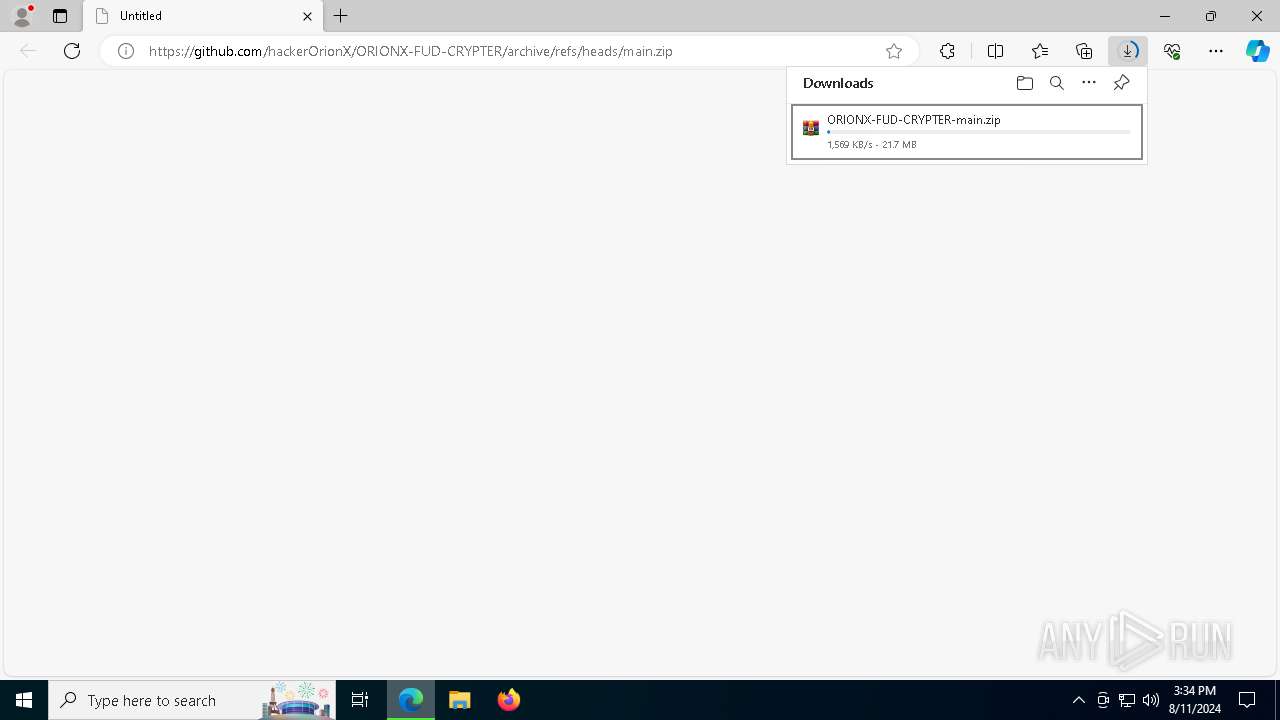
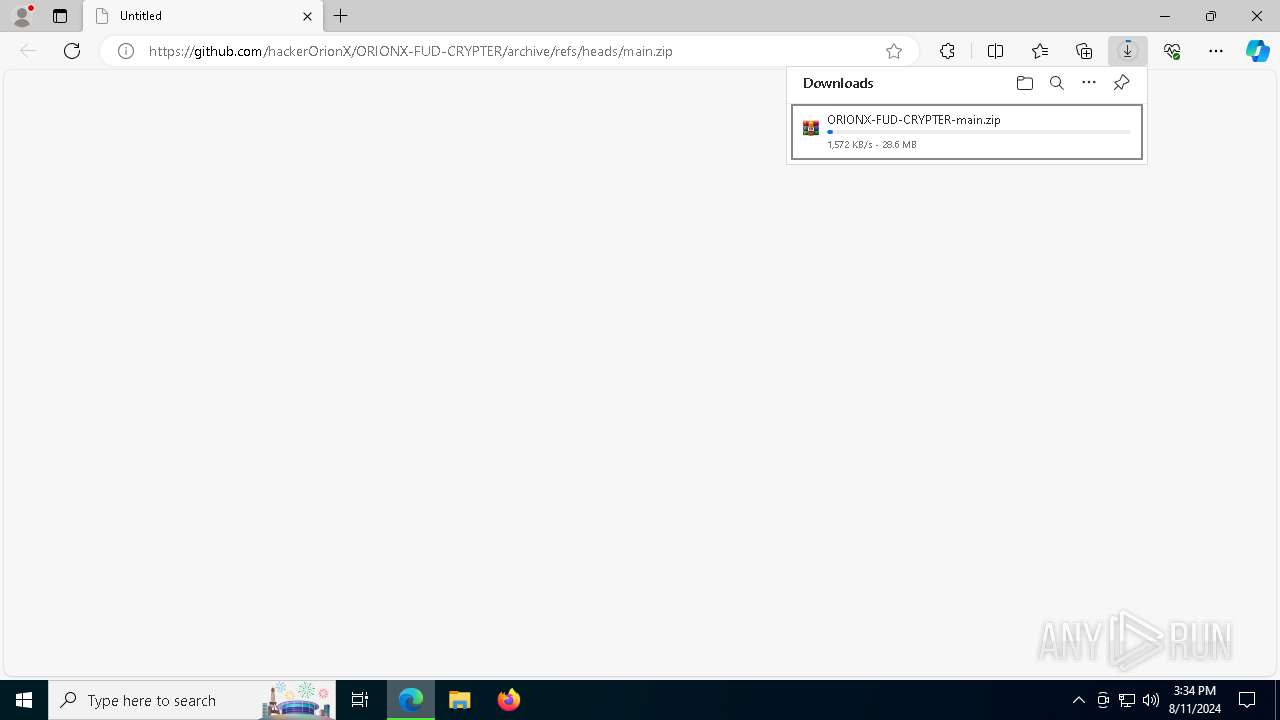
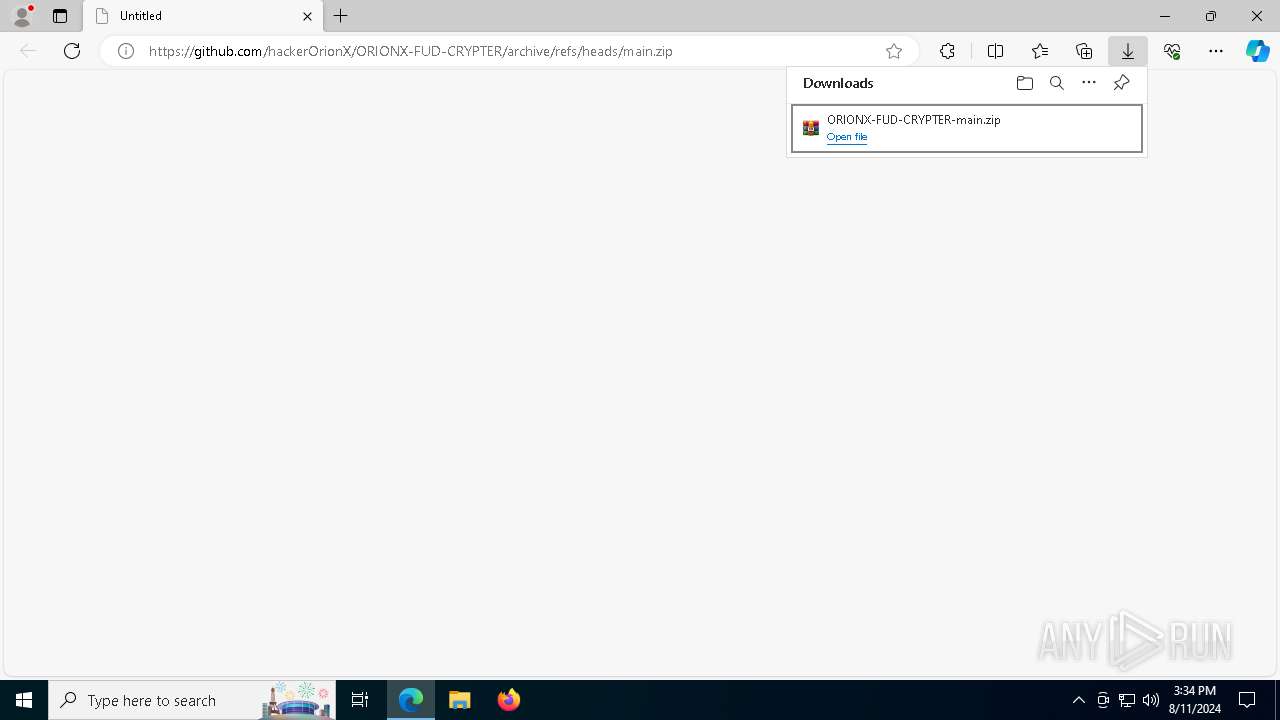
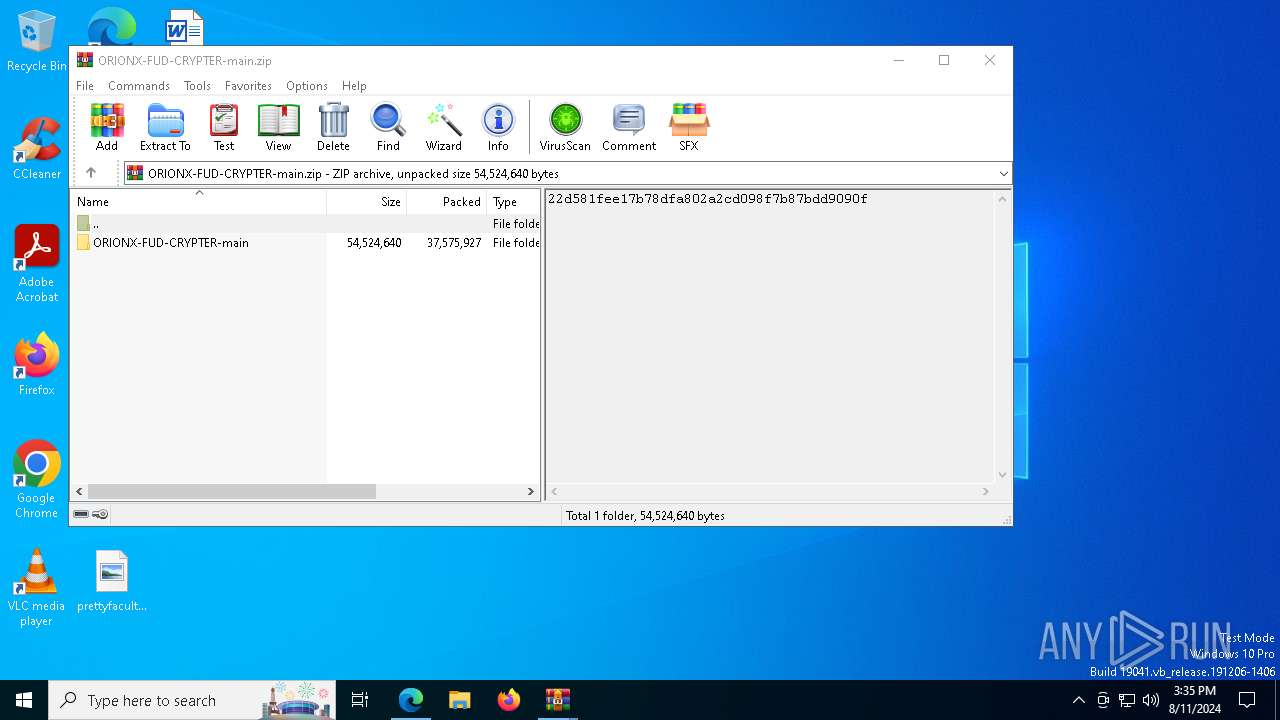
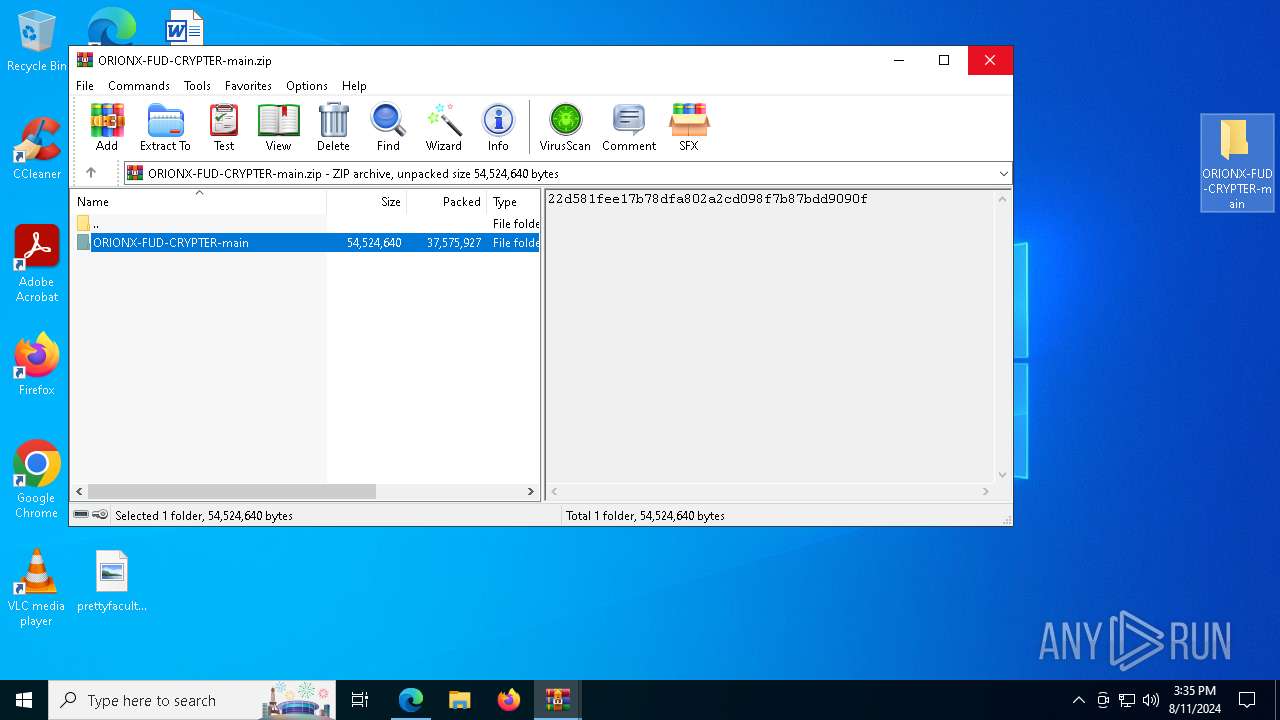
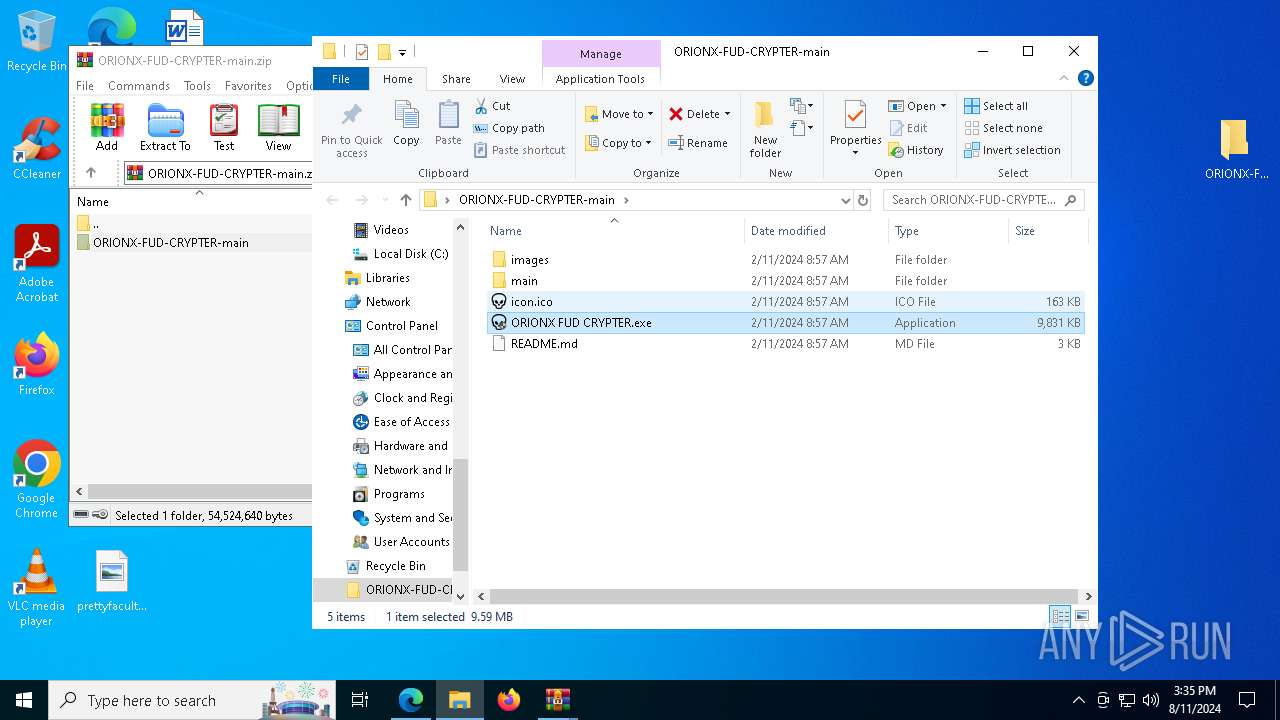
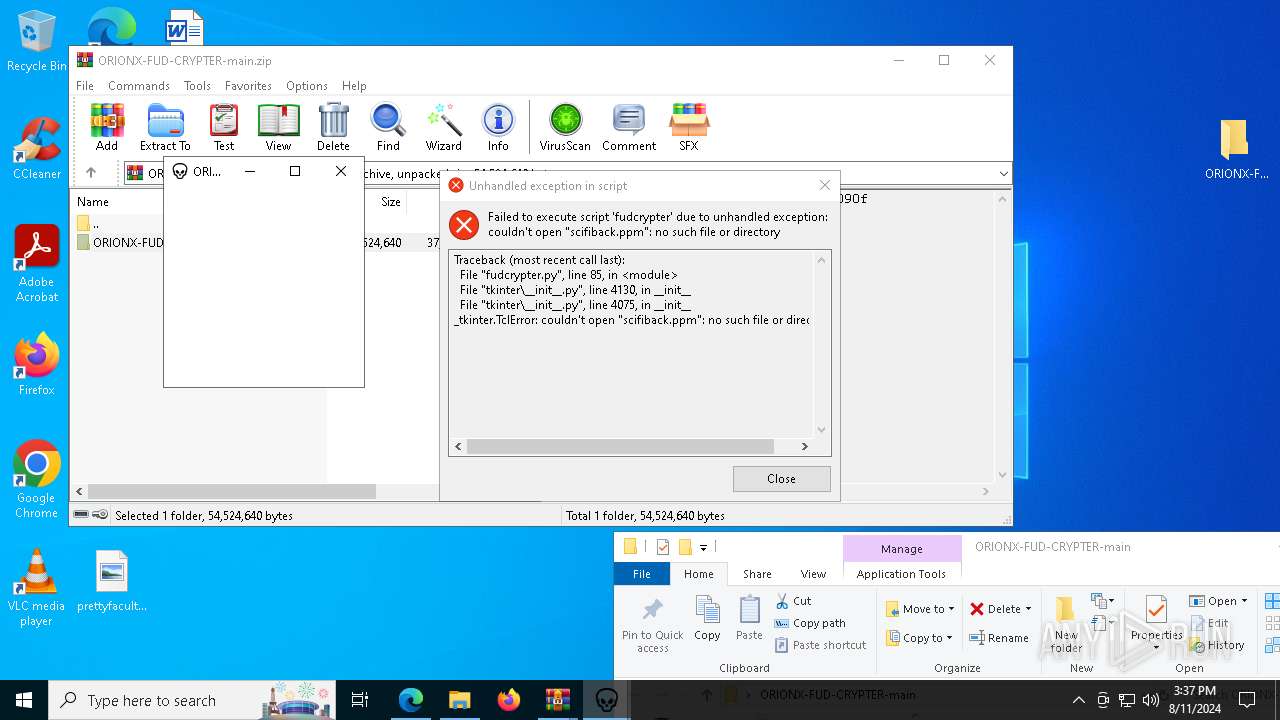
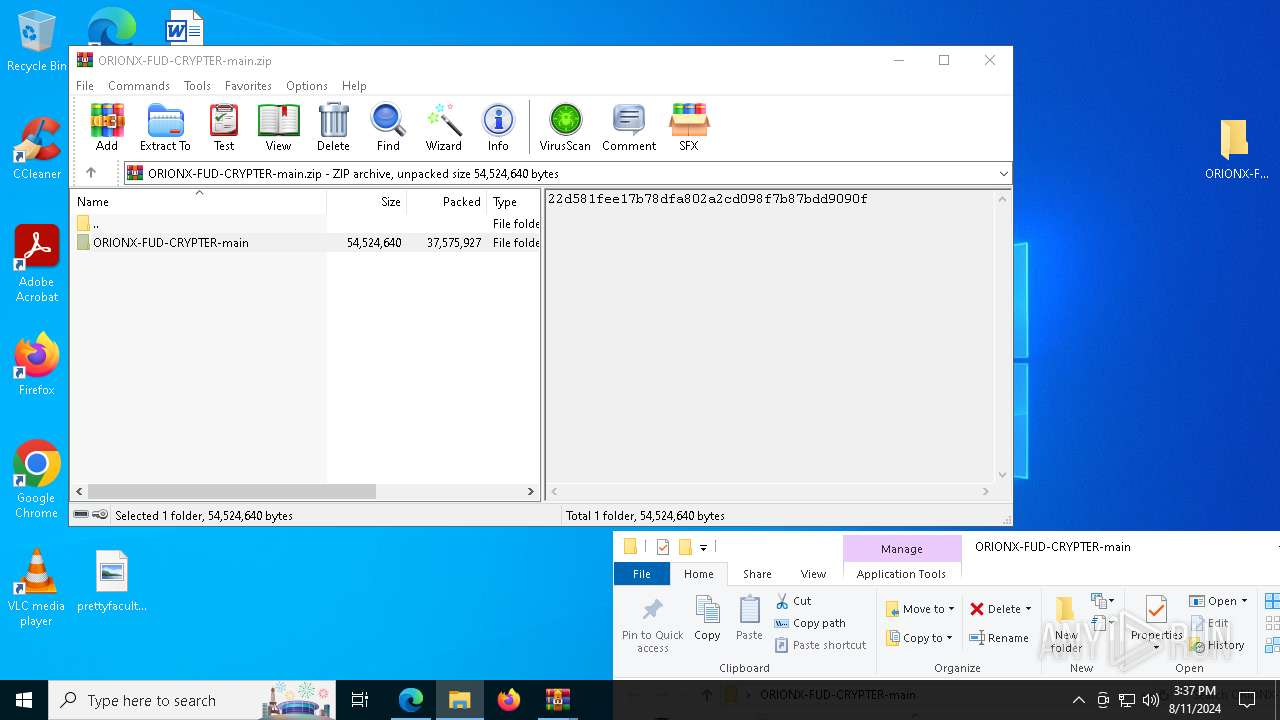
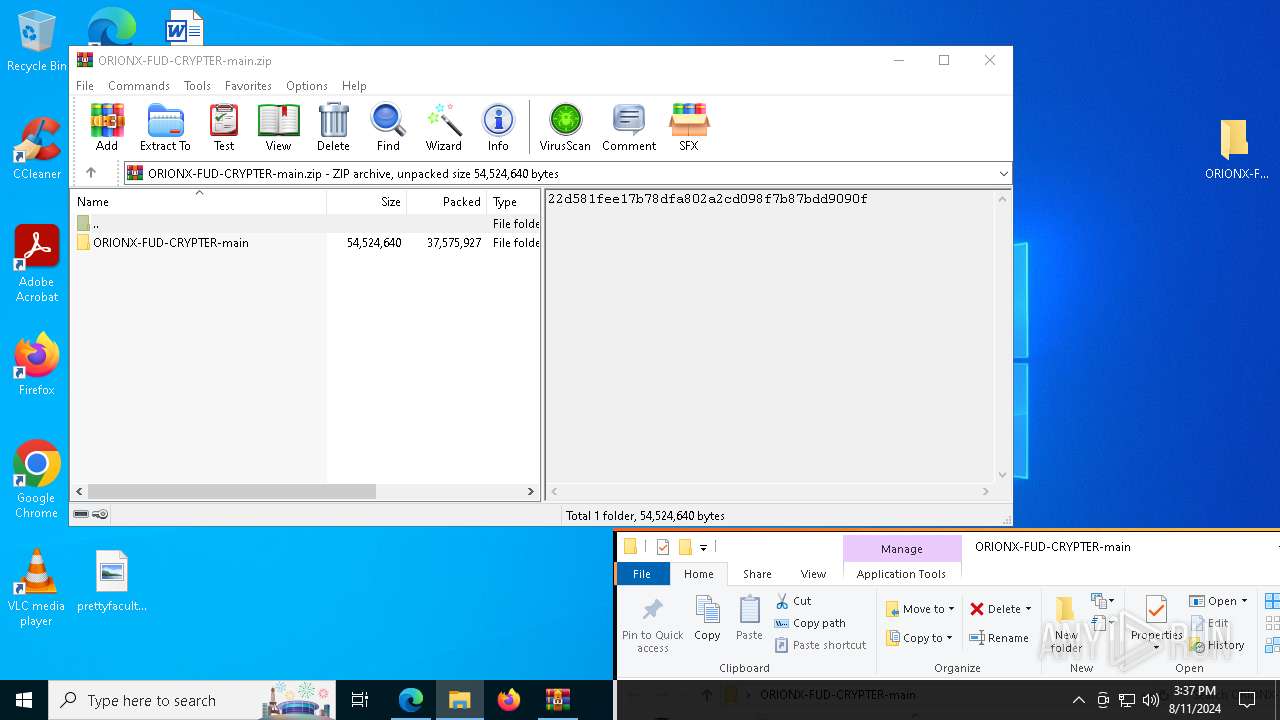
| URL: | https://github.com/hackerOrionX/ORIONX-FUD-CRYPTER/archive/refs/heads/main.zip |
| Full analysis: | https://app.any.run/tasks/86a716bd-1a10-473f-984a-a3d792aaa8ea |
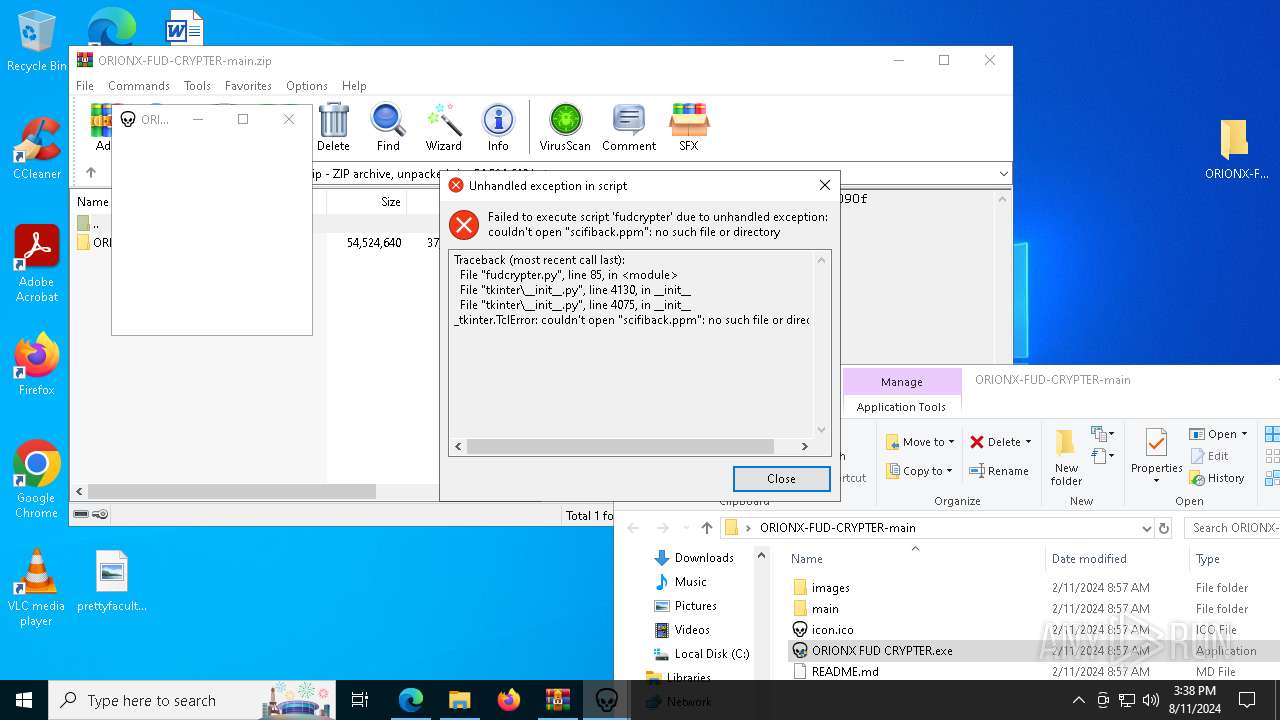
| Verdict: | Malicious activity |
| Analysis date: | August 11, 2024, 15:34:27 |
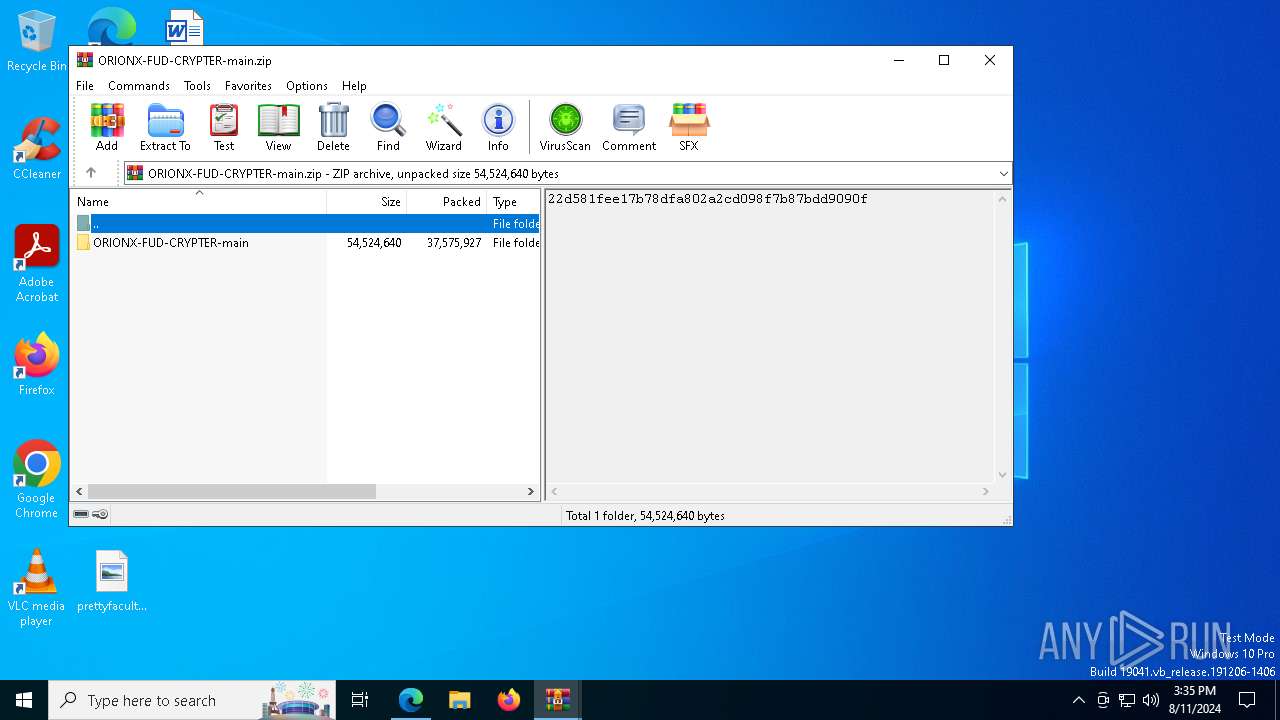
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
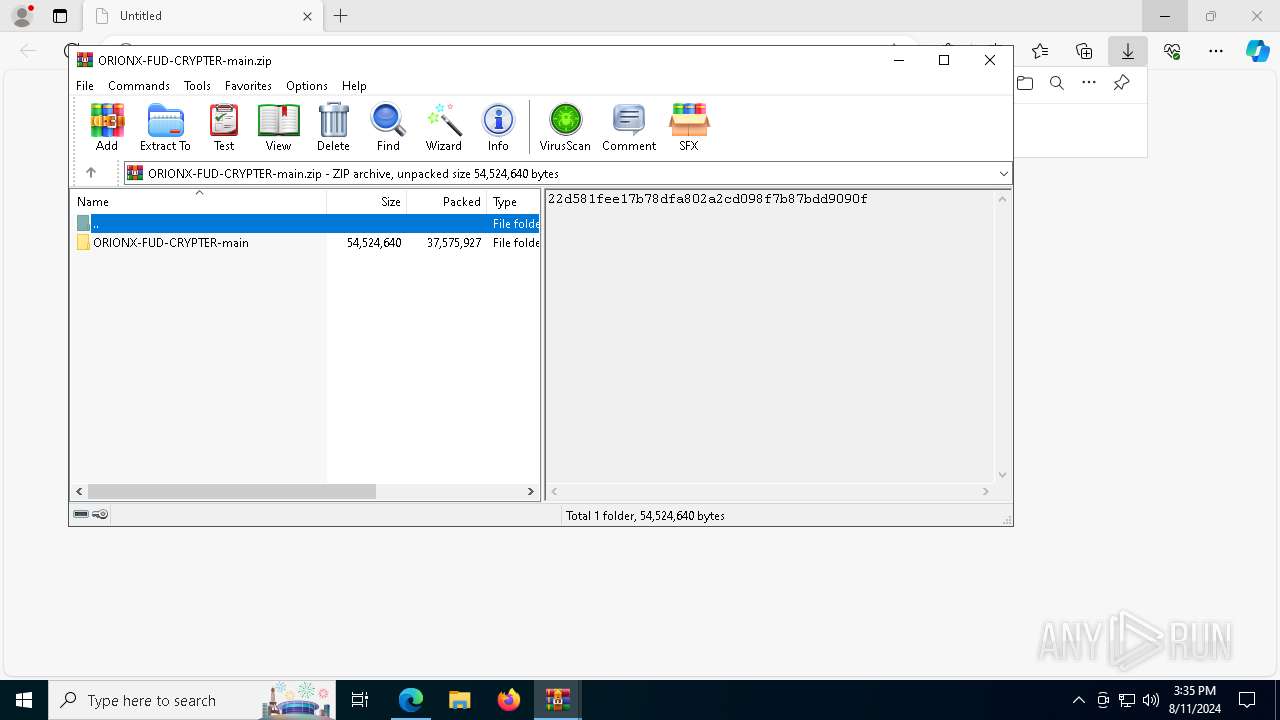
| MD5: | 988AED4B724AB65382860025DDE027E8 |
| SHA1: | 5F6972C5E345F09B06013CEC17786726C20E5564 |
| SHA256: | 4BE7DE115D0D3A03BE20A2B3AB477FB07BE015FDDAD9905587C78A130D72AFE7 |
| SSDEEP: | 3:N8tEd9E3XLL9Kq3sJd24RSLNLc:2uQ3X/3F4ULN4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
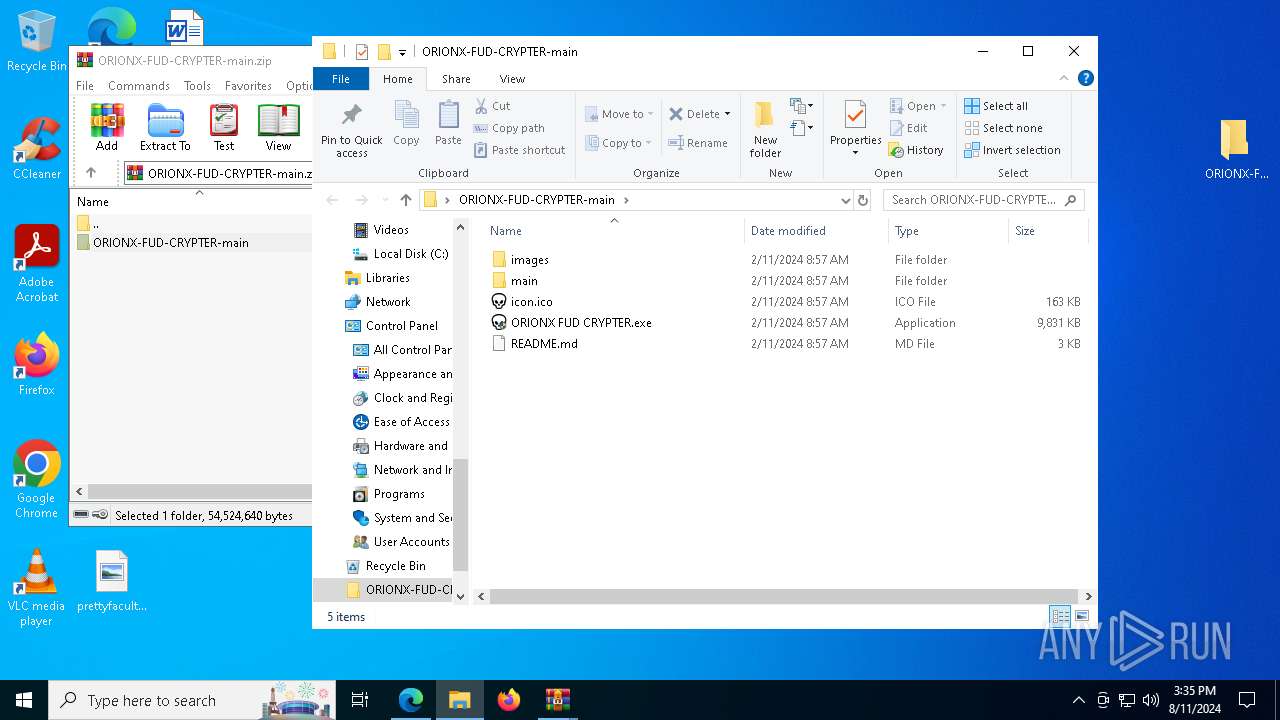
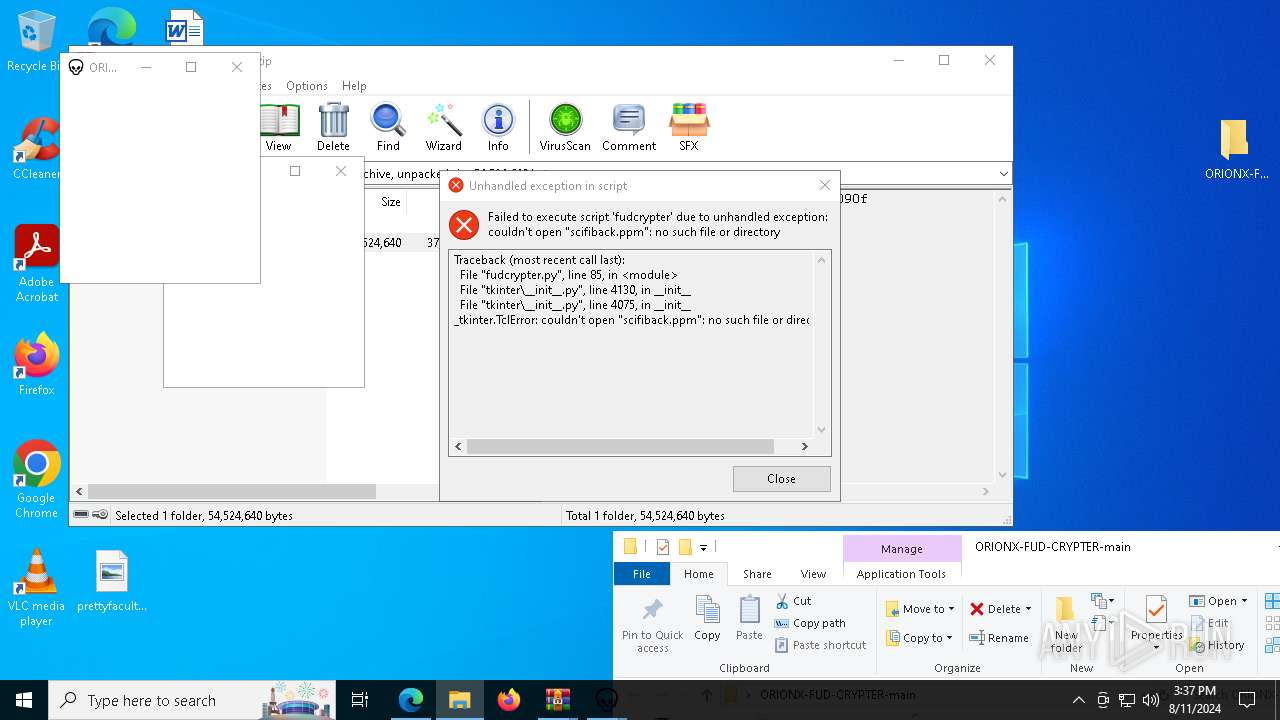
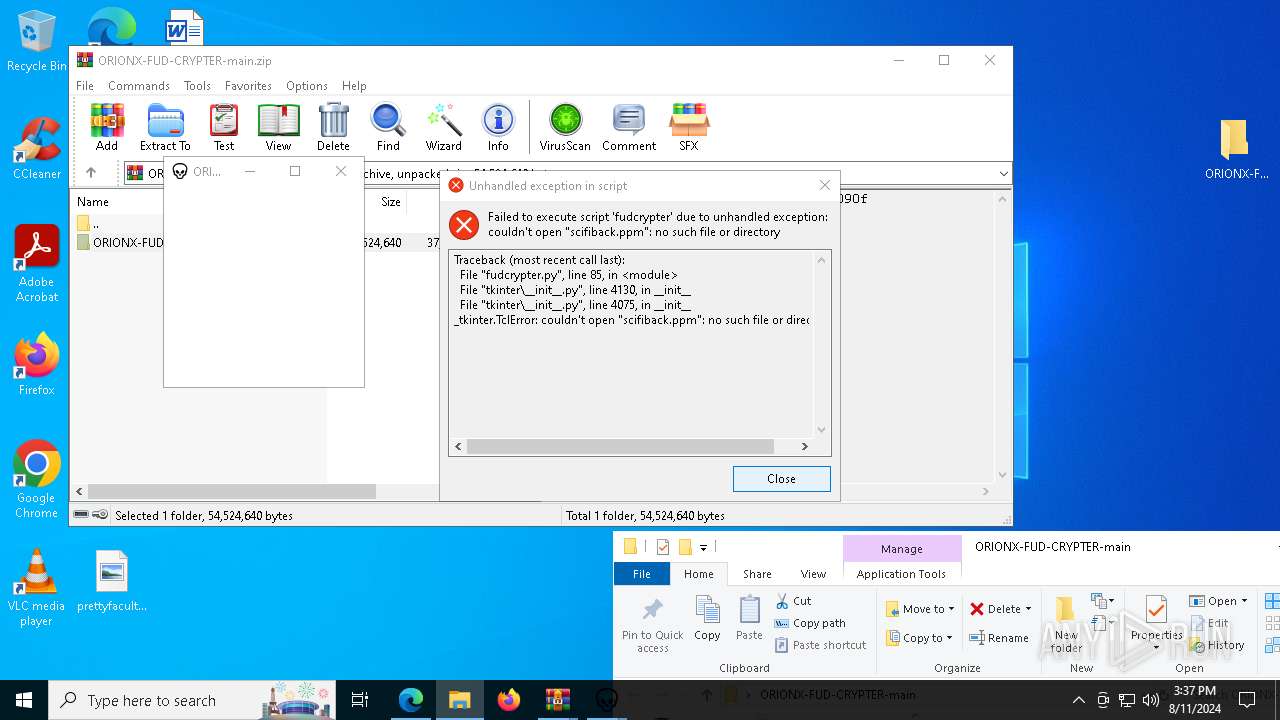
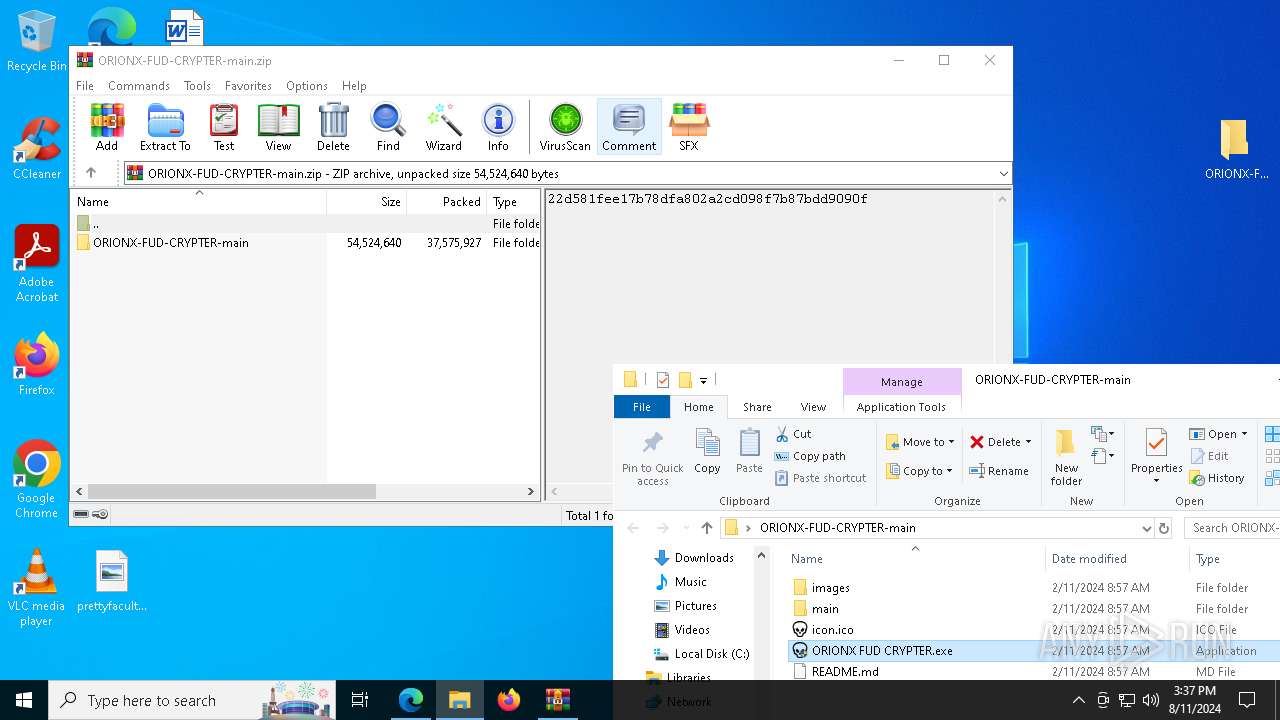
The process creates files with name similar to system file names
- WinRAR.exe (PID: 3916)
Process drops legitimate windows executable
- WinRAR.exe (PID: 3916)
- ORIONX FUD CRYPTER.exe (PID: 7396)
- ORIONX FUD CRYPTER.exe (PID: 4436)
- ORIONX FUD CRYPTER.exe (PID: 6592)
Reads security settings of Internet Explorer
- cookie_exporter.exe (PID: 7592)
Process drops python dynamic module
- WinRAR.exe (PID: 3916)
- ORIONX FUD CRYPTER.exe (PID: 7396)
- ORIONX FUD CRYPTER.exe (PID: 4436)
- ORIONX FUD CRYPTER.exe (PID: 6592)
The process drops C-runtime libraries
- ORIONX FUD CRYPTER.exe (PID: 7396)
- ORIONX FUD CRYPTER.exe (PID: 4436)
- ORIONX FUD CRYPTER.exe (PID: 6592)
Drops the executable file immediately after the start
- ORIONX FUD CRYPTER.exe (PID: 7396)
- ORIONX FUD CRYPTER.exe (PID: 6592)
- ORIONX FUD CRYPTER.exe (PID: 4436)
Executable content was dropped or overwritten
- ORIONX FUD CRYPTER.exe (PID: 7396)
- ORIONX FUD CRYPTER.exe (PID: 4436)
- ORIONX FUD CRYPTER.exe (PID: 6592)
Application launched itself
- ORIONX FUD CRYPTER.exe (PID: 7396)
- ORIONX FUD CRYPTER.exe (PID: 4436)
- ORIONX FUD CRYPTER.exe (PID: 6592)
Loads Python modules
- ORIONX FUD CRYPTER.exe (PID: 1920)
- ORIONX FUD CRYPTER.exe (PID: 2876)
- ORIONX FUD CRYPTER.exe (PID: 6220)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 6440)
Reads the computer name
- identity_helper.exe (PID: 3144)
- cookie_exporter.exe (PID: 7592)
- ORIONX FUD CRYPTER.exe (PID: 7396)
- ORIONX FUD CRYPTER.exe (PID: 1920)
- ORIONX FUD CRYPTER.exe (PID: 4436)
- TextInputHost.exe (PID: 3904)
- ORIONX FUD CRYPTER.exe (PID: 2876)
- ORIONX FUD CRYPTER.exe (PID: 6592)
- ORIONX FUD CRYPTER.exe (PID: 6220)
Application launched itself
- msedge.exe (PID: 6440)
Checks supported languages
- cookie_exporter.exe (PID: 7592)
- ORIONX FUD CRYPTER.exe (PID: 7396)
- identity_helper.exe (PID: 3144)
- ORIONX FUD CRYPTER.exe (PID: 1920)
- ORIONX FUD CRYPTER.exe (PID: 4436)
- ORIONX FUD CRYPTER.exe (PID: 2876)
- TextInputHost.exe (PID: 3904)
- ORIONX FUD CRYPTER.exe (PID: 6592)
- ORIONX FUD CRYPTER.exe (PID: 6220)
The process uses the downloaded file
- msedge.exe (PID: 6440)
- msedge.exe (PID: 5388)
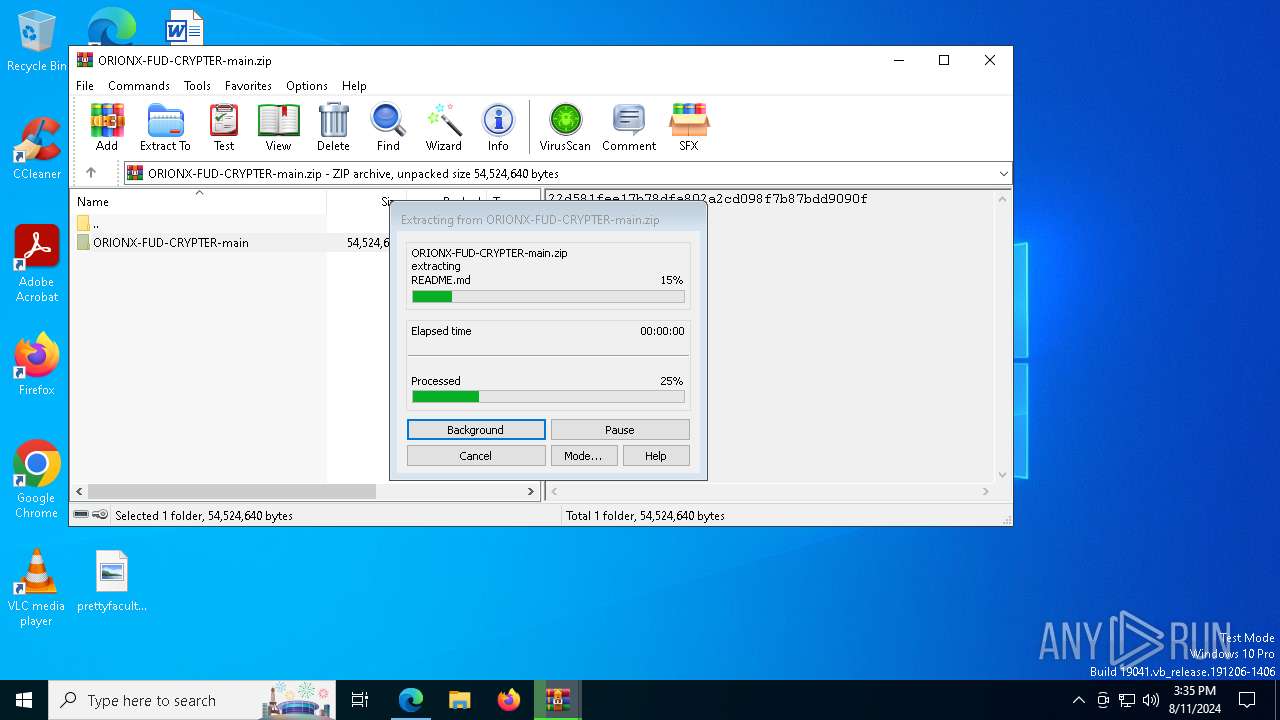
- WinRAR.exe (PID: 3916)
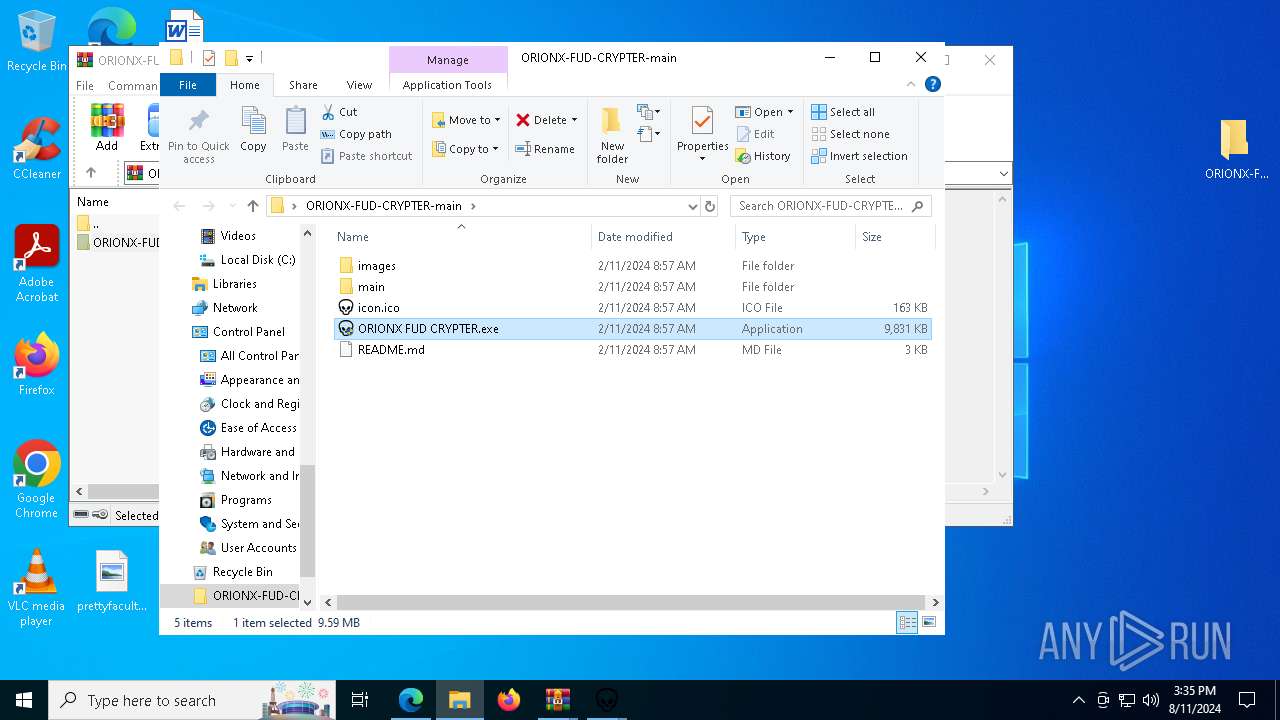
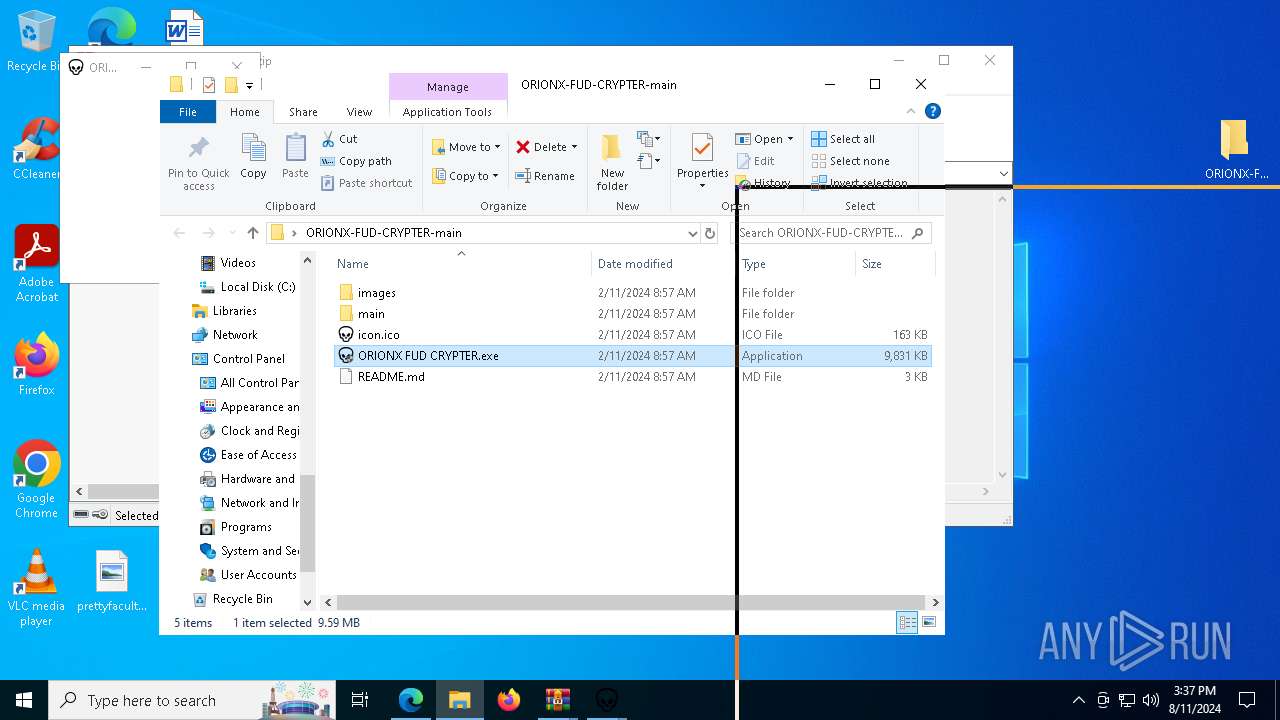
Manual execution by a user
- ORIONX FUD CRYPTER.exe (PID: 7396)
- ORIONX FUD CRYPTER.exe (PID: 7880)
- ORIONX FUD CRYPTER.exe (PID: 7004)
- ORIONX FUD CRYPTER.exe (PID: 4436)
- ORIONX FUD CRYPTER.exe (PID: 788)
- ORIONX FUD CRYPTER.exe (PID: 6592)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3916)
Reads Environment values
- identity_helper.exe (PID: 3144)
- cookie_exporter.exe (PID: 7592)
Checks proxy server information
- cookie_exporter.exe (PID: 7592)
PyInstaller has been detected (YARA)
- ORIONX FUD CRYPTER.exe (PID: 7396)
- ORIONX FUD CRYPTER.exe (PID: 1920)
- ORIONX FUD CRYPTER.exe (PID: 4436)
- ORIONX FUD CRYPTER.exe (PID: 6220)
- ORIONX FUD CRYPTER.exe (PID: 6592)
Create files in a temporary directory
- ORIONX FUD CRYPTER.exe (PID: 4436)
- ORIONX FUD CRYPTER.exe (PID: 7396)
- ORIONX FUD CRYPTER.exe (PID: 6592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
196
Monitored processes
58
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 788 | "C:\Users\admin\Desktop\ORIONX-FUD-CRYPTER-main\ORIONX FUD CRYPTER.exe" | C:\Users\admin\Desktop\ORIONX-FUD-CRYPTER-main\ORIONX FUD CRYPTER.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1508 --field-trial-handle=2280,i,14576415745350811180,13288359696066819255,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1448 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5544 --field-trial-handle=2280,i,14576415745350811180,13288359696066819255,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1716 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7212 --field-trial-handle=2280,i,14576415745350811180,13288359696066819255,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1920 | "C:\Users\admin\Desktop\ORIONX-FUD-CRYPTER-main\ORIONX FUD CRYPTER.exe" | C:\Users\admin\Desktop\ORIONX-FUD-CRYPTER-main\ORIONX FUD CRYPTER.exe | ORIONX FUD CRYPTER.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4260 --field-trial-handle=2280,i,14576415745350811180,13288359696066819255,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=6000 --field-trial-handle=2280,i,14576415745350811180,13288359696066819255,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2876 | "C:\Users\admin\Desktop\ORIONX-FUD-CRYPTER-main\ORIONX FUD CRYPTER.exe" | C:\Users\admin\Desktop\ORIONX-FUD-CRYPTER-main\ORIONX FUD CRYPTER.exe | — | ORIONX FUD CRYPTER.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 3116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --mojo-platform-channel-handle=6616 --field-trial-handle=2280,i,14576415745350811180,13288359696066819255,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3144 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6560 --field-trial-handle=2280,i,14576415745350811180,13288359696066819255,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
22 325
Read events
22 157
Write events
161
Delete events
7
Modification events
| (PID) Process: | (6264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (6264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (6264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (6264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (6264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 140253708 | |||
| (PID) Process: | (6264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31124484 | |||
| (PID) Process: | (6264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6264) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
60
Suspicious files
241
Text files
3 352
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6440 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe4e1c.TMP | — | |
MD5:— | SHA256:— | |||
| 6440 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6440 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe4e1c.TMP | — | |
MD5:— | SHA256:— | |||
| 6440 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6440 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe4e2b.TMP | — | |
MD5:— | SHA256:— | |||
| 6440 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6440 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe4e2b.TMP | — | |
MD5:— | SHA256:— | |||
| 6440 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6440 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe4e3b.TMP | — | |
MD5:— | SHA256:— | |||
| 6440 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
69
DNS requests
54
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7868 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7232 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ca376bd0-11fd-4e22-990e-0134bb331fdf?P1=1723966368&P2=404&P3=2&P4=mBRqpz60FfRoC%2fP4qtPs9AyYUtnMWtx8Q1doCJ41CQ%2feVNNkWlhIxpT5l6vIiaDgDesGa6HLwpGqnBqP1M5RmA%3d%3d | unknown | — | — | whitelisted |
7832 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7232 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ca376bd0-11fd-4e22-990e-0134bb331fdf?P1=1723966368&P2=404&P3=2&P4=mBRqpz60FfRoC%2fP4qtPs9AyYUtnMWtx8Q1doCJ41CQ%2feVNNkWlhIxpT5l6vIiaDgDesGa6HLwpGqnBqP1M5RmA%3d%3d | unknown | — | — | whitelisted |
7232 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ca376bd0-11fd-4e22-990e-0134bb331fdf?P1=1723966368&P2=404&P3=2&P4=mBRqpz60FfRoC%2fP4qtPs9AyYUtnMWtx8Q1doCJ41CQ%2feVNNkWlhIxpT5l6vIiaDgDesGa6HLwpGqnBqP1M5RmA%3d%3d | unknown | — | — | whitelisted |
7232 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ca376bd0-11fd-4e22-990e-0134bb331fdf?P1=1723966368&P2=404&P3=2&P4=mBRqpz60FfRoC%2fP4qtPs9AyYUtnMWtx8Q1doCJ41CQ%2feVNNkWlhIxpT5l6vIiaDgDesGa6HLwpGqnBqP1M5RmA%3d%3d | unknown | — | — | whitelisted |
7232 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ca376bd0-11fd-4e22-990e-0134bb331fdf?P1=1723966368&P2=404&P3=2&P4=mBRqpz60FfRoC%2fP4qtPs9AyYUtnMWtx8Q1doCJ41CQ%2feVNNkWlhIxpT5l6vIiaDgDesGa6HLwpGqnBqP1M5RmA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4560 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6012 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6440 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6664 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6664 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6664 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| shared |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
codeload.github.com |
| whitelisted |
update.googleapis.com |
| whitelisted |