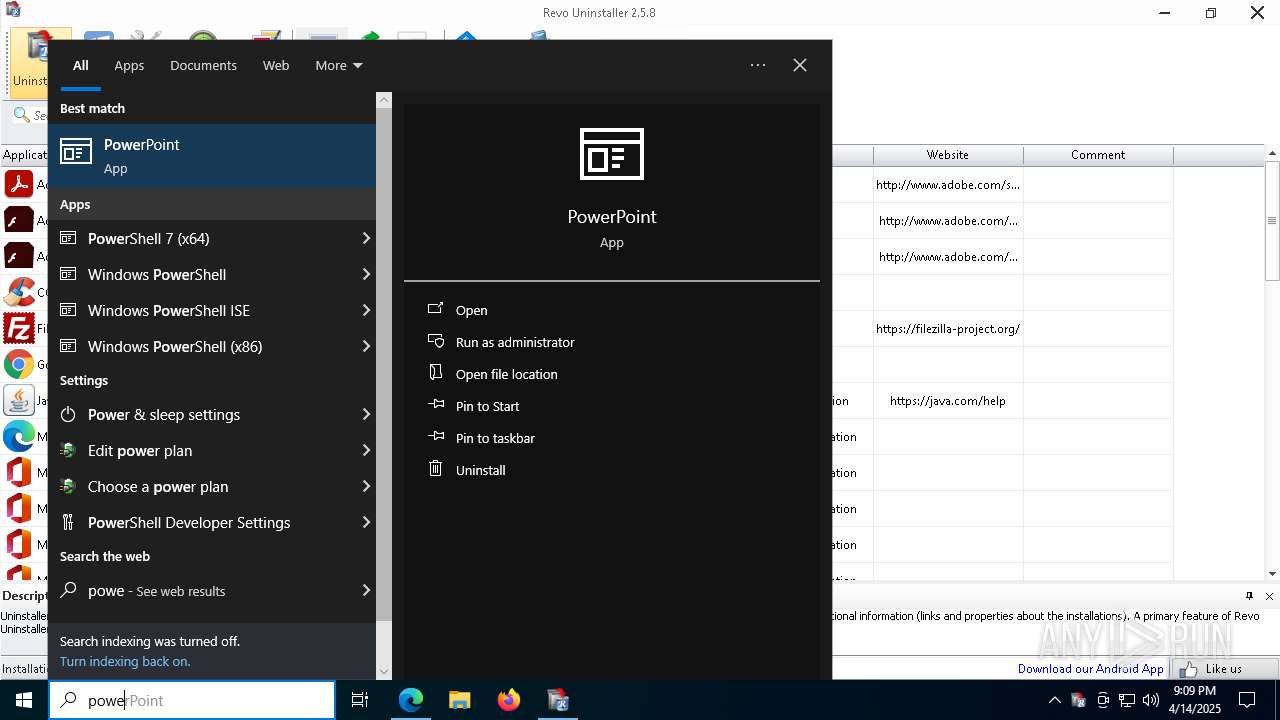
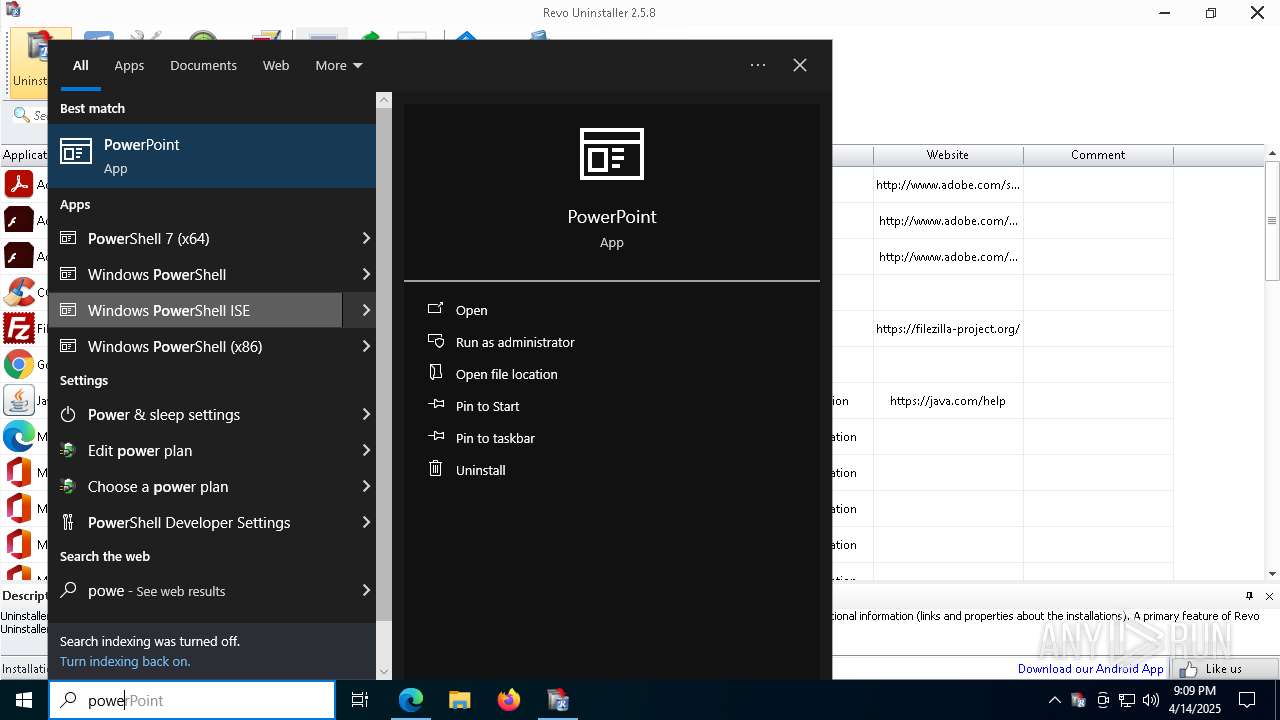
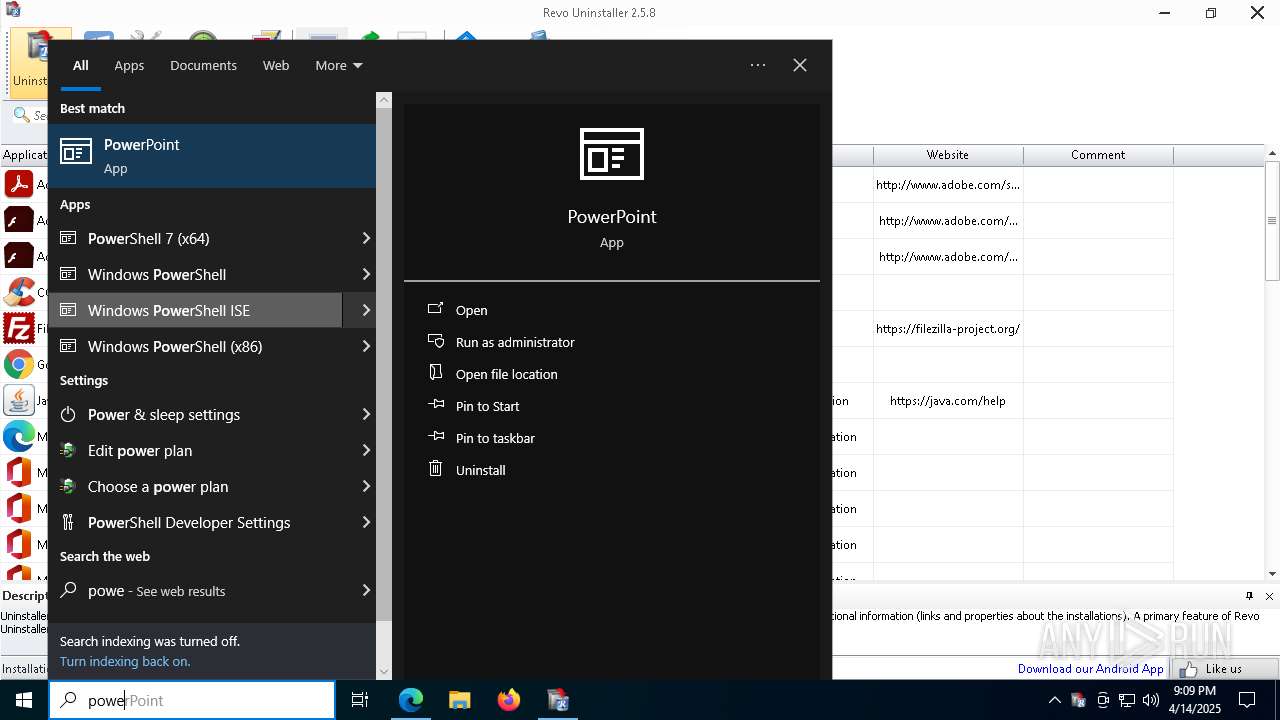
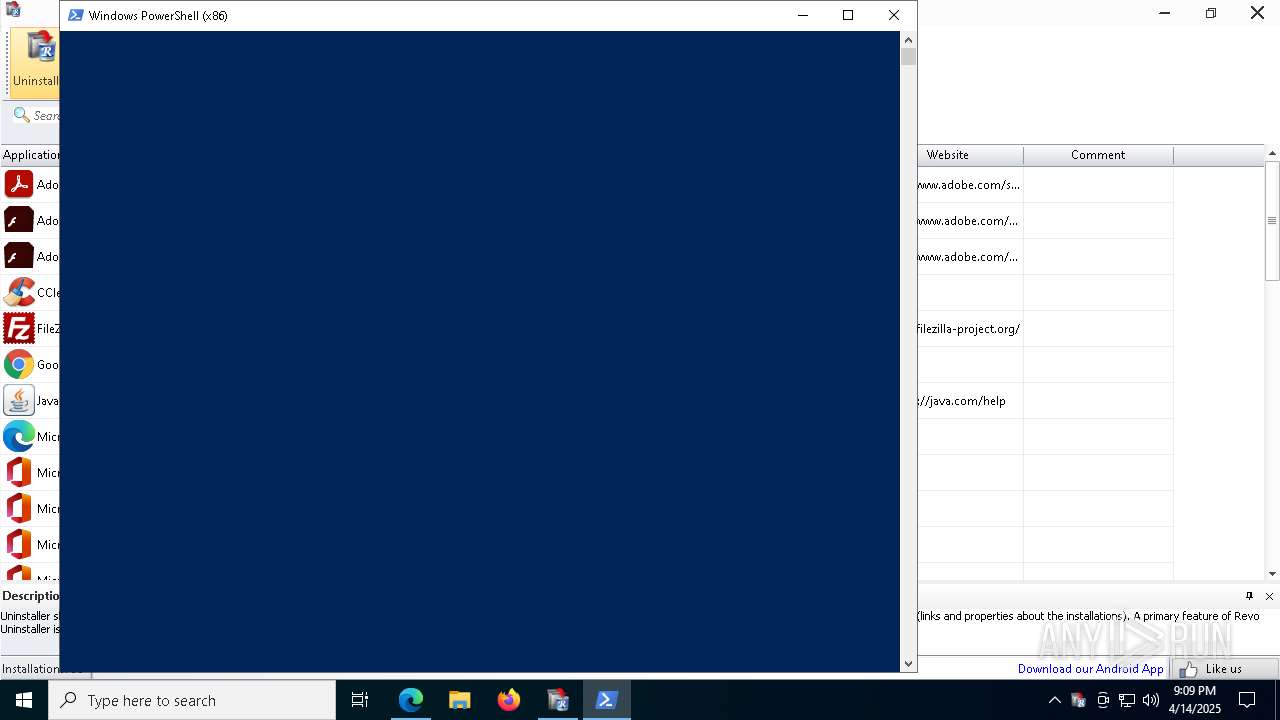
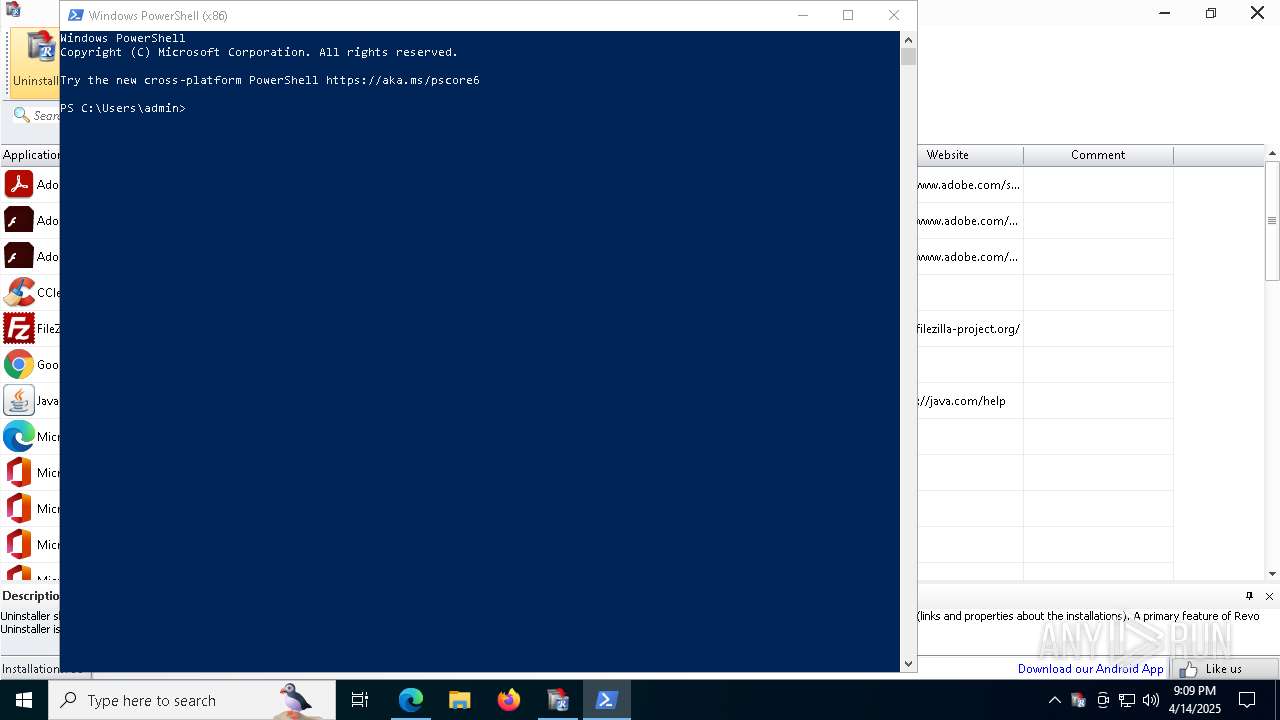
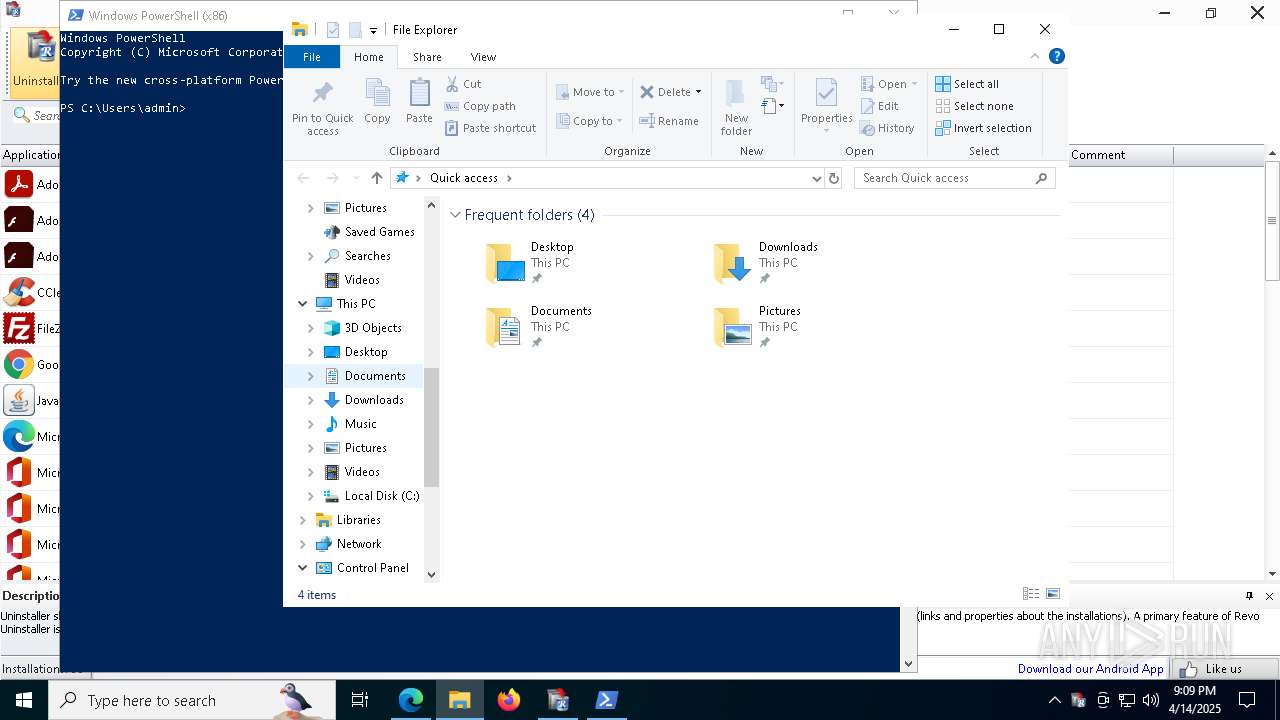
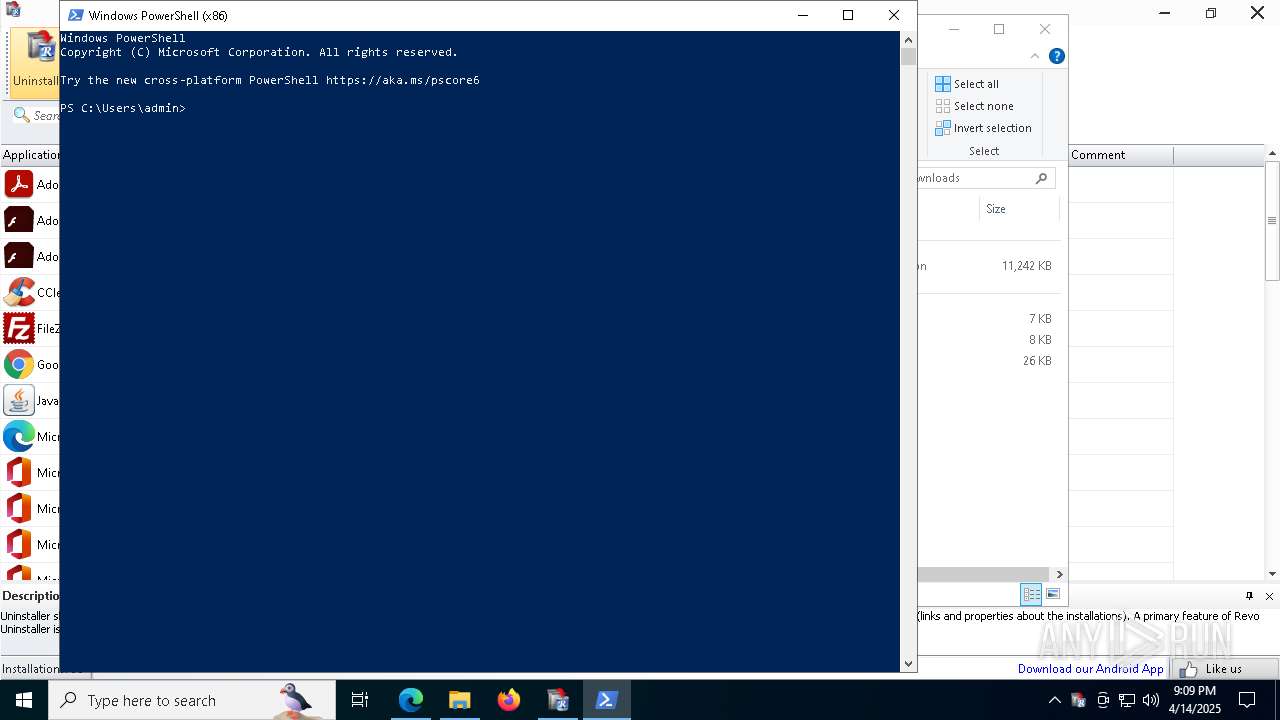
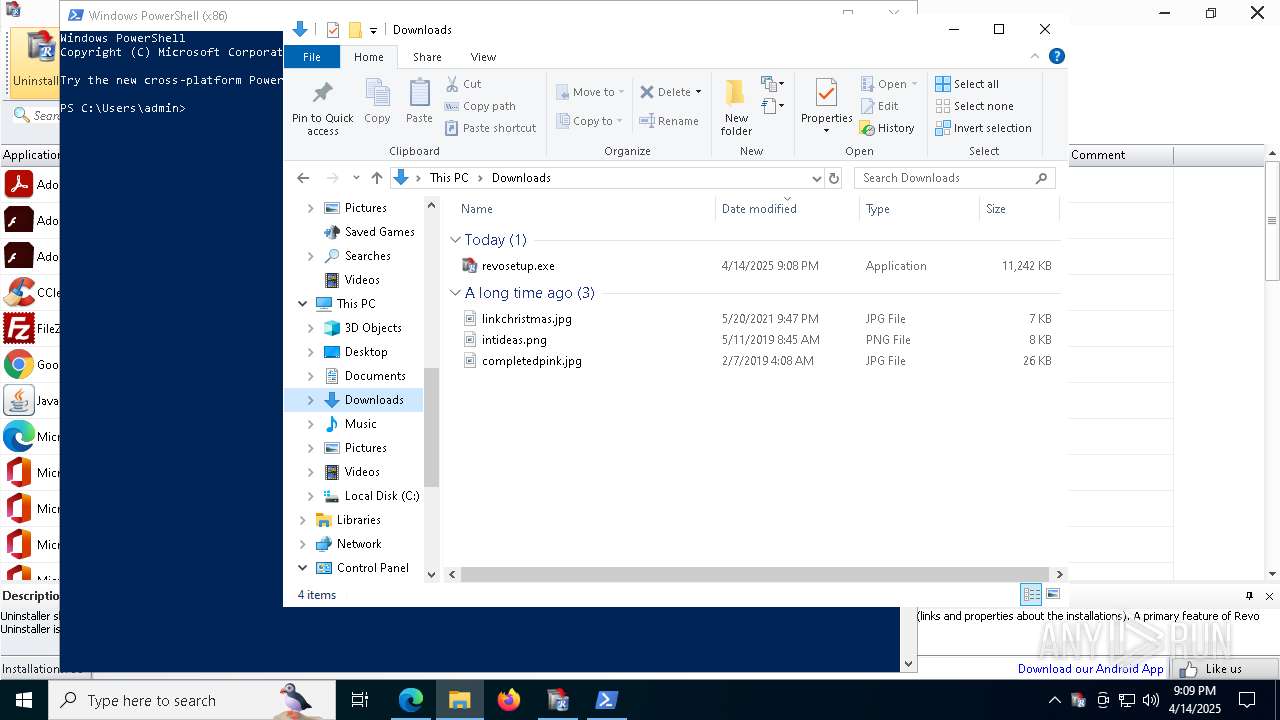
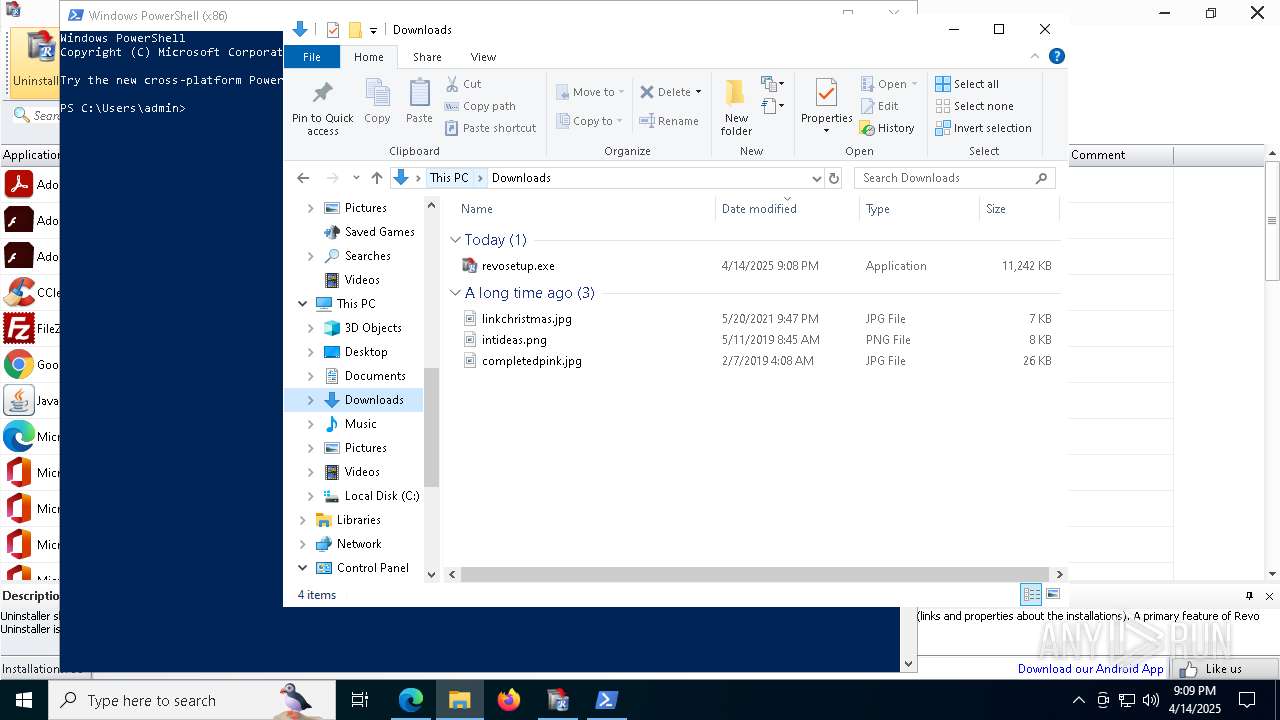
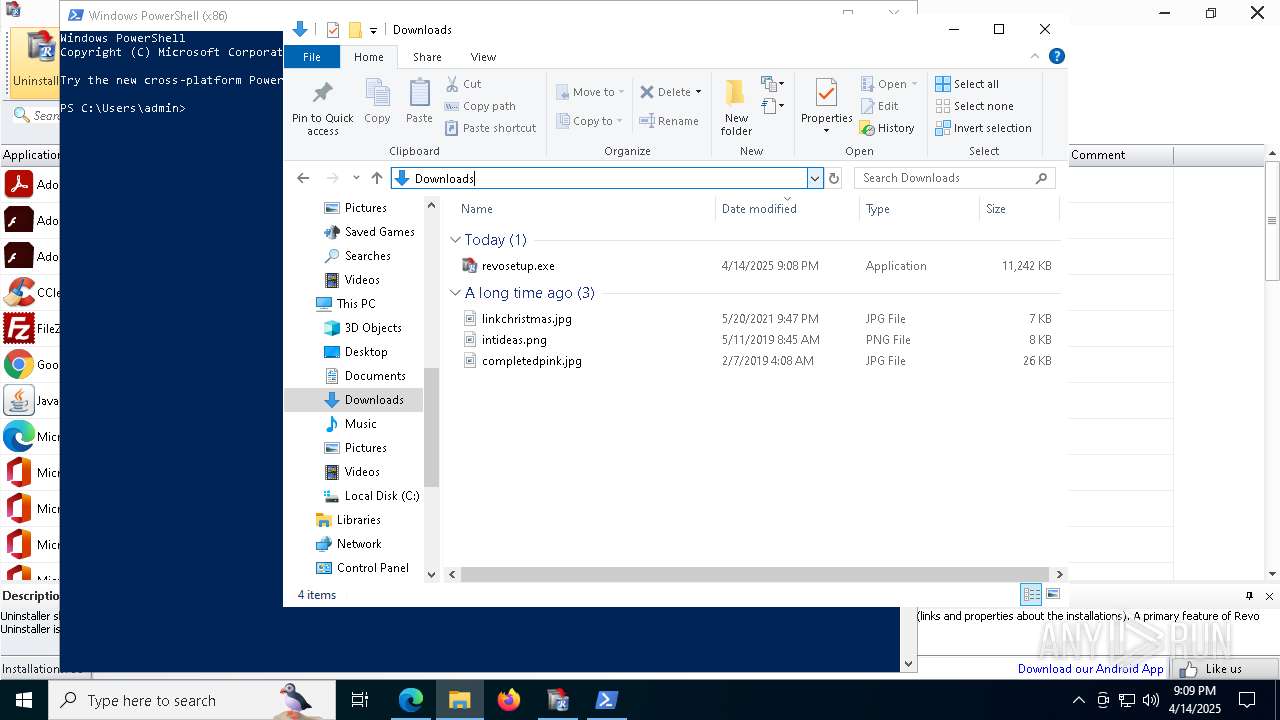
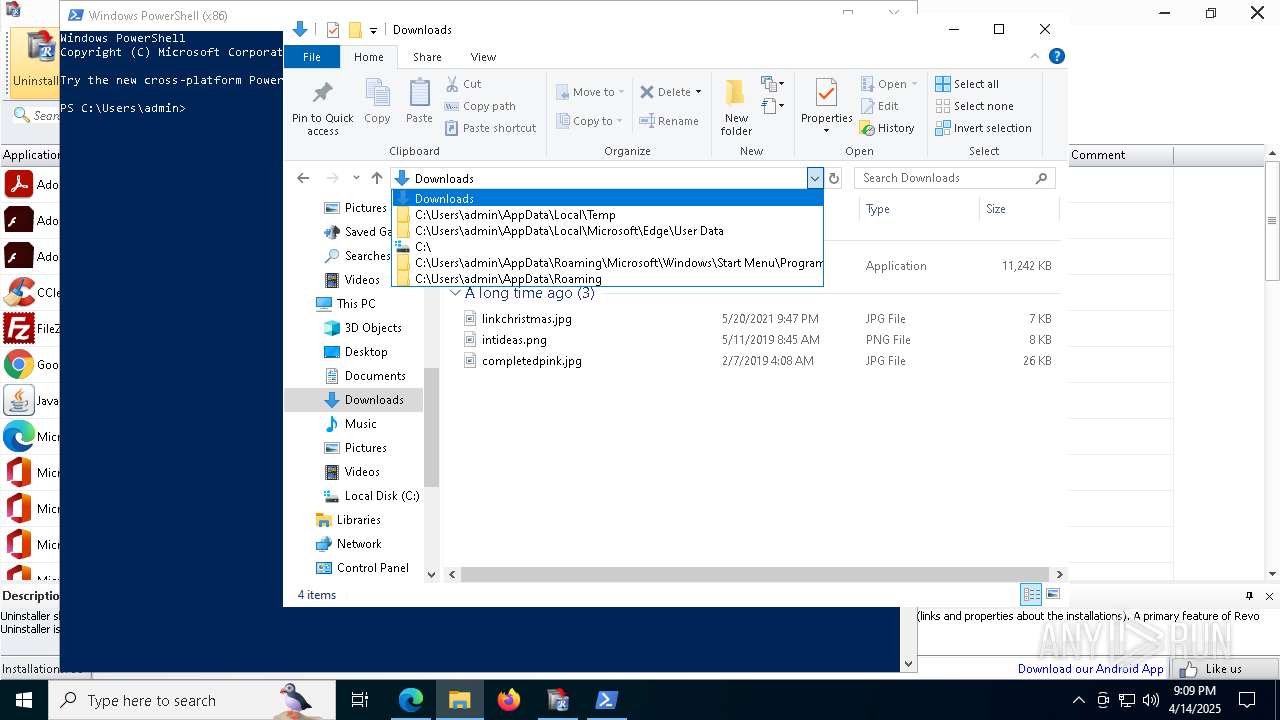
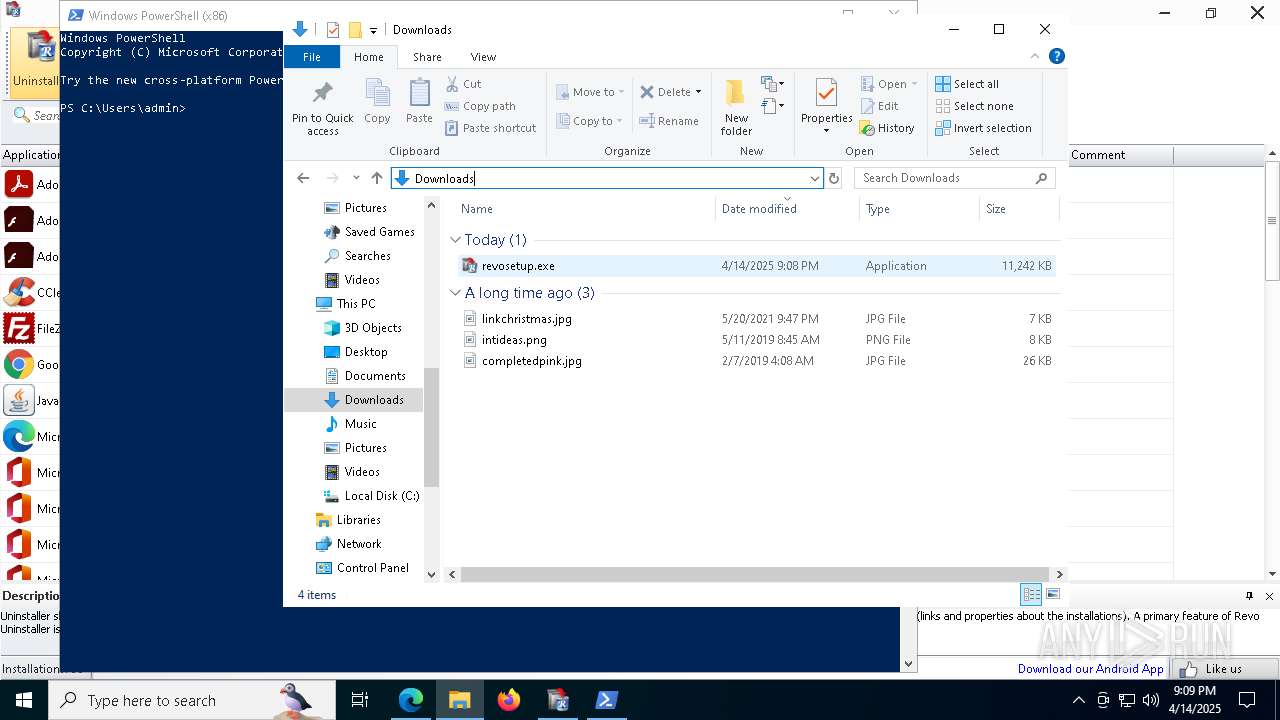
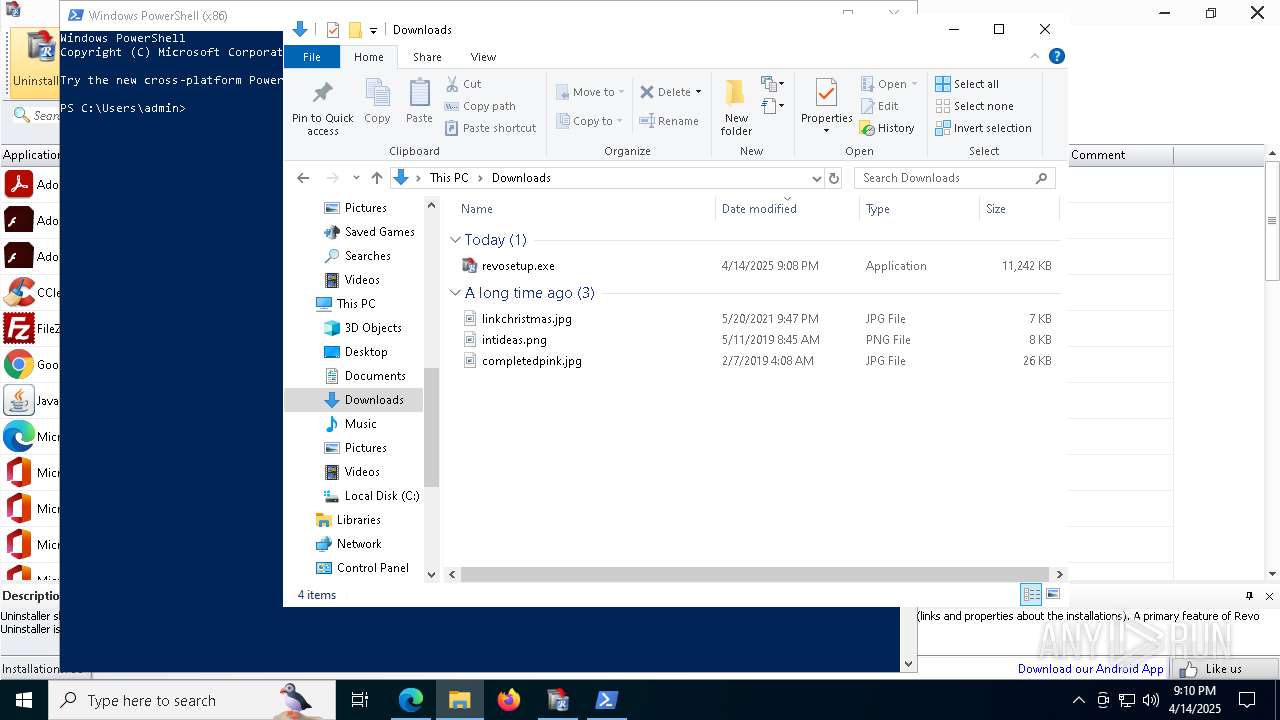
Manual execution by a user
- powershell.exe (PID: 5392)
Reads the software policy settings
- slui.exe (PID: 8556)
- RevoUninHelper.exe (PID: 8840)
- slui.exe (PID: 5344)
Checks current location (POWERSHELL)
- powershell.exe (PID: 5392)
Reads the machine GUID from the registry
- RevoUninHelper.exe (PID: 8840)
Creates files or folders in the user directory
- RevoUninHelper.exe (PID: 8840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
217
Monitored processes
74
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=5472 --field-trial-handle=2400,i,10554329454801084905,1926126473258563193,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 632 | "C:\Windows\System32\sc.exe" stop revoprocessdetector | C:\Windows\SysWOW64\sc.exe | — | revosetup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "f3b1cfc5d488c0384dc3-056ccca39cd416ca6db85fa26f78b9ef.ssl.cf1.rackcdn.com/revosetup.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | "C:\Users\admin\Downloads\revosetup.exe" /SPAWNWND=$30260 /NOTIFYWND=$50348 | C:\Users\admin\Downloads\revosetup.exe | revosetup.tmp | ||||||||||||
User: admin Company: VS Revo Group Integrity Level: HIGH Description: Revo Uninstaller Exit code: 0 Version: 2.5.8.0 Modules
| |||||||||||||||
| 1096 | "C:\Windows\System32\taskkill.exe" /f /im RevoUninHelper.exe | C:\Windows\SysWOW64\taskkill.exe | — | revosetup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6716 --field-trial-handle=2400,i,10554329454801084905,1926126473258563193,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\Temp\is-JUOC8.tmp\revosetup.tmp" /SL5="$40266,10861351,266240,C:\Users\admin\Downloads\revosetup.exe" /SPAWNWND=$30260 /NOTIFYWND=$50348 | C:\Users\admin\AppData\Local\Temp\is-JUOC8.tmp\revosetup.tmp | revosetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2040 | "rundll32.exe " SETUPAPI.DLL,InstallHinfSection DefaultInstall 132 C:\Program Files\VS Revo Group\Revo Uninstaller\RevoProcessDetector.inf | C:\Windows\System32\rundll32.exe | revosetup.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 515
Read events
23 427
Write events
87
Delete events
1
Modification events
| (PID) Process: | (900) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (900) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (900) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (900) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (900) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3E9504BB59912F00 | |||
| (PID) Process: | (900) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8A3711BB59912F00 | |||
| (PID) Process: | (900) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524998 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {897C51F4-591E-4C2D-A0D9-0DFE268049DF} | |||
| (PID) Process: | (900) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CEED55BB59912F00 | |||
| (PID) Process: | (8412) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000067DB5B5381ADDB01 | |||
| (PID) Process: | (900) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
34
Suspicious files
429
Text files
186
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 900 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10be12.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 900 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10be41.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10be41.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 900 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 900 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10be41.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 900 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10be41.TMP | — | |
MD5:— | SHA256:— | |||
| 900 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
67
DNS requests
75
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
900 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.159:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
900 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
900 | msedge.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA%2BuABQbnxYl94AZ8ln%2F%2FN8%3D | unknown | — | — | whitelisted |
6744 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6744 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8156 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744952133&P2=404&P3=2&P4=nnYN9cWfBAJFAQR09%2fOt5GYKMZQQCYghTvO%2bCY9YcdsUakJab00BJQ7j04nDWl14cSqSZw5SZF2Jpo2yW8rShw%3d%3d | unknown | — | — | whitelisted |
8156 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744952133&P2=404&P3=2&P4=nnYN9cWfBAJFAQR09%2fOt5GYKMZQQCYghTvO%2bCY9YcdsUakJab00BJQ7j04nDWl14cSqSZw5SZF2Jpo2yW8rShw%3d%3d | unknown | — | — | whitelisted |
8156 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1744952133&P2=404&P3=2&P4=nnYN9cWfBAJFAQR09%2fOt5GYKMZQQCYghTvO%2bCY9YcdsUakJab00BJQ7j04nDWl14cSqSZw5SZF2Jpo2yW8rShw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.159:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
900 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7392 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7392 | msedge.exe | 23.45.97.130:80 | f3b1cfc5d488c0384dc3-056ccca39cd416ca6db85fa26f78b9ef.ssl.cf1.rackcdn.com | AKAMAI-AS | DE | whitelisted |
7392 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7392 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7392 | msedge.exe | 23.45.97.130:443 | f3b1cfc5d488c0384dc3-056ccca39cd416ca6db85fa26f78b9ef.ssl.cf1.rackcdn.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
f3b1cfc5d488c0384dc3-056ccca39cd416ca6db85fa26f78b9ef.ssl.cf1.rackcdn.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |