analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
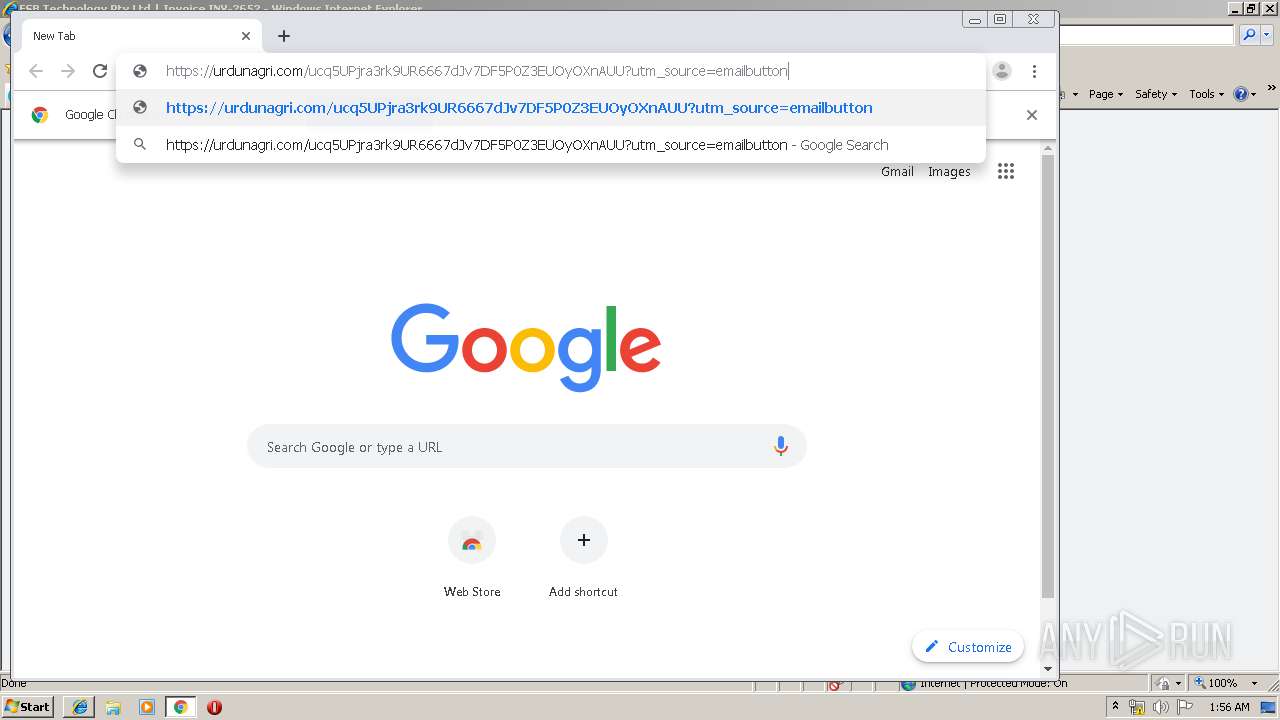
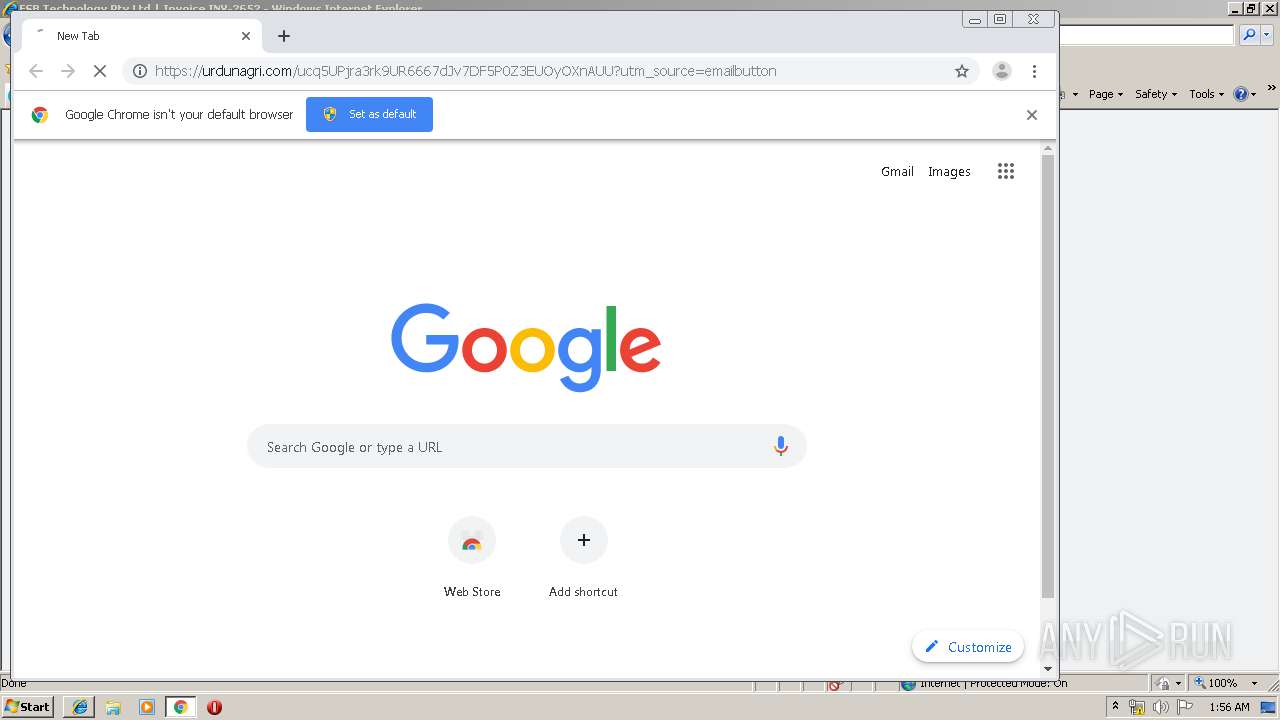
| URL: | http://r.fsbtech.com/mk/cl/f/ZiknRgBT-S3ZA_4NQWkeHRZAbNT4yS99TgOSRXSmB93K4JldFzJ88DH6RiaKcMX9dkyNsNwcyYagHoUuBWR2aLjA_52jTdO5Y4O5rUR3B2U84gMD9ejSMNAfHycgJK_oxCSMok2UZVzakWBWxfxtu0bn8rJCyv0Quq43gTGyluby8StE1TkQ7cxNHKqv2aUfJbAitWUcDx0MX8xaZUCCMHKsIr-_uGZYG3r0azv05ULUSsw |
| Full analysis: | https://app.any.run/tasks/4cc194d8-8e35-4261-ae9d-69ccad2365d0 |
| Verdict: | Malicious activity |
| Analysis date: | December 03, 2019, 01:54:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 357A3B0E9E248B5462A11F432C6A2B32 |
| SHA1: | FB65C0B05557BBBF32D009708A5F09924997F09C |
| SHA256: | 4BE5F73FC4C3CAA57C136B41FE6F5E338A1CADCEF310811852C771EA5B4DC4CA |
| SSDEEP: | 6:CML6YTnwN3cfjYvQpyA+V+26h4SYHbAEb4S:ZVegYCI+lhfY7l |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2480)
- chrome.exe (PID: 3384)
Changes internet zones settings
- iexplore.exe (PID: 2480)
Reads internet explorer settings
- iexplore.exe (PID: 3532)
Creates files in the user directory
- iexplore.exe (PID: 3532)
- iexplore.exe (PID: 2480)
Reads Internet Cache Settings
- iexplore.exe (PID: 3532)
Reads settings of System Certificates
- iexplore.exe (PID: 2480)
Reads the hosts file
- chrome.exe (PID: 2700)
- chrome.exe (PID: 3384)
Manual execution by user
- chrome.exe (PID: 3384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
30
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
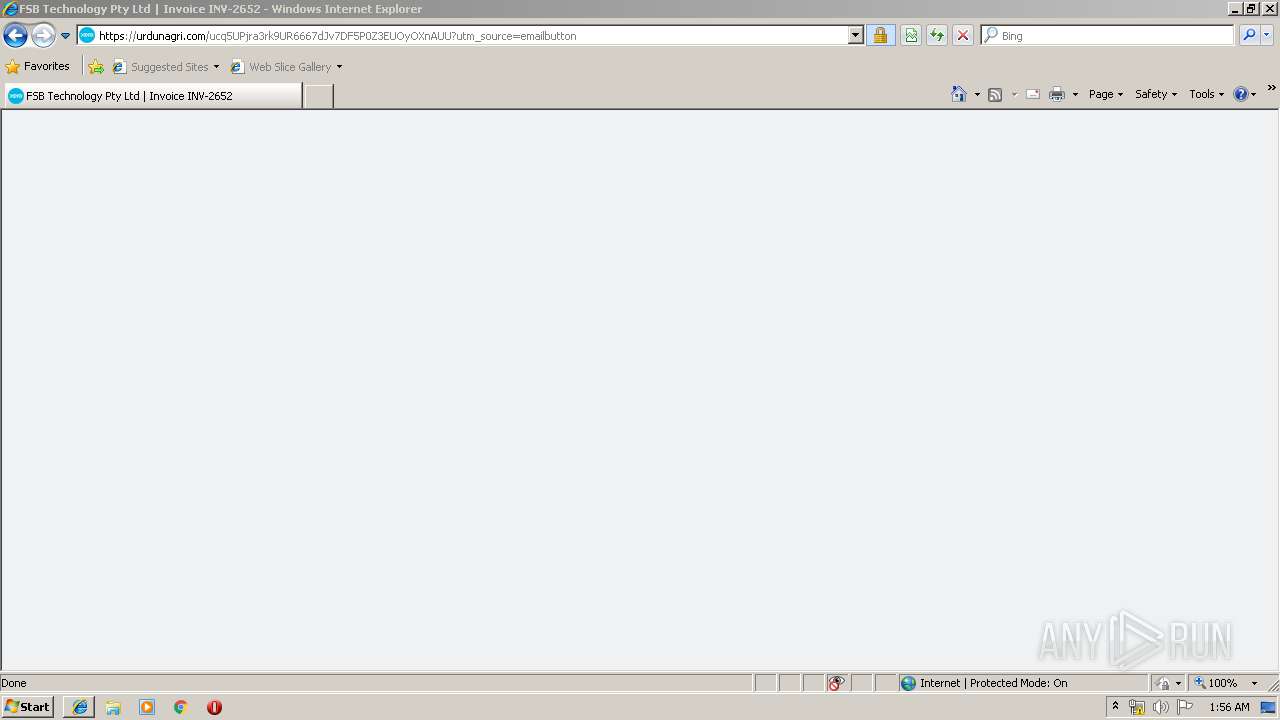
| 2480 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://r.fsbtech.com/mk/cl/f/ZiknRgBT-S3ZA_4NQWkeHRZAbNT4yS99TgOSRXSmB93K4JldFzJ88DH6RiaKcMX9dkyNsNwcyYagHoUuBWR2aLjA_52jTdO5Y4O5rUR3B2U84gMD9ejSMNAfHycgJK_oxCSMok2UZVzakWBWxfxtu0bn8rJCyv0Quq43gTGyluby8StE1TkQ7cxNHKqv2aUfJbAitWUcDx0MX8xaZUCCMHKsIr-_uGZYG3r0azv05ULUSsw" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) | ||||
| 3532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2480 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) | ||||
| 3384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 | ||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6feda9d0,0x6feda9e0,0x6feda9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 3780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3372 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,11388708891548592115,14836134329987801790,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8282757076188467307 --mojo-platform-channel-handle=1056 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 2700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,11388708891548592115,14836134329987801790,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6179212535409429610 --mojo-platform-channel-handle=1612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 4008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,11388708891548592115,14836134329987801790,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12418100045605807520 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,11388708891548592115,14836134329987801790,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14079987368321365265 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 4000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,11388708891548592115,14836134329987801790,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12173062274435263130 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
Total events
643
Read events
501
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
37
Text files
305
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\W3BM0LGX\LjA_52jTdO5Y4O5rUR3B2U84gMD9ejSMNAfHycgJK_oxCSMok2UZVzakWBWxfxtu0bn8rJCyv0Quq43gTGyluby8StE1TkQ7cxNHKqv2aUfJbAitWUcDx0MX8xaZUCCMHKsIr-_uGZYG3r0azv05ULUSsw[1].txt | — | |
MD5:— | SHA256:— | |||
| 2480 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2480 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\64B0QUU2\ucq5UPjra3rk9UR6667dJv7DF5P0Z3EUOyOXnAUU[1].txt | — | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:69A4E7E4E920CDB90581CD380371BD47 | SHA256:905F5F2DD5BC7CEBEB6DCE72960E3A34A284D644CE61E080156E228B8529D426 | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\[email protected][1].txt | text | |
MD5:5B5439F564E97B9A92E3A91796631C14 | SHA256:DF3A39E172DC9F4E6BBD07660D338B790F17B4244C62D9B5D3945E380B327473 | |||
| 2480 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019120320191204\index.dat | dat | |
MD5:9E0FD7B91CFA8A9C530BA8DFD804048B | SHA256:03EF83B18C9DBA990A746A712011A98D1080C0DDA3E400ADEC8F2165E65D9994 | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\W3BM0LGX\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:3280BB8808AE323D65EEBE115761D74F | SHA256:F67280C5C91509C57F1947921B2A888118C8A954E7E7522557F2AA78686EDAE0 | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\R7ZM9SPF\invoice_base-78413da86ba68c97f50128fc0ff86500[1].css | text | |
MD5:5DA78697D2771D19AA1C6C7CA274BBA6 | SHA256:2F436E02B87B6EAA876DCC1C9D3E6F6D4E858643B86E181995B1810A1D816DCD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
28
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2700 | chrome.exe | GET | 200 | 195.95.178.175:80 | http://r4---sn-pouxga5o-vu2s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.203.45.39&mm=28&mn=sn-pouxga5o-vu2s&ms=nvh&mt=1575338121&mv=m&mvi=3&pl=26&shardbypass=yes | RO | crx | 293 Kb | whitelisted |
3532 | iexplore.exe | GET | 200 | 104.16.232.163:80 | http://r.fsbtech.com/mk/cl/f/ZiknRgBT-S3ZA_4NQWkeHRZAbNT4yS99TgOSRXSmB93K4JldFzJ88DH6RiaKcMX9dkyNsNwcyYagHoUuBWR2aLjA_52jTdO5Y4O5rUR3B2U84gMD9ejSMNAfHycgJK_oxCSMok2UZVzakWBWxfxtu0bn8rJCyv0Quq43gTGyluby8StE1TkQ7cxNHKqv2aUfJbAitWUcDx0MX8xaZUCCMHKsIr-_uGZYG3r0azv05ULUSsw | US | html | 432 b | suspicious |
2700 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
2700 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
2700 | chrome.exe | GET | 200 | 195.95.178.177:80 | http://r6---sn-pouxga5o-vu2s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.45.39&mm=28&mn=sn-pouxga5o-vu2s&ms=nvh&mt=1575338121&mv=m&mvi=5&pl=26&shardbypass=yes | RO | crx | 862 Kb | whitelisted |
2480 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3532 | iexplore.exe | 104.16.232.163:80 | r.fsbtech.com | Cloudflare Inc | US | shared |
2480 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2480 | iexplore.exe | 184.25.218.150:443 | in.xero.com | Akamai International B.V. | NL | whitelisted |
3532 | iexplore.exe | 199.195.253.41:443 | urdunagri.com | FranTech Solutions | US | unknown |
3532 | iexplore.exe | 172.64.128.16:443 | sibautomation.com | Cloudflare Inc | US | shared |
2700 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2700 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2700 | chrome.exe | 216.58.210.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2700 | chrome.exe | 199.195.253.41:443 | urdunagri.com | FranTech Solutions | US | unknown |
2700 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
r.fsbtech.com |
| suspicious |
sibautomation.com |
| whitelisted |
www.bing.com |
| whitelisted |
urdunagri.com |
| unknown |
in.xero.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |