| URL: | http://carolscloud.com/media/public/ |
| Full analysis: | https://app.any.run/tasks/176494f4-078a-4f87-b69b-c066a6d6e39a |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 16:27:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F6D6CDCBBBB3BC426938C687E194DBF2 |
| SHA1: | 9BDF3C7223676F01BDF7E651EAF0A380B4FE9176 |
| SHA256: | 4BF2712C945CDBD36B9C4F3991E6D9190DE45FD42CAD0FE27A3898E31070388B |
| SSDEEP: | 3:N1KdEaJWVQDAj6Q:CGaJCQDAjP |
MALICIOUS
Drops known malicious document
- WINWORD.EXE (PID: 3732)
- firefox.exe (PID: 1740)
Application was dropped or rewritten from another process
- 535.exe (PID: 2864)
- 535.exe (PID: 3796)
- serialfunc.exe (PID: 3816)
- serialfunc.exe (PID: 3384)
Emotet process was detected
- 535.exe (PID: 2864)
Changes the autorun value in the registry
- serialfunc.exe (PID: 3384)
Connects to CnC server
- serialfunc.exe (PID: 3384)
EMOTET was detected
- serialfunc.exe (PID: 3384)
SUSPICIOUS
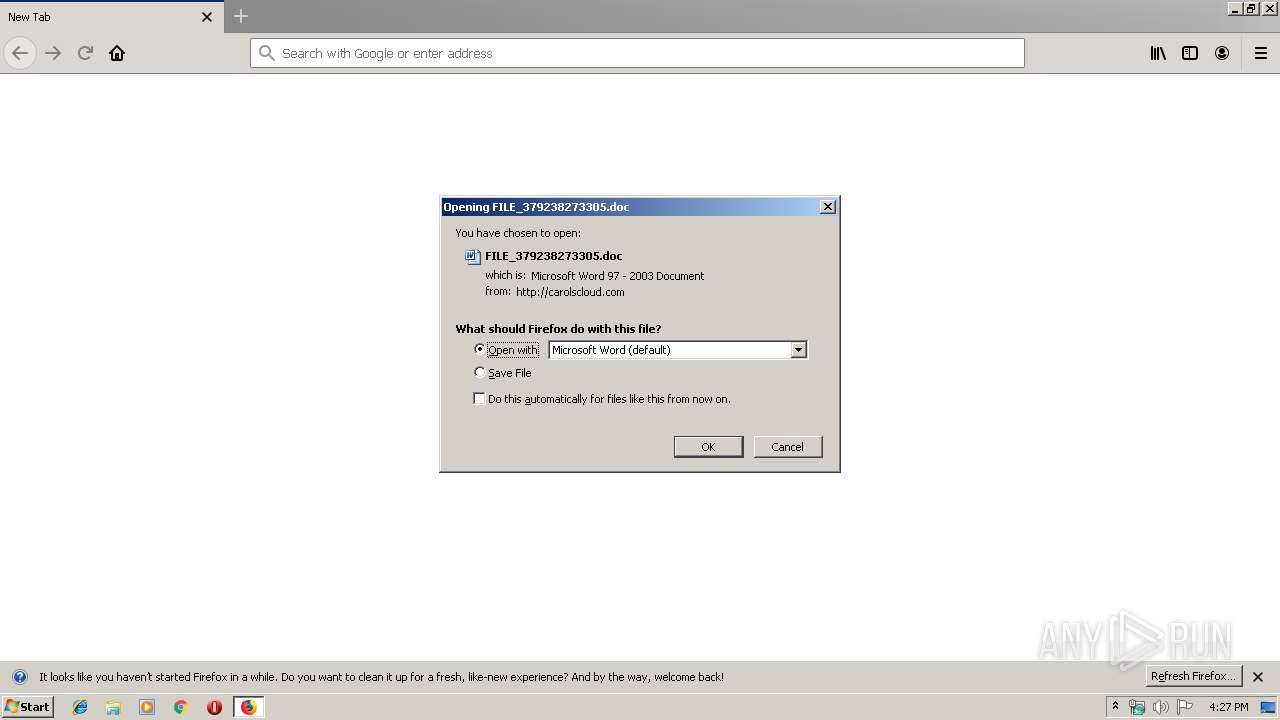
Starts Microsoft Office Application
- firefox.exe (PID: 1740)
- WINWORD.EXE (PID: 3732)
Creates files in the program directory
- firefox.exe (PID: 1740)
Executed via WMI
- powershell.exe (PID: 3876)
PowerShell script executed
- powershell.exe (PID: 3876)
Executable content was dropped or overwritten
- powershell.exe (PID: 3876)
- 535.exe (PID: 2864)
Application launched itself
- WINWORD.EXE (PID: 3732)
- 535.exe (PID: 3796)
Creates files in the user directory
- powershell.exe (PID: 3876)
Connects to server without host name
- serialfunc.exe (PID: 3384)
Starts itself from another location
- 535.exe (PID: 2864)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3732)
- WINWORD.EXE (PID: 3324)
Application launched itself
- firefox.exe (PID: 1740)
Creates files in the user directory
- firefox.exe (PID: 1740)
- WINWORD.EXE (PID: 3732)
Reads CPU info
- firefox.exe (PID: 1740)
Dropped object may contain Bitcoin addresses
- powershell.exe (PID: 3876)
- 535.exe (PID: 2864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
13
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1740.3.1313555930\489307633" -childID 1 -isForBrowser -prefsHandle 1704 -prefMapHandle 1700 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1740 "\\.\pipe\gecko-crash-server-pipe.1740" 1724 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://carolscloud.com/media/public/ | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1956 | "C:\Program Files\Mozilla Firefox\firefox.exe" "http://carolscloud.com/media/public/" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1740.20.1472383201\202573824" -childID 3 -isForBrowser -prefsHandle 3632 -prefMapHandle 3652 -prefsLen 7129 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1740 "\\.\pipe\gecko-crash-server-pipe.1740" 3688 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2864 | --6e6396f5 | C:\Users\admin\535.exe | 535.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3140 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1740.13.1389795052\815133544" -childID 2 -isForBrowser -prefsHandle 2876 -prefMapHandle 2880 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1740 "\\.\pipe\gecko-crash-server-pipe.1740" 2892 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1740.0.43858104\646726711" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1740 "\\.\pipe\gecko-crash-server-pipe.1740" 1164 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3324 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3384 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3732 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\FILE_379238273305.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | firefox.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 496
Read events
2 607
Write events
730
Delete events
159
Modification events
| (PID) Process: | (1740) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 9E05FF1703000000 | |||
| (PID) Process: | (1956) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: B30AFB1703000000 | |||
| (PID) Process: | (1740) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (1740) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1740) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1740) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1740) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1740) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.doc\OpenWithProgids |
| Operation: | write | Name: | Word.Document.8 |
Value: | |||
| (PID) Process: | (3732) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | #-i |
Value: 232D6900940E0000010000000000000000000000 | |||
| (PID) Process: | (3732) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
Executable files
2
Suspicious files
77
Text files
25
Unknown types
58
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1740 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1740 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 1740 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 1740 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 1740 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 1740 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1740 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1740 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1740 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 1740 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json | text | |
MD5:C4AB2EE59CA41B6D6A6EA911F35BDC00 | SHA256:00AD9799527C3FD21F3A85012565EAE817490F3E0D417413BF9567BB5909F6A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
29
DNS requests
71
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1740 | firefox.exe | POST | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1740 | firefox.exe | GET | 200 | 69.89.31.207:80 | http://carolscloud.com/media/public/ | US | document | 194 Kb | unknown |
1740 | firefox.exe | POST | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
1740 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
3384 | serialfunc.exe | POST | 200 | 107.2.2.28:80 | http://107.2.2.28/WNRwobS0xPY7H | US | binary | 132 b | malicious |
1740 | firefox.exe | POST | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1740 | firefox.exe | POST | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3876 | powershell.exe | GET | 200 | 104.28.31.186:80 | http://air-o-trip.com/wp-admin/NG2/ | US | html | 3.97 Kb | unknown |
1740 | firefox.exe | POST | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
1740 | firefox.exe | POST | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1740 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
1740 | firefox.exe | 52.41.39.5:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
1740 | firefox.exe | 54.240.168.103:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
1740 | firefox.exe | 52.33.184.165:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1740 | firefox.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1740 | firefox.exe | 172.217.21.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1740 | firefox.exe | 172.217.18.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1740 | firefox.exe | 13.225.78.71:443 | firefox.settings.services.mozilla.com | — | US | malicious |
1740 | firefox.exe | 172.217.23.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1740 | firefox.exe | 35.155.241.126:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
carolscloud.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1740 | firefox.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3384 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 2 |
3384 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3384 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3384 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |