| File name: | 64bit Patch.exe |
| Full analysis: | https://app.any.run/tasks/f7916ef6-2fb7-4b11-9e37-bf29d557904b |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 05:27:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 91F589C9C32FFBB40FC8E2F27E0ABF12 |
| SHA1: | D05E40F0D27388C85F3F0657B021F42BC85037D8 |
| SHA256: | 4BF6C3C68074D308CC46349D5A883A94D47E0780CD50973359C41E6BC6027E63 |
| SSDEEP: | 49152:OAI+lyuIxV3m78qbdz/e0v5mpjxyqAU2xhO0b1adA:OAI+suIxAnZzh5mpj2x5adA |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 2804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 1992-Jun-19 22:22:17 |
| Detected languages: |
|
| Comments: | - |
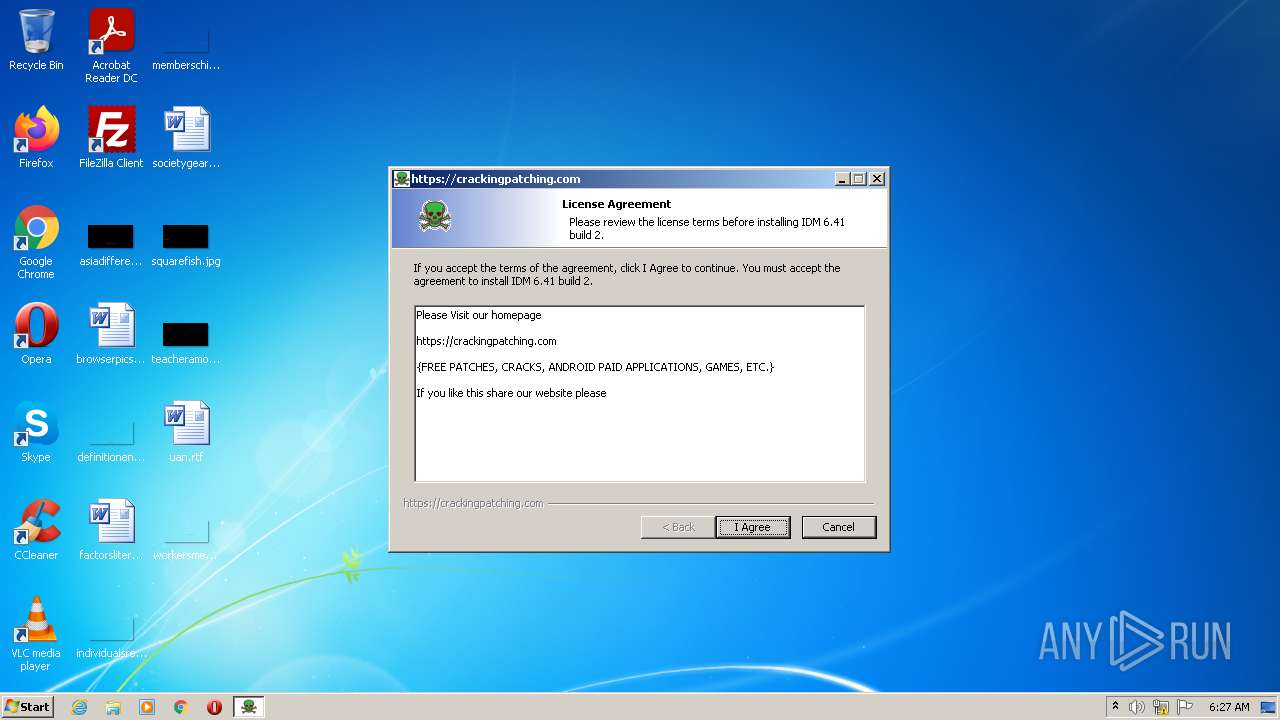
| CompanyName: | CrackingPatching |
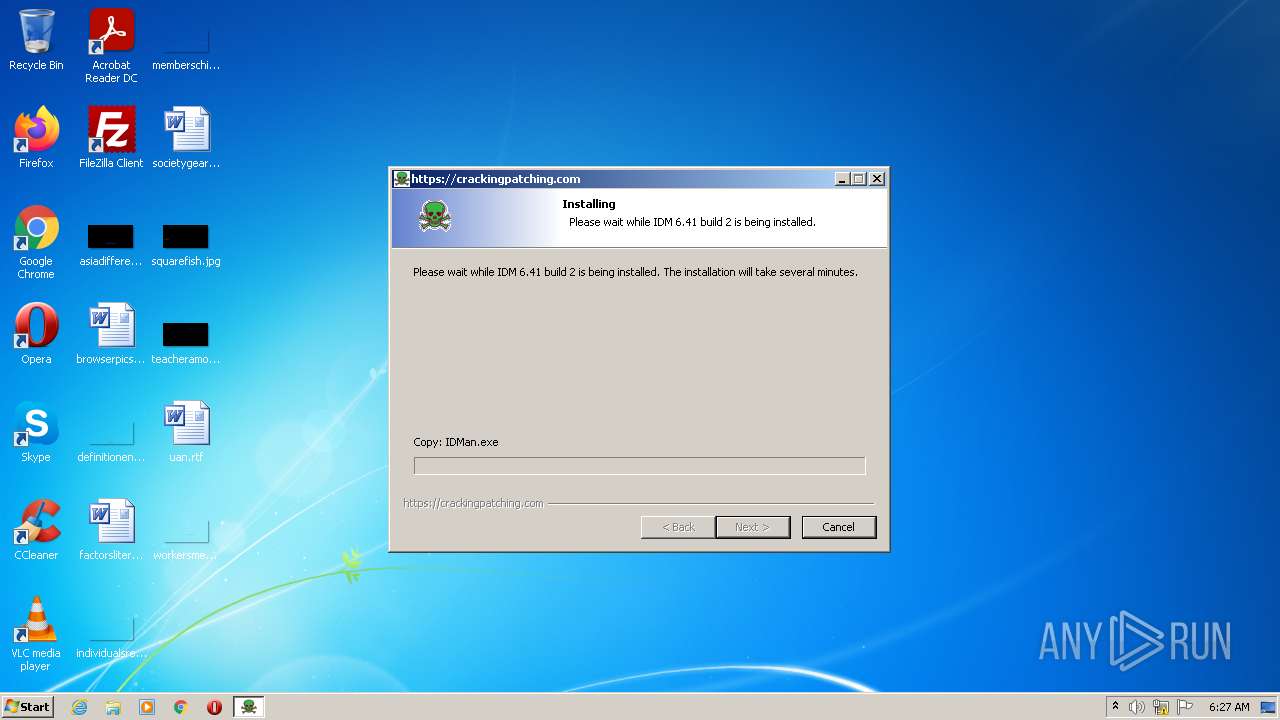
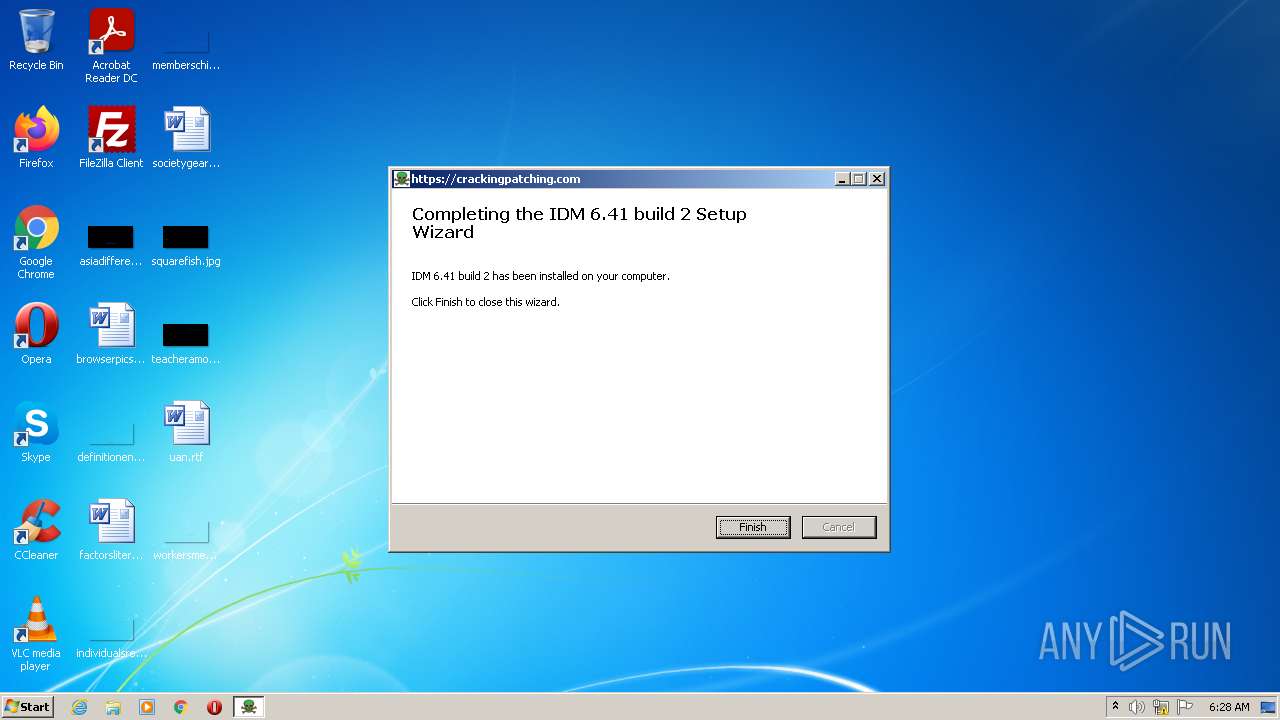
| FileDescription: | IDM 6.41 build 2 1.0.0 Installation |
| FileVersion: | 1.0.0 |
| LegalCopyright: | CrackingPatching |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 80 |
| e_cp: | 2 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | 15 |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | 26 |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 256 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 8 |
| TimeDateStamp: | 1992-Jun-19 22:22:17 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 4096 | 148684 | 148992 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59443 |
DATA | 155648 | 10388 | 10752 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 167936 | 4341 | 0 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.idata | 176128 | 6040 | 6144 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88555 |
.tls | 184320 | 8 | 0 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.rdata | 188416 | 24 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 192512 | 6276 | 6656 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 200704 | 290656 | 290816 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.14034 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.78849 | 884 | UNKNOWN | Russian - Russia | RT_VERSION |
50 | 5.24025 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 4.94231 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 4.73718 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 4.51902 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
54 | 4.05378 | 270376 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.75922 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 (#2) | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
Imports
advapi32.dll |
advapi32.dll (#2) |
advapi32.dll (#3) |
cabinet.dll |
comctl32.dll |
gdi32.dll |
gdi32.dll (#2) |
kernel32.dll |
kernel32.dll (#2) |
kernel32.dll (#3) |
Total processes
43
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | "C:\Users\admin\AppData\Local\Temp\64bit Patch.exe" | C:\Users\admin\AppData\Local\Temp\64bit Patch.exe | — | Explorer.EXE | |||||||||||
User: admin Company: CrackingPatching Integrity Level: MEDIUM Description: IDM 6.41 build 2 1.0.0 Installation Exit code: 3221226540 Version: 1.0.0 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Internet Explorer\iexplore.exe" https://crackingpatching.com/ | C:\Program Files\Internet Explorer\iexplore.exe | 64bit Patch.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2804 | "C:\Program Files\Internet Explorer\iexplore.exe" https://crackingpatching.com/2021/01/idm-crack-patch.html | C:\Program Files\Internet Explorer\iexplore.exe | — | 64bit Patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3252 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2404 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3276 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2804 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3936 | "C:\Users\admin\AppData\Local\Temp\64bit Patch.exe" | C:\Users\admin\AppData\Local\Temp\64bit Patch.exe | Explorer.EXE | ||||||||||||
User: admin Company: CrackingPatching Integrity Level: HIGH Description: IDM 6.41 build 2 1.0.0 Installation Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
Total events
30 039
Read events
29 545
Write events
487
Delete events
7
Modification events
| (PID) Process: | (3936) 64bit Patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202 | |||
| (PID) Process: | (3936) 64bit Patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlot |
Value: 19 | |||
| (PID) Process: | (3936) 64bit Patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (3936) 64bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (3936) 64bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1 |
| Operation: | write | Name: | 1 |
Value: 940031000000000009553268110050524F4752417E3200007C0008000400EFBEFA40C02C095532682A000000890B0000000001000000000000000000520000000000500072006F006700720061006D002000460069006C0065007300200028007800380036002900000040007300680065006C006C00330032002E0064006C006C002C002D0032003100380031003700000018000000 | |||
| (PID) Process: | (3936) 64bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1 |
| Operation: | write | Name: | NodeSlot |
Value: 18 | |||
| (PID) Process: | (3936) 64bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1\1 |
| Operation: | write | Name: | 0 |
Value: 6400310000000000095532681000455053494C4F7E3100004C0008000400EFBE09553268095532682A0000007938010000000300000000000000000000000000000045007000730069006C006F006E0020005300710075006100720065006400000018000000 | |||
| (PID) Process: | (3936) 64bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1\1 |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (3936) 64bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1\1 |
| Operation: | write | Name: | NodeSlot |
Value: 17 | |||
| (PID) Process: | (3936) 64bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\1\1\0 |
| Operation: | write | Name: | 0 |
Value: 5C00310000000000095532681000494E5354414C7E310000440008000400EFBE09553268095532682A0000007A38010000000100000000000000000000000000000049006E007300740061006C006C005200690074006500000018000000 | |||
Executable files
2
Suspicious files
22
Text files
99
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\idm-crack-patch[1].htm | html | |
MD5:— | SHA256:— | |||
| 3252 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\Z4YMY1YA.htm | html | |
MD5:— | SHA256:— | |||
| 3936 | 64bit Patch.exe | C:\Users\admin\AppData\Local\Temp\$inst\7.tmp | image | |
MD5:696641D2325E8B142B6C16D1183ACA43 | SHA256:4A56FFCE0E414F3495F70E9C2960837DF25423B0DBAFD21A073DBDBAA461BC90 | |||
| 3936 | 64bit Patch.exe | C:\Users\admin\AppData\Local\Temp\$inst\15.tmp | text | |
MD5:E5BD9C79F9BB62C0C26D384AFF92BAD2 | SHA256:DB021752781BE4F224D63DE745B577894E9195B02E21A796C35E72BC3557B565 | |||
| 3936 | 64bit Patch.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | compressed | |
MD5:E4CBA70146928D1476A60CAF7A361C45 | SHA256:3A43C24ED0AE4E7365BBA0ADB34E094AB1A1497851B2B10A92961AAD68BB3C6B | |||
| 3936 | 64bit Patch.exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:A293A3FEA114FE9997E9751498E14F80 | SHA256:297344B5EB9BCB4D91760A1BBC48BAE931F782B5211372637A30D6A50F3EA7AC | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\core_style[1].css | text | |
MD5:696080BA6A81A1D37F84D5152EE76307 | SHA256:37AC4091AD3744E2ED138B10D93C971D049C5B8D9E94295B2838EC3E14F79DD2 | |||
| 3936 | 64bit Patch.exe | C:\Program Files\Internet Download Manager\IDMan.exe | executable | |
MD5:2DED289D3F443D6E03B12B7E43540415 | SHA256:D1312373EF775F7C926053B16575A4F3CA3DB795196050E8BC0D886D92B447CE | |||
| 3936 | 64bit Patch.exe | C:\Users\admin\AppData\Local\Temp\$inst\4.tmp | image | |
MD5:4E2B23C37BFF1C3C3E576B48AD6C55FD | SHA256:A72C22F7FB22DEB0153C64EAF1F60E9FB41A426DBBA91CD383C77B3C592722DB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
96
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3276 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3252 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3276 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAeReQ3heodN5gA88rOQrYY%3D | US | der | 471 b | whitelisted |
3276 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3252 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3252 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3252 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3252 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 1.42 Kb | whitelisted |
3252 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDcThR%2BKEYP2BK026EbsM6F | US | der | 472 b | whitelisted |
3252 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 2.18 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3276 | iexplore.exe | 188.114.97.3:443 | crackingpatching.com | CLOUDFLARENET | NL | malicious |
3252 | iexplore.exe | 188.114.97.3:443 | crackingpatching.com | CLOUDFLARENET | NL | malicious |
3276 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3276 | iexplore.exe | 192.0.77.37:443 | c0.wp.com | AUTOMATTIC | US | suspicious |
3252 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3252 | iexplore.exe | 192.0.77.37:443 | c0.wp.com | AUTOMATTIC | US | suspicious |
3252 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3276 | iexplore.exe | 142.250.185.162:443 | pagead2.googlesyndication.com | GOOGLE | US | whitelisted |
3252 | iexplore.exe | 192.0.77.2:443 | i0.wp.com | AUTOMATTIC | US | suspicious |
3252 | iexplore.exe | 192.0.76.3:443 | stats.wp.com | AUTOMATTIC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crackingpatching.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
c0.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
i0.wp.com |
| whitelisted |
apis.google.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
platform.twitter.com |
| whitelisted |