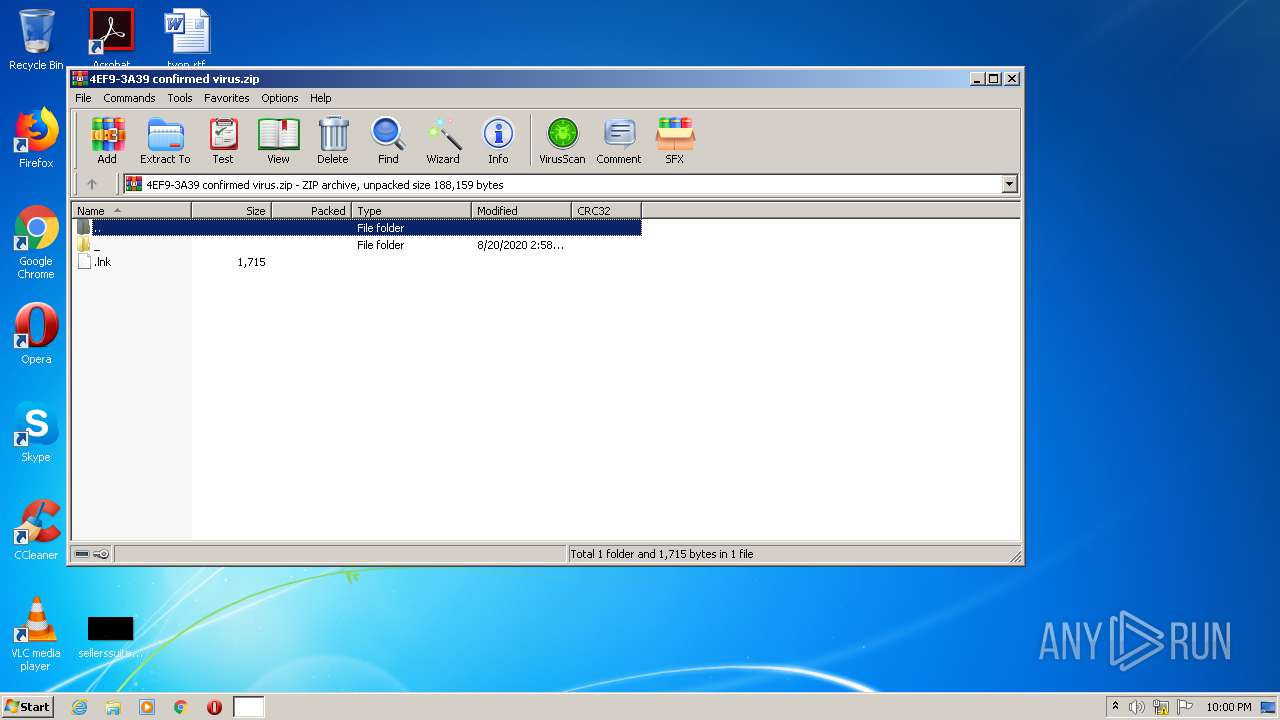
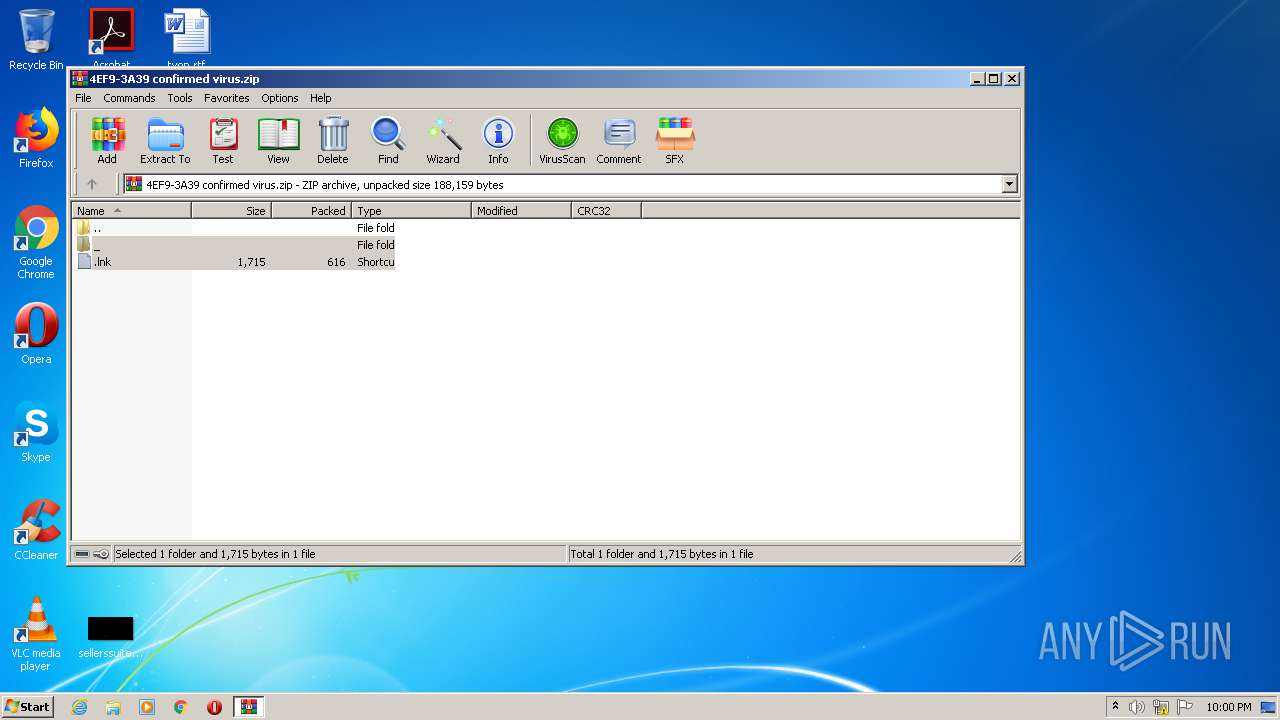
| File name: | 4EF9-3A39 confirmed virus.zip |
| Full analysis: | https://app.any.run/tasks/1f9ad839-48b0-436a-badc-4c71668e5371 |
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2020, 20:59:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8F4F84DC4C900CFB8F53B6D9C1295F5D |
| SHA1: | 84C35FC6B8E4857964DBACBEE3DDBA19AB41649F |
| SHA256: | 4BD99A6F745AEF6DBC2FD18CE9F3F95FCC6ADA5D7EC877814C792A129A026D2E |
| SSDEEP: | 3072:hgyBI/rnD/mLm6VuhseNimv5RxD9n4Ug6j2tIiGdh:dCrnLAm6VuhsFEvfHjPdh |
MALICIOUS
Application was dropped or rewritten from another process
- DeviceManager.exe (PID: 1932)
- winsvc.exe (PID: 2544)
- DeviceManager.exe (PID: 3840)
- DeviceManager.exe (PID: 2300)
Changes the autorun value in the registry
- DeviceManager.exe (PID: 1932)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 628)
- DeviceManager.exe (PID: 1932)
Starts itself from another location
- DeviceManager.exe (PID: 1932)
Creates files in the user directory
- winsvc.exe (PID: 2544)
INFO
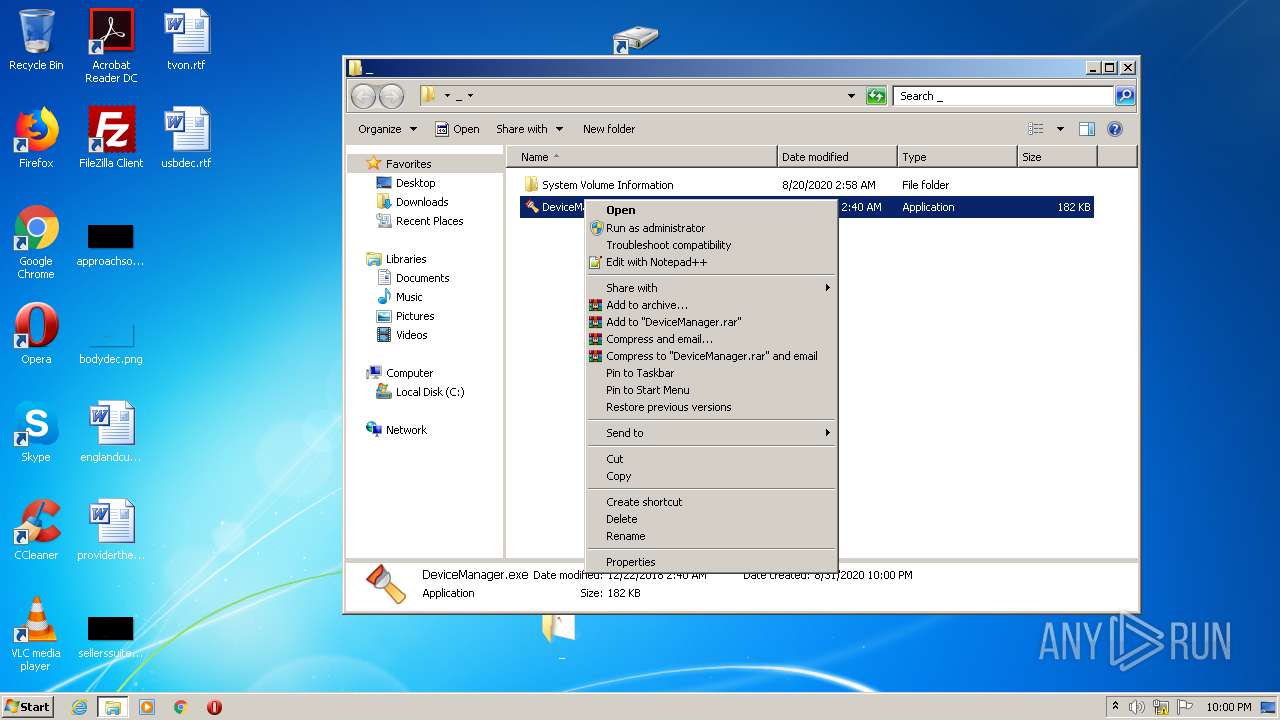
Manual execution by user
- cmd.exe (PID: 752)
- DeviceManager.exe (PID: 3840)
- DeviceManager.exe (PID: 2300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:08:20 02:58:21 |
| ZipCRC: | 0xbb1e456a |
| ZipCompressedSize: | 616 |
| ZipUncompressedSize: | 1715 |
| ZipFileName: | .lnk |
Total processes
43
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\4EF9-3A39 confirmed virus.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 752 | "C:\Windows\System32\cmd.exe" /c start _ & _\DeviceManager.exe & exit | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
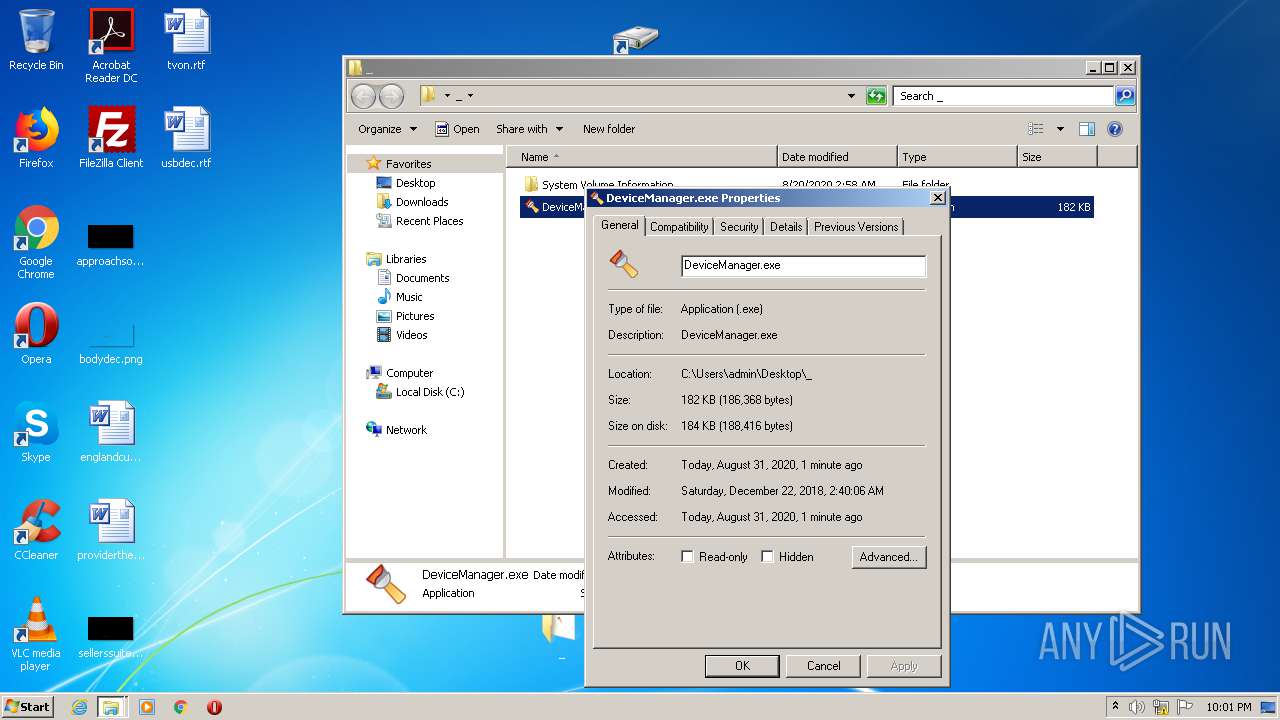
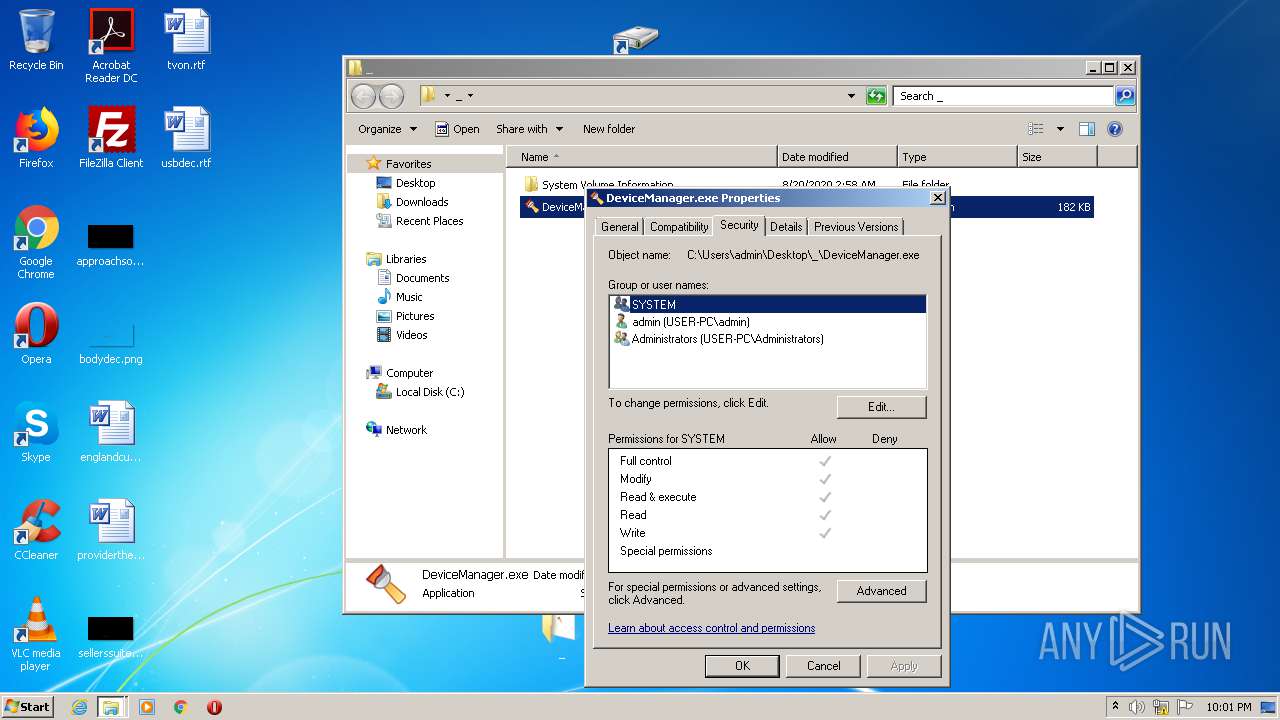
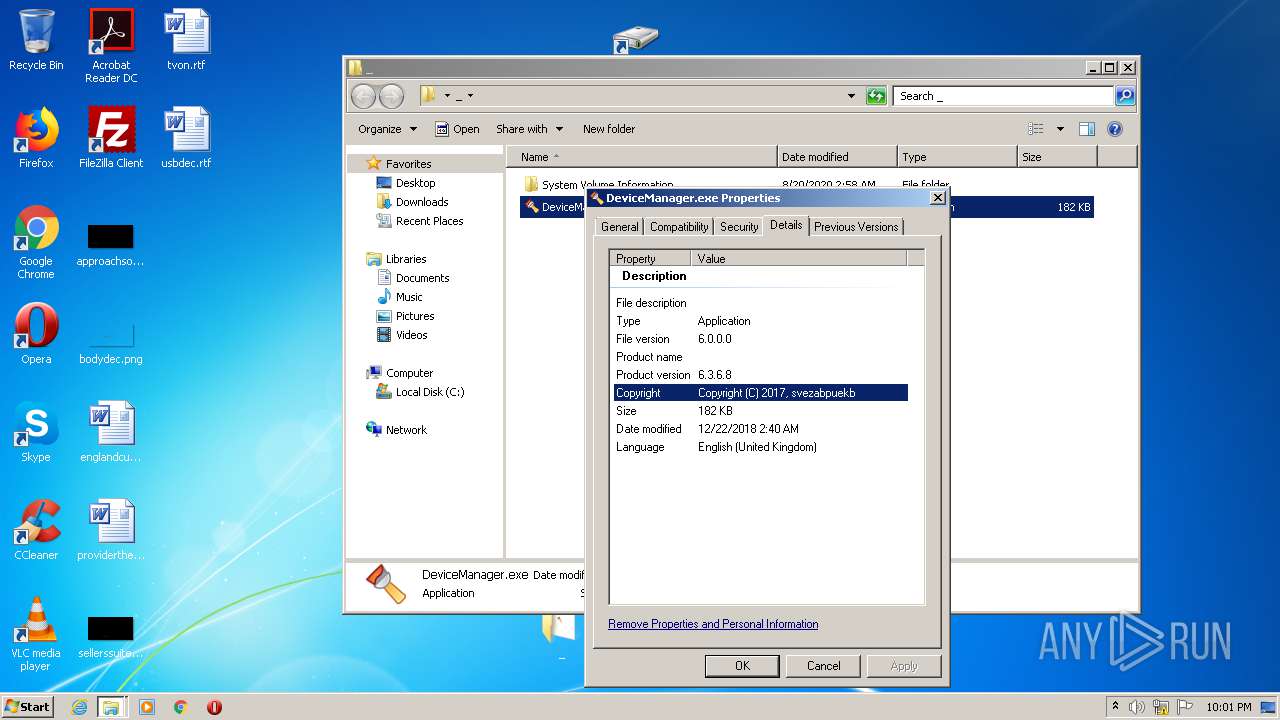
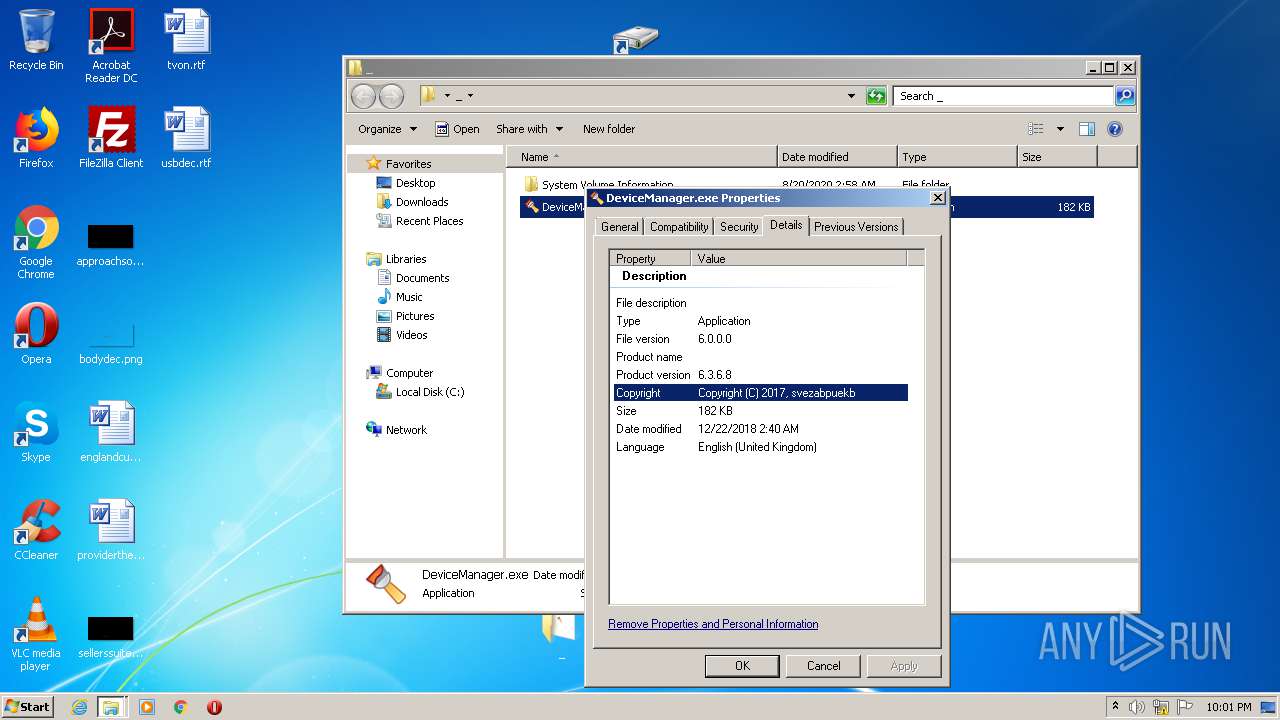
| 1932 | _\DeviceManager.exe | C:\Users\admin\Desktop\_\DeviceManager.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 6.3.6.8 Modules
| |||||||||||||||
| 2300 | "C:\Users\admin\Desktop\_\DeviceManager.exe" | C:\Users\admin\Desktop\_\DeviceManager.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 6.3.6.8 Modules
| |||||||||||||||
| 2544 | C:\Users\admin\T-3262485702408502460\winsvc.exe | C:\Users\admin\T-3262485702408502460\winsvc.exe | DeviceManager.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 6.3.6.8 Modules
| |||||||||||||||
| 3840 | "C:\Users\admin\Desktop\_\DeviceManager.exe" | C:\Users\admin\Desktop\_\DeviceManager.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 6.3.6.8 Modules
| |||||||||||||||
Total events
534
Read events
503
Write events
31
Delete events
0
Modification events
| (PID) Process: | (628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (628) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (628) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\4EF9-3A39 confirmed virus.zip | |||
| (PID) Process: | (628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (628) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
1
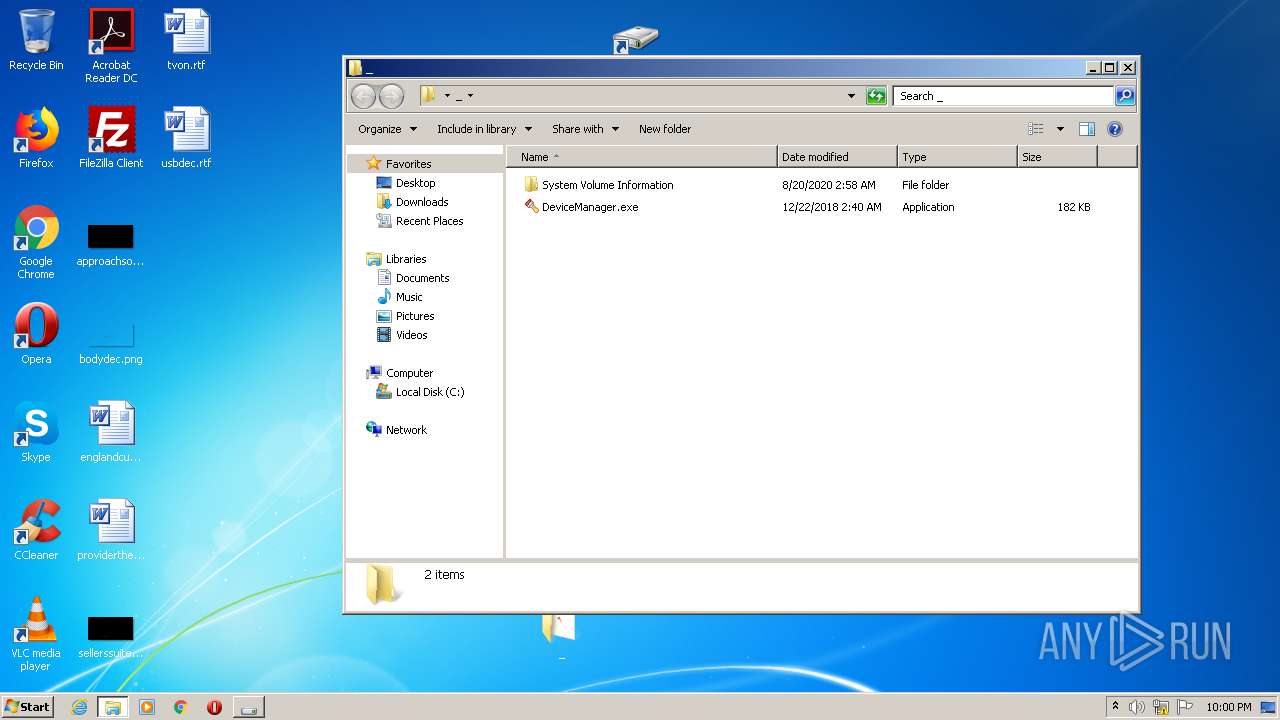
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa628.45010\.lnk | lnk | |
MD5:— | SHA256:— | |||
| 628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa628.45010\_\System Volume Information\IndexerVolumeGuid | binary | |
MD5:— | SHA256:— | |||
| 628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa628.45010\_\DeviceManager.exe | executable | |
MD5:60A2B1821D70DFBEAC4544E4D193E396 | SHA256:58DE3A083077A6F0F178BBF94EE2FC90875475E5277B687751E33CFA4E3CD519 | |||
| 1932 | DeviceManager.exe | C:\Users\admin\T-3262485702408502460\winsvc.exe | executable | |
MD5:60A2B1821D70DFBEAC4544E4D193E396 | SHA256:58DE3A083077A6F0F178BBF94EE2FC90875475E5277B687751E33CFA4E3CD519 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2544 | winsvc.exe | GET | — | 92.63.197.106:80 | http://92.63.197.106/t.php?new=1 | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2544 | winsvc.exe | 92.63.197.106:80 | — | — | RU | malicious |