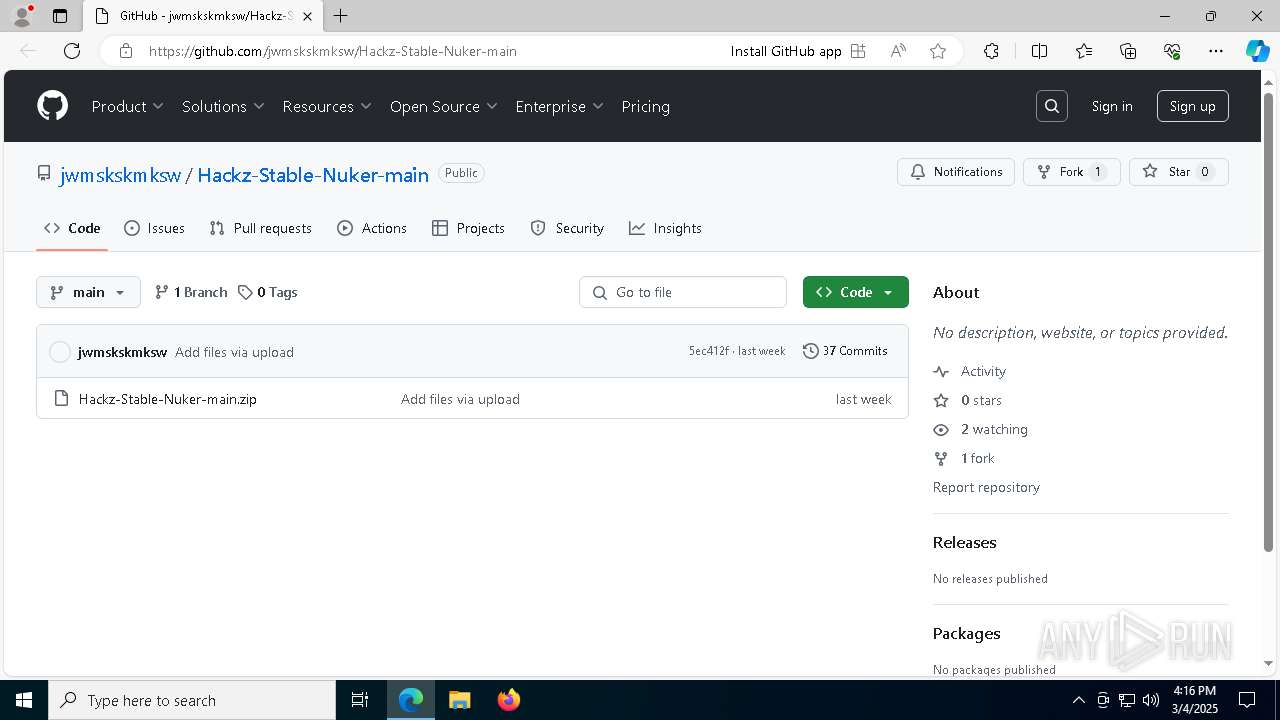
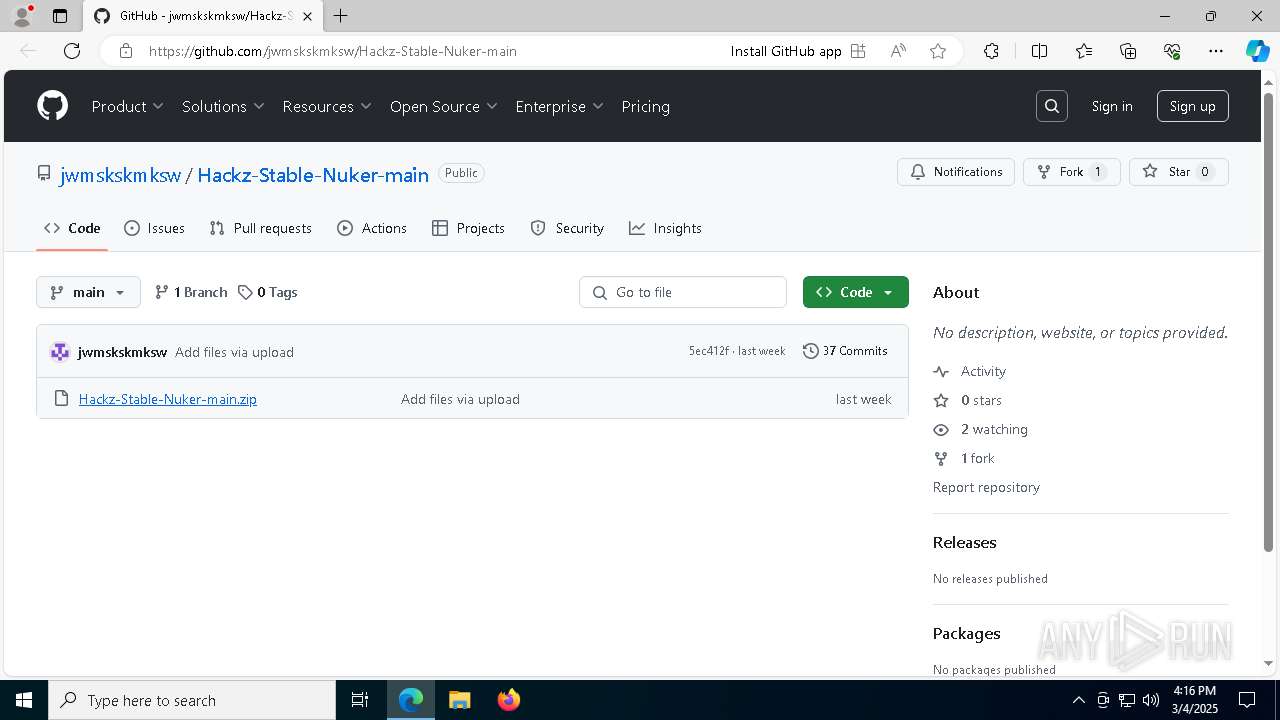
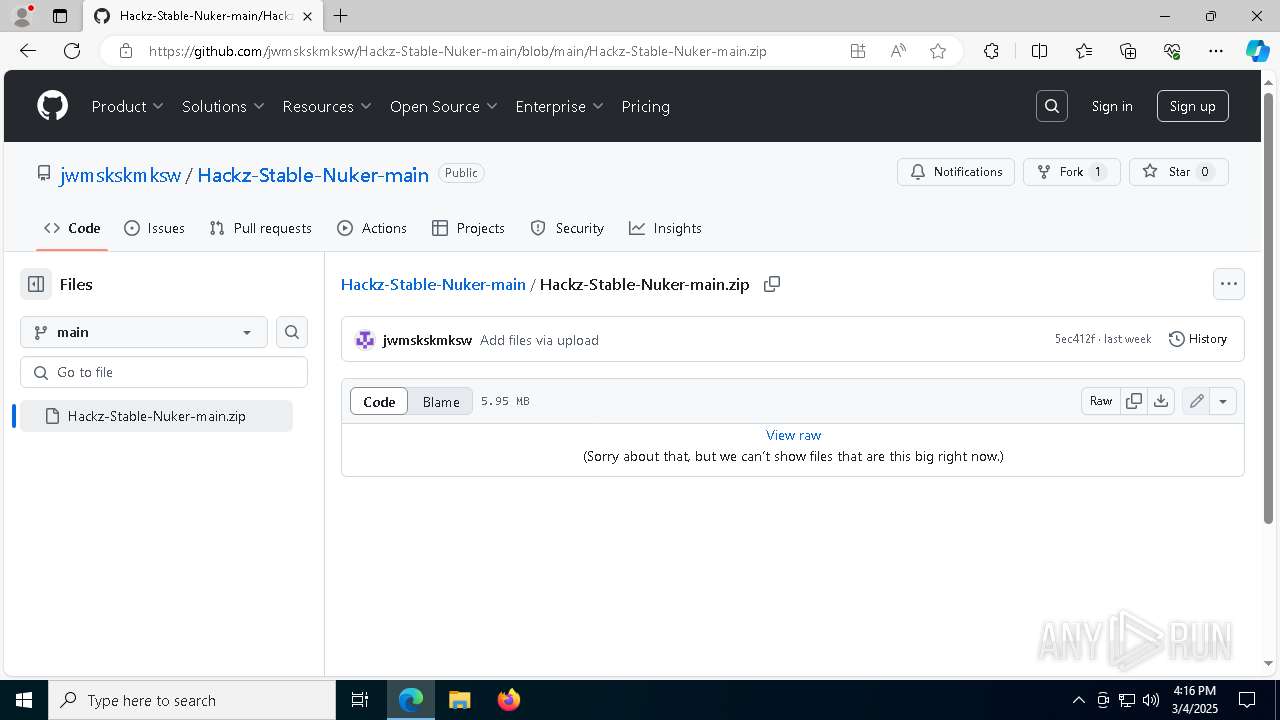
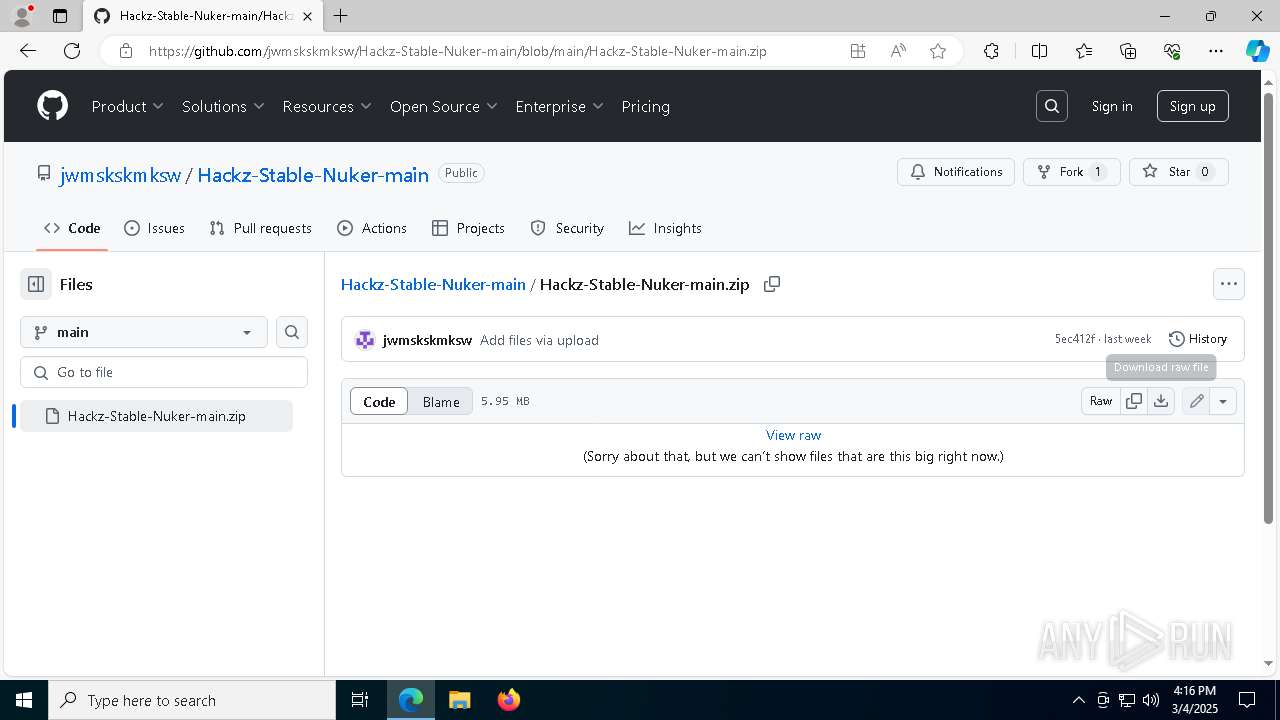
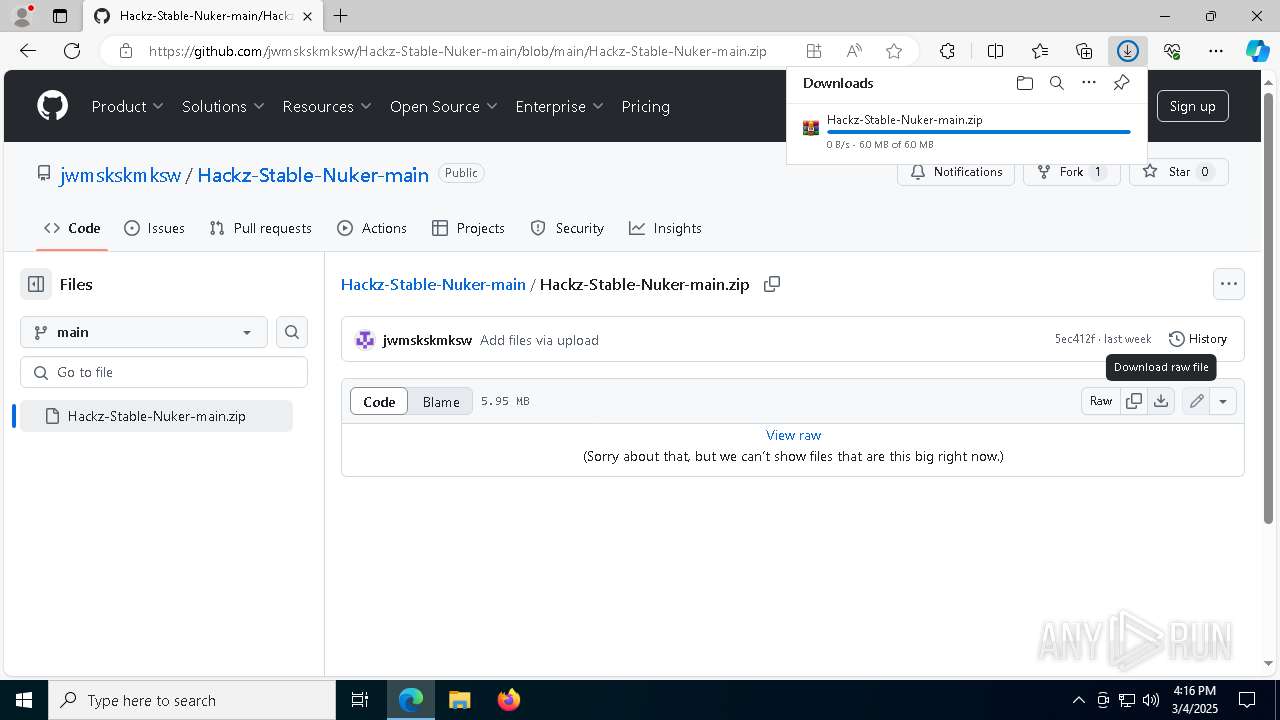
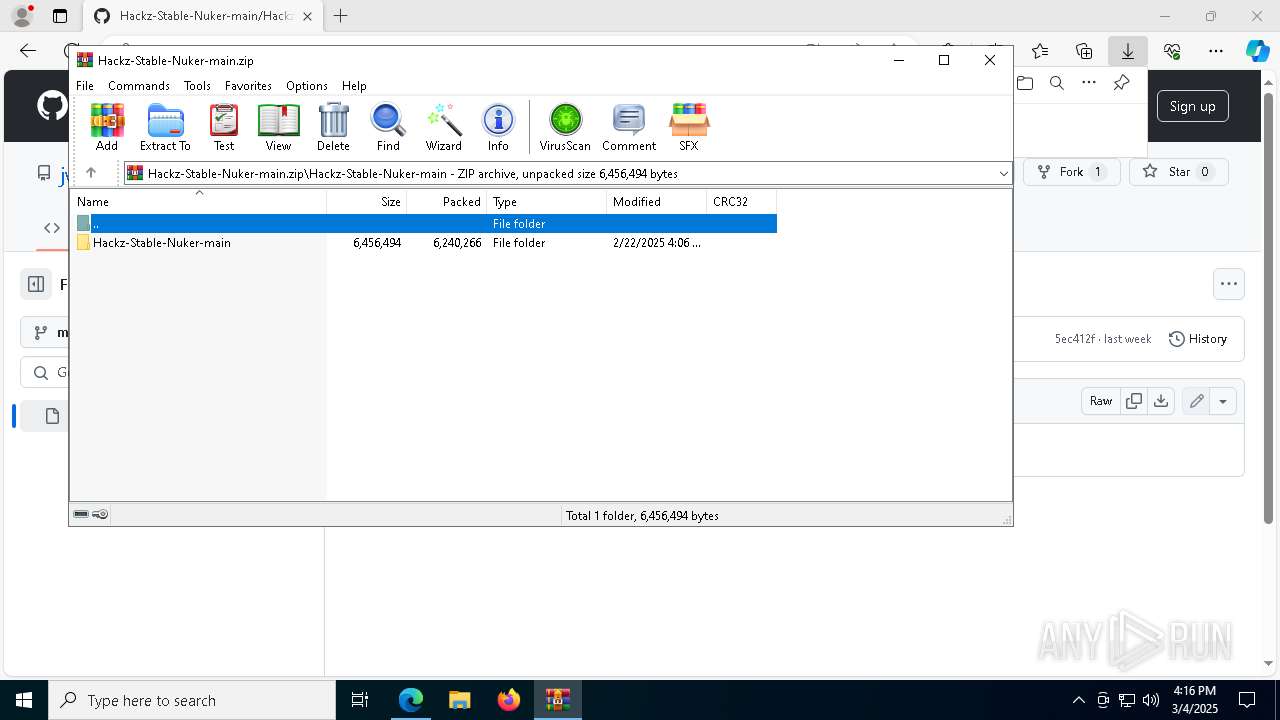
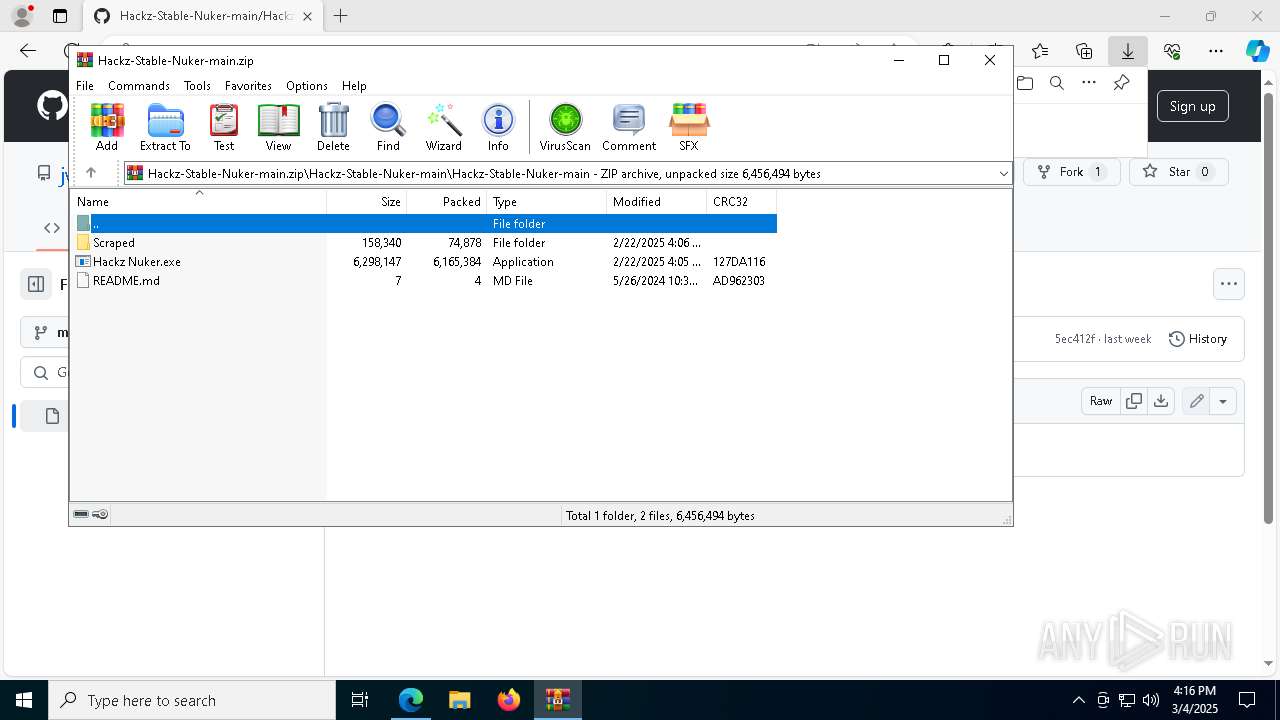
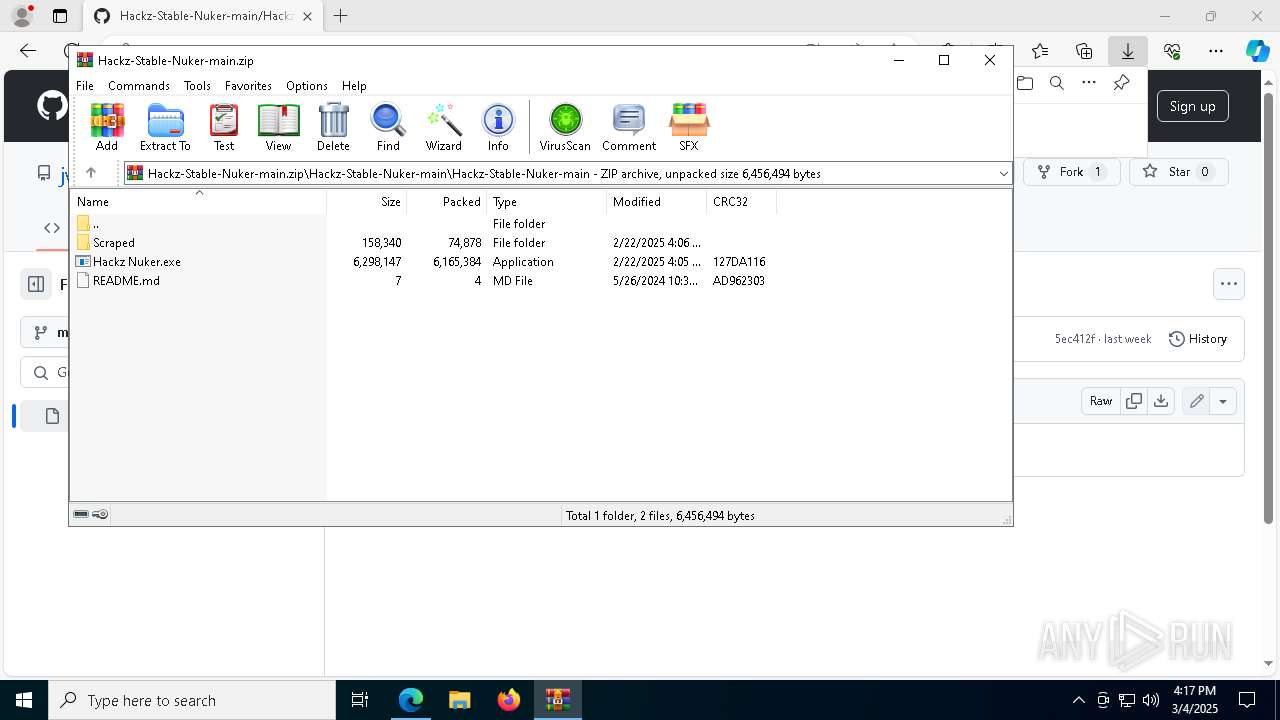
| URL: | https://github.com/jwmskskmksw/Hackz-Stable-Nuker-main |
| Full analysis: | https://app.any.run/tasks/37d3cfd7-794a-4d52-a237-1d3970ec9711 |
| Verdict: | Malicious activity |
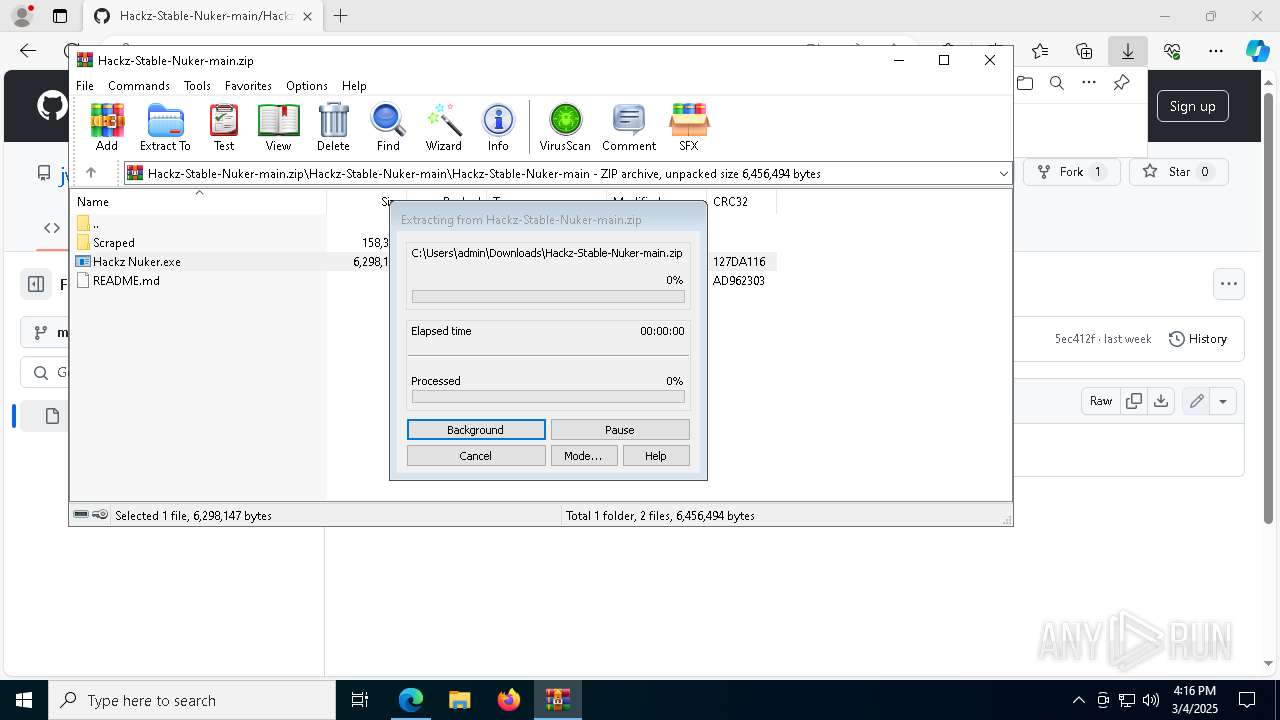
| Analysis date: | March 04, 2025, 16:16:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 33AA6B46DF66C2D7899DEE39383800F6 |
| SHA1: | D5FEBE28CB51CC864174C11E323A90C0C920600E |
| SHA256: | 4BED59DAD7B1EE7AE33F9E93681074C1D1D56C3160A861D7CB959542B329F9AC |
| SSDEEP: | 3:N8tEd/7WJtl2krQOAXI5Kn:2uojZAXOK |
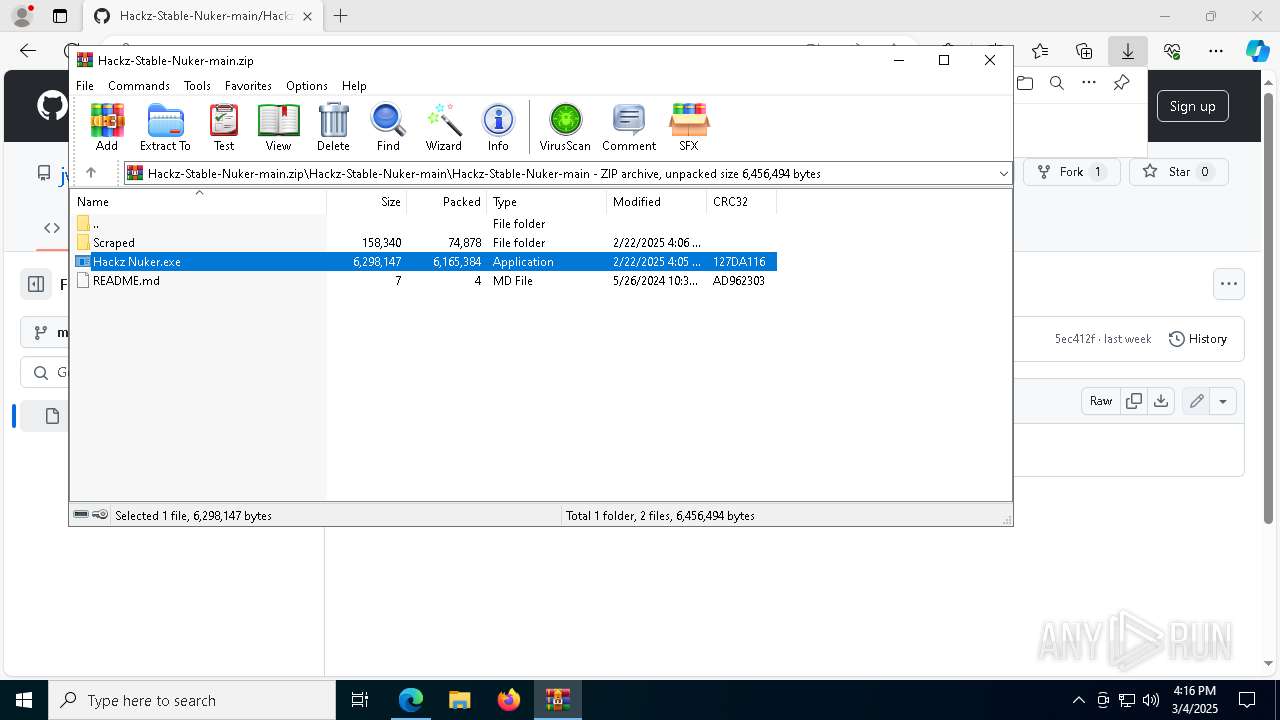
MALICIOUS
Executing a file with an untrusted certificate
- Hackz Nuker.exe (PID: 2240)
- Hackz Nuker.exe (PID: 7932)
- Hackz Nuker.exe (PID: 6112)
- Hackz Nuker.exe (PID: 1272)
Adds path to the Windows Defender exclusion list
- Hackz Nuker.exe (PID: 6112)
- cmd.exe (PID: 4024)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 8056)
Changes settings for real-time protection
- powershell.exe (PID: 6244)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 6244)
Changes Controlled Folder Access settings
- powershell.exe (PID: 6244)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 6244)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 6244)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 6244)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 8464)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 6244)
SUSPICIOUS
The process drops C-runtime libraries
- Hackz Nuker.exe (PID: 2240)
- Hackz Nuker.exe (PID: 1272)
Process drops legitimate windows executable
- msedge.exe (PID: 2284)
- msedge.exe (PID: 7492)
- WinRAR.exe (PID: 4300)
- Hackz Nuker.exe (PID: 2240)
- Hackz Nuker.exe (PID: 1272)
Starts a Microsoft application from unusual location
- Hackz Nuker.exe (PID: 2240)
- Hackz Nuker.exe (PID: 7932)
- Hackz Nuker.exe (PID: 1272)
- Hackz Nuker.exe (PID: 6112)
Process drops python dynamic module
- Hackz Nuker.exe (PID: 2240)
- Hackz Nuker.exe (PID: 1272)
Executable content was dropped or overwritten
- Hackz Nuker.exe (PID: 2240)
- Hackz Nuker.exe (PID: 1272)
Application launched itself
- Hackz Nuker.exe (PID: 7932)
- Hackz Nuker.exe (PID: 1272)
- Hackz Nuker.exe (PID: 2240)
Get information on the list of running processes
- Hackz Nuker.exe (PID: 6112)
- cmd.exe (PID: 3884)
Found strings related to reading or modifying Windows Defender settings
- Hackz Nuker.exe (PID: 6112)
Starts CMD.EXE for commands execution
- Hackz Nuker.exe (PID: 6112)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4024)
- cmd.exe (PID: 8056)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 8056)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 4024)
Script disables Windows Defender's IPS
- cmd.exe (PID: 8056)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 2040)
Checks for external IP
- svchost.exe (PID: 2196)
- Hackz Nuker.exe (PID: 6112)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 3140)
INFO
Checks supported languages
- identity_helper.exe (PID: 7748)
Application launched itself
- msedge.exe (PID: 2284)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 3884)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 3884)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 3884)
- BackgroundTransferHost.exe (PID: 3676)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 3884)
The sample compiled with english language support
- msedge.exe (PID: 2284)
- Hackz Nuker.exe (PID: 2240)
- msedge.exe (PID: 7492)
- WinRAR.exe (PID: 4300)
- Hackz Nuker.exe (PID: 1272)
Executable content was dropped or overwritten
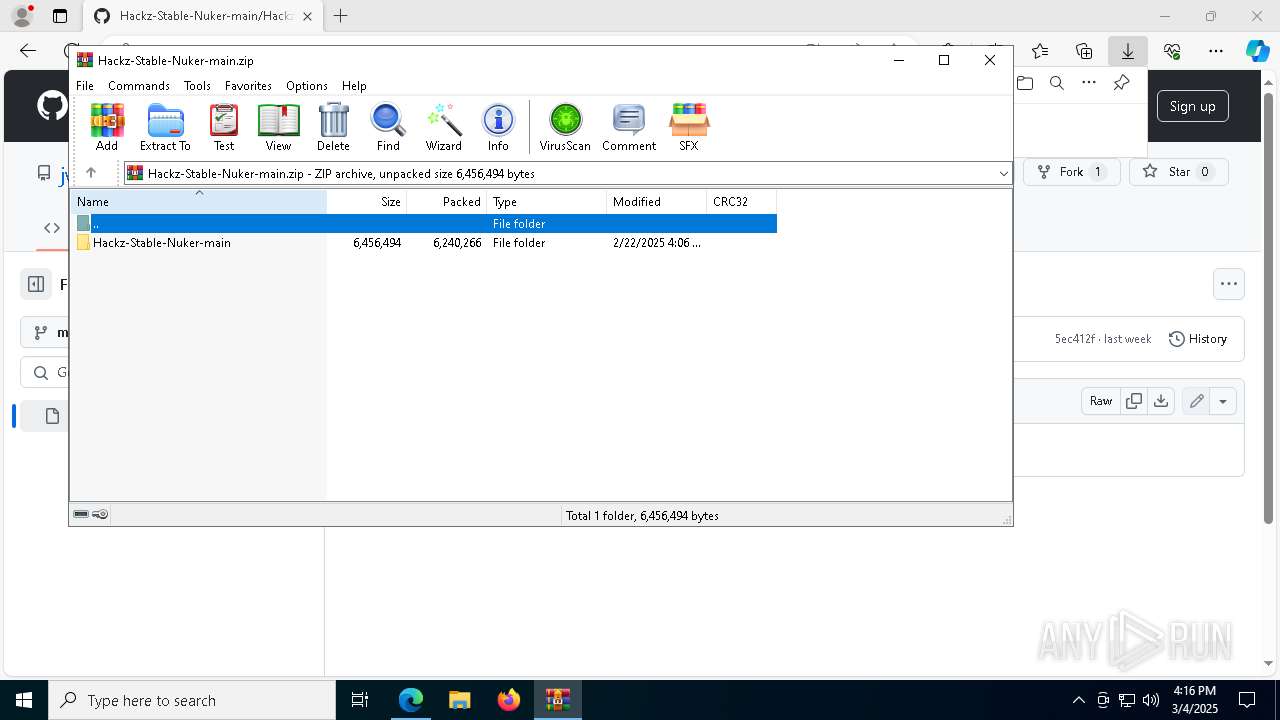
- WinRAR.exe (PID: 4300)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4112)
- powershell.exe (PID: 6244)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4112)
- powershell.exe (PID: 6244)
Reads Environment values
- identity_helper.exe (PID: 7748)
Reads the computer name
- identity_helper.exe (PID: 7748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
209
Monitored processes
68
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5640 --field-trial-handle=2396,i,12556364452700724003,14533088008157511587,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | tasklist /FO LIST | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4300.30968\Hackz-Stable-Nuker-main\Hackz-Stable-Nuker-main\Hackz Nuker.exe" C:\Users\admin\AppData\Local\Temp\Rar$EXa4300.30968\Hackz-Stable-Nuker-main\Hackz-Stable-Nuker-main\Hackz Nuker.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4300.30968\Hackz-Stable-Nuker-main\Hackz-Stable-Nuker-main\Hackz Nuker.exe | Hackz Nuker.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Remote Access Phonebook Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1852 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5224 --field-trial-handle=2396,i,12556364452700724003,14533088008157511587,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2040 | wmic csproduct get uuid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4300.30968\Hackz-Stable-Nuker-main\Hackz-Stable-Nuker-main\Hackz Nuker.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4300.30968\Hackz-Stable-Nuker-main\Hackz-Stable-Nuker-main\Hackz Nuker.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Access Phonebook Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/jwmskskmksw/Hackz-Stable-Nuker-main" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2504 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6444 --field-trial-handle=2396,i,12556364452700724003,14533088008157511587,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
23 195
Read events
23 148
Write events
47
Delete events
0
Modification events
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8F328CE01C8E2F00 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F34195E01C8E2F00 | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9AE14D5D-BDC1-4874-9949-2F99703068AF} | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {31D841EA-35A8-475D-9161-14CBC4163A4E} | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {95E977E9-CE7D-4888-8C86-8560313182B5} | |||
| (PID) Process: | (2284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {53BE1D2A-8FB9-498D-9616-1ACC9A052345} | |||
Executable files
45
Suspicious files
411
Text files
49
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b6de.TMP | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b6ee.TMP | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b6fd.TMP | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b6fd.TMP | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b6ee.TMP | — | |
MD5:— | SHA256:— | |||
| 2284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
78
DNS requests
76
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8000 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3884 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6112 | Hackz Nuker.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
8500 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8500 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8948 | svchost.exe | HEAD | 200 | 84.201.210.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741205673&P2=404&P3=2&P4=hTU5t0DpnZje1xdKl%2bUHJER2ukh4rUTjsRkzIoRNRdjVCYWBqNwjuehd5E6RyHn88Q4Ty9Jjro1l8dqHl41Drg%3d%3d | unknown | — | — | whitelisted |
8948 | svchost.exe | GET | 206 | 84.201.210.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741205673&P2=404&P3=2&P4=hTU5t0DpnZje1xdKl%2bUHJER2ukh4rUTjsRkzIoRNRdjVCYWBqNwjuehd5E6RyHn88Q4Ty9Jjro1l8dqHl41Drg%3d%3d | unknown | — | — | whitelisted |
8948 | svchost.exe | GET | 206 | 84.201.210.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741205673&P2=404&P3=2&P4=hTU5t0DpnZje1xdKl%2bUHJER2ukh4rUTjsRkzIoRNRdjVCYWBqNwjuehd5E6RyHn88Q4Ty9Jjro1l8dqHl41Drg%3d%3d | unknown | — | — | whitelisted |
8948 | svchost.exe | GET | 206 | 84.201.210.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741205673&P2=404&P3=2&P4=hTU5t0DpnZje1xdKl%2bUHJER2ukh4rUTjsRkzIoRNRdjVCYWBqNwjuehd5E6RyHn88Q4Ty9Jjro1l8dqHl41Drg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5544 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7492 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2284 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7492 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
7492 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7492 | msedge.exe | 13.107.253.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7492 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
github.githubassets.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7492 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7492 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6112 | Hackz Nuker.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |